Beruflich Dokumente
Kultur Dokumente
ISMS Implementation - ISO-27003 PDF
Hochgeladen von
prakashtOriginalbeschreibung:
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
ISMS Implementation - ISO-27003 PDF
Hochgeladen von
prakashtCopyright:
Verfügbare Formate
ISMS Implementation ISO 27003
IT Governance
CEN 667
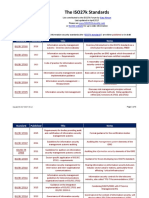
Standard Title: ISO/IEC 27003:2010 Information technology Security
techniques Information security management system implementation
guidance
ISO/IEC 27003 provides implementation guidance to help those
implementing the ISO27k standards.
Purpose of the standard
ISO/IEC 27003 guides the design of an ISO/IEC 27001-compliant ISMS, leading
up to the initiation of an ISMS [implementation] project. It describes the
process of ISMS specification and design from inception to the production of
implementation project plans, covering the preparation and planning
activities prior to the actual implementation, and taking in key elements such
as:
Management approval and final authorization to proceed with the implementation
project;
Scoping and defining the boundaries in terms of ICT and physical locations;
Assessing information security risks and planning appropriate risk treatments, where
necessary defining information security control requirements;
Designing the ISMS;
Planning the implementation project.
The standard references and builds upon other ISO27k standards, particularly the
normative standards ISO/IEC 27000 and ISO/IEC 27001.
3
Structure and content of the 27003:2010 standard
Here is the structure, down to the second level
headings:
1. Scope
2. Normative references
3. Terms and definitions
4. Structure of this international standard
4.1 General structure of clauses
4.2 General structure of a clause
4.3 Diagrams
5. Obtaining management approval for initiating
an ISMS project
5.1 Overview of management approval for initiating the
ISMS project
5.2 Clarify the organizations priorities to develop an
ISMS
5.3 Define the preliminary ISMS scope
5.4 Create the business case and the project plan for
management approval
6 Defining ISMS scope, boundaries and ISMS policy
6.1 Overview on defining ISMS scope, boundaries and
ISMS policy
6.2 Define organizational scope and boundaries
6.3 Define information communication technology (ICT)
scope and boundaries
6.4 Define physical scope and boundaries
6.5 Integrate each scope and boundaries to obtain the
ISMS scope and boundaries
6.6 Develop the ISMS policy and obtain approval from
management
7 Conducting information security requirements
analysis
7.1 Overview of conducting information security
requirements analysis
7.2 Define information security requirements for the
ISMS process
7.3 Identify assets within the ISMS scope
7.4 Conduct an information security assessment
8 Conducting risk assessment and planning
risk treatment
8.1 Overview of conducting a risk assessment and
risk treatment planning
8.2 Conduct risk assessment
8.3 Select the control objectives and controls
8.4 Obtain management authorization for
implementing and operating an ISMS
9 Design the ISMS
9.1
9.2
9.3
9.4
9.5
Overview of designing an ISMS
Design organizational information security
Design ICT and physical information security
Design ISMS specific information security
Produce the final ISMS project plan
Annex A
An ISMS implementation checklist
Annex B
Roles and responsibilities for information security
Annex C
Information about internal auditing
Annex D
Information security policy structure
Annex E
Monitoring and measuring the ISMS
Bibliography
10
ISO 10006:2004 Quality managament systems Guidlines for
quality managamenet in projects
4. Quality managament systems in project
4.1 Project characteristics
4.2 Quality managament systems
5. Managament responsibility
5.1 Managament comitment
5.2 Strategic process
5.3 Managament reviews and process evaluations
6. Resource managament
6.1 Resource-related processes
6.2 Personel-related processes
7. Product realization
7.1 General
7.2 Interdependency-related processes
7.3 Scope-related processes
7.4 Time-related processes
7.5 Cost-related processes
7.6 Risk-related processes
7.8 Purchasing-related processes
8 Measurement, analysis and improvement
8.1 Improvement -related processes
8.2 Measurement and analysis
8.3 Continual improvement
11
ISO/IEC 27003:2010
12
ISO/IEC 27003:2010
