Beruflich Dokumente
Kultur Dokumente
Firewall Mode
Hochgeladen von
subhenduOriginalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Firewall Mode
Hochgeladen von
subhenduCopyright:
Verfügbare Formate
CH A P T E R 16
Firewall Mode Overview
This chapter describes how the firewall works in each firewall mode. To set the firewall mode, see the
“Setting Transparent or Routed Firewall Mode” section on page 2-5.
Note In multiple context mode, you cannot set the firewall mode separately for each context; you can only set
the firewall mode for the entire security appliance.
This chapter includes the following sections:
• Routed Mode Overview, page 16-1
• Transparent Mode Overview, page 16-7
Routed Mode Overview
In routed mode, the security appliance is considered to be a router hop in the network. It can use OSPF
or RIP (in single context mode). Routed mode supports many interfaces. Each interface is on a different
subnet. You can share interfaces between contexts.
This section includes the following topics:
• IP Routing Support, page 16-1
• How Data Moves Through the Security Appliance in Routed Firewall Mode, page 16-1
IP Routing Support
The security appliance acts as a router between connected networks, and each interface requires an
IP address on a different subnet. In single context mode, the routed firewall supports OSPF and RIP.
Multiple context mode supports static routes only. We recommend using the advanced routing
capabilities of the upstream and downstream routers instead of relying on the security appliance for
extensive routing needs.
How Data Moves Through the Security Appliance in Routed Firewall Mode
This section describes how data moves through the security appliance in routed firewall mode, and
includes the following topics:
Cisco Security Appliance Command Line Configuration Guide
OL-12172-02 16-1
Chapter 16 Firewall Mode Overview
Routed Mode Overview
• An Inside User Visits a Web Server, page 16-2
• An Outside User Visits a Web Server on the DMZ, page 16-3
• An Inside User Visits a Web Server on the DMZ, page 16-4
• An Outside User Attempts to Access an Inside Host, page 16-5
• A DMZ User Attempts to Access an Inside Host, page 16-6
An Inside User Visits a Web Server
Figure 16-1 shows an inside user accessing an outside web server.
Figure 16-1 Inside to Outside
www.example.com
Outside
209.165.201.2
Source Addr Translation
10.1.2.27 209.165.201.10
10.1.2.1 10.1.1.1
Inside DMZ
92404
User Web Server
10.1.2.27 10.1.1.3
The following steps describe how data moves through the security appliance (see Figure 16-1):
1. The user on the inside network requests a web page from www.example.com.
2. The security appliance receives the packet and because it is a new session, the security appliance
verifies that the packet is allowed according to the terms of the security policy (access lists, filters,
AAA).
For multiple context mode, the security appliance first classifies the packet according to either a
unique interface or a unique destination address associated with a context; the destination address
is associated by matching an address translation in a context. In this case, the interface would be
unique; the www.example.com IP address does not have a current address translation in a context.
Cisco Security Appliance Command Line Configuration Guide
16-2 OL-12172-02
Chapter 16 Firewall Mode Overview
Routed Mode Overview
3. The security appliance translates the local source address (10.1.2.27) to the global address
209.165.201.10, which is on the outside interface subnet.
The global address could be on any subnet, but routing is simplified when it is on the outside
interface subnet.
4. The security appliance then records that a session is established and forwards the packet from the
outside interface.
5. When www.example.com responds to the request, the packet goes through the security appliance,
and because the session is already established, the packet bypasses the many lookups associated
with a new connection. The security appliance performs NAT by translating the global destination
address to the local user address, 10.1.2.27.
6. The security appliance forwards the packet to the inside user.
An Outside User Visits a Web Server on the DMZ
Figure 16-2 shows an outside user accessing the DMZ web server.
Figure 16-2 Outside to DMZ
User
Outside
209.165.201.2 Dest Addr Translation
209.165.201.3 10.1.1.13
10.1.2.1 10.1.1.1
Inside DMZ
92406
Web Server
10.1.1.3
The following steps describe how data moves through the security appliance (see Figure 16-2):
1. A user on the outside network requests a web page from the DMZ web server using the global
destination address of 209.165.201.3, which is on the outside interface subnet.
Cisco Security Appliance Command Line Configuration Guide
OL-12172-02 16-3
Chapter 16 Firewall Mode Overview
Routed Mode Overview
2. The security appliance receives the packet and because it is a new session, the security appliance
verifies that the packet is allowed according to the terms of the security policy (access lists, filters,
AAA).
For multiple context mode, the security appliance first classifies the packet according to either a
unique interface or a unique destination address associated with a context; the destination address
is associated by matching an address translation in a context. In this case, the classifier “knows” that
the DMZ web server address belongs to a certain context because of the server address translation.
3. The security appliance translates the destination address to the local address 10.1.1.3.
4. The security appliance then adds a session entry to the fast path and forwards the packet from the
DMZ interface.
