Beruflich Dokumente
Kultur Dokumente
Lecture 1: Models of Distributed Systems
Hochgeladen von
Vikas ThadaOriginalbeschreibung:
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Lecture 1: Models of Distributed Systems
Hochgeladen von
Vikas ThadaCopyright:
Verfügbare Formate
Distributed Architectures
Lecture 1 : Models of Distributed Systems
Distributed Architectures
Examples of Distributed Systems
Most popular is the Internet, which is used for applications such as WWW, E-Mail, FTP, and Telnet Intranets
calendars, etc.
May be connected to the Internet, or could be closed, or disconnected. Applications include enterprise human resource portals, collaboration, Laptops, PDAs/Handhelds, wearable devices, embedded devices National Oceanic Atmospheric Association (NOAA) uses Linux cluster for
weather mapping applications Search for Extraterrestrial Intelligence Institute (SETI) leverages unused processing power of your home PC to process data collected from space to locate alien life forms
Mobile Computing Networks Computing Clusters
2005 Thom Anderson
Distributed Architectures
Consequences of Distributed Systems Concurrency p and q are concurrent if either p can happen before q, or q can happen before p, thus having interleaving semantics
Language Parallel: Threads in the BEGIN_PARALLEL and END_PARALLEL block
begin at the same time x=1 y=2 BEGIN_PARALLEL x=x+y print x END_PARALLEL What is the result of this code? What system properties can alter the result of this code? When the completion p and q is unpredictable, this is known as a race condition Synchronization and Coordination are handled by passing messages Potential problems are deadlocks and starvation
2005 Thom Anderson
Distributed Architectures
Consequences of DS (Continued)
No global clock, no global state Not possible to synchronize many computers on a network and guarantee synchronization over time, thus events are logically ordered. Not possible to have a process that can be aware of a single global state. Independent Failures Running processes may be unaware of other failures within context Failed processes may go undetected Both are due to processes running in isolation
2005 Thom Anderson
Distributed Architectures
Reasons for DS
Resource Sharing Hardware Distributing CPU power Sharing storage drives Sharing printers Network Sharing home DSL line across multiple computers Computers on a MAN sharing an OC-48 to connect to a WAN Software Sharing a database server with multiple client applications File Sharing Video and Audio Video On Demand (VOD) Digital Telephony and Voice Mail
2005 Thom Anderson 5
Distributed Architectures
Reasons for DS (continued)
Functional Distribution Separating clients from servers Web browsers from web servers Web servers from database servers Load Distribution Load balancing clusters Physical Separation Connecting multiple locations of an enterprise to single data points Distributing a web infrastructure across multiple WAN segments for improved reliability Economics Leveraging many cheaper systems provides better price to performance rather than buying large mainframes Linux Beowulf Cluster vs. Super Computer
2005 Thom Anderson 6
Distributed Architectures
Design Challenges Heterogeneity of Resources Networks (AppleTalk, Token Ring, Ethernet, etc.) Hardware (RISC vs, CISC) Example: if you compile a C++ program for Solaris Intel-based, it is not portable for Solaris SPARC-based OS (UNIX and its many flavors, Windows, Linux, BEOS, etc.) IPC issues File sharing issues Printer sharing issues Programming Languages (Java, C/C++/C#, Perl, Python, LISP, etc.) Implementation Strategies Integrating a .NET application to a J2EE application can pose its difficulties Integrating a WebSphere based J2EE application to an iPlanet based J2EE application can also pose difficulties!
