Beruflich Dokumente
Kultur Dokumente
Internet Users Handbook. 2012, 2nd Edition, R513A
Hochgeladen von
Dr Don Yates Sr PhDCopyright
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Internet Users Handbook. 2012, 2nd Edition, R513A
Hochgeladen von
Dr Don Yates Sr PhDCopyright:
INTERNET USERS HANDBOOK
2012, 2ND EDITION, R513A - A COMPREHENSIVE GUIDE TO RECOGNIZING AND AVOIDING SCAMS WHILE ONLINE: SPAM, SECURITY AND DOING BUSINESS ONLINE
Dr Don Yates Sr PhD
INTERNET USERS HANDBOOK
INTERNET USERS HANDBOOK 2012, 2ND EDITION, R513a
A Comprehensive Guide to Recognizing and Avoiding Scams While Online: Spam, Security and Doing Business Online By Dr Don Yates Sr PhD Copyright 2009-2013
INTERNET USERS HANDBOOK
PREFACE .................................................................................................................................................. 9 INTERNET USERS HANDBOOK, 2012, 2ND EDITION, R513A .................................................................. 9 A COMPREHENSIVE GUIDE TO RECOGNIZING AND AVOIDING SCAMS WHILE ONLINE: SPAM, SECURITY AND DOING BUSINESS ONLINE ........................................................................................... 9 BACKGROUND ..................................................................................................................................... 9 INTERNET WORLD STATS..................................................................................................................... 9 EDUCATE YOURSELF .......................................................................................................................... 10 LET US TAKE, FOR EXAMPLE: ............................................................................................................. 10 SPAM AND SPAM LINKS..................................................................................................................... 11 INTERNET USERS HANDBOOK, 2ND EDITION, R513 ............................................................................ 12 INTERNET USERS HANDBOOK, 2013, 3RD EDITION, 3 VOLUMES........................................................ 12 1. OUR HANDBOOK AND ISA GROUPS .................................................................................................. 13 THE HANDBOOK HAS A TWO-FOLD OBJECTIVE: ................................................................................ 14 THIS HANDBOOK IS FOR THOSE THAT WILL HELP THEMSELVES! ...................................................... 14 INTERNET SCAMS ANONYMOUS GROUPS ......................................................................................... 15 2. DEFINING SCAMS AND FRAUD ......................................................................................................... 17 2.1 IS IT TOO GOOD TO BE TRUE? ..................................................................................................... 17 2.2 DOES THE OFFER PASS YOUR DUE DILIGENCE TEST? .................................................................. 18 2.3 WHAT IS THE OWNERS TRACK RECORD?................................................................................. 18 2.4 NON-DELIVERY ............................................................................................................................ 18 2.5 LACK OF SUPPORT ....................................................................................................................... 18 2.6 LACK OF ACCESSIBILITY................................................................................................................ 19 2.7 SCAMMERS ARE SPAMMERS TOO ............................................................................................... 19 2.8 ARE TRAINING, TOOLS AND RESOURCES PROVIDED? ................................................................. 19 3. DO YOUR OWN DUE DILIGENCE ....................................................................................................... 20 3.1 WHAT IS DUE DILIGENCE? ........................................................................................................... 20 3.2 12 SIMPLE DUE DILIGENCE MLM INVESTIGATIONS ..................................................................... 22 3.3 HOW TO CONDUCT ONLINE DUE DILIGENCE - BRUNO ............................................................... 24 3.4 DUE DILIGENCE TOOLS ................................................................................................................ 27 4. INTERNET CRIME IS BIG BUSINESS.................................................................................................... 29 4.1 2008 INTERNET CRIME REPORT................................................................................................... 29
CONTENTS
INTERNET USERS HANDBOOK
4.2 INTERNET FRAUD, SCAM AND CRIME STATISTICS - 2009 ............................................................ 29 4.3 FBI INTERNET CRIME REPORT 25/02/2011 .................................................................................. 32 4.4 TOP INTERNET SCAMS OF 2010................................................................................................... 33 4.5 SOME BASIC DEFINITIONS ........................................................................................................... 37 4.6 SEARCH ENGINE PAGE COUNTS 11/09 ........................................................................................ 38 4.7 INTERNET WORLD STATS ............................................................................................................. 38 4.8 SO WHAT IS THE KEY TO SCAM AVOIDANCE? ............................................................................. 39 4.9 BUYING IS NOT A RATIONAL DECISION........................................................................................ 39 5. INTRODUCTION TO INTERNET SCAMS AND FRAUDS ......................................................................... 40 5.1 WHAT IS A SCAM/FRAUD?........................................................................................................... 40 5.2 WHAT IS THE PROFILE OF SCAMMER? ........................................................................................ 40 5.3 THE PSYCHOLOGY OF CONMEN AN INTERVIEW ....................................................................... 40 5.4 SCAMMERS PLAY ON YOUR EMOTIONS ...................................................................................... 44 5.5 OUR VULNERABILITY TO CONFIDENCE TRICKS ............................................................................ 45 5.6 THE PSYCHOLOGY OF BEING SCAMMED (VICTIM) ...................................................................... 45 6. COMMON INTERNET SCAMS ............................................................................................................ 47 6.1 ADVANCE-FEE FRAUD .................................................................................................................. 47 6.2 ADVERTISING SCAMS................................................................................................................... 47 6.3 AUCTION AND RETAIL SCHEMES ................................................................................................. 48 6.4 AUTOMOTIVE FRAUD .................................................................................................................. 49 6.5 CLICK FRAUD................................................................................................................................ 49 6.6 CLOUD COMPUTING SCAMS ....................................................................................................... 53 6.7 COUNTERFEIT POSTAL MONEY ORDERS ...................................................................................... 54 6.8 COUNTERFEIT CASHIERS CHECK SCAM.................................................................................... 54 6.9 CASH THE CHECK SYSTEM ........................................................................................................... 55 6.10 CALL TAG SCAM ......................................................................................................................... 55 6.11 CHRISTMAS/HOLLIDAY SCAMS .................................................................................................. 56 6.12 DATING SCAMS/ROMANCE SCAMS ........................................................................................... 57 6.13 DIRECT MAIL AND TELEMARKETING SCAMS ............................................................................. 58 6.14 DOMAIN NAME RENEWAL SCAMS ............................................................................................ 62 6.15 EMAIL SCAMS ............................................................................................................................ 62 6.16 FOREX SCAMS ............................................................................................................................ 65
INTERNET USERS HANDBOOK
6.17 GUARANTEED SIGN UPS ............................................................................................................ 66 6.18 IDENTITY THEFT ......................................................................................................................... 67 6.19 INTERNATIONAL MODEM DIALING ........................................................................................... 68 6.20 INTERNET FRAUD/SCAMS .......................................................................................................... 69 6.21 INVESTMENT SCHEMES/ STOCK MARKET MANIPULATION ....................................................... 69 6.22 MARKETING AND RETAIL FRAUD ............................................................................................... 70 6.23 MATRIX SCHEME SCAMS ........................................................................................................... 70 6.24 MICROSOFT BETA TEST HOAX ................................................................................................... 72 6.25 MONEY TRANSFERS FRAUD ....................................................................................................... 73 6.26 NIGERIAN HOAX SPAWNS COPYCATS ........................................................................................ 74 6.27 PAYPAL FRAUD .......................................................................................................................... 75 6.28 PHARMING ................................................................................................................................ 75 6.29 PHISHING ................................................................................................................................... 75 6.30 PTR/PTC SCAMS......................................................................................................................... 81 6.31 PURCHASE SCAMS ..................................................................................................................... 82 6.32 REMOTE ACCESS COMPUTER SCAMS ........................................................................................ 83 6.33 RE-SHIPPERS .............................................................................................................................. 83 6.34 SEO INTERNET MARKETING FRAUD ........................................................................................... 84 6.35 SMISHING .................................................................................................................................. 86 6.36 SPOOFING.................................................................................................................................. 86 6.37 SOCIAL NETWORKING DANGER ................................................................................................. 86 6.38 SKYPE SCAMS............................................................................................................................. 89 6.39 TICKET FRAUD............................................................................................................................ 89 6.40 TWITTER SCAM .......................................................................................................................... 89 6.41 TVI EXPRESS WORLDWIDE SCAM ALERT ................................................................................... 91 6.42 WORK-AT-HOME SCHEMES/BUSINESS OPPORTUNITIES ........................................................... 91 7. THE $1,000,000 PER DAY PTC/PTR SCAM ......................................................................................... 93 7.1 RETIRED AND BORED ................................................................................................................... 93 7.2 MY BIGGEST PTC/PTR ACCOUNT PCASH................................................................................... 94 7.3 MY USD 1M OR MORE PER DAY STRATEGY ................................................................................. 98 7.4 PUT ON OUR BUSINESS HAT ........................................................................................................ 98 8. PREPARING TO DO BUSINESS ONLINE? ............................................................................................ 99 8.1 PLANNING TO DO BUSINESS ONLINE?......................................................................................... 99
INTERNET USERS HANDBOOK
8.2 GENERAL ASSUMPTIONS ........................................................................................................... 100 8.3 WHAT IS AN ENTREPRENEUR?................................................................................................... 101 8.4 INVESTIGATE WHY ARE YOU HERE?........................................................................................ 103 8.5 HOW MUCH DO YOU KNOW ABOUT LEADERSHIP? .................................................................. 104 8.6 DO YOU HAVE A PASSION FOR BUSINESS? ................................................................................ 104 8.7 BELIEVE IN YOURSELF AND BOOST YOUR SELF-CONFIDENCE ................................................... 104 8.8 COMMITMENT .......................................................................................................................... 105 8.9 HOW ABOUT ATTITUDE? ........................................................................................................... 105 8.10 DO YOU HAVE A FEAR OF FAILURE? ........................................................................................ 105 8.11 ARE YOU A PROCRASTINATOR? ............................................................................................... 106 8.12 ARE YOU READY TO ACCEPT THE RISK? ................................................................................... 106 8.13 HOW MUCH DO YOU KNOW ABOUT THE FOLLOWING TOPICS? ............................................ 106 8.14 STEPS TO A GREAT BUSINESS PLAN ......................................................................................... 107 9. FOLLOW YOUR PASSION ONLINE BUSINESSES............................................................................. 110 9.1 COMMON QUESTIONS WHERE DO I START? WHAT IS BEST?................................................. 110 9.2 WHAT ARE YOUR INTERESTS? ................................................................................................... 111 9.3 THE IMPORTANCE OF PASSION ................................................................................................. 111 9.4 WHAT ARE THE BEST TYPES OF INTERNET BUSINESSES? .......................................................... 112 9.5 FIVE PERFECT 'SPARE-TIME' ONLINE BUSINESSES ..................................................................... 112 9.6 WHICH IS BETTER, A PRODUCT OR A SERVICE SITE? ................................................................. 115 9.7 10 REAL WAYS TO MAKE MONEY WITH YOUR WEBSITE ........................................................... 118 9.8 INTERNET BUSINESSES THAT ARE PRONE TO FAILURE .............................................................. 120 10. AFFILIATE, PYRAMID AND MLM PROGRAMS ................................................................................ 122 10.1 WHAT IS AN AFFILIATE PROGRAM? ......................................................................................... 122 10.2 TYPES OF AFFILIATE WEBSITES ................................................................................................ 125 10.3 DEFINING A GOOD AFFILIATE PROGRAM ................................................................................ 128 10.4 ISSUES WITH AFFILIATE MARKETING ....................................................................................... 129 10.5 PYRAMID SCHEMES ................................................................................................................. 133 10.6 MULTI-LEVEL MARKETING PROGRAMS ....................................................................................... 139 10.7 Matrix Schemes ........................................................................................................................... 143 10.8 TIPS FOR CONSUMERS AND BUSINESSES .................................................................................... 144 BEWARE OF ANY PLAN: ................................................................................................................... 144
INTERNET USERS HANDBOOK
10.9 FOR THE I DONT DO MLM READERS............................................................................................ 146 10.10 EBAY POLICY MLM, PYRAMID, AND MATRIX PROGRAMS.......................................................... 146 11. MANAGING YOUR ONLINE BUSINESS ........................................................................................... 147 11.1 GET COMFORTABLE................................................................................................................. 147 11.2 WORKING AT HOME ................................................................................................................ 147 11.3 SELF-DISCIPLINE....................................................................................................................... 148 11.4 MANAGING YOUR COMPUTER AND SOFTWARE ..................................................................... 148 11.5 MANAGING YOUR TIME AND COMMUNICATIONS.................................................................. 152 12. WHAT IS SPAM AND ITS IMPACT? ............................................................................................. 158 12.1 WHY SPAM? ............................................................................................................................ 158 12.2 HOW TO AVOID THE SPAM FILTERS ........................................................................................ 159 12.3 ALL I WANT TO DO IS SEND AN EMAIL AND MAKE SOME MONEY .......................................... 161 12.4 FIGHTING SPAM ...................................................................................................................... 162 12.5 WHAT HAPPENED TO SOCIAL ETIQUETTE?.................................................................................. 163 12.6 FIRST LEGAL CASE FELONY - SPAM .......................................................................................... 166 13. ADVERTISE YOUR BUSINESS.......................................................................................................... 167 13.1 ONLINE ADVERTISING.............................................................................................................. 167 13.2 ADVERTISING AIDA ............................................................................................................... 168 13.3 HOW TO CREATE NO-SPAM HEADLINES.................................................................................. 169 13.4 HOW TO ADVERTISE WITHOUT SPAM ..................................................................................... 170 13.6 TESTING AND TRACKING YOUR STRATEGIES ........................................................................... 173 13.7 SEARCH ENGINE OPTIMIZATION (SEO) .................................................................................... 174 13.8 BUILDING YOUR KEYWORD LISTS ............................................................................................ 175 13.9 WHY SEARCH ONLINE ADVERTISING IS VALUABLE .................................................................. 177 13.10 COSTLY SEARCH ENGINE OPTIMIZATION MISTAKES.............................................................. 178 13.11 HOW WEB ADVERTISING WORKS .......................................................................................... 179 13.12 IS THE ONLINE ADVERTISING INDUSTRY SHRINKING? ........................................................... 181 13.13 LIST BUILDING ....................................................................................................................... 183 13.14 BLOGS AND ARTICLES ............................................................................................................ 187 13.15 INCREASING BLOG TRAFFIC ................................................................................................... 189 13.16 EMAIL MARKETING ................................................................................................................ 191 13.17 FREE FOR ALL (FFA) & CLASSIFIEDS ....................................................................................... 194
INTERNET USERS HANDBOOK
13.18 PAY-PER-CLICK ADS................................................................................................................ 195 13.19 SAFELISTS .............................................................................................................................. 197 13.20 TRAFFIC EXCHANGES (TE) ...................................................................................................... 201 13.21 HOW TO INCREASE YOUR SALES UP TO 500%... .................................................................... 204 13.22 HOW TO KEEP YOUR #1 RANKING ......................................................................................... 205 14. FOREX (FX) FOLLIES - A GAMBLERS HEAVEN ................................................................................. 206 14.1 WHAT IS FOREX (FX)? .............................................................................................................. 206 14.2 BENEFITS OF FOREX TRADING ................................................................................................. 207 14.3 FOREX BROKERS ...................................................................................................................... 208 14.4 THINGS TO AVOID ................................................................................................................... 209 14.5 WARNING SIGNS OF A FRAUDULENT BROKER......................................................................... 209 14.6 THE FOREX CURRENCY PAIRS .................................................................................................. 210 14.7 THE TRADING PLATFORM ........................................................................................................ 212 14.8 FOREX CHARTS AND INDICATORS............................................................................................ 212 14.9 FOREX EXPERT ADVISORS AND ROBOTS .................................................................................. 213 14.10 THE FOREX MINDSET ............................................................................................................. 214 14.11 TYPICAL FOREX HEADLINES ................................................................................................... 216 14.12 FORGET THE FOREX HYPE ...................................................................................................... 221 14.13 IS FOREX A GAMBLERS HEAVEN? .......................................................................................... 221 14.14 MY FOREX EXPERIENCE ......................................................................................................... 222 15. PLAN AND PREPARE ...................................................................................................................... 225 APPENDIXES......................................................................................................................................... 227 A. EMOTIONAL TRIGGERS OR POWER SELLING WORDS..................................................................... 227 B. COMMON SCAM AND SPAM WORDS............................................................................................. 229 C. SCAMS AND CONFIDENCE TRICKS ................................................................................................... 233 TERMINOLOGY ................................................................................................................................ 233 NOTABLE SCAMS AND CONFIDENCE TRICKS ................................................................................... 233 PYRAMID AND PONZI SCHEMES ...................................................................................................... 234 CONFIDENCE TRICKS IN MEDIA ....................................................................................................... 234 SEE ALSO.......................................................................................................................................... 234 D. SCAM AND SPAM COMPLAINTS ..................................................................................................... 235 REPORTING INTERNET FRAUD ......................................................................................................... 235 OTHER SCAM/SPAM RESOURCES, REFERENCES OF INTEREST ........................................................ 236
INTERNET USERS HANDBOOK
E. BANNED, SCAM AND WATCH SITES ................................................................................................ 237 GLOSSARY OF COMMON INTERNET TERMS ........................................................................................ 238 GLOSSARY OF COMMON FOREX/INVESTMENT TERMS ....................................................................... 281 ABOUT THE AUTHOR .......................................................................................................................... 304
INTERNET USERS HANDBOOK
PREFACE INTERNET USERS HANDBOOK, 2012, 2ND EDITION, R513A A COMPREHENSIVE GUIDE TO RECOGNIZING AND AVOIDING SCAMS WHILE ONLINE: SPAM, SECURITY AND DOING BUSINESS ONLINE
Registered owners of this handbook are entitled to receive our 3rd Edition Free. Currently planned at 3 Volumes
Internet Crime Security Threats Internet Crime Scams and Fraud Related to Risk Management and Doing Business Online
BACKGROUND
2009. UCLA professor Leonard Kleinrock said: Its the 40th year since the infant Internet first spoke. The fridge-sized computer that sent the first email 40 years ago (1969) But crashed after just two letters were received. Kleinrock, who led the team that first got two computers to communicate online via a network called ARPANET, added: The Internet is a democratizing element; everyone has an equivalent voice. There is no way back at this point. We cant turn it off. The Internet Age is here The computer expert could never have imagined that the fledgling Internet one day would give rise to Facebook, Twitter and YouTube. He referred to spam emails, online scams and malicious software spread by crooks as an unexpected dark side of the Internet. The net is penetrating every aspect of our lives, Kleinrock told a audience of about 200 people in Los Angeles. The World Wide Web, www, or the Internet as we know it today was released 1991. Zakon Timeline Professor Kleinrock went on to say As a teenager, the Internet is behaving badly, the dark side has emerged. The question is when it grows into a young adult, will it get over this period of misbehaving? Daily News Los Angeles The handbook, first published 2009; started to address the dark side of the Internet as it impacts every online user; the student young or old whether online for socializing, gaming, research, shopping, studies, or all of the above. Every business online from an individual start-up to the world largest corporations face the risk of online security threats, spam, scams or fraud. Even Government bodies and organizations cannot avoid the increasing dark side of the Internet. Countries are able to hack into almost every system or network if not all, for internal spying. The dark side has always been around, but as the Internet user base grows, so does Internet Crime in the form of Security Threat and Scams and Fraud primarily through the social networks. Are your employees online during working hours for personal affairs?
INTERNET WORLD STATS
Internet World Stats offers us the Internet Big Picture.
INTERNET USERS HANDBOOK
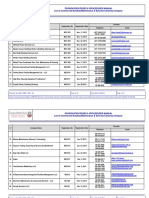
World Internet Usage and Population Statistics; June 30, 2012 Population (2012 Est.) 1,073,380,925 3,922,066,987 820,918,446 223,608,203 348,280,154 593,688,638 35,903,569 7,017,846,922 Internet Users Dec. 31, 2000 4,514,400 114,304,000 105,096,093 3,284,800 108,096,800 18,068,919 7,620,480 360,985,492 Growth Internet Users 2000-2012 Latest Data (%) 167,335,676 1,076,681,059 518,512,109 90,000,455 273,785,413 254,915,745 24,287,919 2,405,518,376 3,607 842 393 2,640 153 1,311 219 566
World Regions Africa Asia Europe Middle East North America Latin America / Caribbean Oceania / Australia WORLD TOTAL
The rise and popularity of Social Networking sites aided by the tremendous growth of mobile device access to the Internet has helped accelerate the growth and reach of Internet Crime. Yours personal devices and those owned by your spouse, sons and daughters, your business, agencies and even your government are at risk. As the Internet continues to multiple its user base, awareness of these various risks also grew. Groups, websites, Blog and Articles attempt to spread the word. Some focus on a particulate type of scam, i.e. Nigerian Letters, PTC Investigations, MLM, Email fraud, Identity theft, etc. As they try to make us aware; many have taken up the difficult task of maintaining lists of banned sites. Until Internet Users Handbook, first published, in 2009 as a support guide for the Internet Scams Anonymous (ISA) Groups. No one book, group, company, organization or website had addressed the bigger problem that is anyone that has an email address and logs onto the Internet is or may be exposed to any and all to the various online scams and/or malicious viruses. That email from an old friend that has not heard from in years opens with nothing but a dangerous link. That connection can either steal your keystrokes, passwords and/or identity; or it may simply disable your device or network.
EDUCATE YOURSELF
Educate yourself about Internet risk and risk avoidance. Learn to recognize the signs that may appear in the email headlines from an unknown source, the mysterious free download, the fake bank emails rather than simply pass them to someones outdated lists. Offline, the scammers usually spread their scam one-on-one with their potential victims; however, the Internet with a rate of growth nearing 50% per year of new users or Newbies, the scammers have found a haven for Internet crime. One scam or virus can reach thousands, if not hundreds of thousands of users or devices.
LET US TAKE, FOR EXAMPLE:
Sons and daughters say age 8 and above can meet their classmates on Facebook by using their parents information or by falsifying their birthdate. Unless we watch over them, they are able to befriend a predator. Everything about the predator can be falsified, a man pretending to be a teenage girl, pictures and all.
10
INTERNET USERS HANDBOOK
A recent Facebook malware disguised as a message allowing the member to operate a Dislike Button to go along with the like button. Activating this option then sent all of the members online activity, passwords, accounts information to the malware author. Your child could have activated this without out your knowledge leaving your computer and activities totally exposed. It spread virally. Sophos Naked Security Perhaps the children, even adults play games online. Other than the fact that the scammers are always looking for information and your credit card information, that next Free Game may contain a virus to shut down your computer or network. Children are exposed to inappropriate material. Most recently, the death of Whitney Houston popular to young and old alike created another virus. Warning: Whitney Houston autopsy video links on Facebook are not what they seem and led to a virus download of a fake adobe flash update from a bogus page. Sophos Naked Security While we cannot learn how many different user or newbies are here for socializing, games or both, we do know that when the world economy turns down, Internet crime goes up. As individuals turn to the Internet for a quick fix to their financial woes, the unemployed as well as the senior citizens that seek to increase their retirement income. Scammers are excellent salesmen; they anticipate your problems, answer your questions and stand ready to take your last dollar with false promises of overnight cures. Check your email. Even if you were not looking for such, the email headlines will entice some to open and read and take that chance of earning a quick dollar. If a single web expert can set up 15 authentic new websites per day, how many site can several scammers set up in a day? Multiply that by the unknown numbers of scammers! It is easy to see the value of knowledge over that of list service and reviews. Legitimate offline businesses are turning to the Internet to globalize their business. Many of them may be startups operating out of their garages or kitchens often, without some research, we cannot see. Larger companies often do have Internet policies for matters of email usage, socializing during working hours, but research indicates that few have risk management policies that address Internet crime and spam. A investigation of your local schools, universities or alumni will show the same result
SPAM AND SPAM LINKS
Can overload your networks Spread Internet crimes Spread viruses and threats that expose your systems and data Can disable your devices and networks Spam Blockers can suspend your email, and articles just for using a single word such as adult in the headline or text. Working Adults Adult Education Programs
11
INTERNET USERS HANDBOOK
INTERNET USERS HANDBOOK, 2ND EDITION, R513
A Comprehensive Guide to Avoiding Scams While Online is the first, an extraordinary 1 of a kind manual that brings an offline business success model online. Registered handbook owners have received this revision for free. R513 streamlines the 2nd Edition from its earlier over 500 pages in preparation for the expanded 3 volume, 3rd Edition Alphabetized, Improved Readability and other Enhancements that allow for Greater Understanding. Register owners of the 2nd Edition get the 3rd Edition for Free Registered owners receive additional support for free joining the free Internet Scams Anonymous Groups or subscribing to our various blogs
INTERNET USERS HANDBOOK, 2013, 3RD EDITION, 3 VOLUMES
Until the R513 release, the handbook had grown to over 500 pages. The 3rd Edition will place greater attention and coverage of Internet Crime. Its 2 components; Security Threats and Scams necessitate publishing the handbook in 3 volumes.
INTERNET CRIME SECURITY THREATS
Although covered in some minor detail along with Spam in the 2nd Edition; the handbook grew to over 500 pages This fascinating and complex issue needs a minimum of standalone volume Make it easy and user friendly for understanding
INTERNET CRIME SCAMS AND FRAUD
New and improved readability standalone volume
RELATED TO RISK MANAGEMENT AND DOING BUSINESS ONLINE
A standalone publication covering the newbie getting started online to companies starting or growing their business online We help educate and train the newbies startup businesses, as well as more seasoned professional that is seeking to establish or expand their online businesses through personal development and analysis and business planning Thanks for Reading and enjoy the handbook. Dr Don Yates Sr PhD
12
INTERNET USERS HANDBOOK
1. OUR HANDBOOK AND ISA GROUPS
Internet Crime, Scams, Fraud and Spam all impact our ability to do business online. Many newbies turn to the Internet as a quick cure for some financial ill; out of work, work at homes, too many debts, etc. They become frustrated and give up when they find themselves scammed and further in debt. They soon learn that there are no real quick financial cures online... Whether you are a seasoned business owner or a newbie to business, this Handbook has been written for you. It brings an offline business perspective to help prepare you for business online or offline. Offline, it is easy to see some of the business aspects that you must prepare for; product or service, location of your space, distribution, licenses, etc. Offline, few prepare themselves for personal or business growth and most fail to understand the risks that they will encounter in business. Perhaps, one of the simplest examples of risk comes from my days a newspaper delivery boy on a bicycle. Risks to my customers included late, wet papers or non-delivery of the news. Risk to me included the weather, wet news, bicycle breakdown, and dogs come to mind. You know, the unchained dogs that chase cars or anything that moves; very few bites but a lot of anxiety and commotion. I remember this one Great Dane that looked bigger than a horse; he never chased, barked or put me in danger, however, his stride would easily catch me, he always drooled and would seek me out to wipe his mouth. One of my offline business included business and development financing; as such, I encountered nearly every financial scam or scheme available. I was my own risk manager for my clients and my business. However, many of my clients of larger firms didnt even have a risk management program or policy and few understood what their business risks were. From a financial perspective; I needed to know what their and my risks were in analyzing and financing their requests. Starting a business offline, whether a franchise or new business is expensive and usually your choice evolves a product or service that you already have a passion for, perhaps a hobby or interest, at least something that you have some knowledge and understanding. This minimal understanding reduces your risk to scams and is a step toward success... It is true, starting a business online is inexpensive, but few understand business or business risks; they over simplify doing business online. Instead of following their passion, interest or hobby, newbies jump at the first sounds good, feels good opportunity proved to their inbox, only to jump to the next and the next opportunity. There is no business pattern, plan or strategy given to their behavior. Without question, Internet Crime, Online Scams and Spam are our greatest online business risk. Your inability or failure to understand and control your emotions, to recognize the broad range of scam you will encounter online, put you and chances of online business success in grave danger. New Internet users (newbies) are growing at a current rate of 44% or more per year and accelerating. Most of them have little or no background for doing business on or offline
13
INTERNET USERS HANDBOOK
Too many newbies turn to the Internet as a last resort to solve their financial crisis; be it out-of-work, excessive debt and related Further, most of our new users lack the business skills and a basic understanding of just how much impact that Scams would have on their potential for a successful online business. More and more businesses are taking advantage of the low cost Internet advertising and the affiliate models, so readily found online, but most fail to understand or include online spam and scams in their risk management plan. Our Internet Users Handbook along with our various Internet Scams Anonymous Groups help fill the void with a broad approach to Avoiding Internet Crime while Doing Business Online. While This Handbook was originally prepared originally as resource for our Internet Scam Anonymous (ISA) Groups, Its value serves a much greater audience, truly a one-of-akind Handbook and Resource for All Internet Users, Individuals, Businesses and Risk Managers that want to start, attempt or grow an online business. The handbook is largely written for the individual user reading, but Business and Risk Managers will find this a valuable resource for formulating their own Internet Usage and Risk Management Policies. Our goals are to combat these crimes by showing our members how to recognize and control their emotional propensity to participate in these scams. With one hand, we seek are helping to protect the members or readers, with the other we are helping by provide them with the tools to succeed online.
THE HANDBOOK HAS A TWO-FOLD OBJECTIVE:
How to Recognize and Avoid Scams To Properly Prepare You to Start or Grow Your Online Business As you may imagine, the Internet is an ever evolving and growing network and while the basics of doing business, as well as the scams may prevail; the strategies, business models, techniques also evolve. Therefore we will continue to try to keep up and make periodic revisions to this handbook which are provided to you freely as the owner of the current edition Forming or participating in business online is so easy and relatively cheap that nearly everybody thinks that they can do it, including the scammers. Business failure rates online are about the same as offline, say 95% over time. To be successful online, certain individual traits still apply; mindset, interest and passion. Because scams and fraud are the greatest online business risks; the due diligence process is just as important online, as offline. The scope and content of this Handbook covers the broad range of topics from personal assessment to scam identification and avoidance, spam, to starting, growing, managing and operating a successful online business,
THIS HANDBOOK IS FOR THOSE THAT WILL HELP THEMSELVES!
We can only provide the blueprint, you must take responsibility to learn and prepare for your own success.
14
INTERNET USERS HANDBOOK
Our Testimonials show that owners, members and affiliates that use this Handbook have one of the most comprehensive references available regarding Scams, Spam and all aspects of Doing Business Online. It is a compilation of years of experience and the Best of the Net, Articles, Blogs, Tools, Tips and How-To and other Resources for newcomers (Newbies), as well as seasoned veterans (but still able to learn new tricks). The use of the strategies and techniques offered herein is supported by our ISA Group members that participate and share their online experiences. If you are new to business, or online, then arm and prepare yourself for success online. Learn the business. As we study Scammers and their schemes, we find that they are Masters of Persuasion and the use of Spam. Microsoft advises us that over 97% of the emails the received each day are unsolicited. Another source says it is at least 60%. The problem is so big that it ties up both individual and organizational systems with junk, Spam. I am reminded of the garbage in garbage out days! To help resolve this problem, Internet Services Providers (ISP), email providers, advertising agencies and even Instant Messaging (IM) sites are all trying to reduce spam and scams by various blocking or screening strategies. However as a result, even legitimate email is sometimes spam blocked, because of a selection and use of the wrong word A great number of, networks, blogs, articles and groups do a great job dealing with various segments of Internet Crime. Much of their work has been complied herein as The Best of the Web, for I could not have said it better. Of course there are many others included that ranked high in our hundreds of searches. Throughout this Reference Handbook, we recognize and appreciate the contributions that these and others have made to the subject of Internet Crime, or Cybercrime, as well as Starting and Growing a Successful Business Online. Every effort has been made to respect copyright issues; sources have been identified, etc.
INTERNET SCAMS ANONYMOUS GROUPS
Ownership of our Handbook is supplemented by free membership in one or more of our Internet Scams Anonymous (ISA) currently located throughout the Internet. Although not necessary, these Groups give you the added benefit of communications with like-minded Internet users, both seasoned and newbies. These groups are Anonymous Groups because few of us will admit out mistakes and even fewer of us will learn from them. Yes, I too have been a victim. My experiences, lessons and research are included throughout this Handbook. The most basic lesson that I overlooked was my own failure to do my own online Due Diligence; something that I had done for years and helped others do offline. Second, I initially succumbed to the temptation of the online wealth headlines. If they can make that kind of money, why cant I? Regardless of whether we are an individual or a business, we always have a monetary need which scammers love to play to as they take our money. Most often it is fast money to them and none for us.
15
INTERNET USERS HANDBOOK
Elsewhere in this Handbook, we speak of the seniors trust in what they read, and the false promises offered by the Scammers. Online, we can forget the put it in writing for me. TIP: A word of caution as you progress online; everything and anything you see online can be fabricated, from fraudulent websites, emails that look like they came from the original source, payment proofs, and testimonials, all! We do not promise great wealth here, but we do offer you an opportunity to get on the right path to success, and to show you a strategy to control your emotional propensity to join these various scams and frauds. We stress doing your own due diligence to avoid the mistakes that I have made. We are especially concerned for those newbies that can least afford it, from wasting their limited resources on Scams. To sum this up, we are about business, your business. Again, This Handbook for all practical purposes is a Business Handbook, taking you from personal assessment, start-up, growth, operations, and the management of business risk. In this case, we focus on scams and spam risk.
16
INTERNET USERS HANDBOOK
2. DEFINING SCAMS AND FRAUD
In the 2nd Edition, we have decided that to follow our scheme of preparing you to do business online while helping you to understand that Scams are your greatest online business risk. Therefore, we have elevated our definition of a scam to a standalone chapter one of the reasons for our definition is that even with the vast resources available to us online, the definition of what is a scam, used interchangeable with the word Fraud, is extremely limited, while Scams themselves are rampant. Second anything that does not seem to work for someone is often also called a scam. Our best offer comes from Answers/Wikipedia the free encyclopedia (Scam) Internet fraud refers to the use of Internet services to present fraudulent solicitations to prospective victims, to conduct fraudulent transactions, or to transmit the proceeds of fraud to financial institutions or to others connected with the scheme. It is easy to see a trend now where the Internet is now facilitating the passing of these scams to your personal mobile devices. While this definition may be accurate, it needs to be broke down to be more of a working definition and to give online business users a better understanding of our interpretation of a scam, as we will show in the following: The Internet Scams Anonymous (ISA) Groups expect online businesses to do business as a business. However, we have to except that not all online businesses were founded by business minded professionals. If they are not accessible or their support systems are lacking; then they are not doing business, and are either poor businessmen or are just scamming us. These guidelines help provide a basis for our interpretation of a Scam
2.1 IS IT TOO GOOD TO BE TRUE?
Does It Makes Sense Is It Logical? Is it Realistic? Does It Make You Think Twice? Does It Satisfy One Of Your Needs? Is it Too Good to Be True? Said that already For many this is the first pass; is it too good to be true? Others see the hype as fulfilling their need for immediate cash flow, more money, increased income during retirement, work at home, etc. It creates an obviously unrealistic expectation that if it were not for the emotion tug to satisfy something, you would normally pass and save your money. Too many Newbies have turned to the Internet, perhaps as a last resort to solve their financial problems or crisis. They become prime targets for the first email that hits their inbox that offers them a solution - most are Scams that drives them further into debt. See how easy, you are out of work or have excessive debt. Too bad, but I can help, how about a data entry job or real my emails? ACCC
17
INTERNET USERS HANDBOOK
2.2 DOES THE OFFER PASS YOUR DUE DILIGENCE TEST?
Any business off or online should be approached as a business. Does it fit your criteria as a business that you can be excited about, does it fit your values, and is it one that you can promote. Sex sites make money online, but not all of us want to be part of that industry. Mobile communications, iPads, iPhones, Smart Phones and such all are the talk of the town, but I dont want ads on my phones, so I dont participate in schemes the put ads on others phone regardless of how much money I am passing up or leaving on the table. What does a Google or Yahoo search have to say about the program?
2.3 WHAT IS THE OWNERS TRACK RECORD?
If a professional can put up 15 new sites per day then certainly a scammer can do as well. New sites are always a problem, because so many members have that must get in first and start building your Team mentality. Great for pre-launches and some that never launches. In social networking, we can watch the members flock to a new site, start creating group after group for the same program to get their personal link out there, praising its virtues, and repeating the hype. In most cases, they get caught up in the emotional flow and promote the site without any form of due diligence. Sure, I will join a new site, on occasion, as I still research sites for scams and new techniques, but most often I dont commit or make payment until it has been around for a while. While I may mass market the new site with an impersonal link; I dont make it oneon-one it with friends, make groups, etc., at least not until I have seen it work and have gotten paid. Doing a routine Due Diligence for a new site will not work because of the lack of history, however, a WhoIs Ownership search will often help. As said elsewhere, hidden ownership turns me off on new sites. Too often the big dogs and have forgotten their roots and go into hiding rather than embracing business as usual and communicating and treating the last customer as they did the first. Of course others hide, because they should hide. For those that do provide ownership data, do your own researches on the owners; if a red flags turn up; I would pass on the program. What does a Whois search show for the owners data?
2.4 NON-DELIVERY
The site does not work, leads and links promised are not provided, and automated systems do not provided the stated results. Payouts are not received within the stated timeframes. The site is often off-line for non-payment of hosting, or whatever. One of the top consumer complaints
2.5 LACK OF SUPPORT
Support systems, forums and telephone numbers that do not respond to your technical or other questions; probably means that they are just a valueless front. Try submitting a support question to see if you get a response. Perhaps ask about some feature not answered in the Terms or FAWs.
18
INTERNET USERS HANDBOOK
2.6 LACK OF ACCESSIBILITY
Other than support, if it is hiding its identity on www.whois.com, and related sites, then it may be assumed that the owners have something to hide. Most successful businesses have channels of communication, support, help desks, forums, and responsive email. Having said that, see next. While I am here if these sites are making so much money; why dont they have international toll-free numbers and a 24/7 available for us? Check out all the big boys, Microsoft, Adobe, and others that have forgot their greatest assets - the customer. Are we not an international community? We dont want your 9-5 mentality, because we are online 24/7 somewhere in the world. One of my larger social network affiliations not only has a 9-5 mentality, but also shuts down their ticket system after working hours. They wont even take your problem or complaint on a ticket and promise a response with 24-48 hours. Makes me wonder just where are their priorities?
2.7 SCAMMERS ARE SPAMMERS TOO
Continual bombardment of emails from the same person or source with the same emails titles, etc. Scams are primarily delivered via email. On the other hand, unsuspecting affiliates are also great promoters of scams, a complaint that we often see in membership sites. More often, than not, these same Affiliates have neither done their due diligence nor have they ever been paid. These same affiliates tend to jump on every new program that comes along and start promoting it. Good, I am repeating myself! Hmm, I do that too as a trial balloon, on free to join sites.
2.8 ARE TRAINING, TOOLS AND RESOURCES PROVIDED?
As an affiliate, we expect that the company will help train us, or at least provide us with the training, tools and resources so that we can help ourselves. Sure, many offer tools and resources, but often they are non-specific to their site, where are the Welcome Letters, the how-to use the site or getting started guides, who is monitoring your success, where is the follow-up? If the program is not a scam, then why do the owners not monitor and provide for the success of their affiliates? Maybe the business owners are just not business minded. How many offline companies, unless they are using independent contractors, have an extensive training and follow-up program to help assure the success of their affiliates? After all, arent they trying to protect their brand? So perhaps some are not always a scam - just poor businessmen. Even with the best of times, partnerships break up, outsourced hosting fail, spam complaints, outsourced payment gateways fail, and business problems come with the territory on or offline. Even with a great program, success is up to you, one mans scam may be another mans bonanza.
19
INTERNET USERS HANDBOOK
3. DO YOUR OWN DUE DILIGENCE
Due Diligence in the offline world of business is done before you buy into or take over a business. The same goes for large land and real estate purchases, also accompanied by a real estate appraisal. You want to know the owners, what is the value of the company and its assets. If a store, shopping center, hotel and such, what kind of traffic is in the area, occupancy, demographics, etc.? How much and what kind of inventory do they have? The same goes for doing a Joint Venture or buying into a Franchise. If you are buying a big-ticket item such as a car, you will usually shop around. Perhaps you will check some form of Consumer Guide. The process is often long and drawn out. Offline it is or should be done by an independent third party. The due diligence process nearly eliminates emotional spending. Why should doing business online be any different even though the transaction can be accomplished quickly, for with less MONEY. However, online leaves the due diligence process you, no one is looking over your shoulder; well perhaps, except for the spouse or partner. We show how to do your own Online Due Diligence with a selected range and number of DD Tools for you to do your own research. Like everything else online, tools and techniques change. As you see such changes share it with us in our groups. We also post updates in our blogs which are later incorporated in a revision to this handbook.
3.1 WHAT IS DUE DILIGENCE?
Due diligence is a term used for a number of concepts involving either an investigation of a business or person prior to signing a contract, or an act with a certain standard of care. It can be a legal obligation, but the term will more commonly apply to voluntary investigations. A common example of due diligence in various industries is the process through which a potential acquirer evaluates a target company or its assets for acquisition. The care that a reasonable person exercises to avoid harm to other persons or their property An investigation or audit of a potential investment. Due diligence serves to confirm all material facts in regards to a sale. Generally, due diligence refers to the care a reasonable person should take before entering into an agreement or a transaction with another party.
INVESTOPEDIA EXPLAINS 'DUE DILIGENCE (DD)
Offers to purchase an asset are usually dependent on the results of due diligence analysis. This includes reviewing all financial records plus anything else deemed material to the sale. Sellers could also perform a due diligence analysis on the buyer. Items that may be considered are the buyer's ability to purchase, as well as other items that would affect the purchased entity or the seller after the sale has been completed. Due diligence is a way of preventing unnecessary harm to either party involved in a transaction. Investopedia Research and Analysis of a Company or Organization done in preparation for a business transaction (as a corporate merger or purchase of securities) M-W Dictionary
20
INTERNET USERS HANDBOOK
DUE DILIGENCE CAN BE DEFINED AS:
The examination of a potential target for merger, acquisition, privatization or similar corporate finance transaction normally by a buyer. A reasonable investigation focusing on material future matters. An examination being achieved by asking certain key questions, including, do we buy, how do we structure the acquisition and how much do we pay? An examination aiming to make an acquisition decision via the principles of valuation and shareholder value analysis.
THE DUE DILIGENCE PROCESS CAN BE DIVIDED INTO NINE DISTINCT AREAS:
Compatibility Audit Financial Audit Macro-Environment Audit Legal/Environmental Audit Marketing Audit Production Audit Management Audit Information Systems Audit Reconciliation audit. Wikipedia
BUT I AM READY TO ACT NOW
Sometimes DD is a just a troublesome mental thingy, because I am ready to act now!
Offline:
Buyers I want to make this large purchase and dont want to wait; but my banker, accountant, lawyer or someone requires that I have a Due Diligence done by a third party unrelated to the transaction. Costs are usually borne by the Buyer. Can be and usually is a long-drawn out process. In my experience, it is surprising how many big money players also react on emotion, save time, save the cost of doing their Due Diligence, only in the end to lose it all. Big enough money to pay cash so no DD requirement was imposed by another, i.e. lawyer, banker, etc. Example, if the seller creates a sense of urgency or perhaps demand, then Buyers are more likely to react more with emotion than reasonableness. A wealthy Malaysian Chinese Buyer wanted to do business with a Vietnamese Seller. The Agreement was drawn up in only 1 language, that of the seller, the buyer didnt have it translated into his own language, therefore didnt understand the fine print. The fine print contained a clause that the caused the buyer to default and forfeit millions in his down payment. Greed, stupidity, a scam, perhaps!
Online:
I want to join this program. I have no idea whether it is a scam, but it sounds great, but my online adviser (Dr Don) says slow down, and do your own Due Diligence. Fast process, can be done in less than a few minutes to an hour. Cost is zero. Why Not! Better Safe than Sorry Due Diligence can vary with the business type and the purpose. Some for legal, tax, financial, IT, operations, management and the list grows. In simplest terms for us; it means doing our homework.
21
INTERNET USERS HANDBOOK
Our objective is to avoid a fraud or scam, and to join a successful program. If it is a new site, then a Google search will provide us with no help. A Whois search may help us find who the owners to enable us to do further research. We need to know who the owners are, how long they have been in business, what is their track-record, are there any legal actions against them. Are customers or affiliates complaining, and have they ever been accused of a Scam or a Fraud? Right away, you can see that this process will slow you down. And sadly, most of you will not bother. While it is much faster than doing an offline due diligence process, it is our objective to slow you done enough to help control your emotional spending. Remember, many of your friends will also offer you something that they, themselves have not investigated; we will support them by joining, then we all lose.
3.2 12 SIMPLE DUE DILIGENCE MLM INVESTIGATIONS
SIMPLEST MLM INVESTIGATION
Get into the "BRAIN & PUSHBUTTON" MLM Detective mindset! Look at the supposed MLM Companys website. First suspect clue would be no street or city address, worse yet, only an email address, no phone number. Then look for the pictures and names of the owners of the company. Not having these on a website is a quick absolute reason NOT to join. Some wise, seasoned MLM distributors doing their Due Diligence Investigation will use http://earth.google.com/ to (free 7 day trial or $20) look at a satellite picture of the size and location of a supposed MLM Company office. Address = trailer house or home? That is a 911 = Run! RUN - TAKING ONLY BANK WIRES, MONEY ORDERS OR CHECKS Use your MLM Detective Investigative "BRAIN." Only use a credit card that will accept charge backs and returns? Honest companies allow refunds within 60-90 days (8 states require a year)! Money by FedEx - UPS only? Yikes! Scam Time! A trained MLM Detective will tell you the scam artists do this to avoid Postal Fraud charges! A PUB (private mailbox) address is an indicator of dodging Postal Fraud Investigators = 911 run a SCAM!
EASY MLM INVESTIGATION TRICKS
Next MLM Detectives will go to the Internet and enter the following into one or two of the major search engines: The MLM Company's name (owners too) and the word "scam". Go through two pages! Look for forum message comments for legitimate complaints (see below). Then do the same for "complaints, lawsuits, and news articles archived on search engines. Also check who registered the website domain of any new company claiming: amazing, incredible, proprietary, never seen before in the universe, revolutionary, products, services or technologies! Check http://www.whois.net/ for the domain lookup. Companies with good offerings would register a name 6 months to a year ahead of time. A warning on MLM due diligence for MLM Researchers! There are sad sites and forums that are unfairly negative toward all MLM - Network Marketing companies. Ignore these "Anti MLM
22
INTERNET USERS HANDBOOK
Zealots" and only look for appropriate information. A good MLM Detective will ignore 99% of their BS!
A SECRET DUE DILIGENCE TOOL
Alexa can give you Internet Web Ranking Due Diligence that on 1 out of 10,000 knows about. Grab scammers by the throat when they come to pester you! http://www.mlmwatchdog.com/mlm_due_dilligence_secret_alexa.html
DON'T SPEND OVER $500 TO START
There are over 22 states that require registration if an opportunity (not just MLM but includes MLM) requires you to spend over $500. Two states say it must be kept under $200. If a company says join for free and spent $501 for product - They had better be registered! A good MLM Detective will run if there is no way to join for under $500 See the new FTC warning (below) this MLM Detective due diligence article and my notes on the $500! SCAM example -Thinking it was MLM Here is a list by the FTC of States requiring "Biz Opp" registrations. Remember this if a recruiter is hustling you for over $500 and no registrations. Why join? They may get shutdown for not having the state Business Opportunity registrations! Why risk joining? You can lose time and money! There goes your opportunity! http://www.ftc.gov/bcp/franchise/netbusop.shtm
LOT OF NUTRITIONAL PRODUCT HYPE
Raise the dead? Live 130 years? Cure Cancer (which is an illegal claim for any nutritional)! If it is not a nutritional, skip down to next due diligence for MLM Detectives. Get a list of the MOST critical ingredients in the MLMs nutritional product and put them beside your computer. Go to the U.S. Government National Institutes of Health nutritional research website PUB MED. Go to Pub Med after you read the next two sentences! http://www.ncbi.nlm.nih.gov/sites/entrez Look up the major ingredient(s) by entering its name in the search box. Read through the scientific studies. Some may be complex, but the END sentence usually gives you a good idea if the study was a Plus or Minus for the product. Read over at least 10 articles use a piece of paper to keep track of studies like this Study #1 Good Study #2 good #3 What did they say? (Or just what?) Study #4 Good Study #5 Bad. Make your own judgment!
NEXT MLM DETECTIVE DUE DILIGENCE RESEARCH
MLM Detective "PUSHBUTTON" Go to the Better Business Bureau website for the city where the MLM-Network Marketing Company is located. Most are free. You are looking for the number of complaints the BBB has NOT resolved. If there are over 24, hold off joining, it very well could mean problems. MLM Detectives don't overly trust BBB reports but we the can be good indicators. Here is the National BBB Advanced Search dont use the quick search. http://search.bbb.org/SearchForm.aspx?mode=Business
23
INTERNET USERS HANDBOOK
WATCH OUT FOR HOT
An email solicits you to a "HOT" MLM, Party Plan or Network Marketing Company! Look for exclamation marks and capital letters used to lend legitimacy or urgency! Beware of disclaimers such as this is not a pyramid selling scheme or scam (legitimate offers don't contain such claims). Don't believe promises of fast wealth. If you feel, see or hear "Get Rich Quick! Run! If it sounds too good to be true, it usually is! MLM - Network Marketing takes some work, like any good Home Based Business. MLM, PARTY PLANS & NETWORK MARKETING COMMON SENSE Dont let the money over-excite you! Use the products or services being sold first! If they excite you, then look at the money. You should try sharing and selling the products/services to test them out. Spending some money to test a company and their offerings is a wise thing to do.
FOLLOWING RESEARCH FOR DEDICATED MLM DETECTIVES
Check with the Attorney General in the state where the company is located. Be very brief with your email or phone call and stick with asking, MLM Company XXX is located in city in your state, do you have complaints against Company XXX? A complete list of Attorney Generals is in MLM WatchDog COMPLAINTS Library.
READ THE FINE PRINT IN THE MLM CONTRACT
MLM Detective "BRAIN." These are the Enrollment Agreement or Terms of Agreement plus Policies and Procedures. These all together are a business contracts, enforceable in a court of law. The Distributor Rights Association says they shouldn't be over 15 pages long. Don't sign if you don't feel comfortable about the contract.
COPY THE PAY PLAN AND ASK QUESTIONS
Then find an expert to analyze it. If it only pays for signing up new people and not sales of products/services - run! There's a copy of my MLM Compensation Pay Plans Book on Amazon. Search for my name by author - Rod Cook. No, this is not a shameless promotion for my book. My book is the only one with big pictures, diagrams and detailed to help both the new person and expert. MLM Watchdog ethics let me say it's a good book! Plus my book has a whole chapter on avoiding Pyramid Schemes. MLM Detective
3.3 HOW TO CONDUCT ONLINE DUE DILIGENCE - BRUNO
Do you enter into business relationships, acquisitions, property investments, partnerships, or enter into a transaction without first verifying a companys identity, associates and affiliations? Most people do and you not alone. However most entrepreneurs still enter into business relationships with curiosity and unanswered questions they may have regarding a company or associate of a particular company. Wouldnt it be beneficial to you and or your company to limit liability and risk by conducting due diligence before entering into business relationships? By limiting your risk and liability, your business will have a far greater chance to succeed. By conducting simple due diligence and developing your own profile on any person or business, you will have a much better understanding of a particular business and its associates.
24
INTERNET USERS HANDBOOK
This is vital to your business decisions. 90% of the information you need to know can be found on-line. You just have to know where to look for it, and how to look for it. I will show you how you can develop your own profile on anyone or any business on-line free Example on a property investment acquisition: I contacted an individual who had placed a classified ad through an on-line newspaper under real estate finance/services for hard money lending, private moneylenders. I was really just trying to get a feel for the market in that specific area of the country. I do this by contacting various types of real estate professionals such Agents, brokers, title companies/escrow, private/hard moneylenders, bird dogs, wholesalers, etc. When I call, I get their personal name and the company name they work for (if any). If its a company its usually an LLC which is very common in the real estate industry or another type of corporate entity. Many times, people talk fast or not very clear on the phone. Therefore, I always have them spell out their name and company name and have them provide me any additional contact numbers that they can provide should I need to speak with them at another time. When the subject I am speaking to on the phone tells me the name of the company he or she represents and it is a corporate entity such as an LLC, S-Corp, partnership, etc. I know right away I can get the corporate members names within a few minutes. I will first go to the states web site in which the individual claims to conduct business in and lookup the entity online by the name of the company. Just about all the states in the US have free online searches at their web sites where you can lookup information about a corporation by company name or agent names. Just go to your favorite search engine like Google or MSN and type in the name of the state and corporations. Example Arizona Corporations, Texas Corporations, Nevada Corporations. The search engines will typically return the results youre looking for within the first two organic search result listings. Once you get to the states web site you will need to find where on the web site you can look up a Corporation. Usually it will just read Look up Corporations. Type in the name of the company and you can find out all corporate members, addresses, resident agents, corporate status- good standing- dissolved, revoked, etc. What I typically do is find out if the name the subject provided to me on the phone is indeed an actual member of the corporation, and then I run his or her name through the states database and see if he or she is involved in any other types of corporations. I find that is quite common to have members involved in several corporations. Sometimes you will not find a companys name in the specific states database. There could be a few reasons for this. The company may be a sole proprietor, or the company is registered in another state but has not filed as a foreign entity in the state they are doing business in. Sometimes companies operate this way. In this case it would be wise to search the Nevada and Delaware corporation web sites to determine if the company or agents are registered in either of those two states.
25
INTERNET USERS HANDBOOK
There are a great number of corporations that register in Nevada and Delaware simply because of the asset protection. It is difficult to pierce the corporate veil under the laws of those two states and that alone drives many, many companies to register in those particular states. I then run the companies name and agents name through online courthouse records in the specific county where they are residing in or conducting business in. Again like with the states, most counties have some type of information that is accessible online. Civil, family law and criminal filings are what you would most be interested in. You can go to the National Association of Counties by going to- http://www.naco.org and look up the county of your interest and you will go to their web site and see what kind of records that are accessible on-line for you to search. If you dont know the name of the county, you can locate a County by just knowing the City and State by going to the US Census Bureau and searching their database located here: http://quickfacts.census.gov/cgi-bin/qfd/lookup?state=01000. Or you can locate a County by Zip Code by searching this database by just entering a zip code http://www.usatrace.com/Search.html As soon as you locate the counties web site that you want to search just run the subjects name and company name through the various online databases. It can be very interesting to what you might find through courthouse records. You should also run the subjects name, company name, and phone number, any addresses separately through Google- Using each category- Main Google, Google Groups, and Google News. I typically run the above search criteria through Google to see what I can find and where it links. You can also verify if any address is a mail drop (like Mail boxes Etc.) or if it is actually a street location by using a free database search located here: http://www.finaid.com/scholarships/maildropsearch.phtml
HOW MY TYPICAL INVESTIGATION STARTS
The individual that I recently contacted in regards to private money lending had provided me his name and company name when I asked, which is typical with any dealings on the phone. I already had his contact number from the ad that he had placed on-line in the classifieds under real estate finance/services. I first ran the phone number to see if it was a cell number or a landline number. I do that by going to http://fonefinder.net I then ran his telephone number through Google to see if it appears online anywhere. I enter phone numbers in Google like this: - area code-prefixphone number. Example- 111555-1212. Running this search gives me a good idea if the phone number he provided me has been used anywhere online. Sometimes I find a different name of the company other than what they provided, or I may find a web site where the phone number was used as a contact number, I may even find a personal add placed where the subject was trying to sell a classic car and the contact number matched that of which I already had. Or I can find out which forums the subject hangs out at, he may have used the phone number
26
INTERNET USERS HANDBOOK
there. If I find a website where the contact number I entered into Google shows up, I find out who owns the web site by searching the Whois directory located here- http://www.betterwhois.com I may find another name or indeed find out my subject owns this particular web site. I start developing my profile of the business and the subject themselves by initially starting with a simple phone number. I can find all kinds of interesting things by simply running a search through Google with the subjects contact telephone number. I then ran the company name that the subject had provided me by going online at the specific states website where I can look up and find out information about corporations. This will allow me to verify or reveal agents names. Sure enough he was a member of the corporation. However, the last name he provided to me was spelled and pronounced much differently than what was revealed with the corporation search. It was way off. I then went to the respective county web site to search online for civil and criminal records on the subject. I knew which county to search based on the subjects phone number and the zip code that was returned for the subjects address revealed in the corporation search through the states website. I found numerous civil filings on the subject regarding business dealings including an Exparte filed for a wiretap on the subjects phone number as well as family law cases involving domestic violence. I also found a criminal case-. Possession of marijuana Now it does not take a rocket scientist to make up ones mind if they would like to enter into a business relationship with this subject. There is a greater possibility that I might have issues with this individual and things may not work out so well in the future. There are many scenarios of why you would need to conduct due diligence on an individual or company. However, remember you should always verify or reveal information on an individual or company prior to entering into a business relationship. Frank Bruno
3.4 DUE DILIGENCE TOOLS
TIP: To help control your Emotional Passion to take immediate action, do your own Due Diligence for the site, before you sign up, or to upgrade your account. Always start any due diligence with a Google Search. The results of that search may reveal enough negative comment to forget doing business. If it is a new site, it probably wont have a history, so then you go to the Whois tools. Always read the FAQs and Terms of Service, as part of doing your own Due diligence.
SITES WITH A HISTORY
A Google search
27
INTERNET USERS HANDBOOK
SITES WITH OR WITHOUT A HISTORY
A Google search is probably the best place to start. Look for the site reviews Red Flags for Scams. Keep in mind, that anyone can make a post reporting a site as an online scam or spam, just as anyone can post a review or testimonial favoring the site including the owners and friends of the scam. Try to dig deeper. http://www.whois.com/ Try it, enter a domain and see what you get: http://whois.domaintools.com/ or http://www.domaintools.com/ Try it, enter a domain and see what you get: http://www.betterwhois.com/ Try it, enter a domain and see what you get: http://www.alexa.com/ Try it, enter a domain and see what you get: http://w3wpy.org Try it, enter a domain and see what you get: http://maps.google.com/
28
INTERNET USERS HANDBOOK
4. INTERNET CRIME IS BIG BUSINESS
This Chapter will give you some background to the magnitude of the Growing Internet crime problem. It will introduce you as to how to get started on your journey to understand and recognize the signs of Internet Crime. The more you understand about these various scams, the more likely that you will be able to avoid being scammed. Scam Avoidance must rank up there with How do I turn this thing on? And OK whats next?
4.1 2008 INTERNET CRIME REPORT
The National White Collar Crime Centre has just released its eighth annual Internet crime report. In December 2003, the Internet Fraud Complaint Center (IFCC) was renamed the Internet Crime Complaint Centre (IC3) to better reflect the broad character of such criminal matters having a cyber (Internet) nexus. The 2008 Internet Crime Report is the eighth annual compilation of information on complaints received and referred by the IC3 to law enforcement or regulatory agencies for appropriate action. From January 1, 2008-December 31, 2008, the IC3 website received 275,284 complaint submissions. This is a (33.1%) increase when compared to 2007 when 206,884 complaints were received. These filings were composed of complaints primarily related to fraudulent and non-fraudulent issues on the Internet. These complaints were composed of many different fraud types such as auction fraud, nondelivery, and credit/debit card fraud as well as non-fraudulent complaints such as computer intrusions, spam/unsolicited email, and child pornography. All of these complaints are accessible to federal, state, and local law enforcement to support active investigations, trend analysis, and public outreach and awareness efforts. From the submissions, IC3 referred 72,940 complaints of crime to federal, state, and local law enforcement agencies around the country for further consideration. The vast majorities of cases were fraudulent in nature and involved a financial loss on the part of the complainant. The total dollar loss from all referred cases of fraud was $264.6 million with a median dollar loss of $931.00 per complaint. This is up from $239.1 million in total reported losses in 2007. Posted on 2009 April 1 by BBVM
4.2 INTERNET FRAUD, SCAM AND CRIME STATISTICS - 2009
Statistics regarding Internet scams and frauds are presented here as snapshots in time January 2009, but below are links to archived statistics from previous years. Web crime statistics are notoriously difficult to obtain, with many sources each calculating them in a different manner and different time frame, using a different source. To provide the most reliable picture, we use the Internet Crime Complaint Center's (IC3) statistics as a baseline. The IC3 began operation on May 8, 2000, as the Internet Fraud Complaint Center and was established as a partnership between the National White Collar Crime Center (NW3C) and the Federal Bureau of Investigation (FBI) to serve as a vehicle to receive, develop, and refer criminal complaints
29
INTERNET USERS HANDBOOK
regarding the rapidly expanding arena of cybercrime. These statistics have the advantage of the FBI's expertise, but the weakness of being 1 to 2 years out of date. To overcome this, we have added our own tracking system statistics to update the FBI / IC3 statistics.
BACKGROUND
The statistics for the current Top 10 frauds and scams list can be found below. A description of these scams is on this page. The greatest challenge in assembling a list and statistics of the frauds is that most fall into several categories. Consumers may characterize crime problems with an easier broad character, which may be misleading. For instance, a consumer that gets lured to an auction site which appears to be eBay may later find that they were victimized through a cyber-scheme. The scheme may in fact have involved SPAM, unsolicited email inviting them to a site, and a spoofed website which only imitated the true legitimate site. The aforementioned crime problem could be characterized as SPAM, phishing, possible identity theft, credit card fraud or auction fraud. In such scenarios, many complainants have depicted schemes such as auction fraud even though that label may be incomplete or misleading. The Internet Crime Complaint Center, in 2009 released its latest annual report on victims' complaints received and referred to law enforcement. From January 1, 2008 December 31, 2008, the IC3 website received 275,284 complaint submissions. This is a (33.1%) increase when compared to 2007 when 206,884 complaints were received. These filings were composed of complaints primarily related to fraudulent and non-fraudulent issues on the Internet. These complaints were composed of many different fraud types such as auction fraud, nondelivery, and credit/debit card fraud as well as non-fraudulent complaints such as computer intrusions, spam/unsolicited email, and child pornography. All of these complaints are accessible to federal, state, and local law enforcement to support active investigations, trend analysis, and public outreach and awareness efforts. From the submissions, IC3 referred 72,940 complaints of crime to federal, state, and local law enforcement agencies around the country for further consideration. The vast majorities of cases were fraudulent in nature and involved a financial loss on the part of the complainant. The total dollar loss from all referred cases of fraud was $264.6 million with a median dollar loss of $931.00 per complaint. This is up from $239.1 million in total reported losses in 2007. Other significant findings analyses of referrals include:
30
INTERNET USERS HANDBOOK
Non-delivered merchandise and/or payment were, by far, the most reported offense, comprising 32.9% of referred complaints. Internet auction fraud accounted for 25.5% of referred complaints. Credit/debit card fraud made up 9.0% of referred complaints. Confidence fraud ("con men"), computer fraud, check fraud, and Nigerian letter fraud (Also called "Advance Fee Fraud" or AFF) round out the top seven categories of complaints referred to law enforcement during the year.
DOLLAR LOSS
Reporting a Dollar Loss, The Highest Median Losses Were Found Among Check Fraud ($3,000), Confidence Fraud ($2,000), Nigerian (West African, 419, Advance Fee) Letter Fraud ($1,650)
AMONG PERPETRATORS
77.4% were male and 50% resided in one of the following states: California, New York, Florida, Texas, District of Columbia, and Washington. The majority of reported perpetrators (66.1%) were from the United States; however, a significant number of perpetrators where also located in the United Kingdom, Nigeria, Canada, China, and South Africa.
AMONG COMPLAINANTS
55.4% were male, Nearly half were between the ages of 30 and 50 and one-third resided in one of the four most populated states: California, Florida, Texas, and New York. Males lost more money than females (ratio of $1.69 dollars lost per male to every $1.00 dollar lost per female). This may be a function of both online purchasing differences by gender and the type of fraudulent schemes by which the individuals were victimized. Email (74.0%) and webpages (28.9%) were the two primary mechanisms by which the fraudulent contact took place.
31
INTERNET USERS HANDBOOK
For the full report, go to the IC3 webpage on statistics.
2008 PATTERNS
In 2008, that ranking has changed considerably - Lottery scams are number 1 followed by Auction scams, non- delivery and check fraud. LOTTERY SCAMS INTERNET AUCTION FRAUDS CONFIDENCE - NIGERIAN ADVANCE FEE FRAUDs (AFF) PHISHING AND PHARMING FOR IDENTITY THEFT "PASSIVE RESIDUAL INCOME" SCAMS CHECK (COUNTERFEIT) FRAUDS WORK-AT-HOME SCAMS MATRIX / MULTI-LEVEL MARKETING AND PYRAMID SCHEMES PROPERTY MORTGAGE AND INVESTMENT SCHEMES FINANCIAL INSTITUTIONS SCAMS
4.3 FBI INTERNET CRIME REPORT 25/02/2011
Mollie Halpern: More than 300,000 people lost a staggering 1.1 billion dollars from online crime in 2010. The Internet Crime Complaint Center, known as IC3, recently released that data in its annual report on online crime. Im Mollie Halpern of the Bureau, and youre listening to FBI, This Week. Bill Hinerman is the FBI unit chief of IC3. Bill Hinerman: Anybody and everybody can potentially become a victim of Internet crime. The most heartbreaking aspect is that we practically can never get the victims money back. Halpern: IC3 is a repository for victim complaints and provides federal and local law enforcement with information to pursue cases. Non-delivery of payment or merchandise, scams impersonating the FBI, and identity theft are the top three complaints. Hinerman says to be vigilant when using the Internet. Hinerman: If something is too good to be true it probably is. Halpern: To file an Internet crime complaint, visit www.ic3.gov. FBI Crime Report Internationally, according to the Cyber Criminals Most Wanted web site only half of the 70 countries recorded even have computer crime laws Cyber Criminals Most Wanted
32
INTERNET USERS HANDBOOK
As I see it, one of the key differences in offline business at least in the United States, is that we have the lawyers, the courts, the consultants, Federal Trade Commission, Consumer Protection Agency, Federal and State agencies and others almost stepping on each other to protect the consumers, and when in doubt rule in favor of the consumer. Yet we still are scammed. Some of the same is effort is being applied to Internet Crime; however, other countries from which these crimes are being initiated are not coming onboard. Internet Cyber Laws, but Scams and Spam are a worldwide problem, and we are a long way from getting worldwide attention. TIP: Complaints: We can file a complaint and become a member of the Statistics; you have a better chance of learning how to recognize and avoid such scams in the future; than getting your money back. In business, I used to say, put it in writing; then I could ask anyone of the experts vet the writing. Online, we do not have the face to face, and more often than not, the names, the legal entities, etc. to locate. Even if you have their names, it seems impossible to get access to them, and maybe it is a fictitious name or address. Now I say - do not believe all, if anything, that you read on the Internet with regard to doing business and/or making money on line. Any webpage can be fabricated, false testimonials, false payouts. On the web do not believe everything you read... As for me, sure, I have been scammed and have invested in excess of $50,000 so that you do not have too. Perhaps you have been scammed too and I suspect that many of the top gurus have also been scammed somewhere in their Internet learning curve. So what to do: join the scammers, or organize ourselves to help our members recognize Scammers and their Programs for what they really are A Scam preying on those that can least afford to lose their money. Help spread the word. I am sure all of us, individuals and business alike would like to make a quick buck or two to cure a cash flow problem. However, like most of you, I am not interested in taking money from or ripping of my mother, father, other relatives, or other people. Therefore, I have chosen to use my experiences and resources to help spread the word, educate them and help them reduce their chances of being scammed. Since you are here - you can help me, we can help each other.
4.4 TOP INTERNET SCAMS OF 2010
Jennifer Clarkes mother isnt as computer savvy as she would hope, so she calls her daughter before doing anything online. I get calls like, Im on YouTube and theres a window flashing and saying I need to update my computer, should I click it? says Jennifer*. I have to say, no, Mom, thats a scam.
33
INTERNET USERS HANDBOOK
While Ms. Clarke is trying to protect herself, she still illustrates a disturbing trend: more and more Internet users are buying into online scams. The FBI reported that the Internet Crime Complaint Center (IC3) received its 2 millionth complaint in November. The IC3 has been the go-to site for online fraud victims since 2003, but, according to Jennifer, most people probably havent heard of that. In fact, themselves a victim of identity theft in 2006, the Clarke family admitted theyd never heard of the IC3 or thought to report the incident. We just moved across town, says Jennifer. The year 2010 has been one of the worst years for online scams, with a 111.4 percent increase of malicious website creation since 2009. Websense, the leading information security company, made their online scam statistic findings public. Websense reports that this year, 79 per cent of malicious codes were found on legitimate, trusted websites such as search engine Google or blogging center WordPress. While email scams decreased by 0.7 percent, nearly 90 percent of fraudulent emails referred the reader to a malicious site, and 9 percent of scams still happen through email alone. Scammers are getting smarter. The invention of Search Engine Optimization (SEO) strategy means viruses can be directed towards a target audience, not just sent in all directions via email. SEO strategizing means a scammer can write a malicious code into a website and then add keywords, or tags, to the page. These tags are what major search engines like Google or Yahoo see during a search. Theyre also what are often displayed when the results of a search load. Using SEO strategy, the scammer can make sure their malicious page will appear near the top of the search results. Victims are actually downloading viruses during innocent web browsing and searching. 52 percent of data stealing attacks this year happened over the Internet. Once a virus has been downloaded from a malicious website or email, it wreaks havoc on computer systems. While most virus symptoms look the same the computer runs more slowly, numerous popups appear, some programs just wont run there are actually many different types of virus programs.
TROJAN HORSES
One of the most common virus programs is called a Trojan horse, named after the Greek myth. This is a virus that looks like a legitimate program, so users are tricked into downloading it and using the software. Trojan viruses gain unauthorized access to computer systems and are what cause those popups to appear, even when users are not surfing the Internet. Other common viruses include program viruses, which (much like Trojans) come in the form of a fake computer program often accompanied by an .EXE file extension. These viruses affect other programs in the computer.
STEALTH VIRUSES
Stealth viruses hide from antivirus software, concealing themselves inside other files, altering their file size, and other tricks to look like legitimate files. Boot sector viruses infect disks, and spread when a person lets their friend borrow a computer CD. All of these are classic viruses which can usually be caught with a good antivirus software or spam filter.
34
INTERNET USERS HANDBOOK
Unfortunately, though, antivirus software cant do everything. Virus writers wanting to steal information, or computer hackers, are evolving as fast as the software trying to shield them out. New viruses include names like article X viruses and Java control viruses, which can attack a computer through web browsers alone, just by having an unsuspecting user visit a website. These are especially devastating to users who dont disable pop-ups or block unknown Java programs from running. A new version of stealth viruses is also emerging, called polymorphic viruses which alter their coding, or virus signature, every time they infect a new file. This makes it very difficult for an antivirus program to even detect the problem, let alone delete it. Some protection programs dont even have the capacity to delete certain viruses, such as macro viruses, which infect any program or file which supports a macro programming language. Such programs as Microsoft Word or Excel support macro languages, and if infected, each document produced is also infected. These viruses can even travel if the unsuspecting user emails the document to friends or family. The goal, for a majority of these viruses, is to steal data. Keystrokes can be recorded, passwords extracted, or identification compromised. In one of the worst cases of data loss, Massachusetts South Shore Hospital reported the data loss of over 800,000 patient files from their systems this year 14 years worth of records. These records included patients full names, birthdays, addresses, phone numbers, drivers license numbers, SIN numbers, medical record numbers, bank account and credit card information, as well as diagnoses and treatments. South Shore Hospital referred to this loss as only a small subset, prompting negative reactions from many victims involved, but the dark reality is that there just isnt a lot that can be done. Another notable online heist this year came when hackers managed to expose the emails of online iPad users; some of these victims included government officials, military members, and the Department of Defenses advanced research team.
WIRELESS NETWORKS
Wireless Internet created an entirely new problem: Wi-Fi attacks. Open-access Wi-Fi points are becoming a huge problem. These free Wi-Fi points appear in airports, along train track routes, and even inside local Starbucks cafs. Because theyre open to everyone, experienced hackers can pose as coffee drinkers reading newspapers online while easily downloading banking information from the computer across from them. The new iPads, which are like portable Wi-Fi stations, are prime targets.
EMAIL SCAMS
One new email scam this year involves false emails that appear to be from a friend or family member, claiming the sender is stranded at an airport and needs financial assistance to get tickets home. Another new strategy is to embed malicious code into the email itself, so a user needs only to open the email to get scammed; no reading of material, external links, or attachments needed. Spam filters and antivirus programs have their metaphorical hands full trying to keep up with the new technology.
35
INTERNET USERS HANDBOOK
WORMS
One thing that can be expected, at least, is a worm. Every year, antivirus software producers prepare for the possibility of a dreaded worm. Its like the computer equivalent to a pandemic. Worms are viruses that dont need to attach themselves to any programs; rather than stealing information from a computer, they can corrupt entire networks of computers, a sort of mass infestation virus that networks and copies itself to new networks wherever it finds them.
STUXNET
This years surprise was Stuxnet, which became the first virus to affect industrial control mechanisms. Stuxnet not only impacted computers, it impacted nuclear power plants, dams, water treatment facilities, and factories in 155 countries. Stuxnet did the most damage in Iran, Indonesia, and India.
SCAREWARE
Another surprise this year was the massive hike in scareware programs. Scareware means fake antivirus, or spyware, programs that are actually malicious a cruel and ironic take on Trojan or program viruses. 40 percent of all false antivirus programs to date were created this year alone. Thats a scary number, but more terrifying is the thought of how theyre downloaded. While some scareware viruses market themselves through traditional pop-ups or advertisements, the growing trend is for coldcallers sometimes the hackers themselves to call victims and deliver a presentation by phone, asking customers to buy the product.
PHISHING, SMISHING AND SPOOFING
Holiday-related variations on phishing, smishing, and online data losses are appearing now. Spoofing, malicious emails and websites that look like more popular legitimate sites, are increasing. For example, PayPal.com, a trusted online banking transaction site used a lot for Internet shopping, is warning customers to stay away from its malicious duplicate PayPa1.com. (The number 1 is nearly identical to the letter l in some computer fonts.) Consumers looking for some extra holiday spending money are also falling victim to false work-fromhome typing jobs. There are two parts to these scams: in the first, victims must provide personal information to get the job. In the other part, once signed up, victims type up what look like numbers, business reports, or bank statements, but are actually facilitating money laundering, even unknowingly withdrawing money from their own bank accounts. Even worse, victims are sometimes charged by police because, however unknowingly, they have participated in a crime! Luckily, even with all these scams and viruses floating around, there are ways for consumers to protect themselves. McAfree, a popular security software publisher, mentioned some seasonal scams to avoid: charity phishing, false email banking, malicious holiday e-cards, fake invoices, fake requests on social networks, holiday-themed downloads such as screensavers, identity theft from shopping sites, and even the theft of entire laptops come up during the winter season. Consumers must also remember that a cell phone is a form of computer. Many cell phones now have Internet surfing capabilities, where consumers can check emails, social networks, online shops, and search engines. Some smart phones even run mobile browsers, such as Safari in the new iPhone 4.
36
INTERNET USERS HANDBOOK
However miniature they appear on the screen, these are real browsers, and malicious webpages can still appear, downloading viral contents or uploading personal information. McAfree warns consumers to watch out for any open Wi-Fi networks, even if the browser in question is a mobile phone.
Meanwhile, some nations are taking action. The European Network and Information Security Agency (ENISA) are testing cyber defense teams in 21 participating European Union nations. The EU has already set up a Cyber Crime task force in Europol, along with a Cyber Crime Training and Education Group. ENISA hopes this will be the first of many cybercrime force tests, and is planning to run joint exercises with the US or NATO.
EDUCATION
The best way to avoid scams is to be educated. Online shoppers should price check everything carefully; some products have labels such as the lowest price on them, which are simply not true. Shoppers should also be wary of fine print, as some online shops have costly return policies.
4.5 SOME BASIC DEFINITIONS
Always check site security before making an online payment; a secure site should have a web address which begins https. Once the transaction has been made, consumers should keep all the records of payment, and compare their bank statements to make sure the correct amount was charged. This year, online scams and viruses swindled people through cell phones, iPads, and even power plants. Its a problem that can be avoided by simple measures disabling pop-ups and keeping a good spyware protection program, for starters. But scammers are a fast evolving breed, producing malicious content that can now infect users who use search engines, open emails, or answer a phone call. Some victims dont even know theyve been scammed. Well, says Jennifer, its a big world. I guess it happens. Its probably happening right now. SamTitlston SEO
Internet
Scam Anonymous
Fraud
The Internet is a combination of several media technologies and an electronic version of newspapers, magazines, books, catalogues, bulletin boards, and much more. This versatility gives the Internet its power. A fraudulent business scheme; a fraud, swindle. Having an unknown or withheld authorship or agency: an anonymous letter; an anonymous phone call, anonymous group Having no distinctive character or recognition factor: "a very great, almost anonymous center of people who just want peace" A deception deliberately practiced in order to secure unfair or unlawful gain. A piece of trickery; a trick. One that defrauds; a cheat. One who assumes a false pose; an impostor. A Scammer
37
INTERNET USERS HANDBOOK
Rip-off, Ripoff, Rip off
A rip-off (or rip-off) is a bad deal. Usually it refers to an incident in which a person pays too much for something. A rip-off is distinguished from a fraud in that a scam involves wrongdoing such as fraud; a rip-off, on the other hand, is in the eye of the beholder. In one of his standup comedy routines, Dennis Miller jokes about seeing an ad in the National Inquirer: "Learn How to Avoid Ripoffs - Send $ 5."
4.6 SEARCH ENGINE PAGE COUNTS 11/09
4.6 SEARCH ENGINE PAGE COUNTS 11/09 Search Google Yahoo Bing Total Scam Pages 38,000,000 167,000,000 32,300,000 Internet Scam Anonymous Internet Rip-Off
25,300,000 93,200,000 8,000,000
139,000,000 61,000,000 135,0000
17,300,000 35,700,000 18,800,000
Note: Both Yahoo and Bing distinguish between rip-off, rip-off, or rip off. Google provided the same result for all combinations The online money at risk may not be as great as a real estate scam, college degrees, or other big ticket scams; but to a mom and pop, retired, or single parent that are looking to make money online, the scam dollars can add up. I lost $ 1,000 on just one scam plus miscellaneous costs. This is not to say that the big-ticket scams are not being pursued online. To be fair to the numbers above, we cannot easily identify how many of these pages are actually scamming sites because many of the pages include blogs or articles dealing with the subject. It is safe to say the number of scam sites will still be in the millions. We have a better chance of understanding the various scams than we do of identifying each scam site. Yes, there are legitimate ways to make money online. However, certainly there are more scams than winners. Further, the numbers of people that are new to the net are growing everyday as you may see from the following section:
4.7 INTERNET WORLD STATS
World Population 2011 Estimated Population 6,930,055,154 Internet Users Dec 2000 360,985,492 Internet Users Latest Data 2,095,006,005 Penetration Growth Population 20002011 30.2 % 480.4%
38
INTERNET USERS HANDBOOK
2000- 2009 Average Growth 40.4% 2011 43.67%
InternetWorldStats
See New Blog
If my math is correct, that is a current average of nearly 44% growth per year. As we push the Internet worldwide into our school systems and our households, the numbers will likely grow at even a faster pace than previously experienced. Yes more New Users and more new Scams and Scammers. Scammers are largely unregulated, hard to prosecute and in many cases it is hard to get a true identity or location.
4.8 SO WHAT IS THE KEY TO SCAM AVOIDANCE?
If the Scammers Use their Persuasive Powers to playing to Our Emotions, how do we control our emotions? Earlier Schneier on Security made a case that once scammed we are likely to be scammed again. Let us not condemn the great salesmen and thinkers, Zig Ziegler, Tony Robbins, Napoleon Hill and many others who provide us with content and value. Scammers, like great salesmen, are also Masters of the Power of Persuasion, and Persistence or follow-up (see auto responders) to get us to part with our money.
4.9 BUYING IS NOT A RATIONAL DECISION
You have heard me say it many times: to succeed out there in commercial cyberspace, you have got to speak to the need your customer feels. I do not say it just because I think it sounds clever - I have many good reasons, not to mention all of the history of successful selling to back me up. In addition, remember, online the customer rules like never before. You go ignoring your customers' needs and feelings and you will not be online for long. It is one of the caveats in convention sales training, in addition - if you want to sell, you have got to think like your customers rather than try to make them think like you. Or in Grok-talk, you got to surf a mile with their mouse. However, underlying that is an even deeper principle: People Rationalize Buying Decisions Based On Facts, But People Make Buying Decisions Based On Feelings Excuse me for shouting, but it is that important. The single biggest motivator in buying is not data, nor is it facts, its emotional response. Humans buy when they feel comfortable, when they feel they can trust you, when the process feels natural and reassuring, and when they come to the feeling that buying will make them feel good. (By the way, Martians are no different.) Fail to address that and most of your prospects will bail out sooner or later in the process. Tap into that correctly and your conversion rate will go up dramatically Buying Decisions
39
INTERNET USERS HANDBOOK
5. INTRODUCTION TO INTERNET SCAMS AND FRAUDS
This Chapter introduces the terms Scams and Fraud. Additional scams or an elaboration of these will take place in the following sections. We also provide our ISA Group Definition of a Scam. Learn to recognize the signs. Profiles of the Scammer and our susceptibility to being a victim are included here. Sample trigger phrases to tempt our emotional needs TIP: Remember this: it is easier to learn to recognize and avoid scams than it is to get your money back!
5.1 WHAT IS A SCAM/FRAUD?
From the earlier table, A Scam is a fraudulent business scheme; a swindle, great, but that leaves us with a number of questions and lacks examples. The range and depth of Internet Crime cannot be summed up with just a few words. This Handbook will expose you to a variety of scams with examples to help you understand, recognize and hopefully avoid them. While the focus of our group will lie in a variety of Scams for Business Opportunities, Traffic, Advertising, Pay to Read Swindles, Data Entry, Make Money At Home schemes and such, but we must be aware of the others. Any scam that can be arranged offline through telephone, paper or in person can be found on the Internet. If you have an email account, for sure some of these schemes will find their way to your inbox or junk mail folders, even though they maybe unrelated to your primary online business interests. Therefore, it is important that you have some brief knowledge and awareness of the scheme.
5.2 WHAT IS THE PROFILE OF SCAMMER?
Well, that was interesting: when I did a search for the profile of a scammer on Google and got 612,000 pages, but... The majority of them were related to Russian brides, Ghana Female Scammers, dating games, which will be covered in Chapter 6. So let us keep it simple and stick with a Master of the Power of Persuasion, and Persistence or followup (see spam), who appeal to our emotions get us to part with our money. I also like the use of words Confidence Man as they instill confidence in the minds of their victims. Read on
5.3 THE PSYCHOLOGY OF CONMEN AN INTERVIEW
How do conmen convince you to part with your money? Who are they? And how do they choose their victims? Learn their secrets from someone who has studied their dark arts. Magician Nick Johnson has some interesting insights into psychology of scams...and some suggestions on how to stop your money from going up in smoke! Damien Carrick: Now from secrets that get lifted from government, to how you and I sometimes inadvertently hand over information or money to con men. How do scammers manage to convince people to hand over their hard-earned cash?