5. When the DMZ web server responds to the request, the packet goes through the security appliance
and because the session is already established, the packet bypasses the many lookups associated
with a new connection. The security appliance performs NAT by translating the local source address
to 209.165.201.3.
6. The security appliance forwards the packet to the outside user.
An Inside User Visits a Web Server on the DMZ
Figure 16-3 shows an inside user accessing the DMZ web server.
Figure 16-3 Inside to DMZ
Outside
209.165.201.2
10.1.2.1 10.1.1.1
Inside DMZ
92403
User Web Server
10.1.2.27 10.1.1.3
Cisco Security Appliance Command Line Configuration Guide
16-4 OL-12172-02
Chapter 16 Firewall Mode Overview
Routed Mode Overview
The following steps describe how data moves through the security appliance (see Figure 16-3):
1. A user on the inside network requests a web page from the DMZ web server using the destination
address of 10.1.1.3.
2. The security appliance receives the packet and because it is a new session, the security appliance
verifies that the packet is allowed according to the terms of the security policy (access lists, filters,
AAA).
For multiple context mode, the security appliance first classifies the packet according to either a
unique interface or a unique destination address associated with a context; the destination address
is associated by matching an address translation in a context. In this case, the interface is unique;
the web server IP address does not have a current address translation.
3. The security appliance then records that a session is established and forwards the packet out of the
DMZ interface.
4. When the DMZ web server responds to the request, the packet goes through the fast path, which lets
the packet bypass the many lookups associated with a new connection.
5. The security appliance forwards the packet to the inside user.
An Outside User Attempts to Access an Inside Host
Figure 16-4 shows an outside user attempting to access the inside network.
Figure 16-4 Outside to Inside
www.example.com
Outside
209.165.201.2
10.1.2.1 10.1.1.1
Inside DMZ
92407
User
10.1.2.27
Cisco Security Appliance Command Line Configuration Guide
OL-12172-02 16-5
Chapter 16 Firewall Mode Overview
Routed Mode Overview
The following steps describe how data moves through the security appliance (see Figure 16-4):
1. A user on the outside network attempts to reach an inside host (assuming the host has a routable
IP address).
If the inside network uses private addresses, no outside user can reach the inside network without
NAT. The outside user might attempt to reach an inside user by using an existing NAT session.
2. The security appliance receives the packet and because it is a new session, the security appliance
verifies if the packet is allowed according to the security policy (access lists, filters, AAA).
3. The packet is denied, and the security appliance drops the packet and logs the connection attempt.
If the outside user is attempting to attack the inside network, the security appliance employs many
technologies to determine if a packet is valid for an already established session.
A DMZ User Attempts to Access an Inside Host
Figure 16-5 shows a user in the DMZ attempting to access the inside network.
Figure 16-5 DMZ to Inside
Outside
209.165.201.2
10.1.2.1 10.1.1.1
Inside DMZ
92402
User Web Server
10.1.2.27 10.1.1.3
The following steps describe how data moves through the security appliance (see Figure 16-5):
1. A user on the DMZ network attempts to reach an inside host. Because the DMZ does not have to
route the traffic on the Internet, the private addressing scheme does not prevent routing.
2. The security appliance receives the packet and because it is a new session, the security appliance
verifies if the packet is allowed according to the security policy (access lists, filters, AAA).
3. The packet is denied, and the security appliance drops the packet and logs the connection attempt.
Cisco Security Appliance Command Line Configuration Guide
16-6 OL-12172-02
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
Transparent Mode Overview
Traditionally, a firewall is a routed hop and acts as a default gateway for hosts that connect to one of its
screened subnets. A transparent firewall, on the other hand, is a Layer 2 firewall that acts like a “bump
in the wire,” or a “stealth firewall,” and is not seen as a router hop to connected devices.
This section describes transparent firewall mode, and includes the following topics:
• Transparent Firewall Network, page 16-7
• Allowing Layer 3 Traffic, page 16-7
• Allowed MAC Addresses, page 16-7
• Passing Traffic Not Allowed in Routed Mode, page 16-8
• MAC Address vs. Route Lookups, page 16-8
• Using the Transparent Firewall in Your Network, page 16-9
• Transparent Firewall Guidelines, page 16-9
• Unsupported Features in Transparent Mode, page 16-10
• How Data Moves Through the Transparent Firewall, page 16-11
Transparent Firewall Network
The security appliance connects the same network on its inside and outside interfaces. Because the
firewall is not a routed hop, you can easily introduce a transparent firewall into an existing network.
Allowing Layer 3 Traffic
IPv4 traffic is allowed through the transparent firewall automatically from a higher security interface to
a lower security interface, without an access list. ARPs are allowed through the transparent firewall in
both directions without an access list. ARP traffic can be controlled by ARP inspection. For Layer 3
traffic travelling from a low to a high security interface, an extended access list is required on the low
security interface. See the “Adding an Extended Access List” section on page 17-5 for more information.
