Beruflich Dokumente
Kultur Dokumente
CS 2012
Hochgeladen von
laxitkumarOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
CS 2012
Hochgeladen von
laxitkumarCopyright:
Verfügbare Formate
2012
Question Booklet Cod~
CS : COMPUTER
Duration:
SCIENCE & INFORMATION
TECHNOLOGY
MaximulIl Marks:
c
100
Three Hours
carefully.
Read the following instructions
1. Do not open the seal of the Question Booklet until you are asked to do so by the invigilator. 2. Take out the Optical Response Sheet (ORS) from this Question Booklet without breaking the seal and read the instructions printed on the ORS carefully. If you find that the Question Booklet Code printed at the right hand top corner of this page does not match with the Booklet Code on the ORS, exchange the booklet immediately with a new sealed Question Booklet. On the right half of the ORS, using ONLY a black ink ball point pen, (i) darken the bubble corresponding to your test paper code and the appropriate bubble under each digit of your registration number and (ii) write your registration number, your name and name of the examination centre and put your signature at the specified location. This Question Booklet contains 20 pages including blank pages for rough work. After you are permitted to open the seal, please check all pages and report discrepancies, if any, to the invigilator. There are a total of 65 questions carrying 100 marks. All these questions are of objective type. Each question has only one conect answer. Questions must be answered on the left hand side of the ORS by darkening the appropriate bubble (marked A, B, C, D) using ONLY a black ink ball point pen against the question number. For each question darken the bubble of the correct answer. More than one answer bubbled against a question will be treated as an incorrect response. Since bubbles darkened by the black ink ball point pen cannot be erased, candidates should darken the bubbles in the ORS very carefully.
3.
4. 5.
6.
7. -Questions Q.l - Q.25 cany 1 mark each. Questions Q.26 - Q.55 cany 2 marks each. The 2 marks questions include two pairs of common data questions and two pairs of linked answer questions. The answer to the second question of the linked answer questions depends on the answer to the first question of the pair. If the first question in the linked pair is wrongly answered or is unattempted, then the answer to the second question in the pair will not be evaluated. 8. Questions Q.56 - Q.65 belong to General Aptitude (GA) section and carry a total of 15 marks. Questions Q.56 - Q.60 carry 1 mark each, and questions Q.61 - Q.65 carry 2 marks each. Unattempted questions will result in zero mark and wrong answers will result in NEGATIVE marks. For all 1 mark questions, 0 mark will be deducted for each wrong answer. For all 2 marks questions, -% mark will be deducted for each wrong answer. However, in the case of the linked answer question pair, there will be negative marks only for wrong answer to the first question and no negative marks for wrong answer to the second question.
9.
10. Calculator is allowed whereas charts, graph sheets or tables are NOT allowed in the examination hall. 11. Rough work can be done on the question paper itself. B lank pages are provided at the end of the question paper for rough work. 12. Before the start of the examination, write your name and.registration below using a black ink ball point pen. Name Registration Number number in the space provided
CS I /_ I ?
I (~..,I -\
I [)