5. Obtaining management approval for initiating an ISMS project
5.1 Overview of management approval for initiating the ISMS project
5.2 Clarify the organizations priorities to develop an ISMS
5.3 Define the preliminary ISMS scope
5.4 Create the business case and the project plan for management
approval
13
ISO/IEC 27003:2010
6 Defining ISMS scope, boundaries and ISMS policy
6.1 Overview on defining ISMS scope, boundaries and ISMS policy
6.2 Define organizational scope and boundaries
6.3 Define information communication technology (ICT) scope and boundaries
6.4 Define physical scope and boundaries
6.5 Integrate each scope and boundaries to obtain the ISMS scope and boundaries
14
6.6 Develop the ISMS policy and obtain approval from management
ISO/IEC 27003:2010
7 Conducting information security
requirements analysis
7.1 Overview of conducting information
security requirements analysis
7.2 Define information security
requirements for the ISMS process
7.3 Identify assets within the ISMS scope
7.4 Conduct an information security
assessment
15
ISO/IEC 27003:2010
8 Conducting risk assessment and planning
risk treatment
8.1 Overview of conducting a risk assessment
and risk treatment planning
8.2 Conduct risk assessment
8.3 Select the control objectives and controls
8.4 Obtain management authorization for
implementing and operating an ISMS
16
ISO/IEC 27003:2010
9 Design the ISMS
9.1 Overview of designing an ISMS
9.2 Design organizational information security
9.3 Design ICT and physical information security
9.4 Design ISMS specific information security
9.5 Produce the final ISMS project plan
17
ISO/IEC 27003:2010
9 Design the ISMS
9.1 Overview of designing an ISMS
9.2 Design organizational information security
9.3 Design ICT and physical information
security
9.4 Design ISMS specific information security
9.5 Produce the final ISMS project plan
18
ISO/IEC 27003:2010
9 Design the ISMS
9.1 Overview of designing an ISMS
9.2 Design organizational information security
9.3 Design ICT and physical information
security
9.4 Design ISMS specific information security
9.5 Produce the final ISMS project plan
19
ISO/IEC 27003:2010
20
ISMS Roadmap
Training and
awareness
Governing board
Governing
Risk
approval
Board assessment
policy
Gap analysis
Proces
aproved
maping
Project
borders
agreement
Record
collection
Implementation
Asset
of controls,
collection &
Asset value Statement of procedures...
applicability
DO
PLAN
Monitoring
and
Auditing Improvements
CHECK
ACT
21
Thank you
22
Das könnte Ihnen auch gefallen
- ISO27k ISMS Implementation and Certification Process v3Dokument2 SeitenISO27k ISMS Implementation and Certification Process v3Chamil KulasekeraNoch keine Bewertungen
- Cobit and Iso 27001Dokument64 SeitenCobit and Iso 27001Antonio ClimaNoch keine Bewertungen
- ISO IEC 27001 Lead Implementer A Complete Guide - 2020 EditionVon EverandISO IEC 27001 Lead Implementer A Complete Guide - 2020 EditionNoch keine Bewertungen
- Iso27002 Documentation Toolkit Contents List: Document ControlDokument5 SeitenIso27002 Documentation Toolkit Contents List: Document Controlharis pratamaNoch keine Bewertungen
- ISO 27001 Gap Analysis Service DescriptionDokument4 SeitenISO 27001 Gap Analysis Service DescriptionBlanche AlmondNoch keine Bewertungen
- ISO IEC 27004 DraftDokument37 SeitenISO IEC 27004 DraftdoyNoch keine Bewertungen
- Qualified Security Assessor Complete Self-Assessment GuideVon EverandQualified Security Assessor Complete Self-Assessment GuideNoch keine Bewertungen
- ISO 27001 Implementation - in SMEDokument81 SeitenISO 27001 Implementation - in SMEbudi.hw748Noch keine Bewertungen
- DCSS enDokument36 SeitenDCSS enashvar9Noch keine Bewertungen
- ISO IEC 27001 Lead Auditor A Complete Guide - 2021 EditionVon EverandISO IEC 27001 Lead Auditor A Complete Guide - 2021 EditionNoch keine Bewertungen
- ISO 31000 Risk Management Best Practice A Complete Guide - 2020 EditionVon EverandISO 31000 Risk Management Best Practice A Complete Guide - 2020 EditionNoch keine Bewertungen
- Slides - Risk ISO 27005 03DEC18Dokument20 SeitenSlides - Risk ISO 27005 03DEC18Fulgen De MurciaNoch keine Bewertungen
- ISO 27001 Germany 1695602942Dokument72 SeitenISO 27001 Germany 1695602942Alex AdallomNoch keine Bewertungen
- ISO IEC 27007 2011 en FR - Pdf-DikonversiDokument11 SeitenISO IEC 27007 2011 en FR - Pdf-Dikonversisay SayfudinNoch keine Bewertungen