Allowed MAC Addresses
The following destination MAC addresses are allowed through the transparent firewall. Any MAC
address not on this list is dropped.
• TRUE broadcast destination MAC address equal to FFFF.FFFF.FFFF
• IPv4 multicast MAC addresses from 0100.5E00.0000 to 0100.5EFE.FFFF
• IPv6 multicast MAC addresses from 3333.0000.0000 to 3333.FFFF.FFFF
• BPDU multicast address equal to 0100.0CCC.CCCD
• Appletalk multicast MAC addresses from 0900.0700.0000 to 0900.07FF.FFFF
Cisco Security Appliance Command Line Configuration Guide
OL-12172-02 16-7
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
Passing Traffic Not Allowed in Routed Mode
In routed mode, some types of traffic cannot pass through the security appliance even if you allow it in
an access list. The transparent firewall, however, can allow almost any traffic through using either an
extended access list (for IP traffic) or an EtherType access list (for non-IP traffic).
Note The transparent mode security appliance does not pass CDP packets or IPv6 packets, or any packets that
do not have a valid EtherType greater than or equal to 0x600. For example, you cannot pass IS-IS
packets. An exception is made for BPDUs, which are supported.
For example, you can establish routing protocol adjacencies through a transparent firewall; you can
allow OSPF, RIP, EIGRP, or BGP traffic through based on an extended access list. Likewise, protocols
like HSRP or VRRP can pass through the security appliance.
Non-IP traffic (for example AppleTalk, IPX, BPDUs, and MPLS) can be configured to go through using
an EtherType access list.
For features that are not directly supported on the transparent firewall, you can allow traffic to pass
through so that upstream and downstream routers can support the functionality. For example, by using
an extended access list, you can allow DHCP traffic (instead of the unsupported DHCP relay feature) or
multicast traffic such as that created by IP/TV.
MAC Address vs. Route Lookups
When the security appliance runs in transparent mode without NAT, the outgoing interface of a packet
is determined by performing a MAC address lookup instead of a route lookup. Route statements can still
be configured, but they only apply to security appliance-originated traffic. For example, if your syslog
server is located on a remote network, you must use a static route so the security appliance can reach
that subnet.
An exception to this rule is when you use voice inspections and the endpoint is at least one hop away
from the security appliance. For example, if you use the transparent firewall between a CCM and an
H.323 gateway, and there is a router between the transparent firewall and the H.323 gateway, then you
need to add a static route on the security appliance for the H.323 gateway for successful call completion.
If you use NAT, then the security appliance uses a route lookup instead of a MAC address lookup. In
some cases, you will need static routes. For example, if the real destination address is not
directly-connected to the security appliance, then you need to add a static route on the security appliance
for the real destination address that points to the downstream router.
Cisco Security Appliance Command Line Configuration Guide
16-8 OL-12172-02
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
Using the Transparent Firewall in Your Network
Figure 16-6 shows a typical transparent firewall network where the outside devices are on the same
subnet as the inside devices. The inside router and hosts appear to be directly connected to the outside
router.
Figure 16-6 Transparent Firewall Network
Internet
10.1.1.1
Management IP
Network A 10.1.1.2
10.1.1.3
192.168.1.2
Network B
92411
Transparent Firewall Guidelines
Follow these guidelines when planning your transparent firewall network:
• A management IP address is required; for multiple context mode, an IP address is required for each
context.
Unlike routed mode, which requires an IP address for each interface, a transparent firewall has an
IP address assigned to the entire device. The security appliance uses this IP address as the source
address for packets originating on the security appliance, such as system messages or AAA
communications.
The management IP address must be on the same subnet as the connected network. You cannot set
the subnet to a host subnet (255.255.255.255).
You can configure an IP address for the Management 0/0 management-only interface. This IP
address can be on a separate subnet from the main management IP address.
• The transparent security appliance uses an inside interface and an outside interface only. If your
platform includes a dedicated management interface, you can also configure the management
interface or subinterface for management traffic only.
Cisco Security Appliance Command Line Configuration Guide
OL-12172-02 16-9
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
In single mode, you can only use two data interfaces (and the dedicated management interface, if
available) even if your security appliance includes more than two interfaces.
• Each directly connected network must be on the same subnet.
• Do not specify the security appliance management IP address as the default gateway for connected
devices; devices need to specify the router on the other side of the security appliance as the default
gateway.
• For multiple context mode, each context must use different interfaces; you cannot share an interface
across contexts.
• For multiple context mode, each context typically uses a different subnet. You can use overlapping
subnets, but your network topology requires router and NAT configuration to make it possible from
a routing standpoint.
