Beruflich Dokumente
Kultur Dokumente
BB 31166168
Hochgeladen von
IJMEROriginalbeschreibung:
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
BB 31166168
Hochgeladen von
IJMERCopyright:
Verfügbare Formate
International Journal of Modern Engineering Research (IJMER) www.ijmer.com Vol.3, Issue.1, Jan-Feb.
2013 pp-166-168 ISSN: 2249-6645
Protection of Web Application against Sql Injection Attacks
Sonam Panda, 1 Ramani S2
VIT University, Vellore, India
Abstract: SQL injection attack is the most common attack
in websites now-a-days. Some malicious codes gets injected to the database by unauthorized users and because of this attack, the actual database can be stolen or destroyed or modified or the device can be taken control by the hacker. The main cause of this type of attacks is poor coding by the developers. Hence, the login phase is more vulnerable to SQL injection attack and prevention technique should be applied on this phase to secure the database. In this paper, some predefined methods are discussed and hybrid encryption method is applied in the database to avoid attack on login phase. This applied hybrid encryption method is a combination of Advanced Encryption Standard (AES) and Rabin cryptosystem. These two level encryption methods are applied to a system where facultys information are kept and the designing of this system are done by using PHP and MYSQL.
Keywords: SQL injection attack, hybrid encryption, AES,
Rabin, PHP
I. Introduction
With the rising use of internet, web application vulnerability has been increasing effectively. SQL injection attack is an easiest method of attack in which attackers inject some SQL codes to the original code in the database to get sensitive information or to destroy the information. History says SQL injection attack has been there around for years and now this is a popular method to exploit the security system. Different techniques and methods have been developed and used to protect the database. But still attackers use this method very often because they are finding it easy to type a few deformed SQL commands into the front-end as well as back-end application. Types of SQL injection are tautologies, illegal/ logically in corrected queries, union queries, piggy backed queries, blind injection, timing attacks etc. [3][4]. Attackers inject codes using tautology statements into the authentication phase to enter into the database, which says 1=1 is always true and so the injected query becomes true even if the wrong username and password are being entered. Similarly they use logically incorrect queries to get an error message and this message works as a hint for them to find out some information. Single quotes, double quotes and backslashes are generally used in query to make these incorrect codes work correctly. Union operator is used while injecting codes to join the injected query to the original query. Piggy backed queries are those which use semicolons with injected codes to make duplicate codes work along with original ones. Hackers use blind SQL injection attack by asking some true or false questions if error messages are costumed by programmer. To make a delay in operation, attackers use timing attack and by taking the advantage of
this, attacker hacks the username and password with the use of BENCHMARKS. Cryptography is an absolutely necessary field that ensures the security of database. By applying encryption method, database attacks can be prevented. Encryption of data helps to change the data into a format that is not readable [1]. Without the proper key, this format cant be deciphered even if attacker hacks the information. Application of encryption in login phase makes it difficult for unauthorized users to access the database. Indrani Balasundaram et al. (2011) proposed a query encryption method using hybrid encryption in which two layer of encryption was applied i.e. AES and RSA encryption [2]. The method of encryption which combines a symmetric and an asymmetric encryption method to take the advantages of each type of method is called hybrid encryption method. In symmetric key encryption, one common key is used by sender and receiver where as in asymmetric key encryption, two keys are used (a public key and a private key). This paper proposes a technique which is similar to previous paper but here Rabin encryption method is applied instead of RSA as Rabin cryptosystem is said to be a good replacement of RSA cryptosystem. Between these two, AES is a symmetric key cryptography where Rabin cryptosystem is an asymmetric or public key cryptography. The other part of the paper includes related work about SQL injection attack, work done, implementation and discussion and conclusion respectively.
II. Related work
Ettore Merlo et al. (2006) presented an approach which detects insider and outsider threat in SQL injection attack and the implementation was done in PHP [8]. Hasan Kadhem et al. (2009) proposed mixed cryptography to encrypt database [6]. Atefeh Tajpour et al. (2010) did a survey on all types of SQL injection attacks and prevention methods and evaluated all approaches [5]. Indrani Balasundaram et al. (2011) proposed a hybrid encryption (PSQLIA-HBE) to prevent SQL injection attack where they used AES encryption and RSA cryptosystem in the login and verification phase to make the authentication scheme more secure.