- ISMS04001 Information Security Management System Policy V1R0 Draft 1Dokument8 SeitenISMS04001 Information Security Management System Policy V1R0 Draft 1Ratna GadheNoch keine Bewertungen
- ISO-IEC 27001 - FAQsDokument4 SeitenISO-IEC 27001 - FAQsRuhyat AzhariNoch keine Bewertungen
- ISO 27001 2013 Vs ISO 20000 2011 Matrix EN PDFDokument10 SeitenISO 27001 2013 Vs ISO 20000 2011 Matrix EN PDFthelmo jarrinNoch keine Bewertungen
- ISO IEC 27001 Lead Implementer A Clear and Concise ReferenceVon EverandISO IEC 27001 Lead Implementer A Clear and Concise ReferenceNoch keine Bewertungen
- ISO IEC 27001 Lead Implementer A Complete Guide - 2021 EditionVon EverandISO IEC 27001 Lead Implementer A Complete Guide - 2021 EditionNoch keine Bewertungen
- ISO - IEC 27001 Standard - Information Security Management SystemsDokument3 SeitenISO - IEC 27001 Standard - Information Security Management SystemsPiiseth KarPearNoch keine Bewertungen
- ISMS Implementer Course - Module 2 - Introduction To ISO27001Dokument21 SeitenISMS Implementer Course - Module 2 - Introduction To ISO27001Anil ChiplunkarNoch keine Bewertungen
- ISO 27001 ISMS Compliance ToolDokument4 SeitenISO 27001 ISMS Compliance ToolRizaldi DjamilNoch keine Bewertungen
- Technical Security Metrics Model in Compliance With ISO/IEC 27001 StandardDokument9 SeitenTechnical Security Metrics Model in Compliance With ISO/IEC 27001 StandardIJCSDFNoch keine Bewertungen
- Security Operations A Complete Guide - 2021 EditionVon EverandSecurity Operations A Complete Guide - 2021 EditionNoch keine Bewertungen
- ISO27k Generic Business Case For ISO IEC 27001 ISMS v2Dokument5 SeitenISO27k Generic Business Case For ISO IEC 27001 ISMS v2Snehal KumarNoch keine Bewertungen
- ISMS Implementation Guide and ExamplesDokument29 SeitenISMS Implementation Guide and ExamplesBabul Bhatt100% (10)
- ISO 27001 Risk Management ApproachDokument52 SeitenISO 27001 Risk Management ApproachSuneel100% (1)
- IT Security Audit: Prepared by Mbabazi SylviaDokument36 SeitenIT Security Audit: Prepared by Mbabazi SylviaMicheal BixNoch keine Bewertungen
- 08.12 Appendix ISO 27001 Internal Audit Checklist Preview enDokument2 Seiten08.12 Appendix ISO 27001 Internal Audit Checklist Preview enBogdan CorneaNoch keine Bewertungen
- Nine Steps to Success: An ISO27001:2013 Implementation OverviewVon EverandNine Steps to Success: An ISO27001:2013 Implementation OverviewBewertung: 1 von 5 Sternen1/5 (1)
- Iso Iec 27032 2012Dokument15 SeitenIso Iec 27032 2012BelhassenNoch keine Bewertungen
- Iso 27005Dokument19 SeitenIso 27005Amr Said83% (6)
- For Training Purposes Only. Do Not Reproduce.: International StandardDokument34 SeitenFor Training Purposes Only. Do Not Reproduce.: International StandardArnel OlivarNoch keine Bewertungen
- ISO27k Standards ListingDokument6 SeitenISO27k Standards ListingTikCGNoch keine Bewertungen
- ISO27001 Tool KitDokument4 SeitenISO27001 Tool Kitl.srinivasakumar65030% (1)
- Iso 27004 - 2016Dokument11 SeitenIso 27004 - 2016RNoch keine Bewertungen
- ISO IEC 27002 Baseline SelectionDokument55 SeitenISO IEC 27002 Baseline SelectionLutfi Swessi100% (3)
- Iso 27001Dokument6 SeitenIso 27001許宏任Noch keine Bewertungen
- Privacy Information Management With ISO 27701: Who Should Implement ISO 27701?Dokument17 SeitenPrivacy Information Management With ISO 27701: Who Should Implement ISO 27701?Sergio RubensNoch keine Bewertungen
- ISO 27001-2013 Transition WorkshopDokument37 SeitenISO 27001-2013 Transition WorkshopALOKE GANGULY100% (1)
- Iso Iec 27005 2022Dokument15 SeitenIso Iec 27005 2022Erick Andrade100% (1)
- CSCF Assessment Template For Mandatory Controls (Version2022) v1.2Dokument179 SeitenCSCF Assessment Template For Mandatory Controls (Version2022) v1.2PetrrNoch keine Bewertungen
- Cism Preparation Course 2015 PDFDokument10 SeitenCism Preparation Course 2015 PDFvivekw2001Noch keine Bewertungen
- Module-1 (The Process of Auditing Information Systems-T)Dokument61 SeitenModule-1 (The Process of Auditing Information Systems-T)yasir_sameemNoch keine Bewertungen
- ISO IEC 27001 Lead Auditor A Complete Guide - 2019 EditionVon EverandISO IEC 27001 Lead Auditor A Complete Guide - 2019 EditionBewertung: 5 von 5 Sternen5/5 (1)
- ISMS SOA Statement of Applicability V1.2 TeamplteDokument11 SeitenISMS SOA Statement of Applicability V1.2 Teampltekabir79Noch keine Bewertungen