I 1- I '3
C's-c
1/20
2012
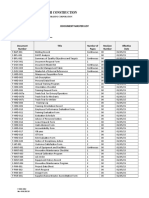
COMPUTER SCIENCE & INFORMATION TECH - CS
Q. 1 - Q. 25 carry one mark each.
Q.l What is the complement of the language accepted Assume 2: = {a} and E is the empty string. by the NFA shown below')
~~a
Y
(C) (B) (D)
a'" {E} {a,E}
~O
all = al2 = all =
Q.2
Let A be the 2 X 2 matrix with elements the matrix A 19 are (A) 1024 and -1024 (C) 4'1/2 and -4'1/2
+ 1 and a22 = -1. Then the eigenvalues
of
(B) 1024'1/2 and -1024'1/2 (D) 512'1/2 and -512'1/2 layer in the Internet (C) Message stack is (D) Frame of the
Q.3
The protocol (A) Segment
data unit (PDU) for the application (B) Datagram
QA
Consider the function f(x) = sin(x) in the interval x E [nI4, 7nI4]. The number and location(s) local minima of this function are (A) (B) (C) (D) One, One, Two, Two, at nl2 at 3n/2 at nl2 and 3n/2 at n/4 and 3nl2
Q.5
A process executes the code forkO; fork(); forkO; The total number of child processes
created
is
(A) 3
Q.6
(8) 4
(C) 7
floating
(D) 8
point representation has
The decimal value 0.5 in IEEE single precision (A) (B) (C) (D) fraction fracti on fraction no exact bits of 000 000 and exponent bits of 000 000 and exponent bits of 100 000 and exponent representation
value of a va Iue of -1 value of a
cs-C
2/20
2012
COMPUTER
SCIENCE & INFORMATION
TECH. -
cs
Q.7
The truth table 1 0 0 1
0 0 1 1 1 1 Y) Y f (X,
represents the Boolean function (A) X Q.8 (B) X + Y (C) X EBY (D) Y
n2n
The worst case running time to search for an element in a balanced binary search tree with elements is (A)
e (n log n)
(B)
e (n2n)
(C)
e (n)
(D)
e (log n)
Q.9
Assuming P '* NP, which of the following is TRUE? (A) NP-complete = NP (C) NP-hard = NP (B) NP-complete n P = 0 (D) P = NP-complete
Q.IO
What will be the output of the following C program segment?
char inChar = 'A' switch ( inChar ) case 'A' : printf case 'B' case 'C' : pri ntf case 'D' case 'E' defaul t : pri ntf
{ ("Choice
A\ n") ;
("Choi ce B")
( " No Choi ce" ) ; }
(A) No Choice (B) Choi ce A (C) Choi ce A
Choice B No Choice
(D) Program gives no output as it is erroneous Q.ll Which of the following is TRUE? (A) Every relation in 3NF is also in BCNF (B)A relation R is in 3NF if every non-prime attribute of R is fully functionally dependent on every key ofR (C) Every relation in BCNF is also in 3NF (D) No relation can be in both BCNF and 3NF Q.12 Consider the following logical inferences. II: If it rains then the cricket match will not be played. The cricket match was played. Inference: There was no rain. 12: If it rains then the cricket match will not be played. It did not rain. Inference: The cricket match was played. Which of the following is TRUE? (A) (B) (C) (D)
CS-C
Both II and 12 are COlTectinferences II is correct but lz is not a correct inference Ii is not correct but lz is a correct inference Both II and 12 are not COlTectinferences
3/20
2012
COMPUTER
SCIENCE & INFORMATION
TECH. -
cs
Q.13
Given the language L = {ab, aa, baa}, which of the following strings are in L*?
1) abaabaaabaa
2) aaaabaaaa 3) baaaaabaaaab 4) baaaaabaa (A) 1,2 and 3 (C) 1,2 and 4 Q.14 Which of the following problems are decidable? 1) Does a given program ever produce an output? 2) If L is a context-free language, then, is 3) If L is a regular language, then, is (B) 1,2 (B) 2, 3 and 4 (D) 1,3 and 4
L also context-free?
L also regular? 4) If L is a recursive language, then, is L also recursive?
(A) 1,2,3,4 Q.15
In
(C) 2,3,4
(D) 3,4
the IPv4 addressing format, the number of networks allowed under Class C addresses is
214
(A) Q.16
Which of the following transport layer protocols is used to support electronic mail? (A) SMTP (B) IP (C) TCP (D) UDP
Q.17
Consider a random variable X that takes values + 1 and -1 with probability 0.5 each. The values of the cumulative distribution function F(x) at x = -1 and + 1 are (A) 0 and 0.5 (B) 0 and 1 (C) 0.5 and 1 (D) 0.25 and 0.75
Q.18