III. Work Done
Some predefined methods like quote block function, regular expressions, parameterized queries are used to avoid quotes and strings because their presence have important roles in SQL injection attacks. Especially in PHP, there are predefined codes using these methods to escape from SQL injection attacks [7]. So these are used in this project and for preventing greater exploitation encryption methods are used. The model proposed by Indrani Balasundaram et al. is used in this paper also. The only difference is that here, Rabin cryptosystem is used instead of RSA cryptosystem www.ijmer.com 166 | Page
International Journal of Modern Engineering Research (IJMER) www.ijmer.com Vol.3, Issue.1, Jan-Feb. 2013 pp-166-168 ISSN: 2249-6645 as it is a good replacement to RSA. So, basically the system model is an adaption of previously proposed model. The system model includes three phases i.e. registration phase, login phase and verification phase. 1. In registration phase, a new user registers his/her name by selecting unique username and password and the data get sent to server and when server receives the username and password, it saves these information in the database in a table and along these data; server keeps a unique key for each username generated by the server itself. Then server sends back a confirmation request to the client. username and password match to the database table, the login request gets accepted.
Fig 3: model of verification phase A little more work is added i.e. after login, a user can search for the facultys information. The faculty information contains the faculty name, employee id, school name, course title, time, date; slot etc. and one can search by the employee id to know about the information related to the id.
Fig 1: model of registration phase 2. In login phase, when a registered user tries to login, the username and password get encrypted by applying AES encryption algorithm which uses users secret key. After that, a query gets generated automatically using the encrypted username and password. Then Rabin encryption is used to encrypt the query where servers public key is used to encrypt the query and once it gets encrypted it is sent to the server.
IV. Implementation
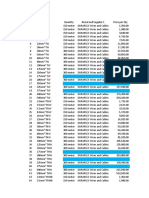
The whole implementation is done in windows operating system and the code is developed by using HTML, PHP and MYSQL. PHP has its own predefined commands such as mysql_real_escape_string and stripslashes which are used in this project. So first part of the paper includes a little survey based on predefined function. Net Beans IDE 7.0 and Wamp Server are used for the implementation. In second part, the system model is an adaption of the model proposed by Indrani Balasundaram et al. (2011). They have implemented the model using core java but here PHP and MYSQL are used. In database, separate tables are there for AES encryption, Rabin encryption, Rabin decryption and AES decryption and all tables have a common column i.e. id. For example,
Fig 4: Secret Key Generation after Registration
Fig 2: model of login phase 3. In verification phase, when server receives the query, it uses Rabin decryption method to decrypt the query where the servers private keys are used. Server then checks the username and password and again the username and password gets decrypted using AES decryption algorithm. After getting decrypted, if the
Fig 5: Sample Example of AES Encryption in Database The third part consists of four tables i.e. school, faculty, course and slot. All these tables are connected to each other by primary key. So when user searches by giving any employee id, it retrieves the related information. This system is to provide information to students as well as teachers when they need. 167 | Page
www.ijmer.com
International Journal of Modern Engineering Research (IJMER) www.ijmer.com Vol.3, Issue.1, Jan-Feb. 2013 pp-166-168 ISSN: 2249-6645
V. Conclusion and Future Work
In this paper, various types of SQL injection attacks as well as predefined prevention methods are discussed. Then the hybrid encryption method is used which includes AES encryption and Rabins cryptosystem. The reason behind the use of two layer of encryption is that it will be more secured. SQL query is generated and encrypted by Rabins cryptosystem because even if hackers hack the information and decode the AES encryption part, it will still be more difficult for them to know about the encrypted query. Between Rabin and RSA, it is difficult to say which cryptosystem is better. So Rabin encryption is applied in this paper because it is a good alternative to RSA and in some cases Rabin is a little faster than RSA. This proposed method is an attempt to add some more security to databases to avoid SQL injection attack.