Unsupported Features in Transparent Mode
Table 16-1 lists the features are not supported in transparent mode.
Table 16-1 Unsupported Features in Transparent Mode
Feature Description
Dynamic DNS —
DHCP relay The transparent firewall can act as a DHCP server, but it does not
support the DHCP relay commands. DHCP relay is not required
because you can allow DHCP traffic to pass through using two
extended access lists: one that allows DCHP requests from the inside
interface to the outside, and one that allows the replies from the server
in the other direction.
Dynamic routing protocols You can, however, add static routes for traffic originating on the
security appliance. You can also allow dynamic routing protocols
through the security appliance using an extended access list.
IPv6 You also cannot allow IPv6 using an EtherType access list.
Multicast You can allow multicast traffic through the security appliance by
allowing it in an extended access list.
QoS —
VPN termination for through The transparent firewall supports site-to-site VPN tunnels for
traffic management connections only. It does not terminate VPN connections
for traffic through the security appliance. You can pass VPN traffic
through the security appliance using an extended access list, but it
does not terminate non-management connections. WebVPN is also not
supported.
Cisco Security Appliance Command Line Configuration Guide
16-10 OL-12172-02
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
How Data Moves Through the Transparent Firewall
Figure 16-7 shows a typical transparent firewall implementation with an inside network that contains a
public web server. The security appliance has an access list so that the inside users can access Internet
resources. Another access list lets the outside users access only the web server on the inside network.
Figure 16-7 Typical Transparent Firewall Data Path
www.example.com
Internet
209.165.201.2
Management IP
209.165.201.6
209.165.200.230 Host
209.165.201.3
92412
Web Server
209.165.200.225
This section describes how data moves through the security appliance, and includes the following topics:
• An Inside User Visits a Web Server, page 16-12
• An Inside User Visits a Web Server Using NAT, page 16-13
• An Outside User Visits a Web Server on the Inside Network, page 16-14
• An Outside User Attempts to Access an Inside Host, page 16-15
Cisco Security Appliance Command Line Configuration Guide
OL-12172-02 16-11
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
An Inside User Visits a Web Server
Figure 16-8 shows an inside user accessing an outside web server.
Figure 16-8 Inside to Outside
www.example.com
Internet
209.165.201.2
Management IP
209.165.201.6
92408
Host
209.165.201.3
The following steps describe how data moves through the security appliance (see Figure 16-8):
1. The user on the inside network requests a web page from www.example.com.
2. The security appliance receives the packet and adds the source MAC address to the MAC address
table, if required. Because it is a new session, it verifies that the packet is allowed according to the
terms of the security policy (access lists, filters, AAA).
For multiple context mode, the security appliance first classifies the packet according to a unique
interface.
3. The security appliance records that a session is established.
4. If the destination MAC address is in its table, the security appliance forwards the packet out of the
outside interface. The destination MAC address is that of the upstream router, 209.186.201.2.
If the destination MAC address is not in the security appliance table, the security appliance attempts
to discover the MAC address by sending an ARP request and a ping. The first packet is dropped.
5. The web server responds to the request; because the session is already established, the packet
bypasses the many lookups associated with a new connection.
6. The security appliance forwards the packet to the inside user.
Cisco Security Appliance Command Line Configuration Guide
16-12 OL-12172-02
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
An Inside User Visits a Web Server Using NAT
Figure 16-8 shows an inside user accessing an outside web server.
Figure 16-9 Inside to Outside with NAT
www.example.com
Internet
Static route on router
to 209.165.201.0/27
through security appliance Source Addr Translation
10.1.2.27 209.165.201.10
10.1.2.1
Security Management IP
appliance 10.1.2.2
191243
Host
10.1.2.27
The following steps describe how data moves through the security appliance (see Figure 16-8):
1. The user on the inside network requests a web page from www.example.com.
2. The security appliance receives the packet and adds the source MAC address to the MAC address
table, if required. Because it is a new session, it verifies that the packet is allowed according to the
terms of the security policy (access lists, filters, AAA).
For multiple context mode, the security appliance first classifies the packet according to a unique
interface.
3. The security appliance translates the real address (10.1.2.27) to the mapped address 209.165.201.10.
Because the mapped address is not on the same network as the outside interface, then be sure the
upstream router has a static route to the mapped network that points to the security appliance.
4. The security appliance then records that a session is established and forwards the packet from the
outside interface.
5. If the destination MAC address is in its table, the security appliance forwards the packet out of the
outside interface. The destination MAC address is that of the upstream router, 209.165.201.2.
If the destination MAC address is not in the security appliance table, the security appliance attempts
to discover the MAC address by sending an ARP request and a ping. The first packet is dropped.
6. The web server responds to the request; because the session is already established, the packet
bypasses the many lookups associated with a new connection.
