Beruflich Dokumente
Kultur Dokumente
Syllabus CNS
Hochgeladen von
senthilvlOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Syllabus CNS
Hochgeladen von
senthilvlCopyright:
Verfügbare Formate
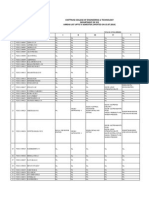
EC2035
LTPC
CRYPTOGRAPHY AND NETWORK SECURITY
3003
AIM
To understand the principles of encryption algorithms; conventional and public key
cryptography. To have a detailed knowledge about authentication, hash functions and
application level security mechanisms.
OBJECTIVES
To know the methods of conventional encryption.
To understand the concepts of public key encryption and number theory
To understand authentication and Hash functions.
To know the network security tools and applications.
To understand the system level security used.
UNIT I INTRODUCTION
10
OSI Security Architecture - Classical Encryption techniques Cipher Principles Data
Encryption Standard Block Cipher Design Principles and Modes of Operation - Evaluation
criteria for AES AES Cipher Triple DES Placement of EncryptionFunction Traffic
Confidentiality
UNIT II PUBLIC KEY CRYPTOGRAPHY
10
Key Management - Diffie-Hellman key Exchange Elliptic Curve Architecture and
Cryptography - Introduction to Number Theory Confidentiality using Symmetric Encryption
Public Key Cryptography and RSA.
UNIT III AUTHENTICATION AND HASH FUNCTION
9
Authentication requirements Authentication functions Message Authentication Codes
Hash Functions Security of Hash Functions and MACs MD5 message Digest algorithm Secure Hash Algorithm RIPEMD HMAC Digital Signatures Authentication Protocols
Digital Signature Standard
UNIT IV NETWORK SECURITY
8
Authentication Applications: Kerberos X.509 Authentication Service Electronic Mail Security
PGP S/MIME - IP Security Web Security.
UNIT V SYSTEM LEVEL SECURITY
8
Intrusion detection password management Viruses and related Threats Virus Counter
measures Firewall Design Principles Trusted Systems.
TEXT BOOKS
TOTAL : 45 PERIODS
1. William Stallings, Cryptography And Network Security Principles and Practices, Pearson
Education, Third Edition, 2003.
2. Behrouz A. Foruzan, Cryptography and Network Security, Tata McGraw-Hill, 2007
REFERENCES
1. Bruce Schneier, Applied Cryptography, John Wiley & Sons Inc, 2001.
2. Charles B. Pfleeger, Shari Lawrence Pfleeger, Security in Computing, Third Edition,
Pearson Education, 2003
3. Wade Trappe and Lawrence C. Washington , Introduction to Cryptography with
4. coding theory , Pearson Education, 2007.
5. Wenbo Mao, Modern Cryptography Theory and Practice , Pearson Education, 2007
6. Thomas Calabrese, Information Security Intelligence : Cryptographic Principles and
Applications, Thomson Delmar Learning,2006.