[1] [2] [3] [4] [5] [6]
References
Berhrouz A Forouzan et al., Cryptography and Network Security, New Delhi: McGraw-Hill Indrani Balasundaram et al. An authentication scheme for preventing SQL injection attack using hybrid encryption (PSQLIA-HBE) Euro journal publishing, 2011. XuePing-Chen SQL injection attack and guard technical research 2011. Varian Luong Intrusion detection and prevention system: SQL injection attacks, 2010. Atefeh Tajpour et al. Evaluation of SQL Injection Detection and Prevention Techniques Second International Conference on Computational Intelligence, 2010. Hasan Kadhem et al. A Novel Framework for Database Security based on Mixed Cryptography Fourth International Conference on Internet and Web Applications and Services, 2009. Ettore Merlo et al. Automated protection of PHP applications against SQL injection attacks IEEE 2007. Ettore Merlo et al. Insider and outsider threat sensitive SQL injection vulnerability analysis in PHP IEEE 2006.
[7] [8]
www.ijmer.com
168 | Page
Das könnte Ihnen auch gefallen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (894)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- HenyaDokument6 SeitenHenyaKunnithi Sameunjai100% (1)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Non Circumvention Non Disclosure Agreement (TERENCE) SGDokument7 SeitenNon Circumvention Non Disclosure Agreement (TERENCE) SGLin ChrisNoch keine Bewertungen
- Interpretation of Arterial Blood Gases (ABGs)Dokument6 SeitenInterpretation of Arterial Blood Gases (ABGs)afalfitraNoch keine Bewertungen
- Data Mining For Fraud DetectionDokument4 SeitenData Mining For Fraud DetectionIJMERNoch keine Bewertungen
- Maverick Brochure SMLDokument16 SeitenMaverick Brochure SMLmalaoui44Noch keine Bewertungen
- IoT BASED HEALTH MONITORING SYSTEMDokument18 SeitenIoT BASED HEALTH MONITORING SYSTEMArunkumar Kuti100% (2)
- Philippine Coastal Management Guidebook Series No. 8Dokument182 SeitenPhilippine Coastal Management Guidebook Series No. 8Carl100% (1)
- Survey On Data Mining and Its Area of ApplicationDokument6 SeitenSurvey On Data Mining and Its Area of ApplicationIJMERNoch keine Bewertungen
- The Dynamics of Two Harvesting Species With Variable Effort Rate With The Optimum Harvest PolicyDokument9 SeitenThe Dynamics of Two Harvesting Species With Variable Effort Rate With The Optimum Harvest PolicyIJMERNoch keine Bewertungen
- Historiography and Caste OppressionDokument5 SeitenHistoriography and Caste OppressionIJMERNoch keine Bewertungen
- Assessment of Steganography Using Image Edges For Enhancement in SecurityDokument11 SeitenAssessment of Steganography Using Image Edges For Enhancement in SecurityIJMERNoch keine Bewertungen
- Liquefaction Susceptibility Evaluation of Hyderabad SoilDokument7 SeitenLiquefaction Susceptibility Evaluation of Hyderabad SoilIJMERNoch keine Bewertungen
- Converting Daily Solar Radiation Tabulated Data With Different Sky Conditions Into Analytical Expression Using Fourier Series TechniqueDokument9 SeitenConverting Daily Solar Radiation Tabulated Data With Different Sky Conditions Into Analytical Expression Using Fourier Series TechniqueIJMERNoch keine Bewertungen
- The Combining Approach of Svms With Ant Colony Networks: An Application of Network Intrusion DetectionDokument8 SeitenThe Combining Approach of Svms With Ant Colony Networks: An Application of Network Intrusion DetectionIJMERNoch keine Bewertungen
- X Chromosomal MinerDokument7 SeitenX Chromosomal MinerIJMERNoch keine Bewertungen