Cisco Security Appliance Command Line Configuration Guide
OL-12172-02 16-13
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
7. The security appliance performs NAT by translating the mapped address to the real address,
10.1.2.27.
An Outside User Visits a Web Server on the Inside Network
Figure 16-10 shows an outside user accessing the inside web server.
Figure 16-10 Outside to Inside
Host
Internet
209.165.201.2
Management IP
209.165.201.6
209.165.201.1
209.165.200.230
92409
Web Server
209.165.200.225
The following steps describe how data moves through the security appliance (see Figure 16-10):
1. A user on the outside network requests a web page from the inside web server.
2. The security appliance receives the packet and adds the source MAC address to the MAC address
table, if required. Because it is a new session, it verifies that the packet is allowed according to the
terms of the security policy (access lists, filters, AAA).
For multiple context mode, the security appliance first classifies the packet according to a unique
interface.
3. The security appliance records that a session is established.
4. If the destination MAC address is in its table, the security appliance forwards the packet out of the
inside interface. The destination MAC address is that of the downstream router, 209.186.201.1.
Cisco Security Appliance Command Line Configuration Guide
16-14 OL-12172-02
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
If the destination MAC address is not in the security appliance table, the security appliance attempts
to discover the MAC address by sending an ARP request and a ping. The first packet is dropped.
5. The web server responds to the request; because the session is already established, the packet
bypasses the many lookups associated with a new connection.
6. The security appliance forwards the packet to the outside user.
An Outside User Attempts to Access an Inside Host
Figure 16-11 shows an outside user attempting to access a host on the inside network.
Figure 16-11 Outside to Inside
Host
Internet
209.165.201.2
Management IP
209.165.201.6
92410
Host
209.165.201.3
The following steps describe how data moves through the security appliance (see Figure 16-11):
1. A user on the outside network attempts to reach an inside host.
2. The security appliance receives the packet and adds the source MAC address to the MAC address
table, if required. Because it is a new session, it verifies if the packet is allowed according to the
terms of the security policy (access lists, filters, AAA).
For multiple context mode, the security appliance first classifies the packet according to a unique
interface.
3. The packet is denied, and the security appliance drops the packet.
4. If the outside user is attempting to attack the inside network, the security appliance employs many
technologies to determine if a packet is valid for an already established session.
Cisco Security Appliance Command Line Configuration Guide
OL-12172-02 16-15
Chapter 16 Firewall Mode Overview
Transparent Mode Overview
Cisco Security Appliance Command Line Configuration Guide
16-16 OL-12172-02
Das könnte Ihnen auch gefallen
- Installing and Configuring Domino 10 On CentOS 7 LinuxDokument41 SeitenInstalling and Configuring Domino 10 On CentOS 7 LinuxDevin Olson50% (2)
- PA ACE-8 1 - Passed80percentDokument12 SeitenPA ACE-8 1 - Passed80percentpisanij12374% (19)
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNVon EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNBewertung: 5 von 5 Sternen5/5 (1)
- Network Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityVon EverandNetwork Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityNoch keine Bewertungen
- Configuring Route Based IPSec With Overlapping NetworksDokument13 SeitenConfiguring Route Based IPSec With Overlapping NetworksRyanb378Noch keine Bewertungen
- Firepower NGFW Labpdf PDFDokument119 SeitenFirepower NGFW Labpdf PDFvelramsenNoch keine Bewertungen
- Hillstone Pantallazos FinalDokument28 SeitenHillstone Pantallazos FinalErnesto PerezNoch keine Bewertungen