7. Atul Kahate, Cryptography and Network Security, Tata McGraw-Hill, 2003.
Das könnte Ihnen auch gefallen
- REF Probabilistic Gate-Level Power Estimation Using A NovelWaveform Set MethodDokument6 SeitenREF Probabilistic Gate-Level Power Estimation Using A NovelWaveform Set MethodsenthilvlNoch keine Bewertungen
- Fadd ExtendedDokument36 SeitenFadd ExtendedsenthilvlNoch keine Bewertungen
- CNS QB 2 MK WaDokument25 SeitenCNS QB 2 MK WasenthilvlNoch keine Bewertungen
- Intruders, Passwords, and Intrusion DetectionDokument41 SeitenIntruders, Passwords, and Intrusion DetectionsenthilvlNoch keine Bewertungen
- Pre Internal 1Dokument2 SeitenPre Internal 1senthilvlNoch keine Bewertungen
- Fundamentals & Link LayerDokument38 SeitenFundamentals & Link LayersenthilvlNoch keine Bewertungen
- Operational Description and Message Format of PGPDokument1 SeiteOperational Description and Message Format of PGPsenthilvlNoch keine Bewertungen
- Quartus Ii V7.2: The Signaltap Ii Logic Analyzer LabDokument15 SeitenQuartus Ii V7.2: The Signaltap Ii Logic Analyzer LabsenthilvlNoch keine Bewertungen
- Genetic Algorithm Model ExamDokument1 SeiteGenetic Algorithm Model ExamsenthilvlNoch keine Bewertungen
- Int 1Dokument1 SeiteInt 1senthilvlNoch keine Bewertungen
- Internal 1 Answer KeyDokument2 SeitenInternal 1 Answer KeysenthilvlNoch keine Bewertungen
- Unit 1 QuestionDokument1 SeiteUnit 1 QuestionsenthilvlNoch keine Bewertungen
- Data Link Layer ConceptsDokument16 SeitenData Link Layer ConceptssenthilvlNoch keine Bewertungen
- Application LayerDokument31 SeitenApplication LayersenthilvlNoch keine Bewertungen
- Model ExamDokument1 SeiteModel ExamsenthilvlNoch keine Bewertungen
- IT 3 QuestionDokument1 SeiteIT 3 QuestionsenthilvlNoch keine Bewertungen
- Simulated Output: Wallace:tree MR (3..0) MD (3..0) Booth - Encoder:booth Partial:ppDokument5 SeitenSimulated Output: Wallace:tree MR (3..0) MD (3..0) Booth - Encoder:booth Partial:ppsenthilvlNoch keine Bewertungen
- Internal Examination - 1 Internal Examination - 1Dokument1 SeiteInternal Examination - 1 Internal Examination - 1senthilvlNoch keine Bewertungen
- Ex. No: Date: Creating Virtual Instrumentation For Simple Application AimDokument3 SeitenEx. No: Date: Creating Virtual Instrumentation For Simple Application AimsenthilvlNoch keine Bewertungen
- MEIDokument1 SeiteMEIsenthilvlNoch keine Bewertungen
- Department of Electronics and CommunicationDokument3 SeitenDepartment of Electronics and CommunicationsenthilvlNoch keine Bewertungen
- Cover PAGEDokument1 SeiteCover PAGEsenthilvlNoch keine Bewertungen
- Introduction To ADCs, TutorialDokument58 SeitenIntroduction To ADCs, Tutorialsenthilvl100% (1)
- MEIDokument1 SeiteMEIsenthilvlNoch keine Bewertungen
- Course WorkDokument7 SeitenCourse WorksenthilvlNoch keine Bewertungen
- Arrer List With Subject Name III Ece-NewDokument18 SeitenArrer List With Subject Name III Ece-NewsenthilvlNoch keine Bewertungen
- Embedded SystemsDokument2 SeitenEmbedded SystemssenthilvlNoch keine Bewertungen
- Analog To Digital Converters PresentationDokument31 SeitenAnalog To Digital Converters PresentationJitendra MishraNoch keine Bewertungen
- Expt No.: 2 Design and Implementation of Code Onvertor AimDokument18 SeitenExpt No.: 2 Design and Implementation of Code Onvertor AimsenthilvlNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Ethical Hacking NotesDokument11 SeitenEthical Hacking NotesB Rohit RajNoch keine Bewertungen
- InfoSec AwarenessDokument51 SeitenInfoSec AwarenessGonçalo Almeida TeixeiraNoch keine Bewertungen
- Lec 3Dokument51 SeitenLec 3Muhammad GodaNoch keine Bewertungen
- Accounting Information Systems 14e Romney Chapter 5Dokument26 SeitenAccounting Information Systems 14e Romney Chapter 5Teo RinNoch keine Bewertungen