- An Efficient Algorithm Based On Modularity OptimizationDokument6 SeitenAn Efficient Algorithm Based On Modularity OptimizationIJMERNoch keine Bewertungen
- Synthesis and Characterization of Partial Blended Green Polymer ElectrolytesDokument6 SeitenSynthesis and Characterization of Partial Blended Green Polymer ElectrolytesIJMERNoch keine Bewertungen
- An Use of Fuzzy Logic For Development and Analysis of Rainfall - Runoff ModelDokument8 SeitenAn Use of Fuzzy Logic For Development and Analysis of Rainfall - Runoff ModelIJMERNoch keine Bewertungen
- Thermodynamic Analysis of Cooled Blade Gas Turbine Cycle With Inlet FoggingDokument9 SeitenThermodynamic Analysis of Cooled Blade Gas Turbine Cycle With Inlet FoggingIJMERNoch keine Bewertungen
- Stabilization of Waste Soil at Karur Dump Yard by Using Polypropylene FiberDokument5 SeitenStabilization of Waste Soil at Karur Dump Yard by Using Polypropylene FiberIJMERNoch keine Bewertungen
- Understanding The Behavior of Band-Pass Filter With Windows For Speech SignalDokument7 SeitenUnderstanding The Behavior of Band-Pass Filter With Windows For Speech SignalIJMERNoch keine Bewertungen
- Biorthogonal Nonuniform Multiwavelet Packets Associated With Nonuniform Multiresolution Analysis With Multiplicity DDokument6 SeitenBiorthogonal Nonuniform Multiwavelet Packets Associated With Nonuniform Multiresolution Analysis With Multiplicity DIJMERNoch keine Bewertungen
- A Study On Corrosion Inhibitor of Mild-Steel in Hydrochloric Acid Using Cashew WasteDokument6 SeitenA Study On Corrosion Inhibitor of Mild-Steel in Hydrochloric Acid Using Cashew WasteIJMERNoch keine Bewertungen
- Heuristics For Routing and Spectrum Allocation in Elastic Optical Path NetworksDokument13 SeitenHeuristics For Routing and Spectrum Allocation in Elastic Optical Path NetworksIJMERNoch keine Bewertungen
- Improved Aodv Routing in Wireless Sensor Networks Using Shortest Path Routing.Dokument6 SeitenImproved Aodv Routing in Wireless Sensor Networks Using Shortest Path Routing.IJMERNoch keine Bewertungen
- A Modified PSO Based Solution Approach For Economic Ordered Quantity Problem With Deteriorating Inventory, Time Dependent Demand Considering Quadratic and Segmented Cost FunctionDokument14 SeitenA Modified PSO Based Solution Approach For Economic Ordered Quantity Problem With Deteriorating Inventory, Time Dependent Demand Considering Quadratic and Segmented Cost FunctionIJMERNoch keine Bewertungen
- Space Ball 2D GameDokument7 SeitenSpace Ball 2D GameIJMERNoch keine Bewertungen
- MHD Flow of A Non-Newtonian Fluid Through A Circular TubeDokument10 SeitenMHD Flow of A Non-Newtonian Fluid Through A Circular TubeIJMERNoch keine Bewertungen
- Effects of Heat, Mass Transfer and Viscous Dissipation On Unsteady Flow Past An Oscillating Infinite Vertical Plate With Variable Temperature Through Porous MediumDokument7 SeitenEffects of Heat, Mass Transfer and Viscous Dissipation On Unsteady Flow Past An Oscillating Infinite Vertical Plate With Variable Temperature Through Porous MediumIJMERNoch keine Bewertungen
- "Analysis of Mechanical Properties of Carbon Fiber Polymer Composite Materials Used As Orthopaedic Implants".Dokument8 Seiten"Analysis of Mechanical Properties of Carbon Fiber Polymer Composite Materials Used As Orthopaedic Implants".IJMERNoch keine Bewertungen
- Combined PWM Technique For Asymmetric Cascaded H-Bridge Multilevel InverterDokument10 SeitenCombined PWM Technique For Asymmetric Cascaded H-Bridge Multilevel InverterIJMERNoch keine Bewertungen