40
INTERNET USERS HANDBOOK
To find the answer, perhaps we could talk to a police officer or a criminologist. But someone with a lateral take is magician Nicholas Johnson. He reckons that both magicians and scammers use the same box of tools: psychology and sleight of hand. Nicholas Johnson: I think what I love most about con artists and the world of scammers is that they are criminals who manage to get their victims to hand over their possessions freely. Most thieves and robbers and the like, tend to use force, or deception, in order for them to take things, whereas a con artist manages to get their victims to freely give up their stuff. And I think that is what really fascinates me the most. Damien Carrick: What makes people susceptible to con men? Nicholas Johnson: The main thing that really makes people susceptible to con artists is the idea that we are going to get something for nothing. Therefore, it really buys into our greed. It buys into sometimes our lust, and at the same time, sometimes even our sense that we are going to do something good. So we're going to get a great feeling from helping someone out, we're going to make some money, we're going to meet a beautiful girlit really ties into our basest desires, and that's what the con artist relies on. There was a study done in the UK just in train stations. They would go up to people and ask them to do a survey, and said 'If you could just answer these ten questions, we will give you a free pen at the end.' And one of the questions was 'What is your security number?' your PIN, or your email number and so on. In addition, a whopping percentage of people were more than happy to hand over that information to a complete stranger in a train station, in exchange for a free pen, because the person looked like they were official Damien Carrick: Not much of a bargain. Nicholas Johnson: Not much of a bargain, no, it was a nice pen, though. [On stage: I think it is important that if you are going to be a con artist that you learn how to lie to people. So what I thought we should do is actually bring up here on the stage some of the best liars in the room and see whether we can spot who's really good at it, and who's really bad at it. So I am just going to have a look. Just by looking at people who here looks as if they may be a good liar. So we are looking for people with sort of cold, dead eyes, the kind of people who would just stab you for your Metlink card. Oh, right there, brilliant, fantastic. Come up, and give him a big round of applause. Fantastic ...] Most con artists rely on this idea that the victim is in control. The victim is the one who is controlling the situation. So a great example of that is the classic Nigerian email scam, the person who writes to you and says, 'I've got this money that I need to get out of the country, and I need your help.' So you are in control, you can help them, you can do a good deed, you can make some money, you have got this fantastic opportunity, and the con artist needs your help. It is not the con artist doing you
41
INTERNET USERS HANDBOOK
a favor. So really, you feel like you are the one who is controlling the situation when really it is the con artist who knows the real deal. On stage: That is a good guess that is a very good guess, but it is not a correct guess, you owe me $2. No, no, no, we will settle up at the end of the night that is fine. OK? What you really should have done is to actually bet on this one over here, but it's completely up to you whether you want to call me a liar and bet over here or whether you want to go with my choice, which is right there. So what is it going to be? Are you going to bet there, or are you going to bet there? Am I telling the truth, or am I lying? OK, you do realize I am a con man, that is $4 you owe me, OK, it is actually right there.] Damien Carrick: Now you cut your teeth around carnival people and circus people, but have you also spoken to, or learned skills from the Real McCoy, the actual con men, the actual criminals? Nicholas Johnson: Yes, I think the real con artists are the people who can really teach you the most. You can read books about it, you can talk to people who have had experience, the victims, but unless you can really get inside the mind of a con artist, you really will not ever understand exactly how it works. I've communicated a lot with some of the Nigerian scammers, the people who write those emails, because if they think maybe they're going to make a few dollars, they're always happy to spill the beans. And it is amazing that most of those people see it as a legitimate job. For them it is a bit like being a telemarketer, they are just working in an office, in a cubicle, sending out emails, trying to get leads just like a salesperson. Damien Carrick: And they were happy to have an email dialogue with you? Nicholas Johnson: They were, yes, but obviously they were fairly cagey about exact details of who they were and what they were doing, but I was surprised, many of them admitted that they were working for organized crime figures and organizations in their home country of Nigeria. Many of them were quite happy to say that they worked on commission and they made a bit of money based on how much money they brought in, and they were quite upfront about it. I think for a lot of con artists they are very proud of their work, and they like people to know exactly what they have gotten away with. Nicholas Johnson: Yes, it is interesting the justifications that con artists use. Some say it is a job, just like any other, 'I'm no different from a used car salesman, I'm selling a dream instead of selling a car.' So I like that one. The other explanation is, 'You can't con an honest man.' Now that is this idea that because you are buying into people's greed and their gluttony and their lust and so on, that those people are guilty. The victim is just as guilty as the con artist, and therefore they get what's coming to them.' Of course we know that is just not true and that it is really just an excuse that they are using.
42
INTERNET USERS HANDBOOK
Damien Carrick: Tell me about some of these short cons that the Australian people that you have spoken to engage in. Nicholas Johnson: Sure. My all-time favorite one only makes the con artist a few dollars every time he does it, but I absolutely love it. These guys used to go door-to-door in the 1970s selling light bulbs and they would offer to replace every single light bulb in your house, so all your old light bulbs would be replaced with a brand new light bulb, and it would cost you, say $5, so a fraction of the cost of what new light bulbs would cost. So the man comes in, he replaces each light bulb, every single one in the house, and does it, you can check, and they all work, and then he takes all the light bulbs that he's just taken from the person's house, goes next door and then sells them the same light bulbs again. So it is really just moving light bulbs from one house to another and charging people a fee to do it. But there are all sorts of those homemaker scams, people offering to seal your roof so they say, 'We'll put a fresh coat of tar on your roof', or 'We'll re-seal your driveway'. In actual fact, all they do is get old black sump oil and smooth it over the roof or smooth it over the driveway. You come home and it looks like wet tar, and so 'Don't step on it for 24 hours', and of course, 24 hours later, they are long gone with the money, and you are left with a sticky, smelly driveway. Damien Carrick: You have spoken to some of the con artists. Have you ever spoken to any of the victims? Nicholas Johnson: I have. I have spoken to a lot of victims. I get a lot of emails from victims and for me, I really love the world of the con artist and I have a real grudging respect for what they do, and I love hearing the stories. But hearing from the victims, you really realize that these scams have a real financial and emotional impact on the people involved. I spoke to a man just the other day who'd lost $5,000 investing in what he thought was an Internet marketing company, and it was just a scam, it was basically an Americanbased pyramid scheme where the only way you make money is of course to try and convince other people to sign up to the scam. And he was absolutely heartbroken. He could afford to lose the money, for him it was only a few thousand dollars, but it wasn't that he lost the money that upset him so much, it was the fact that he really lost control, that he thought he was in control of what was going on, and that he really felt like that he couldn't trust the Internet, couldn't trust other people making particular offers to him, that he couldn't really trust himself and his decision-making abilities. And that's really I think for a lot of people, where they feel the hardest hit. [On stage: All right, so we are going to bet them. Here we go. You bet $1 and then I see your dollar and raise $10, then you bet $10 I bet $100, and then I bet $1,000, then it will be your shoes, I bet my jacket, you bet your wife, I bet my first-born child.
43
INTERNET USERS HANDBOOK
We put everything we own on the table, I reach into my pocket, put my last dollar down on the table and call, what do you have?' Two sixes. Yes, I think I have you beat, because I have one, two, three, four, five, six of a kind. Six kings, ladies and gentlemen. Give him a big round of applause though anyway. Thank you very much for playing. Thank you.] Damien Carrick: When I saw your show the other night, you hammered a nail up your nostril and it was horrible, it was funny, and it was compelling. And how common are scams involving that kind of physical illusion, and what kinds of motivations do they have? Nicholas Johnson: Sure. What you're referring to there is what they call 'psychic surgery', so you'll see photographs of people and video of people reaching inside somebody's stomach, blood spurting everywhere, they'll pull out a tumor which they'll throw into a bowl, wave their hands over the person's stomach and they're instantly as good as new and restored with absolutely no cut whatsoever. Or in the case of the nail in the head, they will get a nail and actually hammer it into somebody's face, just below the nostrils, that is sticking out horizontal. You maybe get a pair of forceps and sort of force them in there and pretend to pull something out, and these kind of gruesome, disgusting displays are so compelling to watch and so intense to experience that people feel that it must be doing you some good, it must be medical and it must be worth paying for. And sadly, lots of people hand over cash for these bogus operations. ABC.NET.AU/Law Report
5.4 SCAMMERS PLAY ON YOUR EMOTIONS
TRY THESE SAMPLES
You need money now, so they promise you cash in 24 hours, even 3 hours or less. You are a retired senior citizen and you need more residual income to supplement your retirement so they take your money and promise you the future. They tell you how to make a million dollars, if you only recruit three or more people. You never have to do anything else. They do not tell you how hard it can be to get three or more people when you are just starting Internet journey. You are a single parent mom and can barely make ends meet: They offer you work- at-home jobs paying you $100 per hour or $500 a day, or anything that gets your interest and motivated all this for $ 49.95. What can be better? I can stay home with the kids, work in my nightgown or whatever and still make money. How about you? Wouldnt you invest only $49.95 if you could earn $ 100 per hour or $ 500 a day, or even $ 22,500 per month? Sounds like a good investment to me.
BUT CONSIDER THIS
How many people in the real world make that much per hour or per month? Does it make sense of course not, then why should you or anyone else believe it? How about: Everything is on autopilot; Do nothing and make money Or we fall in love with a picture, and send money. How about I give $20,000 just to read one email? If you are not satisfied or you are worried about losing your money:
44
INTERNET USERS HANDBOOK
Not to worry, Let me offer you an unconditional guarantee; Or how about I will double your money back. (Who, What, Where, When and HOW)
HOW CAN YOU LOSE?
A better question, how to collect when you do lose? Once again, you have a better chance Of learning how to recognize and avoid such scams in the future; than getting your money back.
5.5 OUR VULNERABILITY TO CONFIDENCE TRICKS
Confidence tricks exploit typical human qualities like greed, dishonesty, vanity, honesty, compassion, credulity or naive expectation of good faith on the part of the con artist. Just as there is no typical profile for swindlers, neither is there one for their victims. Virtually anyone can fall prey to fraudulent crimes. Certainly, victims of high-yield investment frauds may possess a level of greed, which exceeds their caution as well as a willingness to believe what they want to believe. However, not all fraud victims are greedy, risk-taking, self-deceptive individuals looking to make a quick dollar. Nor are all fraud victims naive, uneducated, or elderly. A greedy or dishonest mark may attempt to out-cheat the con artist, only to discover that he or she has been manipulated into losing from the very beginning. Wikipedia Fascinating research on the psychology of con games: "The psychology of scams: Provoking and committing errors of judgment" was prepared for the UK Office of Fair Trading by the University of Exeter School of Psychology. From the executive summary, here is some stuff you may know: Appeals to trust and authority: people tend to obey authorities so scammers use, and victims fall for, cues that make the offer look like a legitimate one being made by a reliable official institution or established reputable business.
5.6 THE PSYCHOLOGY OF BEING SCAMMED (VICTIM)
VISCERAL TRIGGERS
Scams exploit basic human desires and needs -- such as greed, fear, avoidance of physical pain, or the desire to be liked -- in order to provoke intuitive reactions and reduce the motivation of people to process the content of the scam message deeply. For example, scammers use triggers that make potential victims focus on the huge prizes or benefits on offer.
SCARCITY CUES
Scams are often personalized to create the impression that the offer is unique to the recipient. They also emphasize the urgency of a response to reduce the potential victim's motivation to process the scam content objectively.
INDUCTION OF BEHAVIORAL COMMITMENT
Scammers ask their potential victims to make small steps of compliance to draw them in, and thereby cause victims to feel committed to continue sending money. There is a disproportionate relation between the size of the alleged reward and the cost of trying to obtain it. Scam victims are led to focus on the alleged big prize or reward in comparison to the relatively small amount of money they have to send in order to obtain their windfall; a phenomenon called 'phantom fixation'. The high value reward (often life-changing, medically, financially, emotionally or physically) that scam victims thought they could get by responding, makes the money to be paid look rather small by comparison.
45
INTERNET USERS HANDBOOK
LACK OF EMOTIONAL CONTROL
Compared to non-victims, scam victims report being less able to regulate and resist emotions associated with scam offers. They seem to be unduly open to persuasion, or perhaps unduly undiscriminating about whom they allow persuading them. This creates an extra vulnerability in those who are socially isolated, because social networks often induce us to regulate our emotions when we otherwise might not.
AND SOME STUFF THAT SURPRISED ME
Another counter-intuitive finding is that scam victims often have better than average background knowledge in the area of the scam content. For example, it seems that people with experience of playing legitimate prize draws and lotteries are more likely to fall for a scam in this area than people with less knowledge and experience in this field. This also applies to those with some knowledge of investments. Such knowledge can increase rather than decrease the risk of becoming a victim. Scam victims report that they put more cognitive effort into analyzing scam content than non-victims. This contradicts the intuitive suggestion that people fall victim to scams because they invest too little cognitive energy in investigating their content, and thus overlook potential information that might betray the scam. Schneier on Security
46
INTERNET USERS HANDBOOK
6. COMMON INTERNET SCAMS
In this chapter, we introduce you to several of the more commons scams found online. See Appendix C for what seems like an endless list of scams offered by Wikipedia
6.1 ADVANCE-FEE FRAUD
It is a confidence trick where the target is persuaded to advance sums of money in the hope of realizing a significantly larger gain. Among the variations on this type of scam, are the Nigerian Letter (also called the 419 fraud, Nigerian scam, Nigerian bank scam, or Nigerian money offer), the Spanish Prisoner, the black money scam as well as Russian/Ukrainian scam (also extremely widespread, though far less popular than the former) The so-called Russian and Nigerian scams stand for wholly dissimilar organized-crime traditions; they therefore tend to use altogether different breeds of approaches.
6.2 ADVERTISING SCAMS
To introduce you to the subject of advertising Scams.
EMAIL FROM ONE OF MY SITES
Hello, First of all, I highly recommend not using traffic packages! Believe me; most of these traffic packages simply have software in place where they send "hits" to your website not actual visitors. Most of these "guaranteed traffic websites" are scams. They take your money and never actually send you any visitors at all. We strongly advise our affiliates to not use these forms of promotion and use search engine advertising instead. Advertising on search engines may seem more expensive at first but they will result in much higher conversion rates and more referral commissions. It's not the quantity of visitors that counts, but the quality of traffic. Thank you for your patience and please do let me know if there is anything else I can assist you with. Regards, Morgan A. Client Support
DIRECTORIES AND ADVERTISING (FALSE BILLING)
A directory entry or unauthorized advertising scam is a scam that targets small businesses, trying to bill you for a listing or advertisement in a magazine, journal or business register/directory. The scam might come as a proposal for a subscriptions disguised as an invoice for an entry in a bogus international fax, telex or trade directory. Sometimes they are doctored to look like those used by genuine directory publishers. Alternatively, you might be led to believe that you are responding to an offer for a free entrybut in fact, the order is for entries requiring later payment. Another common approach used by scammers is to ring a firm asking to confirm details of an advertisement that they claim has already been booked. The scammer might quote a genuine entry or advertisement your business has had in a different publication or directory to convince you that you really did use the scammers product. If you refuse to pay, the scammers might also try to intimidate you by threatening legal action.
47
INTERNET USERS HANDBOOK
Warning Signs
You receive a call from a business directory or other publication youve never heard of, confirming your entry or advertisement. You receive a document in the mail that appears to be an invoice from a publication youve never heard of. The caller claims that the government requires you to be registered in their register. The caller reads out your listing or advertisement and you recognize it as a listing you put in a different publication.
Protect Yourself from Directory and Advertising (False Billing) Scams
Make sure the business billing you is the one you normally deal with. Always check that goods or services were both ordered and delivered before paying an invoice. Never give out or clarify any information about your business unless you know what the information will be used for. Try to avoid having a large number of people authorized to make orders or pay invoices. Never agree to any business proposal on the phone: always ask for an offer in writing. If you are unsure about any part of a business offer, ask for more information or seek independent advice.
Do Your Homework
If you think that the publication is a legitimate one and you may have authorized an entry, ask for proof of its existence. You should also make sure you keep written records of authorizations for advertising or directory entries so that if you receive an invoice or a telephone call, you can go back to your records to check it. Always get proof of the entry before paying anything. You do not have to pay for any directory entry that you did not specifically authorize in writing. Another way to look into the legitimacy of the directory is to ask for details of other local businesses who have previously advertised and check with them that they received what they paid for.
Decide
Never pay for an advertisement or entry you didnt authorize. If you receive a telephone call or an invoice that comes from a publication you have never heard of, or that you dont remember putting an entry in, dont pay or give out your details until you have looked into the matter further. Report Them If you have received a fraudulent directory entry or advertising invoice or phone call, or if you have sent money to pay for an entry or advertisement which you now realize is a scam, you can report it through the SCAM watch website. You should also spread the word to your friends, family and colleagues.
6.3 AUCTION AND RETAIL SCHEMES
Fraudsters launch auctions on eBay or TradeMe with very low prices and no reservations especially for high priced items like watches, computers or high value collectibles. They received payment but never deliver, or deliver an item that is less valuable than the one offered, such as counterfeit, refurbished or used. Some fraudsters also create complete web stores that appear to be legitimate, but they never deliver the goods. They take payment, but never shipped the order. In some cases, some stores or auctioneers are legitimate but eventually they stopped shipping after cashing the customers' payments.
48
INTERNET USERS HANDBOOK
Sometimes fraudsters will combine phishing to hijacking legitimate member accounts on eBay, typically with very high numbers of positive feedback, and then set up a phony online store. They received payment usually via check, money-order, cash or wire transfer but never deliver the goods; and then they leave the poor, unknowing eBay member to sort out the mess. In this case, the fraudster collects the money while ruining the reputation of the conned eBay member and leaving a large number of people without the goods they thought they purchased.
6.4 AUTOMOTIVE FRAUD
THE SALE
A fraudster posts a vehicle for sale on an online site, generally for luxury or sports cars advertised for thousands less than market value. The details of the vehicle, including photos and description, are typically lifted from sites such as eBay motors or Autoscout24 and reposted elsewhere. An interested buyer, hopeful for a bargain, emails the seller, who responds saying the car is still available but is located overseas. He then instructs the buyer to send a deposit via wire transfer to initiate the "shipping" process. The unwitting buyer wires the funds, and does not discover until days or weeks later that they were scammed. A very "famous" gang from Romania is called "Dragasani Gang". This gang has more than 100 members and produced more than 100 million $ damage. A fraudster feigns interest in an actual vehicle for sale on the Internet. The "buyer" explains that a client of his is interested in the car, but due to an earlier sale that fell through has a certified check for thousands more than the asking price and requests the seller to send the balance via wire transfer. If the seller agrees to the transaction, the buyer sends the certified check via express courier (typically from Nigeria). The seller takes the check to their bank, which makes the funds available immediately. Thinking the bank has cleared the check; the seller follows through on the transaction by wiring the balance to the buyer. Days later, the check bounces and the seller realizes they have been scammed. But the money has long since been picked up and is not recoverable.
THE BUYER
In another type of fraud, a fraudster contacts the seller of an automobile, asking for the vehicle identification number (VIN), putatively to check the accident record of the vehicle. However, the supposed buyer actually uses the VIN to make fake papers for a stolen car that is then sold.
6.5 CLICK FRAUD
Click fraud is an illegal practice that occurs when individuals click on Web site click through advertisements (either banner ads or paid text links) to increase the payable number of click through to the advertiser. The illegal clicks could either be performed by having a person manually click the advertising hyperlinks or by using automated software or online bots that are programmed to click these banner ads and pay per click text ad links. Research has indicated that click fraud is perpetrated by individuals who use click fraud to increase their own personal banner ad revenues and also by companies who use click fraud as a way to deplete a competitor's advertising budget. Webopedia
49
INTERNET USERS HANDBOOK
EXPOSING CLICK FRAUD
Internet marketers facing higher advertising fees on search networks are becoming increasingly concerned about a form of online fraud that was thought to have been contained years ago. The practice, known as "click fraud," began in the early days of the Internet's mainstream popularity with programs that automatically surf Web sites to increase traffic figures. This led companies to develop policing technologies touted as antidotes to the problem. But some marketing executives estimate that up to 20 percent of fees in certain advertising categories continue to be based on nonexistent consumers in today's search industry. The persistence of click fraud has exposed a fundamental weakness in the promising business of Internet search marketing, but most advertisers aren't sure how to address the problem. In one recent example of the problem, law enforcement officials say a California man created a software program that he claimed could let spammers bilk Google out of millions of dollars in fraudulent clicks. Authorities said he was arrested while trying to blackmail Google for $150,000 to hand over the program. He was indicted by a California jury in June. Click fraud is perpetrated in both automated and human ways. The most common method is the use of online robots, or "bots," programmed to click on advertisers' links that are displayed on Web sites or listed in search queries. A growing alternative employs low-cost workers who are hired in China, India and other countries to click on text links and other ads. A third form of fraud takes place when employees of companies click on rivals' ads to deplete their marketing budgets and skew search results. Although the extent of click fraud is impossible to measure with any certainty, its persistence has exposed a fundamental weakness in the promising business of Internet search marketing. Google's pending initial public offering has been widely anticipated as a barometer of online advertising and the post-apocalyptic dot-com climate in general. Unlike advertising in traditional media such as billboards and print publications, "cost per click" Internet ads displayed with specific keyword searches have been promoted as a definitive way for companies to gauge their exposure to potential customers. As a result, U.S. sales from advertiser-paid search results are expected to grow 25 percent this year to $3.2 billion, up from $2.5 billion in 2003, according to research firm eMarketer. From 2002 to 2003, the market rose by 175 percent. As more advertisers have competed for desirable keywords in their industries, the cost for clicks has risen too. On average, advertisers are paying 45 cents per click this year, according to financial analysts, up from 40 cents in 2003 and 30 cents in the second quarter of 2002. In certain sectors, such as travel, legal advice and gaming, the cost can reach several dollars per click. But marketing executives say click fraud is pervasive among affiliates of search leaders Google, Yahooowned Overture Services and FindWhat.com. In a typical affiliation, any Web publisher can become a partner of these large networks by displaying their paid links on a Web page or within its own search results and then share in the profits with every click. Theres a fatal flaw in the cost-per-click model because a ton of marketing dollars can be depleted in a fraction of a second," said Jessie Stricchiola,
50
INTERNET USERS HANDBOOK
president of Alchemist Media, a search-engine marketing firm based in Los Angeles that specializes in fraud protection. "Technology is continuing to be developed that can exploit this pricing model at incredibly high volumes.
GOOGLE'S FRAUD SQUAD
The company said in a statement that it has been "the target of individuals and entities using some of the most advanced spam techniques for years. We have applied what we have learned with search to the click fraud problem and employ a dedicated team and proprietary technology to analyze clicks." In recent documents filed with the Securities and Exchange Commission, the company also acknowledged the problem as a threat to its revenue, of which 95 percent is derived from advertising. Google and other search networks provide refunds to advertisers when click fraud has been discovered. "If we are unable to stop this fraudulent activity, these refunds may increase," Google said in its SEC filing. "If we find new evidence of past fraudulent clicks we may have to issue refunds retroactively of amounts previously paid to our Google Network members." Google and Overture employ "fraud squads," or teams of people dedicated to fighting click schemes. But at least two marketing executives say such countermeasures are missing fraudulent clicks that are responsible for between 5 percent and 20 percent of advertising fees paid to all search networks. Overture spokeswoman Jennifer Stephens refutes that estimate, saying that the numbers likely represent acts of fraud that are ultimately caught. She added that Overture filters most fraudulent clicks with the best antifraud system in the industry, which combines technology and human analysis. "We take this very seriously; it's the foundation of what we do," Stephens said. "If an advertiser has a question about it, we look into all matters." Cost-per-click advertising comes in many forms, but it essentially lets marketers gain exposure on a Web site and pay only when people click on their ads. Google and Overture let advertisers bid for placement of paid links, which appear when certain keyword searches are conducted on the networks' sites or those of third parties that partner with them. Keyword ads can also be distributed according to the content of partners' sites and displayed on non-search pages. (CNET Networks, which publishes News.com, partners with Google for shared advertising revenue.) Most advertisers are aware of the click-fraud issue but have not delved into it because of the technical complexities involved. Others are concerned that they could jeopardize their relationships with the powerful search networks if they complain too loudly.
COVERT CLICKS
Human operations can be more difficult to detect because a wide network of people can click on ads from different computers across many regions, without a steady pattern. According to a report in the India Times, residents are being hired to click paid links from home, with the hopes of making between $100 to $200 per month.
51
INTERNET USERS HANDBOOK
In other instances, the source of bogus clicks can be much closer to home. Joe, the chief executive of an Internet marketing company, enjoys clicking on his rivals' text ads on Google and Yahoo because his competitor must pay as much as $15 each time he does it. Eventually, such phantom clicks can add up and drain a rival's budget. "It's an entertainment," said the executive, who asked to keep his name and company anonymous. "Why do you run into a store without dropping a quarter in the meter? You know it's wrong, but you do it." LATEST ON CLICK FRAUD The latest scam to hit the headlines is the multi-million dollar click fraud, which occurs when advertising network affiliates force paid views or clicks to ads on their own websites via spyware; the affiliate is then paid a commission on the cost-per-click that was artificially generated. Affiliate programs such as Google's AdSense capability pay high commissions that drive the generation of bogus clicks. With paid clicks costing as much as US$100 and an online advertising industry worth more than US$10 billion, this form of Internet fraud is on the increase.
AVOID PAY-PER-CLICK PROBLEMS
One of the most important Internet marketing tools is PPC advertising. With Yahoo and Google leading the pack, the industry as a whole has grown immensely in the past few years. PriceWaterHouseCoopers reports that in 2004 alone, Internet Advertising brought in an estimated $9 billion dollars. Anybody can use this marketing system that is really quite simple in theory. With PPC advertising you choose "keywords/phrases," then bid how much you would like to pay for each click. When a searcher goes to a search engine and types in one of your key phrases, your short text ad appears, and if someone clicks on it your account is then charged. In a "perfect world" this is the way it would work, but thanks to unscrupulous people, there is a dirty little secret known as "click fraud." Click fraud is simply the act of clicking on ads for the direct purpose of costing the advertiser money. It is recognized as the biggest problem today in PPC marketing. According to InternetWeek.com, 60% of people surveyed by the "Search Engine Professional Organization" have stated that fraud is a problem when it comes to PPC advertising. PPC marketing can cost you a lot if you do not administer it right. Bad targeting plus fraud can be a costly problem. The main sources of click fraud are the following four AdSense Users Google AdSense has a program called "AdSense" that pays website owners to run their Adwords ads and compensates them per click. Google does monitor this and it is against their terms of service to click on any of the ads on your own site. If they find publishers doing this, they will lose their accounts, but some may still be clicking under the radar.
YOUR OWN COMPETITORS
Your competitors could be clicking on your ads over a period of several days in order to deplete your ad budget. This way they neutralize your advertising campaigns.
SOFTWARE
There are those who use automated clicking tools, such as robot programs, to click on PPC listings.
52
INTERNET USERS HANDBOOK
PAID CLICKERS
In some Asian countries, people are often paid to click on PPC ads for hours. Many do not know why they do it, and do not care. The only important issue is that they will be well rewarded for their efforts. If you do a search on any search engine you will see plenty of sites offering to hire people for just this purpose. Type in 'earn rupees clicking ads' in Google and you get quite a few leads. Most PPC networks have measures in place to protect you against click fraud. Yahoo's Overture tracks more than 50 data points, including IP addresses, browser info, users' session info and what they call "pattern recognition." They have a "proprietary system" in place for detecting fraud and a specialized team that monitors things and works with the advertisers to stop it. Google offers suggestions to avoid click thru fraud, such as "using negative keywords" to keep your ads from showing up for products and services that are unrelated. They also suggest adding tracking URL's to your links so you can track the traffic coming from Google. If you go through your log files, you'll be able to see your Google traffic at a glance. If you suspect fraud, Google asks that you contact them right away, because they have a team of researchers that will investigate. They also take action to block future impressions from anyone they identify as committing click fraud. Like Overture, they also have "proprietary technology" that distinguishes between normal clicks and invalid ones. Google never bills you for any "bad clicks" that are caught by their system. All honest website owners need to be alert to any "suspicious activity" by researching their server logs or stats. If you're experiencing a lot of clicks and no sales you'll also want to take a closer look. You need to watch for any spikes in traffic, usually on one keyword or phrase and coming from only one PPC source. You need to measure and track all of your PPC accounts closely. A variety of new services have opened recently to help combat the click fraud problem. Some of them also offer web analytic tools that help improve your advertising productivity. You may want to look at these outside services to take care of problems for you. Here are some links: Click fraud is not going away anytime soon. Most probably, it will get worse before it gets any better. It's up to you as a vigilant website owner to do what you can to keep your PPC advertising costs down. You can't stop it, but with the right tracking in place, it can be managed and controlled, and hopefully kept to a minimum. InternetWorldStats
6.6 CLOUD COMPUTING SCAMS
Cloud computing just means that rather than make your own computer do all the work involved in running applications, you access a network of other computers in a cloud to do it; the user does not need to have as much software and hardware installed on their own computer. Using Gmail and Hotmail is an example of cloud computing your information is not stored on your own computer, but in a services computer cloud.
53
INTERNET USERS HANDBOOK
One common cloud computing scam involves Google docs. Phishers use this tool to lure users into sharing their personal information. Google spreadsheets can be used to create forms to collect information, and often look like they are from well-known, reputable companies when they are not. A red flag to watch out for is the URL linking to the scamtastic Google doc; it usually contains the command word formkey, followed by an equal sign and a randomly generated identifier link. Do yourself a favor and do not click on the link or enter personal information in any of the documents or form fields. AlertPay
6.7 COUNTERFEIT POSTAL MONEY ORDERS
According to the FBI and postal inspectors, there has been a significant surge in the use of Counterfeit Postal Money Orders since October 2004. More than 3,700 counterfeit postal money orders (CPMOs) were intercepted by authorities from October to December 2004, and according to the USPS, the "quality" of the counterfeits is so good that ordinary consumers can easily be fooled. On March 9, 2005, the FDIC issued an alert stating that it had learned that counterfeit U.S. Postal Money Orders had been presented for payment at financial institutions. On April 26, 2005, Tom Zeller Jr. wrote an article in The New York Times regarding a surge in the quantity and quality of the forging of U.S. Postal Money Orders, and its use to commit online fraud. The article shows a picture of a man that had been corresponding with a woman in Nigeria through a dating site, and received several fake postal money orders after the woman asked him to buy a computer and mail it to her.
WHO HAS RECEIVED COUNTERFEIT POSTAL MONEY ORDERS (CPMOS)?
Small Internet retailers. Classified advertisers. Individuals that have been contacted through email or chat rooms by fraudsters posing as prospective social interests; or business partners, and convinced to help the fraudsters unknowingly.
6.8 COUNTERFEIT CASHIERS CHECK SCAM
This recent scam has been reported in Atlanta and Minneapolis. Real estate property owners placing advertisements on Craigslist or rent.com receive an email response from a "24 year old in the U.K. on a research program in the United States". Addresses include john.yearwood__@yahoo.co.uk and kevin_taylor@excite.com. The first inquiry seems legitimate. The second usually comes with request for more information, and a bogus attachment from JAPAN TOBACCO INC (who has posted information about this scam on its site) indicated the "student" has won a part time scholarship from the JT UK office. The scam comes with the third email, a request for name and address so that the counterfeit cashiers check can be sent. The amount supposedly includes the rent and fees plus an overage for the "student's" travel.
54
INTERNET USERS HANDBOOK
The owner is instructed to cash the check and wire the difference back to the student so that they can travel to the U.S. The photos often include a young man in graduation uniform from his college. (Note: U.K. colleges are the equivalent to high schools, not universities. One photo includes a rather dumpy, depressed looking girlfriend who must be aware of the scam.) Because of the lag between the cashing and clearing of the check, the owner does not realize he/she has been had until their account is debited the counterfeit cost and the wired sum. Greedy owners may even decide to keep some of the check, only to be had themselves later. It is best not to respond to this type of email and requiring background checks before cashing first rent payments.
6.9 CASH THE CHECK SYSTEM
In some cases, fraudsters approach merchants and ask for large orders: $50,000 to $200,000, and agree to pay via wire transfer in advance. After brief negotiation, the buyer gives an excuse about the impossibility of sending a bank wire transfer. The buyer then offers to send a check, stating that the merchant can wait for the check to clear before shipping any goods. The check received, however, is a counterfeit of a check from a medium to large U.S. Company. If asked, the buyer will claim that the check is money owed from the large company. The merchant deposits the check and it clears, so the goods are sent. Only later, when the larger company notices the check, will the merchant's account be debited. In some cases, the fraudsters agree to the wire but ask the merchant for their bank's address. The fraudsters send the counterfeited check directly to the merchant's bank with a note asking to deposit it to the merchant's account. Unsuspecting bank officers deposit the check, and then the fraudster contacts the merchant stating that they made a direct deposit into the merchant's account. In other cases, fraudsters approach merchants for smaller orders: $2000 to $10,000 offering to pay with a check. They send the check and the instructions state that the merchant has to deposit the check, wait for it a couple days to clear and send the "excess" funds via Western Union money transfer to an account in another country. The fraudsters send fake checks but drawn on the real accounts of large U.S. companies, which will probably clear immediately
6.10 CALL TAG SCAM
The Merchant Risk Council reported that the "call tag" scam re-emerged during the 2005 holidays and several large merchants suffered losses. Under the scheme, criminals use stolen credit card information to purchase goods online for shipment to the legitimate cardholder. When the item is shipped and the criminal receives tracking information via email, he/she calls the cardholder and falsely identifies himself as the merchant that shipped the goods, saying that the product was mistakenly shipped and asking permission to pick it up upon receipt. The criminal then arranges the pickup issuing a "call tag" with a shipping company different from the one the original merchant used. The cardholder normally does not notice that there is a second shipping
55
INTERNET USERS HANDBOOK
company picking up the product, which in turn has no knowledge it is participating in a fraud scheme. The cardholder then notices a charge in his card and generates a charge back to the unsuspecting merchant.
6.11 CHRISTMAS/HOLLIDAY SCAMS
"12 Scams of Christmas" list and offers of free iPads among this years most coveted tech gadgets comes in at No. 1. "With Apple products topping most shopping lists this holiday season, scammers are busy distributing bogus offers for free iPads" via email spam, McAfee said. In the email, "consumers are asked to purchase other products and provide their credit card number to get the free iPad. Of course, victims never receive the IPad
CHARITY SCAMS
"Common ploys include phone calls and spam emails asking you to donate to veterans charities, children's causes and relief funds for the latest catastrophe."
FREE IPADS
Facebook, Twitter or other social media version of the ruse, users are asked to "take a quiz to win a free IPad and must supply their cell phone number to receive the results. In actuality they are signed up for a cell phone scam that costs $10 a week," McAfee said. Here's the rest of the company's "12 Scams of Christmas" list:
FAKE GIFT CARDS
Social media (Facebook, Twitter, MySpace as examples) are used by nogoodniks to "promote fake gift card offers with the goal of stealing consumers information and money, which is then sold to marketers or used for ID theft". "One recent Facebook scam offered a 'free $1,000 Best Buy gift card" to the first 20,000 people who signed up for a Best Buy fan page, which was a lookalike. To apply for the gift card they had to provide personal information and take a series of quizzes."
GRINCH-LIKE GREETINGS
Involving e-cards Electronic cards can save paper and postage, but "cyber criminals load fake versions with links to computer viruses and other malware instead of cheer ... Computers may start displaying obscene images, pop-up ads, or even start sending cards to contacts that appear to come from you." Google admitted for the first time its "Street View" cars around the world accidentally collected more personal data than previously disclosed including complete emails and passwords potentially breathing new life into probes in various countries.
HOLIDAY-THEMED SCREENSAVERS Jingles and animations are an easy way for scammers to spread viruses and other computer threats
especially when links come from an email or IM that appears to be from a friend."
HOTEL AND AIRPORT WI-FI VULNERABILITIES
This is an anytime risk with thieves who are savvy enough to hack into public networks being used by hurried travelers. Hacker-thieves can steal credit card numbers, bank accounts and other forms of
56
INTERNET USERS HANDBOOK
personal identity; try not to access bank accounts, for example, or give your credit card number online while using public Wi-Fi. It's a good rule for every day not just for the holidays.
LOW PRICE TRAPS
Discussed above, as the "too good to be true" deals, which are promoted on some auction sites and fake websites. The aim, McAfee says: "the goal of stealing your money and information."
RECESSION SCAMS CONTINUE
"Scammers target vulnerable consumers with recession related scams such as pay-in-advance credit schemes. McAfee Labs has seen a significant number of spam emails advertising pre-qualified, lowinterest loans and credit cards if" that emphasis is mine "the recipient pays a processing fee, which goes directly into the scammers pocket."
SMISHING
You've heard of phishing? "Smishing" is when a phishing SMS, or text messages, arrives on your cell phone, wanting you to bite. "These texts appear to come from your bank or an online retailer saying that there is something wrong with an account and you have to call a number to verify your account information. In reality, these efforts are merely a ruse to extract valuable personal information from the targets".
SUSPICIOUS HOLIDAY RENTALS
Many of us are looking to save on that Christmas-y cabin in the mountains or chic vacation apartment in the city of our dreams. "During peak travel times when consumers often look online for affordable holiday rentals, cyber crooks post fake holiday rental sites that ask for down payments on properties by credit card or wire transfer."
TRAVEL SCAM
"Help! Ive Been Robbed" "This travel scam sends phony distress messages to family and friends requesting that money be wired or transferred so that they can get home."
TWITTER SCAMS
Offer dangerous links to high-paying, work-at-home jobs that ask for your personal information, such as your email address, home address and Social Security number to apply for the fake job."
6.12 DATING SCAMS/ROMANCE SCAMS
Online dating scams and fraud are almost as old as Internet dating itself. Often called a Sweetheart Swindle this is often a long, drawn out process in which the con artist develops a relationship, and eventually convinces the victim to send money. The scammer often meets the victim in chat rooms or via online dating sites. Their object is not to get into their hearts, but get into their wallets. They will try to earn someone's affections and trust so that they can persuade him/her to send money. The requests for money can either be a onetime event or repeated over an extended period of time. The details of the scammers' stories will vary with each case.
57
INTERNET USERS HANDBOOK
The scenario commonly revolves around a tragedy having befallen the scammer, and he/she desperately needs money. After spending time communicating and building a relationship with the victim, the scammer will ask for help in the form of money. Most online dating services have a hard time dealing with scammers, outside of issuing warnings to their users to be alert for anyone you have never met asking for money.
SOME POTENTIAL INDICATORS YOU MAY BE DEALING WITH A DATING SCAM:
The online sweetie says, "I love you" almost immediately. The person asks for money, to cash a check or money order. The person claims to be a U.S. citizen who is abroad, well off, or a person of importance. The person claims to be a contractor and needs help with a business deal. The person claims to need money for a parent's "operation in the hospital". The person will have a photo that is most attractive posted on the website, but will not be so willing to send you any other photos, there is always a problem with that. The photo is to get you attracted to him/her to begin the interest in building the relationship. Most likely, that is not a real photo of the scammer. Wikipedia TIP: Most want to interact with you privately so they ask you to respond to their email address in most cased they seem to like Yahoo email. While I have tried a number of these scams, Dating in not one of them - smiles
6.13 DIRECT MAIL AND TELEMARKETING SCAMS
BROADCAST AND PRINT ADVERTISEMENTS
In some cases, you may make the telephone call in response to a television, newspaper or magazine ad, or a direct mail solicitation. The fact that you make the call does not mean the business or investment is legitimate or that you should be less cautious about buying or investing on the phone. Those who respond by calling a toll-free "800" number often get a package of materials, followed by high-pressure telephone sales pitches. Fraud investigators speculate that getting victims to call first makes the work of the schemer much easier, since the potential investor has already "bought into" the scheme by taking the first step.
COLD CALLS
You may get a call from a stranger who got your number from a telephone directory, mailing list, or "sucker list." The latter refers to lists of consumers who have lost money through fraudulent prize promotions or merchandise sales. These lists contain names, addresses, phone numbers, and people who have responded to telemarketing solicitations spent other information, such as how much money. "Sucker lists" are bought and sold by unscrupulous promoters and "list brokers".
58
INTERNET USERS HANDBOOK
They are invaluable to scam artists who know that consumers who have been deceived once are vulnerable to additional scams. Telephones create economies of scale by allowing a single caller to target a large number of victims in a short time and at long distances. Offenders maximize proceeds by focusing on target-groups most easily victimized, and by making large numbers of calls quickly, focusing on those who appear susceptible and hanging up on those who resist. Fraudulent telemarketers and sellers may reach you in several ways, but the telephone always plays an important role. You may not know it, but if you get frequent hang-up calls, they are probably telemarketers. In order for them to have the maximum number of calls each hour, they dial ahead. They are on a call, but they are dialing the next two calls. If the current call stays on the phone longer, the future call goes to your house, but when you pick up, it hangs up. Then, when they get done with the current call, they call you back. Even if you have caller ID, it will say "no data sent", as they use blocking features. Some people have had their phone numbers changed because they thought they were being harassed by calls, when the truth is that it is just telemarketers working it so they will have the greatest ability to get people to spend money. They are not concerned with the inconvenience to you or any other discomfort this practice may cause you. A computer known as an auto dialer or predictive dialer is dialing the majority of these telemarketing calls. Predictive dialers can dial 3-5 numbers simultaneously and can make as many as 500,000 calls between 8 a.m. and 9 p.m. If you are not home; or if the computer gets your answering machine, your number will be put back in the database to be called again later.
CONTEST LEADS
Fraudulent telemarketers often purchase Leads or prospect calling lists, which identify individuals who have entered a contest by filling out a personal data card, from "lead brokers". The data cards generally contain your name, address, phone number, and age. Usually you lead them right to you when you fill out these draw ballots or enter contests at fairs, trade shows and restaurants.
DIRECT MAIL
You may get a letter or postcards saying youve won a prize or a contest. Such companies get leads from the bulk mailing of entry forms with an easy crossword and a $3-5 entry fee or from a "scratch and win" ticket. Instructions tell you to respond to the promoter with certain information. Such leads may get a follow up call because they now know that you are prone to such gimmicks. You will be called by a salesperson that may use persuasive sales pitches, scare tactics, and exaggerated claims to deceive you and take your money.
59
INTERNET USERS HANDBOOK
When family members of elderly telemarketing fraud victims have done a search on the Internet for some of the names used in the sweepstakes material, found next to piles of cancelled checks, they invariably find large corporate list management and sales firms that purport to be one thing but appear to be another. It should be considered aiding and abetting a criminal enterprise when it is determined that commercial list managers purposely compile and then sell lists of vulnerable victims as part of their business model. List categories by these firms are not benignly collected demographic profiling, based on product interest of everyday goods and services, but are actively generated campaigns geared, coincidentally, towards the psychological traits, which scammers are seeking in their victims.
ELDERLY VICTIMS ON LOTTERY SCAM SUCKER LISTS
08/07 - Nebraska - Every day envelopes pour into Mary Peters mailbox from all over the world and they all come with guarantees of big lottery winnings. Peters, 88, receives about 6-10 promises that she has won a foreign lottery every time her mail is delivered. She said she has received as many as 18 in a single day. They never stop, Peters said. She has collected several boxes of the offers. Peters name and address of the home where she has lived for nearly 60 years is on a suckers list. Since she responded to an offer several years ago, the mailings have increased ten-fold. People who respond to telemarketing fraud or sweepstakes mailers are often placed on a sucker list. Sucker lists, which include names, addresses, phone numbers and other information, are created, bought and sold by fraudulent mailers and telemarketers. The lists are considered invaluable because dishonest promoters know that consumers who have been tricked once are likely to be tricked again. Its called reloading. As a result, people on the sucker list become flooded with letters, emails and phone calls with various offers lottery wins, investment plans, get rich schemes and work from home offers. And once they start, its difficult to make them stop. Lt. Rick Ryan of the North Platte police said they get 4-5 calls from people about the lottery and sweepstakes offers every single week. Theyre almost all generated from outside the U.S. to avoid prosecution, Ryan said. They look like they come from official U.S. banks or businesses but they dont. Ryan said any offer that requires you to send money is not a legitimate one. Do not send money or a fee to these places, Ryan said. If they ask for money or information, its a scam. Crimes of Persuasion TIP: Online users are now faced with new lead generation techniques such as the Splash or Capture page. Yes these have been around for a while, but now anyone can make a Splash page for any program. Often there is no clue as which program is being advertised along with the request free information. You may never see the information, but your name and some details have already been captured when you signed up.
60
INTERNET USERS HANDBOOK
EMAIL
Commonly known as "junk email," "bulk email," or "spam," unsolicited commercial messages are flooding the Internet each day, ending up on desktops everywhere. Although some of these messages are from legitimate marketers, many are fraudulent solicitations from scam artists who make promises they have no intention of keeping. Spammers and scammers often hide and confuse their identities by obscuring their URLs.
GOLD DUST MEMO
From: Director of Marketing To: Chief Financial Officer To help limit our advertising budget and sales staff it is important to target resources where they will be most effective. As an aid to our marketing efforts, in efficiently selecting prime customers, it is recommended that we take steps to institute the latest technologies in datamining techniques. Data mining can indicate factors that help determine whether our marketing efforts will succeed. Consumers can then be the target of increasingly sophisticated marketing campaigns, which seek to address their individual weaknesses. Through the selected acquisition of established mail order and publishing enterprises, our activities will be able to generate relevant data in the normal course of business. Initial studies have shown some interesting tendencies prevalent to a significant number of existing customers. They tend to believe what they see in print, with emphasis on the exaggerated or unbelievable, as may be found in the tabloid industry. Such a media acquisition would also reduce advertising costs. It would also be desirable to acquire the customer lists of as many infomercial, collectible item business and charities as possible, to name a few. Data mining offers the potential to identify the preferences of specific customer groups and to indicate what sorts of promotional material most affect their purchasing habits. Similarly, identifying preferences can be used to effectively target deceptions for that group.
LAND SALES
Their land sales solicitations allegedly misrepresent that buyers have contacted them with an interest in purchasing land similar to that owned by you; that they are qualified to sell real estate; and that if you call a specified number you can "sell for cash today." Consumers who call then pay several hundred dollars, but in most instances, they never sell your property.
MONEY
"Mooch lists" can contain a disturbing amount of personal information about past victims full name, address, phone number, even bank-card numbers and the amount they've spent on previous scams. Some lists even rank victims based on their perceived vulnerability. Others might include helpful scamming tips: "Mention religion. This person loves Jesus!" People on these lists have been victimized at least once by a telemarketing scam and are susceptible to being victimized again. A list used in a reverse boiler-room event included people who had lost a few dollars up to more than $30,000.
61
INTERNET USERS HANDBOOK
SWEEPSTAKES AWARDS
Their guaranteed award solicitations falsely represent that you are "absolutely guaranteed" to receive one of several valuable awards, such as a car, a vacation, or a cashier's check for several thousand dollars, and that you will receive the award without obligation to pay any money. In fact, when you call to claim your "awards," you find that you must send several hundred dollars to purchase a product or to cover shipping and handling costs in order to receive it. Even then, when you send the money, you often never receive the promised award.
TARGET MARKETING OF FRAUD VICTIMS
Victims are not created at random or by accident. They are chosen by the offenders because they are vulnerable in some way and because they have enough money or assets to be attractive. Victim selection can be done directly by researching specific information about you. Anyone with a phone can be victimized by telemarketing scam artists. Telephone fraud knows no race, ethnic, gender, age, education or income barriers. Fronters will sometimes seek out leads using community books and directories that list former occupations. They will also "cherry pick" elderly-sounding names from the phone book like Edna, Violet or Gertrude.
VACATION OFFERS
Their vacation solicitations promised you a vacation with no obligation to make a purchase or payment when in fact; you must send several hundred dollars to purchase a travel package and often must pay even more money to take your vacation. TIP: While many of the forgoing scams are offline scams; but moving online for the bigger population and a faster spread through social networking
6.14 DOMAIN NAME RENEWAL SCAMS
Scams that send you a fake renewal notice for your actual domain name or a misleading invoice for a domain name that is very similar to your own. ScamWatch
6.15 EMAIL SCAMS
The FBI warns the public against three separate Internet scams that continue to flourish through spam emails. The warning comes after the FBI's Internet Crime Complaint Center (IC3) received a rising number of complaints from citizens over the past few weeks.
GREETING CARDS
The email recipient receives an electronic greeting card containing malware (malicious software). The cards, which are also referred to as e-cards or postcards, are being sent via spam. Like many other Internet fraud schemes, the perpetrators use social engineering tactics to entice the victim, claiming the card is from a family member or friend. Although there have been variations in the spam message and attached malware, generally the spam directs the recipient to click the link provided in the email to view their e-card. Upon clicking the link, the recipient is unknowingly taken to a malicious web page.
IMPOSTERS
Fraudulent emails misrepresent the FBI and/or Director Robert S. Mueller III and give the appearance of legitimacy due to the usage of pictures of the FBI Director, seal, letter head, and/or banners. The
62
INTERNET USERS HANDBOOK
types of schemes utilizing the Director's name and/or FBI are lottery endorsements and inheritance notifications.
SPAM EMAIL
Spam email, which claim to be from an official of the U.S. military sent on behalf of American soldiers stationed overseas. The scam emails vary in content; however, the general theme of each is to request personal information and/or funds from the individual receiving the email. These spam email messages are hoaxes and should be immediately deleted. Consumers need to be wary of unsolicited emails that request them to take any action even if that means just clicking on an attachment. It is possible that by "doubleclicking" on attachments to these messages, recipients will cause malicious software e.g., viruses, keystroke loggers, or other Trojan horse programsto be launched on their computers. FBI
EBAY EMAIL SPOOFING
The sender information shown in emails (the "From" field) can be spoofed easily, though nowadays many domains have the Sender Policy Framework implemented, which helps prevent the email spoofing. This technique is commonly used by Spammers to hide the origin of their emails and leads to problems such as misdirected bounces (i.e. email spam backscatter).
Example: EBay Sellers Beware eBay sent this message to xx.
Your registered name is included to show this message originated from eBay.. This member has a question for you. Do not respond to the sender if this message requests that you complete the transaction outside of eBay. This type of offer is against eBay policy, may be fraudulent, and is not covered by buyer protection programs. Learn More. Dear xx, Hello I was just looking at your auction and have a few questions. Do you have a working PayPal account? How much you are willing sell it? Please be reasonable I am very interested. Please include your regular email to your response because I don`t check my eBay often, so we can talk through email. Thanks This is an exact duplicate of another message from another Member. You acted on this alert in My Messages, but it may still require your attention. eBay sent this message to xx. Your registered name is included to show this message originated from eBay. Learn more.
MC139 SP NOTICE: eBay Ask Seller a Question or Contact eBay Member Alert
Dear xx, Our records show that you recently contacted or received messages from weatherby3cycling through eBay's messaging system. This account was recently found to have been accessed by an unauthorized third party, who may have used the account in an attempt to defraud other members. We've taken action to restore this account to the original owner, but wanted to let you know to be suspicious of any communication you may have received from them. Nothing is wrong with your account at this time this message is just being sent as a precaution. If you have received any messages
63
INTERNET USERS HANDBOOK
from weatherby3cycling that appears suspicious, please feel free to forward them to us at spoof@ebay.com for review.
EBay Notified Me That I Had Sold an Item for $ 1600
I attempted to invoice the buyer per routine eBay practices; however, eBay had already blocked the buyer for resolution of conflicts. Upon further investigation the buyer was no longer a registered member. In fact, she was registered for only 1 day under that name The buyer contacted me directly via email with a Romania Address. I followed-up with buyer to confirm shipping address and the status of the payment. Buyer advises me that payment had already been made and to look for the PayPal notice of payment. Confirms a new address in Nigeria Urgent Matter: birthday present for her partner and she wanted to know the shipping charges (whe
Buyers so-called PayPal Notice showed up in my junk mail
Looked very official with PayPals logo and propaganda, etc. the following exceptions: From Address: linuxtech2@gmail.com; on behalf of; services@Paypal.com [paypalshipment@mail2pal.com] TIP: It was from services@paypal.com, rather than from service@paypal.com, (extra s added) it was addressed to my email and not my name
Subject line was wrong
JanetXXX has sent you an eBay item Payment with PayPal (Routing Code: C840-L001-Q999T5350) Instead of Notification of Payment Received, It said that the payment was received for the cost of the item, and included an extra-ordinary shipping fee of $ 300 (I guess that was an inducement for me to act quickly and ship the item). Shipping address confirmed to the Nigeria address. However, the payment withheld to my PayPal account pending my shipping confirmation which I declined to ship the item without advance payment, per eBay practices.
Warning
Learn the procedures of say eBay, pay attention and verify everything before you send your money. I looked up mail2pal.com in Whois.com and the owner was not related to PayPal TIP: When PayPal sends an email to you, it is addressed to PayPal emails are from service@paypal.com, service@intl.paypay.com, or sendmail@paypal.com
How To Know The email You Received Was Sent By EBay?
Here are some things to watch for: eBay will never ask you to provide account numbers, passwords, or other confidential information through email. If we do request information from you, a copy of the email will also appear in the My Messages section of my eBay. If you don't see a copy there, the email isn't authentic. In addition, spoof emails often begin with a general greeting such as "Welcome eBay User," rather than your name or user ID. They claim that eBay is updating its files or accounts -- this is a common tactic of spoof email contain an "urgent" warning, telling you that your account is in jeopardy and you won't be able to buy or sell on eBay if you don't provide personal information immediately.
64
INTERNET USERS HANDBOOK
Even links that go to real-looking pages can be fake. Never click a link in a suspicious email. Sign in through the usual process. If you suspect an email is fake, please forward it to us at spoof@ebay.com. You can learn more about recognizing and dealing with spoof emails. Need more help? Contact us directly using the customer support options on the right side of the page.
6.16 FOREX SCAMS
Forex scams take many forms. Some scams can be compelling or seem to be very legitimate. They take advantage of traders seeking the magic answer to winning in the Forex markets. Unfortunately, there are no easy answers. Here is a quick list of some popular general Forex scams. Many of the HYIP programs are tied to Forex, increasing your risk of failure. Just because a HYIP fails, it doesnt mean it was a scam! But see a second opinion below
SIGNAL SELLERS
It seems like a new company springs up every day that has the signal service to beat all signal services. They profess to be able to sell you information on which trades you should make. These signal sellers usually charge a daily /weekly /monthly fee for their service and usually do not offer anything that will help improve your trading. There is no such thing as having a magic key to the market and if there were, why would you sell it?
PHONY INVESTMENT FUNDS
In the past few years, funds called HYIP (High Yield Investment Program) have popped up all over the place. Most of these (if not all) are scams. They promise you a high level of return for temporary use of your money in their Forex fund. It is a type of Ponzi scheme where the investors of yesterday get paid back by the investors of tomorrow. Once the fund runs out of prospects, they usually close down and take whatever money they had with them.
MIRACLE SOFTWARE
There is no software that will figure out the Forex market for you. However, a quick Google search will turn up plenty of software sellers that say otherwise. Some companies out there are selling their special packages for upwards of $5,000 and many times it turns out to be something that you can find on the Internet free. It is generally not advisable to buy any type of Forex software that will tell you which trades to make. Popular Forex Scams It is an unfortunate reality...the number of Forex scams is increasing every year, mostly due to the Forex market being under-regulated when compared to the other financial markets like the stock market. Many "snake oil" scammers prey mainly on the gullible that have not done their research and are desperate for a "get rich quick" solution. They tell you to join their services and cajole you with overthe-moon promises such as making thousands of dollars with little capital to invest and no work. They even show you fraudulent but professional looking screenshots of past trades highlighting the profits made and can seem very convincing. Of course not all the companies that provide trade signals are scams, but from personal experience only a third of the service providers are honest and profitable.
65
INTERNET USERS HANDBOOK
6.17 GUARANTEED SIGN UPS
Are you an affiliate marketer who is interested in paying for guaranteed sign ups to help grow your downline? This article will explain what you will receive in return for your money. You have seen the advertisements before where you are guaranteed to receive 100 sign ups to your affiliate program, all for $199. Guaranteed signups are offered by companies online who promise to deliver leads or new sign ups to the affiliate program or MLM opportunity you happen to be promoting in exchange for a fee which they say goes into advertising and promotion of your affiliate link. Primarily they are offering these advertising services for those requiring free sign up programs and not paid programs. This article will take you through what happens after you pay these companies. Guaranteed sign up companies may actually deliver all of the sign ups they say to your affiliate program or MLM opportunity. The only problem is that you are likely to get space fillers. Meaning, that none of the new signups will ever take any action once they join or the leads were not targeted, and therefore are of low quality. You see, it's not enough to get sign ups, they have to be active in order for you to make money or benefit in any way. Even though the company guaranteeing sign ups have lived up to their obligation, all too often the consumer doesn't reap any benefits. The reason that these new sign ups don't take action is because the majority of guaranteed sign up companies have deals on the other end where they pay people per sign up to join your program. It might be a small fee paid for each person who signs up at your site. It is sort of like being paid to take surveys online. In this case they are paid to sign up to your affiliate program or MLM opportunity. These sign ups only interest might by the small amount of money they are paid to sign up. In fact, they may have created the email address they signed up with for the purpose of collecting spam. Which includes any email you might be sending to assist them with the affiliate program or business opportunity? If you still want to go forward with purchasing guaranteed sign ups then testing is definitely in order. A simple way to test whether the new sign ups you receive are active is to send a welcome message to each new sign up (this may already be part of your affiliate marketing strategy). Add a link to a resource or free e-book in this welcome email, but use a tracking URL to count how many times the page has been viewed. You will find that your sign ups from targeted marketing such as article marketing and blogging actually click the links you send them. Those who are space fillers will never click your links because the company was not reputable in the first place. Overall, guaranteed signups are not a viable solution to for any affiliate marketing or MLM business opportunity. In fact, truthful marketers will tell you that there is no quick fix and that it takes consistent action and effort to create sign ups that are responsive and active in your organization. Depending on proven marketing strategies such as article marketing, blogging, and search engine optimization is a proven path to success. Guaranteed sign up companies know how to advertise to those who are desperate to see their affiliate list grow as soon as possible, but patience and the learning of strategies that work is a smarter choice that will cost you much less of your hard earned money.
66
INTERNET USERS HANDBOOK
If you have your own website or blog, you MUST promote it to achieve visitors and more importantly sales. Visit our site today and learn exactly how you can best promote your website using methods that have been proven to work for millions. Buzzle
6.18 IDENTITY THEFT
DO NOT PLAY OR LET YOUR CHILD PLAY, GAMES OR ENTER CONTESTS
At sites which appear on candies, cereal boxes, ads in magazines, online, etc. as they often require dateof-birth, name, address, phone, email, etc. for the purposes of processing and awarding. Their privacy policy and/or terms inevitably contain either an escape clause (if not a complete lie) allowing the eventual abuse and/or redirection of any information gathered. The data compiled may also be assimilated and combined with that obtained from other sources to complete your personal identity profile.
USE EXTREME CAUTION WHEN PUTTING YOUR CREDIT INFO ON-LINE
Instead, consider using a card into which you deposit the amount of money required for your desired transactions. AAA Everyday Funds is an example of one such card.
DO NOT GIVE SOCIAL SECURITY
Dont give Social security number, account number, DOB, etc., out for ANY reason, if you can help it. While this is often unavoidable on some legitimate calls, (such as to the IRS, your doctor or your bank), do it ONLY on calls initiated by you, to numbers obtained, BY YOU, from the institution or off valid documents you KNOW are from THEM.
DO NOT FILL OUT SURVEYS
Surveys/questionnaires/product registration optional sections, as they are gathering personal information such as household income, credit cards possessed, family size, medical needs, buying habits, etc.
WHEN SIGNING UP FOR SOMETHING
On line, registering or installing software, etc., watch out for and unclick the boxes that show up preset with a check, dot or "X" in it which offer "additional info or services". They inevitably set you up for a deluge of unwanted email, plus propagate your profile info to their sites (and their associates, and theirs... and so on).
TRY NOT TO USE CARDS TIED TO YOUR BANK OR CREDITOR
Rather use pre-paid cards or try to use cash, to make store purchases. The purchases you make get fed into massive databases, which could conceivably be used to your disadvantage.
DON'T SEND OFF ONLINE REQUESTS
For free samples, enter contests in Malls, play online gambling games, send off for "free" merchandise, or believe "You are a winner", "You have won", "You have been selected to receive", "free trial offer", "no risk/no obligation offer - cancel at any time", etc. You may never receive anything at all, or get a cheap piece of useless merchandise, but at the very least you can rest assured that you've been entered
67
INTERNET USERS HANDBOOK
on at least one mass-mailing list, not to mention guaranteed to be given abundant similar opportunities with more advanced scams in the future.
BE CAREFUL ABOUT REFERRAL
Referral and family/acquaintance list requests, which when completed offer you a bonus or prize, even from YOUR CHILD'S SCHOOL. The value is neither worth that of the collected personal data you (or you children) provide OR the time required to complete the list, not to mention the possible consequences to the unfortunate listed.
DON'T GO FOR THE VACATION
The vacation/cruise package deals you get in the mail, at the mall, off the office fax, or unsolicited on the web. Your package will not be what it was presented to be, have numerous restrictions and obligations and your cost will ultimately be higher than if you had purchased it normally through a reputable agency. Crimes of Persuasion
WHAT TO DO IF YOU HAVE RESPONDED TO A PHISHING SCAM? Report The Incident To The Proper Authorities:
If you have given out your credit card information, contact your credit company right away. The sooner a company knows your account may have been compromised, the easier it will be for them to help protect you. Contact the company that you believe was forged. Remember to contact the organization directly, not through the email message you received. Or call the organization and speak to a customer service representative.
Change The Passwords On All Your Online Accounts.
Many people use the same password for multiple accounts. Start with passwords that are related to financial institutions or personal information. If you think someone has accessed your email account, change your password immediately. Review your credit reports, your bank, credit card statements, and your credit report monthly for unexplained charges, inquiries or activity that you did not initiate. Finally, make sure you use the latest products, such as anti-spam and anti-phishing capabilities in email services, phishing filters in Web browsers and other services to help warn and protect you from online scams. UK Times Online TIP: One strategy for combating phishing or any scam is to help educate and train our members to recognize the phishing and other scam attempts, and to deal with them. Education can be effective, especially where training provides direct feedback such as our group forums. TIP: I also have been a victim of Phishing. Someone hacked my Gmail account and my passwords and ids were used to log into some of my other accounts before I discovered the problem. What a disaster that was for me. Learn How to Protect Yourself and Your Identity
6.19 INTERNATIONAL MODEM DIALING
Customers of dial-up Internet Service Providers, such as AOL, use a modem to dial a local connection number. Some web sites, normally containing adult content, use international dialing to trick
68
INTERNET USERS HANDBOOK
consumers into paying to view content on their web site. Often these sites purport to be free and advertise that no credit card is needed. They then prompt the user to download a "viewer" or "dialer" to allow them to view the content. Once the program is downloaded, it disconnects the computer from the Internet and proceeds to dial an international long distance or premium rate number, charging anything up to US$7-8 per minute. An international block is recommended to prevent this, but in the U.S. and Canada, calls to the Caribbean (except Haiti) can be dialed with a "1" and a three-digit area code, so such numbers, as well as "10-10 dial-round" phone company prefixes, can circumvent an international block. One example is www4.bux.to
6.20 INTERNET FRAUD/SCAMS
The term "Internet Fraud" generally refers to any type of Scam or Fraud scheme that uses one or more online services to present fraudulent solicitations to prospective victims, to conduct fraudulent transactions, or to transmit the proceeds of fraud to financial institutions or to others connected with the scheme. Internet fraud can take place on computer programs such as chat rooms, email, message boards, or Web sites.
6.21 INVESTMENT SCHEMES/ STOCK MARKET MANIPULATION
These are also called investment schemes online. Criminals use these to try to manipulate securities prices on the market, for their personal profit. According to enforcement officials of the Securities and Exchange Commission, the 2 main methods used by these criminals are:
PUMP-AND-DUMP SCHEMES
False and/or fraudulent information is disseminated in chat rooms, forums, Internet boards and via email (spamming), with the purpose of causing a dramatic price increase in thinly traded stocks or stocks of shell companies (the "pump"). As soon as the price reaches a certain level, criminals immediately sell off their holdings of those stocks (the "dump"), realizing substantial profits before the stock price falls back to its usual low level. Any buyers of the stock who are unaware of the fraud become victims once the price falls. When they realize the fraud, it is too late to sell. They lost a high percentage of their money. Even if the stock value does increase, the stocks may be hard to sell because of lack of interested buyers, leaving the shareholder with the shares for a far longer term than desired.
SHORT-SELLING OR "SCALPING" SCHEMES
This scheme takes a similar approach to the "pump-and-dump" scheme, by disseminating false or fraudulent information through chat rooms, forums, Internet boards and via email (spamming), but this time with the purpose of causing dramatic price decreases in a specific company's stock. Once the stock reaches a certain low level, criminals buy the stock or options on the stock, and then reverse the false information or just wait for it to wear off with time or to be disproved by the company or the media. Once the stock goes back to its normal level, the criminal sells the stock or option at a profit.
69
INTERNET USERS HANDBOOK
INTERNET INVESTMENT SCAMS The US Security Exchange Commission Guidelines:
The Internet allows individuals or companies to communicate with a large audience without spending a lot of time, effort, or money. Anyone can reach tens of thousands of people by building an Internet web site, posting a message on an online bulletin board, entering a discussion in a live "chat" room, or sending mass emails.
If you want to invest wisely and avoid frauds, you must get the facts.
The types of investment fraud seen online mirror the frauds perpetrated over the phone or through the mail. Consider all offers with skepticism. Do not use your credit card number and CVV number to buy products from online lesser-known merchants.
6.22 MARKETING AND RETAIL FRAUD
This is a fast-growing area of Internet fraud perpetrated by dishonest Internet marketing and retail sites. A variety of products and services are involved. The customer is tricked by a legitimate-looking site and effective marketing into giving their credit card information and CVV number, or sending cash by other means, in exchange for what they believe to be the goods or services. The goods never arrive, or they turn out to be fake, or are products worth less than those advertised. Where a credit card is involved, the perpetrators may also aim to use the customer's credit card information to obtain cash or to make purchases of their own. A common example of this type of fraud is pornographic websites that advertise free access. Upon further inspection, however, a credit card is required "for age verification purposes only". The scammers then use your credit card information to make large charges to the credit card. In cases involving fake or worthless goods, many are health products, related to health fraud. These products might advertise anything from a quick way to lose weight to a cure for a serious disease, and may:
PROMISE A LOT, CLAIMING THEY CAN "DO IT ALL"
Claim to be a "scientific breakthrough", featuring fake doctors or scientists making claims for the product, with technical jargon that only experts in the field know is used falsely Feature a long list of "personal testimonials", with no way to check if they are true or fake. Once your credit card information is given to these types of scam companies, they usually will charge you no matter what type of cancellation you attempt to go through. This can often be overcome by contacting the credit card company. Credit and consumer protection laws in many countries hold the credit card company liable to refund their customers' money for goods or services purchased with the card but not delivered. The loss is then suffered by the card company, but ultimately passed on to customers in higher interest and fees.
6.23 MATRIX SCHEME SCAMS
Im sure youve seen many varieties of the matrix program. They usually contain the statement If everyone does the same thing and come in many different flavors. There are 39 matrices and 22
70
INTERNET USERS HANDBOOK
matrices and 33 matrices. There are matrices of unlimited width and matrices that feed into other matrices. In fact, there are as many combinations of matrices as there are ways you can put people into a matrix. You can create almost any type of pay plan with a matrix and there are many, many kinds of plans. There is nothing dishonest about this arrangement, in fact it is one of the few plans that actually pays out less than it brings in, which makes it sustainable. This is good for you and good for the program owner since it means that theoretically the matrix can continue forever. Matrix plans are extremely flexible which are why there are so many variations on the matrix theme. Because you can create almost any kind of pay plan with a matrix they can be created good, no so good and even downright bad by those who let greed overcome them. The pay plans of matrices can be as different as night and day. But, the matrix plans do all have one thing in common. They all rely on the statement If everyone does the same thing. Ask yourself when is the last time you remember that everyone did the same thing. I think youll come up with the same answer that I did Never. So, there are some things you need to know about matrix programs before you join one. The first thing is how things work when everyone does the same thing and the other is how to tell a good matrix from a bad matrix.
HOW TO AVOID THE MATRIX SCAM
First you need to know how much the matrix will potentially pay out if all of the positions are filled. To get this number simply add all of the commissions paid through each level if the matrix were filled. This will tell you how much the owners profit is on the matrix. A lower profit is obviously better since it means more money is being paid out to members. Of course the owner will also have the first position in the matrix. And there is no way to know if he/she has taken additional positions as well. You should also consider the pay outs for positions on each level. Some matrices are set up to pay out a lot for the first level to help members become profitable quickly. This is good if youre in early, but it means that there is less money left for later positions when there are more total members. This can limit the overall potential of the matrix. Other matrices will offer higher payouts for levels 2 or 3 in the members downline. This encourages members to recruit and help build their downline. This can be an effective way to keep the matrix together for a longer period of time. Finally, matrices can be set up to pay out on the bottom most level. This can make some matrices look very attractive since it appears there is a HUGE potential when the matrix is completely filled. Of course the matrix owner knows that almost every person who subscribes will never see anyone on their lowest level so he will never have to make that huge payout. Basically matrix plans can be good, not so good or downright bad. There are some people who do make money in matrix plans and there are also a lot of people who lose money in programs that have matrix pay plans.
71
INTERNET USERS HANDBOOK
The difference is that the people who make money in matrix plans know that everyone wont do the same thing and that it takes a huge amount of time and effort to fill a matrix and keep it filled. Those who lose money in matrix pay plans are the majority of people who sign up and then think that someone else will fill up their matrix because others will do the same thing they did and there will be enough spillover to go around. As youve seen it just doesnt work that way. If you dont want to be one of the people who have lost money in a program with a matrix pay plan then always remember that the only way you will be successful with any program is to put a lot of work into it. There is no such thing as a lazy mans way to get rich and dont expect that everyone will do the same thing. The only way to become successful at anything is through hard work and effort. Dont expect others to do your work for you because they wont. Period. If you do get into a matrix and there is someone else who is working as hard as you in the matrix then that is just icing on your cake. MatrixSchemeScam
6.24 MICROSOFT BETA TEST HOAX
In one of my previous lives, I was a beta tester for several software organizations, including Microsoft. This scam has been around for a while
SUMMARY OF THE SCAM
Revamped version of the Microsoft email beta test hoax includes "testimonies" and a bank account screenshot of supposed money received. The message claims that Microsoft will send money to anybody who forwards it to others (Full commentary below). Subject: FW: Cant lose, try it .... read testimonies below! U won't believe it ...I just had a look at my bank statement & there was an extra .wait for it .......50 000.00 in my account. This really works .........just do it ...I love u Douglas ....thank u some much for thinking of me & this GREAT gift!!! ------ HI GUYS. THIS IS NOT A SCAM - TRY IT!! Hey Ben Ive already done this a few months ago, I received R9 569.00. Regards, I (not me) thought this was a scam myself, but two weeks after receiving this email and forwarding it on, Microsoft contacted me for my address and within days, I received a check for US$24, 800.00. You need to respond before the beta testing is over. If anyone can afford this Bill Gates is the man. It's all marketing expense to him. Please forward this to as many people as possible. You are bound to get at least US$10, 000.00. Were not going to help them out with their email beta test without getting a little something for our time. My brother's girlfriend got in on this a few months ago, when I went to visit him for the Baylor/UT game. She showed me her check. It was for the sum of $4,324.44 and was stamped "Paid In Full". Like I said before, I know the law, and this is for real. Intel and AOL are now discussing a merger which would
72
INTERNET USERS HANDBOOK
make them the largest Internet Company and in an effort make sure that AOL remains the most widely used program, Intel and AOL are running an email beta test. When you forward this email to friends, Intel can and will track it (if you are a Microsoft Windows user) for a two week time period. For every person that you forward this email to, Microsoft will pay you $203.15. For every person that you sent it to that forwards it on, Microsoft will pay you $156.29 and for every third person that receives it, you will be paid $17.65. Within two weeks, Intel will contact you for your address and then send you a check. I thought this was a scam myself, but a friend of my good friend's Aunt Patricia, who works at Intel, actually got a check of $4,543.23 by forwarding this email. Try it; what have you got to lose????
6.25 MONEY TRANSFERS FRAUD
This type of Fraud consists of an employment offer to help transfer money to a foreign company, supposedly because it costs too much to do it through other methods (which is usually not the case). The prospective victim receives an email like these 4 examples:
Example
Dear Sir/Madam, XX is a small scale company in XX. We supply XXX to clients in some countries. We have reached big sales volume in the Europe as a starter, and now we are trying to penetrate the US/Canada market. Quite soon we will open representative offices or authorized sales centers in the US and therefore we are currently looking for people who will assist us in establishing a new distribution network there. The fact is that despite the US market is new for us we already have regular clients also speaks for itself. The international money transfer tax for legal entities (companies) in XX country is 25%, whereas for the individual it is only 7%. There is no sense for us to work this way, while tax for international money transfer made by a private individual is 7%. That is why we need you! We need agents to receive payment for products in money orders, check or bank wire transfers) and to resend the money to us via Money Gram or Western Union Money Transfer. This way we will save money because of tax decreasing. JOB DESCRIPTION? Receive payment from Clients Cash Payments at your Bank Deduct 10%, which will be your percentage/pay on Payment processed. Forward balance after deduction of percentage/pay to any of the offices you will be contacted to send payment to (Payments are to be forwarded either by Money Gram or Western Union Money Transfer). How Much Will You Earn? 10% from each operation! For instance: If you receive 7000 USD via cheques or money orders on our behalf. You will cash the payment and keep $700 (10% from $7000) for yourself! At the beginning your commission will equal 10%, though later it will increase up to 15%!
73
INTERNET USERS HANDBOOK
Advantages: You do not have to go out as you will work as an independent contractor right from your home office. Your job is absolutely legal. You can earn up to $30004000 monthly depending on time you will spend for this job. You do not need any capital to start. You can do the Work easily without leaving or affecting your present Job. The employees who make efforts and work hard have a strong possibility to become managers. Anyway our employee never leaves us. MAIN Requirements: 18 years or older legally capable responsible ready to work 24 hours per week, with PC knowledge email and Internet experience (minimal) and please be informed that everything is absolutely legal. If you are interested in our offer, please reply to the following email address: XX@XXXXX with your; (1) Your full names: (2) Contact address: (3) Tele/cell numbers: (4) Occupation: (5) Age: (6) Sex: Thanks for your anticipated action. And we hope to hear back from you soon.
6.26 NIGERIAN HOAX SPAWNS COPYCATS
URGENT RESPONSE REQUIRED Undisclosed recipients Dear Sir/Madam, With full corporate responsibility under penalty of Perjury, I want to ask your personal assistance and co-operation as I propose hereunder: I am the Manager of Northern Investment Bank, England, United Kingdom and I got your contact details during my search for a reliable, honest and a trust worthy person to entrust with this transaction. I was introduced to the late Yugoslavian President, Mr. Slobodan Milosevic during the Kosovo war in 1999 and when he confidentially deposited 450 Kilograms of Gold Bars and a huge sum in a fixed deposit account with my branch. Unfortunately, Mr. Milosevic did not leave any beneficiary for this deposit and that made it impossible for us to contact any of his Family to claim the Fund. Then I decided to move the fund into a suspense account without beneficiary and find a Partner in the Gulf region who can assist me to withdraw this deposit as beneficiary/depositor. I have already submitted an audited approved end of the year Report for the year 2008 of my branch to our head office at Makola Shopping Mall here in London; this excess will never be discovered. As an officer of the bank I cannot legally withdraw this money, but I want to use you as Front to claim the fund legitimately. Thus I am impelled to request for your assistance to receive this money into your bank account. I intend to part 40percent of this fund and the balance shall be for me. I do need to stress that there are practically no hazard involved in this transaction. The transaction will be a bank-to-bank transfer and I will apply for my annual Leave so that I can travel to meet you once transfer is confirmed into your account. I will send you detail arrangement of the procedures that we shall apply to legally transfer the fund into your bank account, when I receive your confirmation. Your timely response will be appreciated and you can call me on Cell phone: +xx-703-592-3735 anytime 24/7.
74
INTERNET USERS HANDBOOK
6.27 PAYPAL FRAUD
This is new form of fraud where a buyer (a scammer) will target eBay auctions which are "Collection in person" and will have a fake address or storage address with P.O. Box (as eBay/PayPal now allows unconfirmed address and these transactions are not covered by seller protection.) What these people will do is buy an item from the seller and intend to collect it in person. This person will collect the item and will claim back, stating he hasn't received the item. PayPal has user policy that IF they do not have a tracking number they will grant the money back to the scammer (PayPal does not take video evidence, signature proof or any other proof as valid collection.) It is strongly suggested, if you are selling items with collection in person, that you do cash transactions by handing the item and collecting cash to avoid the scheme.
6.28 PHARMING
Pharming is the exploitation of vulnerability in the DNS server software that allows a hacker to acquire the domain name for a site, and to redirect that website's traffic to another web site. DNS servers are the machines responsible for resolving Internet names into their real addresses - the "signposts" of the Internet. If the web site receiving the traffic is a fake web site, such as a copy of a bank's website, it can be used to "phish" or steal a computer user's passwords, PIN or account number. Note that this is only possible when the original site was not SSL protected, or when the user is ignoring warnings about invalid server certificates. For example, in January 2005, the domain name for a large New York ISP, Panix, was hijacked to a site in Australia. In 2004 a German teenager hijacked the eBay.de domain name. Secure email provider Hushmail was also caught by this attack on 24th of April 2005 when the attacker rang up the domain registrar and gained enough information to redirect users to a defaced webpage.
6.29 PHISHING
"Phishing" is the act of attempting to fraudulently acquire sensitive information, such as passwords and credit card details, by masquerading as a trustworthy person or business with a real need for such information in a seemingly official electronic notification or message (most often an email, or an instant message). It is a form of social engineering attack. The term was coined in the mid-1990s by crackers attempting to steal AOL accounts. An attacker would pose as an AOL staff member and send an instant message to a potential victim. The message would ask the victim to reveal his or her password, for instance to "verify your account" or to "confirm billing information". Once the victim gave over the password, the attacker could access the victim's account and use it for criminal purposes, such as spamming. Phishing has been widely used by fraudsters using spam messages masquerading as large banks (Citibank, Bank of America) or PayPal. These fraudsters can copy the code and graphics from legitimate websites and use them on their own sites to create legitimate looking scam web pages. They can also link to the graphics on the legitimate sites to use on their own scam site. These pages are so well done that most people cannot tell that they have navigated to a scam site.
75
INTERNET USERS HANDBOOK
Fraudsters will also put the text of a link to a legitimate site in an email but use the source code to links to own fake site. This can be revealed by using the "view source" feature in the email application to look at the destination of the link or putting the cursor over the link and looking at the code in the status bar of the browser. Although many people don't fall for it, the small percentage of people that do fall for it, multiplied by the sheer numbers of spam messages sent, presents the fraudster with a substantial incentive to keep doing it. Anti-phishing technologies are now available. In the field of computer security, phishing is the criminally fraudulent process of attempting to acquire sensitive information such as usernames, passwords and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT administrators are commonly used to lure the unsuspecting public. Phishing is typically carried out by email or instant messaging and it often directs users to enter details at a fake website whose look and feel are almost identical to the legitimate one. Even when using server authentication, it may require tremendous skill to detect that the website is fake. Phishing is an example of social engineering techniques used to fool users and exploits the poor usability of current web security technologies. Attempts to deal with the growing number of reported phishing incidents include legislation, user training, public awareness, and technical security measures. Almost half of phishing thefts in 2006 were committed by groups operating through the Russian Business Network based in St. Petersburg.
PHISHING TECHNIQUES
People have a built-in reaction to things that seem important. Subjects lines worded to arouse anxiety usually prompt immediate action. An email with the subject: "to restore access to your bank account ..." will usually get instant attention and prompt most people to click to read what happened. Everyone can help educate the public by encouraging safe practices, and by avoiding dangerous ones. Unfortunately, even well-known players are known to incite users to hazardous behavior, e.g. by requesting their users to reveal their passwords for third party services, such as email. Wikipedia
PHISHING EXAMPLE
Reply |Donald Loan Investment Company Show details 6:37 PM (11 hours ago) tolic@mail2world.com to (Empty) date Wed, Nov 4, 2009 at 6:37 PM subject Loan Offer reply-
TIP. GMAIL Warning: This message may not be from who it claims to be. Beware of following any links in it or of providing the sender with any personal information. Learn more ATTN: (Empty)
76
INTERNET USERS HANDBOOK
My names are KLARK DONALD; I am a certified loan lender. I offer secured and unsecured loans to individuals and companies at low interest rate. I offer long and short-term loans. My firm has recorded many breakthroughs in the provision of first class financial services to our clients especially in the area of Loan syndication and capital provision for individuals and companies. In general, we offer mortgages, home loans, car loans, hotel loans, commercial loans, construction loans, start-up- working capital loans, business loans and bad credit loans, etc., at 0.5% interest rate. We would love to fund projects at hand and offer personal loans as well to you, your firm/partners and clients. We offer the right solution to your financial needs. We stand apart from other lenders because we believe in customer service and we stay with you until you get the results you want. We are a group of energetic and experienced loan professionals with through knowledge of financial markets. We have many partners in real estate; banking and technology fields that can assist obtain financing. Almost all of our businesses are through referrals by satisfied and repeat customers. We have brought ailing industries back to life and we back good business ideas by providing funds for their upstart. We have a network of Investors that <DIV> are willing to provide funds of whatever amount discreetly to individuals and organizations to start business and operations. As the leading provider of Commercial, Business and personal loans to individuals and corporations nationwide, we offer the right kind of financing in less amount of time it will take with traditional lenders. In our bid to be useful to you, Funds (Loan) will be electronically wired into your State account, which will be provided by you. Interested Persons should fill out the Application Form below. Application Form: Donald Loan Investment Company
DON'T BE A PHISHING VICTIM
Was that email asking for your password really from your bank? Learn how phishing uses fraudulent email messages and spoofed Web sites to trick you into giving out private information. Better yet, learn to protect yourself from being a victim. PHISHING IS REALLY OLD NEWS, when you think about it. In fact the term "phish" is actually a portmanteau of the words "phone" and "fish" and has nothing to do with the Internet at all. Rather, it stemmed from an age-old credit card scam in which a person pretending to be a representative of a credit card company would make dozens of calls to strangers, "fishing" for a victim. He would warn them that their credit card identities had been compromised and ask that they answer some security questions. Given enough psychological pressure, they eventually reveal their security numbers to him, and bang! The victim was "phished". Phishing works through the manipulation of our desires and fears. Although technology and banking has made significant progress since the first phone cons of the late 1980s, one thing remains the same:
77
INTERNET USERS HANDBOOK
people are still susceptible to psychological trickery. And although the phone phish is still alive and well, the phishing we really have to watch out for these days takes place over the Web. THE EMAIL PHISH The most common kind of phish today is carried out by email. A message arrives in your inbox cautioning you about a security breach in your financial service provider's system, or maybe just to tell you that your account is about to be suspended due to lack of activity. The message asks that you log in to the website immediately to change your password as a precautionary measure. Click the link; and you will be directed to a fake website that looks identical to the official bank's website. The moment you key in your "current" username and password, the criminals behind the scam will have all they need to clean out your bank account. And unless you log on to the real website within the next few minutes and change your password again, that is precisely what they will do. Most banks are well aware of the risks of email phishing. Nonetheless, you can help stem the menace by forwarding any email that you receive to your bank's customer service center. This will allow them to investigate the origin of the email and (hopefully) take action against the perpetrators.