Register renaming is done in pipelined processors (A) (B) (C) (D) as an alternative to register allocation at compile time for efficient access to function parameters and local variables to handle certain kinds of hazards as part of address translation
Q.19
The amount of ROM needed to implement a 4 bit multiplier is (A) 64 bits (B) 128 bits (C) 1 Kbits (D) 2 Kbits
Q.20
Let Wen) and A(n) denote respectively, the worst case and average case running time of an algorithm executed on an input of size n. Which of the following is AL WAYS TRUE? (A) A(n) = (W(n (C) A(n) = 0 (W(n
(B) A(n) = (W(n (D) A(n) = 0 (W(n
Q.21
Let G be a simple undirected planar graph on 10 vertices with 15 edges. If G is a connected graph, then the number of bounded faces in any embedding of G on the plane is equal to (A) 3 (B) 4 (C) 5 (D) 6
CS-C
4/20
2012
COMPUTER
SCIENCE & INFORMATION
TECH. -
cs
Q.22
The recunence relation capturing the optimal execution time of the Towers of Hanoi problem with n discs is (A) T(n) = 2T(n - 2) + 2 (C) T(n) = 2T(n/2) + 1 (B) T(n) = 2T(n - 1) + n (D) T(n) = 2T(n - 1) + 1
Q.23
Which of the following statements are TRUE about an SQL query? P : An SQL query can contain a HAVING clause even if it does not have a GROUP BY clause Q: An SQL query can contain aHA VING clause only if it has a GROUP BY clause R: All attributes used in the GROUP BY clause must appear in the SELECT clause S : Not all attributes used in the GROUP BY clause need to appear in the SELECT clause (A) P and R (B) P and S (C) Q and R (D) Q and S
Q.24
Given the basic ER and relational models, which of the following is INCORRECT? (A) An attribute of an entity can have more than one value (B) An attribute of an entity can be composite (C) In a row of a relational table, an attribute can have more than one value (D) In a row of a relational table, an attribute can have exactly one value or a NULL value
Q.25
What is the conect translation of the following statement into mathematical logic? "Some real numbers are rational" (A) ::Ix(real(x) v rational(x (B) \;fx (real(x) ~ rational(x (C) ::Ix(real(x) /\ rational(x (D) ::Ix(rational(x) ~ real(x
CS-c
5/20
2012
COMPUTER
SCIENCE
& INFORMATION
TECH. - CS
Q. 26 to Q. 55 carry two marks each.
Q.26 Consider the program given below, in a block-structured pseudo-language nesting of procedures permitted.
Program main; Var ... Procedure Al; Var ... Call A2; End Al Procedure A2; Var ... Procedure A21; Var ... Call Al; End A21 Call A21; End A2 Call Al; End main.
with lexical scoping and
Consider the calling chain: Main -7 Al -7 A2 -7 A21 -7 Al The correct set of activation records along with their access links is given by
(A)
(B)
FRAME POINTER
ACCESS LINKS
FRAME POINTER
ACCESS LINKS
(C)
(D)
FRAME POINTER
ACCESS LINKS FRAME POINTER ACCESS LINKS
CS-c
6/20
2012
COMPUTER
SCIENCE
& lNFORMA
TION TECH. -
cs
Q.27
Suppose a circular queue of capacity (n -1) elements is implemented with an array of n elements. Assume that the insertion and deletion operations are carried out using REAR and FRONT as aITay index variables, respectively. Initially, REAR = FRONT = O. The conditions to detect queue full and queue empty are (A) full: (REAR+l) mod n == FRONT empty: REAR == FRONT (C)full: REAR == FRONT empty: (REAR+l) mod n == FRONT (B) full: (REAR+1) mod n == FRONT empty: (FRONT + 1) mod n == REAR (D) full: (FRONT+l) mod n == REAR empty: REAR == FRONT
Q.28
An Internet Service Provider (ISP) has the following chunk of CIDR-based IP addresses available with it: 245.248.128.0/20. The ISP wants to give half of this chunk of addresses to Organization A, and a quarter to Organization B, while retaining the remaining with itself. Which of the following is a valid allocation of addresses to A and B? (A) (B) (C) (D) 245.248.136.0/21 and 245.248.128.0/22 245.248.128.0/21 and 245.248.128.0/22 245.248.132.0/22 and 245.248.132.0/21 245.248.136.0/24 and 245.248.132.0/21
Q.29
Suppose a fair six-sided die is rolled once. If the value on the die is 1, 2, or 3, the die is rolled a second time. What is the probability that the sum total of values that turn up is at least 6? (A) 10/21 (B) 5/12