2005 Thom Anderson
Distributed Architectures
Challenges (continued) Openness Published Applications Programming Interface (API) Standards Compliance Security Types Confidentiality Integrity Availability Non-Repudiation, prevalent in commerce applications Authentication and Authorization Scalability Physical resources Performance Prevent resource loss Bottlenecks Domain Name Server (DNS) example (see textbook) Caching/Replication
2005 Thom Anderson
Distributed Architectures
Challenges (continued) Failure Handling Detection e.g. checksums Some errors are undetectable, such as in the case of Asynchronous messages Masking failures Retransmission Striping Tolerance by means of meaningful action Transaction rollbacks Redundancy Multiple pathways DNS example Database replication Web clustering Linux Beowulf cluster
2005 Thom Anderson
Distributed Architectures
Challenges (continued) Concurrency Session management Resource management Locking Transparency Hiding it all from the users ISOs Reference Model for Open Distributed Processing identifies the following 8 forms of transparency Access (remote and local access are the same) Location (dont care about where resources are) Concurrency (share resources fairly) Replication (dont care which replicated resource is being used) Failure (hide faults from applications and users) Mobility (move resources without affecting users) Performance (adapt to load changes) Scaling (expand capability, leave logic alone)
2005 Thom Anderson
10
Distributed Architectures
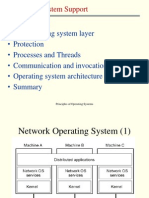
Architectural Models Paradigms Layers Client Server Software Layers Breaking up the complexity of systems by designing them through layers and services layer: group of closely related and highly coherent functionalities service: functionality provided to a superior layer Examples of layered architectures Operating systems (kernel, drivers, windows, processes) Computer Network Protocols
2005 Thom Anderson
11
Distributed Architectures
Architectural Models (continued) Software Layers (continued) Platform combines hardware with operating system Windows/CISC (Intel) Solaris/RISC (Sparc) Solaris/CISC (Intel) Middleware Goal: To achieve communication and resource sharing For example, by remote method invocation Examples of Middleware CORBA, by OMG DCOM, by Microsoft Java RMI, by Sun
2005 Thom Anderson
12
Distributed Architectures
Architectural Models (continued) System Architecture Client Server Model and Variations Server is a process; Client is a process Clients invoke servers, servers send results to clients Servers can be clients of other Servers HTTP (Web) Server is a server process to its client processes (web browsers) HTTP Server may be a client of a database server Service may be provided by multiple servers, as is most often the case within a large enterprise Cache is a repository of recently accessed objects (files, graphics) that is physically closer to the client than the server from which it originated Proxy server sits in between clients and servers and can play many mitigation roles Maintain cache Firewall Restrict site access
2005 Thom Anderson
13
Distributed Architectures
Architectural models (continued) System Architecture (continued) Client Server Model and Variations (continued) Java Applets Mobile Agents Thin Clients Network Computers Web Browsers Mobile device discovery Peer to Peer Services Do not require a server process More interesting architecture than client/server over the Internet
2005 Thom Anderson
14
Distributed Architectures
Architectural Models (continued) Objects and Interfaces The concept of a contract or stub (Interface definition) Separation of Interface from Implementation Review of Objects, Classes, Interfaces, and Implementations Object is the cookie, Class is the cookie-cutter 3 Properties of Object Oriented Programming Inheritance Polymorphism Data Encapsulation Interfaces are only stubs or contracts No actual coded logic, Provides method signatures only Implementations code interface logic Interfaces defer actual work to the implementation Adapter Pattern: It is not necessary to implement every method of an interface Abstract Classes Can implement certain methods, and defer functionality to subclasses