THE MALWARE PHISH
Email systems these days generally block any attachment with an ".exe" extension, so it's been a long time since we've experienced a massive virus outbreak via email. Not to be outdone, however, phishers have resorted to sending out ZIP archive attachments that purportedly contain important shipping information, wire transfer information, or even PDF documents. Look inside these ZIP archives and you will see Excel icons, PDF icons and Word icons: files that looks like ordinary office documents, but are in fact malware executable loaded with evil Trojans. These Trojans are typically variants of "Zeus", "BredoLab" and the infamous "Microsoft Online Helper! Once installed, they work together to steal data from your computer and record your online usernamepassword combinations. The criminals behind the scheme can also remotely operate your computer to engage in other criminal activity such as sending spam while propagating the phish by sending itself to everyone in your address book. To avoid being fooled into running malicious programs disguised as ordinary office documents, make sure you can see file extensions on your PC. Go to any Windows Explorer window and select Folder Options from the Tools menu. Click the View tab and uncheck the "Hide extensions for known file types" option, then click OK. You'll notice that all the files on your PC will now show their extensions such as ".doc", ".xls" or ".pdf". If you see something that looks like an Excel spreadsheet or PDF document but has an ".exe" extension, you'll know it's a virus. Of course, ".exe" extensions are not the only kind of file you should watch out for. There are many other executable file types that can wreak havoc on your computer if activated.. Microsoft Business
DON'T GET CAUGHT BY THE PHISHING SCAMS
In the wake of this weeks large-scale phishing theft of online email accounts from Hotmail, Gmail, Yahoo and more, we contacted Microsoft to ask how concerned readers might protect themselves.
78
INTERNET USERS HANDBOOK
According to the most recent version of Microsofts Security Intelligence Report, more than 97 percent of email messages sent over the Internet are unwanted, have malicious attachments, are phishing attacks, or are spam. Adapted below are the companys recommendations on how to avoid getting caught by the phishers, and what to do if your online identity is compromised by thieves?
HOW CAN YOU RECOGNIZE A PHISHING SCAM?
Any email asking for your name, birth date, social security number, email username, email password, or any other type of personal information, no matter who the email appears to be from, is almost certainly a scam. Emails that are poorly worded, have typos, or have phrases such as "this is not a joke" or "forward this message to your friends" are generally scam emails. Phishing mail often includes official-looking logos and other identifying information taken directly from legitimate Web sites, and it may include convincing details about your personal information that scammers found on your social networking pages. A few phrases to look for if you think an email message is a phishing scam are: "Verify your account." "If you don't respond within 48 hours, your account will be closed."; "You have won the lottery.
WHAT SHOULD YOU DO IF YOU HAVE RECEIVED A PHISHING EMAIL?
Take some time to check up on the email. Most importantly, NEVER click on the link or give out personal information. It is possible for your computer to become infected with malicious software simply by visiting a phishing site without you even realizing it. Sites like snopes.com list common email scams. Go to the website of the company you received the email from and contact their customer service reps via phone or online to verify the validity of the email. Make sure you have created a strong password for your account by using more than 7 characters and having a combination of upper and lower case characters, numbers, and special characters, like the @ or # symbols. It's also a good idea to change your password on a regular basis. Report the phishing scam and help identify new scams. If you use Windows Live Hotmail and received a phishing email, you can select the dropdown next to "Junk, and select "Report phishing scam. Whatever you do, do not reply back to the sender. UK Times Online
ALERTPAY JOINS THE ONLINE SCAM PREVENTION EFFORT
Friday, April 8, 2011 Phishing alert: Recognizing the latest scam involving AlertPay's name AlertPay Scam Prevention. Some of you may have heard about a scam taking place through Facebook regarding our payment platform's name. Someone out there has been posting messages on people's Facebook walls telling them about Alert Pays "Own0" contest. The message directs readers to a website that looks just like our login page, but it actually IS NOT in any way affiliated with the real AlertPay.com. How can you tell if it is not indeed our own website? Well, it's actually quite simple. Our URL is "AlertPay.com", not "AlertPay.own0.com". So if you come across a URL that reads like the latter, DO NOT enter your login credentials as this will compromise your security and the confidentiality of your personal information. Here is what it looks like on Facebook:
79
INTERNET USERS HANDBOOK
It's really quite a clever scam in that the con artist is actually referring to the contest as "Own0" -- the extension at the end of the fake AlertPay URL (what appears after "alertpay"). This subtle move is just enough to convince people that the URL is legitimate when, again, it is NOT. It's also important to note that the alleged "AlertPay Facebook assistant's" post is not well-written. Although we are far from the best writers in the world (there can only be one Hemingway), but we do pay much attention to spelling, format and grammar.
How It Works
If you click on this link, it will whisk you away to a FAKE AlertPay login page and you will be prompted to enter your login credentials. It will appear that the page is reloading and will actually redirect you back to the original login page. Why the reloading? Probably to confuse you! After entering your credentials and clicking on the login button, the scammer is actually recording the information you entered into the "email" and "Password" fields. Once they capture those details, they can come straight to our website and gain access to your account to do what they please. You do not want this, so do not click on the link. If it does not say "AlertPay" or "AlertPay.com/ [name of one of our sub-pages], avoid clicking on it at all costs Furthermore, our Security team is highly skilled in the art of busting people like this, but this is no excuse to be complacent. Your knowledge of these things is ultimately your responsibility so please do a little homework on the types of scams that can (and do) take place regularly in the online world. We are not trying to scare you all, but we believe we need to be blunt and just a little frightening to communicate the gravity of these types of scams. AlertPay
ADOBE PHISHING SCAMS
Adobe software like Acrobat, Reader and Flash has long been targeted by malware developers to deliver all manner of different scams. According to PC World, Adobe phishing scams simply prey on the heightened awareness of Adobe security issues. In other words, Adobe scams come disguised as security patches. Luckily, there are some signs to look out for to tell if a security patch is legit or if its a phishing attempt. Firstly, you might receive an email with the security update. Adobe does not usually email users about their security patches. Rather, the updates are installed automatically when you boot up your computer. If youve received an email that looks like its from Adobe, check the actual sender email address. If it says anything other than [xxxx]@adobe.com, odds are its a phishing attempt. TIP. One of most obvious tell-tale signs of any phishing attempt is atrocious grammar and spelling mistakes, as well as confusing content referring to Adobe Acrobat Reader without specifying which software you will be updating. AlertPay
80
INTERNET USERS HANDBOOK
THE SOCIAL NETWORK PHISH
Emails are not the only way people phish these days Twitter, Facebook and other social networking services are all battling a sharp rise in phishing scams. The most famous example of a social network phish so far this year is TwitViewer: a service that pretends to show you who viewed your Twitter profile recently. There's no way TwitViewer can do this, of course, because Twitter doesn't make this information available. Nonetheless, thousands of users who saw the TwitViewer tweet eagerly logged onto TwitViewer to see who'd checked them out recently. They were asked to key in their Twitter usernames and passwords and were then presented with a fictitious list of Twitter users who supposedly viewed their profiles. The cybercriminals then purportedly uses the victims' real Twitter credentials to flood Twitter with thousands of spam messages. Cyber criminals have also learned that many users tend to use the same usernames and passwords for all their online accounts, which are somewhat true I have the same username for Twitter, Gmail, Amazon, Hotmail and WordPress: marcusgomez. If a criminal manages to trick me into revealing my username and password for one service (the way TwitViewer got people to give up their Twitter credentials, for example), they can try using the same credentials on the other services and thereby hijack my other accounts. They may even try to use the credentials with online banking websites. For this reason, security experts generally recommend you maintain your online financial accounts as entirely separate identities, and that they have their own unique usernames and passwords. Microsoft
6.30 PTR/PTC SCAMS
These sites promise high earnings; the keyword for most of them, but they also claim payouts, when in fact no cash changes hands. Earnings are different from Payment. Why, because the ad revenue could not possible meet the payouts claimed. Most of the ads are self-promoting or promoting within their groups of sites, so PTC/PTR advertising PTC/PTR where is the real money from outside advertisers? Memberships are typically low less than 10,000 as compared to the number of user online looking for business opportunities. Perhaps that means that the majority is smarter than me, and simply avoids the sites. Almost nothing, you read should be believed. The information is usually inconsistent between the pages: home, FAQ, upgrades, etc. Upgrades ranges from about $10 - $500 depending on the site. If you upgrade and expect payouts within a certain period of time as specified in the upgrade page; often the site redemption page will be revised to say your payout will made to you after your account is 30-90 days old.
81
INTERNET USERS HANDBOOK
When that period is reaches the Cashout tab never comes. Online contact and emails are never replied to unless they just want your money. I did get a reply form one company that when I advised them that I wanted to upgrade, but that I have found their name on a Scam List; they came back and said they were not a scam and that they pay according to the terms of their site. Often your site; will never be upgraded even though you have already paid for an upgrade; once again, contact and emails will not be answered. Site offering computers, cameras, etc. are Scams and never send the merchandize. Sites offer 100% refund or guaranties if the site is not upgraded within a certain period are Scams. Most sites can be upgraded in minutes once the payment is accepted, if you think about it. Some sites, when a payment request is made; will respond back to you that they have changed their system, and that if you fund an additional fee called a trade fee of .1 to 1 percent they will send your money immediately. That is another Scam. If you pay for an upgrade, keep your receipts and other details, in order to claim or file a dispute with the payment gateway: PayPal, Alert Pay, etc. I believe this is why many sites can no longer do business with PayPal because of the complaints. Sites that monitors these types of sites, will advise you that any site that offers you more than $1.00 to read and email is a scam. I would change that and say forget any site that offers you more than $0.50 cents. These same reporting sites also advise that if the sites dont offer you a Forum to communicate with them is probably a Scam. I would change to that because even if they have a Forum, they may not allow you to entry a reply or complaint as discussed elsewhere herein. Another group of Scam sites that I had offered Live Messenger, but you couldnt access it. I guess the owner wanted his sites to look more legitimate. These same sites also changed the contract them categories to include a category for nonpayment; however, no replies have ever been received by me for such requests
6.31 PURCHASE SCAMS
The most straightforward type of purchase scam is a buyer in another country approaching many merchants through spamming them and directly asking them if they can ship to them using credit cards to pay. EXAMPLE: From: XX [XXX@hotmail.com] Sent: Saturday, October 1, 2005 11:35 AM Subject: International order enquiry Goodday Sales, This is XX and I will like to place an order for some products in your store, but before I proceed with listing my requirements, I will like to know if you accept credit card and can ship
82
INTERNET USERS HANDBOOK
internationally to Lagos, Nigeria. Could you get back to me with your website so as to forward you the list of my requirements as soon as possible? Regards, Most likely, a few weeks or months after the merchant ships and charges the Nigerian credit card, he/she will be hit with a chargeback from the credit card processor and lose all the money.
6.32 REMOTE ACCESS COMPUTER SCAMS
Hey everyone I want to let you know of a new scam that almost tricked me yesterday I received a phone call from a gentleman claiming he is with a company that does contracting with Microsoft I could hear many people talking in the back ground this is from a call center obviously. He said your computer could have some errors and we can fix them up today he directed me to where the errors where and he was right I had a lot of errors on the computer and he sad dont worry we will fix this up today and sped up your computer then he directed me to a website that does remote access to my computer then I realized this guy was wanting to hijack my banking information so be weary of anyone that calls you up out of the blue and wants remote access to your computer Ken Miami-Water.com/blog I am in Australia too, and despite being on the Don Not Call Register I received half a dozen calls like this. On one those calls I tried to get information about the company the caller was working for. It was obvious she was reading from a script, and had no knowledge of what she was talking about. I hope she took my advice to get a real job, but I doubt that. Neville Dinning
6.33 RE-SHIPPERS
Re-shipping scams trick individuals or small businesses into shipping goods to countries with weak legal systems. The goods are generally paid for with stolen or fake credit cards.
NIGERIAN VERSION (SEE WIKIPEDIA OF OTHER EXAMPLES)
In the Nigerian version, the fraudsters have armies of people actively recruiting single women from western countries through chat and matchmaking sites. At some point, the criminal promises to marry the lady and come to their home country in the near future. Using some excuse the criminal asks permission of his "future wife" to ship some goods he is going to buy before he comes. As soon as the woman accepts the fraudster uses several credit cards to buy at different Internet sites simultaneously. In many cases the correct billing address of the cardholder is used, but the shipping address is the home of the unsuspecting "future wife". Around the time when the packages arrive, the criminal invents an excuse for not coming and tells his "bride" that he urgently needs to pick up most or all the packages. Since the woman has not spent any money, she sees nothing wrong and agrees. Soon after, she receives a package delivery company package with pre-printed labels that she has agreed to apply to the boxes that she already has at home. The next day, all boxes are picked up by the package delivery company and shipped to the criminal's real address (in Nigeria or elsewhere). After that day the unsuspecting victim stops receiving communications from the "future husband" because her usefulness is over. To make matters worse, in most cases the criminals were able to create accounts with the package deliverer, based on the woman's name and address. So, a week or two later, the woman receives a huge freight bill from the shipping company which she is supposed to pay because the goods were shipped from her home. Unwittingly, the woman became the criminal reshipper and helped him with his criminal actions.
83
INTERNET USERS HANDBOOK
TIP: These Types Of Communications Usually Have Many Grammar And Spelling Mistakes. (Most have been corrected here for ease of reading and understanding)
EXAMPLE: RE-SHIPPER EMAILS
Dear XXXX, Thanks for the total quote of my order. The total cost of my order is quite correct and okay by me and I am ready to pay the bills. I shall inform my freight forwarder who will be coming to pick up the order to hold on and come immediately you inform me that the items are ready for pick up then I can give you a call on that day to get the items packed for pick up and they will call you on their arrival at your address. Also I want you to help me Charge another $1200.00 from my card to the shipping agent who will be coming to pick up my ordered items from you. The $1200.00 that will be sent to the freight forwarder is for the shipping of my order and other items I ordered from different part of the country, which is to be picked up by him, and should be deducted from my credit card. Also, I am compensating you with the sum of $150.00 for the transfer fee and for your efforts. Please note that I should have given the shipping agency my credit card for him to deduct the shipping funds but he told me that he doesn't have the facilities to charge or debit credit card, so that's why I bring my vote of confidence in you and I want you to assist me in this measure, so I want you to transfer the funds to him after you have make the charges and the money charged from my credit card is in your account, then you can now make the transfer to the agent via western union. I will have love to do this myself but there are no western union here around me cos I am out of town to monitor my estate construction at a remote village, So the charges you'll make on my credit card will be Order Fee: 3,114.61 Agent fee with shipping fare: $1,200.00 Transfer Fee plus Your Compensation: $150.00 Total: $4464.61 Note that my credit card will be charged for the amounts above. Please do get back to me if you are in the office right now so that I can forward my credit card details to you, then you can charge the funds I await your quick response.
6.34 SEO INTERNET MARKETING FRAUD
Search Engine Optimization (SEO) fraud involves a supposed Internet marketing specialist presenting a prospective client with detailed graphs and charts that indicate that his web site receives (x) thousands of hits per month. The specialist emphasizes that payment for his services will increase web traffic, in return increase costumers. The marketer then proceeds to not provide the proposed services. Wikipedia
SEO FRAUD AND SCAMS BEWARE!
Top 400, 2,000, or 5,000 SE and Directories or whatever. There is no such thing! Anyone who advertises they will submit you to more than 12 search engines and directories is submitting to what are known
84
INTERNET USERS HANDBOOK
in the industry as FFA's (free for alls), classifieds, 404's (errors), not founds (pages which no longer exist), or foreign language sites. It is well known amongst online marketing experts, there are less than 12 working search engines and directories on the Internet today. Some companies take advantage of the uninitiated website owner promising top rankings for $29.95 or something similar. Beware of such promises - if it sounds too good to be true, it usually is. That $29.95 will typically buy an automated submission to 10,000 "engines" that nobody ever visits or possibly even result in a domain ban for over submitting. Once the $29.95 campaign is finished, so is your domain. There is no such thing as #1 ranking in all search engines or "it only takes 2 weeks and $29.95". Getting top search engine ranking doesn't "just happen". SEO fraud is obvious when they guarantee rankings. No one can guarantee rankings. Some people are better at SEO than others, but no one has direct control over how search engines rank (unless you want to pay for top listing).
CONTENT
Half of SEO is content. If you want a higher ranking, you need content that people want to read. If your SEO firm doesnt provide this, and they wont find the proper keywords, they really arent SEOs. SEO is an ongoing process. No one can SEO your website within a month, and expect it to receive high rankings. Dont be fooled. High ranking is not easy, and onetime fees are a waste of money unless you or the SEO Company plans to make weekly changes. Beware Of Fraud!
WATCH THE SEO OPTIMIZATION GUARANTEE SCAMS!
Don't be fooled by so-called "optimization guarantees" that sound good in the headlines but have enough small print to be virtually meaningless. Having your web site rank high in the search engines is a science and the rules for search engine optimization (SEO) are always changing. These companies give true search engine optimization professionals a bad name. Therefore, even if you do not choose us as your website solutions company, we urge you to keep an eye open and stay clear of companies that guarantee #1 positioning. Nobody can guarantee a top search engine placement, you better be sure you're not trapped by unethical SEO services, spam and doorway pages that might jeopardize your website investment. What could appear to be excellent results could sooner or later get your website penalized or banned by a search engine. Carefully inspect the all details about the 'no cure, no pay" SEO guarantee. You should also check when the SEO guarantee expires! The truth is that they are guaranteeing you a #1 position but not necessarily for a keyword that is competitive. For example, it would be easy to get your site to the #1 position in Google for the term Colorless Pink Chocolate. Due to the volatile nature of search engines there really is no way to guarantee specific rankings in any one particular search engine for any one particular phrase.
85
INTERNET USERS HANDBOOK
Affordable Search Engine Optimization Service.com guarantees it will make the strongest effort to achieve top search engine placement for your chosen targeted keyword phrases on the top five search engines: Google, Yahoo, MSN, AOL and Ask.com. Our primary goal is to increase your sales, not just rankings and traffic. We know that our success as a marketing agency depends on your success. In order to keep you as a satisfied client we will do everything within our control and within search engine guidelines to make your online marketing efforts a success. Click this link for more information about SEOs AffordableSEO
6.35 SMISHING
This brings us to 2010s biggest threat: smishing. Online users usually know the term phishing, which refers to email-related scams. The term has been around since the original Nigerian charity donation warnings. email hosts have long since armed themselves with spam security, such as filters, email address blocking, and virus scans to attachments. Its becoming harder and harder to scam through emails alone. Thats where smishing comes in. It stands for SMS text messages. Thats right: viruses can also be downloaded onto cell phones. With many consumers now equipped with Blackberries and smart phones, its a whole new world. Hackers can set up an automated dialing system, which will obtain phone numbers from anywhere in a specific region or area code. The dialing system can also call these numbers with an automated message, another type of scam now labeled vishing, or voice message phishing.They often work the same way as regular email scams: the victim receives a call or text message claiming the victim must renew their bank card or make some sort of deposit. The messages then ask that personal information be keyed into the phone, claiming to be from a telephone banking service. Phone numbers can also be obtained from previous victims contact lists, so phone scams can grow exponentially. Worse, numbers can be obtained from the banks or credit unions themselves, once victims give the hackers access by handing over the required personal information. SamTitlston SEO
6.36 SPOOFING
E-mail spoofing is the forgery of an e-mail header so that the message appears to have originated from someone or somewhere other than the actual source. Distributors of spam often use spoofing in an attempt to get recipients to open, and possibly even respond to, their solicitations. Spoofing can be used legitimately. Classic examples of senders who might prefer to disguise the source of the e-mail include a sender reporting mistreatment by a spouse to a welfare agency or a "whistle-blower" who fears retaliation. However, spoofing anyone other than yourself is illegal in some jurisdictions. TechTarget
6.37 SOCIAL NETWORKING DANGER
Social networking is a great way to increase the visibility of your business on the Web, especially if your employees can pitch in by publicizing your organizations latest activities within their own personal networks. But beware: these same networks are also a security threat to your organizations IT systems and users.
86
INTERNET USERS HANDBOOK
THERE WAS ONCE A TIME when the only kind of virus one had to worry about was the kind that landed in our email inbox with a subject line like "I Love You" or "Britney". But email anti-virus software and firewalls have come a long way since then. That said; the threat of malware malicious software nonetheless remains a clear and present danger. While email viruses are a thing of yesteryear for most end users, the new vector of attack is the Web itself: worms and Trojans that download themselves to users' hard-drives before wreaking havoc on their computer networks. Research by www.webroot.com earlier this year found that 85% of all new malware originates from the Web, but that only 15% of organizations actually have any Web security measures in place. One may ask how this malware spreads without the use of email systems, and the answer is simple: social networking. These are the top three threats that your organization should be aware of.
HEADLINE HOOKING
Headline hooks are essentially short bits of juicy gossip that are propagated via social networks like Twitter and Facebook, They are used as bait to drive users to fake virus-scan web pages. The headlines might tout the resurrection of Michael Jackson or the death of the pope, but the result is the same: when users land on the fake virus-scan pages, they are told that they have been duped and infected with a Trojan. They are then asked to run Windows PC Defender to clear the infection.
THE BEAUTY; HOWEVER, IS THAT THE TROJAN WARNING IS A SHAM
The real culprit here is Windows PC Defender: a known rogue that pretends to be an antimalware tool. What it really does is infect your system and redirect all Google, Yahoo!, Bing and MSN search results through Search-Gala. This might not seem like such a big deal security-wise, but keep in mind that if users can be tricked into downloading this bit of malware, they can be tricked into downloading more serious stuff, too.
KOOBFACE AKA KOOBFOX
Koobface (an anagram of Facebook) is a worm that targets users of social networking websites like Facebook, MySpace and Friendster and attempts to gather sensitive information from victims such as credit card numbers. Koobface (Koobfox to those who use Firefox) spreads through messages from 'friends' to 'friends' with subject lines such as "Paris Hilton Tosses Dwarf On The Street", "LOL", "My friend caught [sic] you on hidden cam", and "My home video :)", followed by a link. Clicking on the link will take users to a third-party website where they are prompted to download a fake 'update' of the Adobe Flash player. Downloading the fake update and installing it will allow Koobface to take over your desktop's surfing activities and steal sensitive data from your hard-drive. It also installs a program that blocks access to well-known security websites and enables the attackers to abuse the infected computer.
SOCIAL NETWORKING SCAMS
Social networking has not only created new avenues for communication between people, it has also given scammers the world over a near infinite variety of ways to con people. With the advent of new social networking sites, there now exists even more opportunity to weave clever webs into which unwitting victims fall and become tangled. Mere hype in enough to ensnare most people, as with already-viral Google+ scams.
87
INTERNET USERS HANDBOOK
Everyone is excited about Googles own social networking site, Google+. The only way you can sample the new service is by invite only. Im sure you can see whats coming now. Thats right scammers have discovered a way to create fake Google+ invitations. They come through email, even Facebook. Heres what to do in both cases dont click on any links because they will take you somewhere you dont want to go. With email, make sure to check the identity of the person sending the email. If you dont know the recipient, dont open or click on any links. If it appears to be from a friend, email them and ask if they sent you an invitation to the new service. With Facebook, if you may receive a message that appears to be an invitation to Google+. You will be asked to allow third-party access to your account. The safest thing to do is to skip this altogether and deny access to your account since if you grant access, the third party can post on your wall and send messages to your friends. To learn how to disable problematic apps like this, watch this video from Sophos: Other scams to look out for through Facebook include the infamous Koobface worm and Facebook login pages with a URL that differs from www.facebook.com. AlertPay
FACEBOOKS DISLIKE BUTTON VIRUS
If you have a Facebook account then Im sure that you might have encountered with a spammy message entitled as Find out who viewed your profile or Use this new dislike button today. This is a message like other spam messages running on Facebook which installs Malware or Trojan to your computer without your knowledge. The message you will displayed as normal Facebook message on your profile, if you click on the message which re-directs you to Malware / Trojan coded page then the small script will be downloaded to your computer. This tiny Trojan application is called genie tool. Below is the screen-shot of the Trojan script.
Internet security, malware and anti-virus developing company Sophos today revealed that a new breed of Facebook Dislike Button trick takes you to a page where a hidden JavaScript code will be installed to your Browser or directly to your system32 folder. Once the JavaScript installed to your computer it sends all the activities of you on your computer to the author.
88
INTERNET USERS HANDBOOK
Sophos also mentioned that, so far the damage done by genie tool is unknown, but its my duty to inform to my reader about this malware. Ignore if you receive such message or delete it immediately. Dont forget to report message as Spam.
6.38 SKYPE SCAMS
The scams that happen through Skype are usually system update phone calls. You may be asked to click on a link to download new anti-virus software. One question to ask yourself is "Why is Skype telling me my computer has a virus?" How would Skype even know to detect this? They do not sell anti-virus software. It's almost like a clothing store clerk asking you if you want fries with that. Skype scams may also involve emails asking you to click on a link or provide personal information, like email addresses and passwords. Always check the URL to make sure the site to which you have been directed is legitimate. For example, Skype URLs and email addresses should show skype.com not something.skype.com. If you are ever worried about your Skype account becoming compromised, the good people at Skype recommend you reset your password immediately. AlertPay
6.39 TICKET FRAUD
A variation of Internet marketing fraud is offering tickets to sought-after events such as concerts, shows and sports events. The tickets turn out to be fake, or they are simply never delivered. The proliferation of online ticket agencies and the existence of experienced and dishonest ticket touts have fuelled this kind of fraud in recent years. Many such scams are run by British ticket touts, though they may base their operations in other countries. The company Euroteam is a well-established ticket scam. Norwegian based they force customers to confirm that they are buying tickets for a company in order to dilute consumer protection laws. They promise to deliver tickets often confirming their delivery up until minutes before an event is due to start. A prime example was the global Beijing Olympic Games ticket fraud run by US-registered Xclusive Leisure and Hospitality, sold through a professionally designed website, www.beijingticketing.com with the name "Beijing 2008 Ticketing". On 4 August it was reported that more than $50 million worth of fake tickets had been sold through the website. On 6 August it was reported that the person behind the scam, which was wholly based outside China, was a British ticket tout, Terance Shepherd.
6.40 TWITTER SCAM
Tuesday, January 25, 2011. All about the scareware campaign running rampant in Twitter Hi members, Some of you may have heard about the recent viral spam campaign running rampant through Twitter. If you haven't, here's the story....
89
INTERNET USERS HANDBOOK
Malicious hackers, also known as "black hats", compromised some accounts and launched a viral scareware campaign in which they used Google's URL shortening service, goo.gl, to hide the true location of the link. They tweet the link along with a text that says "Cool" or something equally nonthreatening. When someone clicks on the shortened link, they are whisked away to an unknown location (thanks to said shortened URL) and scared into downloading and paying for a "Security Shield" program; they are told that their computers have been compromised and the only way they can thwart the problem is to download and pay for the security software. The goal of this scam is to get tweeters to click on the link, download a file and pay for a bogus security program. The problem with this is that it's too easy to click on the link. Why? Because most of the link is hidden from view. Since Twitter only allows tweeters to post a specific number of characters, URL shortening services have popped up to allow people to post their status AND a link without going over the character limit.
HOW DOES SOMETHING LIKE THIS HAPPEN?
It may have all started due to the high incidence of people using the same passwords on different sites. If one of their sites has been compromised, then the hacker has access to all sites sharing the same password. You can understand how this can all go awry.
THE DANGERS OF URL SHORTENING
Some security experts have been saying that URL shortening can lead to an increase in cyber-crimes, giving hackers the ability to post a link without worrying about hiding the true URL; they don't have to since URL shortening services unwittingly help them with this.
SAFETY TIPS
Despite the absence of security tips in the articles we reviewed for this blog, we've come up with a handful to help you stay safe and secure when tweeting and using social media:
Use different passwords on different sites.
Using the same passwords on different sites will put you at risk for a security breach. We don't want to sound alarmist, but it's a fact. Use different passwords and try to make them as complex as possible.
Avoid clicking on shortened URLs.
Because you really have no idea where the link will take you.
Pay attention to the content posted
Posted with the tweeted link. Does it sound like something one of your followers would tweet? If it sounds out of character and if your friend does not usually post links, don't click on it.
WHY DO HACKERS DO THE THINGS THEY DO?
Hackers love to brag; this is just another notch in their belt. Also, greed seems to be yet another guiding force behind online scams. Hackers will go to great lengths to get information and money out of you. Educate yourself and try to stay ahead of the game. Thanks for reading and stay safe! AlertPay
90
INTERNET USERS HANDBOOK
6.41 TVI EXPRESS WORLDWIDE SCAM ALERT
Aug 16th 2010 at 1:10 AM Over 100,000 plus people worldwide have fallen prey to the Travel Ventures International (TVI Express) Worldwide SCAM. When TVI Express first came to the U.S. in the fall of 2009, I like thousands of other unsuspecting people, fell hook, line and sinker for what is now being called by true business experts....."The Mother of All Scams". After seeing many "red flags" and things that just made absolutely no logical sense, I decided to do some detailed investigative research on TVI Express! What I discovered is both shocking and downright disgusting! My goal and intention in creating this Facebook group is to educate as many people as I can worldwide on the truth relative to the TVI Scam so no one else will get hurt financially and emotionally by this Totally Fabricated Shell Company! My sincere hope and prayer is that the massive exposure of this TVI Scam Group here on Facebook will cause a chain reaction from honest, good-hearted people everywhere who will lead to the final undoing and total destruction of this real world "Ponzi" Scheme! It has been said, that the only thing needed for evil to flourish in the world is for good men and women to do nothing! Well, the creation of this group is my humble attempt to "do something". I hope you will join this group, share the information with others and do your part to see that justice is served and that this TVI Insanity will soon be stopped forever! TVI Express is incorporated off shore in Cyprus. Ownership of TVI remains completely hidden. TVI Express does not meet regulatory compliance in The United States, Australia, the UK and more. As a result individuals in those countries are being held accountable. Australia has become the first country to take action against TVI Express. The ACCC (Australian Competition & Consumer Commission) has issued an injunction restricting individuals from promoting TVI Express (alleged illegal pyramid scheme) in Australia pending formal hearing. During this process access to their own bank accounts has been restricted. http://tinyurl.com/23g2jfb Please join me in sharing the truth about TVI with anyone you know who has gotten caught up in this mess by inviting them to join this group! Be sure to visit my YouTube Channel entitled TVI Scam @http://tinyurl.com/2wxfh8g Major Steve Motley
6.42 WORK-AT-HOME SCHEMES/BUSINESS OPPORTUNITIES
Fraudulent schemes often use the Internet to advertise purported business opportunities that will allow individuals to earn thousands of dollars a month in "work-at-home" ventures. These schemes typically require the individuals to pay anywhere from $35 to several hundred dollars or more, but fail to deliver
91
INTERNET USERS HANDBOOK
the materials or information that would be needed to make the work-at-home opportunity a potentially viable business. Often, after paying a registration fee, the applicant will be sent advice on how to place ads similar to the one that recruited him in order to recruit others, which is effectively a pyramid scheme. Other types of work at home scams include home assembly kits. The applicant pays a fee for the kit, but after assembling and returning the item, it is rejected as substandard, meaning the applicant is out of pocket for the materials. Similar scams include home-working directories, medical billing, data entry (data entry scam) at home or reading books for money. The latest work at home scam is very elaborate, which includes an entire website dedicated to feigning the existence of a fake organization. Example: Timothy Scott (not his real name) emails to offer a job with the so-called Travis Gilbert Foundation. To lure gullible participants, they offer unrealistically generous salaries for part-time unskilled labor. (If they were real opportunities then naturally such positions would fill quickly without the need to email the offer to thousands of strangers.) The main responsibility of this well-paying job is to be a middleman for "donations" which are intended for victims of natural disaster. In this capacity, it gives the scammer an excuse to ask for bank account numbers (allegedly to deposit "donations" into the victim's account for redistribution) as well as the victim's SSN and DOB (allegedly to fulfill the typical paperwork obligations of a new employer). Once these vital numbers have been disclosed, the criminal uses that information to monitor account balances. On the day that a larger than normal amount appears in the bank account, such as a weekly pay check, for example, then the account is drained. Generally the scammer will feign to be located in a country other than where he is located. Example: Travis Gilbert Foundation's website lists an address in The Netherlands, but the registration of the domain name is in Beijing. In addition, victims in Western countries are targeted by using a non-threatening pseudonym like Timothy Scott, which does not sound so foreign, while the domain name tgilberthome.org is actually registered to Li Xiang.
92
INTERNET USERS HANDBOOK
7. THE $1,000,000 PER DAY PTC/PTR SCAM
This section culminates my 9 months of research, testing and being scammed in the PTC/PTR arena of Internet Scams. Years ago, I looked at various paid to read email programs, but I figured my time was worth much more than $ .05 for reading 10 emails or a $ .01 per email, or anything like that. Such low paying sites are still available today, and do actually pay. However, to make any money with these sites, you need a downline contributing to your income. It is hard for me to get excited about someone that posts a check for $ 5.00 (as proof of payment) and he or she is happy. How much work did they have to put into to get that $ 5.00; did it pay for his Internet connection, his electricity, computer, etc. This section is another look at todays big money PTC/PTR sites, and the scams they represent... I cannot emphasis the importance of this chapter, as I find too many new users (newbies), are being taken by the promise of big earnings $1 -20,000 per email that will never be taken to the bank SUB-TABLE OF CONTENTS:
7.1 RETIRED AND BORED
I get so very busy in my many endeavors; that I often look for a no-brainer to pass some break time. Chatting is great among the various social networks available, but can lead to problems for you, unless you keep it strictly business, not monkey business. I can say that, as I met my wife online (smiles). After years of various successful businesses, consulting and coaching, etc., I finally decided to retire. I got tired of the local politics and current business gamesmanship. Moreover, I am a foreigner in someone elses land; I do not need to take consultation fees when locals claim to be able to do the same job and work cheaper. . I had been using the Internet for research, financial data/quotes, email, etc. for years in my various businesses. Therefore, I decided to try the net for some productive, paying programs. I believe I already told you that I did not play golf. Having been used to working 12-16 hours days, I needed something to keep me my brain active. After some time of learning and losing at various other interest business opportunities as discussed before, I took another look at the PTC/PTR community. As I said, the low paying sites are still available, but it seems the real way to make any money here is to build a downline, like most online programs. In as much as I had not built a downline for any other program that paid more than these sites. I passed, but then I began finding new PTC/PTR programs that paid, unbelievable, think of it: $20,000 per email? Wow, how can this be true? It is not possible - I told the wife, maybe this is a new money laundering Scheme. It did not make any sense to us, nor should it to you. However, do read on! Real or not, I decided to check out these new sites, joining one lead to joining another, etc. Before I knew it I had several sites promising ridiculous amounts of money per day.
93
INTERNET USERS HANDBOOK
7.2 MY BIGGEST PTC/PTR ACCOUNT PCASH
Site is now shut down, but below are few of the details in the scam which will be used to introduce to and help explain some of the similarities and differences between most of the PTR/PTC sites
HOME PAGE SITE STATISTICS
Members: 7,608 Payouts: 62,093,832,222.00 Mails in queue 2296 Ads in rotation 30 Memberships (free and upgraded) Get Paid By Clicking! All emails Worth $20000 All PTC worth $10000 $20000 signup bonus $2000 referral bonus Redemption starts only $500000 We send redemption with 48 hours No downline required for payout Payments Will be Made via Liberty Reserve, Moneybookers, E-Gold! Fast Payments for Honest Members 2 Ref levels of commission under you; Level 1 - 20%, Level 2 - 10% PCash is not a multi-level marketing site! This is a Pay per Action Site and the membership is completely free to join. You are not required to recruit or sell anything in order to get paid. Advertiser Benefits the most cost effective advertising. Guaranteed Clickthru Ad Options.email
ADVERTISING OR BANNER ADVERTISING.
Advertise to 100% opt in membership. Members are eager to receive your ads. Absolutely no Spam! We will customize your Ad Campaign. Reliable, Friendly Service. Fast respond! Mostly in 24 hours will be processed. Advertising Will Be Made within 24 hours. Choose Your Page
EXPERIENCE
Membership has nearly tripled since I joined this site. Note the claimed payouts of over 62 Trillion, and all this with only 2300 emails and 30 banner ads. Payouts of 62,093,832,222.00 divided by 7,608 members give an average payout to each member of $816,000. Not bad it if were true. But it is not, the payout number increases with each request for payment, but no money changes hands, only the tot board changes. Of course, this is not real, but seeing the numbers get so high, it became a game, a diversion, and sort-of addictive (how high can I go). As you will see, this site and others became a part of my Welcome to My USD 1M or More per Day Strategy. On paper, I was making money with this site, lots of it at a time when I was getting nothing from my other sites or advertising efforts. I accumulated a downline of 58 members. Clearly, this was a winner, by all measures, except that No Payments were received.
94
INTERNET USERS HANDBOOK
Even with my mentality that if you owe me a million, then 1% or $10,000 would be great, since although I would have like to have received something, but didnt really need the money. However, I have learned that scammers dont give up a dime. There is none of this take a little bit now and I will send the balance later stuff. You have no contact with your downline, only the name and a $2,000 bonus tally. For that matter, the downline could be random generation of name to fill a list to keep you in the game. Since most of these scammers, as I have learned, own several sites, the same downline name probably shows more than one site. The home page says payment will be made via different payment gateways. However, PayPal is now missing from the home page. A new name Liberty Reserve is shown. Liberty Reserve came on strong and became the primary gateway for several other sites and No PayPal.
UPGRADE EXAMPLE
When you upgrade your free membership to a Gold Membership, you will receive the following benefits: Free Referrals (3 x) - Your referral URL will be randomly inserted for surfers visiting the web site without a referral URL. 10,000 PTC Worth $10,000 monthly (?? If each PTC is worth $10,000, Why only $10,000 per month?) 10,000 banner impressions monthly $20,000 solo paid email to all monthly
ADVERTISING
Are you interested in advertising with our company? Below are the different types of advertising services we provide. We offer many options and are confident; you will find one to fit your needs. How it works: Click one of our advertisings from below. If these advertise allow targeting - select your target groups. When you are done you will have the price that you need to pay, calculated. After you have paid for your ad package, please fill out the "Order Form" on the last step to complete the advertisement ordering process. Complete all the information requested on the form then click submit. Once your payment has been confirmed, we will process your order immediately.
ADVERTISEMENTS
A Paid-email to Members of our Program All of the people who are receiving the email have all requested it, thus giving you, the advertiser, and a great selection of interested viewers. 20000 USD solo paid email to all 60 sec (pcash) - $2.00 30 x $20000 solo paid email to all 60 sec (pcash) - $55.00 10 x $20000 solo paid email to all 60 sec (pcash) - $20.00 PAID TO CLICK Banner 468 x 60 Exposures have a unique price per click and will last until the purchased number of clicks has been reached.
95
INTERNET USERS HANDBOOK
These are UNIQUE VISITORS as each user may click only ONCE per ad these ads are visible in the members paid2click area. 1,000 PTC Worth $10000 40 sec (pcash) - $0.50 10,000 PTC Worth $10000 40 sec (pcash) - $2.00 100,000 PTC Worth $10000 40 sec (pcash) - $5.00
BANNER IMPRESSIONS ADVERTISING
Your banner inserted into our banner rotation on the top of each page of the website. This is a great way to catch peoples interest, just as much publicity, if not more than, advertising in the member emails. The banners will be displayed on every page of the site, randomly mixed in with other banners... 50,000 Banner Impressions (pcash) - $2.00 100,000 banner impressions (pcash) - $4.00 500,000 banner impressions (pcash) - $18.00 One month unlimited banner impressions (pcash) - $35.00* This ad allows targeting. Price determined after choosing targets.
COST OF ADVERTISING
From the above cost, where is the money? You can buy $ 20, 000 USD solo paid emails to all members, running 60 sec (pcash) - $2.00. If my math is correct $2.00 / 20,000 = .0001 cent. So how can anyone stay in business if each member receives $ 20,000 to read a $.0001 ad?? The fascination continued During my time with this project, I noted that most of the ads and emails were self-promoting or cross promoting between similar sites, probably from the same owner. So where is the revenue?
LIMITATION OF LIABILITY:
pcash.info will not be liable for lost profits, lost business opportunities, or any other indirect, special, punitive, incidental or consequential damages arising out of or related to this Agreement or pcash.info program, even if pcash.info has been advised of the possibility of such damages. Furthermore, pcash.info aggregate liability arising under this Agreement will not exceed the amount of the total fees paid or payable to you under this Agreement. The provisions of this Section survive termination or expiration of the Agreement.
PAYMENTS
Affiliates may earn by receiving paid-emails and visiting the advertiser websites after they have entered their member ID in the area on the website provided by pcash.info. Affiliates may earn by referring new affiliates to the pcash.info program. Affiliates will earn a percentage of advertising revenues collected by pcash.info. Affiliates will be paid via PayPal / eGold. pcash.info will pay affiliates when their balance reaches the minimum payout rate set by pcash.info. Once the member has reached payout they may request payment. Payments will be made within 30 days or a reasonable time after.
96
INTERNET USERS HANDBOOK
PAYMENTS/CASH REDEMPTION
Cash redemption for PCash starts at $ 500,000 and is easy to reach (as most sites will claim). The amount of minimum earnings required before you can make a claim will decrease with an upgrade. PCash claims they will send the redemption within 48 hours. For most sites, this payout period can be shortened with the level of an upgrade. So if you want your money faster, you are motivated to upgrade. Also an upgrade will provide you with some x number of free members to help build your downline. TIP. Clearly PCash and other sites are offering a Cash Payment Redemption link which will pay you with x dollars within x hours or days, but forget what the Home Page says. Read the fine print from the Terms which reveals something different.
TERMS
pcash may, at any time, choose to edit, add and/or delete portions of this agreement and impose changes without prior notification of its affiliates Payments will be made within 30 days or a reasonable time after. Tip. Dont confuse the Earnings with Cash Payments. Pcash.info, unlike some other sites, does tell you that you will earn a percentage of revenue, not full cash value. But, as you will see when you do your Due Diligence; nobody will get anything if their daily revenue is only $4.00. Most of these sites seem to confuse the word redemption with a cash payout. Using some of your cash value to place an ad will usually be redeemed within 24-48 hours. Once an upgrade and a payment request has been made, lets say for a 48 hour redemption, many sites then report that your payment will be made within the redemption period once your account is 30, 60 or 90 days old; and not the immediate 48 hours that you thought that you had upgraded for. If you read the Home page, Terms, Upgrade and the Frequently Asked Questions (FAQS), you will typically find many inconsistencies between them. For example, the front page does not mention PayPal anymore, but when you complete the user profile; the only payment methods are PayPal and EGold. Most of these PTR/PTC sites use only PayPal and E-Gold, but it appears that many are now switching to Liberty Reserve. If you contact them online, you will not get a reply, and if you contact them by email, you will not get a reply.
HONEST MEMBERS
I particularly love the Fast Payments for Honest Members What a lie! With the amount of money I earned on the site, I should have been getting $500,000 every 2days. See my earnings of over $ 180,500,000, Amazing isnt it.
MY EARNINGS
You have directly earned: $ 92,600,000.0000 You have earned from your Downline: $ 84,786,000.0000
97
INTERNET USERS HANDBOOK
Your account balance after all transactions: $ 3,022,000.0000 When the minimum amount for a payout has been earned; in this case $500,000, you can click the Request Payment link, complete the request and you are greeted by the following message Your message has been sent. We will contact you soon. No messages regarding the payment request were ever received, and its seems that as soon as you request a payment, the Payouts Increase, even though no money has actually changed hands. So is any of this realistic Of course not, but watching your earnings increase and increase by $20,000 can be addictive, especially, if you have not seen earnings on other programs. With this information, it is easy to see, that pcash.info claims to have paid out 62 trillion when it has an estimated value of less than $3,000. Ad revenue is estimated at less than My *USD 1m or More per Day Strategy $4.00 per day. How to pay you $20,000 per ad?
FACTS: THIS IS A NO-BRAINER SCAM, PASS
This is just one example of over 200 sites evaluated. As the numbers grew, it became a challenge: Can I Make (earn) a Million Dollars a Day Doing This? I made it a supplemental business endeavor (a non-paying business as you will learn) from 27 October 2008 till 22 Jul 2009.
7.3 MY USD 1M OR MORE PER DAY STRATEGY
I made PTC/PTR a business to see how far I could go with it without getting paid. I kept track of the date that I joined how, many days since joining, average earnings per day, signup bonuses, PTR earnings, PTC earnings, cost of upgrading, payment to who PayPal, Liberty Reserve, etc. I also tracked the date I upgraded, when payouts were due and other factors which I tracked off table. So it was a business and treated as such. I was able to achieve the $ 1,000, 000 earning per day target in about 6 months. It could have been faster; but all programs (over 200 in the test) must be accessed (whether high dollar or lesser dollars) at least once a month, or a week as I did. Like reading email sites, some have a high volume some much lower.
7.4 PUT ON OUR BUSINESS HAT
It should be obvious that businesses cannot payout more than they take in advertising revenue and still be considered a going concern or a business Advertising businesses cannot afford to give away computers, cameras and other such items, signup bonuses and such if the advertising revenue is not there. Take your own perspective, how much are you willing pay others to read your advertisements? Good rule of thumb, sites that might actually pay will pay less than $.50 per click or read.
98
INTERNET USERS HANDBOOK
8. PREPARING TO DO BUSINESS ONLINE?
Perhaps the greatest contributor to our failure on or offline is our lack of personal preparation to do business. Offline business usually start with you, your passion, interest or perhaps a hobby. It is easy to recognize what your need to get started: Money or capital, home or rental/lease location, business cards, signage, etc. Online; it looks so cheap and easy, but soon you find it is not! Entrepreneurs are not always business minded; most have little or no business experience. Both off and online businesses suffer the same problem with their owners. I believe it is reasonable to say that starting an online scam site is easier than a legitimate site. All you have to sell to get paid is satisfaction to someones need, whether you can deliver or not. All legitimate business off or online, can run into problem with cash flow, management and other business ailments, so just because they fail does not mean that they were a scam. With that said, this chapter concerns your personal capability to run a business and works fine both off and online businesses. You are given the opportunity to you to assess your strengths and weaknesses, assess your business potential and facilitate a personal plan of action. Your business will not grow and you will lose most of the potential growth or your business until you realize how important personal preparation is to you. Be fair and honest with your assessments! Take notes and develop your personal Plan of Action for starting or growing a Success Business Online
8.1 PLANNING TO DO BUSINESS ONLINE?
Too many new users (newbies) think that doing business online is easy, and will solve their financial problem. According to the hype It Is! Just look, the start-up costs for doing offline as compared to starting online. However, if you think you can jump into any business without being personally prepared, without a plan and a without a proper mindset to treat your online experience as a BUSINESS, instead of a HOBBY; then you are destined to join and be one of the 95% +/- failure rate statistics that may be found for both offline as well as online businesses. The statistics for Forex failures is even higher at 98%. However, according to a Dr Jeff Cornwall of Belmont University Ask an average group of people what the survival rate is for entrepreneurial ventures and the figures you usually get are 10-20%. The truth is much rosier than common wisdom assumes. As reported by the National Dialogue on Entrepreneurship, a new study from the Bureau of Labor Statistics "examines the survival rates of new businesses started between 1998 and 2002. It finds that 66% of new establishments started in 1998 were still operating two years after they started; forty-four percent were still operating in 2002." The only sector that showed significantly lower rates was the dot.com group, which crashed during this time. Factoring that group out and we are getting closer to the 50% figure that most experts believe to
99
INTERNET USERS HANDBOOK
be an accurate estimate. Studies that examine entrepreneurs who have had training and/or education in entrepreneurial skills consistently show a much higher success rate (as high as 80-90%). While we are here to learn to avoid scams; we are also here to help you succeed. Take your time and see what skills you can improve. Those of you that have joined us, and are already successful online, great, we can use your help. Others, use this section to help determine your needs and to develop your plan of action. With proper planning, learning, mindset and treating your business as a business, you can significantly increase your potential for success. In following sections, we will help you to identify, understand and avoid the Scams. Avoiding Scams will further increase your opportunity for success, but using your resources where they can help you instead of filling the scammers pockets. Business failures are difficult to track because the facts vary with the source and the way the numbers are gathered. For example, we can measure the number of Offline Businesses that start within a year or two and deduct those that do not renew their business license. However, no license is required for an Online Business. While we can document the change in the number of bankruptcies, but just because a business did not renew their license does not mean the business went bankrupt. All we know is that the business may have closed for some reason; wrong business, wrong or obsolete product, timing, lost motivation, divorce and for that matter any reason will do. Online hobbies can be ceased at any time no paper trail.
IF YOU ARE CONSIDERING A NEW BUSINESS?
Have You Evaluated, Researched and Really Understand Your Idea Or Opportunity? Have You Evaluated Your Personal Needs? Does Your Idea or Product, Service Fulfill A Need? Do You Have Start-Up Capital And Reserves? Can You Face and Make Decisions? Are You Ready To Stick With It? Do You Have Adequate Skills, Resources, and Credit? Do You Know Where Get Assistance, Information?
8.2 GENERAL ASSUMPTIONS
Keep it simple and let us just accept the general numbers of 90% +/- failure rate and accept that that is after 5 years. Of these, the failure rate for online business is 50% within the first 6 months to a year, while offline the percentage is say 50% after 2 years. Most of us understand that offline businesses require a greater investment to set up the business, licenses, location, furniture and equipment, etc. Offline businesses are lucky if they breakeven in months to a year, while most take longer, if at all. These entrepreneurs must concern themselves about matters of government regulations, policies and politics, brick and motor location, capitalization, payrolls, risks, etc. Most of the offline business failures are a result of undercapitalization and miss-management., no plan.
100
INTERNET USERS HANDBOOK
Your capital investment for an online business is much less; but that does not mean or guarantee that you can or will be an overnight success, as others would have you believe. Unlike offline business, you are not so concerned about matters of government regulations, policies and politics, brick and motor location, capitalization, payrolls, etc. As said before, those that have some basic business skills or background, training and an entrepreneur sprit have a much greater chance of success and are better suited for business. Add to that, those that have a plan; i.e., business, financial, and marketing plans have a significantly better chance of success. Offline entrepreneurs may have a passion, interest or idea, a product or service that they feel can be marketed online. Those that start online may also have an idea, product or service, but the majorities are just looking for extra money. They most likely become an affiliate of someone elses product or service. A fulltime commitment is better that a part-time effort for any business. Regardless of the type business, you undertake, you should understand your suitability to go into that business, assess your strengths and weaknesses, what are you needs, and what is your understanding of the risks. The Scammers will tell you, you do not need money, or not that much, and that they will do everything or most of the work for you. Just sit back and collect your money. If you believe that, then you may as well stop reading further. In business, we must understand ourselves, what is involved. Some of you want to be your own boss, or you have already started your business, some of you are retired, or work at home moms, whether online or offline. Maybe some you want a change of career or just want to supplement your income. Look at the following and be honest with yourself. Many items are applicable to the offline business, but some for both. Consider them, i.e. what can you do, what do you know, what are your interests, can you do it online?
8.3 WHAT IS AN ENTREPRENEUR?
This applies to someone who establishes a new entity to offer a new or existing product or service into a new or existing market, whether for a profit or not-for-profit venture. Business entrepreneurs often have strong beliefs about a market opportunity and are willing to accept a high level of personal, professional or financial risk to pursue that opportunity. A Risk Bearer, an Organizer, an Innovator, a Leader
IN-BORN TRAITS OF AN ENTREPRENEUR
Entrepreneurs have a Desire to Achieve: The push to conquer problems, and give birth to a successful venture. Hard Work: Are mostly workaholics. A Nurturing Quality: Willing to take charge of, and watch over a venture until it can stand-alone. Acceptance of Responsibility: Are morally, legally, and mentally accountable for their ventures.
101
INTERNET USERS HANDBOOK
Reward Orientation: Desire to achieve, work hard and take responsibility, but also want to be rewarded handsomely for their efforts; rewards can be in forms other than money, such as recognition and respect. Optimism: Live by the philosophy that this is the best of times, and that anything is possible. Orientation to Excellence: Often desire to achieve something outstanding of which they can be proud Organization: Are good at bringing together the components (including people) of a venture. Profit Orientation: Want to make a profit; but the profit serves primarily as a meter to gauge their success and achievement. John G Burch Business Horizons, 1986
A SUCCESSFUL ENTREPRENEUR IS ONE THAT
Is motivated and who is able to motivate those around him / her Is able to manage time effectively Has the ability to leverage off strengths and overcome weaknesses Manages resources well Considers health as well as wealth Is flexible and able to adapt well to change Is willing to learn from others, Reads, Reads and Reads
CHALLENGES OF AN ENTREPRENEUR
Uncertainty of Income Cash Flow Management Risk of Losing Your Entire Investment Long Hours and Hard Work Lower Quality Of Life Until the Business Gets Established High Levels of Stress, In-laws (Now or Future) Complete Responsibility Are You Easily Discouraged? Do you feel personally stressed and feel threatened under pressure Constantly stake personal reputation and tend to give guarantees. Be hard yet more flexible and more streetwise than a corporate executive. Be good at multitasking able to do everything. Intermittent, unpredictable income Self-Discipline, Patience, Listening, reading Personal technological competence, Internet The buck stops with you! Think of new ideas and deliver them to the market and make a profit. Provide leadership to his team against established competition with minimal resources. Raise finance without a track record, collateral or internal experts. Pay staff first; you get paid when it is prudent to do so. Be prepared to lose everything if things go wrong
ENTREPRENEURSHIP OPPORTUNITIES
Create your own destiny Do what you enjoy
102
INTERNET USERS HANDBOOK
Fulfill your vision, Doing and to have ambition and fun at it Passion Contribute to society To be recognized for your efforts Make a difference Reap unlimited profits Reach your full potential
ARE YOU ENTREPRENEURIAL?
Independence Seeking Wealth Seeking Opportunity Seeking Innovative Venture Seeking Risk Accepting Intuitive ARE YOU NON-ENTREPRENEURIAL? Laborers, Bureaucrats, Lenders, Professionals Managers - Access Yourself Assess Your Own Capabilities, Resources And Characteristics. This Helps You Concentrate on Your Strengths As well As Identify the Additional Tools, Resources and Skills You'll Need - From Financing to Market Planning to Bookkeeping. What Do You Want? Do You Have The Right Skills, Temperament and Work Style? Have You Thought About what is involved? Are You Comfortable With Having All The Decisions Rest With You - From Employees, To Suppliers, Production, Sales, And Management?
8.4 INVESTIGATE WHY ARE YOU HERE?
IF YOU HAD A CHOICE, WHAT WOULD YOU RATHER BE DOING?
What concerns do you have? What is attractive to you? What is your idea or marketplace opportunity? What characteristics of an entrepreneur are important to you? What skills and experiences do you have that will help you become successful? What entrepreneurial skills and experiences do you lack at this point in time? How many months can you live without income?
WHAT IS/ARE YOUR MOTIVATIONS?
I want to be my own boss I have identified a new business idea or opportunity I feel I can achieve more in my life through entrepreneurship I believe my job opportunities are limited due to my age, skills and experience
103
INTERNET USERS HANDBOOK
I want a career that will align better with my personal values
8.5 HOW MUCH DO YOU KNOW ABOUT LEADERSHIP?
Planning Problem Solving Vision Innovation Leadership Emotional Intelligence Delegation Communication Self-Development Relationship Building Commercial Financial skills Personal Energy Ethics Transparency
8.6 DO YOU HAVE A PASSION FOR BUSINESS?
How do you know if you have this passion? Ask yourself. If you won the first prize in a competition, would you still want to be online and go into this business? When you love your work, it becomes contagious, as everyone around you is infected.
8.7 BELIEVE IN YOURSELF AND BOOST YOUR SELF-CONFIDENCE
Have trust or faith in a person or thing. Possess a feeling of assurance, especially of self-assurance. The state or quality of being certain: I have every confidence in my idea and my ability to succeed. Do you have a feeling of emotional security resulting from faith in one-self? Confidence is a firm belief in one's powers, abilities, or capacities You gain strength, courage and confidence by every experience in which you really stop to look fear in the face (Eleanor Roosevelt). Self-confidence, trust in one's own self-sufficiency Just think: What difference would it make in your life if you had an absolutely unshakable confidence in your ability to achieve anything you really put your mind to? What would you want and wish and hope for? What would you dare to dream if you believed in yourself with such deep conviction that you had no fears of failure whatsoever? Most people start off with little or low self-confidence, but as a result of their own efforts, they become bold and brave and outgoing. And weve discovered that if you do the same things that other selfconfident men and women do, you, too, will experience the same feelings and get the same results.
104
INTERNET USERS HANDBOOK
The key is to be true to yourself, to be true to the very best that is in you, and to live your life consistent with your highest values and aspirations. Brian Tracy
8.8 COMMITMENT
A pledge to do, an obligation Something pledged, especially an engagement by contract involving financial obligation The state of being bound emotionally or intellectually to a course of action or to another person or persons What one has, one ought to use: and whatever he does he should do with all his might Marcus T. Cicero A person with half volition goes backwards and forwards, but makes no progress on even the smoothest of roads - Thomas Carlyle
8.9 HOW ABOUT ATTITUDE?
Your attitude is a frame of mind with which you approach a subject, a problem, a person or any circumstance. Either it is positive, negative or indifferent. The most important aspect of attitude is that you and you alone are in full control of it , the choice is totally yours, your choose Hence, if you choose to look at things in the positive light, then you will find that many doors will be opened to you because positive outlook presents you with a can-do attitude.
8.10 DO YOU HAVE A FEAR OF FAILURE?
If you are paralyzed by the fear of failure, you will remain inactive. No one wants to fail but when it happens, there is nothing to fear. Courage is not the absence of fear; it is moving forward through fear. Walt Disney formed his first animation company in Kansas City in 1921. Flushed with success, he began to experiment with new storytelling techniques, his costs went up and then the distributor went bankrupt. He was forced to dissolve his company, at one point could not pay his rent, and was surviving by eating dog food. PopCrunch Henry Ford. Unfortunately, he focused too much on the engineering and not enough on marketing, resulting in poor sales and bankruptcy. He was forced to leave the business in 1902 after investors threatened to withdraw their capital. FreeInfoSociety It is the Kiasu syndrome, a self-defeating emotion that creates fear that gets in your way FEAR of losing, One who is afraid to lose out to someone else, often to the point of selfishness; an over-cautious person; afraid of losing out to someone else, and therefore often behaving selfishly and disregarding others; dog in a manger
OVERCOMING YOUR FEARS
Use fear as a propellant. The Dalai Lama: unless you have a strong feeling of self-confidence based on a strong self, it is difficult to do battle with negative emotions. It is the role of intelligence with the full awareness that is provided by education, to judge and accordingly utilize the potential for ones benefit or well-being. ..We have nothing to fear, but fear itself. U.S. President Franklin Delano Roosevelt
105
INTERNET USERS HANDBOOK
Your effective decisions are limited by your knowledge and understanding of business
USE YOUR FEAR AS A MOTIVATOR
On the positive side, fear can be a Motivating Factor. In this business, by the time you realize you are in trouble, it is far too late to save yourself, unless you are running scared all the time. Bill Gates "Courage is doing what you're afraid to do. There can be no courage unless you're scared." Eddie Rickenbacker If the fear is rational, it serves as a warning alarm about real risks you may be taking. If you pay attention to it, apply some reason to it, and think it through objectively, you can keep yourself from taking foolish risks. You can minimize the risks that are unavoidable. (Inc)
8.11 ARE YOU A PROCRASTINATOR?
Procrastination is to put off doing something, especially out of habitual carelessness or laziness, or to postpone or delay needlessly. Some people just never get started. If you want to change your life, then you must take action. No Guts - No Glory Damn the torpedoes, full-speed ahead - Admiral David Glasgow Farragut, First Admiral of the United States Navy The Early Bird Gets the Worm - Meaning: Success comes to those who prepare well and put in effort. John Ray's a collection of English proverbs 1670, 1678 Nothing Succeeds like Success - Meaning: the idea that success breeds further success. Sir Arthur Helps, in Realmah, 1868 TIP: You got the idea! The Scammers love to use these same phrases: Take action now, Do it today, Last chance! Only 5 copies are left You are right; even some legitimate marketers may use some of these techniques
8.12 ARE YOU READY TO ACCEPT THE RISK?
Are you well suited to running a company, what is your business experience? How much are you willing to stake, and what are the potential risks you will face? Will I be dedicated to this venture? How much of my time and myself can I commit? Can I manage the stress on myself and my family and friends at the start-up stage? How can I manage my time effectively? Long hours will test your character in many ways. Can you handle that? Does your venture motivate you enough to make you go for it? What is your MINDSET?
8.13 HOW MUCH DO YOU KNOW ABOUT THE FOLLOWING TOPICS?
Marketing - Types And Various Methods of Online Marketing, email, Traffic Sites, Lead Providers Pricing - Selling EBooks, Or Reselling Books and Products? Regulations (Laws)
106
INTERNET USERS HANDBOOK
Spam Licensing Record Keeping - Track Your Sites, Ids and Passwords Financing Capital/ Other Expenditures - Desk, Computer, High Speed Internet Provider, Printer, Supplies Technology - Keep Your Computer Running Cash Flow Management - Some Sites Charge A Monthly Fee Competition - Big Boy Affiliate Marketing Taxes Employees Benefits/Perks Suppliers - Affiliate Products, Shipping, Payment, Legitimate Health Community - Online Communities and Groups Social/Ethical Issues - Spam, Social Networking Scams TIP: If you have taken the time to go through the preceding and have been fair and honest with yourself; then take the time to make a Plan of Action for Your Personal Development. Take little steps, but DO take the first one.
8.14 STEPS TO A GREAT BUSINESS PLAN
We have discussed your personal Plan of Action for your Personal Development; now we need a Plan of Action for your Business. You can make a business out of your hobby; but you cannot treat your business like a hobby. Failure to plan is said to mean that you plan to fail. Your banker, JV Partner, or sometimes a supplier usually requests business plans Even if you are not looking for a banker, Joint Venture partner, etc., it is wise to have some idea of a plan, what your product or service is, how you are going to market it, what milestones are your using, what is your budget, financial projections, etc. It should include your personal strengths and weaknesses, and your plan of action to improve your potential for success. Write out your basic business concept. Gather all the data you can on the feasibility and the specifics of your business concept. Focus and refine your concept based on the data you have compiled. Outline the specifics of your business, using a "what, where, why, how" approach. Put your plan into a compelling form so that it will not only give you insights and focus Plan should become a valuable tool in dealing with business relationships that will be very important to you. Keep it simple English, use graphics and tables
A SIMPLE BUSINESS PLAN
1.0 Executive Summary Use in a formal report
107
INTERNET USERS HANDBOOK
2.0 Introduction To YOU (The Company)
Strengths and Weaknesses, Plan
3.0 Employment Workers
None at this time
4.0 Product Or Service Development 5.0 Marketing Programs
New or affiliate
How are you going to market, where, how many times, what is budget, measure results, Marketing Plan
6.0 Financial Projections
Financial Plan
7.0 Conclusion or Appendices
Use in a formal report
HOW TO SET UP YOUR BUSINESS PLAN
By setting up YOUR business plan, you are road mapping your way to success. It will help you to develop your business goals and strategies, as well as providing you with a better understanding of the marketplace. It will also highlight any business strengths or weaknesses that you may have, as well as providing you with an opportunity to take a close look at your competitors. If you want, you can also include financial projections, historical data and growth expectations into your plan. With any good business plan, it should show who the target audience is, and just how the product or service that is to be provided will meet or exceed their needs and expectations.
ORGANIZING: BREAK IT DOWN INTO SECTIONS SUCH AS:
Business Summary The product or service you want to provide. Market Analysis Research the product or service. Find out what the competitors are doing Product Positioning How to make it more prominent compared to your competitors. Market Strategy How are you actually going to market it? Customer Analysis Look at what the customer wants or needs. Financial Analysis What you need to invest in order to set up the business and to keep it going while it is just getting started Overall Business Goals What you hope to achieve in, say, a years time. HomeBusiness
108
INTERNET USERS HANDBOOK
The forgoing is another example of various online resources to help you, free. However, if you do not take the time to make and use a plan, at least prepare a schedule of things to do, and allocate the time for each task. Big jobs can be broken into daily tasks.
109
INTERNET USERS HANDBOOK
9. FOLLOW YOUR PASSION ONLINE BUSINESSES
Thus far; you have had the opportunity to assess your skills, develop your plan of action or a personal develop action plan for doing business online. I hope you took advantage of that opportunity. Every business person, off or online, needs personal growth to help grow their business as well. Otherwise you will spend too much of your budget (hopefully profits) outsourcing these tasks to others. Take your plan seriously, implement and follow-up often to check your progress. We have introduced you to Our Internet Scams Anonymous Groups and how our members can supplement this Handbook to help you do business online while recognizing and avoiding the scams We have warned you and given examples of the various Scams that you are likely to encounter online, Spam and how to deal with it as well as Managing your email In this chapter, we start looking at various types of online business. It is widely accepted that the more successful online marketers follow an interest or passion start their own business and have their own web site. Unfortunately, most new users are already looking for money by the time they turn to the Internet. Often is desperation they respond to the first email or site that triggers their need to make money. Admit it or not, they often are taken by the scammers who are Masters in taking your money in return for false promises. They just join this and that program as an affiliate, and never realize the real potential that the Internet has to fulfill their passion.
9.1 COMMON QUESTIONS WHERE DO I START? WHAT IS BEST?
You have been given the opportunity to learn more about yourself, now let us try and find a suitable business for you. Doing business online is not much different than doing business offline, except for the obvious differences; location, brick and mortar, leases, licenses, signage, business cards and letter head, etc. It is not a simple, single step, sign up. We do all the work for you and sit back and collect your money process What do you already know about business and it its various functions, products and pricing, sales and marketing, distribution, after sales support, etc. You need a plan(s); plan for your business, plan for your marketing, a financial plan and a personal action plan. What do you and your business need and where are you going to get it. Most offline business starts from an interest, a hobby or a passion. (Sure you get buy a franchise and they train you, but this is going to be your business)
110
INTERNET USERS HANDBOOK
Online should not be much different: What is your passion? Then Google find product or services that help fulfill your passion. Pick perhaps 3 or 4 and do your own due diligence, Join 1 or 2 and take responsible for your decision
9.2 WHAT ARE YOUR INTERESTS?
OFFLINE
In starting an offline business, it is simple; you may already have a hobby or an interest that you want to turn into a business, or you have a passion for an idea that you believe will be a great business opportunity so you follow your interests. These off liners may take their business to the Internet for purposes of widening their marketing efforts. This is simple for various professional services, including specialized Doctors and Lawyers.
ONLINE
This in itself creates a full range of online service providers; designers, programmers, graphic designers, website developers, online marketing specialists, payment gateways, hosting and copy writers. eCommerce provides a fairly cheap way of gaining exposure for your product. Just for fun; a search for Online Shopping sites = 13,000,000, while a search for Online Shopping Websites = 48,800,000 so go ahead, get your own shopping site. Of course you may have a niche product such as one successful eBay marketer that sells only Big Mens Clothes. Perhaps you are a writer; you can take advantage and ease of being a self-publisher. There is a great demand for Informational sites. Blogs, forums, online news, e-magazines, almost anything that where you are a specialist. Freelancing is an option to consider. Even songwriters introduce themselves and their music online. Many of these free writers, bloggers, etc. are all trying to steer you to a favorite of theirs, so free is free, but do your homework. Therefore, there are many different types of successful online businesses. For almost any product, or service that is offered, there are types of online businesses. Many of these types of online business are very successful. To succeed in any business, you must have a good business plan, be hard working, offer a good product at a fair price, and offer great customer service. WSI Corporate
9.3 THE IMPORTANCE OF PASSION
Whichever business model you choose we believe it should involve something you are passionate about. Something you love to do. Do you LOVE playing video games? Awesome, make that the focus of your business. Do you love chocolate (and who doesn't?), but do you really love chocolate? Great, create a web business around that. Every web business that I have ever started has been based on something I have a passion for and enjoy thoroughly. I cannot tell you how important this is. Because making money online is great, but making money online doing something you, love is even better.
111
INTERNET USERS HANDBOOK
I have a passion for eBusiness (hence this site). The reason I wanted to start this guide was to (yes, hopefully make a little extra money) but also to help other people start web businesses of their own. Not necessarily to become millionaires or retire at the age of 30 or any of that, but to maybe help make ends meet, or maybe provide a little extra cash so they can save for their daughter's education, or provide a little bit of passive income so they can retire a few years early. Not everybody who starts an Internet business is going to be able to give up their day job and to do it full time like I do. However, I am certain most of you can; at the very least, create some incremental revenue for yourselves. When I meet people and tell them what I do, they say, almost without exception, something like "That sounds great, I wish I could do something like that." I tell them that they can, anybody can, and you just have to be willing to try it. When I mention this people; generally they say something like, "But I wouldn't even know where to start." Therefore, I put this guide together so that when people say that, I can just hand them a business card with this web address on it and say, "Now you do" ThreeBusGuide Sure you may have an interest or an idea, but you dont have the resources to develop them online. You can always try the same avenues of getting money as the off liners; friend, family, relative, partners, banker, etc. But online, most just turn to the net to supplement their income or to make a quick buck as promised by the scammers. Unfortunately, they lose to the first scam the sounds like it solves their problem It has little to do with their real interest; their interest is making money to pay bills, send the children to college, and improve their lifestyle and retirement. TIP: You are more likely to succeed in a business that you have some interest in and are passionate about. You are less likely to become a victim of a scam.
9.4 WHAT ARE THE BEST TYPES OF INTERNET BUSINESSES?
The Writer Asks I want to start an Internet business, but haven't yet sorted out my options. I want something that has potential to grow. I would greatly appreciate your responses. Thank U Didn't I read this elsewhere? You should read 'Rich Dad Poor Dad'. You can start any business and be a success or failure It all has to do with mindset. Work on that first BE --- DO --- HAVE Luc Arnold
9.5 FIVE PERFECT 'SPARE-TIME' ONLINE BUSINESSES
It does not take much time or effort to start moonlighting on the Internet. With all the doom and gloom news about the economy, there has never been a better time to make an extra paycheck online with a
112
INTERNET USERS HANDBOOK
minimal amount of time and effort. If you have an Internet connection, you can get started on the road to having the Internet pay for your mortgage, car payment, kids' college tuition, or even that special vacation you have wanted. Now, do not worry that you have to be a tech whiz to start a business online-I am a complete techno-dunce. A perfect part-time business would have to be very easy to start, require little time and money and no technical expertise, be easy to maintain with just a few hours a week and have a proven track record with a high probability of success. There is actually one other important criteria--it has to be perfect for you! Experience has taught me that it is different strokes for different folks, and there is no "one size fits all" perfect business. You are much more likely to be successful if you do something you find fun and interesting. With that in mind, here are five of the best ways to make extra cash moonlighting on the Internet:
AFFILIATE MARKETING
This may possibly be the absolute laziest way to make money because it doesn't require you to have a product, make a sale or ever have any interaction with customers. This is essentially a "referral" business, or as one of my book contributors likes to call it, "passionate recommendations." Basically, you can get paid a referral commission just for sending people to sites (or vendors) that are set up to pay affiliate fees once a sale is made. The vendor does all the selling, fulfills the purchase and handles any customer service issues--and you just collect your check.not bad! Some people choose affiliates based on whom or what is paying the highest commissions and that certainly is a viable option. Most people opt to choose products or goods they are passionate about so that the process is much more fun and engaging. Insurance and credit card companies pay high commissions for referrals that convert to customers ($40 to $150 and up), but the competition is fierce. It may pay well, but is this something you'll enjoy doing for the long haul? Alternatively, you could take a look at your hobbies and other things you enjoy and see which affiliate programs are good matches. As always, do your research to verify the viability of your market. A good place to look for ideas (and downloadable products just waiting for an affiliate) is ClickBank.com.
BLOGGING
This business is best suited for folks who enjoy communicating about a particular subject. Think of blogs as journals of sorts. Although you can have a personal blog, writing about a particular topic will have a higher chance for financial success. The range of topics is virtually endless--photography, sports cars, parenting, dieting, star gazing, the latest gadgets, Hollywood gossip--you name it, as there are blogs on just about everything you can imagine. Don't worry about competition. Folks who read one blog are apt to read others on a topic they're passionate about, as long as you have something interesting to say. Once your blog starts getting traffic, you can make money passively with things like AdSense (Google's ad revenue sharing plan) or actively by doing a little bit of affiliate marketing.
113
INTERNET USERS HANDBOOK
You can see both types of moneymaking strategies at SparkleCat.com, which is a blog about a person's cat. What makes it interesting is that it's written from the cat's perspective and often refers to her "human." At the top of the page are Google AdSense ads, and sprinkled throughout are suggestions for things like cat furniture and premium cat food, which are tied to an affiliate program. Pretty cool, no?
EBAY
One of the largest online marketplaces makes it a piece of cake to get your own business going. You can open an account and start making money within hours on eBay! While I dislike that whole "sell your garbage on eBay" thing, there is some validity to it as many people get their start on eBay by selling items from their garage or attic that pre-eBay would have been thrown out. This approach is fine, but where is the business once you run out of those items? If you want to create an eBay business that doesn't require tons of time and effort, you need to leverage products that can be sold over and over again. This is one of the reasons I'm not a fan of the "eBay seller for these" kinds of opportunities, where you sell things on eBay for other people. You get access to stuff people want to sell, but because each item is unique you have to work to list each and every one. There's no leverage there! Take a look at some of the largest eBay Power Sellers and notice how they specialize in very specific products (iPods, cell phones, dog grooming kits, etc.). This allows them to leverage their efforts. A listing is created once, and money is collected over and over again. Unlike information marketing, this business requires the handling of physical goods, but even that can be automated, so it shouldn't prevent you from considering this idea.
INFORMATION MARKETING
We're in the information age, and the Internet provides you with the ideal medium to exchange knowhow for money. Do you know the best fishing holes? How to play guitar? The secrets to a successful marriage? A recipe for moist and delicious brownies? A trick for saving gas? Think about your career, your hobbies and your interests. Virtually anything you know can be turned into extra cash. And don't worry if you think you're not an expert--as long as you know more than the average person on the topic, that information is valuable. However, if you do not believe you know anything those others would pay for (highly unlikely); you can take someone else's know-how and make money that way! It could be as easy as interviewing a veterinarian to help you create a dog-training product. Ninety-two percent of people go online looking for information, and you could be one of the many people cashing in on selling it.
YAHOO! STORE
This business is very similar to eBay in the sense that it's a monster-sized marketplace but more similar to a store in the true sense of the word. Think having your own retail outlet but without the hassles of rent, employees, utilities and all the other expenses of a traditional brick-and-mortar store. The neat thing is that it can be as hands-on or as hands-off as you want it to be because of companies called drop-shippers, which can do most of the work for you. In fact, you don't even pay for the inventory until
114
INTERNET USERS HANDBOOK
you make a sale. How cool is that? Most people think the hard part of this business is creating your virtual store, but nothing could be further from the truth. Yahoo! has made the templates and wizards so easy that, dare I say, even a caveman can do it! The best way to ensure your success is to do your homework and research what products people most want to buy. You need to find a niche. Once again, start with things you enjoy. Let's say you love fishing. What products do fishing folks want to buy most? (Or get even more specific, like, what are bass fishermen looking to buy?) Then the task is to find the right source of those products so you can carry them in your Yahoo! Store. In most cases, you'll be able to pull pictures and product descriptions directly from your sources and plug them right into your store. Yanik Silver
9.6 WHICH IS BETTER, A PRODUCT OR A SERVICE SITE?
This is one of the fiercest (and most childish, in my opinion) debates in network marketing, and I feel the need to address it head on for two reasons. The first and most important reason is that infighting between network marketers for the sake of making their individual home-based business opportunities look superior is silently one of the biggest cancers that attack the credibility of all of network marketing as a whole. The second reason is to provide some clarity for those unfortunate prospects and/or distributors who may have been confused, misinformed, or misguided (probably a mix of all three) by this catty nonsense. Here's the simple answer: it really depends on YOU. What inspires you, what jives with you, and what you feel most comfortable with? Contrary to its notoriously cookie-cutter image, network marketing is one of THE most customizable home-based business opportunities ---- or businesses period that has ever existed, which is one of the things that I absolutely love about it. So now for the longer answer! The first time I personally caught wind of this little debate was about 10 years ago when I had started my first home-based business in MLM. It was a well-respected service company that is still going strong to this day. A leader from the front of the room was making a snide, tongue-and-cheek remark about how he didn't want to "sell lotions and potions or fill up the trunk of his car with products". I really didn't think much about it at the time. I was one of the flocks, and what he said made perfect sense to me. The more experienced team members that surrounded me nodded their heads in agreement like pew-sitters in a Baptist church. (It was much later that I would find out that almost NONE of them were making any real money after YEARS in the business---but that's another article!) So, my first impression on this whole issue was formed: service companies were the way to go, and product companies were absurd, laughable affairs where you had to carry a trunk full of stuff. This was my way of thinking for years---until I joined a product company! I can't speak for ALL companies (neither product nor service), but here are just a FEW startling comparisons between my first two companies---one product, one service. The biggest eye-popper was the fact that in my first product company, people were making bigger checks with much smaller
115
INTERNET USERS HANDBOOK
organizations. The #1 money earner (my upline) at that time was making about $100,000 each month (I saw his checks with my own eyes). He had 1,000 distributors and 10,000 customers in his organization. The leader of my former team (in the service company) was making about $30,000 each month. This guy had at LEAST 10,000 distributors and tens of thousands of customers. My jaw dropped when I realized this. In my product company, it was easier for me to help others be successful. In the first service company that I was in, you'd never make any decent money unless you were able to recruit large numbers of people into your business. So what about people who weren't that good at recruiting? In my first product company, I noticed that each time I or one of my distributors got an additional customer that equated in several additional dollars in RESIDUAL income. In that company, I was making $100 per month in residuals with just 16 customers. In my service company, I had 20 customers and made about $5 in residual each month. In my service company, your residual never amounted to much unless you had a huge organization that was at least 6 levels deep. The problem with this is that most people will NEVER see 6 levels in their organization. And in home-based business it is critical that people make enough money to keep them in the game until they either "wake up" and start producing, or eventually recruit a superstar. There was a huge difference in the attrition rate. Because almost nobody made CONSISTENT money in my service company (recruiting bonuses don't count. These are promotional. In network marketing, the only income that REALLY matters for longevity is a residual check from real customers); the attrition rate was the typical 90% that exists in MLM. In my product company, that attrition rate was much closer to 50%-60% percent. The people that I brought in made more money. This was what struck me the most. Due to where I was mentally at that time, I never had much success in that product company due to my own unwillingness. However, I learned THE most valuable lessons of my entire network marketing career. One of them was that I noticed was that due to the compensation plan, EVERY person that I ever brought in made money--that was not the case with my service company. Because of this, even when people quit, none of them could say that they had not made money and this helped to not put a strain on my friendships as people decided not to do the business anymore. Now, please understand that this is NOT a cheerleading article for product companies vs. service companies! I am comparing two very specific experiences from two companies that I have personally done business with. If you were to choose a random service company and a random product company and compare the two, you would find a great deal of variation as far as which one was "better"-and that is my point.
116
INTERNET USERS HANDBOOK
There is no "hard and fast rule" of "which is better" when it comes to the service companies vs. product companies debate. As a matter of fact, as soon as I hear anyone, and I do mean ANYONE going in the direction of making the argument one way or another I immediately know that I am dealing with an amateur that does not get the bigger picture of the network marketing home-based business world outside of their company. So should you. LawrenceCole
THE DEBATE: PRODUCT OR SERVICE
For me that was a question when I started online. As I have said, offline many years ago, I had done the AMWAY, Tupperware etc. Online, I can still do all those; but here is the problem. If you are located in the USA, then products are easy to deal with; you can load your car and garage and sell your products. If you are overseas, many products have to be approved for import unless you claim for personal consumption. In some case, the country must license any products to do business in that country. Even then, some of the products that you may want may not be importable. Not all products are properly labeled. If health or diet related, may actually be dangerous. Often these types of products do not come with USDA approval and all you have is the claims and guarantees of the manufacturers. You take the risks. Now days, health drinks of one kind or another and healthy chocolate seem to be the rage. Unlike going out of business in the USA, you cannot easily return products; most online companies are once sold, there is not return policy. Over my beginning years online, I tried several product affiliations since most product sites typically have a better compensation plan than do service sites.
MY EXPERIENCE WITH PRODUCTS
XXXXXX Health Net, now out of business, where I learned to understand autoship and bundling You will receive a shipment every month and you dont get to pick individual products; you have to take one of the pre-bundled packages. Good for them; not so good for you. XXXXXX, a health drink, was a terrible experience, If you like downlines, they give you spillover, lots of it nearly 30,000 names, but the downline is useless to you if it is even real? Because you only have a name, no access, the sponsor retains access. With downline, you need access to your team, to motivate them, help them, etc. Sponsors claim to be available to solve problems, but they were not. Too busy getting more signups than taking care of present members. They wanted a US address, because when I first signed as they were not shipping to Malaysia, at that time. I would have had to re-ship for personal use. This should have been disclosed in advance of any sign-up or upgrade. I upgraded for a $500 shipment during their transition to open Asia operations. Several attempts to get sponsors, support and management, to stop the shipment for re-shipment to me in Asia,
117
INTERNET USERS HANDBOOK
The company made no attempt to reconcile the matter; then claim backs the shipment, since no one was there to accept it, etc. Failed. Lost $500. Nobody helped or even read their emails. XXXXXXX Chocolate, similar problems, wanted a US Address, willing to ship to local and reship, lots of workarounds, helpful, but for $1300 I passed. I had already joined, but wasnt made aware of the problem until I tried to upgrade, and then only after I had made the order and they wanted to ship. Most of the better, organized product sites, advise you in advance before your signup that they do not do business here or there. Check the FAQs and Terms. Most products pay better, if you can manage your shipments, etc. For me, I have learned that I prefer to babysit paper as opposed to products. Make sure the company can do business in your country.
LAST NOTE ON PRODUCTS
I have a concern about all the dietary, sliming, health drinks and beauty products that are pushed via our online affiliate programs. Some come with certifications, research etc. Few if any are FDA or equivalent agency approved. And yes, I have seen those that even after stringent FDA approval guidelines still suffer the recalls. Many companies that market their products through distributors sell quality items at competitive prices. But some offer goods that are overpriced, have questionable merits or are downright unsafe to use. The Federal Trade Commission warns consumers to apply a healthy dose of caution before buying products advertised as having "miracle" ingredients or techniques and guaranteed results. Many of these "quick cures" are unproven, fraudulently marketed and useless or even dangerous. Before using one of these products, the best prescription may be to check with a health professional. FedTradeCommission
9.7 10 REAL WAYS TO MAKE MONEY WITH YOUR WEBSITE
These days we can all use a bigger income, but it is definitely easier said than done. But the Internet has given us all opportunities that were never possible before to create our own success. There are many people who make a good living online and many who claim to have gotten rich, but there are also many people who are trying and trying but nothing is happening. I tried for several years before I started making a good living online so I would like to share some of the things that helped me increase my income. Although I have not tried every method listed below, I have tried several of them and they have worked for me.