(C) 2/3
(D) 1/6
Q.30
Fetch~nd~dd (X, i) is an atomic Read-Modify-Write instruction that reads the value of memory location X, increments it by the value i, and returns the old value of X. It is used in the pseudocode shown below to implement a busy-wait lock. L is an unsigned integer shared variable initialized to O. The value of 0 cOITesponds to lock being available, while any non-zero value cOITesponds to the lock being not available. AcquireLock(L){ while (Fetch~nd~dd(L,l))
L = 1;
}
ReleaseLock(L){ L = 0;
}
(A) (B) (C) (D)
This implementation fails as L can overflow fails as L can take on a non-zero value when the lock is actually available works correctly but may starve some processes works cOITectly without starvation
CS-C
7120
2012
COMPUTER
SCIENCE & INFORMATION
TECH. -
cs
Q.31
Consider the 3.processes, PI, P2 and P3 shown in the table. Process PI P3 P2 time 4 17 3 5 0 Arrival Time Units Required
The completion order of the 3 processes under the policies FCFS and RR2 (round robin scheduling with CPU quantum of 2 time units) are (A) FCFS: PI, P2, P3 RR2: PI, P2, P3 (C) FCFS: PI, P2, P3 RR2: PI, P3, P2 (B) FCFS: PI, P3, P2 RR2: PI, P3, P2 (D) FCFS: PI, P3, P2 RR2: PI, P2, P3
Q.32
What is the minimal form of the Karnaugh map shown below? Assume that X denotes a don't care term. --00 ab 1 (C) 1 X 1 01 10 11 X 1 bd+abed (D) bd+be+ed (B) bd+ be II X
-I
Cd"-
--
I~
-- --
10
Q.33
Let G be a weighted graph with edge weights greater than one and G/ be the graph constructed by squaring the weights of edges in G. Let T and T' be the minimum spanning trees of G and G/, respectively, with total weights t and t/. Which of the following statements is TRUE? (A) T' = T with total weight t/ = t2 (B) T' = T with total weight t/ < e (C) T' =I T but total weight t/ = t2 (D) None of the above
Q.34
The bisection method is applied to compute a zero of the function f{x} = interval [1,9]. The method converges to a solution after __ iterations. (A) 1 (B) 3 (C) 5
x4
x3
x2
4 in the
(D) 7
CS-C
8/20
2012
COMPUTER
SClENCE & INFORMATION
TECH. -
cs
Q.35
Which of the following graphs is isomorphic to
(A)
(B)
(C)
(D)
Q.36
Consider the following transactions with data items P and Q initialized to zero: Tl :read CP);
read CQ); if P = 0 then Q write CQ).
T2:
read CQ); read CP); if Q = 0 then P wri te CP).
P + 1
Any non-serial interleaving of T 1 and T 2 for concurrent execution leads to (A) (B) (C) (D) a serializable schedule a schedule that is not conflictserializable a conflict serializable schedule a schedule for which a precedence graph cannot be drawn
cs-c
9/20
20]2
COMPUTER
SCIENCE & INFORMAT]ON
TECH. -
cs
Q.37
Consider the set of strings on {O,I} in which, every substring of 3 symbols has at most two zeros. For example, 001110 and 011 00 1 are in the language, but 100010 is not. All strings of length less than 3 are also in the language. A partially completed DFA that accepts this language is shown below.
0, 1
The missing arcs in the DF A are
(A)
00 1 10 11 0 0 01 Q 01
(B) 0
01 00
00 10 01 11 Q
0 1
11
11
10
(C)
00 11 10 01 Q 10
(D)
0 1 00
00 01 10 00 11 10 01 0 Q
00
11
CS-C
]0/20
2012
COMPUTER
SCIENCE & INFORMATION
TECH. -
cs
Q.38
The height of a tree is defined as the number of edges on the longest path in the tree. The function shown in the pseudocode below is invoked as heightCroot) to compute the height of a binary tree rooted at the tree pointer root. int height Ctreeptr n) -1; { if Cn == NULL) return if Cn 7 left == NULL) if Cn 7 right == NULL) return else else return ~ ; C1+hl);
0;
II II
B2 are
Box 1
{ hI = height Cn 7 left); if Cn 7 right == NULL) return else { h2 = height Cn 7 right);
return
Box 2
The appropriate expressions for the two boxes Bland (A) B 1: (1+height(n -) right)) B2: (1+max(h1, h2)) (C) B 1: heighten -) right) B2: max(h1, h2) Q.39
(B) B 1: (height(n -) right)) B2: (1+max(h1,h2)) (D) B1: (1+ heighten -) right)) B2: max(h1, h2)