2005 Thom Anderson
15
Distributed Architectures
Architectural Models (continued) Design Requirements Performance Responsiveness is the speed and consistency of a servers or a services response to its clients Throughput is computational speed in general, and computational speed over software layers in the server and client in specific Quality of Service (QoS) Reliability maps to the failure model (2.3.2) Security maps to the security model (2.3.3) Performance maps to interaction model (2.3.1) Adaptability: Mothers Day example Dependability Fault tolerance measures the probability of a system to function in the presence of software, hardware, and network failure Security requirements vary greatly the DoD emphasizes confidentiality and integrity, whereas amazon.com emphasize availability and nonrepudiation
2005 Thom Anderson
16
Distributed Architectures
Fundamental Models Interaction Model Distributed System Multiple processes Communication channels Distributed Algorithm Steps to be taken by each process Communication between processes Synchronization Data flow Communication Channel Performance Characteristics Latency is the delay between sending and receiving a message Bandwidth is the amount of information transmitted over time Jitter is the variation in the time taken to deliver messages Video frames in an ATM network
2005 Thom Anderson
17
Distributed Architectures
Fundamental Models (continued) Interaction Model (continued) Clocks Each computer has a clock Clock drift rate makes it impossible to synchronize without communication Synchronous DS time to execute each step of computation within a process has known lower and upper bounds message delivery times are bounded to a known value each process has a clock whose drift rate from real time is bounded by a known value Easy to handle, hard to find bounds Asynchronous DS exhibit no bounds on Process execution speeds Message transmission delay Clock drift rates Internet is asynchronous QoS requirements can be heavily affected
2005 Thom Anderson 18
Distributed Architectures
Fundamental Models (continued) Interaction Model (continued) Event ordering provides a synchronization model We will come back to this later Failure Model Omission Failures Process Omission Failures Process has crashed Can be detected using timeouts Fail-stop process crash is one that can be detected with certainty by other processes Guaranteed message delivery example Communication Omission Failures Message is not being delivered Network error or outage Overflow in the incoming message buffer
2005 Thom Anderson 19
Distributed Architectures
Failure Model (continued) Arbitrary Failures (Byzantine failures) Worst case scenario Process Arbitrary Failure Arbitrary omission or execution of steps Channel Arbitrary Failure Non-delivery, corruption, or duplication of a message Timing Failures Process Timing Failure Synchronous DS Processs local clock drifts beyond bounds (Clock failure) Process exceeds interval bound between sequential steps (Performance) Channel Timing Failure Message transmission takes longer than bound (Performance)
2005 Thom Anderson
20
Distributed Architectures
Security Model Protect access to object Authentication (username/password) Kerberos example Authorization (Access Control Lists ACLs) Protecting messages and interactions Authenticated messages Secure channels Countermeasures Firewalls IP Filtering Network Address Translation (NAT) Cryptography Sharing a secret key Public Key Infrastructure Secure Channel Secure Socket Layers Virtual Private Networks
2005 Thom Anderson
21
Das könnte Ihnen auch gefallen