- ECSAv10 BrochureDokument14 SeitenECSAv10 BrochureJodieNoch keine Bewertungen
- Eco-479 Exam Practice (Dumps)Dokument33 SeitenEco-479 Exam Practice (Dumps)Sulaiman GbadamosiNoch keine Bewertungen
- IT Audit: Security Beyond The Checklist: Interested in Learning More?Dokument37 SeitenIT Audit: Security Beyond The Checklist: Interested in Learning More?Miyamoto MusashiNoch keine Bewertungen
- Chapter 8 Lab 8-1, Secure The Management Plane: Instructor VersionDokument14 SeitenChapter 8 Lab 8-1, Secure The Management Plane: Instructor VersionGuruparan PrakashNoch keine Bewertungen
- Course: MIS (Management Information System) Title: Security Risks On The Web AssignmentDokument10 SeitenCourse: MIS (Management Information System) Title: Security Risks On The Web AssignmentMohammed AwadNoch keine Bewertungen
- SM 1281 Condition Monitoring - IT SecurityDokument1 SeiteSM 1281 Condition Monitoring - IT SecurityCesar SampaioNoch keine Bewertungen
- Part 1Dokument3 SeitenPart 1Đức MinhNoch keine Bewertungen
- Zero Trust Architecture in Industrial Control Systems 1668146228Dokument24 SeitenZero Trust Architecture in Industrial Control Systems 1668146228Bikash kumar ShowNoch keine Bewertungen
- MD 101T00 ENU PowerPoint - 06Dokument26 SeitenMD 101T00 ENU PowerPoint - 06mloga86Noch keine Bewertungen
- Republic of the Philippines Commission on Elections List of Regular Voters (Precinct LevelDokument46 SeitenRepublic of the Philippines Commission on Elections List of Regular Voters (Precinct LevelAngelika CalingasanNoch keine Bewertungen
- Ensuring Security in Mobile Networks Post QuantumDokument13 SeitenEnsuring Security in Mobile Networks Post QuantumJoy DuNoch keine Bewertungen
- PDF Respuesta A Las Preguntas DLDokument6 SeitenPDF Respuesta A Las Preguntas DLmartaNoch keine Bewertungen
- Mcafee Na Virtual Criminology ReportDokument20 SeitenMcafee Na Virtual Criminology ReportnavvaraNoch keine Bewertungen
- KL 002.11.6 en Unit1 v1.0.7Dokument137 SeitenKL 002.11.6 en Unit1 v1.0.7LuizCannalongaNoch keine Bewertungen
- Lab 3Dokument4 SeitenLab 3Nguyen Dinh Quan (K15 HCM)Noch keine Bewertungen
- Encrypt and decrypt a file using AESDokument5 SeitenEncrypt and decrypt a file using AESShaunak bagadeNoch keine Bewertungen
- Chaos-Based Image Encryption AlgorithmDokument6 SeitenChaos-Based Image Encryption AlgorithmMangata AcaronarNoch keine Bewertungen
- WPAWiley Wireless Security Essentials Fly PDFDokument369 SeitenWPAWiley Wireless Security Essentials Fly PDFCristina NistorNoch keine Bewertungen
- KPN PKIoverheid CPS v5.3 EnglishDokument91 SeitenKPN PKIoverheid CPS v5.3 Englishbob cellNoch keine Bewertungen
- Integrigy IOUG Credit Cards and Oracle How To Comply With PCI-DSSDokument27 SeitenIntegrigy IOUG Credit Cards and Oracle How To Comply With PCI-DSSm.glnsNoch keine Bewertungen
- 32 Topic 4-ActiveDokument3 Seiten32 Topic 4-ActiveVladimir ApostolovNoch keine Bewertungen
- TYPES OF COMPUTER FRAUD AND ABUSE TECHNIQUESDokument92 SeitenTYPES OF COMPUTER FRAUD AND ABUSE TECHNIQUEShilmanNoch keine Bewertungen
- Cryptool Lab f05Dokument6 SeitenCryptool Lab f05Vanesa Daza50% (2)
- Peter O & Alessandra Di Carlo - Lessons From The Frontlines - Ransomware Attacks, New Techniques and Old TricksDokument23 SeitenPeter O & Alessandra Di Carlo - Lessons From The Frontlines - Ransomware Attacks, New Techniques and Old TricksFranklin CordeiroNoch keine Bewertungen
- Cybersecurity NotesDokument16 SeitenCybersecurity NotesPratiksha PatilNoch keine Bewertungen
- AZ-500 Exam - Free Actual Q&as, Page 1 - ExamTopicsDokument6 SeitenAZ-500 Exam - Free Actual Q&as, Page 1 - ExamTopicscotit93331Noch keine Bewertungen