Consider an instance of TCP's Additive Increase Multiplicative Decrease (AIMD) algorithm where the window size at the start of the slow start phase is 2 MSS and the threshold at the start of the first transmission is 8 MSS. Assume that a timeout occurs during the fifth transmission. Find the congestion window size at the end of the tenth transmission. (A) 8 MSS (B) 14 MSS (C) 7 MSS (D) 12 MSS
QAO
Consider a source computer (S) transmitting a file of size 106 bits to a destination computer (D) over a network of two routers (Rj and Rz) and three links (Ll. Lz, and L3). Ll connects S to RI; Lz connects Rl to Rz; and L3 connects Rz to D. Let each link be of length 100 km. Assume signals travel over each link at a speed of 108 meters per second. Assume that the link bandwidth on each link is 1Mbps. Let the file be broken down into 1000 packets each of size 1000 bits. Find the total sum of transmission and propagation delays in transmitting the file from S to D? (A) 1005 ms (B) 1010 ms (C) 3000 ms (D) 3003 ms
QA1
Suppose RI(A, B) and Ri.G, D) are two relation schemas. Let rj and rz be the corresponding relation instances. B is a foreign key that refers to C in Rz. If data in rj and rz satisfy referential integrity constraints, which of the following is ALWAYS TRUE? (A) (B) (C) (D) fh(rj) - TIcCrz)= TIcCrz)- TIB(rj) = TIB(rl) = TIcCrz) TIB(rj) - TIcCrz)"*
0 0 0
CS-C
11/20
2012
COMPUTER
SCIENCE & INFORMATION
TECH. - CS
Q.42
Consider the virtual page reference string 1, 2, 3, 2, 4, 1, 3, 2, 4, 1 on a demand paged virtual memory system running on a computer system that has main memory size of 3 page frames which are initially empty. Let LRU, FIFO and OPTIMAL denote the number of page faults under the corresponding page replacement policy. Then (A) OPTIMAL < LRU < FIFO (C) OPTIMAL = LRU (B) OPTIMAL < FIFO < LRU (D) OPTIMAL = FIFO
Q.43
A file system with 300 GByte disk uses a file descriptor with 8 direct block addresses, 1 indirect block address and 1 doubly indirect block address. The size of each disk block is 128 Bytes and the size of each disk block address is 8 Bytes. The maximum possible file size in this file system is (A) (B) (C) (D) 3 KBytes 35 KBytes 280 KBytes dependent on the size of the disk
Q.44
Consider the directed graph shown in the figure below. There are multiple shortest paths between vertices Sand T. Which one will be reported by Dijkstra' s shortest path algorithm? Assume that, in any iteration, the shortest path to a vertex v is updated only when a strictly shorter path to v is discovered.
s
T
(A) SDT Q.45
(B) SBDT
(C) SACDT
(D) SACET order using the merge-sort
A list of n strings, each of length n, is sorted into lexicographic algorithm. The worst case running time of this computation is (A)
0 (n log n)
(B) 0
(n210g n)
(C)
0 (n2 + log n)
Q.46
Let G be a complete undirected graph on 6 vertices. If vertices of G are labeled, then the number of distinct cycles of length 4 in G is equal to (A) 15 (B) 30 (C) 90 (D) 360
(n;:::
Q.47
How many onto (or surjective) functions are there from an n-element (A) 2" (C) 2" - 2
2) set to a 2-element set?
(D) 2(2" - 2)
CS-C
2/20
2012
COMPUTER
SCIENCE & [NFORMATION
TECH. - CS
Common Data Questions
Common Data for Questions 48 and 49: Consider the following relations A, Band C: A Arun 24 Rohit Name 60 11 Age Shreya 15 25 99 98
B
Id Name Hari Rohit 20 11 24 40 Age Shreya 99 10 Id
C
01 Area Phone 2100 2200 02
Id
Q.48
How many tuples does the result of the following relational algebra expression contain? Assume that the schema of AuB is the same as that of A (AuB) (A) 7
t><l
A.ld>40
vC.ld < 15
C (C) 5 (D) 9
(B) 4
Q.49
How many tuples does the result of the following SQL query contain? SELECT AId
FROM A
WHERE AAge
> ALL (SELECT RAge
FROMB WHERE B.Name = 'Arun')
(A) 4
(B) 3
(C) 0
(D) 1
cs-C
[3120
2012
COMPUTER
SCIENCE
& INFORMATION
TECH. - CS
Common Data for Questions 50 and 51: Consider the following C code segment.