- CS542: Topics in Distributed SystemsDokument39 SeitenCS542: Topics in Distributed SystemsyekoyesewNoch keine Bewertungen
- Distributed Systems Concepts and Design Chapter 12Dokument44 SeitenDistributed Systems Concepts and Design Chapter 12Samiksha MishraNoch keine Bewertungen
- Intro To DS Chapter 1Dokument56 SeitenIntro To DS Chapter 1Habib MuhammedNoch keine Bewertungen
- Distributed CS571Dokument36 SeitenDistributed CS571ajassuhail9Noch keine Bewertungen
- IEC 312 - Distributed System SecurityDokument22 SeitenIEC 312 - Distributed System SecurityBhanu NaikNoch keine Bewertungen
- DS Syllabus Introduction (Reference)Dokument44 SeitenDS Syllabus Introduction (Reference)Joel ShibbiNoch keine Bewertungen
- CS4513 Distributed Computer SystemsDokument23 SeitenCS4513 Distributed Computer SystemsShahnaz ShakirNoch keine Bewertungen
- CS4513 Distributed Computer SystemsDokument32 SeitenCS4513 Distributed Computer Systemsashish_vksiNoch keine Bewertungen
- RMCSDokument127 SeitenRMCSAmita Rathee DahiyaNoch keine Bewertungen
- Characterization of Distributed Systems (Chapter-1)Dokument35 SeitenCharacterization of Distributed Systems (Chapter-1)Melvin JacobNoch keine Bewertungen
- 01 - Ch1Dokument25 Seiten01 - Ch1OmarallasasmhNoch keine Bewertungen
- Introduction To Distributed SystemsDokument36 SeitenIntroduction To Distributed SystemsNavindu AmerasingheNoch keine Bewertungen
- Distributed Systems Conclusions & Exam: Brian Nielsen Bnielsen@cs - Aau.dkDokument18 SeitenDistributed Systems Conclusions & Exam: Brian Nielsen Bnielsen@cs - Aau.dkSalar AhmedNoch keine Bewertungen
- Distributed Operating SystemsDokument54 SeitenDistributed Operating Systemsbeti_1531Noch keine Bewertungen
- Lecture 1 Introduction To Distributed Systems - 034922Dokument6 SeitenLecture 1 Introduction To Distributed Systems - 034922leonardkigen100Noch keine Bewertungen
- IntroDokument32 SeitenIntroAnita Sofia KeyserNoch keine Bewertungen
- Introduction: Operating System SupportDokument63 SeitenIntroduction: Operating System SupportErmercado78Noch keine Bewertungen
- Distributed SystemsDokument68 SeitenDistributed SystemsUtkarshMalikNoch keine Bewertungen
- Course Name-Operating System Course Code-COM-302 Topic - Real Time Operating System Date - 02/11/2021Dokument26 SeitenCourse Name-Operating System Course Code-COM-302 Topic - Real Time Operating System Date - 02/11/2021Gulshan SharmaNoch keine Bewertungen
- DCS IntroDokument28 SeitenDCS IntroRohan DesaiNoch keine Bewertungen
- Distributed Systems: Chapter 1 - IntroductionDokument74 SeitenDistributed Systems: Chapter 1 - IntroductionAbe Marera100% (2)
- Characterization of Distributed SystemsDokument43 SeitenCharacterization of Distributed Systemspatrick7593Noch keine Bewertungen
- Advanced Distributed SystemsDokument15 SeitenAdvanced Distributed Systemsshashank_w85m_312965100% (1)
- PDS Unit 1Dokument59 SeitenPDS Unit 1DineshNoch keine Bewertungen
- Distributed Systems: Tanenbaum Chapter 1Dokument70 SeitenDistributed Systems: Tanenbaum Chapter 1Kassawmar AyalewNoch keine Bewertungen
- IFA - 307 - Introduction To Distributed Computing - Lec2Dokument19 SeitenIFA - 307 - Introduction To Distributed Computing - Lec2Fikri HaekalNoch keine Bewertungen
- OSI ModelDokument33 SeitenOSI Modelsangeetaratan19894026100% (5)
- Distributed Systems Principles and Paradigms IntroductionDokument31 SeitenDistributed Systems Principles and Paradigms IntroductiondinkaNoch keine Bewertungen
- Course Name-Operating System Course Code-COM-302 Topic - Types of Operating SystemDokument20 SeitenCourse Name-Operating System Course Code-COM-302 Topic - Types of Operating SystemGulshan SharmaNoch keine Bewertungen
- Distributed Systems: - CSE 380 - Lecture Note 13 - Insup LeeDokument24 SeitenDistributed Systems: - CSE 380 - Lecture Note 13 - Insup LeeApoorv JoshiNoch keine Bewertungen
- Practical Issues in The Development of Secure Distributed SystemsDokument31 SeitenPractical Issues in The Development of Secure Distributed SystemscarabusuNoch keine Bewertungen