AFFILIATE PRODUCTS
Find quality products and services that offer a commission and sell them on your site. Be sure they are relative to your site and if possible try the product out first so you can give a personal recommendation. Personal recommendations can help increase your sales. You can find affiliate products at AffiliateSeek, Clickbank, and AffiliateTips.
118
INTERNET USERS HANDBOOK
CLASSES AND WORKSHOPS
Organize some informative classes and workshops to teach your visitors how to 'whatever'. Sell space to attend these events. Offer a variety of classes such as a week-long class, month long, etc. You could also produce some effective webinars. You can also recruit affiliates for these services as well.
DONATION BUTTON
You see this more and more often these days. People offer a lot of free resources and content on their sire and ask for donations from the people who utilize this information. You can get the buttons directly from PayPal and place them on your site. To do this, you must provide quality content and value to your visitors so they feel a donation would be appropriate.
DROPSHIP SALES
Dropship means you can sell products without having to ship them or stock them. You find a company that offers drop shipping, sign up with them and start selling their products on your blog. Anytime you get an order, you send it to the main company and they ship the product out to your customer. The customer will think the product came from your store and you get a portion of the profits. You make money simply by taking orders and the dropship company does the rest. Dropship companies will usually require a membership fee, either monthly or annually.
SELL RESELL EBOOKS AND SOFTWARE
You can easily add a digital product store script to your existing blog and sell eBooks and software with resell rights. EBooks are very popular and the demand for them is increasing. You can also sell videos, music and other downloadable files from your digital store.
EXCLUSIVE ACCESS
Offer private content, forums, classes, etc. to members only. Charge a monthly or annual fee for this membership. People will pay for valuable information they can't seem to find anywhere else.
GOOGLE ADSENSE
This is not my favorite but it does work well for some people. What this entails is placing numerous ads on your site, chosen by Google. Anytime these ads are clicked on, you will get paid a portion of what the advertiser has paid Google. Google will choose ads that are relevant to your site's contents. So, what this means is that if you sell jewelry Google will place ads on your site to other people who sell jewelry and related products. So, in essence you are sending people to your competitor's sites. Although I do not agree with this, many people claim to make a good chunk of change each month using Google AdSense!
SELL ADVERTISING
Offer advertising space on your blog. You can offer text ads, banner ads and even video and audio ads. You can charge monthly and annual fees to give your customers a better value.
SPONSORED REVIEWS
Companies like Blogvertiser will connect you with advertisers who will pay you to write reviews about their products and services and place them on your site. You will have the option of accepting or declining any deals the advertisers offer. Other sites that offer this service are PayPerPost, SponsoredReviews and ReviewMe.
119
INTERNET USERS HANDBOOK
The methods above might not make you rich, but they can earn you a good income or add to your existing income. Some of these methods might not be for you but it could be worth your while to check them out. David
WRITE AND SELL YOUR OWN EBOOK
Write an eBook about your area of expertise and put it for sale on your site. You can sell it outright, offer resell rights or recruit affiliates to sell it for you as well. I did this with my first eBook and it worked out very well.
9.8 INTERNET BUSINESSES THAT ARE PRONE TO FAILURE
The types of Internet businesses that fail or should I say are more prone to failure are the ones that try to market goods that are widely available in the supermarket and the high street shops. Do not try and sell bulky goods like furniture, pet food, clothing or groceries on the web. These demands are already being met by well-established retailers online and off line. Do not try to compete with the large brands like Dell computers or Viking Direct as they have perfected the art of delivering products like computers and stationary direct to the end user. Their buying power is massive and they already have the infrastructure to keep most newcomers from succeeding in the market place. So what kinds of Internet businesses are more likely to succeed? The best Internet business ideas are the one that allow you to generate repeat orders from hard won customers. The products supplied will be either expensive or very light or both with decent profit margins built in. The products should also not be readily available in the supermarkets or high street stores. In the best cases you will not be delivering any physical product but instead providing a service on the web whether it is subscription based or an application like software that can be downloaded instantly and sold repeatedly. Be wary of the advice that is offered by so-called experts on the Internet. Most of them have never run an Internet venture before, and make their money solely by giving misleading or incorrect advice for a small payment. I call them "the hopeless Internet gurus." If you have already run a business successfully then you are much more likely to succeed in an Internet business, as the same business skills are required in both. In fact I would go even further and say that even more skills are required to succeed online as you also have to learn specialist skills like search engine optimization and creating great landing pages. A final word of warning; do not give up your day job unless you have ample capital to launch your new business and survive the first year.
120
INTERNET USERS HANDBOOK
Chances are that you will struggle to make a profit in year one. It's not all doom, gloom though for those of you who do have the right idea the world is your market place, and growth can be dramatic once you move into profits. InternetBusFranchise
121
INTERNET USERS HANDBOOK
10. AFFILIATE, PYRAMID AND MLM PROGRAMS
In this chapter you will see that almost anything that can be sold - can be sold online. Find out the differences between the three online networks, legitimate Affiliate, Affiliate Multitier and MLM and the illegal Pyramid schemes. Trying to rank these programs, as to which is best for you, is difficult because most site owners are selling their own affiliations or MLM. Learn the differences between each scheme. What legitimate ways to earn and be successful online are? As in the previous Chapter, find something of interest to you
10.1 WHAT IS AN AFFILIATE PROGRAM?
Wikipedia TIP: As you review the various materials and references, you may note that many references are still confused and treat any multi-tier program or MLM as a pyramid it is not, as we hope to clarify for you herein. Again, as in the previous section, try to find something that interests you and do your own due diligence. From the illustration, you should be able to see that the affiliate is the middle man/woman that exists between the customer and the seller. Other names include associate, broker, agent, dealer, etc. Affiliate program marketing is one of the best ways for newbies to learn how to make money on the Internet and to make a lot of money with. There are thousands and thousands of ordinary people, who are making an extraordinary living from affiliate program marketing. For the newbies affiliate program marketing is when you go to a company A, who sells a product or service. You complete the quick application process. The company approves your application. The company provides you with a unique link. This link contains your own unique affiliate ID. It is up to you to market this product and when you make a sale you get a commission on the sale. Dont worry about
122
INTERNET USERS HANDBOOK
how to make a sale. It can be done without moving from your couch. To join the affiliate marketing program is free. One of the things you may be wondering about is where do I find these companies to become affiliated to? The best way is to go to a search engine on the net and type in Affiliate program marketing directories. You will find thousands and thousands of companies who would kill to get you to market their products or services. The one that I like and use is at clickbank.com. It has a great selection (thousand) of products to market.Clickbank.com also guarantees that you will get paid your commission. They also have a 30 day money back guarantee on the products.
SELECTING A PRODUCT
Now selecting a product is one of the most important aspects off affiliate marketing: To start select a product that now and have interest in or are passionate about. This will make it easier for you to market. Do same research on the product. See if it is popular and does what it claims to do. Look at the commission that you will be generating. It can be anything from 25% to75%.It takes the same effort to make 25% or 75% commission. I would take the 75% commission product. Last but not least. All affiliate program marketing programs are in essence the same, but do differ in some small ways and these small differences can make a big difference in money. Most affiliate program marketing programs are in essence the same, but there are some small differences and these small differences can make a big difference. The difference comes in the amount of money you can generate per month. The first and one of the major differences between different affiliate program marketing programs is, is in the amount of commission that are paid to you. This could be from 25% to 75% it takes the same effort to sell a 25% or 75% commission product. There are lots of programs that pay 75% commission and the product cost more than $100.I know which program I will be promoting. The major reason being the fact that it takes the same effort and expenses to make a lot more money. Dont fool yourself making money is what it is all about. The next kind of affiliate program marketing program to consider is membership websites or as it is also know a residual income program. Here you are marketing membership to an affiliate marketers program or website at a monthly subscription. When people join the program through your efforts, you receive a commission for your sale, but it does not stop there. You also get a percentage of the subscription fee of these members who joined because of you. This you get every month for as long as the person stays with the program. You work once and are paid forever.
123
INTERNET USERS HANDBOOK
There are even same of this affiliate program marketing programs that gives you commission on the subscription of the members who joined the members who joined you. This adds up to a lot of money. This is cold leverage, doing more with less. The next difference comes in the form of customer care and training. This is the biggest difference between the different affiliate program marketing programs. This one can make or break you, so focus. The good programs will have great customer care and would bend over backwards to help you succeed. This will come in the form of pre-written solo-ads-mail, training video's etc. The great programs will have all of the above plus a plan that you can follow to make a success of your Internet business. This is a win, win situation if you succeed and make money they succeed and make money. AffiliateProgram Sometimes it can be an automated marketing program where a Web advertiser or merchant recruits webmasters to place the merchant's banner ads or buttons on their own Web site. Webmasters will receive a referral fee or commission from sales when the customer has clicked the affiliate link to get to the merchant's Web site Web site to perform the desired action, usually make a purchase or fill out a contact form. The most common types of affiliate programs include pay-per-click, pay-per-lead, and pay-per-sale.
HOW AFFILIATE MARKETING WORKS
If you have a Web site or blog and are looking for a way to earn income from your online property, consider affiliate-marketing programs. Affiliate marketing is the term used to describe a revenuesharing plan where an online automated marketing program lets Webmasters place an advertiser's banner ads or buttons on their own Web site. Webmasters will receive a referral fee or commission from conversions when a customer has clicked the affiliate link and performs the desired action, such as make a purchase or opt-in for downloads or newsletters on the advertiser's site. Advertisers invest in affiliate programs for lead generation, and, of course, sales. Not all affiliate plans work in the same way or pay the same rates. Some enable you to place text or image hyperlinks to products or a Web site, others allow you to set up a shopping or store page that offers products related to the content of your Web site, and others require you to place general advertising banners or buttons. The payouts for Webmasters also varies, but in the most common forms the affiliate is paid per click, each time a person clicks the ad (pay-per-click) or you may be paid a commission when a sale is made (pay-per-sale) or you might be paid by lead (pay-per-lead).
LEARN THE LINGO SEE APPENDIX GLOSSARIES
If you're in affiliate marketing, here is a quick reference of some of the more common terms used in conjunction with affiliate marketing. By familiarizing yourself with the terminology you will be better able to understand the affiliate agreement, how different programs work, and how you can earn money. Below you'll find direct links to common affiliate marketing terms from Webopedia.com.
124
INTERNET USERS HANDBOOK
10.2 TYPES OF AFFILIATE WEBSITES
Affiliate websites are often categorized by merchants (i.e., advertisers) and affiliate networks. There are currently no industry-wide accepted standards for the categorization. The following types of websites are generic, yet are commonly understood and used by affiliate marketers. Search affiliates that utilize pay per click search engines to promote the advertisers' offers (i.e., search arbitrage) Comparison shopping websites and directories Loyalty websites, typically characterized by providing a reward system for purchases via points back, cash back CRM sites that offer charitable donations Coupon and rebate websites that focus on sales promotions Content and niche market websites, including product review sites Personal websites (This type of website was the reason for the birth of affiliate marketing; however, such websites are almost reduced to complete irrelevance compared to the other types of affiliate websites.) Weblogs and website syndication feeds Email list affiliates (i.e., owners of large opt-in -mail lists that typically employ email drip marketing) and newsletter list affiliates, which are typically more content-heavy Registration path or co-registration affiliates who include offers from other merchants during the registration process on their own website Shopping directories that list merchants by categories without providing coupons, price comparisons, or other features based on information that changes frequently, thus requiring continual updates Cost per action networks (i.e., top-tier affiliates) that expose offers from the advertiser with which they are affiliated to their own network of affiliates Websites using adbars (e.g. AdSense) to display context-sensitive, highly-relevant ads for products on the site Wikipedia
ADVERTISERS
Different advertisers offer different types of affiliate programs. If you join a search engine affiliate program you most likely will be placing text links or banners to their advertisers and you'll work on a pay-per-click fee. email list affiliates promote email newsletters and are usually paid when a person joins the advertised opt-in email list. Being an affiliate of any merchant usually means you are paid a commission per sale on the advertiser's Web site. Pay-per-click affiliate programs pay the least amount, as affiliates are often paid per thousand clicks (CPC).
PAY-PER-LEAD PROGRAMS
Pay-per-lead programs are when you provide the links to downloads, trial offers, email optin lists and so on. Depending on the advertiser you may be paid per lead generation or you may not be paid unless the user subscribes and pays for a full service from the advertiser. Again, you may also receive fees for both instances.
125
INTERNET USERS HANDBOOK
PAY-PER-SALE AFFILIATE
Pay-per-sale affiliate programs (also called revenue sharing) usually offer the highest commissions, and you will typically receive a set dollar amount per sale or a straight percentage of the total sale. Because a user has to purchase something, you may find this program best suited to high-traffic affiliate sites.
HOW DO THEY WORK?
Knowing what ads to place and what revenue your Web site generates isn't magic. Once you join an affiliate program, you then are able to choose the products or banners you want to include on your Web site, and then receive the code you will need to insert on specific Web page or throughout your Web site. This changes, however, when you select an ad revenue partnership, such as Google AdSense, for example where you have little or no control over the advertisement displayed. In joining the affiliate program, you will agree to their terms of service, called an affiliate agreement, which will tell you what requirements you must meet and how the click-through, lead generation or sales are tracked. For the most part, affiliate programs work by using a combination of a unique user ID and cookies to track your leads and subsequent revenues. Most will offer a private affiliate section on their Web site where you can get your HTML code and also check your affiliate account status and information. Through the use of browser cookies, any person who uses your link to make the desired action within a set amount of time contributes to your affiliate revenue. For example if a user follows your link and looks through an online software store they are tracked as "your referral" by the browser cookie. If the person makes the purchase before the cookie expires, you get the referral commission. So even if a user sits with items in their shopping cart but doesn't go back and make the purchase for two weeks, you can still get the commission, provided the cookie is still active. For the Webmaster, one of the hardest things about using an affiliate program to earn money is finding a good one that will actually produce results for you. To better your chances of earning revenue from affiliate marketing here are some tips to get you started; Always read the fine print. Make sure you understand how the payouts are structured, if you need to earn a minimum dollar amount before a payout, and, of course, compare commissions between similar affiliate programs. Once you have narrowed down your options to a handful of possibilities, take a look at the merchant or marketers' Web site rankings and traffic. If, for example, you have your choice narrowed down to three computer software e-tailers, you can use Google and Alexa rankings to help you determine which may have a better volume of traffic. While their Web site traffic won't directly help you promote their products, this may tell you which company has a larger customer-base (more traffic). A well-known name that your Web site visitors may be familiar with might encourage them to click the advertising links on your own site.
126
INTERNET USERS HANDBOOK
Choose affiliate programs that complement your Web site content. If your site is all about sports, then chances are you'll want to skip on setting up a co-branded Web store for cartoon themed car accessories, for example. Also, if affiliate programs offer customizable banners, buttons or splash pages that can be edited to reflect elements of your own site design, be sure to take advantage of those options. Don't be afraid to play the field and try a couple affiliate programs, or opt out of one and choose another if you're not seeing any results after time. Results are going to be based on how much traffic your own Web site gets. If your site serves only a couple visitors a day, you can't expect high click-through numbers.
CHOOSING AN AFFILIATE PROGRAM
Because there are such a large number of affiliate programs to choose from and many are structured differently, here are some tips to keep in mind while looking for a good match. First, you need to be sure you are comfortable with the product you're promoting or selling and you have confidence in the advertiser you are linking to. Check the pages on the advertiser's Web site. If it's something you yourself would never consider purchasing, or it possibly looks a bit unreliable, then chances are your visitors won't be interested in it either. If you're running a content-based site, you don't want to sell anything that might offend visitors or lower their opinion of your site. The best rule of thumb is to pick affiliate programs that offer something that's relevant to your site. For example, if your Web site is about registering domain names, look for affiliate programs that are related to the topic such as Web site hosting, Webmaster tools and software, Web site templates and so on. There is nothing worse than advertisements that stand out like a sore thumb on your pages (e.g., online casino ads placed on a Web site about elementary school math tutorials). Even niche sites can find affiliate programs that are a good match. What is the Advertiser really offering its affiliates? Make sure you really understand the affiliate agreement and that you'll be able to comply with it. Take the time to check out the advertiser before joining to ensure they really do pay out to affiliates and that their program is not a scam. Look at what the advertiser is offering in terms of tracking and reporting tools for affiliates. Good programs will provide you with a way to access real-time automated statistics to view conversions, sales and commissions. Be sure you have ad and product display options to integrate the advertising into your Web site. Can you change the colors, themes and choose from a selection of different sized banners and buttons? With this type of service it means a little less work for you, the affiliate, and it also means your affiliate program meshes with your site. Some higher-pay programs may look attractive, but may offer a higher
127
INTERNET USERS HANDBOOK
commission because they might not provide support and tools to their affiliates. If this is the case, make sure you determine if this program will be too high-maintenance for you before joining. Pay-per-click programs offer the lowest dollar value for conversions, and you will need a higher click through rate to earn money. Pay-per-lead and pay-per-sale programs will usually offer a higher commission, but you will have less visitors clicking through to complete the transactions, so you need to have many unique visitors. Use your own traffic and reporting tools to determine which type of program will have a better chance of success on your own site. WebOPedia
10.3 DEFINING A GOOD AFFILIATE PROGRAM
Affiliate programs are a popular way to earn money online. But do you know what to search for in an affiliate program? It is important that you know what constitutes the best affiliate program before you sign up with any program. 8 Key factors that define a good affiliate programs are as follows:
REPUTABLE, HIGH QUALITY PRODUCTS, SERVICES OR BUSINESS OPPS
If you join up an affiliate program that does not have a good reputation, you will be wasting your money and time, and your online reputation will also be affected. An affiliate program with high reputation will also enable you to succeed because it will be easy for you to make sales
GOOD REFERENCES AND STABILITY
The Internet is full of scams. You will therefore need to join an affiliate program that has some good reviews and references; and the company must be stable and financially sound. If you do not research this, you risk joining an affiliate program which is a scam.
PAYS HIGH COMMISSION
Various affiliate programs offer a wide range of commissions. You will need to look for an affiliate program where your earnings are high. The affiliate programs commission structure is therefore very important, and you need to be fully informed about the potential commissions you can earn for each sale before you join any affiliate program.
RESIDUAL INCOME OPPORTUNITY
The best affiliate program is one for which you are rewarded several times over, just from a single sale. For example, if you make a sale today, some affiliate programs will reward you if that customer makes another purchase in the future, or if they refer someone who will make a purchase. This will simply increase your earnings in the long run.
RELIABILITY OF PAYMENT
Research on how reliable the affiliate program is at paying its affiliates. When you are in business, you will have some ongoing costs, such as marketing your business, and driving traffic to your affiliate website. You will therefore need to have constant payments to help you with the cash flow. Equally important is how frequent the program pays its affiliates. You would not want to wait months before you get paid.
128
INTERNET USERS HANDBOOK
AVAILABILITY OF SUPPORT AND MARKETING TOOLS TO AFFILIATES
You will need all the support and tools you can get in order for you to make sales and earn some commission. Some affiliate programs are good than others in terms of proving this support. Do your research and find an affiliate programs that offer support and tools that will make your job easier.
A PROGRAM THAT SUITS YOUR INTERESTS OR MATCH YOUR ONLINE BUSINESS
It is important for you to choose an affiliate program that has products or services that are of interest to you, so that you will enjoy marketing them. If you already have an online business and a website, you will need to choose an affiliate program that matches or complements what you already sell on your website. Your affiliate business is a long-term commitment, so you will need to make the right choice so that you sign up with a program that has products that you will enjoy marketing.
A PROGRAM THAT IS STILL GROWING AND HAS A HUGE POTENTIAL MARKET
You must avoid signing up with a program that is not popular or is declining in its reputation. While it is important to choose an affiliate program that has been in existence for a while and is stable, avoid joining a program that has exhausted its market growth potential or is simply losing its attractiveness. You want to sign up with a program that is in high demand and will be easy for you to sell. By using the guideline presented above, you will be able to pick an affiliate program that pays you well and on time. You will also join an affiliate program with easy-to-sell products that have high reputation and are in demand; and you will get the necessary support to make it easy for you to make sales. As an affiliate, you will want to see your commission checks increasing gradually over time; and the above factors will make this possible for you, if you select the right affiliate programs. HomeBasedBusiness
10.4 ISSUES WITH AFFILIATE MARKETING
Since the emergence of affiliate marketing, there has been little control over affiliate activity. Unscrupulous affiliates have used spam, false advertising, forced clicks (to get tracking cookies set on users' computers), adware, and other methods to drive traffic to their sponsors. Although many affiliate programs have terms of service that contain rules against spam, this marketing method has historically proven to attract abuse from spammers.
ADWARE
Although it differs from spyware, adware often uses the same methods and technologies. Merchants initially were uninformed about adware, what impact it had, and how it could damage their brands. Affiliate marketers became aware of the issue much more quickly, especially because they noticed that adware often overwrites tracking cookies, thus resulting in a decline of commissions. Affiliates not employing adware felt that it was stealing commission from them. Adware often has no valuable purpose and rarely provides any useful content to the user, who is typically unaware that such software is installed on his/her computer. Affiliates discussed the issues in Internet forums and began to organize their efforts. They believed that the best way to address the problem was to discourage merchants from advertising via adware.
129
INTERNET USERS HANDBOOK
Merchants that were either indifferent to or supportive of adware were exposed by affiliates, thus damaging those merchants' reputations and tarnishing their affiliate marketing efforts. Many affiliates either terminated the use of such merchants or switched to a competitor's affiliate program. Eventually, merchants and affiliates to take a stand and ban certain adware publishers from their network also forced affiliate networks. The result was Code of Conduct by Commission Junction/beFree and Performics,] LinkShare's Anti-Predatory Advertising Addendum, and ShareASale's complete ban of software applications as a medium for affiliates to promote advertiser offers. Regardless of the progress made, adware continues to be an issue, as demonstrated by the class action lawsuit against ValueClick and its daughter company Commission Junction filed on April 20, 2007.
EMAIL SPAM
In the infancy of affiliate marketing, many Internet users held negative opinions due to the tendency of affiliates to use spam to promote the programs in which they were enrolled. As affiliate marketing matured, many affiliate merchants have refined their terms and conditions to prohibit affiliates from spamming.
CLICK TO REVEAL
Many voucher code web sites use a click to reveal format, which required the web site user to click to reveal the voucher code. The action of clicking places the cookie on the website visitor's computer. The IAB have stated "Affiliates must not use a mechanism whereby users are encouraged to click to interact with content where it is unclear or confusing what the outcome will be. Answers
COOKIE STUFFING
Cookie stuffing involves placing an affiliate-tracking cookie on a website visitor's computer without their knowledge, which will then generate revenue for the person doing the cookie stuffing. This not only generates fraudulent affiliate sales, but also has the potential to overwrite other affiliates' cookies, essentially stealing their legitimately earned commissions.
LACK OF SELF-REGULATION AND COLLABORATION
Entrepreneurs who are working at the edge of Internet marketing drive affiliate marketing. Affiliates are often the first to take advantage of emerging trends and technologies. The "trial and error" approach is probably the best way to describe the operation methods for affiliate marketers. This risky approach is one of the reasons why most affiliates fail or give up before they become successful "super affiliates", capable of generating US$10,000 or more per month in commission. This "frontier" life combined with the attitude found in such communities is likely the main reason why the affiliate marketing industry is unable to self-regulate beyond individual contracts between advertisers and affiliates. Affiliate marketing has experienced numerous failed attempts to create an industry organization or association of some kind that could be the initiator of regulations, standards, and guidelines for the industry.] Some examples of failed regulation efforts are the Affiliate Union and iAfma.
130
INTERNET USERS HANDBOOK
Online forums and industry trade shows are the only means for the different members from the industryaffiliates/publishers, merchants/advertisers, affiliate networks, third-party vendors, and service providers such as outsourced program managersto congregate at one location. Online forums are free, enable small affiliates to have a larger say, and provide anonymity. Trade shows are costprohibitive to small affiliates because of the high price for event passes. An advertiser they promote may even sponsor larger affiliates. Because of the anonymity of online forums, the quantitative majority of industry members are unable to create any form of legally binding rule or regulation that must be followed throughout the industry. Online forums have had very few successes as representing the majority of the affiliate marketing industry. The most recent example of such a success was the halt of the "Commission Junction Link Management Initiative" (CJ LMI) in June/July 2006, when a single network tried to impose the use of a JavaScript tracking code as a replacement for common HTML links on its affiliates.
LACK OF INDUSTRY STANDARDS - CERTIFICATION AND TRAINING
Affiliate marketing currently lacks industry standards for training and certification. There are some training courses and seminars that result in certifications. However, the acceptance of such certifications is mostly due to the reputation of the individual or company issuing the certification. Affiliate marketing is not commonly taught in universities, and only a few college instructors work with Internet marketers to introduce the subject to students majoring in marketing. Education occurs most often in "real life" by becoming involved and learning the details as time progresses. Although there are several books on the topic, some so-called "how-to" or "silver bullet" books instruct readers to manipulate holes in the Google algorithm, which can quickly become out of date, or suggest strategies no longer endorsed or permitted by advertisers. Outsourced Program Management companies typically combine formal and informal training, providing much of their training through group collaboration and brainstorming. Such companies also try to send each marketing employee to the industry conference of their choice. Other training resources used include online forums, weblogs, podcasts, video seminars, and specialty websites. Affiliate Summit is the largest conference in the industry, and many other affiliate networks host their own annual events.
SEARCH ENGINE SPAM
As search engines have become more prominent, some affiliate marketers have shifted from sending email spam to creating automatically generated Webpages that often contain product data feeds provided by merchants. The goal of such Webpages is to manipulate the relevancy or prominence of resources indexed by a search engine, also known as Spamdexing. Each page can be targeted to a different niche market through the use of specific keywords, with the result being a skewed form of search engine optimization. Spam is the biggest threat to organic search engines, whose goal is to provide quality search results for keywords or phrases entered by their users. Google's PageRank algorithm update ("BigDaddy") in
131
INTERNET USERS HANDBOOK
February 2006the final stage of Google's major update ("Jagger") that began in mid-summer 2005 specifically targeted Spamdexing with great success. This update thus enabled Google to remove a large amount of mostly computer-generated duplicate content from its index. Websites consisting mostly of affiliate links have previously held a negative reputation for under delivering quality content. In 2005 there were active changes made by Google, where certain websites were labeled as "thin affiliates". Such websites were either removed from Google's index or were relocated within the results page (i.e., moved from the top-most results to a lower position). To avoid this categorization, affiliate marketer webmasters must create quality content on their websites that distinguishes their work from the work of spammers or banner farms, which only contain links leading to merchant sites. Some commentators originally suggested that Affiliate links work best in the context of the information contained within the website itself. For instance, if a website contains information pertaining to publishing a website, an affiliate link leading to a merchant's Internet service provider (ISP) within that website's content would be appropriate. If a website contains information pertaining to sports, an affiliate link leading to a sporting goods website may work well within the context of the articles and information about sports. The goal in this case is to publish quality information within the website and provide context-oriented links to related merchant's websites. However, examples that are more recent exist of "thin" Affiliate sites which are using the Affiliate Marketing model to create value for Consumers by offering them a service. These thin content service Affiliate fall into three categories: Price comparison Cause related marketing Time saving
TRADEMARK BIDDING
Affiliates were among the earliest adopters of pay per click advertising when the first pay per click search engines such as Goto.com (which later became Overture.com after being acquired by Yahoo! in 2003) emerged during the end of the 1990s. Later in 2000 Google launched its pay per click service, Google Adwords, which is responsible for the widespread use and acceptance of pay per click as an advertising channel. An increasing number of merchants engaged in pay per click advertising, either directly or via a search marketing agency, and realized that this space was already well-occupied by their affiliates. Although this situation alone created advertising channel conflicts and debates between advertisers and affiliates, the largest issue concerned affiliates bidding on advertisers names, brands, and trademarks. Several advertisers began to adjust their affiliate program terms to prohibit their affiliates from bidding on those types of keywords. Some advertisers, however, did and still do embrace this behavior, going so far as to allow, or even encourage, affiliates to bid on any term, including the advertiser's trademarks.
132
INTERNET USERS HANDBOOK
THREAT TO TRADITIONAL AFFILIATE NETWORKS
Cost per action networks may be viewed as a threat to "classic" affiliate marketing networks. Traditional affiliate marketing is resource-intensive and requires continual maintenance. Most of the maintenance includes managing, monitoring, and supporting affiliates. The goal of affiliate marketing is directed toward long-term and mutual beneficial partnerships between advertisers and affiliates. Cost per action networks, however, eliminate the need for the advertiser to build and maintain relationships to affiliates, as that task is performed for the advertiser by the cost per action network. The advertiser makes an offer, usually CPA-based, and the cost per action networks handle the remainder of the process by mobilizing their affiliates to promote that offer. Cost per sale and revenue sharing are the primary compensation models for classic affiliate marketing, and are rarely found in cost per action networks. Affiliate marketers typically avoid the topic of cost per action networks; however, if it is being discussed, the debates can become heated and explosive.
10.5 PYRAMID SCHEMES
Pyramid Schemes are not illegal in many parts of the world, but more countries are getting on onboard. You need to understand them to avoid them. See Speech Below In the classic "pyramid" scheme, participants attempt to make money solely by recruiting new participants into the program. The hallmark of these schemes is the promise of sky-high returns in a short period of time for doing nothing other than handing over your money and getting others to do the same. The fraudsters behind a pyramid scheme may go to great lengths to make the program look like a legitimate multi-level marketing program. But despite their claims to have legitimate products or services to sell, these fraudsters simply use money coming in from new recruits to pay off early stage investors. But eventually the pyramid will collapse. At some point the schemes get too big, the promoter cannot raise enough money from new investors to pay earlier investors, and many people lose their money. The chart below shows how pyramid schemes can become impossible to sustain:
NASecuritiesExchangeCommission(SEC)
133
INTERNET USERS HANDBOOK
FTC GUIDE TO PYRAMIDS
I would like to thank you for the opportunity to speak about the growing international problem of pyramid schemes. What is striking about these schemes is that while they are very old forms of fraud, modern technology has vastly multiplied their potential for harming our citizens. The Internet in particular offers pyramid builders a multi-lane highway to world-wide recruits in virtually no time.
WHAT IS A PYRAMID SCHEME AND WHAT IS LEGITIMATE MARKETING?
Pyramid schemes now come in so many forms that they may be difficult to recognize immediately. However, they all share one overriding characteristic. They promise consumers or investors large profits based primarily on recruiting others to join their program, not based on profits from any real investment or real sale of goods to the public. Some schemes may purport to sell a product, but they often simply use the product to hide their pyramid structure. There are two tell-tale signs that a product is simply being used to disguise a pyramid scheme: inventory loading and a lack of retail sales. Inventory loading occurs when a company's incentive program forces recruits to buy more products than they could ever sell, often at inflated prices. If this occurs throughout the company's distribution system, the people at the top of the pyramid reap substantial profits, even though little or no product moves to market. The people at the bottom make excessive payments for inventory that simply accumulates in their basements. A lack of retail sales is also a red flag that a pyramid exists. Many pyramid schemes will claim that their product is selling like hot cakes. However, on closer examination, the sales occur only between people inside the pyramid structure or to new recruits joining the structure, not to consumers out in the general public.
PONZI SCHEME
A Ponzi scheme is closely related to a pyramid because it revolves around continuous recruiting, but in a Ponzi scheme the promoter generally has no product to sell and pays no commission to investors who recruit new "members." Instead, the promoter collects payments from a stream of people, promising them all the same high rate of return on a short-term investment. In the typical Ponzi scheme, there is no real investment opportunity, and the promoter just uses the money from new recruits to pay obligations owed to longer standing members of the program. In English, there is an expression that nicely summarizes this scheme: It's called "stealing from Peter to pay Paul." In fact some law enforcement officers call Ponzi schemes "PeterPaul" scams. Many of you may be familiar with Ponzi schemes reported in the international financial news. For example, the MMM fund in Russia, which issued investors shares of stock and suddenly collapsed in 1994, was characterized as a Ponzi scheme. Both Ponzi schemes and pyramids are quite seductive because they may be able to deliver a high rate of return to a few early investors for a short period of time. Yet, both pyramid and Ponzi schemes are illegal because they inevitably must fall apart. No program can recruit new members forever. Every pyramid
134
INTERNET USERS HANDBOOK
or Ponzi scheme collapses because it cannot expand beyond the size of the earth's population. When the scheme collapses, most investors find themselves at the bottom, unable to recoup their losses. Some people confuse pyramid and Ponzi schemes with legitimate multilevel marketing. Multilevel marketing programs are known as MLM's, and unlike pyramid or Ponzi schemes, MLM's have a real product to sell. More importantly, MLMs actually selling their product to members of the general public, without requiring these consumers to pay anything extra or to join the MLM system. MLM's may pay commissions to a long string of distributors, but these commission are paid for real retail sales, not for new recruits.
HOW PYRAMID SCHEMES OPERATE
Let's look at how a pyramid scheme operates from three points of view: the potential investor, the promoter or con artist, and the victim. Many pyramid schemes will present a payout formula or matrix much like this one: # Level 1 $150 x 3 = $450 Level 2 $30 x 9 = $270 Level 3 $30 x 27 = $810 Level 4 $30 x 81 = $2430 --------$3960 # ### Payment of $500 # ### # ### #########
################## etc. # # # # # # # # ##########
# # # # # # # # #etc.
This example illustrates what is known as a three by four matrix. Each investor pays $500 to the promoter and is told to build a "downline" by recruiting three new members, who then each should recruit three more members. The investor is told that he will be paid $150 for each of the three members whom he enlists at the first level. The investor is also promised $30 commissions for each recruit at the next three levels. Thus, the investor should receive commissions for four levels of recruits below him, each of whom must recruit three more members, hence the name -- a three by four matrix. To the potential investor/recruit this may look like a very appealing opportunity. The pyramid promoter is likely to persuade the investor that he is "getting in early" and that he should consider himself at the top of the matrix. From this perspective, it appears that he can earn $3,960 on an investment of $500, a whopping 792 percent return.
VICTIMS
Now consider the pyramid from the investor/victim's perspective -- after the entire scheme has collapsed around him. The victim, like the first investor, thought of himself at the top of the pyramid
135
INTERNET USERS HANDBOOK
but suddenly realizes that he is actually at the bottom, unable to find people interested in the program to build out his downline. He is not alone because mathematics shows that MOST investors will find themselves at the bottom of the pyramid when it collapses. The very structure of this matrix dictates that whenever the collapse occurs, at least 70 percent will be in the bottom level with no means to make a profit. A Ponzi scheme could yield even worse results for investors, because it does not pay out any commissions at all. This can have disastrous consequences, as exemplified by Charles Ponzi's infamous fraud in the 1920's. Charles Ponzi, an engaging ex-convict, promised the Italian American community of South Boston that he would give them a 50 percent return on their money in just 45 to 90 days. Mr. Ponzi claimed that he could pay such a high rate of return because he could earn 400 percent by trading and redeeming postal reply coupons. These coupons had been established under the Universal Postal Convention to enable a person in one country to pre-pay the return postage on a package or letter sent back from another country. For a short time after World War I, fluctuations in currency exchange rates did create a disparity between the cost and redemption value of postal reply coupons among various countries. However, Mr. Ponzi discovered that he could only make a few cents per coupon and that handling large volumes of coupons cost more than they were worth. He stopped redeeming any coupons but continued to collect investors' money. When he actually paid a 50 percent return to some early investors, his reputation soared and more money flowed in from around the country. Mr. Ponzi bought a stylish house in the best part of town and purchased a large minority interest in his local bank, the Hanover Trust Company. Eventually his scheme began to unravel, bringing ruin to the bank and thousands of investors. When Mr. Ponzi began to overdraw his accounts at Hanover Trust, the Massachusetts Banking Commissioner ordered Hanover Trust to stop honoring Ponzi's checks. The bank refused and even issued back-dated certificates of deposit to cover Mr. Ponzi's overdrafts. A few days later, the Banking Commission took over Hanover Trust, and Mr. Ponzi was arrested for mail fraud. In the end, Charles Ponzi owed investors over $6 million, an enormous sum of money for that time. He was convicted of fraud in both state and federal court and served ten years in prison.
AMWAY CORP
In re Amway Corp., another landmark decision from the 1970's, the FTC distinguished an illegal pyramid from a legitimate multilevel marketing program. At the time, Amway manufactured and sold cleaning supplies and other household products. Under the Amway Plan, each distributor purchased household products at wholesale from the person who recruited or "sponsored" her. The top distributors purchased from Amway itself. A distributor earned money from retail sales by pocketing the difference between the wholesale price at which she purchased the product, and the retail price at which she sold it. She also received a monthly bonus based on the total amount of Amway products that she purchased for resale to both consumers and to her sponsored distributors.
136
INTERNET USERS HANDBOOK
Since distributors were compensated both for selling products to consumers and to newlyrecruited distributors, there was some question as to whether this was a legitimate multilevel marketing program or an illegal pyramid scheme. The Commission held that, although Amway had made false and misleading earnings claims when recruiting new distributors, the company's sales plan was not an illegal pyramid scheme. Amway differed in several ways from pyramid schemes that the Commission had challenged. It did not charge an up-front "head hunting" or large investment fee from new recruits, nor did it promote "inventory loading" by requiring distributors to buy large volumes of nonreturnable inventory. Instead, Amway only required distributors to buy a relatively inexpensive sales kit. Moreover, Amway had three different policies to encourage distributors to actually sell the company's soaps, cleaners, and household products to real end users. First, Amway required distributors to buy back any unused and marketable products from their recruits upon request. Second, Amway required each distributor to sell at wholesale or retail at least 70 percent of its purchased inventory each month -- a policy known as the 70% rule. Finally, Amway required each sponsoring distributor to make at least 1 retail sale to 10 different customers each month, known as the 10-customer rule. The Commission found that these three policies prevented distributors from buying or forcing others to buy unneeded inventory just to earn bonuses. Thus, Amway did not fit the Koscot definition: Amway participants were not purchasing the right to earn profits unrelated to the sale of products to consumers "by recruiting other participants, who they are interested in recruitment fees rather than the sale of products. PYRAMID SCHEMES IN THE 1990'S The 1990's first brought an important refinement in the law. As the Commission pursued new pyramid cases, many defendants proclaimed their innocence, stating that they had adopted the same safeguards -- the inventory buy-back policy, the 70% rule, and the 10 customer rule -- that were found acceptable in Amway. However, an appellate court decision called Webster v. Omnitrition Int'l, Inc., pointed out that the Amway safeguards do not immunize every marketing program. The court noted that the "70% rule" and "10 customer rule" are meaningless if commissions are paid based on a distributor's wholesale sales (which are only sales to new recruits), and not based on actual retail sales. The court also noted that an inventory buy-back policy is an effective safeguard only if it is actually enforced. While new cases were refining the law in the 1990's, radical changes were underway in the marketplace. Pyramid schemes came back with a vengeance. Like most economic activity, fraud occurs in cycles, and new pyramid schemes exploited a new generation of consumers and entrepreneurs that had not witnessed the pyramid problems of the 1970's.
137
INTERNET USERS HANDBOOK
Also, the globalization of the economy provided a new outlet for pyramiding. Pyramids schemes found fertile ground in newly emerging market economies where this type of fraud had previously been scarce or unknown. In Albania, for example, investors poured an estimated $1 billion into various pyramid schemes -- a staggering 43% of the country's GDP. In the U.S., probably nothing has contributed to the growth of pyramid schemes as much as Internet marketing. The introduction of electronic commerce has allowed con artists to quickly and costeffectively target victims around the globe. After buying a computer and a modem, scam artists can establish and maintain a site on the World Wide Web for $30 a month or less, and solicit anyone in the world with Internet access. Pyramid operators can target specific audiences by posting messages in specialized news groups (e.g., "alt.business.home" or "alt.make.money.fast"). In addition, through unsolicited email messages -known on the Internet as "spam" -- pyramid operators can engage in cheap one-on-one marketing. Whereas it might cost hundreds or thousands of dollars to rent a mailing list and send 10cent post cards to potential recruits, it costs only a fraction of that to send out similar email solicitations. On the Internet, you can acquire one million email addresses for as little as $11 and spend nothing on postage. The Federal Trade Commission's current law enforcement efforts reflect this new wave in pyramiding. The Commission has brought eight cases against pyramid schemes in the last two years, and six of those have involved Internet marketing. One recent case, FTC v. FutureNet, Inc., is particularly instructive because it starkly reflects the potential for abuse in hi-tech and newly deregulated industries. FutureNet allegedly claimed that, for payment of $195 to $794, investors could earn between $5000 and $125,000 per month as distributors of Internet access devices like WebTV. The FTC filed suit, charging that FutureNet's earnings claims were false because the company really operated an illegal pyramid scheme. Near the time of filing, FTC investigators discovered that FutureNet had begun to sell electricity investments as well, riding a wave of speculation in advance of the deregulation of California's electricity market. The Commission obtained a TRO and an asset freeze over the defendants' assets and eventually reached a $1 million settlement with the corporate defendants and two individual officers. The settlement requires the defendants to pay $1 million in consumer redress, bars them from further pyramiding activity of any kind, requires them to post a bond before engaging in any network marketing, and requires them to register with state utility officials before engaging in the sale of electricity. The Commission continues to litigate its case against three non-settling individual defendants.
CONSUMER EDUCATION
Law enforcement is the cornerstone of the Commission's fight against pyramid schemes; however, we also try to educate the public so that they can protect themselves. In our educational efforts, we have
138
INTERNET USERS HANDBOOK
tried to take a page from the con artists' book and use new online technology to reach consumers and new entrepreneurs. For example, on the agency's web site at "www.ftc.gov", the Commission has posted several alerts regarding pyramid schemes and multilevel marketing problems. The Commission records over 2 million "hits" on its home page every month and receives several thousand visitors on its pyramid and multilevel marketing pages. The staff of the Commission also has posted several "teaser" web sites, effectively extending a hand to consumers at their most vulnerable point -- when they are surfing areas of the Internet likely to be rife with fraud and deception. The "Looking for Success" site is one example. It advertises a fake pyramid scheme. The home page of "Looking for Success" promises easy money and talks in glowing terms about achieving "financial freedom." On the second page, the consumer finds a payout plan common to pyramid schemes, as well as typical buzz words like "forced matrix," "get in early," and "downline." Clicking through to the third and final page in the series, however, brings the consumer to a sobering warning: "If you responded to an ad like this one, you could get scammed." The warning page provides a hyper-text link back to FTC.GOV, where consumers can learn more about how to avoid pyramid schemes.
LOOKING AHEAD
Unfortunately, pyramid schemes are likely to continue to proliferate both here and abroad in the near future. However, we can all help stem the tide by working together. Finally, you can encourage the relevant officials in your countries to combat pyramid schemes by educating consumers and businesses about how to recognize and avoid this type of fraud. This can be particularly important in emerging markets, where experience with investment opportunities may be scarce.
10.6 MULTI-LEVEL MARKETING PROGRAMS
The benefit of multilevel marketing could be also known as multilevel earnings. A single avenue of earning is you selling your product or service results in a one-time sale. There are no residual benefits to you unless you have a store such as ClickBank will you possible earn an additional sale of the same customer. Adding a multiple tier opportunity enables you to gain earning from your downline, perhaps one level or more giving you greater and perhaps residual earnings from your one time sale. In another Pay per Click or Pay to Read Section, you will see that those sites that actually pay you, pay your very little and the only way to make any real income, is to get paid from your work and the work of others your downline. The likelihood of a top guru joining your affiliate or MLM site is nil, because they can make their own sites faster that you can join them. So you either take your time and slowly build your downline, or you create your own site with enough content and value, that perhaps your will attract a Joint Venture partner, or o a top performance joins under you and brings his or her downline with them. For one opinion on the differences, see the following video
139
INTERNET USERS HANDBOOK
MLM VERSUS AFFILIATE MARKETING
An interesting MLM versus Affiliate Video. (Subtle selling vs. recruiting and selling) Also discusses Cash Gifting Programs and Pyramids Scheme - Legal issues. Do your homework. Limited money made from 2 tiers, 98% do not make money. Worth seeing! Search for 2 create a website and you will find a very aggressive and successful lady. See the difference ways she advertises from blogs to videos. MLM and Affiliates Marketing, Difference Between Affiliate Marketing and MLM This site wants your direct view so we cannot publish the article, but we can link to the article. Link only site. AffiliatesSeeking.com is a good source of information on this subject and others.
IS IT MLM OR A PYRAMID?
TIP: Without your Due Diligence to check out a program before you spend your money, you may be at risk of participating in a pyramid scheme Multilevel marketing plans, also known as "network" or "matrix" marketing, are a way of selling goods or services through distributors. These plans typically promise that if you sign up as a distributor, you will receive commissions -- for both your sales of the plan's goods or services and those of other people you recruit to join the distributors. Multilevel marketing plans usually promise to pay commissions through two or more levels of recruits, known as the distributor's "downline." If a plan offers to pay commissions for recruiting new distributors, watch out! Most states outlaw this practice, which is known as "pyramiding." State laws against pyramiding say that a multilevel marketing plan should only pay commissions for retail sales of goods or services, not for recruiting new distributors.
WHY IS PYRAMIDING PROHIBITED?
Because plans that pay commissions for recruiting new distributors inevitably collapse when no new distributors can be recruited. And when a plan collapses, most people -- except perhaps those at the very top of the pyramid -- lose their money. The Federal Trade Commission cannot tell you whether a particular multilevel marketing plan is legal. Nor can it give you advice about whether to join such a plan. You must make that decision yourself. However, the FTC suggests that you use common sense, and consider these seven tips when you make your decision: Avoid any plan that includes commissions for recruiting additional distributors. It may be an illegal pyramid. Beware of plans that ask new distributors to purchase expensive inventory. These plans can collapse quickly -- and also may be thinly-disguised pyramids.
140
INTERNET USERS HANDBOOK
Be cautious of plans that claim you will make money through continued growth of your "downline" -- the commissions on sales made by new distributors you recruit -- rather than through sales of products you make yourself. Beware of plans that claim to sell miracle products or promise enormous earnings. Just because a promoter of a plan makes a claim doesn't mean it's true! Ask the promoter of the plan to substantiate claims with hard evidence. Beware of shills -- "decoy" references paid by a plan's promoter to describe their fictional success in earning money through the plan. Don't pay or sign any contracts in an "opportunity meeting" or any other high pressure situation. Insist on taking your time to think over a decision to join. Talk it over with your spouse, a knowledgeable friend, an accountant or lawyer. Do your homework! Check with your local Better Business Bureau and state Attorney General about any plan you're considering -- especially when the claims about the product or your potential earnings seem too good to be true. FedTradeCommission
LOTIONS AND POTIONS: THE BOTTOM LINE ABOUT MLM PLANS
Lose weight! Firm up! Look better! Live longer! 'Tis the season for consumers to be confronted with a wide range of health, beauty and fitness products and promotions. Many of these items aren't available on store shelves and are sold only through distributors.
WHAT ARE YOU BUYING?
Many companies that market their products through distributors sell quality items at competitive prices. But some offer goods that are overpriced, have questionable merits or are downright unsafe to use. The Federal Trade Commission warns consumers to apply a healthy dose of caution before buying products advertised as having "miracle" ingredients or techniques and guaranteed results. Many of these "quick cures" are unproven, fraudulently marketed and useless or even dangerous. Before using one of these products, the best prescription may be to check with a health professional.
WHAT ELSE IS FOR SALE?
Some distributors sell more than diet and exercise plans, vitamin supplements or wonder creams. Many may sell "opportunities," too-a chance for you not only to buy, but also to market, the products. In addition to describing the benefits of their product or program, these distributors may encourage you to become a distributor.
141
INTERNET USERS HANDBOOK
If you sign up as a distributor, you may be promised commissions or other rewards-for both your sales of the plan's goods or services and those of other people you recruit to become distributors. These plans, often called "multilevel marketing plans," sometimes promise commissions or rewards that never materialize. Whats a worse, consumer are often urged to spend or "invest" money in order to make it.
WATCH OUT FOR PYRAMIDS
Steer clear of multilevel marketing plans that pay commissions for recruiting new distributors. They are actually illegal pyramid schemes. Why is pyramiding dangerous? Because plans that pay commissions for recruiting new distributors inevitably collapse when no new distributors can be recruited. And when a plan collapses, most peopleexcept perhaps those at the very top of the pyramid-end up empty-handed.
HOW TO EVALUATE A PLAN
If you're thinking about joining what appears to be a legitimate multilevel marketing plan, take time to learn about the plan before signing on. What's the company's track record? What products does it sell? How does it back up claims it makes about its product? Is the product competitively priced? Is it likely to appeal to a large customer base? What up-front investment do you have to make to join the plan? Are you committed to making a minimum level of sales each month? Will you be required to recruit new distributors to be successful in the plan? Use caution if a distributor tells you that for the price of a "start-up kit" of inventory and sales literature -and sometimes a commitment to sell a specific amount of the product or service each month-you'll be on the road to riches. No matter how good a product and how solid a multilevel marketing plan may be, expect to invest sweat equity as well as dollars for your investment to pay off.
YOUR RESPONSIBILITIES
If you decide to become a distributor, remember that you're legally responsible for the claims you make about the company, its product and the business opportunities it offers. That applies even if you're simply repeating claims you read in a company brochure or advertising flyer. When you promote the qualities of a product or service, you're obligated to present those claims truthfully and to ensure there's enough solid evidence to back them up. The Federal Trade Commission advises you to verify the research behind any claims about a product's performance before repeating those claims to a potential customer. Likewise, if you decide to solicit new distributors, be aware that you're responsible for any claims you make about a distributor's earnings potential. Be sure to represent the opportunity honestly and to avoid making unrealistic promises. If those promises fall through, remember that you could be held liable. FedTradeCommission
142
INTERNET USERS HANDBOOK
10.7 MATRIX SCHEMES
A matrix scheme (also known as a matrix sale or site, and as a hellevator, escavator or ladder scheme) is a business model involving the exchange of money for a certain product with a side bonus of being added to a waiting list for a product of greater value than the amount given. Matrix schemes are also sometimes considered similar to Ponzi or pyramid schemes. They have been called unsustainable by the United Kingdom's Office of Fair Trading
HISTORY
The first known matrix scheme is widely believed to be EZExpo.com, which started the popularity of matrix schemes in 2002. By 2003 more than 200 matrix schemes were in operation, including one which had the same owner as the payment processor Stormpay (TymGlobal). Subsequently TymGlobal and Stormpay were accused of running an illegal Ponzi scheme. Stormpay later claimed to be independent of TymGlobal, and they stopped accepting matrix schemes as customers. Although many have since ceased trading, some schemes are still known to be operating worldwide. The payment processor, Stormpay, is no longer trading.
OPERATION
The operation of matrix schemes varies, though they often operate similar to pyramid or Ponzi schemes. Some of the former participants of these schemes consider them to be a form of confidence trick, although others are happy with their purchase. To move upward in the list, a person must wait for new members to join or refer a certain number of people to the list. This is accomplished through purchasing a token product of marginal value: usually e-books, cell phone boosters, screen savers, or other software CDs/DVDs. When a predefined number of people have purchased the token product the person currently at the top of the list receives their reward item, and the next person in the list moves to the top. The rewards for those at the top of the matrix list are usually high-demand consumer electronics, such as portable digital audio players, high-definition television sets, laptop computers, and cellular phones. Reaching the point on the list where you receive the expensive goods is termed "cycling". In many cases, the token product alone could not be reasonably sold for the price listed, and as such legal experts claim that, regardless of what is said, the real product being sold is the "reward" in question in those situations. In these cases, the operator could be charged with running a gambling game or failing to supply ordered products. Steven A. Richards, a lawyer who represents multi-level marketing (MLM) companies for Grimes & Reese in Idaho Falls, Idaho, has stated that often there are no clear legal tests for Ponzi schemes. But if the product sold has no value or very little value, and consumers wouldnt buy it without the attached free gift, the scheme probably runs afoul of federal and state laws. The Matrix List by which the sites receive their name would be what is known as a straight-line matrix, or 1 by X matrix. This is similar to many MLMs that use Y by X matrices to fill a down-line. For example, one situation may be a 1 by 10 matrix for a Sony PlayStation 2 (a common reward). In such a matrix the site would usually sell an e-book for $50 to be placed on the list. After 9 additional people
143
INTERNET USERS HANDBOOK
purchased a spot, the first person would receive either a PS2 or cash value equivalent and would be removed from the list. The person who had been second would move up to the first spot and an additional 10 people would have to purchase in order for this person to receive a PS2. It is this orderly movement which has also given the name Elevator Scheme to these sites as people would move up the elevator (escalator, ladder) to the top at which they would then cycle out of the matrix. In such a matrix, 9 out of 10 or 90% of all customers will not receive the reward item, because the rules of the scheme are that one reward is issued for every 10 customers that join. (The fact that the reward is issued to the customer at the top of the list doesn't change the proportion of rewards given to customers signed up.) Supporters claim that additional revenue streams from advertising are used to keep the lists moving. However, detractors claim that it is impossible to generate enough outside revenue. If the entire world were to join the list, 90% of the world would be unable to cycle if the site did not draw sufficient alternate revenue streams. Adding more people to the list does not change the fact that the majority would receive nothing without these streams. Additionally, the amount of time needed before a given individual will receive the product in question is often mistaken. In a matrix in which 10 people are required before it will cycle, the first person to join only needs 9 additional sign ups, but the second person needs 18 additional sign ups, 8 more for the person above him, and then 10 more for himself. The third person on the list likewise needs 27 additional signups, 7 for the person on top of the list, 10 for the person directly above him, and then 10 for himself. And then the number of people required continues to grow for each new person joining the list. For the 10th person to cycle it would require 100 people total, and 1000 for the 100th, and so on. Wikipedia
10.8 TIPS FOR CONSUMERS AND BUSINESSES BEWARE OF ANY PLAN:
THAT MAKES EXAGGERATED EARNINGS CLAIMS
Beware of any plan that makes exaggerated earning claims especially when there seems to be no real underlying product sales or investment profits. The plan could be a Ponzi scheme where money from later recruits pays off earlier ones. Eventually this program will collapse, causing substantial injury to most participants.
THAT OFFERS COMMISSIONS FOR RECRUITING NEW DISTRIBUTORS
Particularly when there is, no product involved or when there is a separate, up-front membership fee. At the same time, do not assume that the presence of a purported product or service removes all danger. The Commission has seen pyramids operating behind the apparent offer of investment opportunities, charity benefits, offshore credit cards, jewelry, women's underwear, cosmetics, cleaning supplies, and even electricity.
144
INTERNET USERS HANDBOOK
THAT PURPORTS TO SELL A PRODUCT OR SERVICE
Check to see whether its price is inflated, whether new members must buy costly inventory, or whether members make most "sales" to other members rather than the public. If any of these conditions exist, the purported "sale" of the product or service may just mask a pyramid scheme that promotes an endless chain of recruiting and inventory loading.
THAT CLAIMS TO HAVE A SECRET PLAN
Overseas connection or special relationship that is difficult to verify. Charles Ponzi claimed that he had a secret method of trading and redeeming millions of postal reply coupons. The real secret was that he stopped redeeming them. Likewise, CDI allegedly represented that it had the backing of a special overseas bank when no such relationship existed.
THAT DELAYS MEETING ITS COMMITMENTS WHILE ASKING MEMBERS TO "KEEP THE FAITH."
Many pyramid schemes advertise that they are in the "pre-launch" stage, yet they never can and never do launch. By definition, pyramid schemes can never fulfill their obligations to a majority of their participants. To survive, pyramids need to keep and attract as many members as possible. Thus, promoters try to appeal to a sense of community or solidarity, while chastising outsiders or skeptics. Often the government is the target of the pyramid's collective wrath, particularly when the scheme is about to be dismantled. Commission attorneys now know to expect picketers and a packed courtroom when they file suit to halt a pyramid scheme. Half of the pyramid's recruits may see themselves as victims of a scam that we took too long to stop; the other half may view themselves as victims of government meddling that ruined their chance to make millions. Government officials in Albania have also experienced this reaction in the recent past.
THAT ATTEMPT TO CAPITALIZE ON THE PUBLIC'S INTEREST IN HI-TECH OR NEWLY DEREGULATED MARKETS
Every investor fantasizes about becoming wealthy overnight, but in fact, most hi-tech ventures are risky and yield substantial profits only after years of hard work. Similarly, deregulated markets can offer substantial benefits to investors and consumers, but deregulation seldom means that "everything goes," that no rules apply, and that pyramid or Ponzi schemes are suddenly legitimate.
CONCLUSION
As we continue to pursue pyramid schemes, we would be delighted to coordinate our efforts with law enforcement in your countries. It is only too evident that the expansion of fraud across borders and on the World Wide Web means that no one agency or country can work effectively on its own. We must be collectively vigilant in order to protect the integrity of our marketplaces and the pocketbooks of our consumers. SpeechFTC-IMF
145
INTERNET USERS HANDBOOK
10.9 FOR THE I DONT DO MLM READERS
These are a great view and a must see for the I Dont Do MLM readers: NETWORK MARKETING EXPLAINED - BY TIM SALES MLM: DO MOST PEOPLE FAIL? TIM SALES IS MLM A PYRAMID SCHEME - TIM SALES FIRST CLASS MLM TOOLS
10.10 EBAY POLICY MLM, PYRAMID, AND MATRIX PROGRAMS
POLICY OVERVIEW
We don't allow listings and advertising of multi-level marketing programs (including online payment randomizers), matrix, pyramid, Ponzi schemes, and all similar programs on eBay. These programs are often regulated or illegal. Make sure your listing follows these guidelines. If it doesn't, it may be removed, and you may be subject to a range of other actions, including limits of your buying and selling privileges and suspension of your account.
WHAT ARE THE GUIDELINES? MULTI-LEVEL MARKETING
Not allowed. This includes any business where you receive income from your own sales and income from your recruited members. Online payment randomizers (because the majority of commissions are paid for recruitment of new members, and typically operate by random placement within the program.)
PYRAMID SCHEMES:
These schemes often ignore the actual selling of products and services, and concentrate on the income you can earn by recruiting new distributors. Pyramid schemes might not involve selling products.
MATRIX PROGRAMS:
These programs involve the exchange of money primarily for being added to a waiting list for a product. If you're at the top of the list, you receive a product when a set number of people join after you join.
146
INTERNET USERS HANDBOOK
11. MANAGING YOUR ONLINE BUSINESS
Congratulations on your Decision to Start or Grow your Business Online. This handbook will help put you on the path to building a successful online business while avoiding the scams. It is written with an offline business mindset meaning that we are serious about your business and what it takes for you to prepare yourself. Online, it is not a 9-5 job any more than an offline business. It is not a hobby! While you may have to treat it as a part-time job due to other work commitments until it grows, it should be treated as I will do it when I can or want. Discipline yourself and follow a daily plan of action to build your business. Doing business online is a far cry from just becoming an affiliate or getting your own domain, building a website and off you go!
11.1 GET COMFORTABLE
Get a good chair and desk, table or workstation of proper height for your keyboard to minimize your discomfort.
11.2 WORKING AT HOME
To think, read, write and work without the TV, and other distractions especially if one of your income opportunities includes Forex. Adjust your online work hours for your day job, if you have one, and for the best time to work without distractions. Forget the chat rooms, social networks, Skype, etc. which is time consuming or limit your time to these methods of creating business for yourself. So you have either been in the online business or looking to get into it. I call this section Get Comfortable because this online venture is not a 5 20 minutes a day job, no matter what you are told by others. If you have been online for a while, then you probably already know that. Your website(s) have to be marketed, regardless if it 100% autopilot, no sponsorship required, we do the marketing for you, or any of the other hype stories that you have or will be told.
PAID OR EMAIL ADVERTISING
Set up you ads, spend your money, and wait for the next time you need to top off of advertising budget. Make several ads, ads need to be monitored, tested - to see what works, what doesnt work- ultimately what brings in and converts the buyers. Setup and periodically run your email advertising program. Get leads for your email and check your ads for spam. You need to learn advertising and marketing techniques. And the list goes on....
VARIOUS TRAFFIC PROGRAMS
You either have to buy credits to run your ads, or your click or surf the sites hour after hour to earn credits to posts your ads. Ads often have to be posted on a daily basis, so you have to access each site daily to post your ads. Ads posted to various free, or Free-For-All (FFA), ads blasters, etc.; these often require confirmation, so after you have posted your ads, you need to check your email to confirm the posting.
147
INTERNET USERS HANDBOOK
11.3 SELF-DISCIPLINE
A favorite of the work-at-homers: Work in your pajamas, shorts or whatever. Sounds great, but I recommend that you treat your online venture like any job. No, you do not need a tie, but get up shower and shave, brush your teeth (you get the point ladies) Whether full-time or part-time treat your online job as a business and not a hobby. Your advantage is that you can do it at home. Great: No buses, no traffic and none of all those other inconveniences that you put up with in having to leave the house for an outside job. You will feel better, work better, and be more productive
11.4 MANAGING YOUR COMPUTER AND SOFTWARE
I get very uncomfortable and frustrated when I am trying to do something and my computer and other equipment is not working properly. I need this equipment to do my job, if they do not work properly; how can I be productive?
MICROSOFT VERSUS APPLE
I have with been with Microsoft since the very early days and do not have any Apple experience other than testing and having compatibly problems, so my comments here are Windows based. If you can afford it, get a good high-speed computer, printer/fax combination, broadband or wireless modem, and a bigger monitor. Additional memory is cheap so it is value for dollar to upgrade your memory and graphics Social networking, even email requires that your computer be able to cope with the video and graphic demands made of it. Check your computer Windows Experience rating.
WINDOW EXPERIENCE
Whether you are buying a new computer or using and older one; check your Windows Experience Index base score to see what you might do to improve your computers performance Go to Start Control Panel, System and Maintenance, Performance Information and Tools; Check Your Computers Window Experience Index Base Score. Click on Window Experience Index link The screen will advise you of the weak points in your computer that you might make an upgrade to improve performance, again check the memory. Usually, the memory and graphics will be your computers weak points. Again, if you are buying new, be sure to check this before your leave the shop.
VIRUS PROTECTION
A necessary starting point to maintain and protect your computer. A computer virus is a computer program that can copy itself and infect a computer. The term "virus" is also commonly but erroneously used to refer to other types of malware, adware, and spyware programs that do not have the reproductive ability. A true virus can only spread from one computer to another (in some form of executable code) when its host is taken to the target computer; for instance because a user sent it over a network or the Internet, or carried it on a removable medium such as a floppy disk, CD, DVD, or USB drive. Viruses can increase
148
INTERNET USERS HANDBOOK
their chances of spreading to other computers by infecting files on a network file system or a file system that is accessed by another computer. Most personal computers are now connected to the Internet and to local area networks, facilitating the spread of malicious code. Today's viruses may also take advantage of network services such as the World Wide Web, email, Instant Messaging, and file sharing systems to spread. Wikipedia As an active online user, you must protect your computer and files from any such attacks. Windows defender helps, but I prefer to supplement windows features with a third party solution. While there a many paid commercial and free software available to you, I have had satisfactory results for a free program for personal use offered by Avast, although I have since upgraded to full-protection. This software program automatically runs in the background and is updated to keep your virus detection current. Free version available. Avast New computers normally come with a trial version of virus software leaving it up to you to accept and upgrade or not. I usually delete that program and install Avast.
SLOW COMPUTERS
The daily use of your computer will result in various defragmented files; i.e. a piece of the file here and another there. To improve the computers performance, it is necessary to periodically clean your computer hardrive; usually the C drive. Then defrag your registry and your computer drives. However, Windows will defrag the drives, but does not defrag the registry.
WINDOWS TOOLS
Windows Update Keeping your computer software updated can reduce your changes of a getting a computer virus, better operation and performance. Window update can update both windows and other Microsoft problem as the same time Go to Start lower left hand windows logo All programs Find Windows Update Click and let it run If you leave your computer running all night, you can set the update software to update the computer automatically; however, it will reboot itself to install the changes. Therefore, if you have Forex trades going, then your Forex sites will be offline until you open them again. If there are a lot of updates, then it is recommended that you run the update program again to get updates to the updates. Change happens! Window update can update all your Microsoft products
RECYCLE BIN
When you delete a file from your computer, it is temporarily stored in the Recycle Bin. This usually gives you an opportunity to restore the file to its original location if you discover that the file should not have been deleted.
149
INTERNET USERS HANDBOOK
To permanently remove files from the computer and reclaim any hard disk space they were using, you need to permanently delete files from the Recycle Bin. You can choose to delete individual files from the Recycle Bin or empty the entire Recycle Bin at once. Click to open Recycle Bin. Do one of the following: To delete one file, click it, and then press DELETE. To delete all of the files, on the toolbar, click Empty the Recycle Bin. You can also empty the Recycle Bin, without opening it. Right-click the Recycle Bin, and then click Empty Recycle Bin. To permanently delete a file from your computer without first sending it to the Recycle Bin, Click the file, and then press SHIFT+DELETE.
DISK CLEANUP
If you want to reduce the number of unnecessary files on your hard disk to free up disk space and help your computer run faster, use Disk Cleanup. It removes temporary files, empties the Recycle Bin, and removes a variety of system files and other items that you no longer need. Click to open Disk Cleanup. In the Disk Cleanup Options dialog box, choose whether you want to clean up your own files only or all of the files on the computer. If you are prompted for an administrator password or confirmation, type the password or provide confirmation. If the Disk Cleanup: Drive Selection dialog box appears, select the hard disk drive that you want to clean up, and then click OK. Click the Disk Cleanup tab, and then select the check boxes for the files you want to delete. When you finish selecting the files you want to delete, click OK, and then click Delete files to confirm the operation. Disk Cleanup proceeds to remove all unnecessary files from your computer. Disk cleanup can also delete the files in the recycle bin
DEFRAGMENT YOUR HARD DISK
Fragmentation makes your hard disk do extra work that can slow down your computer. Disk Defragmenter rearranges fragmented data so your hard disk can work more efficiently. Disk Defragmenter can run on a schedule, but you can also defragment your hard disk manually. Click to open Disk Defragmenter. If you are prompted for an administrator password or confirmation, type the password or provide confirmation. Click Defragment Now. Disk Defragmenter might take from several minutes to a few hours to finish, depending on the size and degree of fragmentation of your hard disk. Although not recommended. You can still use your computer during the defragmentation process. If you have not defragmented your computer in a while, then you should repeat the process a second time.
THIRD PARTY TOOLS
I prefer the free third party solutions offered below for defragging my computer. Often they offer more features and in this case are faster and more visible. Find tools to defrag both the hardrive and the registry. Often third party vendors will provide good and viable alternatives to the Microsofts Windows
150
INTERNET USERS HANDBOOK
One Vendor with various free tools, including both registry clean up and defrag, that work well for me may be found at Auslogics. Auslogics is easy to use, fast and nice graphic interface for the Disk Defrag, registry cleaner, etc. Again, recommend performing the defrag more than one, as each pass defrag the majority, but another pass may find more. For the amount of work that I do online, I often need to defrag at least once a week with maybe 2-3 passes While you are there, see the other products Auslogics has to offer. I like their Boost Speed Program.
CHANGE YOUR COMPUTER START-UP PROGRAMS
As you add programs to your computer, some that you will use only on occasion will be installed in your start up folder. This results in unnecessary programs trying to load when you start up, which slows you down
For the more computer savvy: Got to the Widows logo located at the lower left corner. Type msconfiq in the bottom box. The link will show in the window under Programs. Click and this will bring up a new screen Click the Start-up tab and unclick those programs that you dont need at start-up. Keep your Microsoft, virus and related programs. Click Apply and restart your computer. Try it, if you are uncomfortable, then do nothing and let someone else do it for you. Do so, at your own risk.
UPDATE CHECKER
Update Checker updates other programs on your computer for better operation and performance
ROBOFORM
Just managing your affiliations, traffic and other sites, providing signup details for a new site, remembering user name, ids and passwords name for logins can be very time consuming. Window, Google and other offer some help, but the long standing, best rated software that I have found and use is RoboForm RoboForm includes a password generator which is convenient to generate and save different passwords for multiple sites, as has been recommended herein. If you maintain a lot of sites, as I do, then the upgrade is great, but not necessary. Upgrading enables you to click and the site loads and logs you in. The free version will log you in after you have loaded the site. While you are there see what else http://download.cnet.com has to offer for free
OTHER NEED OR NICE TO HAVE PROGRAMS
Adobe Reader 1-Click Answers Edit Pad Lite Free PDF to Word Converter Firefox Browser Free Open Office http://get.adobe.com/reader/ http://www.answers.com/main/download_answers_win.jsp http://www.editpadpro.com/editpadlite.html http://www.hellopdf.com/ http://www.mozilla.com/en-US/firefox/personal.html hhttp://download.openoffice.org/
151
INTERNET USERS HANDBOOK
SUCCESS OFTEN COMES TO THOSE WHO LOOK, FEEL AND ACT THE PART.
Success radiates through others. If you feel good about yourself, then your chances of success improve. In most cases, to be successful, you need to surround yourself with good people. However, since you are most likely working alone, surround yourself with the proper tools and equipment to make your feel successful. Just as you need to keep yourself informed and up to day, you also need to keep your computers and equipment running at its top performance. Get comfortable and enjoy your online experiences.
ADDING NEW PROGRAMS.
We have already talked about doing your own due diligence as part of your decision to join a new program. TIP: before you sign up, spend your money, and reload the site on another tab. Try right clicking and opening the site on the new tab. This will give you is a fresh site in case our tip doesnt work for the site you are considering... Now try to escape or close the first tab, if there is a discount of some kind, it will usually popup. Then if you are still interested, your entry cost has gone down; however, you will lose some digital product or something. At least you have a second or third choice, cheaper entry cost. Then if the program works, you can upgrade from your profits. If you still like the original deal better; then complete your signup up on the second site that you made, before this experiment.
11.5 MANAGING YOUR TIME AND COMMUNICATIONS
Time is a precious commodity, especially if you are starting your online business part-time. Use it wisely and productively
CHATS AND FORUMS
Just like the job offline, some of your associates just to love to mingle and talk, Great for building relationships, but is the relationship productive, will it add to your financial bottomline. Chats are also a great diversion and relaxing, but can eat up your time and take your away from your objectives
SKYPE
Skype is probably one of the best online VOIP solution offering message, telephone and video. Great to for building relationship, directly answering questions and perhaps training with your sponsor or downline. I use it sparingly and dont leave it on. If one, you keep getting popup for so and so ins online.
EMAIL
I should have been paying more attention to this chapter as I will discuss later. Managing your email is a large part of managing your business after you have everything setup.
152
INTERNET USERS HANDBOOK
What to do when email that you want keeps showing up in your junk mail, instead of your regular mail folders? We have spent some time talking about scams and spam mails, but when you are in business you need your mail, when you are sending mail, you want it to get to the other party. What is Whitelisting? How do you dispose of the spam or junk mail that is overloading your junk mailbox and inbox? Why are most sites now recommending the use of Gmail; its advantage and disadvantages?
WHAT IS WHITELISTING?
A Whitelist is a list of email addresses or domain names from which an email blocking program will allow messages to be received. email blocking programs, also called a spam filters, are intended to prevent most unsolicited email messages (spam) from appearing in subscriber inboxes. But these programs are not perfect. Cleverly crafted spam gets through, and a few desired messages are blocked. Most Internet users can tolerate the occasional unsolicited email advertisement that a spam filter misses, but are concerned by the thought that an important message might not be received. The whitelist option is a solution to the latter problem. The list can be gradually compiled over a period of time, and can be edited whenever the user wants. Some spam filters delete suspected junk email messages straightaway, but others allow the user to place them in a quarantined inbox. Periodically, the quarantined messages are observed to see if any of them are legitimate messages. This option is used by some Webbased email clients in place of, or in addition to, a whitelist.
How to Whitelist Your Emails
The Terms and Conditions of most traffic sites state that you must Whitelist their email when you join their site. In other cases, some information or emails that you want to receive may wind up in your junk mail; Whitelisting, or Safelisting is a method of identifying and ensuring that you receive the mail that you want. All this self-policing for spam is great, but affects us as well as the spammers. More and more sites, especially free Traffic sites with their volumes of advertisers email that they out only to have it blocked or sent to junk mail. Many sites now post the following message or otherwise complain about their problems with Yahoo mail getting through to their customers. Please open a gmail.com account to sign up as more ISP's are bouncing Ads. If you use other than Gmail, then see your email provider for Whitelisting instructions.
GMAIL
From your junk mail folder, click the email and click the NOT SPAM tab. To have future emails from the same originator go directly to your INBOX, click the email and go to the MORE Tab.
153
INTERNET USERS HANDBOOK
This will bring an up a drop-down menu, Select FILTER MESSAGES LIKE THIS. A new screen will show your selected email and others from the same source. Click NEXT STEP which will bring up the CREATE FILER screen. Select NEVER SEND IT TO SPAM You can apply of all message if there are any. Finish by clicking CREATE FILER
WHAT IS A BLACKHOLE LIST?
A Blackhole list, sometimes simply referred to as a blacklist, is the publication of a group of ISP addresses known to be sources of spam, a type of email more formally known as unsolicited commercial email (UCE). The goal of a blackhole list is to provide a list of IP addresses that a network can use to filter out undesirable traffic. After filtering, traffic coming or going to an IP address on the list simply disappears, as if it were swallowed by an astronomical black hole. The Mail Abuse Prevention System Real-time Blackhole List, which has over 3000 entries, is one of the most popular blackhole lists.
GMAIL ACCOUNTS BENEFITS OF GMAIL
Gmail is FREE and you can open multiple accounts. Many list builders require that you have at least two accounts, one for admin type mail and one for advertising mail. Go to Gmail.com. All of your Gmail accounts can easily be imported into Outlook. Gmail will retain all of your email, BUT see disadvantages
DISADVANTAGES OF GMAIL
You cannot do sorts, and search results seem to vary from the messages in Gmail from those imported in Outlook. You cannot query junk mail. I prefer the features offered by Microsoft Outlook at this time. However that are some other good ones, try a Google search for your choices. TIP: Since Gmail will retain all of your email, then anyone that hacks your Gmail account, which happened to me, will have access to all of your user IDs and passwords See also your Google Dashboard
REMEDY
Print and maintain an offline file of all accounts, add to RoboForm. Search for User Id and Password emails, and delete them from your Gmail history. Change your passwords and Ids frequently. Use different passwords and Ids on your financial and personal accounts TIP: You can delete from Gmail, but you must also delete from Google Dashboard. TIP: emails that are caught in the Gmail junk mails folder will not get through to your or Microsoft Outlook Access your Gmail Junk Mail folder to screen the emails; move the ones you that you need to your inbox
154
INTERNET USERS HANDBOOK
MY TWO BIG MISTAKES PRIMARY AND LIST ACCOUNTS
Where the signup traffic or list builder site did not offer 2 links, I used my primary email for all mail from that site Dumb! You really receive very little admin mail except, perhaps, for a promos code, your login, etc. So put all of this site mail into your list account. Once in your primary or admin email account, you have to load the login page and reset your email account to your list account. Slow and Painful, but necessary. Try to keep your Primary account clear of unnecessary ads. Dump your trash as Great idea; get a list account so you can keep your primary account free and clear. However, your list account fills up with emails that need to be read or dumped. My mistake, dumpling lets say all the solo ads. Doing this puts them in Trash which also must be dumped. Google says it dumps all trash over 30 days old, it my case something went wrong and I wound up with over 600,000 emails. TIP: Create a minimum of two Gmail accounts Keep your primary account clear of advertisement by directing all such to your list account. You will continue to receive spam.
LOGINS
Many sites expect you to login or read mail to keep your account active. Some offer a vacation mode which will keep your active, but relieve you of the daily email traffic. Most require you to login in to repost your ads for the day, as the ads are only good for 24 hours. If you are trying to make money off these sites, rather than just use them to advertise your products; then you need to surf their site, some require you to surf x number of sites per day to earn from your downline or to post your ad. Joining one site often leads to joining another and another, until there is no way that you can keep up and read all the mail, or surf daily.
BOXBE
This Free Service site has been banned by many traffic sites; but maybe there is a message there. I just want you to be aware of it, what does and how it might impact or benefit your business and good selves.
REDUCE YOUR EMAIL OVERLOAD
Consider this; you now have some programs and you have joined a few advertising sites to promote your business. By now, you are now receiving emails; lots of them, both junk and intended. How to manage all these? Some of your mail will wind in your regular account while others from the same source will be in your junk folder. If you use free traffic sites and safelists for your advertising, then you will be quickly overloaded with email to read just to earn credit for your own ads. First, unless you have no life at all, you will never keep up.
155
INTERNET USERS HANDBOOK
The best you can do is try to visit each of your sites once in a while, surf a little, manage your credits and read some of their emails. TIP: If you have a particular site or probably several that you want to use daily, then you can monitor your junk mail for those sites, and have them filtered to your inbox. See Whitelisting instructions above. Remember, if you are using Microsoft Outlook and perhaps others, email links for credit will not work while that email is in your junk mail folder. Move it to your inbox Once you sign up for these various traffic sites, the mails keeps coming, unless shut them off by going on vacation. Your terms and conditions of the site say that you are willing to read others members email, in exchange for posting your own ads, banners, etc. With so much email coming in each day, you need a methodology to deal with it, since obviously you will never keep up. As I said, I joined many programs for evaluation; some of the confirmation email will show up in my junk mail folder, perhaps before you have whitelisted the source. Further, I may not remember the site names or the source, because some of these jokers dont make it easy for you; i.e. Site XXXa email will come from XX@xx .xx, or a person you never heard of. So then you are stuck with who is XX@xx.xx and is this Site one that I wanted? Still others send email like confirm your site when you never signed up in the first place. TIP: Start With Your Primary email Folder. Search for the Keywords: Welcome, Admin, Support, Confirm, Activate, Validate and Password. Check the junk mail folder for others From your search, take the action required to activate your new accounts.
Save the settings, User Ids and passwords to RoboForm and print the emails for your files. Since you have completed the action required on these emails, they should be deleted Search the remaining emails by site name. You can then delete all email from that site or Click 1 or 2 or all to get the credits you need, and delete the balance. Some site offer promotions, promos codes, others warn you if you site credits are running low. Most of the traffic sites require you to log in daily to post your ads. TIP: If you really want to reduce your Inbox and Junk Mail boxes and start over because you went on vacation, took a break, or whatever; then Search for solo. This will cover the majority of your traffic exchange mail. Delete them form the primary folder and then remember to delete your Trash. I had over 300,000 emails in Gmail with solo.
156
INTERNET USERS HANDBOOK
SPAMMER KEYWORDS
The scammer/spammers are perhaps younger and smarter many of us as they now use the same keywords that we use to sort our email; Welcome, Admin, Support, Confirm, Activate, Validate to flood our emails by using the words in the From list or the Titles
SPAMMERS CREATE NEW PROBLEM
You have been waiting for that Never to be received Support or Admin email, but when you do a search for support or admin you will likely find several scammer/ spammer ads trying to sell you on another site. A search for Password and you will get scammer/spammer ads: Click her to activate you password and site. However, these may very well be emails for sites that you never requested to join in the first place.
ACTIVATING NEW SITES
If you are old and slow like me, then there may be an activation email that you have requested but overlooked. When your click on the link, the link has expired and so has your request. TIP: No Problem. Edit the link in your browser to the base or home page, sign up again, and then wait for a new email with your activation link.
157
INTERNET USERS HANDBOOK
12. WHAT IS SPAM AND ITS IMPACT?
Many of us jokingly recognize Spam as canned meat that is sold internationally and has been around since 1937. Sorry. We could have added Spam to our Advertising Chapter, but the problem is so significant, it needs to stand on its own! Spam is the abuse of electronic messaging systems (including most broadcast media, digital delivery systems) to send unsolicited bulk messages indiscriminately. Today - a more generally accepted definition of SPAM seems to be one of I dont know or remember you, I didnt ask for it; therefore I consider it SPAM (See Blog entry that follows) TIP: Scammers are Spammers. One of their favorite tools is Spam. Learn what it is. Learn How to protect yourself from being Labeled or Blocked for being a Spammer. While the most widely recognized form of spam is email spam; the term is applied to similar abuses in other media: Instant messaging spam Usenet newsgroup spam Web search engine spam Spam in blogs Wiki spam Online classified ads spam, Mobile phone messaging spam Internet forum spam Junk fax transmissions Social networking spam File sharing network spam Attempts to control spam is seemingly out of control as the following blog post suggest
12.1 WHY SPAM?
Spamming remains economically viable because advertisers have no operating costs beyond the management of their mailing lists, and it is difficult to hold senders accountable for their mass mailings. Because the barrier to entry is so low, spammers are numerous, and the volume of unsolicited mail has become very high. The costs, such as lost productivity and fraud, are borne by the public and by Internet service providers. They have been forced to add extra capacity to cope with the deluge. Spamming is widely reviled, and has been the subject of legislation in many jurisdictions. Spam is prevalent on the Internet because the transaction cost of electronic communications is radically less than any alternate form of communication, far outweighing the current potential losses; as seen by the amount of spam currently in existence.
158
INTERNET USERS HANDBOOK
Spam can be used to spread computer viruses, Trojan horses or other malicious software. The objective may be identity theft, or worse (e.g., advance fee fraud). Some spam attempts to capitalize on human greed whilst other attempts to use the victims' inexperience with computer technology to trick them (e.g., phishing) Wikipedia According to a recent Microsoft report, 97% of the email that is sent each day is unsolicited, virus or spam mail. Another says that it is 60% spam. As such, nearly everyone, as you will see, is on a Spam Watch. Everyone for Internet Service Providers (ISP), to Instant Messaging, (IM) to email providers is trying to find ways to stop the mail from getting through. The problem created by this change of mentality, is that every email is treated as guilty mail until proven innocent. Your good email may be filtered out for the choice of a wrong word. Anyone, even as a prank, can label your email as Spam, and give you the headache of a lifetime. Your ability to recognize spam can help you reduce yourself from being a victim of a Scam, and give you a better chance of getting your own marketing email through to the intended receiver. Further, it will reduce your likelihood of being penalized for being a spammer.
12.2 HOW TO AVOID THE SPAM FILTERS
To avoid being labeled or blocked as a spammer, learn what about spam and how to protect yourself against it or being penalized for using it Email marketing as many of us know, can be a powerful and inexpensive method of reaching our most active potential and/or existing customers. It can boost not only our direct sales, but also our credibility and referrals. One of the major benefits of email marketing is that email is free, but obviously, this is the same reason that spam has become so popular and so frustrating. With spam also comes the spam filters and with spam filters comes the blocking of legitimate email.
SELECTION OF WORDS
Many spam filters work by analyzing the email based on its content and the words used. Many words - such as free, sex and so forth -- are very heavy spam trigger keywords. Your priority should be to avoid such words while keeping your newsletter as professional as possible. Later in this article, I will show you a technique that I use to help me detect words that could trigger spam filters that I may have missed.
PAY ATTENTION TO YOUR FORMATTING
When formatting your email, keep it simple and professional. Excessive use of different colors, fonts, sizes, images and so forth will result in a higher spam filtering rate. Keep your email as clean as possible,
159
INTERNET USERS HANDBOOK
and try to stick to a maximum of 2 or 3 different font types and sizes. Overly large sized fonts will surely add to an email being flagged as spam, as will too many images (not enough text). Try and use a short and simple style sheet rather than using font tags excessively. Most spam filters don't appreciate a multitude of font tags and inline formatting, and the more primitive filters can't detect style sheets so they will not penalize as easily.