int static Line a, b, 2 int '''I a %d = 1; 2; ", a, b); = 0; 1c "I ++b; prtFun(void); ma in ( ) { a prtFun( += 1; ); printf(" \n %d %d void prtFun(void)
..
j'" I'"
}
Q.50 What output will be generated by the given code segment?
d by
2 4 1 1 3 4 6 2 5 0 2 6 6 2 1 2 auto int a = 1; (B) (C) register (D) int = given 2; What output will be generated bya the code segment if: (A) Line 1 is replaced by
CS-C
14/20
2012
COMPUTER
SCIENCE & INFORMATION
TECH. - CS
Linked Answer Questions
Statement for Linked Answer Questions 52 and 53:
For the grammar below, a partial LL(1) parsing table is also presented along with the grammar. Entries that need to be filled are indicated as El, E2, and E3. E is the empty string, $ indicates end of input, and, I separates alternate right hand sides of productions. S-7aAbB A-7S B-7S
I
bAaB
IE
b a B-7S El E2 B-7S E3 A-7S A-7S S-7E $error
Q.52
The FIRST and FOLLOW sets for the non-terminals A and Bare (A) FIRST(A) = {a, b, E} = FIRST(B) FOLLOW(A) = {a, b} FOLLOW(B) = {a, b, $} (B) FIRST(A) = {a, b, $} FIRST(B) = {a, b, E} FOLLOW(A) = {a, b} FOLLOW(B) = {$} (D) FIRST(A) = {a, b} = FIRST(B) FOLLOW(A) = {a, b} FOLLOW(B) = {a, b}
(C) FIRST(A) = {a, b, E} = FIRST(B) FOLLOW(A) = {a, b} FOLLOW(B) =
Q.53
The appropriate entries for El, E2, and E3 are (A) El: S -7 aAbB, A -7 S E2: S -7 bAaB, B -7 S E3: B -7 S (C) El: S -7 aAbB, S -7 E E2: S -7 bAaB, S -7 E E3: B -7 S (B) El: S -7 aAbB, S -7 E E2: S -7 bAaB, S -7 E E3: S -7 E
(D) El: A -7 S, S -7
E2: B -7 S, S -7 E3: B -7 S
E E
Statement
for Linked Answer Questions 54 and 55:
A computer has a 256 KByte, 4-way set associative, write back data cache with block size of 32 Bytes. The processor sends 32 bit addresses to the cache controller. Each cache tag directory entry contains, in addition to address tag, 2 valid bits, 1 modified bit and 1 replacement bit. Q.54 The number of bits in the tag field of an address is
(A) 11
(B) 14
(C) 16
(D) 27
Q.55
The size of the cache tag directory is (A) 160 Kbits (B) 136 Kbits (C) 40 Kbits (D) 32 Kbits
CS-C
15/20
2012
COMPUTER
SCIENCE & INFORMATION
TECH. - CS
General Aptitude (GA) Questions Q. 56 - Q. 60 carry one mark each.
Q.56 Which one of the following options is the closest in meaning to the word given below? Mitigate (A) Diminish Q.57 (B) Divulge (C) Dedicate (D) Denote
Choose the grammatically INCORRECT sentence: (A) They gave us the money back less the service charges of Three Hundred rupees. (B) This country's expenditure is not less than that of Bangladesh. (C) The committee initially asked for a funding of Fifty Lakh rupees, but later settled for a lesser sum. (D) This country's expenditure on educational reforms is very less.
Q.58
Choose the most appropriate alternative from the options given below to complete the following sentence: Suresh's dog is the one (A) that (B) which
was hurt in the stampede.