- Des Tribute DDokument8 SeitenDes Tribute DAmr El GhamrawyNoch keine Bewertungen
- LecturesDokument223 SeitenLecturestruong nguyenNoch keine Bewertungen
- 2 Dist Arch (Week 2) Week 3 6Dokument65 Seiten2 Dist Arch (Week 2) Week 3 6Muhammad Awais ShahNoch keine Bewertungen
- Introduction To Distributed Systems: Brian Nielsen Bnielsen@cs - Aau.dk Bnielsen@cs - Aau.dkDokument54 SeitenIntroduction To Distributed Systems: Brian Nielsen Bnielsen@cs - Aau.dk Bnielsen@cs - Aau.dkIhab AmerNoch keine Bewertungen
- Networking - Fundamentals - Reference Models - 2020-1Dokument67 SeitenNetworking - Fundamentals - Reference Models - 2020-1Jefry Mateus100% (1)
- Three-tier Architecture OptimizedDokument59 SeitenThree-tier Architecture Optimizedrakesh_cs_jsrNoch keine Bewertungen
- DC Module1Dokument54 SeitenDC Module1Dev SharmaNoch keine Bewertungen
- Distributed Operating Systems Course Structure and Relevance/TITLEDokument57 SeitenDistributed Operating Systems Course Structure and Relevance/TITLEJohn DoeNoch keine Bewertungen
- Memory in Multiprocessor SystemDokument52 SeitenMemory in Multiprocessor SystemPriyanka MadaanNoch keine Bewertungen
- Distributed Computing Unit 1 - Introduction: Lecture 1a - Prof Ruchi SDokument17 SeitenDistributed Computing Unit 1 - Introduction: Lecture 1a - Prof Ruchi SShobhit ShahNoch keine Bewertungen
- (NPM) Lecture Note CH-1Dokument28 Seiten(NPM) Lecture Note CH-1Guyo Dida Karayu100% (1)
- IT1100 IWT Lecture 01Dokument46 SeitenIT1100 IWT Lecture 01Pawani PereraNoch keine Bewertungen
- IntroductionDokument59 SeitenIntroductionCIRI CORPORATENoch keine Bewertungen
- 1455 - Effects of Global Warming - 1Dokument8 Seiten1455 - Effects of Global Warming - 1Dipanjan DasNoch keine Bewertungen
- Distributed Computing I OutlineDokument27 SeitenDistributed Computing I OutlineAaron Paul Oseghale OkosunNoch keine Bewertungen
- CC Unit1Dokument9 SeitenCC Unit1shindesanket928Noch keine Bewertungen
- Distributed Systems FinalDokument15 SeitenDistributed Systems FinalIdrees HafeezNoch keine Bewertungen
- 02 SystemModels Architecture 2Dokument7 Seiten02 SystemModels Architecture 2Kool PrashantNoch keine Bewertungen
- Distributed System: Definition: A Distributed System Is A Piece of Software That En-Sures ThatDokument34 SeitenDistributed System: Definition: A Distributed System Is A Piece of Software That En-Sures ThatMangesh ThoratNoch keine Bewertungen
- Complete Unit 1Dokument14 SeitenComplete Unit 1rag33100% (1)
- Distributed Systems Lecture 1-2Dokument20 SeitenDistributed Systems Lecture 1-2onele mabhenaNoch keine Bewertungen
- UNIT-IV - Operating System SupportDokument51 SeitenUNIT-IV - Operating System SupportsatyaNoch keine Bewertungen
- Client/Server Computing: Operating Systems: Internals and Design Principles, 6/EDokument79 SeitenClient/Server Computing: Operating Systems: Internals and Design Principles, 6/Enaumanahmed19Noch keine Bewertungen
- Cs 422 - Distributed Computing: Threats and DifficultiesDokument8 SeitenCs 422 - Distributed Computing: Threats and DifficultiesPearzel KateNoch keine Bewertungen
- Distributed SystemDokument76 SeitenDistributed SystemTulipNoch keine Bewertungen
- Cloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingVon EverandCloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingNoch keine Bewertungen
- Multicore Software Development Techniques: Applications, Tips, and TricksVon EverandMulticore Software Development Techniques: Applications, Tips, and TricksBewertung: 2.5 von 5 Sternen2.5/5 (2)
- Oracle Utilities Customer Care and Billing: Batch Operations and Configuration Guide Ver 2.3.1 E18372-01Dokument68 SeitenOracle Utilities Customer Care and Billing: Batch Operations and Configuration Guide Ver 2.3.1 E18372-01LakshmiNarayana PuttamchettyNoch keine Bewertungen
- Principles of Data Visualization (Elective - 1) (BDA 5132)Dokument3 SeitenPrinciples of Data Visualization (Elective - 1) (BDA 5132)deepakbhatrNoch keine Bewertungen