CONSISTENCY IS KING
Use a template if you plan on sending newsletters consistently. This will make sure that all your newsletters look and feel the same. It will also add a touch of professionalism and branding to your newsletters. Whilst not directly affecting spam filters, this will enable your readers to distinguish your newsletter instantly, thus not reporting it as spam accidentally. Some spam filters work by querying a spam server, whereas others report individual emails as spam. If your email gets reported as spam, then more than likely multiple spam filters will flag your email. Being consistent with your timing of the newsletter also helps. For example, if you send a newsletter once per month (I personally do not recommend you send out any more than this, unless you have something interesting to say), then aim to send it out at the same time, on the same day each month. Once again, your potential readers will learn to expect your email, adding professionalism and often improving open rates, also reducing accidental spam flagging as well.
ALWAYS DOUBLE OPT-IN
Always make your mailing lists double opt-in. This means that when a user subscribes to your mailing list, they will be sent an email with a link that they must click on to confirm their subscription. This is very important because many people can accidentally enter an incorrect email address or even the email address of someone else on purpose. When that person receives a newsletter they did not subscribe to, they will assume they have been spammed, and your newsletter (and possibly your web server) will be reported as spam.
UNSUBSCRIBE AND CONTACT INFORMATION
Every newsletter you send out should contain a way for the reader to unsubscribe. Not doing so is illegal in some countries and is an instant sign of spamming. You should also display your contact information (Phone, Fax and Address) clearly, as this greatly increases confidence in your email and your company, as well as conforms to spam laws in the United States. Contact information also allows a potential customer to contact you if need be.
TEST, TEST, TEST
The key to avoiding spam filters is testing. The first method of testing I use is to send the newsletter to multiple email accounts with existing spam filters. For example, I have a Gmail (http://www.gmail.com) account and a Hotmail (http://www.hotmail.com) account that I make sure I send my newsletter to. If the newsletter ends up in the junk folder, then I've got some work to do.
160
INTERNET USERS HANDBOOK
I also have a couple of email accounts with different web hosts that have spam filters in place. In particular, they mostly use spam assassin -- a popular piece of spam filtering software. Spam assassin is useful because every email that it flags as spam is given a report and a list of why that email was considered spam. I also have a local spam filtering application called No Spam Today! For Workstations, that runs a local copy of spam assassin on my PC. It acts as a very close replica to the same software used on thousands of servers world-wide, by sending myself copies of the newsletter No Spam Today! -- Using the spam assassin checking techniques -- gives me feedback as to why my email may have been flagged. If I have used words or formatting that I should not have, or if I have included too many images, etc. InterSpire
12.3 ALL I WANT TO DO IS SEND AN EMAIL AND MAKE SOME MONEY
I have to admit, it is getting tough even for the Good Guys to get email through the spam blockers. We introduce Spam and spam blockers her, but see the next chapter for more detail. You will quickly note from the following that almost everyone knowingly or unknowingly violates some aspect of the spam guidelines. For example, look at one of my advertising programs: BuzzBee Advertising email guidelines:
BUZZ BEE MAILER
To keep emails from bouncing, please cloak your URL with a service like tinyURL.com or lil-URL.com. The reason for this is many of the URLs being promoted are often BLACKLISTED by many ISPs. Please comply with this request. We take SPAM very seriously, if we receive a complaint, we will follow through, and the member whom is spamming will be deleted and banned permanently. No HTML please. No adult, offensive or illegal ads
THE SPAM HUNTER 1.0 PROGRAM
Copy and paste a mail you would normally send out on other sites. You will notice under the subject and the body that it will tell you words or phrases in your mail that should not be there. These are words that you need to change to keep mails getting through. Note: after you add your mail just click outside the edit box to put the spam hunter to work. You will not see the send button until your mail is free of spam words and phrases and you click outside the text box. Yes it is a bit more work but when you compare the numbers you will see far more clicks and that means more mails getting through. TIP: Keep It Short And Sweet. When you click your mouse outside the edit boxes the hunter goes to work. The Following are spam words you are not to use if we find you are trying to get around it by adding dots and dashes we will delete your mail and risk losing your account.
161
INTERNET USERS HANDBOOK
You are not to discuss ANYTHING to do with making money in your mails. Leave that to the site to sell for you. Your job is simply to get people to click your links. Buzz Bee See Appendix B for words that are not to be used in your headlines if you want to avoid the spam blockers
12.4 FIGHTING SPAM
EMAIL SERVICE PROVIDERS
Starting out on the Internet during the late 1970s, I used MSN and Hotmail email accounts. These accounts became too restrictive because they limited the amount of mail and the size of the attachments. Now they have improved as server storage space became cheaper Recently, even with space, many email providers have become more selective with the types of accounts, or maybe better said the types of emails that they will take. They use various spam checkers and I suspect with the amount of spam emails floating around, the vendors are being overloaded with their own spam checkers junk. More and more sites have stopped taking Yahoo and other email accounts. Most are now recommending Gmail for all business. Perhaps the following will clarify Yahoo:
YAHOO SENDING MARKETING EMAIL INTO JUNK-FOLDER PURGATORY
Changes to Yahoo's internal rules determining whether an email is spam. Legitimate marketers began reporting in July and August that they were being shut out of the Yahoo inbox. For marketers whose mailing list is primarily Yahoo addresses, this is a major concern. Others have countered that Yahoo's ultimate client is the consumer. The wholesale blocking of legitimate marketers who refuse to pay to play, they contend, would prompt consumers to flee Yahoo to use more email friendly services. And that's not in Yahoo's best interest. But the fact remains that Yahoo is testing new delivery algorithms that have adversely affected legitimate email marketers. And once you are in junk-folder purgatory, it is difficult not only to get out but to eliminate the ability of marketers to purge those who legitimately want off their lists as well. The reason is that feedback loops that alert marketers to complaints made at the ISP level (i.e., those who click on the "spam" button rather than the unsubscribe link) don't function if the email is already being sent to the junk folder, making list hygiene issues difficult for the marketers. New Rules for email Marketers
TWITTER ENLISTS USERS TO HELP FIGHT SPAM
Twitter has added a "Report as spam" feature to its service in an effort to get help from its users in fighting spam, the company wrote in a blog post on Tuesday. "Folks can now help us conquer spam by calling our attention to a profile they find questionable," a company representative wrote. "Click the 'Report as spam' button under the Actions section of a
162
INTERNET USERS HANDBOOK
profile's sidebar and our Trust and Safety team will check it out to see what needs to be done." To stop users from simply using the spam feature as a weapon against others they don't like, Twitter said that "no automated action will be taken as a result of reporting a user as spam." That said, users who click the button would automatically have the profile blocked from following or replying to them. Twitter's decision to add a "Report as spam" button is just another way the company is trying to combat spam accounts. It's fighting an uphill battle. Out of my more than 12,000 followers, I've found several that do nothing but spam users. That said, I do believe that the "Report as spam" feature will be quite helpful in limiting that going forward. Of course, all that depends on our willingness to report others. I'm all for it. Are you? D Reisinger
CHECK YOUR GOOGLE DASHBOARD
Google, Yahoo and probably others know more about you than you even remember. Check it out for yourself Summary Of Data Stored With This Account. View and manage all the data stored with this account. Learn more. Security Note: We may sometimes ask you to verify your password, even if you have already signed in. This may happen more frequently for services involving your personal information. Sign in to Google Dashboard with your email: yourname @gmail.com
REDUCING SPAM
It seems like anybody, including your competitors, can report anyone for spam - by mistake or prank. You risk losing or tying up your email accounts and websites. Yahoo offers you a spam button to report those people who are not on your contact list that might find and contact you.
ONE OF MY FAVORITE WEBSITES BLOCKED BY TRIPOD
One of my favorite programs had their account closed by their Internet Service Provider (ISP) (TriPod) for alleged spam complaints. Although this client had been doing business with TriPod for years, the vendor showed no mercy and shut down their sites. As a result, the site owner had to change his ISP/Hosting companies that also meant new URLs for everyone. As an affiliate, I lost my momentum, time and money, especially since I was both paying for advertising and using free ads on probably 100 plus sites. I am still trying to catch up to avoid the wasted clicks for a 404 page or a route to the companys home page where the potential client is assigned to someone else.
12.5 WHAT HAPPENED TO SOCIAL ETIQUETTE?
I have already written of Facebook which for me was too social, the sharing of family albums, music trivia, etc. I was struck by Paying Social Business Networking! Why not! Although I had prior introductions such as Direct Matches and a few others unnamed, I was not bitten until I saw SWOM a social business network were I upgraded on Day 1 of sign up and have been paid continuously for 18 months as of this writing. Later introductions such as BIZOPPERS (Swoms sister site) ISMmagic , myNetworkingPro and APSense to our list that serve as hosts for our Internet Scams Anonymous (ISA) Group
163
INTERNET USERS HANDBOOK
Each of these has one form of payment or another for Likes, Q&As, referrals, etc. Each allows the creation of Groups by upgraded members for a particular programs or cause of action. Members can create posts and /or comments for sharing. I still see these sites as relationship building among members having a common interest of sharing their businesses online. The polarity of this concept continues to lead with new sites cropping up trying to learn and improve on the other. While it is nearly impossible to keep up with them all especially for those that seek to have their earning pay their monthly fees, it is this focus on monthly fees that drives members resort to any tactic that might produce a like, a point, or whatever for a question, a video offering or activity. All too often, these activities and like or vote sharing reduce the effectiveness of social Internet marketing because the questions, the videos and activities are NOT related to business or building relationships except in blocks of I will like you if you like me or please vote for my video. For many, there is little real reading or learning except to earn the point, the like or . One of my groups Swom Success with over 16,000 members used to be a hive of activities as to how to Swom, learn, connect and network with others. The tips are among the best for Swomming and networking, were praised and referred to others, but nowadays few even take the time to read them It is this concern to earn the monthly fee where many members lose their focus. Members have resorted to thinking small, tying to meet the monthly fee, rather than thinking big networking and marketing their business opportunities. The value of the relationship has been lost to many, or never understood, as does the real money which may be made from their bizop, product or offering. Some member focus so much on earning their monthly fee, that they spam us for votes, likes, watch my movie, and their FREE offer sites to make money online. Others are upgraded one month and then downgraded the next losing all benefit of the upgraded membership, and further reducing their marketing potential to other Upgraded members. They have truly lost the Big Picture and the Art of Thinking Big, Their mindset has changed! For others of us, the value remains; the networking and relationship building continues and improves, learning continues and business (as intended) is conducted. However, we still have to spend too much time policing our groups, posts etc., to try to retain the focus. Attempts to retain the purity of the concept and to eliminate the spam falls on deaf ears.
EXAMPLES SPAM: LACK OF SOCIAL ETIQUETTE OR RESPECT?
Groups are created by members for a particular program or cause of action. Other members should respect that groups program or cause and other than the typical hello, good morning, etc., posts and/or comment should related to the groups purpose and not introduce, share or SPAM the group with another program or cause.
164
INTERNET USERS HANDBOOK
In other words, stick to the subject, do not introduce another program, i.e. do not introduce program B in program As group. I recall a post to my Swom Success Group, a popular group for how to Swom where a lady recommended that the members go to a competing group following a different strategy. Spammers post their comment without regard to the originators or subject of the post. They may make the same post several times in the same thread of conversation
POST OR COMMENTS. SAME AS GROUPS, STICK TO THE SUBJECT Post Example 1:
From Steve Motley@facebook: WARNING: Facebook has been hacked by someone pretending to be Facebook Security saying that "your account is reported to have violated the policies that are considered annoying or insulting". It will ask for you to confirm your Contact details ... or it will disable your account. DO NOT 'CONFIRM', otherwise your account will be hacked. PLEASE pass this on....warn everyone!!! Comment: hi don like for you please also view my video for today ty have a gold day view @ swom.com/videos/14267 Remarks: Obviously this member is just looking for likes with total disregard for the Urgency or Nature of the Post from Steve
Post Example 2:
Welcome to SWOM and my SWOM SUCCESS GROUP, my pleasure to connect with you. Our sister site BIZOPPERS bizoppers.com/?r=36756, is a natural for you, and your Double Upgrade to Gold is our best value. FOCUS on your wall or PROFILE tab, Respond to all Posts and Use our Daily Plan for Success. See Income and FAQ tabs. Log into our group, Read and Copy the Tips to your Desktop, Introduce yourself and look for connections. Gold Members get paid for "Like(s). Enjoy Judith Comment: Good morning Mary, happy gold bizopping one like for sweet music for you, hope you visit my video tnx bizoppers.com/videos/17369 Remarks: Instead of Welcoming the new member Judith, this member ignored the member to whom the my post was made (Judith), but the comment was made to another commenter (Mary) and has nothing to do with the Subject Welcome
Post Example 3:
From Kathy Youla (Swom)> "Hi Dr Don, everyone is interested in the new Google plus project should perhaps read this first, there is a new phishing scam going round based on the new site blog.alertpay.com/2011/07/alertpay-scam-prevention-evenmore.html? Comment: Hello there, simply click on my picture and see my profile for the best money making program - do not wait click now and get the full details. Remarks: Need I say more? This one is not even addressed to anyone.
TAILOR AND LIMIT YOUR COMMENTS
It is always nice to have a newbie ask to me to go gold, when he or she is not gold themselves, Further, they havent paid attention to the member that they are posting too.
165
INTERNET USERS HANDBOOK
Some members repeated ask me to join the same program, which if that had read my profile, they would have seen I am already a member. The old offline tale of making 5 calls to make a sale does not work online. Online, it is easier just to call it Spam Some member repeats the same post several times or several different posts at the same time. Sort of overkill I would think. Monopolizing someones profile with your own interests does not help. Check a spammers profile and you wont see interaction; all you will see are posts after posts. Where is the relationship building?
12.6 FIRST LEGAL CASE FELONY - SPAM
VA Court Declares Spam Law Unconstitutional 2008 The Virginia Supreme Court Friday declared the state's anti-spam law unconstitutional, reversing the conviction and nine-year prison sentence of a Jeremy Jaynes, a man once considered to be one of the world's most active spammers. The court unanimously agreed with Jaynes argument that the law violates the First Amendment of the U.S. Constitution because it restricts non-commercial email as well as commercial messages. In rendering the courts opinion, Justice G. Steven Agee wrote Virginias anti-spam law is unconstitutionally overbroad on its face because it prohibits the anonymous transmission of all unsolicited bulk emails, including those containing political, religious or other speech protected by the First Amendment of the United States Constitution. Virginias Anti-Spam Act prohibits the sending of unsolicited bulk email by fraudulent means, such as changing the header or routing information to prevent recipients from contacting or determining the identity of the sender. According to prosecutors, Jaynes in 2003 sent tens of thousands of unsolicited emails with false headers and return-address information to AOL subscribers advertising dubious products such as a FedEx refund-claim product, a penny stock picker and an Internet history eraser. Police searching Jaynes home found discs with more than 176 email addresses and 1.3 billion user names on them, according to officials. They also reportedly found discs containing 107 email addresses that had been stolen by a former AOL employee. In November of 2004, Jaynes was convicted by a jury in Loudoun County Circuit Court on three counts of violating Virginias Anti-Spam Act, which was passed in 2003. The case was the nations first felony conviction for spamming. After Jaynes was sentenced in 2005 to nine years in jail, he appealed, claiming Virginias spam law is unconstitutional. DirectMag
166
INTERNET USERS HANDBOOK
13. ADVERTISE YOUR BUSINESS
Focus Chapter - it should be obvious to you that it means nothing to own a site yours or someone elses along with a hosting account for your site, if you do not advertise the site. No traffic equals any sales. This section will offer you some suggestions as to how and where you might place your site and get some business. Online advertising is attracting everyone, including big corporations who often offer their own affiliate program in order to get more business. The corporation advertises and the affiliate advertises for the corporation. Some ads offer your 186 complete sites for just a $20 bill. Other Affiliate sites claim they will do the advertising for you just sit back and collect your money. We have shown that affiliates are competing with their site owners to get a piece of the pie, and Affiliates are competing with other affiliates to sell the same sites; often using the same canned email headlines. Again, this section will offer you some suggestions as to how and where you might place your site and get some business. We cover various categories of advertising methods, since what works today, but may not work tomorrow. You may be limited to your budget, so see what free resources are available to you. Besides, you should take advantage of several marketing methods to get your message out. If something isnt working for you, then investigate the alternatives. Do an online search and see what others are doing using the same method; otherwise drop it. There is plenty of free advice online (usually linked to sites of their choice to make their point.) Oh yes, we have already established that online advertising is not Scam Proof. One of the best tools is Pay-Per-click/SEO advertising. It is not free and be sure to read the potential scams risk.
13.1 ONLINE ADVERTISING
The term online advertising is simply a term that relates to advertising online, or advertising over the Internet. In practice, online advertising is about getting your website in front of the people who are interested in your product or service. All you have to do is find the best terms and phrases that people search for who would like to purchase exactly your goods and services. If you can do this then your online advertising will be successful, however, if you select the terms and phrases that do not relate to the goods you are selling then your keyword based online advertising efforts will likely fail. It really is as simple as that. In fact more small business owners are using online advertising to market their goods and services to their target audience testing different keywords to specific pages of their website in an attempt to get more leads from their online advertising campaigns. And guess what? Yes-small business people are finding out that without a doubt advertising online is the most economical way to market their goods or services. You do not need to be a rocket scientist to use online advertising programs like Google Adwords or Yahoo Marketing. What you do need is patience testing keywords and logic when it comes to the message you list on the search engine and on the page that prospective buyers come to.
167
INTERNET USERS HANDBOOK
HOW CAN ONLINE ADVERTISING HELP MY SMALL BUSINESS?
Online advertising is so flexible that even small businesses can afford to look into advertising online. Where else can you track leads per advertising keyword? Where else can you track the cost per lead? Where else can you track the dollar cost per sale? Only online advertising allows you to select the keywords for your online advertising campaign and track the effectiveness of each keyword in terms of sales and revenues. This is the ultimate power of online advertising. You wonder why Google has become a powerhouse in keyword based online advertising.
WHY DO I WANT TO USE ADVERTISING ONLINE FOR MY WEB SITE?
First off the traffic to search engines is becoming more valuable - how can we say such a thing? Well in the latest quarterly earnings from Google it is stated: Aggregate paid clicks, which include clicks related to ads served on Google sites and the sites of our AdSense partners, increased approximately 17% over the first quarter of 2008 and increased approximately 3% over the fourth quarter of 2008. A 17 percent increase in paid clicks over last year is significant considering that surfers are aware of the differences between sponsored areas and non-sponsored areas in Google's search results page. Having your web site advertised on a search engine is important when you know recent findings on the habits of search engine users. Researchers at Pennsylvania State University found that 80% of users typically visit only the first three results from a search query. 54% of the users views only one page of results in each keyword search 19% of the users view the second page of search engine results, and less than10% looked at the third page of search engine results.
HOW CAN WE BE SURE THAT ONLINE ADVERTISING WORKS?
According to market research sources, search engines outperform all other online advertising media in driving visitors to web sites. Moreover, consumers are five times more likely to purchase products after seeing search listings versus banner advertising. In fact, statistics show the following: 77% of Internet users employ search engines more frequently than any other online advertising media, surpassing banner ads, Web links, and email links as the leading tool for discovering information about a product or service. 84% of Internet users who are online four or more hours each day reported they use search engines frequently to discover Web sites and find products or services. 55% of Internet users are more likely to purchase online after seeing search listings versus 9% for banner advertising.
13.2 ADVERTISING AIDA
A powerful ad is one of the most important aspects of your success. The secret to a successful ad is your HEADLINE. You only have a split second to grab your targets attention. Your potential customer will most likely scan the ads and only read one if it catches their attention. Write your ads with passion, excitement, and benefits. Use This Powerful Approach When Creating Your Ad Copy - AIDA A Attention Grab your targets attention I Interest Create curiosity
168
INTERNET USERS HANDBOOK
D Detail Provide details A Action Call for action Create an urgency to act now. Creating a successful ad will take a great deal of time and effort. You'll need to write it and re-write it over and over again before you come up with a great ad. We all know the importance of a powerful headline. However, writing a great headline is not as easy as it sounds. An effective headline will literally force your potential customers to learn more. It will instantly ignite a certain emotion and intrigue them to read on. In order to write an effective headline, you must learn how to use specific words to achieve a specific reaction.
THE HEADLINE
Before writing your headline, you must first learn a little bit about the basic human motivators. According to psychologist Abraham Maslow, human behavior is always the result of one or more of five basic needs. He listed these needs in a sequence that he refers to as "the hierarchy of human needs." He believes that until a less important need is met; there will not be any desire to pursue a more important need. Below are the five human motivators, beginning with the basic needs and continuing to the most important needs. Physiological Basic human needs include hunger, thirst, shelter, clothing and sex. Human need for physical, emotional and financial security. Human need for love, affection, companionship and acceptance. Human need for achievement, recognition, attention and respect. Human need to reach their full potential.
Safety (Security) Social (Affiliation)
Esteem (Self Esteem)
Self-actualization
When you are aware of the basic human needs, you can incorporate these needs into your writing. A great headline will appeal to your potential customers' emotions. You must feel their needs, wants and desires and write your headlines with passion and emotion. When writing your headlines, keep in mind, you only have a few seconds to grab your potential customers' attention. If your headline doesn't immediately catch their attention, they'll simply move on and never return. Below are several different formulas used by professional copywriters to write compelling headlines?
13.3 HOW TO CREATE NO-SPAM HEADLINES
Other than the message above of using How To in your headlines, several searches in different combinations, nobody has come up with an answer for you. Many identify spam, other talk about forums, articles, etc., but no one seems to have the No Spam Headlines Solution. Some sell or provide
169
INTERNET USERS HANDBOOK
free Spam software. They tell us what not to do, tell us how to do how to eliminate Spam, but they dont tell us how to be creative without using Spam. This reminds me of being in business; when managers come to you with their problems, but they dont offer a recommended course of action or alternatives to solve the problem. Therefore, our challenge remains, how to Write Headlines and Advertisements without using Spam that will still motivate the reader to click. Maybe someone that joins our group will have an answer for us all.
13.4 HOW TO ADVERTISE WITHOUT SPAM
WHERE DID YOU GET YOUR EMAIL ADDRESSES?
Did you buy an email address list from a reputable company that consumers opt-in to receive such mailings? Did you collect your email addresses from newsletter subscribers and tell them up front they may receive special offers from time to time by signing up? Know the answer to these questions before beginning your email ad campaign. If you went to a message board covering your type of business and grabbed the first 1,000 email addresses, you see for your email ad campaign, you are a spammer.
KNOW WHAT TO LOOK FOR WITHIN YOUR OWN MESSAGE.
People who have asked for your mailings may not be getting them because spam blocker software and email filters are set so high that they sometimes catch mail you really do want to receive. For someone about to embark on an email ad campaign, you can reduce your chances of your message getting discarded by these automations by using these quick tips:
AVOID CAPS
Just because you think your message will be loud and clear in all caps doesn't mean it will actually make it to your recipient. Spam blocker software and email filters are designed to look for capital letters and will immediately flush your email.
AVOID EXCESSIVE EXCLAMATION MARKS.
Your message is powerful!!!!!! What could say that better than a few dozen exclamation points at the end of your sentences? This is another alarm signal for spam blocker software and email filters. Exclamation points can't prove a point any better than simple text...especially when those exclamation points get your message trashed before it even reaches your intended audience.
AVOID REPEATING THE SAME WORDS AND PHRASES OVER AND OVER.
In advertising, you're taught to use a subtle message while driving home points within your copy. You can do this without being repetitive. Many people Buy Diet Pills and when they run out they Buy Diet Pills and what could be better than if you Buy Diet Pills. This is another tip off to spam and spam blocker software and email filters will catch it. Send your message to yourself using spam blocker software. If your own spam blocker software catches the email, chances are it's going to be caught by someone else's. Play around with your message until you receive it without your spam blocker software or email filter catching it. When it arrives in your inbox without being caught; you are ready for your email ad campaign to begin. Advertising-About
170
INTERNET USERS HANDBOOK
BANNER ADS
Affiliate posts and advertisement for your business in exchange for compensation when the banner ad produces a desired effect such as generating website traffic or generating a sale. The terms of these agreements are determined beforehand and are generally based on a scale of pay per impression, pay per click or pay per sale or lead. Now that you understand what banner ads are, it is also important to understand how they can be overused and appear to be spam. Judiciously placing your banner ad on a few websites which are likely to attract an audience similar to your target audience is smart marketing, placing your banner ad on any website which will display the ad regardless of the target audience can be construed as spam. Internet users who feel as though your banner ads are everywhere they turn will not likely take your business seriously and are not likely to purchase products or services from you because of your banner ads.
EMAIL CAMPAIGNS
Email campaigns can also be very useful tools in the industry of Internet marketing. These campaigns may involve sending periodic e-newsletters filled with information as well as advertisements, short, informative email courses or emails offering discounts on products and services. Loyal customers who opt into your email list will likely not view these emails as spam and may purchase additional products and services from your business as a result of this marketing strategy. Additionally, potential customers who have specifically requested additional information on your products and services will also find this type of marketing to be useful. However, email recipients who did not request information are likely to view your emails as spam. Harvesting email addresses in a deceptive manner and using these addresses to send out mass emails will likely always be considered to be spam.
MESSAGE BOARDS
Finally, message boards provide an excellent opportunity for business owners to obtain some free advertising where it will be noticed by members of the target audience. If the products and services you offer appeal to a specific niche, it is worthwhile to join message boards and online forums related to your industry of choice. Here you will find a large population of Internet users who may have an interest in your products. You might consider including a link to your business in your signature or posting the link when it is applicable to the conversation. However, care should be taken to carefully review the message board guidelines to ensure you are not doing anything inappropriate. This technique is smart marketing. Conversely, replying to every message with a link to your website when it is not relevant to the conversation is likely to be construed as spam by other members. Once they begin to view your posts as spam, they are not likely to visit your website via the links you post. Howtoadvertsizewithoutspam
171
INTERNET USERS HANDBOOK
13.5 A SIMPLE GUIDE TO INTERNET ADVERTISING
There are many ways to advertise on the Internet. Most of the effective advertising methods are simple and easy to do. Here is a quick guide to Internet advertising.
START WITH A BASIC MARKETING PLAN
If online marketing was a basketball team, here would be my starting five. Natural Search Engine Optimization Pay Per Click Media Campaigns Newsletter Promotions
ONLINE ADVERTISING WITH SEARCH ENGINE OPTIMIZATION
Search engines are the number one way to drive traffic to a website. There are a few components to having a site rank well in search engines.
BUILD A SITE THAT THE CRAWLERS CAN EASILY NAVIGATE.
Make sure each page has a unique title tag, description tag and lots of well-written unique content.
BUILD ONE-WAY LINKS FROM TOPICAL SITES.
Now there are entire books written on this subject, but most of it is overdone. Stick to the basics of a site that can easily be crawled, lots of good content, and links from topical sites and you'll do fine.
PAY PER CLICK INTERNET ADVERTISING
Pay per click programs from Google and Yahoo where bids are placed on terms that show up in the search results. Depending on your budget there are a few options. You can hire a firm to do it or do it yourself. The key to a good pay per click program is to understand your conversion rates. Tune your pay per click program by bidding on words that convert and lower bids or drop them all together on terms that do not convert.
PURCHASING MEDIA
Similar to pay per click options the key is to understand your conversion rate. Most media is purchased on a CPM basis. That's the cost per 1000 impression of your ad Google offers a contextual advertising network and depending on your budget there are many full service options available. Media for performance-based campaigns may be complex, but just be sure to make more than you spend.
EMAIL MARKETING
Collect email addresses from your users to keep them up to date on specials and other options. Email marketing is still one of the most cost effective and best ways to keep in contact with customers.
PROMOTIONS
I have one friend that makes his entire living off of an email list that he gives great Promotions of new products and services. It is sort of an early adopters program. Until I saw this, I never knew how effective they could be. Offer something unique that your audience wants regularly on your site. Hubpages
172
INTERNET USERS HANDBOOK
13.6 TESTING AND TRACKING YOUR STRATEGIES
Developing and implementing a strategic marketing plan is an essential part of your success. However, unless you're testing and tracking your strategies, you may be losing a great deal of time and money. You can dramatically increase your sales simply by taking the time to test and track your results. Not only will it help you to determine what's working and what's not, but it will also enable you to focus your efforts on the strategies that produce results. When testing your marketing strategies, keep in mind, a strategy that produces results for one person may not produce results for you. There is no 'set in stone' strategy that works for everyone. You must develop your own style and technique and test your results to determine what works for you. Below are some ads tracking resources to assist you in your testing and tracking endeavors.
AD TRACKING CGI SCRIPTS
LnkinLite If you're looking for a simple way to track clickthroughs, then LnkinLite may be your answer. This free script will enable you to easily keep track of the number of clicks a specific link receives. Instead of using your standard link within your advertising, you can use a link created by this script. It will track the number of clickthroughs and instantly redirect your visitors to your URL. Willmaster's ProLinkz This powerful script is a link creator, tracker, disguiser and manager all in one. It will enable you to create uniquely coded links that redirect to any URL you specify and count all hits and referrers. Cost $45.00 AdTrackZ This script will enable you to set up an entire ad tracking campaign including statistical reports for referring URLs, what browsers your visitors have installed, what operating systems your visitors are using and much more. Cost - $47.00
AD TRACKING SERVICES
LinkCounter A free service that tracks the clickthrough rates of your links. In addition to tracking your links, LinkCounter hides the URL of the link destination. This will prevent users from removing or changing your affiliate ID when visiting an affiliate site through your link. HyperTracker The PRO version of HyperTracker contains a number of advanced features including: unlimited advertising campaigns, tracking of sales and actions, special scripts that let you promote your own website address in your campaigns and much more. Adminder An online tracking system that will enable you to track an entire advertising campaign. It will enable you to see how many visitors were generated by each of your ads, keep track of sales that were generated by each ad and calculates the cost-per-click, cost-per-sale, and click-tosale ratios for each ad
173
INTERNET USERS HANDBOOK
If you'd rather not use any of the products and services listed above, you can use some alternative methods. Below is some example tracking methods you can use to track your response rates:
URL (Universal Resource Locator)
You can track your ads simply by adding some special coding to your URL. To code your URL, add a question mark followed by a special tracking code to the end of your web address. Your coded link will still open your web page. Your code should look something like this: http://www.yourdomain.com/?ad1 The text after the question mark should identify a specific ad you can code it however, you would like. To view your results, you'll need to look at your log files. Your code will be displayed within your log files beside your URL.
EMAIL
Track your email responses to specific ads by using the email subject. Select a specific word to be placed within the email subject for each ad. Although you can request that a certain word be placed within the email subject, many times it won't be supplied. To avoid this problem, you can create a special email link that will automatically fill in the subject when clicked on. Your link should look something like this: mailto:you@yourdomain.com?subject=ad1 Testing and tracking your strategies is an essential part of doing business. By concentrating your efforts on strategies that produce results, you can not only increase your sales, but you'll also save yourself a great deal of time and money. WebSourceNet TIP: AIDA is a standard (Advertising 101) for most advertising, but unfortunately, most of the headlines created will not pass through Scam/Spam Filters. What to do? Most Scam/Spam Experts Will Advise To Avoid the Use Of Scamp/Spam Words, So Our Challenge Is To Create Headlines And Ads That Motivate The Viewer To Click And Go To The Website And Let The Website Sell Their Program, Guarantees, etc.
13.7 SEARCH ENGINE OPTIMIZATION (SEO)
We cannot make you a SEO expert within these few pages, but we can give you a good beginning, things to watch for and typical SEO Scams. Search engines are considered the prime source of traffic for any website. The higher your search engine ranking will be, higher will be the number of visitors to your website, thereby leading to significant increase in sales, apart from gaining strong web presence as well as brand recognition. Search engine ranking, otherwise known as search engine placement, simply refers to the creation of a website in such a way that it ranks as high as possible in the given search engines such as Google, Yahoo, and MSN. In other words, search engine ranking is a yardstick to determine the online promotional
174
INTERNET USERS HANDBOOK
success of a web page or website. A high search engine ranking is regarded as a more effective advertising tool than paid advertising. Among the plethora of strategies adopted by SEO specialists to ensure top search engine ranking are preparation of pertinent content, selection of the most appropriate keyword or key phrases for your product or service, implementation of meta tags, HTML validation and link building. Nowadays, a lot of SEO specialists are in the scenario to offer search engine ranking services. Many of them guarantee top search engine rankings. However, search engine ranking proves effective and beneficial only when professional and knowledgeable SEO personnel do it. Before you approach a SEO firm or SEO specialist, make a thorough analysis regarding its professionalism and Ethics. Be sure they prepare content-rich information and adopt the most sophisticated SEO tools to optimize your website. There are certain SEO firms that offer search engine ranking services for low rates. Hence, before choosing such firms, their quality of service must be checked. Further, make sure that the SEO firm that you have chosen solely engage in SEOrelated works, and does not treat it as a secondary.
INCREASE YOUR SEO RANKING WITH KEYWORDS RICH PAGE CONTENT
It is the fervent wish of every website owner that his or her website attains a position of prominence with regard to search engine rankings. It is easier said than done and this is why so many website owners are giving up with search engine optimization and turning to SEO consultant to increase their search engine rankings.
MAIN ASPECTS OF SEO IS CREATING KEYWORDS RICH PAGE CONTENT.
Search engine optimization with keywords rich page content involve rearrangement or addition of keyword rich web content to specific location on your web site. You should start by positioning the keywords and a good place where to start is the page title, and at the very least, in the first paragraphs. It pays to have the keyword appearing frequently on your page body. Keeping your keywords frequency between three and five percent is recommended. More than that is considered ''Spamming'' By the search engines. Try to find targeted keyword phrases that your competitors are missing. Your competitors when searching for the top competitive search terms often overlook combinations of two and three word phrases. Doing a proper keyword research is a must! Make sure to spread your main keywords and keywords phrases in a natural manner. Also, using sub-topics will effectively make the keywords work well together. Making use of keyword rich content on your site will increase both your relevancy and search engine rankings leading to more traffic that convert in more sales.
13.8 BUILDING YOUR KEYWORD LISTS
The first step in search engine marketing is determining the right keywords for your business. These are the words and phrases your potential customers type in to search engines when theyre looking for the products you sell. Theyre also the first thing search engines look for when determining the most relevant web pages to list in search results.
175
INTERNET USERS HANDBOOK
Building an accurate keyword list is critical to the success of your search engine marketing efforts. Successful search engine marketers develop their keyword list first, and then build a single, highly relevant web page for each keyword phrase.
TYPES OF KEYWORDS
Before you being to create your keyword list, its helpful to understand the different types of keywords people use in search engines:
GENERIC KEYWORDS
The most basic words used to describe a product or service category, such as digital camera and accountant.
DESCRIPTIVE KEYWORD PHRASES
Generic keywords modified with adjectives to narrow their focus, such as two mega-pixel digital camera and Seattle accountant.
TARGETED KEYWORDS
Keywords that apply to one and only one product or service, such as Coolpix 2100 and tax accountant. As you build your keyword list, it will be important to brainstorm all three types of keywords, as each one has a unique purpose. Generally speaking, home pages are optimized for generic keywords, product category web pages are optimized for descriptive keywords, and individual product pages are optimized for targeted keywords.
BRAINSTORM
To start the keyword selection process, sit down with other people in your company and try to think of a few words and phrases that best describe your site, company, and products. Ask each person to come up with at least 50 keywords the more the better. If youre a one-person company, then ask your friends and relatives for help. You may also want to look at your internal search data for keyword ideas. If your web site has internal search functionality, mine that data to uncover phrases your customers use to describe the products or services they are looking for. Most importantly, ask your customers what terms they use when searching for specific products. Getting this feedback from them is crucial, as they will probably have a different, and possibly more accurate, idea of what keywords your potential customers are using.
GET HELP ONLINE
Also take advantage of free keyword-enhancement tools online. One of the most popular applications available is Yahoo! Search Marketings (formerly Overture) Keyword Selector Tool. The tool works as follows: enter your sites main keywords and phrases into the system. You then receive a list of related search phrases in the order of popularity. The list will tell you how exactly how many people searched on each particular phrase in one month, giving you a clearer idea of what words work and what dont.
176
INTERNET USERS HANDBOOK
You can take this process an extra step by incorporating fee-based tools like Wordtracker by Rivergold Associates Ltd. Wordtracker works in a similar fashion to Yahoo! Search Marketings Keyword Selector Tool, but offers additional options at prices starting at around $7 per day.
BE DESCRIPTIVE
Once you have your initial keyword list in place; expand on it as much as possible by adding descriptive and specific terms to each phrase. Including colors, geography, or location, plus brand names and model numbers will enable customers to find product pages more easily when they conduct searches. The more detail you can provide, the better results you will achieve.
BE RELEVANT
One of the most common mistakes people make in brainstorming keywords is including non-relevant keywords. Words such as weight loss and Brittany Spears may be highly searched, but if they are not relevant to your business, you should not include them in your list. In fact, you will be penalized for keyword stuffing by using these words.
CHECK YOUR WORK
Once you have your list in place, ask yourself the following questions: Are the keywords and phrases relevant to my business? Have I brainstormed all of the descriptive terms? Are the page-specific keywords relevant to those pages? Are there any pages that are more suitable for a particular phrase than others? Is there another way to phrase this term? Once youve verified that these words match your marketing objectives and are the right keywords to target, you need to review the following to make sure that the keywords are actually supported: Page Titles Product Titles Product Description Page Content Remember, the keyword selection process is the most critical step in the optimization process, so doing your homework up front can go a long way to ensuring your success. Take advantage of your peers, customers, and online tools at your disposal to make sure youre not forgetting any critical terms. It is also important to update your list often, especially when adding new products or services to your site.
ADDITIONAL KEYWORDS RESOURCES
Steps to creating a Keywords List Google Microsoft Advertising Intelligence Add- in for Microsoft Excel and costs a minimum of $5.00 to sign up Market Samurai a top of the line paid Keyword Tool
13.9 WHY SEARCH ONLINE ADVERTISING IS VALUABLE
Search online advertising brings keyword based search traffic to your door. Keyword based search brings exactly your targeted audience to your ad message. Technology experts predict that more and more people will access the Internet at a higher speed than ever before and this added speed makes
177
INTERNET USERS HANDBOOK
getting audio or video news and information simple and fast. Keyword based video advertising will get increasingly popular as the cost of broadcasting that video over the Internet falls and as more and more people can see that video clearly (as a result of increasing access speeds). How neat would that be if we could see a video of the product or service before we actually bought it, or see the people behind the company that sell us that "catalytic converter". Online advertising via video feeds to your cell phone from live or recorded messages are only a moment away. Technology is moving so fast even the online advertising industry can barely come up with applications that meet the changing (and better) Internet technologies. The future of online advertising looks bright and very exciting to be sure. It is up to you to make sure you understand the changes that are taking place and up to you to become part of the online advertising boom.
MAKE ONLINE ADVERTISING EASY TO UNDERSTAND?
Online advertising is made easy by the use of search engines. Put it this way, if you can read then you can get your product or service on any of the big three search engines in less than ten minutes. All you have to do is open an account at Google or Yahoo or MSN and away you go. It does not get any easier than that. They have experts who help you every step of the way, and frankly, their advertising programs are so user friendly it is incredible. Online advertising made easy. OnlineAdvertising
13.10 COSTLY SEARCH ENGINE OPTIMIZATION MISTAKES
As website owners you already know the importance of traffic. Getting a steady flow of visitors to your site is the only thing that really matters. If you can't generate traffic your online business is destined to fail. You need traffic to make sales! The key for generating targeted traffic is the search engine. Search engine optimization is by far the most cost effective method of advertising your website. Unfortunately, many Internet marketers do not understand search engine optimization, which leads to targeted traffic that convert in sales. They are making terrible mistakes when optimizing their websites. Try To Avoid The Following Common Search Engine Optimization Mistakes:
CHOOSING THE WRONG KEYWORDS:
It is so important that your site target the right audience. Select the right keywords and your audience will find you. Use the wrong keywords and you will get poor traffic, but most importantly, no sales!
KEYWORDS SPAMMING
(Repeating the same keywords): Never use keywords spamming or stacking. The search engines will downgrade and penalize your website for doing this. Instead, use keywords rich content on your page.
USING A FREE DOMAIN NAME OR WEB HOSTING SERVICE:
If you are serious about doing business online you need a real domain name with a real hosting company. In most case the search engines will not index the content from these free hosts. If you want to make money online you need to spend some!
PUTTING HIDDEN TEXT TO INCREASE RELEVANCY:
Putting on-page hidden text will not help you to achieve a better ranking. The search engine robot will detect the hidden text and penalize your site for using unethical SEO techniques.
178
INTERNET USERS HANDBOOK
USING UNRELATED KEYWORDS:
Using unrelated keywords that have nothing to do with your website is considered spam by the search engines and may cause your site to be removed from the search engine index. This is just a few of the unethical search engine optimization techniques that you should not give a try. Using these methods will not do any good and you are taking the risk of getting your site banned from the major search engines and directories. AffordableSEO
13.11 HOW WEB ADVERTISING WORKS
INTRODUCTION
Two different things are happening right now: More and more sites are asking you to pay a fee to subscribe to all or part of the Web site. Advertising is becoming more and more "in your face." There are now pop-up ads, ads that play music and sound tracks, ads that swim across the screen, and so... The second trend is true of nearly all commercial Web sites. There are many new forms of Web advertising, and they are more and more obvious. Many Web users have questions about all of these new ad types. For example: Why Do Web Sites Have So Many Ads Now? Why Do Web Sites Allow Pop-Up Ads That Open New Windows? (People Hate Closing Them All.) Why Do Web Sites Allow the Floating Ads That Cover The Content So I Cannot Read It? How Can I Make All These Ads Go Away?
IN THE BEGINNING: BANNER ADS
When the Web first started being a "commercial endeavor" around 1997 or so, thousands of new sites were born and billions of dollars in venture capital flowed into them. The sites divided into two broad categories:
E-COMMERCE SITES
E-commerce sites - sell things. E-commerce sites make their money from the products they sell, just as a brick-and-mortar store does.
CONTENT SITES
Content sites -create or collect content (words, pictures, video, etc.) for readers to look at. Content Web sites make their money primarily from advertising, like TV stations, radio stations and newspapers. Banner ads the ads you see at the top of almost all Web pages today. In 1998 or so, banner advertising was a lucrative business. Popular sites like Yahoo could charge $30, $50, even $100 per thousand impressions to run banner ads on their pages. These advertising rates provided fuel for much of the venture capital boom on the Web.
EFFECTIVENESS OF BANNER ADS
At some point, advertisers concluded that banner ads were not as effective as full-page magazine ads or 30-second TV commercials. At the same time, there was an incredible glut of advertising space -thousands of sites had a million or more page impressions available per month...
179
INTERNET USERS HANDBOOK
The economic principle of "supply and demand" works the same way on the Web as it does everywhere else, so the rates paid for banner advertising began to plummet. Today, if you shop around, you can buy banner ads from thousands of Web sites or brokers for 50 cents or so per thousand impressions -which are exactly what they are worth to a person who is trying to sell something with banner ads using a direct sales model. But for most other Web sites, there is very little money to be made from banner ads. In order to charge more than 50 cents per thousand impressions, Web sites have to offer ads that either: Have a lot more branding power or Get a much higher click-through rate
NEW ADVERTISING FORMATS AND EXPERIMENTS SIDEBAR ADS
A sidebar ad (also known as a skyscraper ad) is similar to a banner ad, but it is vertically oriented rather than horizontally. Because it is vertical, the height of a sidebar ad can often reach 600 pixels or more, and sidebars are generally 120 pixels wide. A sidebar ad has more impact than a banner ad for at least two reasons: A tall sidebar ad is two to three times larger than a banner ad. You cannot scroll a sidebar ad off the screen like you can a banner ad. With a banner ad, you can scroll just 60 pixels down and the ad is gone. With a sidebar ad, the ad is with you much longer. Because of this increased impact, sidebar ads have higher branding power and a higher click-through rate. A typical sidebar ad has a click-through rate of 1 percent (10 clicks per 1,000 impressions), or about two to three times that of a banner ad Advertisers will typically pay $1.00 to $1.50 per 1,000 run-ofsite impressions for sidebar ad placement. Advertisers pay more for targeted sidebar ads, just like they do with targeted banner ads.
VARIED SHAPES AND SIZES
Banner ads and sidebar ads have standard sizes. But in the last year or two people have tried all different sizes and placements. Here are three examples: Sites arent paid much for these smaller ads, because generally the click-through rates are low. But by putting 10 ads on the page, it can add up to $2 per 1,000 page impressions.
POP-UP AND POP-UNDER
A pop-up ad is an ad that "pops up" in its own window when you go to a page. It obscures the Web page that you are trying to read, so you have to close the window or move it out of the way. Pop-under ads are similar, but place themselves under the content you are trying o read and are therefore less intrusive.
Pop-up and pop-under ads annoy many users because they clutter up the desktop and take time to close. However, they are much more effective than banner ads. Whereas a banner ad might get two to five clicks per 1,000 impressions, a pop-up ad might average 30 clicks.
180
INTERNET USERS HANDBOOK
Therefore, advertisers are willing to pay more for pop-up and pop-under ads. Typically, a pop-up ad will pay the Web site four to 10 times more than a banner ad that is why you see so many pop-up ads on the Web today.
FLOATING ADS
If you have ever been to a Web site that uses them, you know what "floating ads" are. These are ads that appear when you first go to a Web page, and they "float" or "fly" over the page for anywhere from five to 30 seconds. While they are on the screen, they obscure your view of the page you are trying to read, and they often block mouse input as well. Floating ads are appearing more and more frequently for several reasons: They definitely get the viewer's attention. They are animated. Many now have sound. Like TV ads, they "interrupt the program" and force you to watch them. They can take up the entire screen. From a branding standpoint, they are much more powerful than something like a banner ad or a sidebar ad they cannot be ignored. They have a high clickthrough rate, averaging about 3 percent (meaning that 30 people will click through for every 1,000 impressions of a floating ad). The high click-through rate, as well as the greater branding power, means that advertisers will pay a lot more for a floating ad -- anywhere from $3 to $30 per 1,000 impressions depending on the advertiser and the ad Because they can pay a lot of money, Web sites are willing to run floating ads. The only problem with floating ads is that they annoy people. Some people become infuriated by them, and will send death threats and three-page-long rants via email. That is why you do not yet see them everywhere. The annoyance problem points out something interesting about advertising, however. When pop-up ads first appeared, they bothered lots of people and you did not see them on very many sites. After a while, people got used to them and stopped complaining, and now pop-up ads can be found on tons of sites. As people get used to floating ads, they will become more common.
WHY YOU SEE SO MANY ADS ON WEB SITES TODAY? IT IS EITHER: LOTS OF ADS
Switch over to subscriptions (hope you can get 50,000 people to subscribe -- no easy task).
OR GO OUT OF BUSINESS
A Web site is a business, and it must cover its expenses to survive. HowStuffWorks-Bain
13.12 IS THE ONLINE ADVERTISING INDUSTRY SHRINKING?
Growth in online advertising for the first time will shrink to single-digits in 2009, according to eMarketer - yes it is still growing despite our worldwide recession. Search engine keyword based marketing, like Google AdWords, is still growing at double digit growth rates. Look at the pricing revolution online advertising news article for April. The fact remains that there may be a big pricing revolution in advertising online; however when you are focused on search engine online advertising then growth is fine.
181
INTERNET USERS HANDBOOK
More and more business people understand the power and simplicity of search engine marketing and how online advertising benefits their business (in terms of sales). So yes the US economy is shrinking, ever so slightly, however online advertising (specifically search) continues to grow. The world of online advertising can be divided into a several different advertising options. These options are not exclusively the only areas from which to choose, however they represent the most popular areas within the online advertising menu.
SEARCH ENGINE ADVERTISING: 50%
More than 50% of the total spent last year in online advertising. This relates to keyword based search engine optimization and paid advertising via pay per click campaigns. The three biggest sources of this type of advertising are Google, Yahoo, and MSN. There are plenty of additional smaller online search advertising options but these three are the best of the best and each one has a pay per click advertising interface that is simple to use. Just in case you are wondering the big three search engines represent 98% of the entire search advertising market. Get it correct with the big three search engines and you are getting it right with 98% of your keyword based search audience. The great thing about search engines is that they make it so easy to purchase traffic. In fact online advertising has now become as easy as click, setup, and pay. All you need to do is select the appropriate keyword(s) for your service offerings, select the geographic region you want to represent, and away you go. Note that search advertising is paid per visitor so if your ad is not clicked on you pay nothing. How would you like to buy a billboard on the road that you only pay when someone calls you? Experts refer to this type of online advertising as an outstanding deal. Even Google will give you free credit card processing for all the goods you sell online providing you are purchasing traffic from them and providing your ROI (return on investment) is less than or equal to 1,000 percent. Even Google thinks you should be able to make ten times your online advertising spend in total revenues. That says something right there.
DISPLAY ADS: 21%
21% of the total online advertising last year and falling fast. Banner or contextual advertising is not popular and is not working; even at these cheap costs per thousand impression rates. Here you rent space on a web site and if you get many visitors to your site great since you pay for the space and not for the visitors. This is not the best way to advertise, but there are plenty of places to get CPM deals in the $0.60 or lower range so why not pay next to nothing and see what sticks.
CLASSIFIED ADVERTISING: 17%
17% of all spending last year or just over $4 billion dollars spent on classified advertising. So next time you say classifieds are not for your company or service offering you better think again. In terms of dollars spent last year classifieds came in at roughly one third of the amount spent on keyword based
182
INTERNET USERS HANDBOOK
search. Classified ads run at a cost per space and not for visitors directed to your website so again you are paying per thousand page impressions whether people click on your ad or not.
LEAD GENERATION: 6%
Lead generation 6% of all advertising spending last year, or over $1.4 billion dollars. It is interesting to see Google use lead generation in some cases since we all know Google is getting short end of the stick on their paid keyword based advertising (per click). How do we know that? Well if I am a company and I spend $1 to make $3 from traditional advertising (TV, radio, newspaper) and now I am spending money with Google to the tune of $1 for each $9 in revenues then it stands to reason that Google is getting the sorry end of the stick compared to the cost of traditional advertising. Some argue this is exactly why keyword based search advertising is destined to grow.
RICH MEDIA: 4%
4% of all spending last year or almost $1 billion dollars. This sort of relates to display ads, except that these ads are video targeted and most networks know that the targeting aspect alone will improve conversion rates. In advertising, the better the targeting, the higher value and the greater the advertising revenues. Could this be why Google bought YouTube for over $1.5 billion dollars?
EMAIL: 2%
Holding on at 2% of total online advertising last year. Hard to believe email advertising accounted for $500 million dollars in revenues last year. That is a lot of money spent on email advertising. eMarketer
13.13 LIST BUILDING
If you have been kicking around the net for a while; someone will always tell you the money is in the list. Great, but what if you have a 30,000 member downline, as I had with Vemma, but you have no access, you effectively have nothing, unless one of your downliners is real, a producer, a leader, and helps build you some income. For that matter, your sponsors can pull your downline and move them to another program. Later, we will discuss some list scams, guaranteed signup as such.
A BASIC GUIDE TO LIST BUILDING
Without the list, your Internet business is a non-entity. It is that simple. The lifeblood of online businesses such as network marketing or MLM and content-driven sites rely on their lists. In fact, every beginner and experienced Internet marketer by now is probably familiar with the mantra, 'the money is on the list.' This is why careful attention is required in order to build a listing that is relevant to a specific marketing campaign. Here is some essential information you need to know about list building:
WHAT, EXACTLY, IS A LIST?
It is simply a mailing list - a list of names and corresponding email addresses, each of which represents a potential customer, subscriber or recruit. Each time you have news, updated information, a fresh article or video or are promoting a new product; you will be using this list to send emails to.
183
INTERNET USERS HANDBOOK
HOW LISTS ARE BUILT
The most common way of building a list is through on-site invitations. Let us say you are promoting a weekly newsletter regarding pet care. Now a newsletter is useless if it does not have any readers, so your goal is to find as many subscribers as you can. To do this, you must create an invitation from your website through a signup tag. This invitation must contain all the necessary information that your subscriber will need to fully understand what exactly it is you are offering. The opt-in invitation should be specific to a particular product or service you are trying to promote. In this case, the tag should inform the recipient that it is an invitation to sign up for a weekly newsletter that will be sent through email. Something like, 'To receive more tips or articles on pet care, sign up for my free weekly newsletter. Once the recipient agrees to be part of your listing, you can then keep his email address in a database or a spreadsheet. You could use a program to help you manage and organize this listing so email addresses relevant to a particular product or service you have are easier to access.
THE IMPORTANCE OF EFFECTIVE LIST BUILDING
An effective list building effort should result to a quality list. A quality listing consists of individuals who belong to your target audience. If your website is about pet care, for more detail visit to www.mailinglist-gold.com then the quality audience for you is one that is composed of pet owners and pet lovers. Anyone who is uninterested in pets will not and should not be part of your list building efforts The goal here is simple - effective list building helps you filter a segment of the huge market out there that will not respond favorably to your campaigns. With a quality list, you are more likely to interact with an audience who is more likely to participate in your marketing efforts, for more detail visit to www.freelist-pro.com sign up for future offerings, become your recruits or referrals or even purchase from you.
OPTING IN
There is one very important thing you should remember about list building and that is permission. It is considered an unethical practice for a legitimate online business such as yours to include email addresses of people to your list when they did not agree to such an arrangement. Without an express permission from these people, your email messages, no matter how well intentioned, will be viewed as spam. Effective list building involves permission-based marketing which comes in the form of the opt-in listing. The opt-in list is simply a list of email addresses of people who agreed to a specific offer you made. Without this explicit expression of acceptance, you cannot and should not include these individuals in your list, no matter how tempting or valuable they are.
184
INTERNET USERS HANDBOOK
WHAT ARE THE BEST TECHNIQUES FOR MLM LIST BUILDING?
If you have ever tried to build an MLM list, you know how difficult it can be. There are quite literally dozens of excellent tools and techniques available for MLM list building and building an opt-in list for your MLM website. This article provides covers eight proven MLM list building techniques to create and expand a profitable opt-in list of qualified MLM prospects. For more details www.37-list-buildingsecrets.com MLM list building is similar to the human emotions of dating. If you start out on the wrong footing, you may ruin a potential rewarding relationship between you and the subscribers. On the other hand, if you provide valuable information to your list, you could look forward to building valuable and lasting relationships. When you start your MLM list building, do some due diligence and research on what your target prospects are looking for. If you already have a list, ask your prospects what kind of information or service they desire in a broadcast email. In its simplest form, list building a two-step process: the one-step is the act of capturing a potential customers name and email address and the second step is to use that information to create a relationship with that person. Notice I said create a relationship not to sell. I will get back to that in a minute. You want to use your list building process to collect the names and email addresses of as many people who have shown an interest in you and your business as possible. You want to put a list-building link (subscription form or something like it) in front of as many visitors as you possibly can. This will also show that you care about your customers and help build a long-term relationship. You might go one step further and search for fresh and exciting things that you think they will be interested in. Having new and fresh things to excite your customers will definitely keep them waiting for your next email. Here are eight techniques for MLM list building. Add a subscription box to every page on your website and make it attractive, visible and easy to use. Add a link to a sample issue or your archive so potential subscribers can preview what they are signing up to. Clearly stating your Privacy Policy is also an important MLM list building technique. It helps potential subscribers trust you. Get in touch with other newsletter editors and offer a trade for advertising. They promote your newsletter and you do likewise. Be sure to choose publications that are related to yours but not direct competitors. Registering your Newsletter with Newsletter (Ezine) Directories such as jogging, directory of Ezines is an effective MLM list building strategy. It helps increase the number of links to your website and newsletter. Another MLM list building approach is to offer your subscribers a free tool, e-book or report when they subscribe. For more details www.mailing-list-gold.com Write something original that they cannot get anywhere else, and you will add value and establish your expertise. Brand your newsletter by creating a unique image and advertising headlines that you use as you promote it both online and offline. Invite
185
INTERNET USERS HANDBOOK
your current subscribers to forward your email newsletter to others. Following these MLM list-building strategies will help you attract qualified and educated MLM prospects. Techniques
HOW TO BUILD YOUR LIST OF LEADS QUICKLY
You know that it's much easier to earn a profit from a lead that has already shown an interest in what you have to offer. Chances are very good that if someone has already signed up, or "opted in" to receive updates from you, then they are willing to take a look at products and programs that you recommend. So, if you want to make any type of steady money online, the first thing you'll need to do is create a mailing list of subscribers. Keep in mind the bigger your list grows the more profitable it will become. But for the purposes of this article, beginning your list and getting a few hundred subscribers will do just fine and help you begin earning some extra cash. There are actually several ways to quickly build a list of subscribers.
I'm going to describe a few ways to get started below. If you don't understand some of the things that I talk about mention, don't worry I will do my best to clear things up for you in upcoming articles. And remember if you have any questions you can contact me at any time. Just use the link in my author box to visit my blog. Let's get started...
PLACE A SIGN-UP FORM FOR YOUR LIST
First, place a sign-up form for your list on your website, blog, and even on your "About Me" Pages on your favorite social or auction websites, like Facebook, My Space or EBay. If you need help doing this it's best to check with your autoresponder service. They should have complete set-up tutorials and if you don't have an auto-responder yet, it's vital that you choose the right service. There are a couple of good ones, and I personally use and recommend Aweber.
JOIN FREE-TO-JOIN LISTS
There are list building programs, such as Listdotcom and ListQuik that are free to join. With these programs you sign-up, and then promote the service using the marketing materials that they have created for you. Put them up on your blog and website, and interested people will subscribe under you. You then get to mail to these new members as well as the number of people that are allowed when you first join. Often there is an upgrade that gives you the ability to mail to several thousand people once or up to a few times every week.
YOU CAN DO JOINT VENTURES.
Once you have a list of a few hundred people then you can build faster by getting in touch with the owners of similar lists or Ezines and strike a deal for a JV. This involves recommending each others newsletter or product to your own subscribers. Keep in mind that most people don't just sign up to one list so it could be very beneficial for both of you. You may also want to check out JV-Network.com. It's great for finding joint venture partners.
186
INTERNET USERS HANDBOOK
JOIN PRODUCT GIVEAWAYS
These are simply another form of joint venture. They usually consist of several list owners banding together and offering one of their products for free to anyone who participates in the event. This benefits you as a contributor by requiring all of the people who want the product you're offering to register for your list so that they can download your gift. These events can bring you hundreds of new subscribers targeted to your niche. There are several other ways and ideas that will help you build your list, but these suggestions should get you headed in the right direction. The main goal is to start a list of valid email addresses that optin, which means they give you permission to send them email. Using any of the four ideas above, or better yet, starting all of them one by one will begin building your list. Out of the four ways above the fastest way to amass more subscribers is by participating in giveaway event. You can find them by subscribing to free marketing Ezines, and by joining specialized marketing forums such as Free Advertising Forum, The Internet Marketing Warrior Forum, or IM4Newbies Forum. When building your list it is a good idea to avoid safe lists, MLM programs, or purchasing lists of random bulk email addresses. These methods are nearly useless for list building purposes, and are huge timewasters. Now let's discuss how you will compile and manage your marketing list. You can accomplish this with an autoresponder system. There are two main types of autoresponder to choose from: A php script that you run yourself, or an online service that you register for and pay a monthly fee. You can download a free script from Hotscripts.com or do a Google search to find other script sites online. If you prefer not to go through the lengthy and confusing process of setting up your own mailing list script, then just go with one of the paid services. The one that I use is Aweber.com, and another good one is GetResponse.com. A terrific feature with these autoresponder is that you can sign up for a free account, in order to experience the service before you spend any money. This is a great way to get started with list building when you're budget is limited. QuickList
13.14 BLOGS AND ARTICLES
Many successful online entrepreneurs are doing very well with their blogs and articles. They have branded themselves as an expert in on one subject or another. Do not overlook the potential of this method of advertising and building your subscriber list. All of us are expert in one thing or another; how about your job, your hoppy, your experiences on line, or even your life experiences.
HOW TO PROMOTE BLOGS AND ARTICLES
If you're new to writing online, you need to promote blogs and articles to maximize your chances of driving in more traffic, and making money online. You can drive traffic to your sites and make good money. It can be difficult; a lot of work, but it can be done if you put in the time. You need to understand
187
INTERNET USERS HANDBOOK
some of the basics in SEO words, where to promote your blogs, websites, or articles you write online for like ehow, or other writing sites.
INSTRUCTIONS
Use good SEO words. This is one of the most important ways on driving traffic to your sites, and promotes your work. Search engine optimization is using search friendly words that are familiar with what you are writing, or product you are using to sell. If you are going to drive in traffic to your sites, you need to understand simple terms of SEO words. For help, use Googles search-based keyword tool. This will help beginners to writing online, or blogs. Sometimes it can be difficult, and easy, it takes time adjusting. It is very important if you want to make money on the Internet. This will help promote more traffic to your blogs and articles.
USE SOCIAL BOOKMARKS
You should use social bookmark sites like Digg, Mixx, and Stumble Upon as ways to promote your blogs, or articles. It is a great way to expose more views to your work. You are going to need to create many backlinks, and use good SEO words when it comes to making money online. Those are key. Also, check out shetoldme. It is a promoting site, that allows you to not only create free promotion, but they have a Google AdSense program. If you have a Google AdSense blog, you are probably familiar with it. If not, you need to sign up for Google AdSense, which is free. You keep 100% of the shetoldme clicks on Google AdSense. This is great way to make money on a site, while getting more traffic at the same time. Check out Xomba as well, to create links to your sites. They also have a Google AdSense program to make money from as well. You can also write articles on their site. Both sites are extremely helpful.
USE SEARCH ENGINE SUBMISSIONS
Go to submitepxress.com, for free submission. Your blog or articles will go to over 40 search engines. Why just limit your exposure to Google, or Yahoo? This is a helpful way to drive more traffic to your site. You cannot underestimate the smaller search engines, and using them to drive traffic to your site. Obviously, Google and Yahoo are the big ones, also very important but there is also more competition on those sites. The more search engines, the better for your site.
USE SOCIAL NETWORKS TO PROMOTE YOUR WORK
Place likes Facebook, MySpace, along with Twitter is very helpful. If you can generate a large following on twitter, you can definitely increase quite a bit of exposure to your site. It all depends on the following you can get, though. Adding more friends to your social network can definitely help drive a decent amount of traffic to sites. If you want to make really good money, I wouldn't rely on that alone, though. How To Promote
MORE ON SOCIAL NETWORKING LEADS
One of my first blogs regarded my retirement boredom and that I had turned to the Internet. For sure it is hard to adjust from 12-16 hour days to zip, narda hours with nothing to do. I tried many social networks; however, I found some popular sites too Social for me and lacked the business minded members that I was looking for.
188
INTERNET USERS HANDBOOK
I retreated to my 1-on-1 networking, just me and my computer. I knew the computer and it knew me and my frustrations. Although I belonged to several social networks including a paying Direct Matches, now called myNetworkingPro, I could not find the satisfaction that I was looking for in trying to interact with these members. For the most part, unless they were really social, the interaction was more of spam and link pushing than trying to get to know me and interact with me. As of this writing, myNetworkingPro has gone into Phase2 with a cleaner interface, improved communications, etc., and is now considered a must-have social business network and is the largest such site online. Swom became my first real social business network where I took an early position and leadership role in helping others focus on business, connecting and interacting with others. Since then I have added several others all of which support our ISA Groups: Swom, BizOppers, Fast Business Network (formally Sonar 247), ISMmagic, myNetworkingPro and APSense. While these sites all have different personalities, benefits, etc., the members all represent leads, FREE Leads for your business opportunities. While the previous post Use social networks to promote your work closed with If you want to make really good money, I wouldn't rely on that alone, though. I havent found the statistics as yet, but I feel that these social business networks are increasing market share as advertising resource that cannot be ignored.
I am sure not many might admit it, but every member that you connect with is a potential Lead for your business ops, but like many downlines, the numbers mean little, unless you learn to cultivate them. Unlike neighbors, that you cannot always choose, members can be connected and disconnected. (I disconnect with the spammers and link pushers) Be sure to consider Social Networks as one of your better resources. Where else can you talk and interact with your leads.
13.15 INCREASING BLOG TRAFFIC
Simple Ways to Get Your Blog Noticed in the Blogosphere. The blogosphere is a big and busy world with over 100 million blogs and growing. How do you attract visitors to your blog? Follow these simple tips to drive traffic to your blog.
WRITE WELL AND WRITE OFTEN
Frequently updating your blog with useful content is the first step to building your blog's audience. The content you write is what will keep readers coming back for more. Make sure you have something meaningful to say to them and say it often to maintain their interest and keep them loyal. Furthermore, post frequently to increase the number of chances you have for your blog's content to be noticed by search engines such as Google or Technorati.
SUBMIT YOUR BLOG TO SEARCH ENGINES
Get on the radar screen for the popular search engines such as Google and Yahoo! by submitting your blog's URL to them. Most search engines provide a 'Submit' link (or something similar) to notify the search engine of your new blog; so those search engines will crawl it and include your pages in their results.
189
INTERNET USERS HANDBOOK
It's important to understand that simply submitting your blog to search engines doesn't mean your pages will appear at the top of a Google search results screen, but at least your blog will be included and will have the chance of being picked up by a search engine.
USE AND UPDATE YOUR BLOGROLL
By adding links to sites you like in your blogroll, the owners of those blogs will find your blog and will be likely to add a reciprocal link in their blogrolls. It's an easy way to get the link to your blog in front of many readers on other blogs. The hope is that some of those readers will click on the link to your blog on the other blogs' blogrolls and find your content interesting and enjoyable turning them into loyal readers.
HARNESS THE POWER OF COMMENTS
Commenting is a simple and essential tool to increase your blog's traffic. First, respond to comments left on your blog to show your readers that you value their opinions and draw them into a two-way conversation. This will increase reader loyalty. Second, leave comments on other blogs to drive new traffic. Make sure you leave your blog's URL in your comment, so you create a link back to your own blog. Many people will read the comments left on a blog post. If they read a particularly interesting comment, they are highly likely to click on the link to visit the commenters website. It's important to make sure you leave meaningful comments that are likely to invite people to click on your link to read more.
SYNDICATE YOUR BLOG'S CONTENT WITH AN RSS FEED
Setting up an RSS feed button on your blog makes it easy for your loyal readers to not just read your blog but also know when you publish new content.
USE LINKS AND TRACKBACKS
Links are one of the most powerful parts of your blog. Not only are links noticed by search engines, but they also act as a tap on the shoulder to other bloggers who can easily identify who is linking to their sites. Linking helps to get you noticed by other bloggers who are likely to investigate the sites that are linking to them. This may lead them to become new readers of your blog or to add links to your blog from theirs. You can take links to other blogs a step further by leaving a trackback on the other blog to let them know you have linked to them. Blogs that allow trackbacks will include a link back to your blog in the comments section of the post that you originally linked to. People do click on trackback links!
TAG YOUR POSTS
It takes a few extra seconds to add tags to each of your blog posts, but it's worth the time in terms of the additional traffic tags can drive to your blog. Tags (like links) are easily noticed by search engines. They are also the key to helping readers find your blog when they perform searches on popular blog search engines such as Technorati.
SUMIT YOUR POSTS TO SOCIAL BOOKMARKING SITES
Taking the time to submit your best posts to social bookmarking sites such as Digg, StumbleUpon, Reddit and more can be a simple way to quickly boost traffic to your blog.
190
INTERNET USERS HANDBOOK
REMEMBER SEARCH ENGINE OPTIMIZATION
When you write your blog posts and pages, remember to optimize your pages for search engines to find them. Include relevant keywords and links but don't overload your posts with too many relevant keywords or completely irrelevant keywords. Doing so can be considered spamming and could have negative results such as your blog being removed from Google's search entirely.
DON'T FORGET IMAGES
Images do not just make your blog look pretty; they also help people find you in search engine listings. People often use the image search options offered by Google, Yahoo! and other search engines, and naming your images with search engine optimization in mind can easily boost your traffic.
CONSIDER GUEST BLOGGING
Guest blogging can be done when you write a guest post on another blogger's blog or when another blogger writes a guest post on your blog. Both methods are likely to increase traffic as your blog will be exposed to the other blogger's audience. Many of the other blogger's readers will visit your blog to see what you have to say.
JOIN FORUMS, WEB RINGS OR ONLINE GROUPS
Find online forums, web rings, groups or social networking sites such as Facebook and LinkedIn where you can share ideas and ask questions of like-minded individuals. Add a link to your blog in your signature line or profile, so each time you post on a forum or participate in another online network, you're indirectly promoting your blog. Chances are many people will click on that link to learn more about you.
PROMOTE OUTSIDE YOUR BLOG
Promoting your blog should not stop when you step outside the blogosphere. Add your blog's URL to your email signature and business cards. Talk about it in offline conversations. It is important to get your name and your blog's URL noticed offline, too.
NOMINATE YOURSELF AND OTHER BLOGS FOR BLOG AWARDS
There are a number of blog awards given out throughout the year. Nominating yourself and other blogs and bloggers can draw attention to your blog and drive traffic to it.
DON'T BE SHY
The most important part of the blogosphere is its community and much of your success as a blogger will be tied to your willingness to network with that community. Do not be afraid to ask questions, join conversations or just say hi and introduce yourself. Do not sit back and hope the online world will find you. Speak out and get yourself noticed. Let the blogosphere know you have arrived and have something to say! BloggingTips
13.16 EMAIL MARKETING
Like many small business owners, I work with a small marketing budget. Okay, truth be told, I hate to spend money on advertising. Especially if I can get better exposure at a very low cost, sometimes even FREE!
191
INTERNET USERS HANDBOOK
During the past three years online, I've learned some great ways to do just that. Today I'd like to share them with you. Don't worry; I'm not going to tell you to spend days and days at free classified sites or newsgroups. The methods I will be sharing with you are much more powerful. So how does the costconscious marketer get the best free and low-cost exposure? Simple. By utilizing various forms of the best free marketing tool ever invented... email! There are many ways to utilize email marketing. For the most part, email marketing can be broken down into two distinct categories... Targeted and Untargeted. First, I'll touch on the untargeted, just to show you why it is a waste of time.
UNTARGETED EMAIL MARKETING
Untargeted email marketing on the Internet usually takes on the form of "Unsolicited Bulk email". Whether you are doing it yourself or hiring one of the thousands of email blasting companies online, it makes no difference. Bulk email is NOT a smart way to market. Let me explain exactly why... "Spamming or sending mass email to "unqualified" email addresses is considered bad "netiquette". If you send unsolicited email to addresses that do not want commercial email, not only do you risk the reputation of your business, you can get into more trouble than you would expect. What kind of trouble? Well, since many ISP's do not allow this activity, they will discontinue your account as soon as the inevitable complaints start to trickle in. If you want better results without the risk, consider the following alternatives...
TARGETED EMAIL MARKETING WORKS.
Truly targeted email means getting your email to recipients that HAVE approved of it. Not only do your get better results, you won't have to worry about ISP cancellation and more importantly, the reputation of your business. Here are the best-targeted email marketing methods I've used. (Listed from most expensive to least expensive.)
"OPT IN" EMAIL LIST RENTAL
Did you know that you could actually rent email lists of people who have approved email about certain topics? This method is not the cheapest form of targeted email marketing, but it works! On average, you'll have to spend about ten to fifteen cents per address. The companies that rent the addresses even do the mailing for you. You just sit back and wait for the orders! When I released my book, "Insider Internet Marketing", I used this method and sold a few thousand dollars worth of books in a twoday span. The company I used is called Postmaster direct.
EZINE ADVERTISING
I'm a big fan of Ezine advertising and regularly utilize this low budget technique. I'm not just saying that to drum up advertisers for my own newsletter, actually I have a waiting list of about a month just to get an ad in here. Why? Quite simply, email advertising works! Take a look at the advertising section of your favorite email Ezine. The reason there are so many ads there is because the advertisers get results. Not only do you reach your target audience, you reach
192
INTERNET USERS HANDBOOK
them by the thousands. Of all the online marketing methods available, Ezine advertising could be the most effective. Many larger companies are just starting to realize this and are entering into this exciting new advertising medium. Compared with the high costs of web site banner advertising, Ezine advertising is a bargain. One-step better than "advertising" in Ezines, is actually publishing your own. If you are not already publishing your own e-newsletter, I highly recommend you do so. It is much easier than you might imagine. Your customers and prospects will constantly be "in touch, your Ezine can keep them abreast of new products, and services as you make them available. You can also generate income offering classified or sponsorship advertising if you wish. Unlike traditional newsletters, there are no printing or postage costs. Since your own cost is zero, you can offer free subscriptions, thus insuring a steady flow of new prospects. To get started publishing your own Ezine, you do not need to pay for list management. You can manage and deliver your Ezine yourself with a good email program like Qualcomm's Eudora or Pegasus Mail by David Harrris. These are the best email programs available on the Internet and they can be downloaded for free at the following URL's http://www.eudora.com, http://www.pegasus.usa.com Once you have your email program installed, practice mailing to a few people at once by using the BCC (blind carbon copy) feature. It's important to use the BCC field when mailing to a list. This insures that everyone on the list does not see other email addresses on the list. No one wants their email address publicized all over the net. After you have perfected your emailing skills, all you need is some subscribers. That is easy; simply post a message announcing your newsletter to the "NewList Announcement List". Full details on posting are here: http://scout.cs.wisc.edu/scout/new-list/format.html
EMAIL DISCUSSION GROUP PARTICIPATION
An email discussion group is delivered via email like an email newsletter. But a discussion list differs from an email newsletter in one major way -- you are allowed to voice your opinion, usually through a moderator. Discussion lists also allow you to ask for help from others with similar interests. What's more, you can assist people in need while your sig file (the footer you include at the end of every email message you send) invites readers to your site. Discussion group marketing works because the posts are delivered directly TO a targeted audience. Once again, push marketing at its finest! In addition to posting to discussion groups, you should consider advertising if the group you join offers it. No matter what you are marketing online, participating in discussion lists makes sense. Not only will you learn some valuable information, it's is a great way to soft-sell some of your wares.
193
INTERNET USERS HANDBOOK
To find some discussion groups on your particular area of interest, visit http://www.egroups.com. While you're there you can even start a group of your own! Now that you are armed with the facts about email marketing, go out and start your email marketing campaign today! And remember, whatever email marketing method you choose, be sure that everything single email you send out includes your URL and a brief description of exactly how YOU can be of service to anyone who may be reading that email! JimDaniels
13.17 FREE FOR ALL (FFA) & CLASSIFIEDS
There are hundreds, probably thousands of free advertising sites available to you on the worldwide web. Most offer classified ads that cost you nothing. Others offer free links to your page or web site. Here are some tips that might make the process simpler and a couple of things that you might consider doing first.
HAVE YOUR ADS READY TO GO
You should have several variations of each ad. Some should be 25 words, some 50 words, and some 100 word ads. Ideally you should have them already typed up on your text editor such as Write or Note Pad, so that you can just call one up and paste it into the box that is normally found at the site. This will speed up the entire process
WHEN YOU GO TO EACH SITE
Check out what the policies and procedures are. These will normally tell you the number of words that are allowed, how long your ad will stay listed and any restrictions. They will also tell you whether they provide an active link for your URL and/or email address.
GO TO THE CATEGORY
Go to the category that you are considering and check out other ads listed. See how they are set up. This will also show you if they furnish active links and how they are set up. If the site does not provide active links then you have to include your site URL and/or email address in your text if appropriate.
When reviewing the ads, check to see if any are similar to your ad. If so, consider changing your headline or wording to make it a little different. Also check the sequence of dates of the ads (if the dates are listed) to see whether your ad will be entered at the top or the bottom of the list. Many of the sites rotate, with the oldest falling off as new ones are added.
IF YOU PLAN TO MAINTAIN ADS ON THE FREE SITES
Consider creating some type of log or index card system. List the site address, how long the ad will stay up, how many words and the date it expires, plus anything else you might think is appropriate. Some sites we have placed ads listed our ad for seven days, two weeks, thirty days and others longer. Each is different. Some send you an email reminder that your ad is about to expire, but most do not. Therefore, it is advantageous to keep some type of log if you are going to place these type ads on a regular basis.
194
INTERNET USERS HANDBOOK
Some sites also offer upgraded or premium ads. For an additional nominal amount they will list your ad with a color headline and your ad will stay at the top of the category you choose for a predetermined period. Some of the upgrade offers are pretty good and insure that your ad will not get lost in the hundreds of other ads that may be in the same category. Remember, your goal is to create traffic to your web site or inquiries regarding your product and/or services. This is just one of a number of avenues to use in your marketing plan. You should also include paid advertising, direct email (not spamming), and targeted advertising in Ezines such as the one you are reading. JoeRienbold
13.18 PAY-PER-CLICK ADS
As advertisers started to push into more colorful, more multimedia "rich media ads" online, a surprisingly simple text ad started to make a huge impact. The idea started with the GoTo.com search engine, which listed search results depending on how companies bid for keywords. The advertisers only paid GoTo.com each time someone clicked through to their site, a system known as pay-per-click (PPC). Even though earlier attempts at commercializing search results had failed, GoTo.com was more successful because they started life as a commercial search engine. Meanwhile, Google made a crucial change to the PPC system when it launched its AdWords service in 2000, listing "sponsored links" next to search results. These simple ads consisted of a text headline, a couple short lines and a link, and they eventually proved to be a powerhouse for Google. These ads were successful for three important reasons: They were tied to keywords, which meant that searchers were getting ads that were highly relevant to what they were searching for; Advertisers only paid for the times people clicked on the ads; and Popular Google search engine drove huge amounts of traffic to these ads. Google later branched out and started serving up PPC ads on third-party sites such as online newspapers and blogs through the AdSense network, delivering ads depending on the content of the page, rather than from search results. Problems have persisted with PPC ads, as some companies will buy keywords using trademarked terms or the name of rival firms in order to divert traffic to their own websites. So far, courts have sided with Google, allowing people to use trademarked terms in PPC ads as long as they are not posing as the rival company and confusing consumers. The other problem with PPC ads is click fraud, with hackers or rival firms driving up the cost of ads by clicking repeatedly on ads. Google and other search engines downplay the cost of click fraud, but researchers estimate that 10% to 20% of clicks on PPC ads are fraudulent, costing advertisers from $500 million to $1 billion per year.
195
INTERNET USERS HANDBOOK
MEASURING THE PHENOMENON
Over the past few years, online advertising has become a juggernaut, leading all other ad mediums in growth worldwide. Why, as more people get broadband Internet connections, they tend to spend more of their time online and less time with print publications, TV and radio. As the attention of the public shifts to the Internet, advertisers must follow them in order to keep reaching people. Despite rosy projections, it pays to remember that advertising is a cyclical business, and online advertising dropped like a lead balloon after the dot-com bust in 2000
CHALLENGES
As marketers fall over each other to reach the growing online audience, hosts of challenges remain for them. Because online advertising is a new frontier, marketers often find themselves crossing ethical boundaries for users. email advertising led to spam, or unsolicited email, which has almost ruined the email experience for many people. Advertisers also started using pop-up or pop-under ads that served an ad in a new browser window, forcing people to close the window and view the ad. That led to people using popup blocking software, now a standard feature in the Firefox and Internet Explorer browsers. Advertisers have had to worry about being associated with these types of ethically challenged ad methods online, along with adware and spyware companies that deliver ads via software that's loaded onto unsuspecting people's computers. In one example, ads sold by Yahoo in its search-advertising network ended up being served through adware companies unbeknownst to the advertisers. So their ads showed up through adware companies that might have upset viewers -- not exactly a good forum for selling or promoting a product. Advertisers also face the challenge of gauging just how many people have viewed online ads. Tracking ads online is a tricky proposition, despite the Internet's claim to better trackability. The problem is that it's difficult to gauge how many unique people are actually viewing an ad, versus the same people viewing the ad multiple times on different computers, or automated Internet spiders or bots that scour the web for search engines. Pay per click (PPC) is an Internet advertising model used on websites, in which advertisers pay their host only when their ad is clicked. With search engines, advertisers typically bid on keyword phrases relevant to their target market. Content sites commonly charge a fixed price per click rather than use a bidding system. Wikipedia The article was sourced from Internet World Stats which is also a great resource for targeting your advertising marketing campaigns. Internet World Statistics provided the scope of the user and scam problem in an earlier section. The following breaks down the data for further analysis and as a useful tool for your target marketing where to place adverting, who you are trying to reach. Click the link for an additional break down of the data. Internet World Stats
196
INTERNET USERS HANDBOOK
13.19 SAFELISTS
ARE SAFELISTS SAFE?
If you are like me, you are ALWAYS on the lookout for an easier way to sell your products, get people to join your opportunity, or subscribe to your Ezine. Today we take a look at how to do that using safelists. Safelists CAN BE one of the hidden gems of Internet marketing. You can sell any product or service with safelists, but if you are a member of SFI, Cash Evolution, or another opportunity-oriented program, pay special attention. If you've ever wondered "Do people really READ that mail?" or "Isn't that just a trick to get my email address?" then read on. Today we look at the good, the bad, and the ugly when it comes to safelists. Here is a situation that happens every day. A person, much like you or me, who wants to quit the dayto-day grind of working for someone else, joins an affiliate program. Alternatively, maybe they create an eBook. Or maybe they invent a product they want to sell. In any event, they are now entering the world of Internet marketing. That is right folks, 97% of us will fail online. The only sure way to become one of the 3% (no, I am not selling an eBook) is to use EVERY tool to your advantage. Let's look at one of the lesser known, yet more powerful, tools available.... safelists.
WHAT IS A SAFELIST?
A safelist is an email mailing list that people join (of their own free will) which enables them to send email offers to all the other members in exchange for agreeing to receive email from those other members. So you get to mail, but you have to agree to receive mail too. And no one gets spammed. Some safelists are free while others charge a small annual fee. Those that charge a fee often offer you the ability to send mail without having to receive any. So how does this crazy arrangement work? Don't people just sign up with a Yahoo account and never read the mail in order to get to send mail? Today, safelists have grown up. It had to happen. After all, every advertising medium started out rough and then became more polished.
SAFELISTS HAVE MATURED IN THREE IMPORTANT WAYS
In order to get people to actually read the mail that is sent, smart safelist operators now give away cash money every week. The trick is; they hide it in some random email. So in order to win the $1000, you've got to read the mail. This strategy alone has caused safelists to become very appealing, since much more of the mail is now being read. Safelist owners have instituted rules to stop people from ruining their list. By placing a limit on how often you post, banning attachments and more safelist operators control their lists tightly. Safelists have become web-based. This is the big one. You NEVER download some list, add them to your address book and send to them via your email program. It's all on the web now and can be done in only a few minutes. And the mail is sent from their web server, not yours.
197
INTERNET USERS HANDBOOK
WHY USE A SAFELIST?
This one is easy. Ever see those ads, "Send your message to a zillion people a day without spamming!!!" While the message may be what you find at the north end of a southbound bull, the IDEA is not. Safelists attract thousands and thousands of people who want to promote the affiliate program they recently joined, test market a new product or service, get people to sign up for their newsletter, and more. These people are opportunity seekers. While they may not read the latest herbal Viagra ad that is sent to them unsolicited, they DO pay attention to ads from the safelist that interest them. And there are thousands of members to advertise to.