(C) who
(D) whom
Q.59
The cost function for a product in a firm is given by where q is the amount of production. The firm can sell the product at a market price of 50 per unit. The number of units to be produced by the firm such that the profit is maximized is
sl,
(A) 5 Q.60
(B) 10
(C) 15
(D) 25
Choose the most appropriate alternative from the options given below to complete the following sentence: Despite several (A) attempts the mission succeeded in its attempt to resolve the conflict. (B) setbacks (C) meetings (D) delegations
Q. 61 - Q. 65 carry two marks each.
Q.61 An automobile plant contracted to buy shock absorbers from two suppliers X and Y. X supplies 60% and Y supplies 40% of the shock absorbers. All shock absorbers are subjected to a quality test. The ones that pass the quality test are considered reliable. Of X' s shock absorbers, 96% are reliable. Of Y' s shock absorbers, 72% are reliable. The probability that a randomly chosen shock absorber, which is found to be reliable, is made by Y
IS
(A) 0.288
(B) 0.334
(C) 0.667
(D) 0.720
CS-C
16/20
2012
COMPUTER
SCiENCE & INFORMATION
TECH. - CS
Q.62
Which of the following assertions are CORRECT? P: Adding 7 to each entry in a list adds 7 to the mean of the list Q: Adding 7 to each entry in a list adds 7 to the standard deviation of the list R: Doubling each entry in a list doubles the mean of the list S: Doubling each entry in a list leaves the standard deviation of the list unchanged (A) P, Q (B) Q, R
(C) P, R
(D) R, S
Q.63
Given the sequence of terms, AD CG FK JP, the next term is (A) OV (B) OW (C) PV (D) PW
Q.64 Wanted Temporary, Part-time persons for the post of Field Interviewer to conduct personal interviews to collect and collate economic data. Requirements: High School-pass, must be available for Day, Evening and Saturday work. Transportation paid, expenses reimbursed.
Which one of the following is the best inference from the above advertisement? (A) (B) (C) (D) Q.65 Gender-discriminatory Xenophobic Not designed to make the post attractive Not gender-discriminatory
A political party orders an arch for the entrance to the ground in which the annual convention is being held. The profile of the arch follows the equation y = 2x - O.]x2 where y is the height of the arch in meters. The maximum possible height of the arch is (A) 8 meters (B) 10 meters (C) 12 meters (D) 14 meters
END OF THE QUESTION PAPER
CS-C
17/20
Das könnte Ihnen auch gefallen
- Simple LCM Logic in CDokument1 SeiteSimple LCM Logic in ClaxitkumarNoch keine Bewertungen
- Simple Start Java From Command LineDokument1 SeiteSimple Start Java From Command LinelaxitkumarNoch keine Bewertungen
- Read File in JavaDokument1 SeiteRead File in JavalaxitkumarNoch keine Bewertungen
- Read File in JavaDokument1 SeiteRead File in JavalaxitkumarNoch keine Bewertungen
- How To Start Java From Command PromptDokument1 SeiteHow To Start Java From Command PromptlaxitkumarNoch keine Bewertungen
- Simple Frame Demo in JavaDokument2 SeitenSimple Frame Demo in JavalaxitkumarNoch keine Bewertungen
- Use of This Keyword in JavaDokument1 SeiteUse of This Keyword in JavalaxitkumarNoch keine Bewertungen
- Multiplication of Two Big IntegersDokument1 SeiteMultiplication of Two Big IntegerslaxitkumarNoch keine Bewertungen
- Add2Numbers - TXT in JavaDokument1 SeiteAdd2Numbers - TXT in JavalaxitkumarNoch keine Bewertungen
- Ambient BackscatterDokument2 SeitenAmbient BackscatterlaxitkumarNoch keine Bewertungen
- Expt Matlab Convolution and CorrelationDokument2 SeitenExpt Matlab Convolution and CorrelationlaxitkumarNoch keine Bewertungen
- Multiplication of Two Big IntegersDokument1 SeiteMultiplication of Two Big IntegerslaxitkumarNoch keine Bewertungen
- Conv MatlabDokument1 SeiteConv MatlablaxitkumarNoch keine Bewertungen