- HillstonDokument70 SeitenHillstonCARMEN FLOR AYLLON BASURTO100% (2)
- FirewallDokument40 SeitenFirewallomarsvits100% (5)
- Sagemcom - Fast5355 - Gateway User Guide PDFDokument34 SeitenSagemcom - Fast5355 - Gateway User Guide PDFlinmar7071100% (1)
- Checkpoint Firewall Interview Questions Answers Vol 1.0Dokument16 SeitenCheckpoint Firewall Interview Questions Answers Vol 1.0santhosh437100% (3)
- CCNA Security v2.0 Final Exam Answers 100 1 PDFDokument26 SeitenCCNA Security v2.0 Final Exam Answers 100 1 PDFLêTrungĐức100% (3)
- CentOS 7 Hardening GuideDokument31 SeitenCentOS 7 Hardening GuideNeil TNoch keine Bewertungen
- PCI DSS 3.2.1 Guide: PCI DSS Requirements v3.2.1 Milestone Wazuh Component How It HelpsDokument13 SeitenPCI DSS 3.2.1 Guide: PCI DSS Requirements v3.2.1 Milestone Wazuh Component How It Helpspham huy hungNoch keine Bewertungen
- CCNA 3 v70 Final Exam Answers Full Enterprise Networking Security and Automation PDFDokument49 SeitenCCNA 3 v70 Final Exam Answers Full Enterprise Networking Security and Automation PDFDallandyshe CenaNoch keine Bewertungen
- Assessment System: Take Assessment - CCNAS Chapter 2 - CCNA Security: Implementing Network Security (Version 1.0)Dokument9 SeitenAssessment System: Take Assessment - CCNAS Chapter 2 - CCNA Security: Implementing Network Security (Version 1.0)idanucaNoch keine Bewertungen
- Sample Configurations: Example 1: Multiple Mode Firewall With Outside AccessDokument44 SeitenSample Configurations: Example 1: Multiple Mode Firewall With Outside AccessSiddhartha SarmahNoch keine Bewertungen
- Take Assessment - EWAN Chapter 4 - CCNA Exploration: Accessing The WAN (Version 4.0)Dokument10 SeitenTake Assessment - EWAN Chapter 4 - CCNA Exploration: Accessing The WAN (Version 4.0)crysin21Noch keine Bewertungen
- Sample Configurations: Example 1: Multiple Mode Firewall With Outside AccessDokument44 SeitenSample Configurations: Example 1: Multiple Mode Firewall With Outside Accessagus kurniawanNoch keine Bewertungen
- GlobalProtect VPN For Remote Access SopDokument9 SeitenGlobalProtect VPN For Remote Access SopankitNoch keine Bewertungen
- Types of NAT PDFDokument34 SeitenTypes of NAT PDFgowthamaraj rajendran100% (1)
- Lab Sec 250Dokument21 SeitenLab Sec 250greyhattNoch keine Bewertungen
- Network Security Assignment: AuthorsDokument16 SeitenNetwork Security Assignment: AuthorsAshen SiriwardanaNoch keine Bewertungen
- 4.all ChaptersDokument154 Seiten4.all ChaptersAkwinderKaurNoch keine Bewertungen
- Azure - Windows Server - Host Scan - 2024 Jan q5trvkDokument410 SeitenAzure - Windows Server - Host Scan - 2024 Jan q5trvkeshensanjula2002Noch keine Bewertungen
- Hotel Basic Network Configuration - PNPDokument12 SeitenHotel Basic Network Configuration - PNPAndi Eky Rezky AtmuldinNoch keine Bewertungen
- VPN Site To Site ScenarioDokument74 SeitenVPN Site To Site ScenarioEalrada PiraNoch keine Bewertungen
- Auditing Firewalls Via Packet Crafting With Hping and NemesisDokument23 SeitenAuditing Firewalls Via Packet Crafting With Hping and NemesisFlorick Le MahamatNoch keine Bewertungen
- CCNA Security v20 Final Exam Answers 100Dokument14 SeitenCCNA Security v20 Final Exam Answers 100JonathanNoch keine Bewertungen
- Firebird 2.0 and 2.1 Quick Start Guide: Ibphoenix Editors Firebird Project MembersDokument38 SeitenFirebird 2.0 and 2.1 Quick Start Guide: Ibphoenix Editors Firebird Project MembersRyan KnappNoch keine Bewertungen
- Firewall Design and Deployment: BRKSEC-2020Dokument107 SeitenFirewall Design and Deployment: BRKSEC-2020djdylan78Noch keine Bewertungen
- IOS Zone Based Firewall Step-by-Step Basic ConfigurationDokument14 SeitenIOS Zone Based Firewall Step-by-Step Basic ConfigurationMario NikićNoch keine Bewertungen
- DNS Rebinding Attack LabDokument7 SeitenDNS Rebinding Attack LabTty SmithNoch keine Bewertungen
- Assessment System: Take Assessment - EWAN Chapter 4 - CCNA Exploration: Accessing The WAN (Version 4.0)Dokument3 SeitenAssessment System: Take Assessment - EWAN Chapter 4 - CCNA Exploration: Accessing The WAN (Version 4.0)Mario VicidominiNoch keine Bewertungen