HOW TO USE A SAFELIST
If you are going to use a safelist to promote your product, service, or opportunity, do it smart. Here are some key elements to help you get started. This is hard-won information, folks, so use it wisely.
USE ONLY WEB-BASED SAFE LISTS
NEVER download a list, buy a CD, or anything else where you send the mail from your ISP. You will lose your Internet connection and more. If you stick with web-based safelists you will do well.
FOLLOW THE RULES
I know you wouldn't violate the rules on purpose, but who has time to read all that fine print? Let me save you some time. If you don't promote porn or hate, don't use an autoresponder as the email address where you receive mail, and don't post more often that you are allowed (each list has different rules), you will be fine on 99% of safelists. So go forth and make money!
HERE IS AN INSIDER TIP FROM THE DOE INSIDER
This one really works, although it sounds stupid. Don't try to sell your primary product on safelists. Told you it sounded stupid. What I mean is this: People on safelist read a *lot* of mail. Don't try to close the sale in the three to five seconds they give you. Think of it just like you would a classified ad. Use a powerful headline (subject line) and try to create *curiosity* about your product. Get the reader to send for more information or visit your website. Use safelists to get them into your marketing system, and let your follow-up system make the sale. Don't hype it up and don't over-promise. What you offer is the real deal. Tell them what's in it for them. That's what they want to hear. And don't copy and paste the same ad that every other affiliate is using. If at all possible, write your own ad or pay someone twenty bucks to write you a good one. But don't sound like everyone else.
TARGET YOUR AD.
Good safelists are broken into categories you choose when you join. This way you can advertise to a smaller, but much more targeted, group of people who have expressed a prior interest in your product or opportunity.
USE THE POWER OF REPETITION.
Get a great ad. Go to your safelists on a set schedule and post the same ad over and over. This really works! The reason it works is that repetition is the mother of learning (surveys prove people need to
198
INTERNET USERS HANDBOOK
see the same ad seven times in order to buy), in addition to the many new people who join the safelist every week. It doesn't matter if you are sick to death of your ad. It matters that your ad works. When it stops working, pull it. Until then, if it ain't broke ... don't fix it.
ARE SAFELISTS REALLY SAFE?
To be sure, there was a dark side to the old-fashioned safelists. You would sign up and get spam out the ... ear. It still makes sense to use a free email account on safelists, although it is not as critical as it was before. And now you can pay a little and never get mail. The good news is that safelists have been around long enough that they have become a legitimate Internet marketing tool, even if most of your competitors haven't figured that out yet. Big-time Internet marketers like Andrew Fox and Lawrence Pryor have started their own safelist services. Most wellknown Internet marketers have used safelists from time to time to boost sales or add new subscribers to their Ezine. The bottom line is this: safelists work. How well they work is up to you. Use the information above as a starting point and give some safelists a try. Don't expect to get rich overnight, but you should see results quickly if you do it right. Good luck! CharliePage
HOW TO SUCCESSFULLY MARKET WITH SAFELISTS
Opt-in email safelists are one of the best Internet marketing strategies for getting your product or service immediately in front of many thousands of people. In this article, I will show you how you can successfully work with them.
BENEFITS OF OPT-IN SAFELISTS
Email to thousands - this can be done with free safe lists or paid safe lists. Even if you only get a 1% response from thousands, you interact with those that will respond. Its immediate you can instantly send your ad and receive an immediate response from those interested. With Ezine ads, you often have to wait for days or weeks before your ad is displayed.
TEST YOUR PRODUCT OR SERVICE
Safelists are a good place to begin testing your ad, before you spend a lot of money on other advertising methods.
TRACK YOUR ADS
Track those ads that pull the best. (Some safelists incorporate tracking in their subscriptions). You can then use these same ads repeatedly in other forms of advertising. The key is to have a great headline, because users will be scanning them for what catches their eye.
HOW TO USE SAFELISTS EFFECTIVELY CHOOSE A TARGETED LIST
If you are targeting Internet Marketers, then dont subscribe to lists that are contains home owners. The more focused the list, the better your chances of success.
199
INTERNET USERS HANDBOOK
USE A BENEFIT-LADEN HEADLINE IN YOUR AD
If you dont capture the attention of users in the brief second they see your headline, they will pass you by.
USE A FOLLOW-UP STRATEGY
Direct customers from your ad to your web site or your sequential autoresponder. It often takes up to 7 times for users to see your ad before they respond to your offer. Instead of losing them after the first message, allow them to see another sample of your offer by following up on them every few days. This will increase your chances of making the sale.
TRACKING AND TESTING
Track the responses to your ads to know exactly which one works and which does not. You can then test which headline pulls the best. After a one-month subscription, you will have some idea if the safelist is worth staying with. If it isnt, unsubscribe! If you are getting a good response from the free lists, then pay the monthly subscription fee, so you can send your ad more often. You will also benefit from all the features they provide.
USE SEVERAL SAFE LISTS
Subscribe as a free member to several paid lists. Test which safelist pulls the best response. Paid safe lists are of higher quality than the ones that are free (no paid subscriptions). As a free member, you can often send your ad once a week to all members. If the response is great, pay your subscription and send your ad more often. Utilizing Opt-in safelists is one strategy in your marketing arsenal that will quickly determine if your ad will be successful. Now explode your sales by implementing an email marketing campaign. Herman Drost
LOW COST WAY OF EMAIL MARKETING
This is a much faster, less expensive way to market than offline marketing. You can reach many more people in a shorter space of time. No Fear of Spamming Or Being Penalized For Spamming This is because all subscribers are strictly opt-in.
TYPES OF OPT-IN SAFE LISTS
Free Safelists Pros Cons
It is free to email to the whole list you can mail to Fills your email box with thousands of offers from all free and paid subscribers. other subscribers. Email to thousands immediately Pays commissions on referrals No tracking of ads provided email once a week only
200
INTERNET USERS HANDBOOK
Paid Safelists Pros
Cons
Email the list (free and paid) every day or Most customers will not see your ad at all. People on these lists are more concerned about others every2days seeing their own ad, than seeing yours. Does not require you to receive other email ads Lose money if you paid to subscribe, but did not get from subscribers. any sales. Membership fees are low Tracking of your ads Pays higher commissions Personalize your messages This is just a general list of safelist features; however, each safelist has its own unique features and benefits.
13.20 TRAFFIC EXCHANGES (TE)
In your search for traffic and online advertising options; Traffic Exchanges must be considered as they are easily found and even for sale. Reviews are mixed; some think they work; some do not. Some say only the TE owners are making money, while others claim a nice monthly income once they have built their downline. TEs are for clickers to earn credits for their own ads. But like Paid to Read/Paid to Click sites, discussed later, most are resellers/advertising other traffic exchanges. Some say use videos and splash pages, as other pages dont get anyones attention. What are they, do they work. Again, some say nothing great, slow process, time consuming. Most are free to join, and worthy of a look. If you have time, then try Traffic Hoopla as one of the best ranked sites to start and it links you to other tops sites. Advantage, advertise one site and get business to 50.
BRIEF EXPLANATION OF TRAFFIC EXCHANGES
If you have a website and you want to increase the amount of visitors (also known as traffic) to your website, you can sign up for a free account at any of the thousands of traffic exchanges available online or choose one from the list below. Then once you have gone through the registration process, you will be able to add links to the website you want to promote, for example, I promote one of my home business websites on many traffic exchanges and this is the address I use http://www.carolking.ws you would simply add your own link. Traffic exchanges work on a credit basis, in order for your website to be seen you must first generate credits by viewing the sites of other members. The credits you earn enable your site to be viewed by other members across the system. This increases the number of visitors to all of the websites involved.
201
INTERNET USERS HANDBOOK
Traffic exchanges usually enforce a credit ratio, meaning members earn a certain amount of credits for visiting one member site, and each credit is translated into one page view. Ratios can vary from program to program so before registering for a traffic exchange it is wise to check out their ratio first. A ratio of 1-1 is best, that way you will get your page viewed once for every (1) page you view. All traffic exchanges have specific viewing times of all member pages. These viewing times can range from 10-30 seconds, so whilst surfing the system, every page that is shown to a member will remain in view for 10-30 seconds, you will not be able to proceed to the next site until the specified time has passed. Most traffic exchanges have a toolbar at the top or bottom of the page that has a timer on it so you can see when the timer reaches 0 and it is ok for you to continue on to the next page. This is put in place to make sure each member site is promoted equally and fairly. If you try to go on to the next page before the timer reaches 0 you will be penalized in some way, the penalty varies from exchange to exchange. To make surfing traffic exchanges a little more interesting, some services offer different ways to surf such as, playing games for credits or listing to radio stations whilst surfing. If you do not want to surf manually for credits you can purchase them, again prices vary. Many traffic exchanges are free to join but also have Pro versions that allow you to generate more credits from referrals. Always thoroughly check out what is available in the Pro version when you first sign-up.
HOW TO USE TRAFFIC EXCHANGES EFFECTIVELY
Using traffic exchanges to promote your business can be extremely effective, but as with all Internet marketing methods, there is a right way and a wrong way to go about it. I myself have wasted a great deal of time going about it incorrectly and consequently I did not gain the full benefit. I even went as far as to say that traffic exchanges did not work. Fortunately soon after, I became a Plug-in Profit Site member and the training that is given with the program soon educated me. I quickly learnt that traffic exchanges are very powerful and could channel a lot of traffic to my websites and blogs. Even now, as I surf my favorite exchanges I still see so many people making the same mistakes I did, this is one of the reasons why I started this lens. I hope to offer straightforward, helpful tips to stop people from wasting their credits on the exchanges.
USING SALES PAGES IN TRAFFIC EXCHANGES
You know the ones I mean, affiliate pages that contain long-winded text, graphics, images and video. These pages are a waste of the surfer's time. It is not the product or the wording of the page that is the problem; it is a simple matter of loading time. It may not sound very important but it is crucial to your success on traffic exchanges. All traffic exchanges use a timer, which means you normally have between 10 and 30 seconds to grab the interest of the viewer and get them to click through your page. This is not a lot of time; so if you have a long sales page with graphics and images on it, guess what is going to happen?
202
INTERNET USERS HANDBOOK
Yep, your time is going to run out and the surfer will move on to the next page without having read a word of your page. How can this be avoided?
SQUEEZE AND SPLASH PAGES FOR TRAFFIC EXCHANGES
By using squeeze pages, also known as lead capture pages. Squeeze pages are designed to GRAB the attention of the reader and then tell them about your product or service in as few words as possible. These pages are also designed to build your list of subscribers to your newsletter, by placing a sign-up form on the same page. Splash pages keep it is short, to-the-point and attention grabbing; and because of the clean concise design, it loads extremely quickly, thereby giving me the maximum viewing time in traffic exchanges. If you would like to learn more about growing your list with lead capture pages, take a few minutes and read the post on my blog entitled Traffic Exchange Tips TIP: Online users now receive the lead generation techniques such as the Splash or Capture page. Yes, these have been around for a while, but now anyone can make a Splash page for any program. Often there is no clue as which program is being advertised along with the request free information. You may ever see the information, but your name and some details have already been captured when you signed up. Further, you will get sign up requests from more than one affiliate, until you finally sign up for the program and your details are found in the master program database Another common mistake is trying to use pages that contain AdSense ads in traffic exchanges. This is a definite no, and will get your website banned by Google because it is against their term and conditions. It is possible to use other types of contextual ads on TE's. Better Text Ads for instance are TE compliant. But it is still best not to use pages with ads on them in TE's. Use squeeze pages to build your subscriber list instead.
HOW TO USE WEBSITE ROTATORS WITH TRAFFIC EXCHANGES
Website Rotators are necessary for anyone using more than one TE to promote their websites. This simple idea will save your hours when you want to change any of the sites you are promoting. So what are website rotators? They are sites that allow you to advertise multiple websites using one single URL. After you sign up for membership with a TE the first thing you would normally do, is start adding the URL's of the sites you want to promote. Lets say for example you have registered with 10 traffic exchanges and you have 5 websites to promote. That would mean you have to enter your URL's 50 times. It would also mean that whenever you want to edit or delete a URL, you have to do it at each of your traffic exchanges, that means 10 sites, 10 sets of editing or deleting, which equals a great deal of time.
203
INTERNET USERS HANDBOOK
Website rotators make adding, editing or deleting your URL's so much quicker and easier. All you need to do is put the URL's of the websites you wish to promote into your rotator, then the rotator gives you 1 single URL to use on your traffic exchanges. This changes the equation dramatically. Now, if you have the same 10 TE's and the same 5 websites, when you want to make changes, instead of having to go to 10 sites and make 5 changes on each, you will only have to make 1 change on your rotator. The website rotator will rotate all 5 of your websites using 1 single URL. There are many rotators available online such as Free Rotator, TPM Rotator and HotScripts to name a few. I have recently started using Page Swirl; this rotator is a free service with options to upgrade to the paid service if you wish. I like this rotator because there are no pop-up or ads, it is totally transparent so no one will know you are using a rotator and you get up to the minute stats. This rotator is simple to use and most of the changes you wish to make to your URL's can be done in just a few clicks. When you are adding your rotator URL to the traffic exchanges, remember to check the terms of service, as some traffic exchanges prefer you to use specific rotators or their own rotators. Squidoo TE
13.21 HOW TO INCREASE YOUR SALES UP TO 500%...
Headlines beginning with 'how to' are very successful, as the Internet is all about information. Internet users have a strong desire to learn. A headline beginning with 'how to' immediately grabs your potential customers' attention and forces them to read on.
QUESTION: "ARE YOU SICK AND TIRED OF WORKING FOR SOMEONE ELSE?"
Headlines written in the form of a question are very effective, as they appeal to your potential customers' emotions. When they read a headline written as a question, they will answer the question in their mind. If the question identifies a specific need, want or desire, they will read on.
COMMAND: "DOUBLE YOUR INCOME WITHIN THE NEXT 12 MONTHS -- GUARANTEED!"
A command headline focuses on the most important benefit your product or service has to offer. It instantly demands your potential customers' attention and intrigues them to read on.
NEWS: "ANNOUNCING A BRAND NEW BREAKTHROUGH IN E-PUBLISHING"
News headlines are very effective and used to announce new products and services. They are written in the form of an announcement or introduction and create curiosity.
204
INTERNET USERS HANDBOOK
TESTIMONIALS: "INTERNET MARKETING EXCLUSIVE IS PURE GENIUS -- OUR SALES HAVE INCREASED BY 40%!"
Headlines written in the form of a testimonial are very effective, as they instantly begin building trust. When writing your headlines, certain words, when combined together, will literally draw your readers' attention to your ad See List for "Power Words" that consistently work. Just as certain words ignite different emotions, certain subjects have a broader interest than others do. Some of the most popular subjects include wealth, love, health and safety. Take your time and try the different formulas according to your needs. Use a combination of the power words and write a headline that sells. By learning the art of writing headlines that focus on the basic human needs and emotions, you can increase your sales considerably. WebSource
13.22 HOW TO KEEP YOUR #1 RANKING
No Matter What Tricks Your Competition Tries To Pull! As it is said, it is far easier to reach the top, but maintaining that position is the most difficult part. With some serious SEO, one could improve the page rankings of a website. But, with thousands of new web pages being indexed by search engines daily, and the search algorithm employed by the search engines changing quite frequently, a once-done SEO can no longer guarantee top results. To continuously maintain a top ranking, one has to do something dynamic and innovative in SEO and that quite periodically. Few tips to do so are mentioned in the following paragraphs. The very basic thing to do is to make search engine spiders come and crawl your website periodically. For that, you have to change your website content and code periodically. If your page does not change at all, its rankings will also remain the same. Other new websites with better content and SEO will then push you from the top spots. Another aspect that is crucial in keeping the #1 ranking is how effectively you employ the SEO concepts in your website. Virtually every website owner uses SEO in order to make his or her websites search engine friendly, so at the end of the day, it is the Darwinian theory of the survival of the fittest that matters. For best results, you need to do well in all the areas instead of concentrating on a single aspect. Since SEO is quite a wide territory that requires core expertise all the way down, this job must be best left to a professional to accomplish. If you make any mistake, it will be difficult or sometimes impossible for a novice to bring things back on track. Finally, submit your websites only to the top directories and search engines. Submitting to the hundreds of directories and search engines mostly illegitimate - does not serve any purpose. If you do link building, do it carefully, one at a time. Also stay away from link farms and mass link exchange offers. Those things could land you in a hot soup. AffordableSEO
205
INTERNET USERS HANDBOOK
14. FOREX (FX) FOLLIES - A GAMBLERS HEAVEN
In this Chapter, you are introduced to Forex (FX), a favorite subject of mine. Like most online income topics, Forex has not escaped it share of scams and frauds. Because of the high risk involved, most newbies lose their money and blame Forex. For that matter, as we will see, most traders or 67% also lose money. It is a gamble, yes because for every trade, there are winners and losers. It is high stakes, high risk and fast moving. Like any gamble, there are some winners, winners that have learned the trade, winners have a winner mindset, winners are those that have prepared, learned and understand the gamble. Winners that win more than they lose. Forex is about you and the trade, it is not about networking, affiliations personal relationship, advertising, SEO and all the other factors that complicate other forms of online income. Herein we cover the basic Forex tools, selected Robots or Expert Advisors, Mindset and Scams. Forex trading used to be for the big boys only. In the late 1990s, online trading for individuals began, following suite with stock market programs like eTrade. These new Forex sites use software call bots to automate your trades. The bots make the decision to trade or not for you. Because these programs are automated; most vendors advise you can simply install the bot and walk away Do Not! We will look at a few of these Bots. This is a grave mistake on your part if you allow the robots to run your Forex business as will be shown in this section. Never invest more than you can afford to lose! If you do not have time to monitor your trades, dont Trade
14.1 WHAT IS FOREX (FX)?
The Foreign Exchange market, also referred to as the "FOREX" or "Forex" or "Retail Forex" or "FX" or "Spot FX" or just "Spot" is the largest financial market in the world, with a volume of over $4 trillion a day. If you compare that to the $ 25 billion a day volume that the New York Stock Exchange trades, you can easily see how enormous the Foreign Exchange really is. It actually equates to more than three times the total amount of the stocks and futures markets combined! Forex rocks! Forex is arguably the best online business, prepare and never invest more than you can afford to lose.
WHAT IS TRADED ON THE FOREIGN EXCHANGE MARKET?
The simple answer is money. Forex trading is the simultaneous buying of one currency and the selling of another. Currencies are traded through a broker or dealer, and are traded in pairs; for example the euro and the US dollar (EUR/USD) or the British pound and the Japanese Yen (GBP/JPY). Because you are not buying anything physical, this kind of trading can be confusing. Think of buying a currency as buying a share in a particular country. When you buy, say, Japanese Yen, you are in effect buying a share in the Japanese economy, as the price of the currency is a direct reflection of what the market thinks about the current and future health of the Japanese economy. In general, the exchange
206
INTERNET USERS HANDBOOK
rate of a currency versus other currencies is a reflection of the condition of that country's economy, compared to the other countries' economies. Unlike other financial markets like the New York Stock Exchange, the Forex spot market has neither a physical location nor a central exchange. The Forex market is considered an Overthe-Counter (OTC) or 'Interbank' market, due to the fact that the entire market is run electronically, within a network of banks, continuously over a 24-hour period. Until the late 1990's, only the "big guys" could play this game. The initial requirement was that you could trade only if you had about ten to fifty million bucks to start with! Forex was originally intended to be used by bankers and large institutions - and not by us "little guys". However, because of the rise of the Internet, online Forex trading firms are now able to offer trading accounts to 'retail' traders like us. All you need to get started is a computer, a high-speed Internet connection, and the information contained within this site. BabyPips.com was created to introduce novice or beginner traders to all the essential aspects of foreign exchange, in a fun and easy-to-understand manner. BabyPips
14.2 BENEFITS OF FOREX TRADING
There are five things give trading the Forex market some unique advantages.
24 HOUR MARKET
Since the Forex market is worldwide, trading is continuous as long as there is a market open somewhere in the world. Trading starts when the markets open in Australia on Sunday evening, and ends after markets close in New York on Friday.
HIGH LIQUIDITY
Liquidity is the ability of an asset to be converted into cash quickly and without any price discount. In Forex this means we can move large amounts of money into and out of foreign currency with minimal price movement.
LOW TRANSACTION COST
In Forex, typically the cost for a transaction is built into the price. It is called the spread. The spread is the difference between the buying and selling price.
LEVERAGE
Forex Brokers allow traders to trade the market using leverage. Leverage is the ability to trade more money on the market than what is actually in the trader's account. If you were to trade at 50:1 leverage, you could trade $50 on the market for every $1 that was in your account. This means you could control a trade of $50,000 using only $1000 of capital. Typical 100:1 leverage is used
PROFIT POTENTIAL FROM RISING AND FALLING PRICES
The Forex market has no restrictions for directional trading. This means, if you think a currency pair is going to increase in value; you can buy it, or go long. Similarly, if you think it could decrease in value you can sell it, or go short Benefits
207
INTERNET USERS HANDBOOK
14.3 FOREX BROKERS
The Forex (FX) market has many similarities to the equity markets; however, there are some key differences. This article will show you those differences and help you get started in Forex trading.
CHOOSING A BROKER
There are many Forex brokers to choose from, just as in any other market. Here are some things to look for:
LOW SPREADS
The spread, calculated in "pips", is the difference between the price at which a currency can be purchased and the price at which it can be sold at any given point in time. Forex brokers don't charge a commission, so this difference is how they make money. In comparing brokers, you will find that the difference in spreads in Forex is as great as the difference in commissions in the stock arena. Bottom Line: Lower Spreads Save You Money!
QUALITY INSTITUTION
Unlike equity brokers, Forex brokers are usually tied to large banks or lending institutions because of the large amounts of capital required (leverage they need to provide). Also, Forex brokers should be registered with the Futures Commission Merchant (FCM) and regulated by the Commodity Futures Trading Commission (CFTC). You can find this and other financial information and statistics about a Forex brokerage on its website or on the website of its parent company. Bottom Line: Make Sure Your Broker Is Backed By A Reliable Institution!
EXTENSIVE TOOLS AND RESEARCH
Forex brokers offer many different trading platforms for their clients - just like brokers in other markets. These trading platforms often feature real-time charts, technical analysis tools, real-time news and data, and even support for trading systems. Before committing to any broker, be sure to request free trials to test different trading platforms. Brokers usually also provide technical and fundamental commentaries, economic calendars and other research. Bottom Line: Find A Broker Who Will Give You What You Need To Succeed!
WIDE RANGE OF LEVERAGE OPTIONS
Leverage is necessary in Forex because the price deviations (the sources of profit) are merely fractions of a cent. Leverage, expressed as a ratio between total capital available to actual capital, is the amount of money a broker will lend you for trading. For example, a ratio of 100:1 means your broker would lend you $100 for every $1 of actual capital. Many brokerages offer as much as 250:1. Remember, lower leverage means lower risk of a margin call, but also lower bang for your buck (and vice-versa). Bottom Line: If You Have Limited Capital, Make Sure Your Broker Offers High Leverage.
IF CAPITAL IS NOT A PROBLEM
Any Broker With A Wide Variety Of Leverage Options Should Do. A Variety Of Options Lets You Vary The Amount Of Risk You Are Willing To Take. For Example, Less Leverage (And Therefore Less Risk) May Be Preferable For Highly Volatile (Exotic) Currency Pairs.
208
INTERNET USERS HANDBOOK
TYPES OF ACCOUNTS
Many brokers offer two or more types of accounts. The smallest account is known as a mini account and requires you to trade with a minimum of, say, $250, offering a high amount of leverage (which you need in order to make money with so little initial capital). The standard account lets you trade at a variety of different leverages, but it requires a minimum initial capital of $2,000. Finally, premium accounts, which often require significant amounts of capital, let you use different amounts of leverage and often offer additional tools and services. Bottom Line: Make Sure The Broker You Choose Has The Right Leverage, Tools, And Services Relative To Your Amount Of Capital.
14.4 THINGS TO AVOID
SNIPING OR HUNTING
Sniping and hunting - or prematurely buying or selling near preset points - are shady acts committed by brokers to increase profits. Obviously, no broker admits to committing these acts, but a notion that a broker has practiced sniping or hunting is commonly believed to be true. Unfortunately, the only way to determine which brokers do this and which brokers don't is to talk to fellow traders. There is no blacklist or organization that reports such activity. Bottom Line: Talk To Others In Person Or Visit Online Discussion Forums To Find Out Who Is An Honest Broker.
STRICT MARGIN RULES
When you are trading with borrowed money, your broker has a say in how much risk you take. As such, your broker can buy or sell at its discretion, which can be a bad thing for you. Let's say you have a margin account, and your position takes a dive before rebounding to alltime highs. Well, even if you have enough cash to cover, some brokers will liquidate your position on a margin call at that low. This action on their part can cost you dearly. Bottom Line: Again, Talk To Others In Person Or Visit Online Discussion Forums To Find Out Who The Honest Brokers Are. Signing up for a Forex account is much the same as getting an equity account. The only major difference is that, for Forex accounts, you are required to sign a margin agreement. This agreement states that you are trading with borrowed money, and, as such, the brokerage has the right to interfere with your trades to protect its interests. Once you sign up, simply fund your account, and you'll be ready to trade! Investopedia
14.5 WARNING SIGNS OF A FRAUDULENT BROKER
Most brokerage firms are legitimate places of business that can give people access to the Forex market. Unfortunately, there are unscrupulous companies that attempt to scam traders. New traders are particularly vulnerable to these types of companies. The Forex market remains largely unregulated so new traders cannot rely upon governmental regulations or safeguards to protect them from these scam artists.
209
INTERNET USERS HANDBOOK
But the Commodity Futures Traders Commission (CFTC) has developed warning signs to help traders protect themselves from unscrupulous dealers. All traders should be aware of these signs and report this type of activity to the CFTC or the National Futures Association.
SIGNS
A company that guarantees large profits A company that promises little or no financial risk A company that claims to trade in the Interbank market A company that refuses (or delays) giving their performance track record A company that engages in high-pressure tactics Any company that encourages quickly transferring money by overnight delivery or the Internet Any company that contacts you by unsolicited phone calls, particularly using offshore salespersons Not every company that engages in these activities is fraudulent. However, any type of high pressure sales activity, particularly involving the transfer of cash, is a cause for concern. And, of course, any opportunity that sounds too good to be true should also be cause for concern. A trader can investigate a brokerage firm that they suspect could be engaged in fraudulent activity. Any individual can perform a search on the National Futures Association online directory. The NFA will have information (including complaint and disciplinary history) on every member broker. This information can be very useful. However, since membership is voluntary, some legitimate companies do not belong to this organization. Otherwise, a trader can check on a company through the Commodity Futures Trading Commission (CFTC), the Better Business Bureau, or Consumer Protection Bureau. WarningSigns
14.6 THE FOREX CURRENCY PAIRS
Foreign Exchange trading is in general the trading of many currencies of the world. It is emerging as the largest and least regulated market providing the greatest liquidity to investors. This trading is always done in pairs Currency Pairs, one currency is bought and the other is sold. Together, they make up what is known as the "exchange rate". For example, you may buy Euros with Dollars, anticipating that the Euro to increase in value relative to the Dollar. If the Euro rises relative to the Dollar, you sell the position and can earn a profit.
MOST COMMONLY TRADED CURRENCIES OR THE MAJORS ARE:
US Dollar (USD) Japanese Yen (JPY) Euro (EUR) British Pound (GBP) Canadian Dollar (CAD) Australian Dollar (AUD) Swiss Franc (CHF)
210
INTERNET USERS HANDBOOK
MOST COMMONLY TRADED CURRENCY PAIRS ARE:
US Dollar and the Japanese Yen (USD/JPY) Euro and US Dollar (EUR/USD) US Dollar and Swiss franc (USD/CHF) British Pound and US Dollar (GBP/USD) While quoting currency pairs, the first currency is referred to as the base currency and the second as the counter or quote currency. The base currency is always equal to 1 monetary unit of exchange, for example, 1 Dollar, 1 Pound, 1 Euro.
TRADING FOREX CURRENCY PAIRS FOR MAXIMUM PROFIT
It is also known as domestic currency or accounting currency and sometimes also referred to as the primary currency of a Forex currency pair. The price represents how much of the quote currency is needed to get one unit of the base currency. When a currency is quoted against US Dollar, it is known as direct rate. Any currency not against the US Dollar is called a cross rate. The quote currency is translated into a certain number of units of the base currency. This is also referred to as the foreign currency, secondary currency or counter currency. For example, if you find that a quote of USD/JPY is at 1.30, it says that for every 1 US Dollar, you get 1.30 Japanese Yen. When you quote for AUD/JPY of 67.73, it says that for every 1 Australian Dollar, you get 67.73 Japanese Yen. Currency pairs are generally traded as 100,000 units of the base currency. For example, if you were buying EUR/USD at 0.95 you would be paying Dollars for Euros as follows: 100,000 x .95 = $95,000 for 100,000 Euros When you find a quote going up, it means that the value of the base currency is rising or in other words, it is getting stronger. If a quote is going down, it means that the base currency is weakening.
THE DOMINANT BASE CURRENCIES ARE:
Euro - EUR/USD, EUR/GBP, EUR/CHF, EUR/JPY, EUR/CAD British Pound - GBP/USD, GBP/CHF, GBP/JPY, GBP/CAD US Dollar - USD/CAD, USD/JPY, USD/CHF The currency pairs are usually traded and quoted with a bid and ask price. The bid is the price at which you are willing to buy and the ask is the price at which price you are willing to sell. For example, if the USD/EUR currency pair is quoted as - USD/EUR = 1.5 and you purchase the pair, this means that for every 1.5 euros that you sell, you get US$1. If you sold the currency pair, you receive 1.5 euros for every US$1 you sell. The key to successful trading lies in selecting one or two pairs of currencies that you wish to trade in as a beginner. As you gain confidence, you may wish to add more pairs in your trading portfolio. But for a new trader or investor it is always advised to have limited pair just to ensure simplicity. InstantForexIncome
211
INTERNET USERS HANDBOOK
14.7 THE TRADING PLATFORM
We have hopefully established and will provide some examples that Forex is dangerous and a gamble, especially to the Newbie. Since the platform is one of your main Forex tools, get a demo account and practice, get real familiar with this trading platform. The following videos will be of great help FOREXMETAVIDEOS Play with the platform on your demo account; figure out how things change from a 1 minute chart to a 1 hour, 1 week etc. Click and hold the click to move to drag the chart to the right to look at history of the trade Click on the dates at the bottom to expand the chart trades; i.e. if you are using Candlesticks and cannot read the signals. Clicking the dates with make the sticks more visible Click on the right hand values to change the scale of the numbers
14.8 FOREX CHARTS AND INDICATORS
There are 3 main types of charts in Forex; the line chart, bar chart, and candlestick chart. The line chart is constructed by connecting daily closing prices. The bar chart is a depiction of the price performance of a currency pair, made up of vertical bars at set intraday time intervals (e.g. every 30 minutes). Each bar has 4 'hooks', representing the opening, closing, high and low (OCHL) exchange rates for the time interval. The candlestick chart is a variant of the bar chart, except that the candlestick chart depicts OCHL prices as 'candlesticks' with a wick at each end. When the opening rate is higher than the closing rate the candlestick is black (sometimes - red). When the closing rate exceeds the opening rate, the candlestick is white (sometimes - green). Technical indicators (for example, RSI, MACD, Bollinger bands, Stochastic) help to analyze the price movements, expressed in Forex charts.
THE RELATIVE STRENGTH INDEX (RSI) IS A POPULAR OSCILLATOR.
The name Relative Strength Index is slightly misleading, as the RSI does not compare the relative strength of two securities, but rather the internal strength of a single security. A more appropriate name might be Internal Strength Index. Relative strength charts that compare two market indices, which are often referred to as Comparative Relative Strength.
INDICATOR OF BOLLINGER BORDERS (BOL)
Indicator of Bollinger borders (BOL) is represented by two lines, which are built on the distance equal to certain amount of standard deviations. Since the value of standard deviation depends on volatilessness of the price, the lines controls their width automatically. The width increasing when the market is more volatile and decreasing when the market is less volatile.
MACD
MACD is the most famous indicator, which is built on the basis of difference of the average values. This indicator was suggested by Jerald H. Appler as the difference between two exponentially smoothed averages (EMA). MACD is the most effective under conditions when
212
INTERNET USERS HANDBOOK
the market swings with high amplitude in trading. The most frequently used signals of MACD are intersections, overbuying/overselling states and divergences.
THE STOCHASTIC OSCILLATOR (STO)
The Stochastic Oscillator (STO) shows the moments, when the price reaches the border of its trade diapason within predefined period of time (this is an indicator of speed of changing or the Impulse of Price). It contains of 2 curves: the fast (%K) and the slow (%D). ForexRealm
14.9 FOREX EXPERT ADVISORS AND ROBOTS
A Forex robot or bot is a piece of software that analyzes the market based on settings entered by the user. A Forex robot makes automated trades that can be carried out even as you sleep. Forex robots are a good way to trade a mechanical system that requires no human evaluation.
HOW DO YOU USE A FOREX ROBOT?
Forex Robots is a pretty general term. It can refer to different types of Forex software. The most common type is a Metatrader expert advisor. Metatrader is a trading platform that is used by multiple brokers. Metatrader expert advisors can take control of your trading account and make trades according to whatever parameters you set. TIP. Get thoroughly familiar with your trading platform, its features and how to use it
ARE THERE ANY PROFITABLE FOREX ROBOTS OUT THERE?
This is the question most commonly asked by traders looking for the Holy Grail answer to Forex trading. There is no holy grail that will get you around to understanding the markets and studying how they work. To answer the question, yes there are profitable Forex robots out there. The problem is that it takes testing over a reasonable period to figure out how profitable they are. Most of the companies and individuals that sell these robots are great about writing sensational claims, but the customers soon find out that the Forex robot is not the road to riches. To summarize, a Forex robot is not a substitute for learning how to trade and acquiring the necessary skills to succeed. However, if you wanted to employ an additional mechanical strategy to your trading, a Forex robot would work. Just keep in mind, there is no software that is a substitute for your good human judgment.
ROBOTS (BOTS)/EXPERT ADVISORS
These experts should have several advantages over us beginners; sure we can watch the charts, try to keep up with the news, etc., but they make their living off Forex with specialize software, charts and tools, the latest market information and should have much better resources then we could ever have. Regardless dont put your blind faith in them - it is your money. A friend of mine paid a couple of $1,000 for a Forex experts How to Course He would up losing the cost of admission, and his investment trades. Regardless of the hype you get from the affiliate ads, or
213
INTERNET USERS HANDBOOK
Forex system sites; a good broker will give you the proper disclosures and documents for you to read, understand and sign. Nothing can be guaranteed! Take the advice of most brokers or experts and practice using a demo account for 3-6 months or until you have a good understanding of the platform, the charts, the indicators, and are experiencing a high probability of success in your trades. Be aware the money used in the demo account, call it USD5,000 is probably more than you will want to invest, so no matter what the result, scale the result down to the size of your investment.
14.10 THE FOREX MINDSET
Get the proper mindset for Forex; you will never always be right or wrong. Be aware of your mindset when your trading on a Demo account, you will freely play of other peoples money and may freely make profits. When you go live, your mindset will likely change and you may make more mistakes because you are now using your own money. The thinking that made you profitable on the Demo account will likely make you profitable on the live account, if your mindset is ok Take time to read about the market as you prepare to trade. Check the news. Remember bad news for one country, maybe good news for another. In a pair: 1 wins and 1 loses. If you do lose big, as I did on the first trade, you may not have enough money in the broker account to make a second trade and you will have to add funds to continue to trade. TIP: Do not rely on the so-called experts or 100% hands off, Just Walk Away hype. There is no such thing a Forex Broker or Robot System that never loses.
EVERY TRADER LOSES ONE TIME OR ANOTHER
That why most traders quote a percent of accuracy. I dont trust my money with my mechanic, never mind trust my financial future with 100% robot. Yes, anything about money attracts the hype, how about some reality. IvyBot claims several times in their various videos and Handbooks that all you have to do is set it up and JUST WALK AWAY, but before you believe that, see one of my blog entries that follows: According to About Forex Trading, 67% of the Retail Forex traders lose money. If so, Is it possible to be a profitable Forex Trader? You bet it is. Is it easy? Not in the least. Rely on your gut feeling; learn Forex and hopefully, you will do better than the experts? It is your money. Check your mindset at the keyboard. Many people practice with a Demo account and they learn to make quick and proper decisions, and create profits. It is Other Peoples Money. Something happens when suddenly you go live and it is your money. Your fears and emotions take over, and you start losing instead of winning. These same fears and emotions can attack you when you have a few losses in a row from your Forex Expert.
214
INTERNET USERS HANDBOOK
KEY CHARACTER TRAITS WHICH YOU NEED TO WIN
In Forex trading 95% of traders lose money and that is a huge percentage but they don't lose because they can't learn to win, they fail because they simply cannot adopt the right mindset to win and this article is all about getting the right mindset for success. 67% of the retail trader lose money. When trading Forex you only need a simple trading system to win and anyone can learn a method which can win in a few weeks but even if its a good system. You need to trade it with discipline to succeed most traders simply cannot do this and we will look this key trait in a moment but first, lets start with how to learn Forex correctly and that means accepting this key Fact.
ACCEPT RESPONSIBILITY
All the best traders know that no one else will give them success and there on their own Most new traders however think they will win by following a cheap piece of software, so they buy one of the numerous Forex robots or laughably named Forex Expert Advisors and think they will make money with no effort, guess what? They all Lose Money! If you want to win you have to accept you need to get an education and this is needed to give you confidence in what youre doing, because if you are not confident you won't be disciplined and will lose
DISCIPLINE
All the best traders know they are going to lose money at some point and their aim is to keep losses small, they don't mind losing because they know they are going to hit trends again and run them, to cover their losses. To win you need to be disciplined, keep your losses small. This is hard for most traders, they take losses personally and let them get out of control and lose. If you want to be a winner learn to take them and your time will come, when trends and profits reemerge.
COURAGE
All traders have the courage to make their own trading decisions, are prepared to standalone, and against the majority opinion, while this can be uncomfortable, keep in mind 95% of traders lose so its the best place to be!
REALISM
The best traders are trading Forex for long-term gains and they have realistic expectations about how much money they can make. Don't try to hurry profits and expose their accounts to unnecessary risks. Many new traders think theyre going to double their account in a few weeks or get rich quick but consider this - the best traders in the world aim for 50 - 100% per annum, in terms of compound growth so if you achieve that, youre up there with the best.
YOU CAN DO IT IF YOU WANT TO!
Forex trading is simple to learn - but you must gain confidence in what youre doing to trade through periods of losses and have the courage to stand alone and this relies on getting the right mindset. A good method needs the right mindset to apply it and if you can't get it, you will fail - its as simple as that. ForexMindSet
215
INTERNET USERS HANDBOOK
If you can get the right Forex mindset, you can enjoy currency trading success and earn a great second or life changing income. Always keep in mind in Forex trading the trader doesn't get beaten by the market, he beats himself.
14.11 TYPICAL FOREX HEADLINES
Make Money Just By Clicking Guaranteed To Make Money with One Click Non-Stop Forex Trading, We Give You the Trade IvyBot, A Forex System That Never Loses Math Geniuses Develop the Best Forex System The Only Forex System That Never Loses Math Geniuses Knock Out a Forex System That Never Loses Forex Is a Big Scam; Dont Quit Your Day Job The Best 100% Mechanical Forex Systems for You 1,044%.54% Net Profit In the Last 190 Days Attention! Whether You Are New to Spot Forex Trading, Or Have Been a Forex Trader for Years, You'll Need All the Edge You Can Get to Improve Your Net Profit, Bottom Line! We Personally Use All EA's (Expert Advisors) On This Page And Are Exceptionally Pleased With The Net Profit Results Gained! We're already Up To 1400% NET PROFIT Thus Far This Year - 2009. Will We Hit The 2000% Net Profit By The End Of This Year? You Be the Judge.
AFFILIATE HEADLINES
According to your fellow affiliate headlines for their various Forex Programs, its simple, just click, walk and way and you never lose. Whether you have been online or you are new to the Internet, and you are seeking to earn extra income, make money; your email will bring you hundreds, if not thousands of offers including Forex affiliate offers. Taken at face value, the headline offers are almost irresistible to your emotional needs or passion to find something that will make you money. By now, you should have learned to recognize the obvious signs of false and misleading advertising. These are your fellow affiliates trying to catch your eye with non-compliance spam, untrue email headlines - they want your money!
FAP TURBO HEADLINES
Get A Forex Robot That Is Capable Of Doubling Your Money Every Single Month... Trade with the most accurate and profitable Forex robot in the world - 95+% Winners. Cannot Monitor the Forex Market because of a day job, commitments, etc. and want automatic software to do it for them. Want to trade Forex profitably but don't know how (no need to know, the robot does everything for you...from A to Z!) Want a secondary or primary income source that is consistent. Want to be amongst the 1% of Forex traders who grow their trading account like wild mushrooms.
216
INTERNET USERS HANDBOOK
Want to break out from the boring and frustrating routine of hard work and no money (but frequently a lot of debt!) Want to start making money today, not 2 months from now! You Need To Know ABSOLUTELY NOTHING About The Forex Market Or Forex Trading To Benefit Day In And Day Out From FAP Turbo's Cash Producing Power... Living A Worries-Free...Debt Free... Luxury Life Is a Reality No One Should Pass We are giving a select group of people the opportunity to live the dream that EVERY single trader in the world has: trading with an automatic Robot that doubles cash every month! You Will Experience The Real Deal...You Will Experience The LIVE Proof....And You Will Experience Why FAP Turbo Is Not Just A Claim...But One Of The Most Profitable Forex Robot In Existence... 100% No Questions Asked Money Back Guarantee... GIVE Me The FAP Turbo Details NOW!
IVYBOT HEADLINES
Attention! You Are About To See a New, Never Before Released Program that Makes Millions! Would You Like A Sneak Peak? WHY THE IVYBOT? Developed by Ivy League Graduates, 4 Separate Robots at 1 Price, Free Robot Upgrades, 100% Hands off Trading Robot, No Experience Necessary, Most Profitble of All Robots $ 500 Turning Into $ 3,736 - In 30 Days, - $ 2,500 Turning Into $ 9,733 - In 45 Days $ 5,000 Turning Into $ 17,154 - In 60 Days, - $ 10,000 Turning Into $ 36,391 - In 90 Days Now It Is Time To Get Real.... Are You Ready? Come See the Results, Be a Part Of The Phenomenon, Watch the Exclusive Webinar. 100% No Questions Asked Money Back Guarantee...
COMMENTS
Personally, I prefer having the choice of monitoring several trades and yes you can make trades with your broker outside of those initiated by the robot, or you can double up or more on their recommended trade if you like it. Remember with Forex MegaDroid, you can trade only trade one pair: EUR/USD. If for example, the EUR is strong against the USD, then EURO may be strong against other currencies as well. I never like just putting my money into just one revenue source. Depending on your Broker, you can double up on the trade if you like what the expert is doing, or you can trade other pairs at the same time. How much you can trade, depends on your deposits and the size of the trade. If you are on a limited budget, then maybe you can only make one trade. If that trade is going against you; then you will not have money to counter-trade or to protect yourself. This Ad also says No Experience Necessary and Most Profitable again. Since these guys are a new bot, how can it be established that they are most profitable over time?
217
INTERNET USERS HANDBOOK
If all trades are International; how are these how are these guys doing so well? Then I must be doing something wrong, as you will see As discussed in the following, IvyBot has and continues to be a loser for me. Now whenever IvyBot want to make a trade, and I am not there to watch the trade, I feel I am at risk. I have no confidence in IvyBot; or their support system. If IvyBot is making multiple trades, some of which are profits; take your profit to help offset your losses, before you leave or shut down the computer. If there are no trades; one way to protect yourself, is to click the Expert Advisor tab, before leaving your computer. This will keep Ivy from executing trade while you are gone and you may want to leave the computer running, if you have other trades, or whatever Smiles, I understand that the word whatever was recently voted the United States most annoying word? I wonder what was second. IvyBot tale of set it up and "Just Walk Away - doesn't work. Leave the computer and let the Bot do its thing - doesn't work! Obviously, after taking such a loss on my first trade; I have been trying to dig my way out of the hole. The other day, I finally reduced my loss to something less than 50% (sounds a little funny, but going from 82% down to 50% down is a reduced loss). I left the computer and IvyBot running and retired for the night. The next morning, I found the Ivy has struck again during the night on another bad trade (a buy, instead of a sell), and I had lost 56 pips before it shut itself down. Talk about losing money while you sleep, and another DO NOT Just Walk Away lesson. Take your time to learn about the platform, orders and charts, etc. For those of you are still laughing, youre correct, I didn't know I could "right click" on the order number and close it or modify it. Let us call it a good first trade mistake and an expensive lesson. See the video link above
I LOST 82% OF MY INVESTMENT ON MY FIRST TRADE WITH IVYBOT
Hello, Thanks for stopping by. I pulled my original post, which was a strong complaint, and offer this replacement post as a Constructive Update for my fellow Forex "newbies" and those that are using or considering using the IvyBot Program. I first reported my loss problem 22 Aug 2009 to IvyBot support who pro-ported to have a personal interest in all questions since this program was a new Affiliate Launch for them. I was down about 55-56% at that time, and ended up with an 82% percent loss by the time the Bot shut down. After several follow-ups to support I finally receive a form response on 29 Aug which read like this: "We're very sorry you are having difficulty. We are seeing much better results than this. Please make sure you are using a recommended broker and that you are using default settings. We are seeing results much like at this site.
218
INTERNET USERS HANDBOOK
..http://www.forexpeacearmy.com/metatrader_expert_advisor/ivy_bot/demo Thanks, IvyBot team" Of course, I felt that this autoresponder form of response was less than humane and certainly lacked the personal touch that a client who had just lost 82% of his portfolio should have received. I guess the Ivy League School's do not teach customer relations or basic business. After some, more follow up from me, which included a constructive review and evaluation of their site; the errors of omission, the conflict between their videos and printed matter, etc., guess what after all my efforts, I finally got another reply: "We're very sorry you are having difficulty. We are seeing much better results than this. Please make sure you are using a recommended broker and that you are using default settings. We are seeing results much like at this site. ..http://www.forexpeacearmy.com/metatrader_expert_advisor/ivy_bot/demo Thanks, IvyBot team" I would have expected something like, "Thanks for your input, we are working it, we will get back to you soon", etc. Fundamentally, I just wanted to know what went wrong; my IvyBot are properly configured, per the video; and once set up "Just Walk Away" which they "hype" several times on their site. My mistake - I did walk away, expecting that the system would take care of me, and protect me against such an "extraordinary" loss. I found an article on the web saying that IvyBot doesn't use a "Stop Loss" and upon pressing IvyBot, they claim they have an internal trigger that doesn't show on the order. I guess the trigger did not work in my case. Since this experience, I do not walk away and have watched other Ivy trades that were going bad, and then were cut short. This has left me with the impression that this is a Manual "Close Order" rather than the so-called robot doing it thing. Manual must have been asleep at the switch on my 1st order. The experts will tell you to use a "demo" account, practice until you are profitable for most of the time, before going "live. Again, this is great advice for learning the platform, orders and charts. Too bad, I am from the old school of OJT (On the Job Training). I guess I like my knuckles cracked a few times, and when you are "live, you pay more attention - least I do now. It is a job, not a hobby; it real money not play money. TIP: This Is Where I Should Say Do as I Say and Not As I Do; Practice With the Demo Account Take a meal break before you set up your trades and decide to take your profits and/or losses or let them ride.
219
INTERNET USERS HANDBOOK
If you leave the computer running as I said before, the IvyBot can get you while you are gone. We all would like to believe a bad trade can be offset by a good one. However, I am still waiting the really good one, up 206 pips (EURJPY) or 56 pips (USDJPY). TIP: Read and Listen, Join Forex Forums. One misspoken word or a decision can rile the markets.
MEGADROID HEADLINES
No Forex Broker in the World Will Ever Know You Are Trading With Forex MegaDroid; No Forex Broker Will Ever Be Able To Stop Forex MegaDroid From At Least Quadrupling Every Dollar You Deposit; setting a new standard in automatic FOREX signals is FOREX MegaDroid. What separates it from the rest is the 38 years of experience the creators have trading FOREX & the software is undetectable by FOREX brokers (which is why most systems don't work). We decided to give this baby a try using a free account prefunded with $ 25. In 30 days we had generated nearly $ 1,250. And all we did was enter the trade when it said and exit when we wanted to pocket the cash! You don't have to baby sit your trades at all... You don't use any form of judgment.... You can fit it around your 9 - 5 (if you have one)... You just spend 5 minutes setting up the software, and then let it automatically give you advices and be off for the day... Forex MegaDroid HAS Proven To Spit Out Unheard Of, Industry Breaking Performance, YEAR AFTER YEAR...Steadily And Consistently Producing As Much As 100% NET Profit Per Month... Not Only Has Forex MegaDroid Withstood the Test of Time in the "Old" Market Reality... Because of RCPTA Technology, it has adapted to the NEW Market Reality to the Tune of OVER 100% NET Profit per Month... 100% No Questions Asked Money Back Guarantee...
COMMENTS
I strongly disagree with their statements You don't have to baby sit your trades at all, You don't use any form of judgment, You can fit it around your 9 - 5 (if you have one), You just spend 5 minutes setting up the software, and then let it automatically give you advices and be off for the day MegaDroid only trades one pair; the EUR/USD. I dont know how these jokers claim to have funded a free account with $25 and claimed to have made$ 1,250? I have not seen MegaDroid initiate enough trades to earn that much on a $25 bill. Ok someone tell me I have been out of the country too long. Demo accounts are usually pre-loaded with $5,000 or more. This $5,000 package gives you a false sense of earning lots of money, which you will not earn, especially if you only fund your account with $50-500. My first trade with MegaDroid resulted in a minor loss (4.5%). What was strange was that I like the trade, would have made it myself; but the robot cut it off early and did not cover the spread. The next
220
INTERNET USERS HANDBOOK
two trades were profitable but small; again barely covering the spread. Some of the EUR/USD trades available that I thought the bot should have participated in it did not. Over the last 3 days 12-15 October the EUR has climbed through the roof while all the experts said to sell. My mistake was listening to the experts and was heavily invested when I should have done my usual thing. Instead of realizing this steady increase and taking advantage of it MegaDroid did nothing, unless there was some wrong with my machine. No Buy trades were made WARNING, Broker FXDD (or any broker) will not let you continue your losses while you wait for the market to come back. It will execute a StopOut that will close All your transactions (winners and losers) once your equity is gone.
14.12 FORGET THE FOREX HYPE
Regardless who makes the claim; does it make sense; use your gut and your brain. Like most things in life, it is still up to you, your decisions. It is still one winner and one loser on every transaction. IvyBot and others prepare and use some Affiliate Guidelines for advertising; "the IvyBot program that never loses, or the most successful Bot available" What an insult to the professionals who have been doing this for years and years, who may have their own bots or strategies. Where is the track record for IvyBot?? For that matter, even the IvyBot Program oversells itself. Let us not forget, IvyBot needs a support system makeover. Lastly, for now, make your own decisions. Experts are there like consultants; do not take their advice and blindly follow them; you will lose. IvyBot has made a few decisions that I did not agree with so when they enter a trade, I usually cancel the order; then make an opposite order and continue my recovery from my original loss. Sometimes when you see the charts, it is better to do nothing, regardless of what the experts say. Learn how to read the charts. TIP: One more time, pay attention to your trades and dont let the experts run your business. Use the experts as a guide, or shut of the expert advisor tab. All-in-all; IvyBot trades has been losers for me Let me mention couple more Forex Programs that the forgoing ad didnt advertise, but ones that I use. If my memory is correct, the above sites are all onetime fees.
14.13 IS FOREX A GAMBLERS HEAVEN?
In the simplest of terms, whether you roll the dice, play a hand of cards, or spin the wheel or make a Forex trade, someone wins and someone loses. For all practical purposes, and disregarding the potential for side bets, there is generally one hand, one bet and one winner. You can bet all your money with one bet. You can walk away from the dice or the wheel to take a break, and you can leave your hand of cards on the table till you return, or fold the hand. If you do leave your hand on the table; then your hand, the dealers and the other players cards wont change.
221
INTERNET USERS HANDBOOK
HOWEVER WITH FOREX:
You can have several trades (bets) going on at the same time. I will call it a bet, because I am betting that I am going to be right and win the trade. You can bet all your money to the limits of your account, with one or more trades. Each trade can have difference Stop Loss and/or Take Profit settings, or you can ride the trade without limits and close when you want. You can change your bet, for example if the trade is going against you, you can close the trade to minimize your loss. If you see a long-term trade that you like, but it is temporarily going against you; you can double up with the opposite trade, take your profits and continue with the original trade. If the trade is in your favor, but weak, you can close the trade. Watch the charts for the optimum time to close. If the trade is in your favor and going better than you expected, you can increase your take profit settings. If you particularly like a certain trade, you can place multiple trades and bets for that same trade. You can hedge yourself if you are unsure of the trade, place a buy and a sell, or maybe two buys and one sell for the same pair. If you walk away while you have an active trade or several trades, you can lose everything! YES IT IS A GAMBLERS HEAVEN IF YOU CANNOT AFFORD TO LOSE; STAY OUT OF FOREX. IF YOU DO TRADE TO KEEP AN EYE ON YOUR TRADE
14.14 MY FOREX EXPERIENCE
As a newbie to Forex trading, my experiences should be of help to others that want to venture into Forex trading. Most of us newbies will most likely start with a Forex Bot. Which one? Most of these new bot sites are marketed through Affiliate Programs. Anybody can be an affiliate, whether they know how to spell Forex or not. Unfortunately most of these sites do not monitor the affiliates and this Laissez Faire management of the affiliates communications has resulted in a lot of false, untrue hype being used to sell these programs. Even the robot site owners have hired the wrong copywriters and programmers to design their sites. As a result; they give the buyer a lot of false as to their mystical expertness and profitability claims. I imagine that they have to pay to meet more support staff to cover all the beginners questions. I am a new Forex Trader (2009), I am not an expert. Not sure that there are any experts; some are just more successful than others. In any case, I have been in data services, charts analysis, etc. for nearly 40 years. I can interpret the charts with some success and I am an active trader. When I am paying attention to my trades and not writing this Handbook, I seem to make more money than these experts. I want to stress paying attention because you cannot allow the experts to run your business. Think of these experts as consultants, they are there to offer you advice and recommendations, but the final decisions that are to be made should be your own.
222
INTERNET USERS HANDBOOK
I am comfortable to discuss my experiences, mistakes, etc. If you decide to venture into Forex, I hope that you will learn and gain from my mistakes and not repeat them. Let there be no question about it, it is dangerous, fast moving and yes - you can lose everything fast; it is a gamble. Later I will tell you why I love it. While most sites offer you a demo account, you will need a broker to trade live. If you read the fine print offered by your broker; then the real picture, the real risks are explained, and all of the hype provided by the site and their affiliates will be dispelled. Regardless of what you have been sold or led to believe, you can lose and lose big fast in Forex trading. I lost 82% of my investment on my very first trade! Most brokers are regulated; site owners and affiliate are not. Regulated The experts will tell you to use a "demo" account, practice until you are profitable for most of the time, before going "live. This is great advice for learning the platform, orders and charts. Too bad, I am from the old school of OJT (On the Job Training). I guess I like my knuckles cracked a few times, and when you are "live, you pay more attention - least I do now. It is a job, not a hobby; it real money not play money. TIP: This Is Where I Should Say Do as I Say and Not As I Do; Practice With the Demo Account TIP: Take a meal break before you set up your trades and decide to take your profits and/or losses or let them ride. I lost money just going to the toilet, but at least I was a bit relieved, while my wallet was also relieved of some cash. If you leave the computer running as I said before, the IvyBot can get you while you are gone. We all would like to believe a bad trade can be offset by a good one. However, I am still waiting the really good one, up 206 pips (EURJPY) or 56 pips (USDJPY). TIP: Read and Listen, Join Forex Forums, Etc. One misspoken word or a decision can rile the markets. Recently while still trying to recover from the Sept 29-1Oct AUDUSD market which went rapidly north of nearly every expert and Bot order to " SELL" Hype: Does it make sense; use your gut and your brain. IvyBot should put out some Affiliate Guidelines for advertising; the "the IvyBot program that never loses, or the most successful Bot available" What an insult to the professionals who have been doing this for years and years, who may have their own bots or strategies. Where is the track record for IvyBot?? For that matter, even the IvyBot Program oversells itself. Let us not forget, IvyBot needs a support system makeover. Lastly, for now, make your own decisions. Experts are there like consultants; do not take their advice and blindly follow them; you will lose. IvyBot has made a few decisions that I did not agree with so when they enter a trade, I usually cancel the order; then make an opposite order and continue my recovery from my original loss. Sometimes when you see the charts, it is better to do nothing, regardless of what the experts say. Learn how to read the charts.
223
INTERNET USERS HANDBOOK
WHY I LOVE FOREX?
I avoided getting into Forex, for years, because I did not have time to learn about it. When I finally signed up, I took a heavy loss due to a robot. Which led to my first Forex blog entry which ended with: Thanks Again - Take Care, Jump in, I love it Most of my affiliate experiences have been a learning curve for me, the people, the scams, the ridiculous claims, the un-kept promises, false guarantees, the paid and unpaid advertising all provided me little to no results. Many thousands of dollars and hours after hours were wasted, except for the learning: the big people have got us over a barrel. For me, it did not matter whether I joined a site on the recommendation of my big boy membership, a pre-launch - with advance warning, a new launch, or an older established program until your prepared yourself and learn, they all just take your money. It is difficult to compete against the same person who created the program, because they have their established downlines, marketing plans and advertising that the big boys can afford. We all wind up selling the same program; the creator, their downlines and us wannabes. Further, I cannot hype my potential customers so maybe that why I am not so successful online. Spillover seems like just a word, because I never got any. No sponsoring required never happened for me, Help from my sponsor never was there. Just join have never produced the so-called guaranteed results. Support systems are a farce; you get no response, or you get a useless response.
224
INTERNET USERS HANDBOOK
15. PLAN AND PREPARE
Success can be yours if you properly plan and prepare. We have given to the keys to success, the blueprint, and the path; but as in all things in life - you must take the responsibility for going for it. The choices you make from now on will determine your future on or offline success. This Handbook has been written for you; whether you are a seasoned professional or a newbie; whether you are starting or growing a business online. Our approach to online business is much the same as our approach to offline business. Business is business. There are no-short cuts, no free rides or free lunches. Follow our approach and turn your passions, interest or hobby into a lifelong online business. In all business online or offline, you are your own greatest risk! Do you have the mindset for business, do you have the required skills, have you prepared for business and do you have a plan for yourself as well as for your business, and is there a market for your business? Without these, you cannot succeed online! Your greatest risk to your business online success is Internet Crime. The Internet knows more about you, than you remember about yourself. Scams and spam is big business; it affects you as an individual, your business or other businesses trying to capitalize on the potential of the Internet to expand their markets. It can shut down or overload your systems and equipment with spam, or a virus. It can steal your identity or destroy your data with a virus. Click fraud can eat up you advertising budget. Other viruses can shut down your computer, putting your out of business. Two ways to minimize this risk is to be doing something that you understand, your and to learn as much as you can about avoiding scams while doing business online. Learning is a lifelong endeavor, enjoy it. Our Internet Users Handbook is a Comprehensive Guide to Avoiding Scams while Doing Business online. Use it and promote it to others. Help us combat Internet Crime. Whether, you are newbie or a seasoned professional. You are here! Many of you have turned to the Internet for the wrong reason, to solve a financial crisis; out of work or too many debts. Unfortunately, you will be inclined to look for a quick fix there are none. Others of you are here for an additional source of income, to supplement retirement, to improve your lifestyle, or even to start a new career. The latter has the greatest chance for online success by following the plan we have laid out for you in this handbook. In either case, the scammers have an offer for you. They do not discriminate; they want any and all of you money. Many fine sites, blogs, articles and sites specialize and do a great job in various areas of the problem. However, we believe that this handbook along with our Internet Scams Anonymous Groups have taken the broadest, most comprehensive view of avoiding scams while doing business online. Obviously, book after book has been written on every type of scam and fraud. Other books help you analyze yourself, start a business, grow your business, and advertise your business and others offer you another winning strategy to be successful in business. Any one of the topics herein can fill books on their own. This Handbook gave you the big picture with discussion, experience, examples and tips. Take
225
INTERNET USERS HANDBOOK
time to learn more each day. A particular subject of interest should supplement with your own online search. It was easy to show and recognize that Scammers play to your emotions by their use of persuasion, trigger words and spam. We all have some trigger that will get us thinking and a willingness to take the action offered by the scammer. Everyone would like to think that the next deal to be the one that will cure our ills or greed. Spam is a major contributor to the spread of Scams. Entry cost and advertising costs are minimal and the penalties few. New sites and email addresses are freely available to further these scams. Further because it reduces the productivity of both individuals and organizations by jamming their systems with junk. Further, because of the size of the problem, Spam has attracted everyones attention and has a priority greater than the Scams it represents. Perhaps some feel that the reduction of spam will reduce the Scams. These Lets Stop Spam methods have affected both the scammer and the legitimate business. These scammers can keep going, but business cannot simply change their sites and email addresses without further affecting their own business. The reduction of spam alone does very little to help the individual who is simply trying to find a way to makes ends meet; especially those that have limited resources to apply to the task. A scammer will take your last dollar and does not give change. The Advertising section shows you how to prepare your advertising and to avoid the spam blockers and being a spammer. The challenge remains; how to grab the customers attention, without the use of spam trigger words used by everyone else. The Handbook has demonstrated that just by doing your own due diligence is the cheapest and easiest way to avoid the Scam. A simple search, with Google or other search engines, will help uncover the problems of a given site. Additional due diligence tools dig deeper into ownership and other problems. For that matter, learning how to do a simply search is quicker than scanning a list for banner or watch program. One of the best ways to avoid the scam is too slow down and take the time to check out the site. Other sections of the Handbook covered Affiliate Programs, MLM, Pyramids and Networking Programs, with special sections for Paid-to-Read/Click and Forex Programs. There are so many sites and scammers, that no list from anyone can possibly keep up. Some tips and tools to manage your time, email and office were included to round out our objectives. The Glossarys are a simple, easy-to-read resource for quick answers Thank you and Welcome! It is my pleasure to champion this cause. With your help, we can grow as an Association, and take a large chunk out of this bad apple. You have the signs; hopefully you understand them, and will reduce or avoid the scam in the future. Take advantage of the references and resources offered herein as well as the support of your fellow members in our group sites.
226
INTERNET USERS HANDBOOK
Success if yours, if you accept our plan and prepare for it and please accept my very best wishes for your continued or future success. Dr Don Yates Sr PhD
APPENDIXES A. EMOTIONAL TRIGGERS OR POWER SELLING WORDS
The following are key emotional triggers or power selling words often used in advertisements to motivate you to buy or join. The words that are highlighted are also found on the Scam/Spam List, and if used may be blocked; keeping your ad, email or other form of promotion from getting through to the intended reader. Absolutely Advice Affordable Alert Amazing Announcing Approved Astonishing Attractive Authentic Bargain Beautiful Better Big Bonanza Bottom Line Breakthrough Challenge Colorful Colossal Compare Compete Competitive Complete Compromise Confidential Crammed Daring Delighted Delivered Destiny Direct Discount Discover Discovery Download Enormous Excellent Exciting Exclusive Expert Exploit Famous Fascinating Focus Fortune Free Full Fundamentals Genuine Gift Gigantic Greatest Growth Guaranteed Health Helpful Hidden High Tech Highest How To Huge Hurry Imagination Immediately Important Improved Incredible Information City Informative Innovative Insider Instructive Last Minute Latest Launching Lavishly Liberal Lifetime Limited Love Lowest Luxury Magic Mainstream Mammoth Master Miracle Money Monumental New Noted Now Obsession Odd Opportunities Promising Proven Quality Quick Quickly Rare Reduced Refundable Reliable Remarkable Results Revealed Revealing
227
INTERNET USERS HANDBOOK
Easily Easy Edge Emerging Endorsed Energy Save Scientific Secret Secrets Security Selected Sensational Spotlight Startling Strange Strong Sturdy Successful Suddenly Superior Sure Fire Surging Surprise Survival Technology Terrific Tested Timely Tremendous Ultimate Unconditional Uncovered Under Priced Unique Unlimited Unlock Unparalleled Unsurpassed Unusual Outstanding Personalized Perspective Pioneering Popular Portfolio Powerful Practical Professional
Interesting Introducing It's Here Just Arrived Largest Last Chance Sizable Skill Soar Special Special Offer Urgent Useful Valuable Value Wealth Weird Willpower Wonderful You Your Zinger
Revisited Revolutionary Reward Safety Sale Sampler Scarce
228
INTERNET USERS HANDBOOK
Profitable Profits Shocked Shocking Shrewd Simple Simplified Simplistic
B. COMMON SCAM AND SPAM WORDS
The use of any of these words may well result in your ad, email or other form of promotion being blocked by the ever increasing numbers of spam blockers. While some seem pretty innocent; your use of them may keep you from reaching your intended target. $ $$$ 100% Free 4u Accept Credit Cards Act Now! Don't Hesitate! Additional Income Addresses On Cd All Natural Amazing Amazing Stuff Apply Online As Seen On Auto email Removal Avoid Bankruptcy Be Amazed Be Your Own Boss Being A Member Big Bucks Billing Address Billion Billion Dollars Bonus Brand New Pager Bulk email Buy Direct Buying Judgments Cable Converter Call Free Call Now Calling Creditors Cancel At Any Time Claims You Can Be Removed From The List Claims You Registered With Some Kind Of Partner Click Below Click Here Link Click To Remove Click To Remove Mailto Collect Child Support Compare Rates Compete For Your Business Confidentially On All Orders Congratulations Consolidate Debt And Credit Copy Accurately Copy Dvds Credit Bureaus Credit Card Offers Cures Baldness Dear email Dear Friend Dear Somebody Different Reply To Dig Up Dirt On Friends Direct email Direct Marketing Discount Discusses Search Engine Listings Do It Today Dollars
229
INTERNET USERS HANDBOOK
Cannot Be Combined With Any Other Offer Can't Live Without Cash Cash Bonus Cashcashcash Casino Cell Phone Cancer Scam Cents On The Dollar Check Or Money Order Claims Not To Be Selling Anything Claims To Be In Accordance With Some Spam Law Claims To Be Legal Claims You Are A Winner Fantastic Deal Fast Cash Financial Freedom Find Out Anything For Free For Instant Access For Just $ For Just $ (Some Amt) For Only $ Fr.Ee Free Free Access Free Cell Phone Free Consultation Free Dvd Free Gift Free Grant Money Free Hosting Free Installation Free Investment Free Leads Free Membership Free Money Free Offer Free Preview Free Priority Mail Free Quote Free Sample Free Trial Free Website Freedom Full Refund Get It Now Get Paid Get Started Now Gift Certificate
Don't Delete Drastically Reduced Earn $ Earn Extra Cash Earn Per Week Easy Terms Eliminate Bad Credit email Harvest email Marketing Expect To Earn Extra Income F Or Free FREE F.R.E.E. Lifetime Limited Time Only Long Distance Phone Offer Lose Weight Spam Lower Interest Rates Lower Monthly Payment Lowest Price Luxury Car Mail In Order Form Make $ Marketing Solutions Mass email Meet Singles Member Stuff Message Contains Disclaimer Million MLM Money Money Back Money Making Month Trial Offer More Internet Traffic Mortgage Rates Multi-Level Marketing Name Brand New Customers Only New Domain Extensions Nigerian No Age Restrictions No Catch No Claim Forms No Cost No Credit Check No Disappointment No Experience
230
INTERNET USERS HANDBOOK
Great Offer Guarantee Have You Been Turned Down? Hidden Assets Home Employment Http:// Or Www. Human Growth Hormone If Only It Were That Easy In Accordance With Laws Income Increase Sales Increase Traffic Insurance Investment Decision It's Effective Join Millions Of Americans Laser Printer Passwords Once In Lifetime One Hundred Percent Free One Hundred Percent Guaranteed One Time Mailing Online Biz Opportunity Online Pharmacy Only $ Opportunity Opt In Order Now Order Status Orders Shipped By Priority Mail Outstanding Values Pennies A Day People Just Leave Money Laying Around Per Day Per Week Please Read Potential Earnings Price Prices Print Form Signature Print Out And Fax Produced And Sent Out Profits Promise You...! Pure Profit Real Thing Refinance Home Removal Instructions
No Fees No Gimmick No Inventory No Investment No Medical Exams No Middleman No Obligation No Purchase Necessary No Questions Asked No Selling No Strings Attached Not Intended Off Shore Offer Expires Offers Coupon Offers Extra Cash Offers Free (Often Stolen) Serious Only Shopping Spree Sign Up Free Today Social Security Number Special Promotion Stainless Steel Stock Alert Stock Disclaimer Statement Stock Pick Stop Snoring Strong Buy Stuff On Sale Subject To Credit Supplies Are Limited Take Action Now Talks About Hidden Charges Talks About Prizes Tells You It's An Ad Terms And Conditions The Best Rates The Following Form They Keep Your Money -- No Refund! They're Just Giving It Away This Isn't Junk This Isn't Spam University Diplomas Unlimited Unsecured Credit/Debt Urgent Us Dollars Vacation Offers
231
INTERNET USERS HANDBOOK
Remove In Quotes Remove Subject Removes Wrinkles Reply Remove Subject Requires Initial Investment Reserves The Right Reverses Aging Risk Free Round The World Safeguard Notice Sale Satisfaction Guaranteed Save $ Save Big Money Save Up To Score With Babes Search Engine Listings Section 301 See For Yourself Sent In Compliance Serious Cash
Viagra And Other Drugs Wants Credit Card Warranty We Hate Spam We Honor All Weekend Getaway What Are You Waiting For? While Supplies Last While You Sleep Who Really Wins? Why Pay More? Will Not Believe Your Eyes Work At Home Winner You Have Been Selected Winning Your Income
232
INTERNET USERS HANDBOOK
C. SCAMS AND CONFIDENCE TRICKS TERMINOLOGY
Confidence trick Conman Error account Shill Sucker list
NOTABLE SCAMS AND CONFIDENCE TRICKS
Advance fee fraud Advance-fee fraud Art student scam Avalanche (phishing group) Badger game Bait-and-switch Black money scam Bogus escrow Boiler room Charity fraud Click fraud Clip joint Coin rolling scams Computer crime Cramming (fraud) CyberThrill Dark Market Domain slamming Drop swindle El Gordo de la Primitiva Lottery Email authentication Email fraud Embarrassing cheque Employment scams Employment scams Fiddle game Fine print Foreclosure rescue scheme Forex scam Fortune telling Fraud Getrich-quick scheme Green goods scam Hustling Intellectual property scams Internet vigilantism Lottery scam Miracle cars scam Mock auction Patent safe PayPal Phishing Pig in a poke Pigeon drop Ponzi scheme Pump and dump Pyramid scheme Referer spoofing Reloading scam Ripoff Report Rock Phish Romance scam Russian Business Network Safernet Scam baiting Shadow Crew Shell game Slavery reparations scam Spanish Prisoner Spoofed URL Spoofing attack Stock Generation Strip search prank call scam Swampland in Florida Telemarketing fraud Thai gem scam Thai tailor scam Three-card Monte Trojan horse White van speaker scam Whitemail Work-at-home-scheme
233
INTERNET USERS HANDBOOK
Kansas City Shuffle Long firm
PYRAMID AND PONZI SCHEMES
Dona Branca Caritas Bernard Cornfeld Foundation for New Philanthropy High-yield investment program Investors Overseas Service Bernard Madoff MMM Make Money Fast Petters Group Worldwide Pyramid schemes in Albania Reed Slatkin Scott W. Rothstein Stanford Financial Group
CONFIDENCE TRICKS IN MEDIA
Books and literature Fictional con artists Television and movies
SEE ALSO
List of real-life con artists List of confidence tricks List of Ponzi schemes Wikipedia
234
INTERNET USERS HANDBOOK
D. SCAM AND SPAM COMPLAINTS
Internet Crime Complaint Center Gptboycott MyWot RIP-OFF Report Complaints Board Interpol Better Business Bureau Federal Trade Commission Scam Shield If you live in Australia World Investment Companies Canadians can complain here Users from India can complain here
REPORTING INTERNET FRAUD
The best way to fight Internet fraud is to learn how to avoid becoming a victim. However, if you have become a victim, there is help available. Below is a list of official government web resources to help you report and learn about Internet fraud. Bear in mind that you are unlikely to recover your loss, Avoiding Internet Investment Fraud Child Pornography on the Internet Complaints about Foreign Companies Consumer Complaint Form Cyber Crime Information Cyber Criminals Most Wanted FBI Kids' Page Internet Safety Tips FBI Warning about False FBI emails Financial Crimes (International) Further Ways to Report Internet Fraud from Cybercrime.gov Identity Theft Identity Theft Information Identity Theft: Trends and Issues Internet Crime Complaint Center Internet Do's and Don'ts for Kids Internet Investment Fraud Internet Protection Information for Consumers and Businesses Kids' Privacy and the Internet Personal Information and Computer Security Phishing Scams Protecting Your Identity Online
235
INTERNET USERS HANDBOOK
Simple Secure Passwords Social Media Safety Issues Spyware Statistical Data and Reports on Internet Fraud USA Government
OTHER SCAM/SPAM RESOURCES, REFERENCES OF INTEREST
Confessions of a scam artist email Scam Resource Federal Trade Commission for Spam GPTBoycott GPTBoycott Blog How a Bank Got email Scammed Looks Too Good To Be True.com Meet the Nigerian email Grifters Nigerian Hoax Spawns Copycats PTC-Investigation Scam Review Sites Scam.Com ScamBustersOrg ScammerHunters SpamAbuse SpamOrg Websites of Trust
236
INTERNET USERS HANDBOOK
E. BANNED, SCAM AND WATCH SITES
Our 1st Edition contained various lists compiled from a number of sources that include those Scam Sites with which I have had personal experience, as well as Complaints Boards, GPT Boycott, UROnlineBiz, WebsiteOutLook, BeenPaid, Alexa, WebofTrust and many others. However, lists change almost daily as do the number of new users and new scams, making nearly impossible, even for targeted sites such as PTC - Investigation to keep them up-todate. The PTC Investigation site offers a variety of PTC lists including legit sites, but qualifies the legit sites as potential scams tomorrow. I do not concur with that opinion as I feel that most scam sites start out with the intent to scam; while legit sites can run into other problems, ownership, hosting, financial, etc. which does not mean that they are scams. New sites are launched that claim to be reviewers, best sites, and some sites now claim to certify others, watch the source. Still for the best results, go with your gut feeling; otherwise follow the tips and guides that have been provided herein, before you put your money down. Do your Due Diligence. The easiest way to start is by doing a Google Search. One of the best ways to help reduce your emotional spending is for you toslow down; take the time to search the Internet for the program. Check Google, Whois, DomainTools and other resources previously discussed. Do your homework and make a decision. Hopefully you wont be scammed again and your chance of success will improve. Our purpose here is to help each other to learn to recognize and avoid scams while doing business online, not to make lists. There are too many bad programs and scams to list them all. We want to verify and build a list of the good ones. Your traffic exchange may post a list of general ad exclusions; such as Family Friendly Manual Traffic Exchange. No HYIP sites, no PTP sites, no Autosurfs. Others sites, No Adult, No Gaming, and No Investment. Many offer their own list of banned sites which often come from one of the following sites. Below are some popular sites with the lists that they offer
237
INTERNET USERS HANDBOOK
GLOSSARY OF COMMON INTERNET TERMS
This Glossary is a condensed compilation of several sites:Hackers, Hits and Chats: An ECommerce and Marketing Dictionary of Terms; Affiliate Wiz glossary of Affiliate Marketing Terms; SiteNexus Glossary. A handy tool for you: One Click Answers Above the Fold: Describes the part of an email message or web page that is visible without scrolling down the page. This term is important because all content above the fold is assumed to be more valuable to the reader as they see it first. The size of the "above the fold" area will depend on the resolution of the users computer monitor and the number of pixels their monitor displays. Advertiser: The person selling the goods or service; also knows as the merchant. The advertiser or merchant pays affiliates for sending traffic to the merchant's web site after a product or service is purchased. Advertising: Online advertising comprises a variety of forms of advertising. The most popular has been banner advertising, although text advertising is gaining ground rapidly as a form used by the two networks: Google Adwords and Overture / Yahoo! Interstitials, Pop ups and 'buttons' round out the more common forms of Internet advertising. Advertising Network: Advertising network refers to an infomediary, which serves between a group (network) of web sites (which want to host advertisements) and advertisers which want to run advertisements on those sites. DoubleClick is the most well-known advertising network for banner advertisements. DoubleClick can serve advertisements on any of its member sites, and can mine data from users who interact with those sites in order to serve more appropriate advertisements. An advertiser can buy a run of network package, or a run of category package within the network. The advertising network serves advertisements from its ad server, which responds to a site once a page is called. A snipet of code is called from the ad server that represents the advertising banner. Google and Yahoo!'s search engine programs also run advertisements on other sites within their respective networks. Adware: Adware is advertising-supported software. Essentially the business model for the software that is downloaded is the advertisements that are played as part of the download, or when the software is being used. Adware should be distinguished from spyware which is designed to observe and report data of the user. Affiliate: A Web site owner that earns a commission or finders-fee for referring clicks, leads, or sales to a merchant. Affiliate Agreement: terms between a merchant and an affiliate that governs the relationship. This includes the terms on which the affiliate will be rewarded for the traffic sent to the merchant's web site. Affiliate Information Page: A page on your web site that explains the terms of your affiliate program including your commission rates, affiliate agreement, a link for existing affiliates to login, as well as a link to the signup page for new affiliates. Affiliate Link: A URL tracking link that identifies the affiliate and sends traffic to the merchant's web site. For example, a link might look like http://www.yourdomain.com/yourpage.asp?AffiliateID=5999 These links are unique in order to track the traffic coming from the Affiliate site. Typically these links can be simple text links, images, product links, etc.