- Conv MatlabDokument1 SeiteConv MatlablaxitkumarNoch keine Bewertungen
- Insertion SortDokument1 SeiteInsertion SortlaxitkumarNoch keine Bewertungen
- Conv MatlabDokument1 SeiteConv MatlablaxitkumarNoch keine Bewertungen
- Bresenham Line Drawing ProgramDokument2 SeitenBresenham Line Drawing ProgramlaxitkumarNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Programmers PDFDokument5 SeitenProgrammers PDFSrinivasan SridharanNoch keine Bewertungen
- US - Osnove JAVA Programiranja - Zbirka PDFDokument320 SeitenUS - Osnove JAVA Programiranja - Zbirka PDFssteticNoch keine Bewertungen
- CounterACT Console User Manual 7.0.0 PDFDokument763 SeitenCounterACT Console User Manual 7.0.0 PDFlazarusNoch keine Bewertungen
- Cse Viii Advanced Computer Architectures 06CS81 Notes PDFDokument156 SeitenCse Viii Advanced Computer Architectures 06CS81 Notes PDFHarshith HarshiNoch keine Bewertungen
- Browser Automation - IMacrosDokument10 SeitenBrowser Automation - IMacrosAnshumandutta100% (1)
- Sepa Credit Transfer Pain 001 001 03 XML File Structure July 2013Dokument28 SeitenSepa Credit Transfer Pain 001 001 03 XML File Structure July 2013Francisco XascasNoch keine Bewertungen
- Dte - AitDokument44 SeitenDte - AitMuvvala Santosh KumarNoch keine Bewertungen
- Auto LispDokument22 SeitenAuto LispWin ThanNoch keine Bewertungen
- WSGI Werkzeug and The Challenges of Building A Python Web FrameworkDokument22 SeitenWSGI Werkzeug and The Challenges of Building A Python Web FrameworkIgor Guerrero FonsecaNoch keine Bewertungen
- Powerful FSL Tools for Brain Imaging AnalysisDokument38 SeitenPowerful FSL Tools for Brain Imaging AnalysissiolagNoch keine Bewertungen
- Logic in Computer Science: BITS PilaniDokument11 SeitenLogic in Computer Science: BITS PilaniPranjal GuptaNoch keine Bewertungen
- Differential Equations With Boundary Value Problems SolutionsDokument9 SeitenDifferential Equations With Boundary Value Problems SolutionsAbdu Abdoulaye67% (6)
- 01 Document MasterlistDokument3 Seiten01 Document MasterlistHorhe SmithNoch keine Bewertungen
- Spooky2 User's Guide 20170204 PDFDokument228 SeitenSpooky2 User's Guide 20170204 PDFAndi OlivierNoch keine Bewertungen
- L6 Systems of InequalitiesDokument25 SeitenL6 Systems of InequalitiesFlorence FlorendoNoch keine Bewertungen
- News Portal Project ReportDokument34 SeitenNews Portal Project ReportAbkash Khatua83% (12)
- Managing Government Records Module 1 Benefits ARCS ORCSDokument4 SeitenManaging Government Records Module 1 Benefits ARCS ORCSAndrea ManaloNoch keine Bewertungen
- Game Development Using BuildboxDokument2 SeitenGame Development Using BuildboxGm SudheerNoch keine Bewertungen
- Experian Dispute FormDokument1 SeiteExperian Dispute Formmainester100% (3)
- IPF NextLifter InstructionsDokument25 SeitenIPF NextLifter Instructionsema94mayNoch keine Bewertungen
- Ami Bios Beep CodesDokument10 SeitenAmi Bios Beep CodestaingashuNoch keine Bewertungen
- PPL 2017 Aktu PaperDokument2 SeitenPPL 2017 Aktu PaperShivanand PalNoch keine Bewertungen
- DAS 3224 ManualDokument67 SeitenDAS 3224 ManualyencalseNoch keine Bewertungen
- C++ Lab MaualDokument89 SeitenC++ Lab MaualRajat KumarNoch keine Bewertungen
- MS HandoutDokument3 SeitenMS HandoutJayant JawanjalNoch keine Bewertungen
- Noa MopDokument103 SeitenNoa MopRaja SolaimalaiNoch keine Bewertungen
- CFX Intro 16.0 App-A ScriptingDokument53 SeitenCFX Intro 16.0 App-A ScriptingJorge Luis Ramos Cuipa100% (2)
- Information Resources Information Systems: Management Information Systems 8/E Raymond Mcleod, Jr. and George SchellDokument34 SeitenInformation Resources Information Systems: Management Information Systems 8/E Raymond Mcleod, Jr. and George SchellAbdul LatifNoch keine Bewertungen
- MembacaDokument13 SeitenMembacaKurniawatiNoch keine Bewertungen
- Huawei CommandsDokument2 SeitenHuawei CommandsRade Pralica100% (1)