- Customer Inter@Ction SOLUTIONS'2004 Product of The Year AwardsDokument8 SeitenCustomer Inter@Ction SOLUTIONS'2004 Product of The Year AwardsLakshman ReddyNoch keine Bewertungen
- U14 A1 Report-HubertwojciechowskiDokument7 SeitenU14 A1 Report-Hubertwojciechowskiapi-496855127Noch keine Bewertungen
- Integrating Zabbix and PA Subinterfaces Via APIDokument16 SeitenIntegrating Zabbix and PA Subinterfaces Via APIlawNoch keine Bewertungen
- Common Software in Website MakingDokument8 SeitenCommon Software in Website MakingIbanez, Romulo IIINoch keine Bewertungen
- Report Renderer ActionDokument8 SeitenReport Renderer ActionShailesh MishraNoch keine Bewertungen
- Software Company IndexDokument103 SeitenSoftware Company IndexAvineesh NandanNoch keine Bewertungen
- Inside OutDokument904 SeitenInside OutDenisa PetrisorNoch keine Bewertungen
- Embedded Wireless ProjectsDokument3 SeitenEmbedded Wireless Projectspraveen_kodgirwarNoch keine Bewertungen
- Linux Essentials Chapter & Labs 1-8Dokument214 SeitenLinux Essentials Chapter & Labs 1-8wowno20055173100% (5)
- F5923 3G Soho Mobile Router User ManualDokument19 SeitenF5923 3G Soho Mobile Router User ManualChelsea MedellinNoch keine Bewertungen
- ChtSht91 RTFDokument64 SeitenChtSht91 RTFElvis Henry Guzman AquijeNoch keine Bewertungen
- Bartender ActivationDokument7 SeitenBartender ActivationJung YeonNoch keine Bewertungen
- Tesda Training Questionnaire ResponsesDokument57 SeitenTesda Training Questionnaire ResponsesvicentemariscalNoch keine Bewertungen
- Hands-On Exercise No.1 Batch-09 E-Commerce Management Total Marks: 10 Due Date: 04/03/2021Dokument3 SeitenHands-On Exercise No.1 Batch-09 E-Commerce Management Total Marks: 10 Due Date: 04/03/2021sbspuNoch keine Bewertungen
- Student Accomplishments Dec 2014Dokument8 SeitenStudent Accomplishments Dec 2014Amit ShethNoch keine Bewertungen
- Answer: Windows Service Explanation: A Windows Service Is An Application That Runs in The Background and Does Not Have Any User InterfaceDokument148 SeitenAnswer: Windows Service Explanation: A Windows Service Is An Application That Runs in The Background and Does Not Have Any User InterfaceKei OnderNoch keine Bewertungen
- Indonesian IoT Ecosystem v.0.2Dokument2 SeitenIndonesian IoT Ecosystem v.0.2budi rahardjoNoch keine Bewertungen
- FTC Google Probe RecommendationDokument85 SeitenFTC Google Probe RecommendationJason MickNoch keine Bewertungen
- Cream, Green, and Black Geometric Blocks Clean Minimal PresentationDokument25 SeitenCream, Green, and Black Geometric Blocks Clean Minimal PresentationJoseph Franklin NOUBINoch keine Bewertungen
- Hsslive XII Computer Science Quick Notes Biju JohnDokument15 SeitenHsslive XII Computer Science Quick Notes Biju JohnSuhail latheef100% (1)
- Source of Information Information Provided Plenary Affairs Bureau (PAB)Dokument24 SeitenSource of Information Information Provided Plenary Affairs Bureau (PAB)Saila KumarNoch keine Bewertungen
- Hide Solution Discussion: Correct Answer: CDokument88 SeitenHide Solution Discussion: Correct Answer: C000-924680Noch keine Bewertungen
- Cinfiguration of Adobe Document ServicesDokument36 SeitenCinfiguration of Adobe Document ServicesTarun ReddyNoch keine Bewertungen
- Basics of HFMDokument27 SeitenBasics of HFMVenkatesh VenkusNoch keine Bewertungen
- Online Order/Reservation SystemDokument75 SeitenOnline Order/Reservation SystemJay-r MatibagNoch keine Bewertungen
- Identifying The True IP of I2P Service HostsDokument23 SeitenIdentifying The True IP of I2P Service HostsHaddad SammirNoch keine Bewertungen
- CCC Vmware Server Installation Guide: Document Version 1.0-02.00.1 Build 016Dokument16 SeitenCCC Vmware Server Installation Guide: Document Version 1.0-02.00.1 Build 016raddouaneNoch keine Bewertungen
- ExamScheduling System DocumentationDokument82 SeitenExamScheduling System Documentationdenekew50% (2)