238
INTERNET USERS HANDBOOK
Affiliate Manager: The person responsible for running the merchant's affiliate program. This includes recruiting affiliates, establishing incentive programs, creating media for the affiliates, reporting on sales and paying affiliates. Affiliate Program: Can also be called an Associate Program, Partner, Referral or Revenue sharing program. In such a program the merchant rewards the affiliate for web traffic, sales or leads on a payper-click, pay-per-sale, or pay-per-lead basis. Affiliate programs enable affiliates to leverage their traffic and customer base in order to profit from e-commerce while merchants benefit from increased exposure and sales. Affiliate Program: An affiliate program is a form of advertising, on the web, that rewards the affiliates (self-selected advertisers) for driving traffic to the advertiser (PPC) or for subsequent transactions (CPA). An affiliate program uses a multi-level marketing concept where consumers (affiliates) attract additional consumers. Some affiliate programs are multi-tiered, thus increasing the income earning opportunities for the affiliates (rewarded for their traffic and the traffic of affiliates they recruit). Affiliate Marketers have the option of developing their own in-house affiliate program (Amazon.com and bn.com are examples) or joining one or more of the large affiliate networks (Beefree, Linkshare or CommissionJunction). Affiliates have the potential to earn significant money, if done correctly. This book store is the author's example of an Amazon affiliate. Marketing vehicles may sign up for an affiliate program to use their excess advertising inventory (unsold banners). Since affiliates link directly to the site which sponsors the program this increases the number of links into the site which can have a positive effect on the ranking of the sponsoring site in search engines (good for search engine optimization.) Affiliate links also have a positive branding effect for the sponsoring site. Affiliate Program Directory: A comprehensive listing of merchants' affiliate programs. The directories are typically categorized by industry and include the typical payout or commission rates. Click here for a sample list of affiliate program directories. Affiliate Software: A software program such as Affiliate Wiz for running and managing an affiliate program. This typically includes signing up affiliates, managing links, tracking impressions, clicks, sales, leads. This also includes paying affiliates, etc. Affiliate Solution Provider: 3rd party company that provides an affiliate tracking solution on a hosted basis. Typically an affiliate software solution is hosted by you with your web site. With an affiliate solution provider, they provide the hosting for you. Affiliate Tracking: The process of tracking a link uniquely by affiliate using an Affiliate Link. Aggregator: (News Reader) Aggregator is an application, either for the web, windows, mac, or linux, that aggregates dynamic content (RSS or Atom files) for the subscriber to view. The dynamic content is typically generated by blogs, news organizations or other sources interested in distributing news to subscribers, using the XML format to generate the RSS feed. It becomes an effective means for users to manage their view of updated news across the web. Users control which 'feeds' they subscribe and unsubscribe, this channel is also spam free. Aggregators are one of the web 2.0 technologies. Examples of web-based aggregators include bloglines and NewsIsFree. Algorithm: In the context of search engines, it is the mathematical programming system used to determine which web pages are displayed in search results. Alpha/Beta: The terms alpha and beta refer to releases of software that are typically not ready for commercial use. Alpha refers to the very early release, which is typically very buggy and only released
239
INTERNET USERS HANDBOOK
to a few people who are internal to the organization. It is helpful, in development, to get feedback very quickly from the hacker community, or potential customers with the beta version. Releasing a beta version has become standard practice with the evolution of the Internet as a mode of distribution for the software. Companies are also apt to leave releases of products in beta for a while (Google). It is a part of the development model for open source software. API: API refers to Application Programming Interface. It is the interface that gives program developers access to develop programs that work on a particular platform. Thus for Microsoft's Windows platform, the API is win32. To develop a program to run on the windows platform, you must write to the win32 API, thus the win32 API is the software developer's platform for windows. By encouraging other software programmers to develop to your platform, you are able to encourage lock-in as more people become dependent on the platform. A key strategic issue for a software company is whether to develop a developer's community, which builds software to its platform, or whether to keep the development internal to the organization. Architecture: Architecture refers to the planning phase of the software development process, much like architecture refers to the same in the process of building a house. The builders are the coders of the product, once it is architected. This is an extraordinarily important phase of the overall development of the product, and consists of thoroughly understanding and articulating the needs of the users (of the system) and the coders (for the system). This serves as a roadmap for current and future development for the product. Poor architecture may not be apparent during early releases of the product (the alpha and beta phases), but as the product evolves and newer versions are created, architectural decisions will become more impactful to development. This has been cited as a cause for the demise of the Netscape development process. Associate: Synonym for affiliate. Asynchronous/Synchronous Communication: Direct communication, where all parties involved in the communication are present at the same time (an event) is a form of synchronous communication. Examples include a telephone conversation, a company board meeting, a chat room event and instant messaging. Asynchronous communication does not require that all parties involved in the communication need to be present and available at the same time. Examples of this include email (the receiver does not have to be logged on when the sender sends the email message), discussion boards, which allow conversations to evolve and community to develop over a period of time, and text messaging over cell phones. Auction Pricing System: Using an auction pricing system, sellers are not constrained by having to fix a price without knowing what the market will bare (traditional pricing methodology). If a seller sets a price too low, using a classified advertisement for example, the demand will be high and the product will be purchased. The seller, however, will not get the most revenue the market would have paid if the buyers had had to compete for the purchase. The buyer who wanted the product most (willing to pay the highest price) would not automatically receive the product. Conversely, if the seller advertises too high a price, using a classified advertisement, the product will not sell. By allowing buyers to bid up the price from a low price point, the product will sell to the highest bidder (assuming it clears a minimum asking price). The auction pricing system is a dynamic pricing model, much like the reverse pricing model. Game Theory can impact the strategies involved in setting
240
INTERNET USERS HANDBOOK
a starting price (for the seller) and bidding strategies for the buyers. Examples include: EBay and QXL.com. Autoresponder: Autoresponders are used to send an automatic email in response to an incoming email message. This allows for the sender to know the email has been received, which is important due to the asynchronous nature of the medium. They are often used by company employees to alert people they are away on vacation, thus delaying a potential response. They can also be used effectively in customer service by indicating to the consumer: The query was received Other alternate means to find information A response timeframe Additional marketing material Note: An autoresponder can also be used to distribute a digital product, as a response to an email request. Average Costs: The average cost of a unit of product is made up of its fixed costs / # units produced, and the variable cost per unit. With digital products, where the variable costs are very small (and in some instances zero), the average cost of the product declines as more units are produced and sold. Thus the market leader for a product typically has the lowest average cost per unit. This allows the leader to have increased margins, and increased flexibility to lower price. This is one of the reasons why first-mover advantage can be so important. Auto-Approve: Affiliate application process whereby all application are immediately accepted/approved upon submittal by the affiliate. This term can also be used to describe the process of automatically accepting all sales recorded by affiliates. B2C: B2C refers to business-to-consumer trade, retail trade. Similarly B2B refers to business-tobusiness, distribution channel (value chain). C2B refers to consumer-tobusiness, and uses a reverse pricing model (Priceline for example). C2C refers to consumerto-consumer, an auction-style model (eBay for example). Bandwidth: [band] Bandwidth refers to the capacity of the connection of the Internet. Typically a user's connection to the ISP is the aspect of the Internet experience with the least bandwidth (last mile issue.) The closer to the Internet backbone, the greater the bandwidth of the connections. Bandwidth is also shared among users of an ISP, thus the activities of one user can have a negative impact on the experience of all other users. File sharing sites have been blocked (by firewalls) from some ISPs (universities) for their penchant for hogging bandwidth. Banner Ad: An electronic advertisement or billboard such as an animated GIF, Flash Movie, JPEG that advertisers a product, service, or web site. Banners: Banners, a form of Internet advertising, were the primary form of advertisements on the web (this is now challenged by text advertisements). The standard banner usually appears at the top of a web page, and will link to a target web page, that may be the homepage of the advertiser or a target page developed by the advertiser that is more directly relevant to the message of the banner (a better use). The IAB has developed banner size standards. Banner Exchange: A banner exchange program is a program designed to allow marketers to exchange banners (a form of bartering) to enable marketers to promote their sites without the outlay of cash. A program typically allows a marketer to display one advertisement, across the network, for every two advertisements it hosts on its site. Unlike a straight exchange with one entity, exchange programs allow
241
INTERNET USERS HANDBOOK
for the possibility for the banner to be displayed on many web sites (those sites that participate in that particular network). The Free Banner Exchange Megalist is a good resource for identifying these exchanges. Barrier(s) To Entry: Barrier to Entry refers to the costs incurred for a new entrant to enter a marketplace. Examples include fixed costs such as the development of a factory (for traditional manufactured goods), branding, and lock-in established by current competitors in the form of switching costs. Barriers to entry can also refer to any "hidden" cost established to reduce freedom of choice. Traditional retailing environments that had relied on geography as a competitive advantage now need to build barriers to entry to protect their client base from Internet-based businesses. Barter: Bartering is the trade of goods from one enterprise to another, without the transfer of payments. Many Internet businesses trade their products and services, to avoid payments and / or to stimulate demand, at the early stages of their life-cycle. This has also become common practice for the trade of banner advertisements. Banner exchange programs enable small advertisers to exchange advertising space, but large enterprises are also involved in this practice. Bartering was the means of exchange between traders and customers in markets, before money was developed as a medium of exchange. Bartering is therefore closely associated with very early market development! In the early model, money was developed to make markets more liquid. With the early Internet, bartering was used due to the lack of liquidity of many Internet businesses. Bookmark: Bookmark is a term used to suggest a user saves the location of a web page in order to return to that page in the future. It stems from the bookmark option in the Netscape browser. The dominant browser Internet Explorer has the same option, called favorites. Since it is easier to ask someone to "bookmark" a page than to add a page to a "favorites" list, despite Internet Explorer becoming the standard browser, the "bookmark" term has persisted! Bots: Bots are software programs developed to help the user search the web to identify and compare products for purchase. Examples include: Froogle, MySimon, DealPilot.com, FrictionLess.com, and Epinions.com. They are also referred to as intelligent agents. They are also used as software for Forex Experts Brand: A brand is a product from a known source (organization). The name of the organization can also serve as a brand. The brand value reflects how a product's name, or company name, is perceived by the marketplace, whether that is a target audience for a product or the marketplace in general (clearly these can have different meanings and therefore different values). It is important to understand the meaning and the value of the brand (for each target audience) in order to develop an effective marketing mix, for each target audience. The value of the brand for a web-based company may have heightened importance due to the intangible nature of the web. The economic value of a brand can be determined by looking at what a company is able to charge for a product, over and above a generic alternative product, in its marketplace. Break Even Analysis: Break Even Analysis refers to the calculation to determine how much product a company must sell in order to break even on that product (revenue = costs). It is an effective analysis to measure the impact of different marketing decisions. It can focus on the product, or incremental changes to the product to determine the potential outcomes of marketing tactics. The formula for a break even analysis is: Breakeven point ($) = (Total Fixed Costs + Total Variable Costs) Total Variable Costs = Variable cost per unit x units sold
242
INTERNET USERS HANDBOOK
Unit contribution (contribution margin) = Price per unit - Variable cost per unit. Broadband: Broadband refers to the ability of the user to view content across the Internet that includes large files, such as video, audio and 3D. Broadband refers to an increased ability to do so. The term narrowband can refer to the inability to do so. A user's broadband capability is typically governed by the last mile issue, the connection between the ISP and the user. Users increasingly have access to broadband such as cable modem and DSL access. Once broadband is no longer an issue, the web is likely to become much more useful, and users of the Internet will likely change their behavior in terms of what they do with the Internet, as a consequence of being able to leave the connection open all the time, rather than having to dial-in and leave. Browser: A client program (software), such as Internet Explorer, Netscape, or Opera, that is used to look at various kinds of Internet resources. Bugs: A bug is the term used to describe a coding error in a computer program. Bugs can be discovered throughout the development process. As systems are tested with live users (through alpha and beta versions), and systems become more interrelated, bugs tend to surface that were not recognized during the early stages of development. Bugs are also included in commercial products that have already been shipped. Once discovered, companies will use patches to update the software for the users. Bundling: Product Bundling refers to the bundling together of more than one product for a sale. This is very common for digital products, where the marginal costs of each product is very low. If most of the marginal cost is associated with packaging and distribution, this is further reduced when the products are bundled together, as they share the same costs of packaging and distribution. Thus the incremental cost to the firm (i.e. Microsoft) for bundling together additional software products is very small (actually zero aside from any opportunity cost). Thus a suite of products may allow for greater market penetration into different software markets than if the software was sold separately. For software that is not currently used by the consumer, but is purchased through a bundled package, it works to lock-in the consumer once he/she decides to use that category of software. Thus bundled software can ensure strong market positions across multiple markets. Burn-Rate: Burn-rate refers to the amount of money a company spends from month to month (money burnt) in order to survive. Thus a burn-rate of $50,000 would mean the company spends $50,000 a month above any incoming cash flow to sustain its business. Entrepreneurial companies will calculate their burn-rate in order to understand how much time they have before they need to raise more money, or show a positive cash flow. Business Plan: A business plan is a document that articulates a new business idea (and its business model). It is used to gain interest in the business idea for potential investors (Venture Capital investors for example), as well as used as a guide for the team to build out the business. Particular focuses of the plan include the idea itself, the management team, the marketing mix, and the cash flow projections. Business Model: Business Model is the business' value proposition, and how it determines to satisfy that value proposition. Essentially it refers to the entire process of how it intends to do business with its customers profitably. Web sites need to have a specific business model. Many company web sites are operated on a ROI model, presuming the web site serves multiple marketing functions. Alternatively search engines operate with an advertising revenue business model (PPC). In fact Google's entire business model relies on its Google Adwords program. News sites may combine advertising revenue with site subscriptions
243
INTERNET USERS HANDBOOK
for a business model. The subscriptions may or may not be paid subscriptions, and the data acquired may or may not be resold to third parties to generate additional revenue streams. Software vendors need to determine whether their business model should focus on the sale of the software, or its after sales support. If the former, this can present potential cash flow problems in the long run as the software requires additional support. Call to Action: Call to Action is the action that is requested by a marketer's content (either from an Internet advertising or web-site copy for example). This may be to click-through to enter a contest, enter a survey to win a free prize, or purchase a product. Caching: Caching is the process used to save web content that is served, for viewing at a later time (cached on the client machine) or for others to view (popular pages, cached at the ISP for others to view who use that ISP to connect to the Internet.) Google also caches content that is available for browsers' to view with the search results. The principle reason for caching is to improve the web browsing experience by increasing the speed web pages can be presented to the client. Caching does not work well if web pages are updated often, as older copies are cached which are then served to browsers. Caching is also an issue for content providers who wish to remove their content from the Internet. They do not control the caching process and thus are unaware of the extent to which the content has been cached across the Internet. Cannibalization: Cannibalization refers to the notion of a company making a business decision that will have a negative impact on either a current product within the same product line or member of a distribution channel (or entire channel, via disintermediation). This type of decision is typically designed to allow the company to survive in the long-term, and avoid having its products challenged by competitors' products as technology progresses. Captive Market: A captive market is a group of consumers who have limited choice in terms of the products they can select/purchase (no choice)! This type of market was common during the production era when there was a limited supply of goods (and greater demand). It occurs when the market is monopolistic, thus there is only one supplier in the marketplace. This is more likely to occur with digital products (Microsoft is a good example of this). It can occur when a marketer has achieved significant lock-in for its installed-based. Thus the switching costs for the consumer to try a competing product become prohibitive. Cash Flow: Cash flow is the collective outcome of all incoming and outgoing cash over a fixed period of time. Having a positive cash flow is critical to the long term survival of the company, in the short term a company can survive with a negative cash flow if this is seen as only a temporary situation. A negative cash flow is also known as the burn rate and is common at the beginning of a company's life. Channel Conflict: Channel conflict is the outcome of developing additional channels between the producer and consumer (often direct in terms of using the web) that targets the same group of consumers. This creates a "conflict" with existing channel members along the value chain, which are concerned with getting disinter mediated. This is a common problem for legacy businesses as they explore the web for commerce. Charge Back: Chargeback is an invalid sale that results in the affiliate's commission being forfeited. Click Fraud: Click fraud comprises clicking on a link that either provides monetary gain for the clicker or adds cost to the marketer whose link is being clicked (a competitor of the 'clicker' for example). This process can be automated. This causes problems for links that are based on a PPC model, and is thus a problem for search engine advertising programs and affiliate programs. The problem is compounded in
244
INTERNET USERS HANDBOOK
search engine marketing as the host, who manages the advertising programs, actually benefits from the rogue behavior. Click-through: The action when a user clicks on a link and follows through to the merchant's web site. Click-Through Ratio (CTR): percentage of visitors who click-through on a link to visit the merchant's web site. Client: The client refers to the user end of the web. Thus the web browser (Internet Explorer or Firefox) serves as a client. This is in contrast to the server, which hosts the web information. Client-side Scripting: Client-side scripting is used to present content to the web browser, with which the user can then interact, or content that data from the users' machine interacts (date / time etc.). Client-side scripts rely on the capabilities of the client machine / browser, which contrasts with serverside scripts which rely on the server for functionality. Co-branding: situation where affiliates are able include their own logo and branding on the pages to which they send visitors through affiliate links. Co-branding This is a system that provides your website's content with the look of your partners website creating a seamless transition for the visitor. Commission: Income an affiliate earns for generating a sale, lead or click-through to a merchant's web site. Sometimes it is called a referral fee, a finder's fee or a bounty. Cookies: small text files stored on the visitor's computer, which record information that is of interest to the merchant site. In affiliate software cookies are utilized to track which affiliate the web visitor came from and which banner or link they clicked. They can also store the date/time of the click for purposes of tracking the time elapsed between a click and a conversion to a sale or lead. Cookie Expiration/Cookie Retention: When a cookie is planted on a web browser, a date when the cookie expires is defined. This date is important because affiliate sales can only be recorded before the cookie expiration date. This period will also determine if repeat sales will be recorded. Conversion Rate: Percentage of clicks that result in a commissionable activity (sale or lead). CPA (Cost Per Action): The amount of cost for a conversion such as a sale or lead. CPC (Cost Per Click): Cost of an individual click when paying on a per click basis. CPM (Cost Per Thousand): The cost of 1000 banner impressions. CPO (Cost Per Order): Same as CPA but refers specifically to sales. Customer Bounty: Pays the affiliate partner for every new customer that they direct to a merchant. Collaborative Filtering: Collaborative filtering is a process used to match data of one user with data of similar users, based on purchase patterns, in order to generate recommendations for the user for future purchases. Amazon is a good example of a company that uses collaborative filtering in order to make its recommendations, based on a customer's prior purchases and the purchases of those who have purchased similar products. This is an example of market segmentation, based on customer behavior, rather than the more traditional metrics of demographics and psychographics. Contextual Marketing: Contextual marketing is marketing that occurs in the context of when a person is more likely to be interested in the product/industry. Thus, a page sponsorship can be considered contextual, as the viewer has elected to view the page, and assuming the sponsorship is for a product that is related to the content of the page, the product has the right context (the viewer self-selected to view the content).
245
INTERNET USERS HANDBOOK
Text advertisements that are relevant to the content of the web page on which they appear are another example of contextual marketing. An example of this is the advertising programs run by search engines that have advertisements served based on the keywords that the user uses to search. Contextual Marketing is becoming more popular with increasing use of search engine marketing, and will only gain greater strength with the evolution of wireless marketing (mcommerce). Wireless marketing will take advantage of knowing where the consumer is located using GPS. This can then translate into marketing messages that have direct relevance to the consumer as the messages relate to the context of the consumer at the point in time they are being delivered. Chat Rooms: See Discussion Boards Contribution Margins: Contribution margins (or margins) refer to the amount of revenue per product that is available to "contribute" towards the fixed costs and the profit of the company. Since, for digital products, the variable costs are typically very small, or zero, most of the revenue earned from the sale of a product form the contribution margin. Assuming the contribution margin (unit price - unit variable cost) > 0, then the product merits marketing, since the fixed costs are sunk. This also assumes the product does not cannibalize sales from another product in the product line, if so, the opportunity costs need to be considered. Cookie File: The cookie file is a file that resides on the client machine. It contains data passed from web sites, so that web sites can communicate with this file when the same user (client machine) returns. The web site only has access to the part of the cookie file that represents the interaction with that particular web site. The cookie file has caused some issues with respect to privacy. Considering that as consumers, we do not know what information is being stored in the file, we should become concerned! The cookie file was first developed in order to help sites with the transaction process of the web. Without a cookie file, web sites are not able to track a single user's path through a web site, thus a transaction that required multiple pages (as most do) would simply not be workable. Copyright: Copyright refers to the rights provided to the author of certain types of intellectual property, including software. The author uses a license to establish how others can use the software. Even free software will include a license to ensure the work remains free. CPM, PPC, CPC, CPA: [cpm] CPM (Cost per 1,000), PPC (Pay per Click), CPC (Cost per Click) and CPA (Cost per Action) are types business models for calculating the charge for pages (advertisements) being served. CPM is a holdover from traditional media advertising, and does not take advantage of the Hypertext nature of the medium. It charges purely on the number of times the advertisement is served. It does account for branding effects that are not accounted for in the other models. PPC and CPC refer to a cost (payment) associated with each click on the advertisement to the target page. CPA is a cost associated with each lead created from a click on the advertisement (CPL), or each sale (CPS). Both PPC / CPC and CPA are much more accountable means of developing a price for the advertisement, and either are also used for affiliate programs and text advertisements on search engines. They become a variable cost in terms of generating the number of people exposed to the target page (this number is based on the CTR from the host vehicle), the number of leads generated (CPL) or the number of sales (CPS). The downside for the vehicles is they do not control the design of the banner (poor design = low click-through etc.) and they are not rewarded for the branding effect of the banner. Click fraud is also an increasing problem. CRM: (Customer Relationship Management) is a business strategy built around the concept of being customer-centric. The main goals are to optimize revenue through improved customer satisfaction via
246
INTERNET USERS HANDBOOK
improved interactions at each customer touch point. This can be accomplished by a better understanding of customers, based on their purchasing patterns and demographics, and better information empowerment at all customer touch points, whether with employees or other media interfaces. Cryptography: Cryptography is the field of securing data. It began with a focus on securing data in transit (data encryption), but has expanded to other areas such as digital cash and authentication (digital signatures and timestamps). The field of encryption pre-dates modern times (frequency analysis) but gained particular significance during World War II as a means to secure data from and listen to the enemy. It has become very important in the information age. A simple example of cryptography is the public key cryptography. The sender and receiver must have both a public key (to read the data) and a private key to encrypt the data. The public key can be made freely available to recipients of a message as long as the private key remains private. Encryption presents problems for governments which need to 'listen' to data transferred over the Internet. Governments need to do this to track illegal money transfers and listen to terrorist chatter for example. Thus governments prefer weaker standards of encryption than those who require data to be secure, such as those requiring legitimate security for ecommerce. Until 2000 the US Government restricted the use of "strong" encryption for export (encryption of over 56 bits in symmetric algorithms). This has now been relaxed somewhat unless the end user is from specific countries (i.e. Cuba, Iran, Iraq etc.) RSA Security - Crypto FAQ is a good resource for Cryptography. CTR: CTR (Click-Through Rate) is the number of times an advertisement is clicked upon over the number of times the advertisement is served. Typical click-through rates have been declining (a click through rate of 1% would be very high). While click through rates help determine the effectiveness of the online advertisement, advertisements also contain a branding impact. The click-through rate will determine the cost of an advertising campaign that was based on PPC / CPC and CPA. CSS: CSS (Cascading Style Sheets) are used by web designers to describe the design of the web page (entire web site.) Rather than rely solely on HTML (structure), CSS allows for more central control such that making one edit in the CSS file can make consistent changes across an entire web site. CSS content can be included as a separate file (pointed to in the header of the web page); included entirely in the header of the web page; or included directly in the body of the web page. CSS also allows for creating different presentations dependent on the media, so a document that is printed out can be printer-friendly versus the same document on screen. Cybersquatting: Cybersquatting refers to the behavior of acquiring a domain name with the principle purpose of reselling that domain name. The resale could be to an entity that would be willing to pay a higher price (typically a trademark holder); or an entity who had previously used the domain name but inadvertently lost it as a consequence of not reregistering. Diffusion Process: The diffusion process refers to the process of adoption of new products by the consumer marketplace. The consumer marketplace is segmented into four groups: innovators (2.5% of population), early adopters (13.5%), early majority (34%), late majority (34%), and laggards (16%). Thus innovators are more likely to adopt a new product earlier than the early majority etc. This has implications for target marketing with new products. Digital Cash: Digital cash is money exchanged only over the network (web). PayPal is a provider of digital cash. Smart cards are also used to provide electronic money exchange, more frequently used outside the US. Encryption is used to maintain the integrity of digital cash.
247
INTERNET USERS HANDBOOK
Digital Divide: Digital divide represents the gap between those who have access to the Internet and those who do not. Those who have access to the Internet typically come from wealthier segments of society, and wealthier countries. Access can be defined in terms of access to the physical infrastructure of the Internet, or access via literacy. Access to the Internet itself creates significant advantages to those who have it, further exacerbating the divide. Digital Products: Digital products are intangible products that can be downloaded over a digital network. They have zero copy costs, and users can make perfect copies. The cost structure of digital products (high fixed costs that are sunk, and tending towards zero marginal costs) in conjunction with the above features changes the economics of digital products vs. traditional goods. Diminishing Returns: Diminishing returns refers to the notion that the return that a company receives for additional effort decreases as the number of units / output increases. This is typical of industrial goods, but is in contrast to the phenomena of network effects and increasing returns for digital goods. Diminishing returns explains why industrial companies become more inefficient once they grow over a certain size. Thus firms do not compete as effectively when in a large monopolistic market than they do in an oligopolistic market (car company for example) assuming the size of the market is over the scale limit that traditional firms can operate efficiently. Directory: A directory is a web site that focuses on listing web sites by individual topics; it is a quasi Table of contents. A search engine lists pages, where a Directory (such as Looksmart or The Open Directory Project) lists websites. Discussion Boards and Chat Rooms: Discussion boards allow for asynchronous discussion between 2 or more people over a period of time. Chat rooms are designed for synchronous discussion at one time. Discussion boards are typically available for review, at any time, chat rooms have no data until a chat session begins. Discussion boards are useful to allow many people to become involved in online "conversations" over a period of time. A site that has used discussion boards effectively is slashdot.org. This site is a community that serves as a meeting place for those interested in the advancement of all things digital, as they say: "News for nerds!" The site's content essentially is created by its community, which in turn becomes more closely associated with the site as they are developing the site. Other sites attempt to achieve this without as much success. Slashdot's success lies in its structure: initial discussion content short, but with enough information to establish context, this allows discussion to follow. The ClueTrain Manifesto, while being radical in its approach and view points, makes a compelling case for commercial sites to include a discussion board to allow for conversations among consumers, and between consumers and employees. The Student 2 student aspect of the Wharton MBA Admissions site follows this thesis. The content on this site is content marketing could not pay for, and comes from credible sources. Chat Rooms are useful for gathering people together for "quick" events that are centered around specific topics. They are very good for brainstorming events, and to resolve problems that need quick discussion. Chat rooms are often used in conjunction with discussion boards to satisfy communication needs of the organization. Unfortunately the terms, discussion boards and chat rooms, are often confused, people referring the two as chat rooms. Instant Messaging and blogging are other forms of communication evolving on the web. In fact, slashdot, noted above, is a blog in its truest sense, but behaves very much like a discussion board.
248
INTERNET USERS HANDBOOK
Disintermediation: Disintermediation refers to the potential for members of traditional value chains (distribution channels) to become obsolete as the producer markets more directly with its consumers using the web. This occurs with legacy businesses. While channels (using the web) are presumed to become shorter, in reality, the channels actually include different types of intermediaries (infomediaries) such as meta-markets (also referred to as industry portals) that help gather many industry players and consumers into a market space. Disruptive Technology: This is a technology that changes the industry in such a way that previous competitive and business rules change. Since the Internet has had such a profound effect on the fundamental rules of business, it can be considered a disruptive technology. CD technology was another good example of a disruptive technology. When CDs were introduced to the music business, they were a disruptive technology, changing the status quo, and requiring users to purchase new hardware, despite there being a significant installed-base of record players and record collections. P2P, and more recently iTunes are similarly changing the music industry and those that rely on CD sales. Domain Name: A domain name (also known as a host name) is an alphanumeric name that identifies a computer on the Internet. While it is possible to reach computers on the Internet by using the IP address, IP addresses are not easy to remember. Domain names provide an easily referenced way of reaching remote computers. The domain name is the first part of the web address or URL. For example, this web page's domain name is www.udel.edu The Domain Name Service (DNS) stores a database of mappings from domain names to IP addresses and performs lookups for the IP address when a domain name is used in a network request. To avoid network congestion, lookups are performed on root servers with current copies of the central directory. These root servers are further copied by ISPs. To register a domain name for the .com, .org, .biz, .net, .info and .name, you can use one of the accredited registrars, and their resellers. ICANN.org is the accrediting agency that approves resellers and resolves disputes. You can learn about information behind the ownership of a domain name by using the WHOIS service. ccTLDs (country code top level domains, such as .uk, .at and .fr) are handled independently and visiting the country's site is important to understand the rules. Domain names are an important branding tool for a business. Businesses are thus keen to protect their trademarks by acquiring their appropriate domain name(s). Cybersquatting is the behavior of a user who acquires a domain name for the sole purpose of reselling at a higher price. Clearly domain names can have significant economic value, the highest price reported to be $14m. Dynamic Pricing: Dynamic Pricing refers to a fluid pricing scheme between the buyer and seller, rather than the more traditional (and more recent, over the last 100 years) fixed pricing. Dynamic pricing is a legacy from the past that has lost its prominence with the advent of the industrial revolution and mass marketing and mass communication. Before the industrial revolution, most trade occurred in markets, with many buyers and sellers bartering for goods. Current and evolving models for dynamic pricing include the auction pricing system, group pricing system and reverse pricing system. Typically these systems will better reflect the true market value of the product involved, but also require additional work on the part of the purchaser. These systems will evolve more rapidly when better standards are established and when intelligent agents evolve. Not all markets will be served well with a dynamic pricing model.
249
INTERNET USERS HANDBOOK
E-Commerce: E-commerce refers to all forms of business activities conducted across the Internet. This can include E-tailing, B2B, intranets and extranets, online advertising, and simply online presences of any form that are used for some type of communication (customer service for example). Economies of Scale: Economies of scale refers to the notion of increasing efficiencies of the production of goods as the number of goods being produced increases. Typically the average costs of producing a good will diminish as each additional good is produced, since the fixed costs are shared over an increasing number of units. Due to economies of scale, larger companies have greater access to markets in terms of selecting media to access those markets, and can operate with larger geographic reach. For traditional companies, size does have its limits, where additional size actually increases costs to companies (impacts communications costs etc., diminishing returns). Thus many industries tend to operate more effectively in an oligopolistic fashion, with few large firms, rather than one monopolist. (This should occur even if the government allowed monopolists and monopolists behaved legally). Digital companies tend not to suffer from this scale limitation. Ecosystem: An ecosystem is a system whose members benefit from each other's participation via symbiotic relationships (positive sum relationships). It is a term that originated from biology, and refers to self-sustaining systems. The bumblebee hive is an example of an ecosystem, highlighted in Bernd Heinrich's book, Bumblebee Economics. The bumblebees' hive is a living system with one goal, to gather enough energy to ensure the survival of the bumblebee's genetic information. Bumblebees (unlike most other species) live in colonies and depend on each other for survival. Bumblebees extract pollen for protein and nectar for their sole source of energy from neighboring plants. Plants, in turn, rely on bumblebees to inadvertently brush pollen from one plant to another, to enable the plants' reproduction process to begin. The relationship between the bumblebee and the plant is symbiotic, as each benefit from each other's participation. The bumblebee hive goes through a life-cycle, through the year. Entering the fall the queen bee lays eggs that are fed a different diet. These eggs turn into virgin queens and males. When the frost hits, the remaining worker bees die as does the queen, the virgin queens and males fly off, mate, the males die and the inseminated queens seek shelter through the winter. The process then begins again. As it applies to business, an ecosystem can be viewed as a system where the relationships established across different industries become mutually beneficial, self-sustaining and (somewhat) closed. This is clearly the case for Silicon Valley with the entrepreneurial industry, the venture capital industry needed to fund the entrepreneurial industry, and Stanford University (birthplace of Google and Yahoo! etc.), supplying the human capital needed to develop innovative/creative ideas and technologies. The goal of this ecosystem is to generate entrepreneurial ventures. Once an ecosystem is established, and is able to take first-mover advantage, it becomes very difficult for other regions to emulate. The region exhibits network effects and is able to establish lock-in since the switching costs associated with moving to another region are prohibitive. The collective costs of many moving out of the region (i.e. if another region tried to incentivize a large move) would be prohibitive. Thus current members have a clear incentive to remain, and new would-be entrepreneurs, venture capitalists and students interested in this industry have a significant incentive to relocate to this region. Email Campaign: These campaigns contain appealing content concerning your product, and are targeted at a specific market.
250
INTERNET USERS HANDBOOK
Email Link: An affiliate link to a merchant site in an email newsletter, signature, or a dedicated email blast. EPC (Earnings Per click): Average earnings per 100 clicks. A relative rating that describes the ability to turn clicks into commissions. E-tailing: E-tailing refers to retailing over the Internet. Thus an e-tailer is a B2C business that executes a transaction with the final consumer. E-tailers can be pure play businesses like Amazon.com or businesses that have evolved from a legacy business, Tesco.com. E-tailing is a subset of e-commerce. eWallet: eWallet is a system that stores a customer's data for easy retrieval for online purchases. Since completing forms as part of an e-tail transaction can be a reason for aborting a transaction (shopping cart abandonment), an eWallet service can reduce this inconvenience for the consumer. Extranet: Extranet refers to a group of web sites, belonging to independent entities, that are combined together in order to share private information. This is in contrast to an intranet, which is a private site that is only accessible to one entity. Extranets are used in the supply chains to allow for more effective communications along the supply chain. Firewalls are used to protect the extranet from those excluded access. Extranets are replacing proprietary standard networks that are considerably more expensive to establish, and therefore were only used by large organizations (EDI). FAQ: FAQ is an acronym for Frequently Asked Questions. A FAQ document is a document found on company web sites that addresses basic questions. These documents are updated from queries that come from the customers, so they should evolve over time. Filesharing: Filesharing refers to peer-to-peer technology that allows one user of the Internet to access files of another user of the Internet through a public directory. Before the advent of WWW, this was the primary form of Internet information sharing, through public (and private) FTP sites. It has now emerged as a methodology for sharing digital files across the web. Napster pioneered this, distributing music files. Others, such as gnutella are proving to be interesting distribution models for music etc. Filesharing is coming under increasing scrutiny for copyright issues. Think of a WWW model being a 24-hr shopping mall. The stores are web sites. They are always there. You can always go to the same place to find the same items. Peer-to-peer is more of a bazaar where the vendors come and go as they please. You never know what you'll find until you get there. The products aren't in the same place every time. All these wondering gypsies could pack up and leave town tomorrow and you'd be out there in the mall again, trying to track down where they went so you could go, too. Firewall: A firewall is a piece of software or hardware designed to serve as a barrier to exclude outside intruders, typically those on the Internet, access to internal content. Companies often adopt firewalls in order to keep their internal communications private (intranets and extranets). Firewalls can also sometimes prevent those behind the firewall communicating with websites on the Internet that require cookies for the transaction. First-Mover Advantage: The First-Mover Advantage refers to the advantage gained by the first company that enters a certain market. This advantage is exacerbated for digital products and markets. There are a number of reasons this advantage exists. A company that is able to increase sales quickly is able to reduce the average cost of the product, over other competitors. This allows the first company to have more flexibility with pricing, either reducing the price to make it less attractive for new entrants (increasing barriers to entry) or increasing the margin and therefore profit while prices remain fixed, this additional profit can then be used for further innovation.
251
INTERNET USERS HANDBOOK
The first-mover can also take advantage of the learning curve effect. First-mover advantage can be further successful if the company is able to achieve lock-in of its installed-base. Thus once lock-in occurs, it is more difficult for other marketers to attract those customers away from the first marketer. Risks of being the first mover include the opportunity for others to imitate and follow best practices (learn from any mistakes). First-mover advantage is not always sustainable, and Microsoft has been very effective at being the second company in many markets, and subsequently dominating those markets. A simple example of this was the Netscape's browser vs. Microsoft's Internet Explorer. Netscape was the first-mover, gaining upwards of 90% market-share, but was not able to sustain its position with the onslaught of Microsoft. Netscape did not establish ANY lock-in, either due to the user interface, or proprietary functionality and both products were essentially being given away, so there was no price advantage. Microsoft is clearly positioned to give a product away for the long-term to gain market share. Fixed Costs: Fixed costs refer to the costs associated with a product that are fixed over a number of units. Thus regardless of the number of units produced and sold, the fixed costs remain the same. Examples of fixed costs are rent on equipment, utility costs, and research and development costs. With digital products, much of the fixed costs are actually sunk costs, and therefore non-recoverable costs. A large portion of the costs associated with digital products are fixed, and sunk, and not variable costs, which are more typical of traditional manufactured goods. Break even analysis, which is a tool that determines the volume at which a company must sell a product in order to break even, distinguishes between fixed and variable costs in its calculations. Flexibility of the Communications Medium: The flexibility of the communication's medium refers to its ability to serve multiple roles for the marketer. Media typically are limited in terms of the types of transactions they can accomplish. TV is very good for reaching a large audience with a 30 second message, but is not useful for customer service. The web, however, is truly flexible. It can communicate information to multiple target audiences, simultaneously. It can provide and support customer service initiatives and it can be used to execute transactions. It is the first medium that can serve multiple roles simultaneously. The web also breaks the reach versus richness tradeoff of more traditional media. Forking: Forking refers to the notion that a software project may evolve in multiple directions as multiple people have different goals for the project. This may occur under the open source development model. It is highly discouraged, as it does not maximize the use of resources. A good leader of an open source project will develop a process to try to avoid this situation. An exception to this was the development of Firefox, a fork of the Mozilla Project. Firefox is now the Mozilla's main development focus. Free-Rider: The free-rider effect refers to the notion that non-contributors to a project can benefit from other people's work on the project. This effect is posed as a criticism of open source. The question is, does the free-rider effect negatively impact an open source project. Since free-riders do not actually diminish any resources as they use the product (open source software) and assuming they are not adding any additional costs to the project (asking questions etc.) then the answer is no. Free Software: Free Software is software that allows the owner the 'freedom' to use the software, and alter the software in any way he / she desires. Thus it is more akin to freedom of speech, rather than free as in zero cost (in fact, free software licenses can allow for the sale of free software under certain
252
INTERNET USERS HANDBOOK
conditions). Free software development has evolved from the early hacker culture, where all software was free software. Free software is distributed with its source code. Access to this source code allows developers to improve and adapt the code for the individual use. Developers that do modify the code may be required (via the software's license) to submit any modifications back to the initiators of the project (submitting a patch). This allows any improvements, or resolved bugs, to be included in new releases of the product. FTP: File Transfer Protocol (FTP) is a protocol used on the Internet in order to transfer files. It was a popular means of making files available over the Internet, either via public or private FTP sites, before the advent of the web. Site developers now use FTP to upload / download files to the server when making changes / additions to web pages. Game Theory: Game Theory is a theory of rational behavior of participants in interactive decisionmaking scenarios. It helps predict how other participants of the situation / scenario (game) will respond in certain situations, or to certain decisions. Understanding participants' responses ahead of a decision, should help the initial decision maker make better decisions. It is applicable in areas such as: open source development. Free-rider issues for example. Should you contribute resources when someone else may benefit without contribution? standards setting. Should you cooperate with your competitors to help expand and standardize the marketplace? dynamic pricing. Should you bid at a price point, and will that create a higher bid from someone else? competitor reactions to decisions. When making marketing decisions, you cannot only analyze how your customers may respond without considering how your competitors will respond, as this will in turn impact your customers' responses. GPS: Global Positioning System (GPS) is a satellite-based system that identifies the location of a receiver. This is useful in mobile commerce as it allows the marketer to design content based not only on the individual, but where the individual is at the point the message is delivered. GPS systems are also used in cars to provide mapping systems, which can also be aligned with appropriate marketing messages. GPS is a US-based system, the EU has recently announced the development of a competing system, Galileo. Group Buying Model: Group Buying Model refers to the notion that the Internet allows individual consumers to develop a community and participate in purchases by multiple people with similar needs. TogetherWeSAVE.com is an example (Note: Mercata and Accompany closed, signaling this model is not yet matured!) Individuals are now able to take advantage of purchasing economies of scale that previously were only afforded to large companies. This in itself helps the power shift away from the company, to the individual consumer, but when combined with the reverse pricing model can create a potent consumer weapon. The essay, COMsumer Manifesto, details possible implications. Groupware: Groupware refers to technology that allows for groups of people to communicate from remote locations. The Internet can be considered the ultimate open standard groupware technology! Applications typically included in groupware technology are calendars, discussion boards, project management tools, email facilities etc. Microsoft Exchange and Lotus Notes are the more common commercial applications. Hackers and Crackers: Hackers is a term used for those who have been closely associated with the development of the computer, outside of the traditional corporate structure, and the free software movement (also known as the Open Source movement). Those that help develop code to improve (or
253
INTERNET USERS HANDBOOK
create new) software, and share that code with fellow hackers. Hackers therefore make things. Crackers break things. Crackers are those who get their thrills by cracking software, creating viruses, and destroying things. Unfortunately media often confuse the terms, thus the term hacker, when mentioned in mainstream media, usually refers to crackers! The hacker philosophy is one of sharing, openness, and decentralization (a distinct disdain for bureaucracy), that helps the innovative process and increases the knowledge-base of the culture. The hacker culture typically has an antagonistic relationship with the corporate entities who dominate the technology industry (this used to be IBM, and now Microsoft). Their values and belief systems are not aligned with these bureaucracies (who hoard knowledge and turn it into their selfish gain, rather than share knowledge and believe in the freedom of knowledge). Along these lines, hackers believe in the selflessness in favor of the common good. Communities of hackers can be found at sites like Slashdot.org. Clearly this culture experiences network effects. The more people involved and contributing to a particular project, the more each person involved benefits from each others innovations. This clearly answers the question as to how the Linux operating system was able to become a more robust operating system (according to some) than the Windows operating system, in a much shorter time frame. Header: The header component of a web page comprises the title and the meta tags and any style sheet content (CSS). All elements critical for marketing and design of a web page. A web page includes two components, the header and the body component. The body component includes the content that is visible to the user. By clicking the "view" and then the "source" option of the web browser, you can see the header and body tags for this document. Hits: Hits refer to the number of files served when users access a web page. Total hits for a page will therefore equal the number of times the page is accessed X the number of files included on a page. Thus a page that includes one graphic file will serve two files when it is accessed; the html file of the page, and the image file the page calls. This is a metric that is often misused when media quote the activity a web page receives. (To double the number of hits, simply double the number of files the page includes.) Better metrics, for web analytics, include impressions and page views. Homepage: The homepage of a web site is the entry point to the site. It is the page that will usually have a web address (URL) that ends with .com, .edu, .org, .gov or .cc (the 2 letter code for the country outside the USA). The actual filename, in the above scenarios, is index.html Users can create their own homepages that may be subsidiary to the above, and therefore use a subdirectory, but using index.html as the filename is still better (otherwise viewers can see the files in your directory by typing that filename with the file path). While the homepage is designed to be the entry point to a web site, designers cannot assume that all viewers will enter the web site by that page. It is important to consider all pages as potential entry points, and design all pages to market the site online (search engine optimization etc.) and for easy navigation to find the homepage. Hypertext: Hypertext refers to the connectivity between web documents, which is nonlinear. Thus any part of the document (word or phrase) can launch another document, or another part of the same document, via a hyperlink. In this example, the word web is hyperlinking to an explanation of the word, which appears at the end of this dictionary!
254
INTERNET USERS HANDBOOK
HTML: HTML (Hypertext Markup Language) is the original and principal language of the world wide web. Invented by Tim Berners-Lee in 1990, it is a derivative of SGML. The W3C is the organization charged with ensuring the compatibility of HTML with competing browsers and other web languages. The following is a brief historical timeline of the development of HTML. To learn HTML two popular guides are NCSA's Beginners Guide to HTML and The Barebones Guide to HTML. You can also view the HTML used for this (and any page) by accessing 'view' 'view source' from the top left of your browser. HTML code: Refers to the lines of code that an affiliate places on their web page(s) for linking to the merchant's site. This HTML code contains the unique identifier that identifies the traffic as coming from the Affiliate's web site. Identity Theft: Identity theft refers to the stealing of information about a person that allows a second person to assume the identity of the first. Essentially this only requires knowledge of very limited information, including a social security number. While most Identity Theft still occurs through traditional means of scouring house hold waste materials, the threat of theft over the Internet is a concern for e-commerce. It can occur as data is in transit (for a transaction) or data that is stored on a company's site, that is stolen, or from phishing activities. Theft can also occur via Google hacking (i.e. documents that are available on the Internet that should not be available, but are easily found via the search engines.) Identity theft is a major concern for privacy advocates Impressions: Impressions refers to the number of times a page is accessed over a fixed period of time. Thus if a page receives 1,000 impressions per day, then that page is accessed 1,000 over the course of the day. This term is often confused with hits, which is actually an incorrect use of this term (hits and number of impressions would be the same if the page was simply a text page with no additional files associated with it). Page impressions also equals the number of times an advertisement is served, assuming a banner is served each time the page is accessed. Impressions are a metric used in web analytics. Increasing Returns: Increasing returns refers to the notion that the greater the size of the network, the greater the advantage of each participant of the network (network effects). Each participant of the network brings value to the overall network. This is in contrast to diminishing returns which refers to the greater the size (number of users) the less each participant can benefit from participation. Broad examples of increasing returns include an open source project (the more contributors, the better the product) and a proprietary communications device (the more users of the device, the more people with whom a user can communicate). Google's search engine experiences increasing returns. The more content it houses in its databases; the more links it has pointing to various sites on the Internet. In bound links are an aspect of the PageRank system that provides the Google results. These results therefore improve as the volume of content increases (this was not the case for more traditional engines like Alta Vista that were based principally on keywords only, which does not scale as well.) Another example of increasing returns can be seen with Amazon's recommendation system, via collaborative filtering. The more users that are using the Amazon system; the greater the integrity of the recommendation system. Infomediaries: Infomediaries are channel intermediaries that are based on the transfer of information using the web. They are replacing traditional intermediaries in many distribution channels. Infomediaries include meta markets, portals, search engines, and bots.
255
INTERNET USERS HANDBOOK
In-house: alternative to using an affiliate solution provider; building and managing your own affiliate program internal to your company. Typically this is accomplished by purchasing a 3rd-party product such as Affiliate Wiz. Installed-Base: The installed-base refers to the customer-base of digital products. The company will have records of these customers (demographic and purchase behavior), and will be able to use these records in order to try to monetize the installed-base. Companies try to develop switching costs, in order to encourage their installed-base to remain loyal. By estimating the life-time value of a customer in the installed-base, we can estimate the value of the company. Instant Messaging: Instant messaging is a form of synchronous communication that allows users, on a specific network (AOL Instant Messenger, ICQ.com and MSN Messenger for instance) to communicate with other users, on that network, by sending short messages. Instant messaging services also allow users to determine when other users are online. Given that users can only communicate with other users on the same network, these services are certainly good examples of services that take advantage of viral marketing. It is likely that, with time, these services may standardize, so users of one network will be able to communicate with users on another network. This model makes more sense, and is used for a similar service, text messaging on cell phones, more common in countries outside the United States. Internet Backbone: The Internet backbone is the term used for the connections of the Internet of the large ISPs (for example MCI, British Telecom and UUnet). These ISPs provide the fastest data transfer and will be the most heavily trafficked nodes of the Internet. They then connect to smaller, regional ISPs and so on. Intellectual Property: Intellectual property refers to the rights provided to the owner of an expressed idea; invention; authored piece of work; a process; or a name attached to a company or product. A copyright protects creative content such as books, software and art. The copyright controls the potential for reproduction of the works. A patent protects an invention and an innovative process. A patent provides exclusive use of the invention for a fixed period of time. This creates a monopoly for the invention. A trademark is a sign, name or symbol that distinguishes one company, or product, from another. It is designed to reduce customer confusion. Intellectual property is granted on a territorial basis, but harmonization is occurring via international treaties within the WTO for instance. Intelligent Agents: Intelligent Agents are "bots" designed to work for the user in terms of executing transactions (typically search queries at this point) across the web. It is assumed that as Intelligent Agents become more sophisticated, they can accomplish more complex tasks for their users. Once they understand their users' requirements, they can act somewhat independently of user interaction, in terms of making online purchasing decisions and other tasks that currently require significant search and user decision making processes. Intelligent Agents will also become more useful as the semantic web develops. Interstitial Pages: Interstitial pages are a form of online advertising that appears between web pages that the user requests. Thus when a user elects to enter or exit a web-site, a page appears with its advertisement, in place of the requested page, the user then needs to select from that page to receive the page requested (or the advertisement page will disappear after a fixed time). This is a form of interruption advertising (similar to broadcast models) but this form of web advertising breaks information design rules, as the user had a certain set of expectations when making the page selection, the interstitial page did not match expectations.
256
INTERNET USERS HANDBOOK
Intranet: An Intranet is a network based on the Internet TCP/IP open standard. An intranet belongs to an organization, and is designed to be accessible only by the organization's members, employees, or others with authorization. An intranet's Web site looks and acts just like other Web sites, but has a firewall surrounding it to fend off unauthorized users. Intranets are used to share information. Secure intranets are much less expensive to build and manage than private, proprietary-standard networks (EDI). IP Address: An IP address is a numerical address of the computer broken into 4 groups of 3 digit numbers lower than 254. In most cases, these addresses are unique for each Internet connected computer throughout the world. Originally, addresses were obtained from Internet's Network Information Center (InterNIC) and later, in the Americas, the American Registry for Internet Numbers (ARIN). Today, only large ISPs are eligible to obtain addresses from ARIN, everyone else must request and address from their ISP. There is an exception to the uniqueness of addresses: Specific groups of addresses are set aside for use on internal networks for machines not connected to the Internet or trying to conserve address space. These addresses are either 10.x.x.x, 172.16.x.x, or 192.168.x.x. Use of these addresses is becoming more popular due to the shortage of addresses, which makes individual addresses expensive to obtain and keep, and the costs associated with changing all network addresses when changing ISPs, and the popularity of Internet connection sharing in small business or home networks. The IP address can also be used to help determine from where a web browser is located. This enables sites to present content specific to the location of the browser. For example Amazon is able to present amazon.co.uk content to browsers who are accessing the site from the UK. Sites can also restrict access to a range of IP addresses, therefore Google is able to limit IP addresses originated in China to google.cn. Similarly sites can present unique content to individual IP addresses based on previous activity with that IP address. This helps with personalization. As a web browser, we access a computer on the web by calling the domain name, which masks the IP address. Domain names are easier to recall. Domain names serve as the first part of the URL (web address). IPO: Initial Public Offering (IPO) refers to the offering of stock in a company to the public through a public market. NASDAQ is a popular market for e-commerce related companies. The IPO of a company serves as a significant liquidity opportunity for early investors, including founders and the Venture Capital investors. Internet: This is the network of networks, developed in the 1960s as a result of a US defense industry project DARPANET. It encompasses what we now know as email, Usenet Newsgroups, the Web, FTP and Telnet. ISP: ISP (Internet Service Provider) is the access consumers have to the Internet. Commercial ISPs include companies like AOL. There are many regional ISPs, and students can consider their University as their ISP if that is how they access the Internet. The connection between the consumer and the ISP is typically the slowest aspect of the Internet (also known as the last mile problem). The ISP will then have a connection to the backbone of the Internet, which is essentially a collection of larger ISPs (MCI, British Telecom, UUnet) via a T1 line or similar. Keyword: Keyword is the term used for words included in a web page that would match words used by web surfers in finding that web page (via a search engine). Identifying appropriate keywords and using them on a web site is important for search engine optimization. Keywords can simply be words included in the body text of the document, or added to the header using meta tags to increase the number of
257
INTERNET USERS HANDBOOK
keywords. Using keywords in the title tag is also important. Selecting keywords, that match your target audiences' use of the web when searching your product, is a critical marketing tactic. A singular word or phrase that is typed into a search engine search query. Keyword mainly refers to popular words which relate to any one website. For example, a web site about real estate could focus on keywords such as House, or phrases such as Home for Sale. Last Mile Issue: The Last Mile issue refers to the connection between the user and the ISP, which is typically the slowest aspect of the Internet access. As with a chain, the quality of access is governed by the weakest link, thus the slow connection impacts the entire web browsing experience. This issue evolved due to the lack of competition in the telecom industry, until very recently. Therefore technology innovation was not as rapid (read very slow) compared to other innovations governed by Moore's Law. Some users (in the U.S.) typically connect from home with a 56K modem. Broadband access, via cable modems and DSL technologies are beginning to become more widely adopted. Learning Curve: The learning curve (also known as the experience curve) represents the outcome of a company's experience when developing a product. As the company becomes more experienced, it is able to develop a better product, and / or develop products more efficiently at reduced cost. The learning curve effect has a significant role in helping companies benefit from first-mover advantage. Later entrants into the marketplace have a difficult time overcoming the experience advantage, as firstmovers release additional versions of the product. Legacy Business: Legacy Business refers to a traditional business that develops a web presence to transact business. Barnes and Noble is an example. This is in contrast to a pure play business, which is developed as a new entity for the web, and had no prior presence, such as amazon.com. License: A license is used to allow the author of a piece of software (intellectual property) to establish the rights of a user in terms of the copy of that software that contains the license. Unlike tangible goods, which are clearly limited in terms of what an owner can do with the product, digital goods are easy to make perfect copies. It is therefore important to establish limits. While the user may have purchased a digital copy, this does not imply freedom of use of that copy. The license will detail what the user is able to do (in terms of resell, number of machines the software can be applied, making modifications to the software etc.) The free software movement (also known as open source) has created a set of licenses that creates greater freedom of use of software, which is more appropriate for innovation among the hacker community. Lifetime Value: Lifetime Value of the Customer determines the value of a customer to a firm, over the lifecycle of that customer. This removes the focus on individual transactions with customers and has become increasingly used with the developments of technology and market research, and thus the ability to focus on narrower target markets, even to the individual consumer in some cases. Lifetime Value is an important measure used for relationship marketing programs. Lifetime Value of Customers was a popular metric for Internet firms as they built their customer-bases. In order to calculate the Lifetime Value, the company needs to determine the cost of customer acquisition, and the cost of customer retention, the average lifetime of a customer, and the average value the customer provides over its lifetime. It is important to distinguish between customer acquisition and retention, as this will allow marketers to understand the true value of a specific marketing campaign (cost of acquisition), and the value new customers can bring over their lifecycle (value to company - cost of retention).
258
INTERNET USERS HANDBOOK
The Lifetime Value of the Customer = The revenue provided to the company by the customer over its lifetime - (Cost of Customer Acquisition + Cost of Customer Retention). Link Exchange - When two websites swap links to point at each other. Link Popularity - A count of the number of links pointing (inbound links) at a website. Many search engines now count linkage in their algorithms. Lock-in: Lock-in refers to the ability of companies to ensure their customers do not switch to competitors, thus switching costs can establish lock-in. Switching costs can be established in many ways. The usability of a product can establish lock-in for that product, as customers learn how to use the product, they don't want to reinvest in learning how to use competing products. Wall Street Journal is a good example of trying to establish this type of lock-in. It heavily discounts its product to the education market, hoping that as people get used to getting their business information via the Journal, they will continue to do so after they graduate and begin working. The user interface of digital products are another example of this type of lock-in. The airlines establish lock-in by developing frequent flyer programs. As people fly more with one airline, the benefits they receive increase, in a non-linear fashion. B2B markets that increasingly rely on relationships and long-term contracts are clearly prone to lock-in. Manual Approval: Refers to the process of validating an affiliate application and then approving them after validation. This can also refer to the process of approving sales after they have been validated. Marginal Costs: Marginal costs are the costs associated with creating an additional unit of product. This is similar to variable costs, which are the costs that increase directly with the increase in production (unlike fixed costs). Digital products typically have very low marginal costs, when compared with traditional goods (materials, labor etc.) and if the product is distributed via a web site, then the marginal costs can be zero. The consumer is bearing the distribution costs, and there are no packaging costs. This is why companies are able to market their products for free on their web sites, in order to try to entice further purchases at a later time (in the hopes of creating lock-in perhaps). Netscape pioneered this approach and was able to offer its versions of its browser on its web site, changing the way software is marketed. This enabled them to create significant market share very quickly. They were able to do this, due to zero marginal costs. Marginal Consumer: Marginal Consumers are the consumers that value the product least in terms of it satisfying their needs (the value proposition for the product is weakest among those that purchase the product). They are most likely to switch to other products to satisfy their needs, and will be the first in the marketplace to do so, if the marketplace changes in favor of another product to satisfy the same needs. Market: A market traditionally referred to a place where buyers and sellers met to exchange goods. The exchange is a function of the positive sum relationship of the buyer and seller. A market is now better defined as a group of buyers and sellers for a particular product (a group of people who share a similar need). The advent of technology (industrial revolution) has seen the separation of supply and consumption, hence the broader term for a market. Types of markets include consumer (the exchange involves the final consumer, also known as B2C); business (exchange involves another organization, also known as B2B); global (exchange involves overseas parties); and government or non-profit. Each of these types of markets includes different marketing challenges, and thus different focuses within the marketing mix.
259
INTERNET USERS HANDBOOK
For markets to be effective, rules (legal framework) need to be established. Thus as emerging markets (countries) mature, and legal frameworks are better established, their respective markets will become more vibrant. Marketing Mix: A Marketing Mix is the combination of product offerings used to reach a target market for the organization. The marketing mix comprises the Product (what the actual offering comprises), Price (the value exchanged for that offering), Promotion (the means of communicating that offering to the target audience, promotional mix) and distribution (also known as Place, the means of having the product offering available to the target audience). The marketing mix is also known as the four Ps. Market Segmentation: The method of identifying a group of consumers, within a broader market, that has similar characteristics and needs. Segments can be identified by examining demographic, psychographic, and behavioral differences. Thus a car manufacturer may identify different types of consumers preferring different styles of cars, so they will segment their car buying markets accordingly. Perhaps identifying that younger car buyers, with high incomes, will be more likely to buy a sports car, while an older population of car buyers may be more apt to purchase a town car. Once these segments are identified, marketers can develop unique marketing mixes that target each segment. For example, the marketer may identify a number of specialty magazines that the young affluent market reads, thus they will run their advertisements for sports cars in these magazines. Mass Customization: Mass Customization is the ability to produce products, customized to the individual, at a large scale, at a price that is similar to mass produced products. Mass customization requires a system for customers to specify their requirements and a build-toorder approach (thus there is no inventory in this system). Dell is a good example of a company that has adopted mass customization. Mass customization is not the same as personalization, the use of data about an individual to create a unique marketing presentation to that individual. MadeForOne.com is a useful resource for information on Mass Customization and Personalization. M-Commerce: M-Commerce (Mobile Commerce) refers to access to the Internet via a mobile device, such as a cell phone or a PDA. Once m-commerce becomes ubiquitous (it has greater rates of acceptance in places like Europe and Japan than it does in the US due to standards that have developed (Japan the standard is I-mode, in Europe is WAP), it will change the utility of the web from a business standpoint. Contextual Marketing, the ability to communicate with a person when the person is likely to be receptive to the communication, will further evolve, due to the mobility of access versus a PC. GPS is used to identify where someone is located. SMS is the messaging system across mobile devises that complements m-commerce. Medium, Media: Medium is the means of communication. Commonly referred to by its plural, media. Typical commercial media are TV, radio, newspapers and magazines. A piece of paper is also a medium, as it can carry a message, communicated between the sender (the author of the note/memo/story) and the receiver (those reading the content of the paper). The Internet, and its various components are media. The web, as a medium, is quite different to other, more traditional, media. It is a distributed medium, thus the content that the medium communicates originates from many web servers around the world (75 million web-sites January 2006).
260
INTERNET USERS HANDBOOK
The web is a non-linear medium. Thus unlike other media, the consumer controls the navigation, due to the hypertext design. With other media, the marketer has more control on how the receiver receives the message. The web is a multi-media medium. This is in terms of its hyperlinking scheme, and its use of text, audio and video. If one considers various components of the web (chat rooms and discussion boards) and email (actually an aspect of the Internet, but enhanced by the web) then multi-media takes an additional meaning in terms of the types of communication it fosters. The web is a niche medium, it can satisfy the needs of those with obscure interests much like it can for those with mainstream interests. The web is an unobtrusive medium, thus users need to seek out the website, rather than having the web presence "pushed" to the consumer (obtrusive, like TV, radio, email etc.) The web is a self-serve medium. Consumers can use the web, when they want, in order to satisfy their informational needs. RSS and other Web 2.0 technologies are now providing a push environment which is controlled by the consumer. Merchant: The person selling the goods or service is referred to as the merchant. The merchant pays affiliates for sending traffic to the merchant's web site after a product or service is purchased. Meta Market: Meta Market is a web-based market centered around an event or an industry, rather than a single product. These are markets of complementary products that are closely related in the minds of consumers, but spread across different industries. The web allows us to match producers' desire for economies of scale, and consumers' desire for variety of choice to satisfy a set of needs. Thus we can have a meta market for a wedding (event) that includes honeymoon recommendations, sources for engagement rings and wedding gowns. Equally we can have a meta market for an entire industry (for example chemical industry) where the industry can trade excess inventory, source new suppliers and find new vendors. These types of markets are easier to establish in the web world, than they were before the web, and can prove very effective. Edmunds.com is an example of a meta market for the auto industry, the knot for weddings. Meta Tags: Meta tags are tags that can be included in HTML source code in the header section. The most common meta tags allow the designer to include additional keywords into a document (keyword meta tag) and specify the text that appears when a search engine includes the document in its database (subject meta tag). They are therefore useful for increasing the utility of the document as it is cataloged by a search engine (SEO). If you click on the View option of your browser, and click on source, you can view these two meta tags for this dictionary. Author generated source code that is placed in the header section of an HTML document. Current popular meta tags that can affect search engine rankings are keywords and description. The meta KEYWORDS tag is used to group a series of words that relate to a website. These tags can be used by search engines to classify pages for searches. The meta DESCRIPTION is used to describe the document. The meta description is then displayed in search engine results. Metcalfe's Law: Metcalfe's Law states the number of possible cross-connections in a network grow as the square of the number of computers in the network increases. This is the law that governs network effects. The original quote, by Robert Metcalfe: "The power of the network increases exponentially by the number of computers connected to it. Therefore, every computer added to the network both uses it as a resource while adding resources in a spiral of increasing value and choice." Micropayment: Micropayments are small transactions, perhaps of the order of a few cents. They are being considered for digital content on the web. For example, a magazine selling an article (unbundled)
261
INTERNET USERS HANDBOOK
rather than an entire issue (bundled) with additional information that may not be of interest to the consumer. This may then create alternate business models for content providers. Monopoly: Monopoly is a marketplace structured such that it is supplied by one marketer, or one marketer has an overwhelming market share. There is thus no material competition in the marketplace. A monopoly is sometimes mandated (and supported by the government) but is also oftentimes not legal and there have been cases where a firm was 'dismantled' by the FTC once it was clear it had a monopoly (AT&T in 1982). A monopolistic company has such advantages over consumers and other firms it tends to 'misbehave'. Moore's Law: Moore's Law posits that the cost of technology declines by 50% every 18 months. Gordon Moore, in 1965, observed that the number of transistors per square inch on integrated circuits had doubled every year since the integrated circuit was invented. In subsequent years, the pace has slowed down a bit, but data density has doubled approximately every 18 months, and this is the current definition of Moore's Law, which Moore himself has blessed. Multi-Level Marketing: Multi-level marketing (MLM) is a marketing system that rewards consumer resellers for the sale of the product and for the recruitment of other resellers for the product. Typically resellers are paid a commission on what they directly sell, and a smaller commission on their recruits' sales (and their recruits' recruits' sales etc.) This is the multi-level aspect of the term. Amway and Avon are the more recognized marketers that use this sales method. With the evolution of the web, we are seeing Internet firms adopting this strategy with a viral marketing style program. Both viral marketing and MLM programs rely on the connectivity of consumers. Viral marketing programs do not offer an economic incentive to attract new customers, unlike MLM programs. Affiliate programs are also an example of MLM. Multi-Level Marketing (MLM) has some similarities to viral marketing, in terms of taking advantage of the connectivity of customers with potential customers, but MLM offers a direct incentive for customers to recruit additional customers. Negative and Positive Spirals: These are events that reinforce each other, either positively or negatively, depending on the situation. For a positive spiral, a positive event occurs, this triggers another positive event, this then has a positive effect on the first event etc. (known as increasing returns to scale). Thus if someone enters to participate in a network (purchases a fax machine) then that person increases the value of each fax machine in the network, since the fax machine is now more useful. This increased value encourages more people to purchase fax machines, which in turn increases the value of each fax machine, as a user can use it to communicate with more people. This is more commonly known as the fax effect, and while its example is a little dated, the concept still applies for growing networks. A negative spiral occurs when simultaneous negative events impact each other. Thus as consumers leave the market place for a product, they can either decrease the value of the product for those remaining in the marketplace (this is common for digital (networked) products) and / or increase the price of the product for the remaining consumers, as the average cost of the product increases. Either instance with have a further impact on the remaining consumers, and more consumers may therefore leave the market for the product, compounding the effect. Once this spiral occurs, many products will inevitably not survive. The Betamax standard is a good example of this. Traditional news media are also falling prey to a negative spiral as people source their news online and classified advertisements, part of a newspaper's business model, are also moving online.
262
INTERNET USERS HANDBOOK
Netiquette: Netiquette refers to "Internet etiquette." Since the Internet does not have a set of rules established by a government, or an independent agency, it can (potentially) be a pretty chaotic environment. For such an environment to be effective, those participating need to follow the etiquette that is established. Thus netiquette refers to an established set of rules developed by the community itself, rather than an independent body. Since each participant of the Internet has an incentive to see the Internet prosper, we are more likely to want to follow netiquette to insure future growth of the Internet, similar to the prisoners dilemma scenario. While as an individual, over the short term you may benefit from violating certain aspects on netiquette (defecting: using spam for example), in the long run, if everyone adopted such a philosophy, the Internet would no longer be a useful medium, for anyone Networked Economy: [net] This refers to the fact that as consumers, we are now connected together, through the network of the Internet. This increases the likelihood of consumers sharing information, as the cost of sharing information decreases and the means for doing so increases. This has a significant impact on the field of marketing and brand management. No longer do marketers control the messages they use to market their products to consumers. Consumers are now talking to each other and are becoming a viable source of information for other consumers. The viral marketing effect occurs due to a networked economy, as information is passed through networks at great speed. The connectivity that occurs in the market is enhanced as markets adopt specific communications standards. Once a standard has been adopted, the market can become more effective. Thus standards become very important in establishing a market and the subsequent success of the market in a networked economy. Network Effects: Network effects refers to the notion that as more people participate in a network, the network becomes more valuable to each participant (a significant part of the value of the product/network, are the other participants of the network). This is also known as increasing returns to scale and a positive spiral. This effect is common in digital products, more specifically, products that benefit from the connectivity of the customer base. The fax has been used as a very good example of this. The first fax machine that was made available to the first consumer had no value to that consumer, since there was no one with whom to correspond. Once a second consumer owns a fax machine, each consumer has one person with whom he/she could communicate. When the third fax machine was sold, each owner could now communicate with two people, increasing the value of the product. The "fax effect", as this is known, is governed by Metcalfe's law. Markets that experience network effects are prone to become more effective as more people join one network (product in the market) rather than having the market segmented with many proprietary networks (competitive market). Once network effects are established, markets tend to tip, favoring the market leader at the expense of other products in the marketplace. Thus, while we may not appreciate the dominant position that Microsoft has established in the software market (and they may have behaved inappropriately as a function of this dominant position) there is no doubt that as consumers we are better off using software that each of us can transfer to each other when communicating with each other, and when moving from one organization to another (that may require employees to learn different software packages that accomplish the same tasks (different word processing packages etc.) Off-line Promotion: This refers to the marketing and promotion of your site in such traditional manners as networking, print advertising, media, event sponsorship, and merchandising. Open Source: Open Source is a term, developed in 1997, that represents free software. The term was designed to emphasize the freedom of use aspect of the software (source code is open), and not allow
263
INTERNET USERS HANDBOOK
people to assume free meant no cost (which it did not). Aside from the marketing aspect of the new term, there are also differences in the ideologies of the proponents of the open source movement as a "branch" of the free software movement. The open source movement (Eric Raymond et al.) believes that open source should be a business choice, and only appropriate when it makes business sense (Magic Cauldron paper discusses this). The free software movement (evangelized by Richard Stallman) believes that all software should be free, and only if all software is free will free software be truly effective. Since all software development relies on previous "knowledge", and that previous knowledge is public domain, then new knowledge, as a derivative, should also be free. Opportunity Costs: Opportunity costs refer to the costs associated with giving up an opportunity. They are relevant in the marketing of digital products when one considers the value lost to the company when giving away a product for free. Since digital goods primarily consist of fixed costs and often have zero marginal costs then marketing strategy often dictates to give-away a version of the product to encourage consumers to upgrade at a later time (assuming lock-in etc.) The only cost incurred here would be the opportunity cost of the lost revenue from the consumers that would have paid for this version of the product in the first place. To avoid this situation, companies typically segment their markets, and offer a free product, with limited functionality (and no customer support or documentation) to a casual user group, and an upgraded version, at a price, with customer support etc. to a more sophisticated customer. The company will hope the casual users will upgrade to the upgraded version as they become more sophisticated users and more reliant on the product. They also assume the sophisticated user will not be satisfied with the free version, due to its lack of functionality. Examples of companies employing the tactic of giving something away for free, in the hopes certain users will upgrade, include Blogger and Jot. Opt-in/Opt-out: Opt-in / Opt-out refers to the mechanism used by marketers to allow users to signal their interest in receiving information from the web site owner. They are used to develop permissionbased marketing programs. Users have to be careful when transacting with a web site, often times the site will design the transaction so the user automatically opts-in to receiving marketing information by not explicitly opting out. Sending mass emails to users who have not given explicit permission is known as spamming. Typically an opt-in process will generate a smaller, but more qualified, list of users. P3P Privacy Policy: Platform for Privacy Preferences (P3P). A protocol for sharing private information over the Internet from the World Wide Web Consortium (W3C). A Web site's privacy policy is defined by the Webmaster answering a standard set of multiple-choice questions, which result in tags embedded in the Web site's home page. Users also define their privacy requirements in their P3Penabled browsers; for example, whether they allow their names disclosed to third parties. If the Web site policy and user preferences are not the same, the browser alerts the user. P3P also assists with online sales. It lets users decide what specific data they are willing to divulge automatically to the site, such as shipping address and credit card number. If the site requests more data, the browser alerts the user, who can then decide whether to share it or not. For more information, visit www.w3.org/P3P. Paid Placement: A paid placement search engine charges websites on a per visitor basis. Patch: A patch is an addition to a piece of software program, used either to repair the software (fix a bug), or submitted for inclusion in updated versions in the case of open source software.
264
INTERNET USERS HANDBOOK
Patent: A patent is a form of protection afforded the inventor of a process. It is a form of intellectual property protection (copyright protects ideas, patents protect processes / inventions.) A patent holder can provide a license to establish use of the protected invention by others. Pay-Per-Sale: An affiliate marketing program that rewards affiliates based on each conversion to a sale such as when purchasing a product or service from the merchant's web site. Pay-per-sale programs usually offer the highest commissions but tend to have the lowest conversion rates. Pay-Per-Lead: Affiliate program that rewards affiliates for conversions to leads. A lead might include a signup form, software download, survey, contest or sweepstakes entry, signup for a trial, etc. Pay-perlead generally offers midrange commissions and midrange to high conversion ratios. Pay-Per-Click: Rewards an affiliate for each unique click to the merchant's web site. This type of affiliate program is uncommon because of click fraud or fake clicks. Peer-to-Peer: Peer-to-peer refers to the design of a service that does not rely on centralized networking services such as DNS to connect end users' computers. This design accounts for the unpredictable accessibility of these end nodes in making connections between users. Traditional networks follow a spoke-and-wheel design, where the network is organized around a central hub, the site's users come to interact with that hub from client workstations. In peerto-peer applications, many or all of the functions performed in connecting a traditional, server-based, network are off-loaded to the client machines connected to the network. Performance-Based Marketing: Marketing in which the merchant only pays commissions for results such as conversions to sales or leads. Permission Marketing: Permission Marketing refers to a communications process, between the marketer and the consumer that the consumer gave "permission" to the marketer to participate. This is becoming more common with the web, as consumers "opt-in" to a mailing list from a company's website. This allows the marketer to develop an ongoing dialog, in order to build a positive relationship and communicate messages relevant to the marketer's product. Product information, combined with additional incentives (prizes or other rewards) can be used. Personalization: Personalization is the ability of a web-site to present content that is unique to the individual (client machine) viewing the content. This unique content is based on the individual's past behavior with the site. Tools for web-site personalization include the cookie file which identifies the user; server-side scripting (this allows the presentation of data, stored in the company's databases, to be presented dependent on the cookie file) and collaborative filtering (makes predictions on preferences based on similar customers' preferences). Phishing: Phishing refers to the act of trying to gain sensitive data from a user by sending the individual an email that requests an update to an account of a legitimate web-site (eBay, Amazon for example), i.e. a trusted source. While the web-site is legitimate that the email requests the individual to update, the request is not. The actual update occurs on a site other than the site noted in the email, which is gathering the data to exploit for illegitimate purposes (identity theft for example). A user can identify such a request by looking at the URL to which the site is pointing that is making the request. If the URL 'appears' to be from the legitimate site, then it is an image, masking the site that is gathering the data. Phishing tactics are responsible for a portion of email spam. Platform: A platform is an environment needed to run a piece of software. Thus the Windows Operating System serves as a platform for the Windows Office Suite. Further a browser would be considered a
265
INTERNET USERS HANDBOOK
platform that a plug-in would need for it to function (thus Internet Explorer is a platform for Windows Media Player and Real Networks). Plug-In: Plug-in refers to additional software that is required to execute a transaction via a web browser. Thus if the webpage is designed to run with something that is not standard to the browser, the viewer needs to download an additional plug-in. This may be used to run enhanced graphics (Flash), sound (Real Audio) or 3D (Cosmo Player), or other such rich media applications. Before designing a site to require a plug-in, it is important to note how much of your target audience has the additional plug-in, the likelihood of those not having the plug-in downloading it, and whether the design functions without the plug-in (i.e. does the additional feature(s) compliment or replace the information design of the site). As the web browser develops, the requirements of use of plug-ins will diminish, so this is a temporary situation. It is advised not to require the use of plug-ins on the homepage, especially if the information from the plug-in is required to meet the informational goals of the site. Podcasting: Podcasting is a term used for broadcasting audio and video files (MP3) over the Internet that includes two features. The content has an RSS feed, which enables users to subscribe (thus the content is pushed out to the subscribers) and the content syncs with an audio device such as an iPod (hence the name). Pop-up Advertisements: Pop-up advertisements are a form of Internet advertisements that appear in a separate window, either as a full screen (but behind the current window, and also known as a Popunder ad.) or partial screen (over laying the current window). These advertisements, similar to some interstitial advertisements, do require the user to take some form of action (even if it is to simply close the window). The benefits are the user can simply continue to browse the web without being interrupted, yet still engage an action with the advertisement if desired, at a later time (unlike other forms of web advertising). Balancing this, they do create another window in the user's screen that the user did not request; this can be considered somewhat annoying. Portable: Portable refers to the ease of mobility of the medium. A portable medium is one that can be carried with the consumer, wherever the consumer is. Newspapers and magazines are more portable that the TV or the web, the radio falls between the extremes. As the web becomes wireless, its portability (and hence utility) will increase. As the web migrates to portable devices (cell phones and PDAs) m-commerce will evolve. Portal: Portal refers to the entry point webpage for a particular theme; whether it be an industry (chemical or auto industry sales perhaps) or an occasion (wedding purchases). Portals serve as the ones-shop starting point to execute all transactions within the theme. They are also referred to as an infomediary. Positive Sum Relationship: A positive sum relationship is a relationship between two entities which are, as a sum, better off from the participation of that relationship. This is in contrast to a zero sum relationship, where the outcome of the relationship is a gain for one participant at the direct expense of the other. Examples of positive sum relationships can be found in business transactions (trade in general) and in biology (bumblebee and the flower). Long term positive sum relationships are also known as symbiotic relationships. Zero sum relationships can also been seen in biology (the food chain) and in games, such as chess and checkers. Game Theory tries to predict best decision making outcomes based on the relationships of participants, and the consequence of decisions based on positive sum relationships or zero sum relationships.
266
INTERNET USERS HANDBOOK
Pre-Money Valuation: Pre-Money Valuation refers to the value of the company before an outside investment is made. Thus if a company has a pre-money valuation of $5 million, and a Venture Capitalist invests $10 million, then the Venture Capital firm will own 66% of the business after the investment ($10M / $15M = 66%) Prisoners Dilemma: Prisoners Dilemma is a popular game theory model. It is a game between two players that is designed to see how one player reacts to another player's decision. The following is a good description of the scenarios the game provides. The choices for each move are to either cooperate or to defect, and depending on the combination of both players' decisions, points for the move are assigned to each player as follows: If players A and B both defect, each gets 1 point If player A defects, and player B cooperates, A receives 5 points, B receives 0 If player B defects, and player A cooperates, B receives 5 points, A receives 0 If players A and B both cooperate, each receives 3 points. Unlike a zero-sum game (chess for instance) cooperation becomes the best solution. The problem is, for single moves, regardless of the decision of the other player, the best decision is to defect. It has been shown (Axelrod) that the best outcome of this game is for a player is to adopt a "tit for tat" strategy that begins with a cooperative move (this assumes a long term relationship is involved!) This can be applied to players involved in a symbiotic relationship such as entrepreneurs and venture capitalists! It is also very important in alliance forming for the standards setting process. Privacy: Due to the need to disclose data during transactions (unless for cash or smart card transactions), privacy can be compromised. An individual's Rights to Privacy is becoming more of an issue as businesses are increasingly able to gather data and use data for multiple purposes. With the Internet, privacy issues are exacerbated, as data is not only captured more easily during transactions, but data gathering is not exclusive to transactions (sites can track your movements etc.). The customer should better understand four things with respect to data transfer: How data is gathered? What data is gathered? When data is gathered? How data is being used subsequent to gathering? These issues (data gathering by cookies for example) and data usage (using data for own business, reselling data to gain additional revenue streams, combining data from multiple sources to create new sets of information) are increasingly unknown to customers. This uncertainty can lead customers to avoid transactions in the first place (and therefore compromise an individual's freedom). TRUSTe and similar organizations are evolving to help establish standards in data gathering and usage. Gathering data about a customer can often lead to a better service provided by the company. Thus there is a tension between the need to gather data (privacy concerns) and the need to provide a better service to customers (better personalization for example). Aside from the need to offer data as part of a transaction, another issue with respect to privacy is the ability for "outsiders" to view data that was not intended for them (either data that is stored or in transit). Cryptography is the field that is designed to protect information from those with whom it is not intended. Identity theft is also a growing issue with the activities of phishing.
267
INTERNET USERS HANDBOOK
Google is starting to create concerns for privacy advocates. Its Gmail product runs advertisements based on the content of emails received. This created concerns about the privacy of email content. You can type in a telephone number to the search engine and get the name and address of its owner (as well as a map of the destination). Google also has a lot of search pattern data at its disposal. Users trust Google will keep this private. Product Line: Product line is a collection of products, offered by a firm, that satisfy similar needs for different target audiences. Thus all products within a product line are related, but may vary in terms of size, color, quality etc. The product line is part of the broader product mix, which is the full suite of products offered by the company. Purchasing Process: The purchasing process refers to the entire process a consumer will go through before making a purchase. A simple model follows: Consumer Awareness (understands there is such a market/product) Interest (consumer learns more about the value of the product) Desire (consumer understands the need for the product) Action (consumer makes a decision to purchase a product) Depending on the stage of the purchasing process, the marketer will adopt different tactics to move the consumer to the next stage. The web is the only medium that is clearly useful at all stages of the process, simultaneously. The Consumer Purchasing Process contrasts to the Business to Business Process that requires the following stages: Problem Recognition; General Need Description; Product Specification; Supplier Search; Proposal Solicitation; Supplier Selection; Order Routine Specification; Performance Review, and also requires many people involved in the decision making process. Pure Play Business: Pure Play Business refers to a business that was established for the web, but had no prior physical presence. Amazon.com and eBay are examples of pure play businesses. This is in contrast to a Legacy Business; these businesses are the traditional businesses that also use the web (Walmart). Qualified Traffic: Visitors who are specifically seeking websites with content such as yours. Reach of Communication: Reach refers to the number of people a communications can reach. TV typically has high reach, although cable programs are more focused and therefore the reach is more limited as the programs are more targeted. A salesperson typically has a reach of one at a time. Reach of communication is usually a trade-off with richness of communication. The web is the first medium that breaks this relationship, and allows for reach and richness simultaneously. Recurring Commissions: The process of rewarding an affiliate on a recurring basis whenever the merchant charges a customer a recurring fee. For example, a web host that charges customers on a monthly basis might reward the affiliate a percentage of each month's payment from the customer. Referral Program: Referring a customer to your website in a manner outside the realm of the Internet. Referrer URL: Referrer URL refers to the URL of the web page that preceded the page in question. It is useful to know the referrer URL as this allows you to understand how users are finding the web page and which external pages are linking to you. You can also see which keywords are being used to discover your site from search engines. It is a part of web analytics. Relationship Marketing: Relationship marketing, refers to the notion of marketing to a customer with the expectation of a long-term relationship. This removes the need to focus on each individual transaction needing to be profitable, but rather the relationship, over its lifetime, be profitable.
268
INTERNET USERS HANDBOOK
Marketers are now able to segment their target markets to the individual consumer (one-to-one marketing) and understand the value each consumer can bring to the relationship (life time value of the customer). Relationship marketing also focuses on customer share, versus market share. The share of the customer dollar, rather than the number of customers within the market. Relationships between the buyer and the seller are also likely to incur lower transaction costs. Residual Earnings: Programs that pay affiliates not just for the first sale a shopper form their sites makes, but all additional sales made at the merchant's site over the life of the customer. Return on Investment: In relation to search engine advertising, it often refers to sales per lead. ROI: stands for 'Return on Investment'. This is what all marketing managers want to see from the money they spend on their marketing and advertising campaigns. The higher the sales, the large the number of shoppers and the greater the profit margin generated by sales the better the ROI. Reverse Pricing Model: [rev] Reverse Pricing Model refers to a model that allows the consumer to establish his/her requirements and offer those requirements for bid by the seller. Thus rather than the seller marketing a product to the buyer, the reverse occurs. Priceline has pioneered this model in the consumer marketplace, using airline tickets as the product. This model further reflects the changing power in the market from the supplier to the consumer. When this model can be effectively combined with the group buying model one can envision powerful groups of buyers creating interesting demands on companies. RFID: Radio Frequency Identification (RFID) is a system that allows for the tracking of a product, with an appropriate tag, throughout its lifecycle. It is useful in the supply chain of a company; it is also useful once the product has been sold to understand its subsequent uses. The latter creates privacy concerns. Rich Media: Rich media refers to media on the web that offers an enhanced, interactive experience. VRML for 3 D, Macromedia Flash and Shockwave would be good examples of languages for rich media. The Rich Media SIG is a good resource for emerging technologies. Rich media is often used for banner advertisements, for homepage's and for email communications. It is important, however, for designers considering the use of rich media, to understand the audience they are designing for, and make sure the audience has access to the information being conveyed via the rich media (browsers do not have many rich media technologies built into their viewing capabilities, therefore plug-ins are required). Many successful e-commerce web-sites, like Amazon.com, avoid rich media, and use a lowest common denominator design strategy. Richness of Communication: The richness of communication refers to the depth and interactivity of the communication. The ability to use multimedia to present compelling information to the consumer. While a TV commercial may be able to take advantage of audio, visual and text, it can only present a generic presentation to a broad audience, this is therefore not tailored to the individual consumer. Moreover, the TV is not interactive, further limiting the richness of the communication as the consumer cannot transact with the marketer. A sales person can develop a very rich presentation, based on the specific needs of the individual customer. The sales person can also execute a transaction during the presentation. This is a very rich medium. The web is also a very rich medium, as it is able to take advantage of multimedia, present information based on the individual and execute transactions. Richness of communication is usually a trade-off with reach of communication. The web is the first medium that breaks this relationship, and allows for reach and richness simultaneously.
269
INTERNET USERS HANDBOOK
ROAS: stands for 'Return on Advertising Spending'. This is the amount of revenue generated for every dollar spent on advertising. For instance, a ROAS of $1 means you're generating $1 in sales for every $1 in advertising spend, and a ROAS of $5 means you generate $5 in sales for every $1 in spending. Robot: A program that automatically does "some action" without user intervention. In the context of search engines, it usually refers to a program that mimics a browser to download web pages automatically. A spider is a type of robot. See also: Spiders. RSS: RSS (Rich Site Summary or Really Simple Syndication) is a means of distributing dynamic content (content syndication), using the XML format, to subscribers of that content. In order for a user to subscribe, he / she will need to sign up for a news reader aggregator (Bloglines etc.) RSS has become a popular technology for bloggers and podcasters to distribute their content, essentially 'pushing' content out to subscribers of the content rather than relying on readers to visit the site to determine if there is new content. RSS is also useful for news organizations which publish content as a matter of their business model (and update regularly). Examples include CNN and India Times. It would be useful for companies that publish news releases of newsletters for subscribers in email form. While RSS does require a reader to subscribe to a news aggregator before accessing content (this may soon be bundled with the web browser which will surely impact its rate of adoption) it avoids the problem plaguing email distribution of content: SPAM. Scalable: Scalable refers to the ease and flexibility of increasing the output of a given product, or the reach of a medium (marginal cost of increasing output or reach). The cost of increasing output (the reach of a medium) by one unit. If this is insignificant (or zero!) then the product/medium is highly scalable. The web and digital products are highly scalable. Search Engine: Search engines are web sites that are designed to allow you to search across the web. Search engines are a type of infomediary. Google is now clearly the most popular search engine. It trumped Altavista due to better results based on its PageRank algorithm. Yahoo! is a distant second. Amazon's A9 search engine is emerging as an interesting alternative. Among its features, it takes into account a user's previous search behavior in an attempt to personalize the search. Search engines rely on web designers to submit their pages to the engine, and on a spider that crawls the web to identify new sites. Search Engine Optimization is becoming a critical Internet marketing activity. Search is one of the most popular activities on the web for web surfers. It is second only to email, 90% of Internet users performing searches. US usage has grown 55% from 2004 to 2005. Search engines are an increasingly popular source of advertising space. Since people are using search engines to seek out information and go elsewhere on the web, this fits with hypertext advertisements. Emerging search engine advertising programs include Google Adwords and Yahoo! / Overture (which were goto.com the pioneer of ppc search engine advertising). These are PPC advertising programs that host text advertisements. Traditional search engines provide results based on the relevancy of the site to the keywords searched. Blog entries will also appear among the results in the traditional search engines; however there are blog search engines that only search the blogosphere. These search engines base their output on time. The most recent entry written, that includes the keyword, is thus the first entry returned. Major blog engines include Technorati, Google Blog Search and Feedster.