- The Reality of Application of Total Quality Management at Irbid National University From The Perspective of AcademiciansDokument8 SeitenThe Reality of Application of Total Quality Management at Irbid National University From The Perspective of AcademiciansIJMERNoch keine Bewertungen
- Increasing Efficiency of Wireless Sensor Network Using Decentralized ApproachDokument6 SeitenIncreasing Efficiency of Wireless Sensor Network Using Decentralized ApproachIJMERNoch keine Bewertungen
- Biokinetic Study of Fish Processing Industrial Effluent Treatment in FBBRDokument4 SeitenBiokinetic Study of Fish Processing Industrial Effluent Treatment in FBBRIJMERNoch keine Bewertungen
- ConductorsDokument4 SeitenConductorsJohn Carlo BautistaNoch keine Bewertungen
- AFNOR IPTDS BrochureDokument1 SeiteAFNOR IPTDS Brochurebdiaconu20048672Noch keine Bewertungen
- PRODUCTDokument82 SeitenPRODUCTSrishti AggarwalNoch keine Bewertungen
- Liebert PSP: Quick-Start Guide - 500VA/650VA, 230VDokument2 SeitenLiebert PSP: Quick-Start Guide - 500VA/650VA, 230VsinoNoch keine Bewertungen
- Axe Case Study - Call Me NowDokument6 SeitenAxe Case Study - Call Me NowvirgoashishNoch keine Bewertungen
- Passenger E-Ticket: Booking DetailsDokument1 SeitePassenger E-Ticket: Booking Detailsvarun.agarwalNoch keine Bewertungen
- BPL Millipacs 2mm Hardmetrics RarDokument3 SeitenBPL Millipacs 2mm Hardmetrics RarGunter BragaNoch keine Bewertungen
- 2014 mlc703 AssignmentDokument6 Seiten2014 mlc703 AssignmentToral ShahNoch keine Bewertungen
- Marketing Plan for Monuro Clothing Store Expansion into CroatiaDokument35 SeitenMarketing Plan for Monuro Clothing Store Expansion into CroatiaMuamer ĆimićNoch keine Bewertungen
- Experiences from OJT ImmersionDokument3 SeitenExperiences from OJT ImmersionTrisha Camille OrtegaNoch keine Bewertungen
- Leaked David Fry II Conversation Regarding Loopholes and Embezzlement at AFK Gamer LoungeDokument6 SeitenLeaked David Fry II Conversation Regarding Loopholes and Embezzlement at AFK Gamer LoungeAnonymous iTNFz0a0Noch keine Bewertungen
- Survey Course OverviewDokument3 SeitenSurvey Course OverviewAnil MarsaniNoch keine Bewertungen
- Music 7: Music of Lowlands of LuzonDokument14 SeitenMusic 7: Music of Lowlands of LuzonGhia Cressida HernandezNoch keine Bewertungen
- TWP10Dokument100 SeitenTWP10ed9481Noch keine Bewertungen
- Reflection Homophone 2Dokument3 SeitenReflection Homophone 2api-356065858Noch keine Bewertungen
- IDokument2 SeitenIsometoiajeNoch keine Bewertungen
- 621F Ap4405ccgbDokument8 Seiten621F Ap4405ccgbAlwinNoch keine Bewertungen
- Book Networks An Introduction by Mark NewmanDokument394 SeitenBook Networks An Introduction by Mark NewmanKhondokar Al MominNoch keine Bewertungen
- MID TERM Question Paper SETTLEMENT PLANNING - SEC CDokument1 SeiteMID TERM Question Paper SETTLEMENT PLANNING - SEC CSHASHWAT GUPTANoch keine Bewertungen
- Resume of Deliagonzalez34 - 1Dokument2 SeitenResume of Deliagonzalez34 - 1api-24443855Noch keine Bewertungen
- Requesting A Query in Zemanta Using PHPDokument10 SeitenRequesting A Query in Zemanta Using PHPAther SajjadNoch keine Bewertungen
- 2-Port Antenna Frequency Range Dual Polarization HPBW Adjust. Electr. DTDokument5 Seiten2-Port Antenna Frequency Range Dual Polarization HPBW Adjust. Electr. DTIbrahim JaberNoch keine Bewertungen
- Skuld List of CorrespondentDokument351 SeitenSkuld List of CorrespondentKASHANNoch keine Bewertungen