- Network Lab Mid Revision 2024 Last EditDokument55 SeitenNetwork Lab Mid Revision 2024 Last Editzuuo658Noch keine Bewertungen
- Assessment System: Take Assessment - EWAN Chapter 4 - CCNA Exploration: Accessing The WAN (Version 4.0)Dokument4 SeitenAssessment System: Take Assessment - EWAN Chapter 4 - CCNA Exploration: Accessing The WAN (Version 4.0)Mario VicidominiNoch keine Bewertungen
- Csit Pre Gate 2016Dokument94 SeitenCsit Pre Gate 2016vinayNoch keine Bewertungen
- Amswms Code 0780aDokument4 SeitenAmswms Code 0780aaliporNoch keine Bewertungen
- Chapter 2 Test - CCNAS v1.1 - Invisible AlgorithmDokument12 SeitenChapter 2 Test - CCNAS v1.1 - Invisible AlgorithmScott RhodesNoch keine Bewertungen
- CCNAS Final Exam Answer 2Dokument54 SeitenCCNAS Final Exam Answer 2ayion100% (1)
- Cisco CCNA Security Chapter 2 ExamDokument7 SeitenCisco CCNA Security Chapter 2 ExamCCNA5.NETNoch keine Bewertungen
- User Manual For Professional Firmware WZR-HP-G300NH / WZR-HP-G300NH2Dokument184 SeitenUser Manual For Professional Firmware WZR-HP-G300NH / WZR-HP-G300NH2ARVEY ORDOÑEZNoch keine Bewertungen
- 1: Prpoject Overview: Function of Switches, Routers and FirewallDokument9 Seiten1: Prpoject Overview: Function of Switches, Routers and Firewallالمساعدة الأكاديمية للطلابNoch keine Bewertungen
- Take Assessment - CCENT Practice Certification Exam # 1 - CCNA Exploration: Accessing The WAN (Version 4.0)Dokument5 SeitenTake Assessment - CCENT Practice Certification Exam # 1 - CCNA Exploration: Accessing The WAN (Version 4.0)marksafwatNoch keine Bewertungen
- Radware DDOS v1Dokument22 SeitenRadware DDOS v1mejamesonNoch keine Bewertungen
- 1-As A Recommended Practice For Layer 2 Security, How Should VLAN 1 Be TreatedDokument10 Seiten1-As A Recommended Practice For Layer 2 Security, How Should VLAN 1 Be TreatedTaoufic Ben HcineNoch keine Bewertungen
- DCS-932L Firmware Release Notes: ContentDokument5 SeitenDCS-932L Firmware Release Notes: Contentdočasná emailová adresaNoch keine Bewertungen
- DWR-921 C3 FW Release Note - 20170823Dokument6 SeitenDWR-921 C3 FW Release Note - 20170823Tomás PGNoch keine Bewertungen
- Which Security Implementation Will Provide Control Plane Protection For A Network DeviceDokument34 SeitenWhich Security Implementation Will Provide Control Plane Protection For A Network DeviceCallyNnaemekaOkekeNoch keine Bewertungen
- 4.3.3.4 Packet Tracer - Configuring VPN Tunnel ModeDokument3 Seiten4.3.3.4 Packet Tracer - Configuring VPN Tunnel ModeFahadNoch keine Bewertungen
- Chapter1-Vpn Fundamentals - With - Comments - FRDokument39 SeitenChapter1-Vpn Fundamentals - With - Comments - FRnour.barrani2019Noch keine Bewertungen
- Cisco DMZDokument6 SeitenCisco DMZReza ChalabiNoch keine Bewertungen
- CR50-100 Ing QSGDokument12 SeitenCR50-100 Ing QSGPaul Anim AmpaduNoch keine Bewertungen
- 6 Firewallvpn UvxjzadhDokument6 Seiten6 Firewallvpn UvxjzadhRAKTHI VNoch keine Bewertungen
- Chapter4 PDFDokument38 SeitenChapter4 PDFJayesh DeshmukhNoch keine Bewertungen
- Arnaldy 2020Dokument5 SeitenArnaldy 2020rahul49cloudNoch keine Bewertungen
- Kwfsbs62 en v2Dokument52 SeitenKwfsbs62 en v2Isui AtemizNoch keine Bewertungen
- Assessment System: Take Assessment - EWAN Final Exam - CCNA Exploration: Accessing The WAN (Version 4.0)Dokument16 SeitenAssessment System: Take Assessment - EWAN Final Exam - CCNA Exploration: Accessing The WAN (Version 4.0)Euri SubiagaNoch keine Bewertungen
- AMSWMS Code 0740CDokument7 SeitenAMSWMS Code 0740CimkzbyNoch keine Bewertungen
- Amswms Code 0740cDokument7 SeitenAmswms Code 0740cimkzbyNoch keine Bewertungen
- Review On Bastion Hosts: G.Vijayababu, D.Haritha, R.Satya PrasadDokument8 SeitenReview On Bastion Hosts: G.Vijayababu, D.Haritha, R.Satya PrasadMalika AsimNoch keine Bewertungen
- Mapping Security Controls Against Security Guidance RecommendationsDokument23 SeitenMapping Security Controls Against Security Guidance RecommendationsRuslan SoloviovNoch keine Bewertungen