270
INTERNET USERS HANDBOOK
Search Engine Marketing (SEM): SEM comprises SEO and search engine advertising. Search engine advertising, in its current model, typically uses text-based advertisements that the marketer bids on based on the keywords the marketer wants to associate with the advertisement (contextual advertising). The business model is typically PPC. Goto.com pioneered the PPC model for search engine advertising. Goto.com was purchased by Overture which was ultimately purchased by Yahoo! Google's Google Adwords is the main competitor. Both these networks supply advertisements for other sites. Search Engine Optimization (SEO): SEO refers to the art of designing a web-site for better listings in search engines. This includes ensuring you have the appropriate keywords in the body text of the site, in the title tag and the meta tags. Google's PageRank algorithm also rewards sites that have inbound links, and even considers the anchor text of the inbound links. Search engines also reward sites with fresh content. Regularly updated blogs therefore serve as a good SEO tool. SEO has spawned a number of spamming efforts, which includes link spam (generating inbound links) a subset of Spamdexing. Search Engine Submission - A service that will automatically submit your pages or website to many search engines at once. Semantic Web: The semantic web is a reference to the efforts to apply machine-readable meaning to the web. The web's meaning is for the most part designed to be understood by humans, HTML is primarily used for visual presentation. Adding meaning for machines will make searching the web for appropriate content more accessible. An early example of adding meaning, using HTML, are the use of meta tags. Tags (Technorati Tags) are now being used in the blogosphere to help better categorize blog postings. Server: The server refers to the host of the information on the web. A software that runs on the server side is used to manage the information on the server. This is in contrast to the client-side, which refers to the user interface of the information (web). Server-side Scripting: Server-side scripting allows web designers to present dynamic content that is useful for personalization. PHP, .ASP and Javascript are popular scripting languages. They allow for content to be drawn from databases that are also dependent on the client cookie file. Amazon is a common example of this type of process. Shopping Cart Abandonment: Shopping Cart Abandonment refers to the loss of a customer who is going through the check-out process of an online transaction. Some statistics suggest that this can be as high as 75%. It is principally caused by poor usability of the site and the check-out process (too time consuming, too many clicks), and hidden shipping charges. Shopping Cart Technology: Shopping Cart Technology provides turnkey solutions for e-tail sites. These solutions include web site connectivity with a product database, capability for users to "store" purchase intent before the final transaction (this requires interaction with your cookie file) and payment processing. Signature File: The signature file (also known as the .sig file) is a file that can be incorporated into your email such that each time you send an email, the file is attached at the bottom. This can be considered as a replacement for the letterhead of your company. It should include your contact information, and should be no longer than four lines (according to netiquette). It is considered poor netiquette to create a signature file that is greater than the length of the email message!! Silicon Valley: Silicon Valley refers to the region of Northern California which serves as a hotbed for entrepreneurship. Hewlett Packard essentially served as the catalyst for this region, in the 1930s. It is the home for many notable high-tech firms, a major part of the venture capital community and Stanford
271
INTERNET USERS HANDBOOK
University. Due to the symbiotic relationships between entrepreneurship, venture capital and Stanford University, a robust ecosystem has evolved. Smart Card: Smart Card refers to a card that includes an imbedded chip that can store data. Since smart cards can store data, they can be used in transactions that allow the consumer to remain anonymous (data storage with the consumer, not the company) which is a key benefit for those concerned with their privacy. Smart Cards have not reached full adoption at this point, (higher rate of adoption in Europe versus U.S.) The Smart Card Alliance is an alliance of industry leaders working for the widespread acceptance of Smart Card technology. SMS: SMS refers to the standard adopted for text messaging via a cell phone. This allows people on separate networks to send text messages across networks. SMS supplements standards being developed for m-commerce. Source Code: The source code refers to the programming code that is written to develop the program, oftentimes it is compiled before it is run, therefore not viewable to the end user. Go to Once the program is compiled, it is readable by a machine, but very difficult for a programmer to understand. All free software (open source) programs are distributed with the source code as well as the compiled object code. One nice thing about writing web documents is you can see the source code for the page you are viewing. This allows you to more easily learn html. If you are using Internet explorer to view this page, simply click on the edit option at the top of the page, then select source. A similar process works with Firefox. Spam: Spam is the term used for unsolicited email sent by marketers and individuals who typically have purchased an email mailing list. The first major Internet spam actually occurred when two attorneys, Canter and Siegel, spammed UseNet news groups with their green card lawyer offer. View EFF's Canter & Siegel Green Card Lottery Net. The problem with spam is it can make the communications vehicle, whether the email inbox, the UseNet newsgroup, or the web discussion board, useless, as it becomes difficult to identify good information from spam. Spam should not be confused with marketing messages you receive via a permission-based marketing program, where you have elected to receive information from a company. However, some companies are reasonably tricky in terms of how they use the opt-in option to get customers to give permission (often as one of the final steps of a transaction), so while permission is granted, the customer's intent to grant permission is not always there. Spam can also refer to the notion of spamming a search engine. Spamdexing refers to all the means of spamming search engines, link spam refers to creating additional inbound links to a site to try to increase a search engine ranking Spamdexing: (also known as search spam or search engine spam) involves a number of methods, such as repeating unrelated phrases, to manipulate the relevancy or prominence of resources indexed by a search engine, in a manner inconsistent with the purpose of the indexing system. Some consider it to be a part of search engine optimization, though there are many search engine optimization methods that improve the quality and appearance of the content of web sites and serve content useful to many users. Search engines use a variety of algorithms to determine relevancy ranking. Some of these include determining whether the search term appears in the META keywords tag, others whether the search
272
INTERNET USERS HANDBOOK
term appears in the body text or URL of a web page. Many search engines check for instances of Spamdexing and will remove suspect pages from their indexes. Also, people working for a search-engine organization can quickly block the results-listing from entire websites that use Spamdexing, perhaps alerted by user complaints of false matches. The rise of Spamdexing in the mid-1990s made the leading search engines of the time less useful. The success of Google at both producing better search results and combating keyword spamming, through its reputation-based PageRank link analysis system, helped it become the dominant search site late in the 1990s. Although it has not been rendered useless by Spamdexing, Google has not been immune to more sophisticated methods. Google bombing is another form of search engine result manipulation, which involves placing hyperlinks that directly affect the rank of other sites. The problem arises when site operators load their Web pages with hundreds of extraneous terms so search engines will list them among legitimate addresses. The process is called "Spamdexing," a combination of spamming the Internet term for sending users unsolicited information and "indexing." Spider: A spider (also known as a crawler) is used by a search engine to identify web pages in order to be cataloged in the database of the search engine (web site designers can also submit web pages to be cataloged in a search engine). Spiders therefore help search engines to keep up with the evolution of web content by crawling through the web seeking new sites. To control spiders in terms of cataloging a web site, a designer can include a robots.txt file that instructs a spider to exclude pages that are not to be cataloged. Spiders: The main program used by search engines to retrieve web pages to include in their database. See also: Robot. Spider Detection: The process of detecting and ignoring automated spiders or bots such as search engines like Google/Googlebot. Spyware: Spyware is software downloaded on a computer that 'spies' on the user and reports user behavior to a third party and or takes control of the computer. Spyware does this without disclosure. Adware can sometimes be confused with spyware, but adware operates with full disclosure and may report data to a third party. Spyware is an obvious concern for privacy advocates, and is a type of malware. Stock Options: Stock Options are options, usually given to employees, to purchase stock in the company at a future date. The price of the option is established, thus if the company's stock price rises above the option price, the owner of the option is able to take advantage of the stock increase (current stock price - established stock price). Options therefore work well for high growth companies and are used to increase loyalty of early stage employees. They are also used to replace some part of the salary which helps reduce the company's cash flow (burn rate). Stock options may vest over multiple periods of time. Thus a certain amount of the options become available at certain stages. Standards: Standards are very important in order to establish a robust networked marketplace (A marketplace that relies on connectivity across consumers and multiple vendors etc.) If a market is fragmented with incompatible proprietary standards, it is not effective in serving all customers and businesses alike. Once a standard is established, the market may increase in size significantly. Standards can be proprietary, owned by one company (or a group of companies), i.e. Wintel. Standards can also be open, designed to increase the utility of the marketplace, where companies then compete
273
INTERNET USERS HANDBOOK
within a larger marketplace. Examples of standards setting bodies in the open format include W3C (evolution of HTML) and Web3D (evolution of a 3D standard). In order to develop open standards, alliances across competing firms need to form. Alliance formation is a political process that involves aspects of game theory. Sunk Costs: Sunk costs refer to costs that are non-recoverable fixed costs. Digital products usually have significant sunk costs (when compared to other fixed costs) in the form of research & development and intellectual property (copyright, patents etc.) for the product. If the product is not successful in the marketplace, the costs associated with the product development (intellectual property, labor) cannot be recovered. Thus when making pricing decisions about the product in the future; one should not factor in the sunk costs. If a product's cost structure is made up of sunk costs (no other fixed costs) and zero marginal costs then any price above zero will contribute to the company's bottom line. Other fixed costs that are not sunk (rent, depreciation on equipment etc.) should be factored in when making pricing decisions in the future, since these are ongoing costs to the company. The company will continue to have to pay these costs in the future, this is not the case for sunk costs. Streaming Media: Streaming media is media that can be played as it is being downloaded. This is useful for audio and video on the web as it reduces the inevitable delay involved in downloading large files. Streaming media is used for live broadcasts via the web. Super Affiliates: The highest performing affiliates. Typically less than 1% of affiliates are super affiliates yet that 1% typically will bring more than 90% of your sales. Symbiotic Relationship: A symbiotic relationship is a relationship between two entities which is mutually beneficial for the participants of the relationship. Thus there is a positivesum gain from cooperation. This is a term commonly used in biology to explain the relationship between two entities that need each other to survive and prosper. The bumblebee and the flower would be an example. The bumble bee extracts the flower's pollen for protein and its nectar for energy. The bumblebee, while collecting these sources, inadvertently brushes pollen from one flower to another to ensure the flower's reproduction process begins. The bumblebee needs the flower to survive, the flower needs the bumblebee to survive. These are positive sum relationships. Other relationships in biology, especially with respect to the food chain, are not so forgiving, a zero sum relationship. One 'actor' clearly benefits from the other (typically consumes the other). In this type of relationship, it is still essential that both players (as species not individuals) survive, or the dominant player will lose its food supply, and therefore die. If the foxes kill all the chickens, the foxes die as they lose their source of survival. If the predator kills all its prey, the predator will die. One can see a symbiotic relationship between Venture Capitalists and Entrepreneurs. Venture Capitalists need early stage investment opportunities. These are provided by entrepreneurs. Entrepreneurs need investment capital to develop their ideas; these are provided by the Venture Capital community. Thus both industries benefit from each others participation, a positive sum game. It is important that each keeps this in perspective, as if one industry tried to exert additional pressure (prisoners dilemma!) then in the short term they may be better off, but the long term survival of the relationship would be put at risk if it meant that the other player may not survive. Supply Chain: Supply Chain refers to the distribution channel of a product, from its sourcing, to its finished good status. The value chain comprises the supply chain and the distribution channel(s)
274
INTERNET USERS HANDBOOK
(finished good to consumer). The supply chain is typically comprised of multiple companies who are increasingly coordinating activities y via extranets. Switching Costs: Switching Costs refer to the notion of the hidden costs a consumer is faced when switching from one product to another in the marketplace. Consumers should really try to factor in the switching costs when making purchasing decisions, since these impact purchasing decisions they may be faced with in the future (limiting freedom of choice). Switching costs are developed by companies in order to try to establish lock-in. Target Marketing: Communicating with a specific group of consumers with similar characteristics, within a broader group of consumers who purchases a type of product. Market Segmentation is the process of target marketing. Once target market(s) are identified, the organization develops a product offering (marketing mix) that is positioned to be attractive to that segment. Offering the right offer to the right customer at the right time. TCP/IP: TCP/IP stands for transmission control protocol and Internet protocol. It is the basic language of network communication that allows all computers, anywhere in the world, to understand each other. It is the open standard that allowed the Internet to evolve. Text Advertisements: Text advertisements are text links that are paid for by the sponsors of the target page of the advertisement. They are a form of advertisement that can be considered more contextual (assuming the text link is relevant to the subject of the web page), and less obtrusive than other forms of advertising on the web. Text advertisements can also be used for affiliate advertising and the emerging search engine advertising programs from Google Adwords and Overture. Text Messaging: Text messaging refers to sending short text messages from a mobile phone to other mobile phone users using the SMS standard. This is becoming an increasingly popular form of communication outside of the United States. This is due to the economics of text messaging versus being online. Key advantages of text messaging (versus being online) include a user's ability to text people independent of computer access, rather than only being able to communicate when logged onto the Internet, it's less intrusive than a phone call, and it is less expensive than a phone call. Text messaging is a form of asynchronous communication. Tipping Point: The tipping point is the point at which the growth of the company's installedbase accelerates significantly. It occurs with products that are able to take advantage of viral marketing. A tipping point can also refer to the nature of the market, and how its balance turns to favor one company over another. Thus once one company experiences a positive spiral from network effects, its competitor(s) will experience a negative spiral, and the market will have tipped to favor the market leader. This may lead to a winner takes all scenario, where the balance of the market clearly favors one company over all others. Title Tag: The title tag (of HTML) refers to the element in the header that allows the developer to create a title for the document. This title is used for pages that link to the web page, including search engines and users' bookmarks / favorites list. The title needs to be very descriptive in order to encourage users to click-through to the webpage. The title should not be confused with heading tags within the page that are viewed by the user on the page. The title does not actually appear on the page. The title tag can be considered similar to the subject header of an email in terms of its utility and function. The title tag is important 'real estate' for keywords for search engine optimization.
275
INTERNET USERS HANDBOOK
Tracking Method: the way that a program tracks referred sales, leads or clicks. The most common are by using a unique web address (URL) for each affiliate, or by embedding an affiliate ID number into the link that is processed by the merchant's software. Some programs also use cookies for tracking. Text Link: link that is not accompanied by a graphical image. Tracking Code: Refers to the hidden 1X1 pixel tracking code that is placed on the confirmation page of your store for tracking sales conversions. Trademark: Trademark is a term, sign or symbol that distinguishes one company, and one product, from another. This is a form of intellectual property that needs to be protected in order not to confuse consumers when making choices. Protecting the trademark also helps develop the company's brand. Trademark holders have realized the importance of protecting their rights to their respective domain names. Cybersquatting is the deliberate attempt to acquire specific domain names with the hope of reselling them at a higher price, oftentimes to the trademark holder. Trademark law is typically implemented at the national level, which creates problems for the global Internet. However harmonization via bodies like the WTO helps with cross national dispute resolution. Traffic: A reference to the number of visitors a web site receives. Trojan Horse: A Trojan horse, similar to a virus, infects a user's machine by "appearing" to be a useful program (electronic greeting card, screen saver etc.) that users willingly forward to other users, unaware of the hidden maliciousness of the file. Two-tier: Affiliate marketing model that allows affiliates to sign up additional affiliates below themselves, so that when the second tier affiliates earn a commission, the affiliate above them also receives a commission. Two-tier affiliate marketing is also known as MLM (Multilevel Marketing). Unique Click: The process of only counting unique clicks from each web visitor. Unique clicks are typically tracked by recording the IP address and browser header. Unique Page Views: Unique Page Views refers to the number of unique users that access a page. This is determined by a combination of the IP address of the user accessing the page and the cookie file. Thus the unique page views metric is designed to calculate the number of individuals exposed to a page over a period of time, rather than the number of times the page is served, which is the number of impressions. Unique page views are a part of web analytics. Unique Visitor: A single individual website visitor. Visitors (or users) can visit multiple pages within a site. Unique users are important because it is an indication of success of a website. If you have high visitor counts, but relatively low page per user counts, that indicates that people are not finding your site attractive enough to sit and read through it. On the other hand, if you have low visitor counts and very high page per user counts, that is an indication your site is providing good information to people and you should do a better job of promotion. High page per user counts indicate good site potential, while low page per user counts indicate you need to rework the site with more content or better displays. URL: URL (Universal Resource Locator) is the web address of a web page. Thus the URL for this document is http://www.udel.edu/alex/dictionary.html. his is comprised of the domain name www.udel.edu, the directory Alex and the filename dictionary.html Many times you will see a URL that ends with either the domain name or the subdirectory, this is achieved by using an index.html filename. User Interface: User Interface refers to the intersection of the technical aspect of a system and its users. Users could be internal to the business / system (customer service support) or external to the business / system (customers). The design of the user interface typically has a significant impact on the
276
INTERNET USERS HANDBOOK
performance of the system. Users of a system also learn how to use the system over time, so good usability can help to create lock-in to the business for the customer. A business' homepage is an example of a user interface, as is any other webpage hosted by the business. Value Proposition: Value Proposition refers to the marketer's offering to the marketplace. It states the target market for the offering and the differentiating value the offering provides to its customers. Variable Costs: Variable costs refer to the costs that are associated directly with the number of units of product that are produced. For example, the materials used in making a product are considered variable costs of a product. Each product requires X amount of material, the costs associated with that material is considered variable (X * number of units produced) since the total cost to the firm changes depending on the number of units produced. The more products produced, the greater the costs incurred. Vehicle: Vehicle refers to a host that is used to carry an advertising message. Thus with the TV, a TV program (Seinfeld for example) would represent a particular vehicle, that attracts a specific target audience and is priced at a certain level. In the case of the web, websites that host advertisements can be considered vehicles (Google, Yahoo! Wired etc.) Other business-related sites on the web are those focused on marketing and business transactions, rather than on developing compelling content that attracts an audience in order to sell advertising space. Venture Capital: The Venture Capital (VC) Industry is a major source of funding for the entrepreneurial community. The industry itself has evolved over a number of years, but has only recently emerged as a popular career for many new MBAs. The industry focus is on early stage, pre-IPO funding opportunities. Typically a fund will be raised, that will be invested in a number of different opportunities that are reasonably high risk. In return for the investment, the VC receives an equity stake in the business. The VC also helps the business develop its management team, and takes seats on the board of the company. VCs are typically interested in making few large investments, due to the manpower needed to support each investment (recruiting and board seats). They focus not only on the business opportunity that is presented to them, but closely on the management team that is offered (human capital is clearly becoming the differentiating advantage of any business at this point!) In order for an entrepreneur to have an audience with a VC, s/he needs to have a pre-existing connection (a reference to the VC). Without this, the VC is less likely to review the business plan. Vesting: Vesting refers to the ability to monetize the investment in stock options. Thus if your options are available in three years, they vest in three years. Viral Marketing: Is a marketing technique that takes advantage of a marketer's customers in promoting the product. This technique was pioneered by Hotmail. Hotmail launched its free web-based email service with the tag line (at the bottom of each email) "Get your free email at Hotmail." As customers used this email service, and were emailing others, they were effectively sending an advertisement for the product. This attracted new customers, who repeated the process. Once a critical mass of consumers were using Hotmail, a tipping point was reached, where the number of new users started to increase non-linearly. Hotmail soon became the fastest growing media company in history. Illustrations of its success include it being the leading provider of email service in India, without having a physical presence in India. The term viral marketing comes from biology and the notion of how a virus spreads. A virus spreads very slowly within its host, until it reaches a critical mass (tipping point,) at that point it spreads through
277
INTERNET USERS HANDBOOK
the host quickly. The rapid adoption of a product or passing on of an offer to friends and family through word-of-mouth (or word-of-email) networks. Any advertising that propagates itself the way viruses do. Viral marketing is the extremely powerful and unique ability of the Internet to build self-propagating visitor streams, bringing about exponential growth to a company's Web site. This can consist of such things as affiliate programs, co-branding, link exchanges, email campaigns, and off-line promotion. Virtual Domain: A Virtual Domain is a domain name which is associated with an IP address, but is not the primary domain name for that IP address. This is used by web hosting companies to provide web hosting services for web sites whose addresses are not part of the hosting company's domain. Therefore when selecting a web host provider, you are not limited to using their domain name as part of your URL. Use of virtual domains means that an individual server does not have to exist for each individual domain name. Virus: A virus, a term "borrowed" from biology, is a malicious program that inserts itself into other program files to cause damage to the files. A user can inadvertently transfer infected files to other users using email (infected files can also be transferred by other means). Voice Over IP: Voice over IP (VoIP) enables the use of the Internet for carrying voice communications (most commonly telephone calls). This allows users to talk to each other without the use of the telephone network (of course indirectly using the network if dialing in via a modem, which does not offer the best VoIP experience). Sound is converted into digital format and sent, in packets, as data. VoIP is becoming more popular with the increasing use of broadband connections. Skype is a leading provider. Web: The web, also known as WWW, is the graphical multimedia aspect of the Internet. It comprises content, with the basic language of HTML (developed by Tim Berners-Lee circa 1990) and a browser (developed by Marc Andreesen et al. circa 1993) Internet Explorer; Firefox or Safari. The content resides on a web server. The design of the web follows a peerto-peer structure. Web 2.0: Web 2.0 comprises technologies such as blogs, wikis, podcasting and RSS. It is a term that tries to embrace a participatory web; a web where all can now participate in content creation and consumption. It thus presumes that Web 1.0 was a 'static' environment. Web Analytics: Web Analytics is the field of data mining the data that is generated from those navigating a web-site. Web Analytics allows a site designer to understand the flow of those going through a site, essentially measuring the behavior of the site's users. Which pages are most popular, which are the entry and exit points, and which the referrer URLs are. Metrics used include page views, hits, sessions and impressions. There are a number of software providers who provide web analytics tools, and a host should also provide this service to its clients. Weblog (blog): A blog is a website that is updated frequently by its author, in a standard format, with the most recent entry at the top, and older entries archived. Each entry is a unique URL, a permalink. Entries also include trackbacks and the option for allowing comments. Blogging software (such as Blogger.com and typepad.com) allow anyone the opportunity to be a publisher on the web (no need to know html), thus truly democratizing the process of publishing information (a potential threat to traditional media organizations). Blogs are used to annotate and collect news sources across the web; used as personal journals and for sharing experiences; and used by businesses to reach out to their customers and engage in conversations. The three main blog search engines Google Blog Search, Technorati and Feedster are good sites to discover blogs. They are also good sites to use to subscribe to search results that include keyword
278
INTERNET USERS HANDBOOK
phrases you want to watch (your company, your product, your competitors). You can subscribe to these results in your news aggregator. Blogs are also a good SEO tool. Search engines like sites that update often, and blog authors can certainly be deliberate about including the appropriate keywords in the title and body texts of entries. Web Ring: Web ring refers to a "ring" of web sites which forms a common navigation to allow browsers to view each site within the ring. The rings are comprised of sites with a common interest, so it allows those sites to potentially broaden their audience by linking with each other. This is a form of free advertising, much like bartering and banner exchange programs. You can view WebRing to search current networks. WiFi: WiFi networks use radio technologies (IEEE 802.11b or 802.11a) to provide fast wireless connectivity. A WiFi network requires an access point (base station) and each computer attached to the network needs a wireless network card. A computer that has a wireless card can participate in all "open" networks, but not proprietary networks (it's up to the hub administrator if the network is open or proprietary) without knowing the wireless network settings. Even with a proprietary network, security is an issue. WiFi security is easily compromised, so you should consider anything transmitted via WiFi as public knowledge. The encryption is auto-crack able, and the clients can be monitored or subject to man-in-the-middle attacks. Its almost impossible to make a wireless network private; their range will be more than you expect and can be picked up for long distances. This can be a good thing (public commons) or a bad thing (compromised corporate networks). One unauthorized access point on a poorly set up network can compromise the entire network. Wiki: A wiki is a web-based resource that allows multiple users to edit and contribute to the same web documents. Among a wiki's features, it requires only limited or no knowledge of HTML and keeps a revision history so it is easy to roll back changes if necessary. Wikis are considered a web 2.0 technology. The most 'famous' wiki is a web-based encyclopedia that anyone can edit and update. Wikis are useful for instances where collaboration is useful. Winner Takes All: The winner takes all phenomena, for digital marketplaces, highlights the notion that markets tend to favor the market leader to such an extent, other competitors can be driven out of the marketplace. This is a result of two issues. The network effects and positive spiral experienced by the market leader, making its product more compelling for the consumer, and the learning curve effect and reduced average costs of the market leader, enabling it to potentially reduce prices to a price point with which competitors cannot compete. Markets will tend to tip, and this is when the winner takes all phenomena come into play. Word of Mouth Marketing: Word of Mouth Marketing (WOMM) refers to the marketing that can be gained by actively engaging customers to share insights with each other (create buzz that goes viral). WOMM has clearly been around since the inception of marketing, but has gained more prominence with the evolution of the Internet, and the ease with which customers can share their stories. Web 2.0 technologies such as Blogs and News Readers are enabling WOMM. Discussion Boards have helped customers form communities. Good WOMM relies on great products that customers willingly evangelize. Marketers have been prone to try to 'effect' this by incentivizing 'fake' customers to talk about their products. This can backfire. One can now consider marketing initiatives as three concentric circles: the inner circle representing traditional / push marketing; the middle circle representing a
279
INTERNET USERS HANDBOOK
company's direct efforts to engage with customers with the web (hosting a blog, a discussion board etc.), WOMM; the outer circle representing the broader web, where the company's product is being discussed outside of its own web domain. Worm: A worm, as contrasted from a virus, is a self-replicating program that duplicates itself by means of the network, rather than a user taking action (inadvertent) to forward the file. XML: XML (eXtensible Markup Language) is used to enable the sharing of data across different sites on the web. A popular use of XML is RSS, used to subscribe to news feeds and blogs. XML is a means of describing data, in a customizable fashion, in order to apply a structure to the data that is necessary for the export of that data.
280
INTERNET USERS HANDBOOK
GLOSSARY OF COMMON FOREX/INVESTMENT TERMS
This Glossary is primarily from ForexGlossary; however, changes or amplifications were made where the original entry was particularly weak, Where some terms are still weak; try sharpening your Google search skill, A handy tool for you: One Click Answers Adjustable Peg: Exchange rate regimen where a currency's exchange rate is pegged (fixed) in relation to a stronger currency, such as the US dollar or the euro. The pegged rate is adjusted occasionally in an attempt to improve the country's competitive position. For example, China's Yuan is sometimes pegged to the US dollar. Aggregate Risk: A bank's exposure to Forex contracts from a single customer. Agio: A fee charged to exchange money from one currency to another. API Trading: Trading that is conducted through an Application Programming Interface. APIs, such as the one available for FXTrade, enable users to build custom trading functionality into their own software systems. APIs: Application Programming Interface, used in Forex to automate trading. See also: API Trading Arbitrage: Profiting from differences in the price of a single currency pair that is traded on more than one market. Asian Option: An option that pays off according to the average prices of the underlying asset over time. Ask: The price at which sellers are willing to sell a currency pair, also known as the 'offer', 'ask price', and 'ask rate'. See also: Ask Price Asset: An item that has value. Asset Class: An item that has value; an investment such as stocks, options, or Forex. AUD/USD: The abbreviation for the Australian dollar and U.S. dollar (AUD/USD) currency pair or cross. The currency pair tells the reader how many U.S. dollars (the quote currency) are needed to purchase one Australian dollar (the base currency) Trading the AUD/USD currency pair is also known as trading the "Aussie". Aussie: Dealer slang for the AUD/USD currency pair. See also: AUD/USD Authorized Dealer: Depending on the regulatory body, a dealer authorized to deal in Forex. Glossary of Common Forex/Investment Terms Automated Trader: A trader who uses an automated system to input trades without any human input. Back Office: The office location, or department, where the processing of financial transactions takes place. Balance of Trade: In economics, a country's exports minus its imports. Band: In countries where the currency is pegged, the range in which the rates are permitted to fluctuate. Bank Rate: The rate at which a central bank is prepared to lend money to its domestic banking system. Banking Day: Days of the week when commercial banks are open for business in the country of the particular currency traded. Bar Charts: A popular format for studying the price action of currency pairs. Base Currency: In terms of foreign exchange trading, currencies are quoted in terms of a currency pair. The first currency in the pair is the base currency. The base currency is the currency against which exchange rates are generally quoted in a given country. Examples: USD/JPY, the US Dollar is the base currency; EUR/USD, the EURO is the base currency. Basis Point: One hundredth of one percent, or 0.0001.
281
INTERNET USERS HANDBOOK
Basket of USD Shorts: A number of operations where the USD is being sold against various currencies. Bear: A trader who believes prices will fall. Bear Market: An extended period of general price decline in an individual security, an asset, or a market. Bid: The price at which an investor can place an order to buy a currency pair; the quoted price where an investor can sell a currency pair. This is also known as the 'bid price' and 'bid rate'. Bid/Ask Spread: The point difference between the bid and offer (ask) price Big Figure: The first two or three digits of a foreign exchange price or rate. Examples: USD/JPY rate of 108.05/10 the big figure is 108. EUR/USD price of .8325/28 the big figure is .83 Book: The total number of currency positions a dealer has at any given moment. Typically, the dealer aims to have a net position of zero in terms of risk. This means that for the aggregate, all customer's long and short positions balance each other out. Bretton Woods: The site of the conference which in 1944 led to the establishment of the post war foreign exchange system that remained intact until the early 1970s. The conference resulted in the formation of the IMF. The system fixed currencies in a fixed exchange rate system with 1% fluctuations of the currency to gold or the dollar. Broker: An agent, who executes orders to buy and sell currencies and related instruments either for a commission or on a spread. Brokers are agents working on commission and not principals or agents acting on their own account. In the foreign exchange market brokers tend to act as intermediaries between banks bringing buyers and sellers together for a commission paid by the initiator or by both parties. There are four or five major global brokers operating through subsidiaries affiliates and partners in many countries. Brokerage: A company that offers trading services to the public. Bull: A trader who believes that prices will rise. Bull Market: A market which is on a consistent upward trend. Buy Limit Order: An order to execute a transaction at a specified price (the limit) or lower. Buy On Margin: The process of buying a currency pair where a client pays cash for part of the overall value of the position. The word margin refers to the portion the investor puts up rather than the portion that is borrowed. Cable: The British pound/US Dollar exchange rate GBP/USD. Central Bank: A bank, administered by a national government, which regulates the behavior of financial institutions within its borders and carries out monetary policy. Carry Currencies: High interest rate currencies. Carry Grid: A grid of positions (including open orders, take profits, and stop losses) built on a carry trading strategy. Carry Positive: A carry trade where you are long the high interest currency and short the low interest currency. Excluding the volatility of the currency pair, this strategy is profitable based on the interest rate differential between the two countries. Carry Trade: The carry is the cost of keeping a position open overnight. Each currency has a different interest rate associated with it. You are paid interest on the currency you are long on, and you must pay interest on the currency on which you are short. The difference is the carry, sometimes referred to as the cost of carry. Cash on Deposit: Funds deposited in a trading account.
282
INTERNET USERS HANDBOOK
Chartist: A person who attempts to predict prices by analyzing past price movements as recorded on a chart. Clearing House Automated Payment System: A Forex settlement system used in the UK. Clearing House Interbank Payment System: An international wire system used by major banks. Closed Position: A transaction that offsets the number of units in a previous open position. In the case of a long position, selling the exact number of units so that your exposure in the market is zero. Closing a Position: The process of selling or buying a foreign exchange position resulting in the liquidation (squaring up) of the position. Closing Market Rate: The rate at which a position can be closed based on the market price at end of the day. CME: Chicago Mercantile Exchange. Commission: The fee that a broker may charge clients for dealing on their behalf. Commodities Exchange: An exchange where various commodities and derivatives products are traded, including wheat, barley, sugar, maize, cotton, cocoa, coffee, milk products, pork bellies, oil, metals, and so on. The Chicago Board of Trade and New York Mercantile Exchange are the largest and most wellknown commodity exchanges in the world. Commodity Futures Trading Commission: The United States regulatory agency for commodity futures trading Confirmation: Written acknowledgment of a trade, listing important details such as the date, the size of the transaction, the price, the commission, and the amount of money involved. Consumer Price Index (CPI): A month to month economic indicator which gauges changes in the cost of living by measuring price changes in a common basket of goods and services that most people use, such as food, clothing, transportation, and entertainment. Conversion Rate: The value of one currency exchanged for another currency. Convertible Currency: A currency that can be exchanged for another without special permission. Today, most of the currencies which were previously unconvertible are now convertible, such as the Polish Zloty. Copey: Traders' term for the Danish Krone. CORRA: Canadian Overnight Money Market Rate - The rate used by financial institutions to borrow money to cover a shortage of funds (primarily for end-of-day settlement) from those institutions with a surplus of funds. Correlation: A statistical term that refers to a relationship between two seemingly independent things. In Forex for example, one could argue that the Euro and the Sterling have a higher correlation than, for example, the Euro and the Brazilian Real. Correspondent Bank: The foreign banks representative who regularly performs services for a bank which has no branch in the relevant centre, e.g. to facilitate the transfer of funds. In the US this often occurs domestically due to interstate banking restrictions. Counterpart: A participant in a financial transaction. Counterparty: The other party in a Forex deal. In online spot Forex, the counterparty is the market maker. Country Risk: By virtue of economic, political, and geographical factors, some countries are more stable than others. Country risk in reference to Forex means the stability of the currency and the creditworthiness of its bonds.
283
INTERNET USERS HANDBOOK
Cover: (1) To take out a forward foreign exchange contract. (2) To close out a short position by buying currency or securities which have been sold. Cross-Rate: The exchange rate between 2 currencies where neither of the currencies are USD. Currency Code: The currency codes are specified by ISO 4217. Most codes are composed of the country's two-character country code, and the first character of the national currency name. Currency: Money issued by a government coins and paper money. It is a form of money used as a unit of exchange within a country. Currency Pair: The two currencies in a foreign exchange transaction. The EUR/USD is an example of a currency pair. See also: Currency Currency Risk: The risk that shifts in foreign exchange rates may undermine the dollar or any other foreign currency value of overseas investments. DAX: Deutsche Aktien Xchange, Germany's primary stock index. Day Order: A buy or sell order that will expire automatically at the end of the trading day on which it is entered. Day Trade: A trade opened and closed on the same trading day. See also: Day Trader Day Trader: A trader who tries to profit from short-term price movements, often taking and closing a position within the same trade day. Day Trading: The trading style of a Day Trader. See also: Day Trade Deal Blotter: A list of all the deals that were done in a trading day. Deal Ticket: A record of the basic details of a transaction that a dealer keeps, as opposed to the statements that customers receive. Dealer: An individual or firm that buys and sells assets from their own portfolio, acting as a principal or counterparty to a transaction. Dealing Desk: Used loosely as the place where dealers facilitate pricing and executing trades. Dealing Systems: Computer networks that link up banks to create the Forex market. Examples of dealing systems are Reuters' terminals and Bloomberg machines. Default: A term for breaching a contract. Deficit: In economics, when the balance of trades or payments are negative. Deflation: A deep and long-lasting decrease in the price of goods and services within an economy. It is the opposite of inflation which is an escalation in prices. An extended period of deflation can lead to a deflationary spiral - this is a decrease in prices resulting from reduced demand for goods and services which leads to lower employment. With fewer people earning wages, demand falls even more and further perpetuates the cycle. Deflator: The equivalent of the effect of inflation when one considers the difference between real and nominal GDP. See Gross National Product. Delivery: Date When a Forex contract matures, usually two days after the transaction is entered. In the scope of online Forex trading, delivery of the actual currencies is not taken. Rather, profits and losses are credited or debited from one's account balance. Delivery Risk: Risk where a counterparty is not able to fulfill his side of the deal even though he is willing to do so. Depreciation: When the value of a particular currency falls substantially. Depth of Market: The volume of buy and sell orders waiting to be transacted for a particular currency pair at a particular point in time.
284
INTERNET USERS HANDBOOK
Derivative: A financial contract whose value changes in relation to an underlying security. For example, an option changes value according to the asset that underlies it. Desk: See also: Dealing Desk Details: The information necessary to facilitate a Forex transaction. For example: the currency pair, rate, time and date, and the quantity. Deutschmark: The former currency of Germany, replaced by the Euro when Germany joined the European Union. Devaluation: When a government allows the value of its currency to weaken in relation to other currencies. Direct Quotation: Quoting in variable units of domestic currency per fixed units of foreign currency. Dirty Float: Exchange rate policy where the value of a currency is allowed to fluctuate, but the central bank will intervene from time to time. Discount Spread: Refers to the situation where the bid price of a forward spread rate is less than the ask price. Discretionary Account: An account where a customer allows the institution to make trading decisions and buy and sell on his or her behalf. Diversified Carry Basket: A portfolio of carry trade positions that is distributed among different carry currencies and funding currencies in order to limit losses in one particular carry trade position. Dollar Rate: The amount of foreign currency quoted against one US Dollar. Some currencies are quoted in the amount of US Dollars per foreign currency unit, like the British Pound. Domestic Rates: The interest rates that apply to deposits or borrowing of a particular foreign currency. These rates are similar to those offered within the foreign country to citizens who keep money in deposit accounts. Done: The term used by traders to signal that a contract has been agreed upon. Drawdown: The size of a drop in the value of an account from its peak to its low. Durable Goods Order: An economic indicator that marks the change in sales levels of products that have a lifespan of three years or more. Easing: Refers to either a small price decline in a currency or when a central bank engages in monetary policy to spur spending. An example of central bank easing would be lowering of interest rates. ECB: See European Central Bank. ECB Conferences: The top functionaries of the European Central Bank (ECB) hold regular press conferences in which they outline Central Bank decisions and concerns. See also: ECB ECN Broker: Forex ECNs broker provide access to an electronic trading network, supplied with streaming quotes from the top tier banks in the world. By trading through an ECN broker, a currency trader generally benefits from greater price transparency, faster processing, increased liquidity and more availability in the marketplace. Economic Indicator: A statistic that is used to gauge current economic conditions. See Consumer Price Index and Durable Goods Order as examples. ECU: See European Currency Unit. Effective Exchange Rate: Explanation of a country's currency strength or weakness entirely on its trade balance. EFT: Electronic Funds Transfer.
285
INTERNET USERS HANDBOOK
Either Way Market: A condition in the Euro interbank deposit market where both bid and offer rates for a particular period are the same. Electronic Communication Network: An electronic communication network (ECN) is the term used in financial circles for a type of computer system that facilitates trading of financial products outside of stock exchanges. The primary products that are traded on ECNs are stocks and currencies. FX ECNs broker provide access to an electronic trading network, supplied with streaming quotes from the top tier banks in the world. By trading through an ECN broker, a currency trader generally benefits from greater price transparency, faster processing, increased liquidity and more availability in the marketplace. Elliot Wave Principle: An attempt to explain market activity by ascribing a pattern of eight waves to any complete cycle. The eight wave patterns consist of a five-stage advance and a three-stage correction. EMS: See European Monetary System. End of Day Mark to Market: The value of all open positions in a dealer's book based on the closing market rates. In addition, any profits or losses are recorded. Entity Trading Account: A trading account that does not belong to an individual, but rather to a company that has designated a person to be responsible for its trading decisions. Equities: Ownership interest in a corporation in the form of common stock or preferred stock. Equity: Total assets minus total liabilities; also called net worth. See also: Asset Equity Curve: The value of a trading account graphed over a period of time. Escrow Account: A segregated account where customer money is kept separate from a dealer's operating funds. Euribor: Euribor (Euro Interbank Offered Rate) is the rate at which euro interbank term deposits within the euro zone are offered by one prime bank to another prime bank. See also: LIBOR Euro: See also: European Monetary Unit. Euro Interbank Offered Rate: The Euro Interbank Offered Rate or Euribor is a daily reference rate based on the averaged interest rates at which banks offer to lend unsecured funds to other banks in the euro wholesale money market or interbank market. Eurocurrency: A currency that is deposited in a financial institution located outside the currency's country of origin. Eurodollar: US dollars deposited in a bank outside the USA. European Central Bank: Established in Frankfurt in 1998, the ECB is responsible for all monetary policy decisions that influence the Euro currency. Based on the Maastricht Treaty, the ECB's main responsibility is to ensure price stability. To this end, it is authorized to issue the Euro and is responsible for setting interest rates for those countries that have converted to the Euro. European Currency Unit: The predecessor of the Euro. European Monetary System: An arrangement in the 1970s and 1980s where many European countries linked their currencies to prevent large fluctuations in value. It was one of several initiatives leading to the deployment of the Euro. European Monetary Unit: The currency of the European Monetary Union (EMU), introduced in 1999. The following countries and their currencies were replaced with the Euro European Option: An option whose holder can exercise it only at the expiry date.
286
INTERNET USERS HANDBOOK
European Union: The group of European countries joined together to promote economic, political, and social co-operation. Excess Margin Deposits: Deposited funds in a trading account above and beyond what is required for margin requirements. Exchange: The physical location of trading activity. Some famous examples include the New York Stock Exchange or the Chicago Mercantile Exchange. Exchange Control: Various devices a central bank uses for controlling the movement of foreign exchange so as to not deplete a country's reserves. Exchange rate : In finance, the exchange rate (also known as the foreign-exchange rate, Forex rate or FX rate) between two currencies specifies how much one currency is worth in terms of the other. For example an exchange rate of 102 Japanese yen (JPY, ) to the United States dollar (USD, $) means that JPY 102 is worth the same as USD 1. Execution: Completing a trade. Exercise Price: See Strike Price. Exit: In the case of a long position, the sale of the long currency. In a short position; the purchase of the short currency, resulting in a closed position. Exotic: As opposed to the major currencies which are heavily traded, exotics are the less traded currencies. Exotics: The lesser traded currencies, as opposed to the major currencies which are heavily traded. Expiration Date: The day on which a financial option is no longer valid. Exposure: The net of all long and short positions for a particular currency. Based on the traders' positions for all currencies, his/her exposures can result in either loss or gain. Factory Orders: An economic indicator that marks the change from one period to another of the orders for durable and nondurable goods. More orders mean economic growth whereas the opposite signifies a slowdown. Fast Market: Strong buying and/or selling pressure in the market, in which prices often gap and move too quickly to be disseminated. Fed Fund Rate: The interest rate on Fed fund account balances that is closely monitored to gauge the Fed's view on the economy. The accounts are held by member banks and are usually used for lending or borrowing from one another. Fed Funds: Account balances held by banks at their local Fed Bank. Fed Meetings: The Federal Reserve System (the Fed) is the US central bank responsible for conducting US monetary policy by influencing money and credit conditions in the economy. The Federal Reserve Board of Governors and the Federal Open Market Committee (FOMC) hold regularly scheduled and special meetings that are followed closely by market watchers. Federal Deposit Insurance Corporation: FDIC The US regulatory agency that administers bank deposit insurance. Federal Open Market Committee: FOMC Committee made up of Federal Reserve members who meet eight times a year to discuss current monetary policy and its effect on the present economy, and to address any possible changes needed. Federal Reserve: The Central Bank of the United States.
287
INTERNET USERS HANDBOOK
Federal Reserve Board: The senior members of the Federal Reserve, each of whom is appointed by the US President. The chairman of the Fed Reserve Board serves a 4-year term, while the other members serve 14-year terms. Fiat Currency: Fiat currency is the opposite of a gold standard arrangement. In a fiat currency system, the currency value rises and falls on the market in response to demand and supply pressures. It is this fluctuation that makes it possible to speculate on future currency values. Fill: Completing an order to buy or sell. Fill or Kill: An order that must be executed immediately based on certain criteria such as price and quantity. If it cannot be executed, the order is immediately canceled. Fill Price: The price at which a buy or sell order goes through. Financial Risk: The possibility that a business won't be able to meet its financial obligations. Finex: Currency trading at the New York Cotton Exchange. Firm Quote: When a buyer or seller requests a firm quote, the dealer provides a bid and ask quote that can be immediately executed if the buyer or seller wishes. See also: Indicative Quote Fiscal Policy: Using tax policy to affect economic conditions. Fisher Effect: The effect of interest rates on international money movement such that money moves into currencies paying higher interest rates. Fixed Exchange Rate: Foreign exchange policy where a central bank maintains an official rate for their currency, often intervening to keep the rate fixed within a limited range. Fixing: Determining rates by selecting a level which, as well as possible, balances buying and selling pressure. An example is London Gold Fixing. Flat: Term describing a trading book with no market exposure. See also: Square Flexible Exchange Rate: An exchange rate that is fixed, but is re-evaluated frequently. Floating Exchange Rate: An exchange rate whose value is determined by market forces. Force Majeure: French for greater force. Represents a clause in a contract that relieves either party from fulfilling the obligations of the agreement should an extraordinary event prevent the completion of the contract. Typical examples include war, labor strikes, riots, and natural disasters. Commonlyincluded in futures and options contracts especially when dealing with commodities such as oil and agricultural products. Foreign Exchange: Buying or selling one currency against another currency. Foreign Exchange Centers: The largest Forex center in the world is London. Other financial centers which follow the sun across the sky are New York, Tokyo, Hong Kong, Singapore, and Zurich. Trading passes from one center to the next, the traders in one bank's dealing desk handing off the trading book to their colleagues in another center. Forex: Acronym for Foreign Exchange. Forex Charting Software: An analytical, computer-based tool used to help currency traders with Forex trading analysis by charting the price of various currency pairs along with various indicators. Forex charting software packages are used by many traders to determine the direction on any given currency pair. Most Forex brokers allow traders to open a demo account prior to funding a full account or mini account. This allows users to try out each broker's charting software during a trial period. Forex Club: Groups formed in the major financial centers to encourage educational and social contacts between foreign exchange dealers, under the umbrella of Association Cambiste International.
288
INTERNET USERS HANDBOOK
Forex Demo Account: Free Forex Practice Account, trading software and charts. Forex demo accounts allow you to practice Forex trading without risking a monetary loss. Once you've sharpened your skills, you can begin to make big bucks by moving on to Forex live accounts. Forward: A transaction that settles at a future date. Forward Contracts: A transaction that settles at a future date. The buyer and seller are bound by the contract to settle on the specified date. Forward Point: Differential added to or subtracted from the spot rate to calculate the forward rate. The differential is based on anticipating future conditions and fluctuates accordingly. Forward Rates: An exchange rate that differs from the spot exchange rate by forward points. The forward points are either added to or subtracted from the spot rate depending on anticipation of future conditions. Free Reserves: The margin by which excess reserves exceed borrowings. Fundamental Analysis: The study of economic factors (GDP, Trade Balance, Employment, and so on) that can influence prices in financial markets. Fundamental Trader: An investor who uses fundamental analysis. Fundamentals: Economic factors (GDP, Trade Balance, Employment, and so on) that can influence prices in financial markets. Funding Currencies: Low interest rate currencies. Futures: An obligation to exchange a good or instrument at a set price on a future date. The primary difference between a Future and a Forward is that Futures are typically traded over an exchange while forwards are traded over the counter (OTC). G7: The seven leading industrialized countries. G8: G7 and Russia. Gearing: A term related to margin trading where you are controlling a position whose face value is greater than the money you deposit. Globex : An afterhours electronic futures and options trading platform developed by Reuters. Going Long: The purchase of a currency pair. Going Short: Selling a currency pair by first borrowing it, then returning it at a later time by buying it back (hopefully once prices are lower). See also: Selling Short Gold Standard : A commitment made by certain countries to fix the prices of their domestic currencies in terms of a specified amount of gold. Also known as the Bretton Woods System, the Gold Standard was enacted in 1946 and created a system of fixed exchange rates that allowed governments to sell their gold to the United States treasury at a fixed price. On August 15, 1971 President Richard Nixon ended the Bretton Woods system. Golden Cross: In technical analysis, when two moving averages intersect, usually a short one like a 20 day and a long one such as 40 day. This is considered a favorable sign that the underlying currency will move in the same direction. Goldilocks Economy: Term which describes an economy that has steady growth and acceptable inflation. In this sense, the economy is not too hot and not too cold. Good Until Canceled: An order that does not expire at the end of the trading day as is usual practice. Unlike what its name suggests, it does expire at the end of the trading month though, as opposed to being open forever.
289
INTERNET USERS HANDBOOK
Good-Till-Cancelled order (GTC): A type of limit order that remains in effect until it is either executed (filled) or cancelled, as opposed to a day order, which expires if not executed by the end of the trading day. A GTC option order is an order which if not executed will be automatically cancelled at the options expiration. Grid Trading: A series of positions and open orders that are built with a predetermined spread defined by the trader. Gross Domestic Product (GDP): The total value of a country's output produced within its physical borders. Gross National Product: GDP plus production and income from nationals abroad. IFEMA: International Foreign Exchange Master Agreement Indicative Quote: A market maker's price. It is not deal able, but is for information purposes only. See also: Firm Quote Inflation: A rise in prices or a drop in the purchasing power of money. Initial Margin: The first deposit by a customer which determines a corresponding maximum trade size. Initial Margin Requirement: When entering a position, the minimum amount that must be paid in cash. Interbank Market: A market in which financial institutions can trade. The term refers to short term money or foreign exchange markets that are only accessible to banks or financial institutions. There is no physical market place; the transactions take place over communication networks such as Bloomberg or Reuters. Interday Trading: Positions that are opened and closed within the same trading day. Interdealer Market: Same as Interbank Market. Interest Rate: The rate charged or paid for the use of money. An interest rate is expressed as an annual percentage of the principal. Interest rates often change as a result of inflation and Central Bank policies. Interest Rate Swap: A swap that exchanges the revenue generated by the two legs of the agreement. One party pays an agreed-upon fixed interest rate for the notional amount in exchange for the interest that same amount earns for the duration of the agreement. International Monetary Fund (IMF): Supranational organization established in 1946 to provide international liquidity and loans to member countries. International Monetary Market(IM): The futures trading arm of the Chicago Mercantile Exchange. International Organization for Standardization: The organization responsible for developing the standardized Forex trading codes used by traders, such as EUR for Euros or CAD for the Canadian Dollar. Intervention: See Central Bank Intervention. Intra Day Position: Positions that are opened and closed within the same trade day. Introducing Broker: A person or firm that introduces customers to a market maker often in return for commission or a portion of the spread. A person or firm that introduces customers to a market maker often in return for commission or a portion of the spread. ISO: See International Organization for Standardization. ISO 4217: ISO 4217 is the international standard describing three-letter codes (also known as the currency code) to define the names of currencies established by the International Organization for Standardization (ISO Japanese Housewives: A term coined by the financial press to refer to the Japanese households that speculated on the carry trade and became a major seller of yen, thereby driving the currency against the levels forecast by financial institutions.
290
INTERNET USERS HANDBOOK
Japanese yen: The yen is the Japanese currency unit. It is the third most-traded currency in the foreign exchange market after United States dollar and the Euro. See also: JPY Jobber: A trader who trades for small, short-term profits during the course of a trading session, rarely carrying a position overnight. JPY: Japan's currency code becomes JPY JP for Japan and Y for yen. Jurisdiction Risk: The risk that funds will be lost when placed under the jurisdiction of a foreign authority. K: A Nasdaq stock symbol specifying that the stock has no voting rights. Key Currency: For smaller countries, the act of orienting their currency to that of a major trading partner. Kill or Fill: An order that does not permit partial filling. If it cannot be completely filled, then the order is to be canceled (i.e. "killed"). Kiwi: Traders term for the New Zealand Dollar. See also: NZD Ladder Option: An option that locks in gains as the underlying asset reaches predetermined price levels, In this way, these levels are like rungs of a ladder. The gains are locked in even if the asset price should subsequently drop. Lagging Indicator: Economic indicators that change after the overall economy has changed used to confirm effects of Fed policy. An example is the Consumer Price Index (CPI). Leading Indicators: Economic indicators used to predict future economic activity, such as the levels of the S&P 500 index. Left-Hand Side: Refers to the bid quote, which is the price at which customers who are long a currency pair sell it. Leverage: The ratio of margin to the maximum position size. With a deposit of $5000 and a leverage of 50, a trader could enter a position with a face value of $250,000. Leveraging allows you to profit quickly, but lose money just as fast. Liability: The obligation to deliver currency as part of a spot transaction. In speculative Forex trading, currency is not delivered. All profits and losses are subtracted from margin deposits. LIBOR: London Interbank Offered Rate - The rate that banks use when borrowing from one another. See also: London Interbank Offered Rate LIFFE: London International Financial Futures Exchange Limit Order: An order to transact at a specified price or better. See Buy Limit Order and Sell Limit Order. Limit Price: The specified price as part of a limit order. Line Chart: The simplest form of charting, a line chart plots a series of lines connecting the various price levels over a specified time period. Liquid: Term used to describe a market where there are lots of buyers and sellers generating a great deal of volume. Liquidation: This is what happens as a result of a margin call. All positions are closed to prevent further loss. At margin call, the value of the account is not sufficient to sustain the position size. Liquidity: Term used to describe a market where there are lots of buyers and sellers generating a great deal of volume. London Interbank Offered Rate: The London Interbank Offered Rate or LIBOR is a daily reference rate based on the interest rates at which banks borrow unsecured funds from other banks in the London wholesale money market (or interbank market). It is roughly comparable to the U.S. Federal funds rate.
291
INTERNET USERS HANDBOOK
Long Call: An option which gives its holder the right, but not the obligation, to buy the underlying asset. Long Position/Long: When a currency pair is long, the first currency is bought while the second currency is sold short. To go long on a currency means that you buy it. A long position is expressed in terms of the base currency. Long Put: An option which gives its holder the right, but not the obligation, to sell the underlying asset. Lookback Option: An option that lets the holder look back at the prices of the underlying asset during the life of the option and select the ideal price to exercise at. Lots: Standardized method of trading in Forex which requires a trade of 100,000 units of a particular currency. M1: Money supply component which consists of all cash in circulation, plus all of the money held in checking accounts, as well as all the money in travelers checks. M2: Money supply component which consists of M1 plus all of the money held in money market funds, savings accounts, and small Certificates of Deposits. M3: Money supply component which consists of M2 plus all of the large Certificates of Deposits. Maintenance: A set minimum margin that a customer must maintain in his margin account. Maintenance Margin: The minimum margin that must be available in an account to support all open trades. Make A Market: A dealer makes a market by providing a two-way quote a bid and ask price in which they stand ready to buy or sell. In this way, dealers are also known as market makers. Managed Float: Exchange rate policy where central banks regularly intervene to stabilize and/or steer the direction of their currency. Manual Trader: A trader that inputs his/her trades Manually without an API. Margin: The minimum deposit required to maintain an open position. For example, with an open position of $250,000 and a leverage of 50, the required margin would be $5000. Margin Account: An account that allows leverage buying and short selling on credit. Margin Call: A notification that more funds must be deposited into an account because the value of the account has fallen below the minimum margin needed to cover the size of existing positions. Mark-To-Market: For an open position, what its value would be if it were closed out at the current market rates. Market Close: In the 24-hour Forex market, the market never closes. For administrative purposes, many banks institute 5pm EST as the market close in order to differentiate between value dates, as well as mark delivery dates. Market Maker: A dealer who provides a two-way quote a bid and ask price in which they stand ready to buy or sell. In this way, dealers are also known as market makers. Market Order: An order for immediate execution at the best available price. Market Rate: The most current quote for a currency pair. Market Risk: The risks that occur when demand and supply pressures in the market cause the value of an investment to fluctuate. Martingale System: A betting strategy where the gambler doubles his/her bet after every loss, so that the first win recovers all previous losses plus wins a profit equal to the original stake. This strategy may be seen as a sure thing by those who practice it, but will eventually bankrupt people reckless enough to try it because winning may require infinite wealth due to the exponential growth of betting amounts. Maturity: The date on which payment of a financial obligation is due.
292
INTERNET USERS HANDBOOK
Maximum Leverage: The biggest position that a margin deposit would cover. At a leverage of 50, one could enter a maximum leveraged position of $100,000 by depositing $2,000 worth of margin. Mean Reversion: A theory suggesting that prices and returns eventually move back towards the mean or average. MetaTrader: MetaTrader 4 is an online trading platform designed for financial institutions dealing with Forex, CFD, and Futures markets. MetaTrader 4 Mobile: MetaTrader 4 Mobile program is comparable with full-function trading terminal. You have a possibility of full access to financial markets and making deals from anywhere of the world. Middle Rate: The price halfway between the bid and ask quote offered by dealers. Mini Account: A special type of trading account where traders can trade partial lot sizes. Mobile Trading: Controlling of trading account via mobile devices such a cellular phone or a PDA (Personal Digital Assistant). Wireless access technologies WAP and GPRS provide access to the Internet. Module: A portion of a program that carries out a specific function and may be used alone or in combination with other modules of the same program. Momentum: The tendency of the market to continue moving in the same direction in which it is currently moving. Monetarists: People who believe that money and monetary policy have a strong effect on capacity and growth in the economy. Monetarists focus on the work of Milton Friedman. Monetary Base: Required and non-required deposits made at the central bank by member banks and the currency in circulation. Monetary Easing: When a central bank encourages spending by easing monetary controls. An example would be lowering interest rates. Monetary Policy: Central bank attempts to influence the economy through money supply levels. Monetary Policy Committee: The Monetary Policy Committee (MPC) is a committee of the Bank of England that meets every month to decide the official interest rate in the United Kingdom. Money Manager: A person who is responsible for the entire financial portfolio of an individual or other entity. A money manager receives payment in exchange for choosing and monitoring appropriate investments for the client. Most Favored Nation: Preferential treatment in trade between World Trade Organization (WTO) members. Moving Average: Method of smoothing out data on price charts so that trends are easier to spot. Average refers to a mathematical average or a statistical mean that is plotted over the original curve. MXN: The currency symbol for the Mexican peso. Naked Put: A put sold by someone who is not short the underlying asset. Narrow Market: Also known as a thin market, where there is light trading. Net Asset Value (NAV): The total value of an asset less liabilities. In the case of a trading account, the NAV is the balance of deposits, realized and unrealized profit/loss, and interest, minus withdrawals. Negative Carry Pairs: A carry trade where you are long the lower interest currency and short the higher interest currency. This type of trade might be part of a hedging strategy. Negative Sloping Yield Curve: A yield curve is a graph that plots the various yields (usually government bonds) beginning with short term rates on the left side of the graph and extending towards long term rates to the right. Negative sloping refers to the fact that on such a curve short term rates are actually
293
INTERNET USERS HANDBOOK
higher than long term rates. This is contrary to normal yield curves as dictated by the time value of money. Net Interest Rate Differential: The difference in the interest rates associated with two currencies. Net Position: Currency positions that have not been offset with opposite positions. Netting: Settlement method where only the difference (profit or loss) is settled at the close. New Zealand dollar: The New Zealand dollar is the currency of New Zealand. It also circulates in the Cook Islands, Niue, Tokelau, and the Pitcairn Islands. It is divided into 100 cents. See also: NZD News Trader: An investor who bases his/her decisions on the outcome of a news announcement and its impact on the market. NFP (Non-Farm Payroll): Reported monthly, this figure represents the total number of paid U.S. workers of any business, excluding farm employees, general government employees, private household employees, and employees of nonprofit organizations that provide assistance to individuals. The NFP report also includes estimates of the average work week and average weekly earnings of all non-farm employees. Noise: The term used to describe market activity that does not always match overall market sentiment, resulting in a series of variables that, in reality, do not match their modeled counterparts. In general, the shorter the time frame, the more difficult it is to separate the meaningful market movements from the noise. NOK: Currency symbol for the Norwegian Krone. Non-Client Order: An order on an exchange that is made by a participant firm or on behalf of a partner, officer, director, or employee of the participant firm. Where a participant firm is a firm that is entitled to trade on the exchange, also known as a member firm. While these orders are allowed, priority must be given to client orders for the same securities. NYCE: New York Cotton Exchange. NZD: NZD is the currency symbol for the New Zealand Dollar. See also: Kiwi OCO: See also: One Cancels the Other Order Odd Lot: A non-standard transaction size. In Forex, a standard lot is usually 100,000 units of a particular currency. Off-Shore: A business entity that may or may not be physically located in a country, but whose operations and regulation fall outside the country, primarily because it is incorporated elsewhere. Offer: Also known as the Ask Price, it is the price at which a seller is willing to sell. Old Lady: Term for the central bank of England. Omnibus Account: An account that one futures commission merchant carries for another in which the transactions of multiple individual account holders are combined. The identities of the individual account holders are not revealed to the holding merchant. One Cancels the Other Order: Two orders that are submitted simultaneously. If either one is executed, the other one is automatically canceled. Open Order: Buy or sell order that does not expire until canceled. In theory the order does not expire. However, it usually does so at the end of the trading month rather than lasting forever. Open Position: A position whether long or short that is subject to market fluctuations and thus profits or losses. See also: Closed Position Options: The right, but not the obligation, to buy (long call) or sell (long put) an underlying asset. Order: Instructions to buy or sell.
294
INTERNET USERS HANDBOOK
Oscillators: Technical analysis tools that provide buy and sell signals, characterized by a signal that oscillates between overbought and oversold levels. Out of the Money: When the strike price of the option is more expensive than the underlying asset's current price. Over the Counter: Refers to trading that is not done over a formal exchange. Traditional Forex is traded over the counter, meaning traders entered into Forex transactions with one another over telephones or electronic devices. Counter refers to counterparty, in that with Forex one trades with counterparty instead of through an exchange. In online Forex trading, the counterparty is the market maker. Overbought: A currency pair is overbought when its price rises much more quickly than usual in response to net buying. Once overbought, the pair is then expected to make a contrarian move, meaning its price is expected to fall. Overheated Economy: An economy with high inflation and high interest rates. Overnight: Trades that extend past the current trade day into the next. Overnight Limit: The maximum amount of a net long or short position that a dealer can carry over into the next dealing day. Overnight Position: A dealer's net position that is carried into the next trading day. Oversold: A currency pair is oversold when its price falls much more quickly than usual, declining too far in response to net selling. Once oversold, the pair is then expected to make a contrarian move, meaning its price is expected to rise. Owner: The account holder, the name under which a Forex account is held. Par: The official value of a currency. Par Spread: The term used to describe the situation where the bid and ask prices for a forward spread rate are identical. Parity: See Purchasing Power Parity. Partial Lot: Some brokerages allow trading in partial lots, which are fractions of 100,000 units that normally make up a full lot. Pegged: A system where a currency's value is tied with that of another currency. For example: the Chinese Yuan with the US dollar. Most pegs are allowed to deviate within a small band. Petrodollars: Refers to the Forex reserves as a result of oil sold by oil producing nations. Pip: The smallest upward or downward price movements quoted in Forex. In EUR/USD, a movement of 0.0001 is one pip (for example, from 140.005 to 140.004 euro). In USD/JPY, a movement of 0.01 is one pip (for example, from 116.32 to 116.31 yen). Point & Figure Charts: Technical analysis graphs that focus solely on price without any consideration of time. Political Risk: Changes in government policy or to a wider extent, government instability that might have negative effects on the currency. Position: A trade that is still in effect. See Open Position and Closed Position. Premium: See Carry. Premium Spread: Refers to the situation where the bid price of a forward spread rate is greater than the ask price. Price: The cost of purchasing a second currency in terms of a first currency. Price Transparency: The ability of all market participants to trade at the same price. Principal Value: The original amount invested.
295
INTERNET USERS HANDBOOK
Principals: Refers to the major currencies that are traded. Producer Price Index: An economic indicator that gauges the month-to-month price change that producers receive for their output. Profit Taking: Closing a position in order to realize a gain. Purchasing Power Parity: Refers to functional equivalency. It is the relationship between the amount of currency needed to buy a common good in one country and the amount needed to buy the same good in the second country. This is one way to establish an exchange rate between two currencies. Put Writer: The writer of a put option is another name for the seller of a put. Quantitative Analysis: A technique used to analyze an observed behavior by employing complex mathematical and statistical modeling, measurement, and research. Quantitative Easing: Quantitative easing is a monetary tool used by central banks to encourage spending within an economy. One of the most well-known instances of quantitative easing remains the Bank of Japan's attempts to fight domestic deflation in the early 2000s. Interest rates during this time were already close to zero and further cuts could not be implemented so the Bank flooded commercial banks with excess funds to promote lending and by extension, encourage spending. Quote: When both a bid and ask price are provided for a currency pair. Quote Currency: The second currency of two in a currency pair. For the EUR/USD, USD is the quote currency. The exchange rate quoted is how many units of the second currency you will receive for one unit of the base currency. Rainbow Option: An option that has two or more underlying assets. The option only pays out when all the underlying assets act accordingly. Rally: A period where prices surge upward. Range: The difference between the highest and lowest price of a currency pair during a given trading period. Rate: Price at which a currency can be purchased or sold against another currency. Rate Differentials: The difference between the interest rates of two countries. The country with the higher interest rate will attract investment that will be financed in the lower rate country. Rate of Return: The percentage of money gained or lost on an investment relative to the amount of money invested. Ratio Spread: Holding an unequal amount of long and short options positions. Two short and one long is a popular ratio spread strategy. Reaction: When prices fall after a period of advance. Realized P/L: The profit and loss that is generated by closing a position. Reciprocal Currency: A currency pair involving the US Dollar in which the US Dollar is not the first currency quoted. An example is the euro which is the base currency when paired with the US dollar. EUR/USD is the way of quoting these two currencies. Regulated Market: A market in which a government agency monitors and regulates industry activity to protect investors. An example is Forex trading in the United States. Resistance: The term resistance is a technical analysis term that refers to lines on your trading chart that cap a rise in the current price. A resistance line can be just a horizontal line, or it can be sloping with a trend. Resistance only refers to a line that caps the current price. Once the current price definitively breaks through the resistance line, the resistance line becomes a support line.
296
INTERNET USERS HANDBOOK
Retail FX Market: Comprises a wide range of non-institutional traders, from large organizations to individual investors. In less than 10 years, a relatively small number of online currency brokers and market makers have had a massive effect on this market by efficiently exploiting technology, driving a five-fold decrease in the cost of trading. Retail Side: The sale of services, goods, or commodities in small quantities directly to consumers. Revaluation: Daily calculation of potential profits or losses on open positions based on the difference between the settlement price of the previous trading day and the current trading day. Revaluation Rate: A rate, possibly historical (as in the closing rate for the previous trading day), which is used to revalue a dealer's position or book. Right Hand Side: Refers to the ask, or offer price. This is the price at which traders buy. Risk (Foreign Exchange Risk): The risk that the exchange rate on a foreign currency will move against the position held by an investor such that the value of the investment is reduced. Risk Capital: The amount of money one could risk without impinging on one's accustomed lifestyle. Risk Management: The use of strategies to control or reduce financial risk. An example is a stop-loss order that minimizes maximum loss. Roll-Over: Extending the settlement value date on an open position to the next trade date. Rollover Credit: Amount credited to a trader's account when the long currency of a currency pair has a higher yielding interest rate than the shorted currency. Rollover Debit : Amount debited from a trader's account because of an overnight rollover, when the long currency of a currency pair has a lower yielding interest rate than the shorted currency. Rollover Rate: Generally, the daily rollover interest rate is the amount a trader either pays or earns, depending on the currency pairs in question. Round Lot: In most cases, 100,000 units of a currency. Round Trip: The buying and selling of a currency pair and having the profit or loss applied to one's account currency. Running a Position: See Open Position. Same Day Transaction: A position that is opened and closed on the same day. Sell Limit Order: An order to execute a transaction only at a specified price (the limit) or higher. Sell Stop: A limit order with a limit placed below the current market price. Once triggered, the limit order becomes a market order. Selling Rate: Same as the Ask or Offer rate. Selling Short: Selling a currency pair that involves being short the base currency and long the quote currency, with the intent of buying the currency pair at a later time when prices are lower in order to make a profit. Settlement: The physical delivery of currencies made when a contract matures. In Forex, it is usually two days after the trade. In practice, traders don't take delivery, but profits and losses are applied directly to their account balance. Settlement Date: In Forex, the date when physical delivery must take place. For most currency pairs it is two days after the trade date. However, the USD/CAD currency pair settles one day after its trade date. Settlement Risk: Loss as a result of one's counter-party being unable to settle.
297
INTERNET USERS HANDBOOK
Short: Selling a currency pair that involves being short the base currency and long the quote currency, with the intent of buying the currency pair at a later time when prices are lower in order to make a profit. Short Call: An option that obliges the seller to sell the underlying asset to the buyer. Short Covering: Buying the exact same units of a currency pair to offset an earlier short sale of the same currency pair. Short Position: In foreign exchange, when a currency pair is sold, the position is said to be short. It is understood that the primary currency in the pair is 'short', and the secondary currency is 'long'. Short Put: An option which obliges the seller to buy the underlying asset from the buyer. Short Sale: See Selling Short. Short Squeeze : When short sellers frantically scramble to cover their short positions as the market is experiencing a sharp upward movement. The attempt exacerbates the problem because more buying makes the prices higher and more difficult for other short sellers to cover their positions. Shout Option: An option that lets the holder lock in profits while continuing to participate in the movement of the underlying asset. Sidelined: When there is above ordinary interest in a currency pair, other major currency pairs that are thinly traded as a result of this are considered sidelined. Slippage: It's the experience of not getting filled at (or even very close to) your expected price when you place a market order or stop loss. This can happen because either: market price is simply moving too fast, the market is not liquid or you're talking to an unmotivated broker. Society for World-wide Interbank Telecommunications: Global electronic network for Forex settlement, whose office is based in Belgium. Known for the SWIFT Code, which is an 8 or 11 alphanumeric character international standard that uniquely identifies financial institutions for the purpose of transfers and settlement. The SWIFT code is also known as BIC (Bank Identifier Code). Soft Market: Where there are more sellers than buyers resulting in the potential for a quick downtrend. Sovereign Risk: Risk that a country will default on its bonds. Speculative: The condition where there is no guarantee that money will be made and tremendous risk that you will lose all your capital. The attraction to speculative trading is that you can make a great deal of money very quickly. However, you can also lose it just as fast. Spike: A larger than usual price movement. It can be caused by a financial institution entering an erroneous price that appears as a valid price, even though it gets corrected almost immediately. Spot: Buying and selling Forex with the current date's price for valuation, but where settlement usually takes place in two days. Trades on FXTrade are settled immediately. Spot Market: Market where people buy and sell actual financial instruments (currencies) for two-day delivery. Spot Price: The current market price of a currency traded in the spot market. See also: Spot Market Spot/Next Roll: See Roll-Over. Spread : The value difference between the bid and ask price of a currency pair. Square : A condition where all positions in a dealer's books are closed. Squeeze: Central bank attempts to reduce the money supply in order to increase the price of money. Stable Market : A market that can accommodate huge volumes of buying and selling without large moves. For example, the trading of the EUR/USD pair.
298
INTERNET USERS HANDBOOK
Sterilization: The process by which central banks offset intervention in the Forex market by activities in the domestic money market. Sterling: Another name for the British Pound (GBP). See also: Cable Stochastic Oscillator: The stochastic oscillator is a special type of oscillator used for technical analysis. Each type is derived from a different equation and focuses on different aspects of price action. Stock Broker: An agent in the buying and selling of stocks or other securities. Stocky: Traders' term for the Swedish Krona. Stop Loss Order: Order to buy or sell when a given price is reached or passed to liquidate part or all of an existing position. Stop Loss Strategy: A trading strategy that involves setting limit orders at different price levels to avoid incurring further losses. See also: Stop Loss Order Stop Losses: A limit order to close a position when a given limit is reached. When long, the stop loss order is placed below the current market price. When short, the stop loss order is placed above the current market price. Stop Order (or Stop): An order to buy or to sell a currency when the currency's price reaches or passes a specified level. Stop-buy: A buy order for a currency price that is above the current market, or current price. It becomes a market order when the specified price is reached. Stop-buys are used by traders to establish positions in markets which they perceive to be rising in value. Straddle: An option strategy involving holding both a call and put with the same strike price and same expiry date. Strangle: Similar to a straddle, the strangle is a cheaper strategy since the strike prices of both the call and the put are far out of the money. Strike Price: The price at which the underlying asset can be bought or sold as specified in an option contract. Sub-account: Some broker allows users to segregate their accounts into various subaccounts to simplify various trading and hedging strategies. Support Levels: A level or floor beneath which it is difficult for a currency to fall, characterized by strong buying pressure. Swap: A transaction that moves the maturity date of an open position to a future date. See also: RollOver SWIFT: See Society for Worldwide Interbank Telecommunications. Swissy: Trader's nickname for the Swiss Franc. T-Bills: See Treasury Bills. T-Bonds: See Treasury Bonds. T-Notes: See Treasury Notes. T/N: See Tomorrow Next. Take Profit Order: A customer's instructions to buy or sell a currency pair which, when executed, will result in the reduction in the size of the existing position and show a profit on said position. Take Profits: A limit order that is placed above the market with a long position or below the market with a short position. When the market reaches the limit price, the position is closed thereby locking in a profit.
299
INTERNET USERS HANDBOOK
Take the Offer : A verbal order where a trader agrees to the price with which to sell a currency pair to a dealer. Technical Analysis: An effort to forecast prices by analyzing market data, i.e. historical price trends and averages, volumes, open interest, etc. Technical Correction: A price adjustment based on technical factors like resistance and support levels, as well as overbought and oversold levels, instead of market sentiment. Technical Indicators: Short-term trends that technical analysts use to predict future price movements of securities and/or commodities. Also called technicals, technicalities. See also: Technical Analysts Technical Side: The use of historical rates, price charts, and other market data to forecast future prices by means of statistical analysis. Technical Trader: An investor who uses technical analysis. See also: Technical Analysis Technicalities: Short-term trends that technical analysts use to predict future price movements of securities and/or commodities. Also called technicals, technical indicators. TED Spread: Indicates the difference between the London Interbank Offered Rate (LIBOR) and shortterm government debt in the form of three-month U.S. T-bills and expressed in basis points. Seen as a measure of perceived risk in the currency markets. See TED Spread for more information. The City: Located within greater London, UK, The City is one of the largest concentrations of financial and business institutions in the world, and is the largest currency trading center. Thin Market: See Narrow Market. Tick: The smallest possible change in a price, either up or down. Also known as a pip. Ticker: Streaming display of the current or recent historical price of a currency pair. Tier One: The Bank of International Settlements' measure of a bank's financial strength. Tier One is the highest grade. Tomorrow Next: The process of not taking delivery of a currency by closing the position and reopening it with the current trade date so the settlement date is pushed forward to the next trade date (tomorrow). This is done indefinitely until the trade is closed. Trade Date: The date on which a position is opened. Tradeable Amount: The smallest transaction size allowed. For many brokers the tradeable amount is the round lot, which is usually 100,000 units of a particular currency. With FXTrade, it is 1 unit. Trading Margin Excess: Extra funds beyond the margin requirements for existing positions that can be used to enter new positions or increase existing positions. Trading Model: A sophisticated program that provides you with expert buy/sell recommendations for trading currencies on the foreign exchange markets. A Trading Model, based on its evaluation of historical analyses, forecasts, and your trading profile, makes recommendations about currency positions by anticipating fluctuations in the foreign exchange markets and capitalizing on these movements. Trading Platforms: A software application used for trading Forex, usually over the Internet. Trailing Stop Loss: Similar to a stop loss in that it limits potential losses in an open order. But unlike a simple stop loss where the threshold does not change, a trailing stop loss can be instructed to automatically adjust the limit price closer to the market price when the market price moves in your favor. Transaction: Buying or selling a currency pair.
300
INTERNET USERS HANDBOOK
Transaction Cost: The cost involved in buying or selling a currency pair. Some consider the transaction cost to be the actual value of the contract, while others feel it is the price of facilitating the trade, such as commissions and spreads. Transaction Date: The date on which a position is opened or closed. Treasury Bills: US government short-term obligations with 13-, 26-, and 52-week maturities. Treasury Bonds: US government long-term obligations with 15-year or more maturities. Treasury Notes: US government medium-term obligations with 2- to 10-year maturities. Trend: The current direction of the market, whether up or down or sideways (which is sometimes referred to as non-trending or trading market). Trend Lines: Lines, arcs, or other visual cues plotted on a line chart used to predict possible future market directions. Trend lines are often projected from historical points on the graph that are considered significant (retracements, highs, lows, and so on). Turnover: The total volume of all executed transactions in a given time period. Two-Tier Market: A dual exchange rate system in which only one of the rates is open to market pressure, as with the pre-1995 South African Rand. Unconvertible Currency: A currency that cannot be exchanged for another because of foreign exchange regulations. Uncovered: See Open Position. Undervalued: When a currency is below its purchasing power parity it is considered undervalued. Unit: A widely used quantity of currency. In FXTrade, one unit of USD is equal to one United States dollar, while one unit of EUR is one euro. For JPY, one unit is equivalent to one yen. One unit is the smallest trade size in FXTrade. Unrealized P/L: A hypothetical valuation of the current position and the resultant profit or loss if the position were to be liquidated at that moment. Uptick: A trade that must be executed at a price higher than the previous trade. Certain rules on the New York Stock Exchange require this during sessions of extreme volatility. US Dollar: The currency of the United States of America. US Prime Rate: The interest rate at which banks in the US will lend to their most valued customers. US Treasury: The department within the United States government that is responsible for issuing Treasury bills, notes, and bonds. Valuation: The process of determining the value of an asset or company. Value Date: The settlement date for a currency contract, usually two business days. For USD/CAD it is one business day. Variation Margin: Funds, which are required to bring the equity in an account back up to the initial margin level, calculated on a day-to-day basis. Volatility: Measure of how much the price of a currency changes over time. Vostro Account: An account of a foreign bank held at a domestic bank where the foreign bank has no branches. It is used for cash management purposes. Vostro means yours in Latin. See Nostro Account. Warrants: A certificate, usually issued along with a bond or preferred stock, entitling the holder to buy a specific number of securities at a specific price, which is usually above the current market price at the time of issuance, for a specific period of time. Wealth Creation Business: A professional service that includes a combination of investment advice, tax services, and estate planning.
301
INTERNET USERS HANDBOOK
Whipsaw: Refers to when a position is taken and a stop loss is created. The market moves down to trigger the stop loss and then turns around. In this way, the trader suffers two losses Go to Whisper Number: Analyst predictions about earnings or economic indicators. They're considered whispers because they are not made public, but inevitably become public through leaks. Some people call them rumors and attribute as much credibility to them as they do rumors. Wholesale: The sale of services, goods, or commodities in large quantities to individual clients. Wire Transfer: Electronic transfer of funds from one bank to another. Withholding Tax: Income tax withheld from employees' wages and paid directly to the government by the employer. Working Day: When the banks in the country of origin for a particular currency are open for business. For currency pairs, this is compounded by the fact that both banks must be open. World Trade Organization: WTO A global organization of countries that trade with one another and set rules by which trading is conducted. X: A Nasdaq stock symbol specifying that it is a mutual fund. Yard: Traders' term for a billion as in a billion dollars. Yield: The return on an investment. The yield is usually calculated in percentage terms. Yield Curve: A curve that shows the relationship between yields and maturity dates for a set of similar bonds, usually Treasuries, at a given point in time. Z-Score: A statistical measure that quantifies the distance (measured in standard deviations) a data point is from the mean of a data set. In a more financial sense, Z-score is the output from a creditstrength test that gauges the likelihood of bankruptcy. ZAR: Currency symbol for the South African Rand. Zero-Bound: A policy where interest rates are at or very near to zero percent. The major implication of a zero-bound economy is that Central Banks cannot use further interest rate cuts to stimulate an economy in this situation, Central Banks typically turn to an alternate monetary tool known as quantitative easing.
302
INTERNET USERS HANDBOOK
303
INTERNET USERS HANDBOOK
ABOUT THE AUTHOR
DR DON YATES SR. PHD, MBA
Managing Director - Pyrium Web Enterprises Pty Ltd with interests in Networking, Safety, Marketing, Hosting, Design, and Writing Author Internet Users Handbook Platinum Author - Risk Management Founder: The Internet Scams Anonymous (ISA) Groups Forex, Investment Adviser, Entrepreneur, Mentor, Coach, Adviser New Venture: Internet Crime Fighters Org See more at http://about.me/drdony Connect With Me Facebook Twitter LinkedIn Google+
304
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- ISO 27001-2022 Transition BookDokument20 SeitenISO 27001-2022 Transition BookzghibNoch keine Bewertungen
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Lesson 7Dokument42 SeitenLesson 7Nithya NairNoch keine Bewertungen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Imvu Free Credits-Fast-Free-Usa-Ios-Pc-AndroidDokument8 SeitenImvu Free Credits-Fast-Free-Usa-Ios-Pc-Androidapi-538330524Noch keine Bewertungen
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (894)
- Samaresh Das: Education SkillsDokument1 SeiteSamaresh Das: Education SkillsSamaresh DasNoch keine Bewertungen
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Pspice Model For Flicker Noise PDFDokument11 SeitenPspice Model For Flicker Noise PDFmikedelta28Noch keine Bewertungen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- CSE3003-Operating Systems-Laboratory-Practical ExercisesDokument9 SeitenCSE3003-Operating Systems-Laboratory-Practical ExercisesXodiNoch keine Bewertungen
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- WP SOX ComplianceDokument13 SeitenWP SOX ComplianceanandsivNoch keine Bewertungen
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Oed 2,0 2022Dokument139 SeitenOed 2,0 2022Ellish ErisNoch keine Bewertungen
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- BioSystems A-15 Analyzer - Maintenance Manual PDFDokument23 SeitenBioSystems A-15 Analyzer - Maintenance Manual PDFGarcía XavierNoch keine Bewertungen
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- AWUS036EW User Guide PDFDokument29 SeitenAWUS036EW User Guide PDFFelipe GabrielNoch keine Bewertungen
- V Flower Vocaloid Wiki FandomDokument1 SeiteV Flower Vocaloid Wiki FandomFlower chanNoch keine Bewertungen
- Industry LayoutDokument31 SeitenIndustry LayoutGiriraj T KulkarniNoch keine Bewertungen
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- June Exam 2018 Feedback.Dokument3 SeitenJune Exam 2018 Feedback.Jordan MorrisNoch keine Bewertungen
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Compact NSX - SchneiderDokument296 SeitenCompact NSX - SchneiderNicolás Santiago UgarteNoch keine Bewertungen
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Abstract Data TypeDokument19 SeitenAbstract Data TypeAnkit AgrawalNoch keine Bewertungen
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Harsh Environment UPS Features for Critical Industrial ApplicationsDokument2 SeitenHarsh Environment UPS Features for Critical Industrial Applicationsandy175Noch keine Bewertungen
- DS-160 Fault CodesDokument9 SeitenDS-160 Fault CodesKrum KashavarovNoch keine Bewertungen
- Aerial Robot Swarms: A ReviewDokument9 SeitenAerial Robot Swarms: A ReviewIAES International Journal of Robotics and AutomationNoch keine Bewertungen
- Easily Share Your Mobile Broadband Virtually Anywhere: 3G/4G Wireless N300 RouterDokument3 SeitenEasily Share Your Mobile Broadband Virtually Anywhere: 3G/4G Wireless N300 RouterHadiNoch keine Bewertungen
- Fourier Series: Yi Cheng Cal Poly PomonaDokument46 SeitenFourier Series: Yi Cheng Cal Poly PomonaJesusSQANoch keine Bewertungen
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Igad Policy Youth 2022 - Document 1aDokument112 SeitenIgad Policy Youth 2022 - Document 1aRICHARD BONYONoch keine Bewertungen
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- Development of A Buffer Monitoring DashboardDokument47 SeitenDevelopment of A Buffer Monitoring DashboardtelegenicsNoch keine Bewertungen
- Life Elementary A2 Teachers Book Resources For TeaDokument1 SeiteLife Elementary A2 Teachers Book Resources For TeaNguyenhuuhoiNoch keine Bewertungen
- InteliCompact NT Operator Guide 8 2016Dokument13 SeitenInteliCompact NT Operator Guide 8 2016GiangDoNoch keine Bewertungen
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- 04 SQLQueriesDokument18 Seiten04 SQLQueriescccc gggg oooNoch keine Bewertungen
- DX5 EuserguideDokument20 SeitenDX5 Euserguidegabriel ferreyraNoch keine Bewertungen
- Commercial Building Maintenance and External Cleaning CompanyDokument8 SeitenCommercial Building Maintenance and External Cleaning Companybisankhe2Noch keine Bewertungen
- RF Basics - Part 1: Demystifying The DBDokument6 SeitenRF Basics - Part 1: Demystifying The DBRaúl InfanteNoch keine Bewertungen
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Tech MX800Dokument16 SeitenTech MX800Djordje DokicNoch keine Bewertungen
- EC20 HMI Connection GuideDokument3 SeitenEC20 HMI Connection GuideGabriel Villa HómezNoch keine Bewertungen
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)