- Securing the Virtual Environment: How to Defend the Enterprise Against AttackVon EverandSecuring the Virtual Environment: How to Defend the Enterprise Against AttackNoch keine Bewertungen
- Intrusion Detection System Using SNORT & BASE (Basic Analysis and Security Engine)Dokument43 SeitenIntrusion Detection System Using SNORT & BASE (Basic Analysis and Security Engine)subhenduNoch keine Bewertungen
- Snort ProjectDokument12 SeitenSnort Projectsubhendu0% (1)
- Ipv 6Dokument12 SeitenIpv 6subhenduNoch keine Bewertungen
- Configuring IP Routing: How Routing Behaves Within The ASA Security ApplianceDokument36 SeitenConfiguring IP Routing: How Routing Behaves Within The ASA Security AppliancesubhenduNoch keine Bewertungen
- FortiWiFi 60DDokument4 SeitenFortiWiFi 60DpaanNoch keine Bewertungen
- Ppars2 Security (Pci Comp)Dokument7 SeitenPpars2 Security (Pci Comp)Alex PiasetskiyNoch keine Bewertungen
- CISSP SG Telecommunications and Network SecurityDokument120 SeitenCISSP SG Telecommunications and Network Securitydkdel0046Noch keine Bewertungen
- CP R81 Gaia AdminGuideDokument466 SeitenCP R81 Gaia AdminGuideEphrem TafesseNoch keine Bewertungen
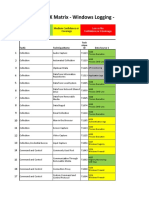
- Mitre ATT@CK Matrix - Windows Logging - Basic: High Confidence or Covereage Medium Confidence or CoverageDokument27 SeitenMitre ATT@CK Matrix - Windows Logging - Basic: High Confidence or Covereage Medium Confidence or CoverageTuba ŞengünNoch keine Bewertungen
- Ipcop - The Perfect Linux Firewall PDFDokument42 SeitenIpcop - The Perfect Linux Firewall PDFsanxetNoch keine Bewertungen
- Ipr2018 00391Dokument54 SeitenIpr2018 00391Tim BillickNoch keine Bewertungen
- interface EthernetDokument4 Seiteninterface EthernetJavier FloresNoch keine Bewertungen
- Cryptography and Network SecurityDokument8 SeitenCryptography and Network SecurityAnish KumarNoch keine Bewertungen
- Chapter 6 WhitmanDokument71 SeitenChapter 6 WhitmanMalaika MunawarNoch keine Bewertungen
- ZScaler Cloud Web Security - DatasheetDokument7 SeitenZScaler Cloud Web Security - DatasheetShahimNoch keine Bewertungen
- Design and Simulation of A Banking NetwoDokument13 SeitenDesign and Simulation of A Banking NetwobelisaNoch keine Bewertungen
- Bharathiar University Arts & Science College ValparaiDokument5 SeitenBharathiar University Arts & Science College ValparaiSathish JuliusNoch keine Bewertungen
- Palo Alto Networks CEF Certified Configuration Guide 03 02 11Dokument12 SeitenPalo Alto Networks CEF Certified Configuration Guide 03 02 11SilvaNoch keine Bewertungen
- Resume - KarthikeyanSDokument2 SeitenResume - KarthikeyanSkarthiksundaram100% (2)
- Performance TunningDokument459 SeitenPerformance TunningramamaheswarareddyNoch keine Bewertungen
- FFT - Introduction To Fortinet Network Security Theory Presentation r3.01Dokument35 SeitenFFT - Introduction To Fortinet Network Security Theory Presentation r3.01FitrahNoch keine Bewertungen
- NSBUNSX NEW Icon Library - Communities - Fall2016Dokument21 SeitenNSBUNSX NEW Icon Library - Communities - Fall2016ElizabethNoch keine Bewertungen
- Asav971.qcow2 GNS3 VM Image InstallDokument11 SeitenAsav971.qcow2 GNS3 VM Image Installtracker00Noch keine Bewertungen
- Understanding Hosts - Allow and Hosts - Deny: Host-Based Access Control List Ultimate Security MeasureDokument10 SeitenUnderstanding Hosts - Allow and Hosts - Deny: Host-Based Access Control List Ultimate Security MeasureAfit FitrianaNoch keine Bewertungen
- Cyberoam CR 250i: Unified Threat ManagementDokument2 SeitenCyberoam CR 250i: Unified Threat ManagementmdrhallyNoch keine Bewertungen
- CP R80.40 SmartProvisioning AdminGuideDokument198 SeitenCP R80.40 SmartProvisioning AdminGuidesdgsdgNoch keine Bewertungen
- OSM Server Manual v1.4.12Dokument125 SeitenOSM Server Manual v1.4.12Orlando Barreto100% (1)
- 3800 Security Gateway DatasheetDokument4 Seiten3800 Security Gateway DatasheetPupsikNoch keine Bewertungen
- 2014-03-03 - NCC Group - Whitepaper - Cyber Battle Ship v1-0Dokument10 Seiten2014-03-03 - NCC Group - Whitepaper - Cyber Battle Ship v1-0Cerys WatkinsNoch keine Bewertungen