Beruflich Dokumente
Kultur Dokumente
Email Policy
Hochgeladen von
Ninoyz™0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
164 Ansichten23 SeitenCompany encourages the use of electronic mail and respects the privacy of users. It does not routinely inspect, monitor, or disclose electronic mail without consent. Electronic mail, whether or not created or stored on company equipment, may constitute as company record.
Originalbeschreibung:
Copyright
© Attribution Non-Commercial (BY-NC)
Verfügbare Formate
PPS, PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCompany encourages the use of electronic mail and respects the privacy of users. It does not routinely inspect, monitor, or disclose electronic mail without consent. Electronic mail, whether or not created or stored on company equipment, may constitute as company record.
Copyright:
Attribution Non-Commercial (BY-NC)
Verfügbare Formate
Als PPS, PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
164 Ansichten23 SeitenEmail Policy
Hochgeladen von
Ninoyz™Company encourages the use of electronic mail and respects the privacy of users. It does not routinely inspect, monitor, or disclose electronic mail without consent. Electronic mail, whether or not created or stored on company equipment, may constitute as company record.
Copyright:
Attribution Non-Commercial (BY-NC)
Verfügbare Formate
Als PPS, PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 23
Email Policy
INTRODUCTION
• Electronic Mail (Email) System or Services: Any
messaging system that depends on computing
facilities to create, send, forward, reply to,
transmit, store, hold, copy, download, display,
view, read, or print computer records for
purposes of asynchronous communication
across computer network systems between or
among individuals or groups, that is either
explicitly denoted as a system for electronic
mail; or is implicitly used for such purposes.
The company encourages the use of electronic mail and
respects the privacy of users. It does not routinely inspect,
monitor, or disclose electronic mail without the holder's
consent. Nonetheless, subject to the requirements for
authorization and notification, the company may deny
access to its electronic mail services and may inspect,
monitor, or disclose electronic mail when required by and
consistent with law, when there is substantiated reason
that violations of policy or law have taken place, or, in
exceptional cases, when required to meet time-dependent,
critical operational needs. These provisions are
comparable to those of policies that apply to other forms of
communications, such as conventional mail.
CAUTIONS: Users should be
aware of the following:
• 1.1 Both the nature of electronic mail and of the
company’s business makes electronic mail less
private than users may anticipate. For example,
electronic mail intended for one person
sometimes may be widely distributed because of
the ease with which recipients can forward it to
others. Furthermore, even after a user deletes
an electronic mail record from a computer or
electronic mail account it may persist on backup
facilities, and thus be subject to disclosure under
the provisions of public records law. The
company cannot routinely protect users against
such eventualities
1.2 Electronic mail, whether or not created or
stored on company equipment, may constitute as
company record. Thus, may be subject to full
disclosure if necessary
1.3 The company, in general, cannot and does
not wish to be the arbiter of the contents of
electronic mail. Neither can the company, in
general, protect users from receiving electronic
mail they may find offensive. Employees, however,
are strongly encouraged to use the same personal
and professional courtesies and considerations in
electronic mail as they would in other forms of
communication.
1.4 There is no guarantee, unless
"authenticated" mail systems are in use, that
electronic mail received was in fact sent by the
purported sender, since it is relatively
straightforward, although it is defined as a violation
in this Policy, for senders to disguise their identity.
Furthermore, electronic mail that is forwarded may
also be modified. Authentication technology is not
widely and systematically in use in the company as
of the date of this Policy. As with print documents,
in case of doubt receivers of electronic mail
messages should check with the purported sender
to validate authorship or authenticity
1.5 There will be occasions that IT personnel and system
administrators may, during the performance of their duties,
inadvertently see the contents of email messages.
1.6 Except as provided elsewhere in this Policy, IT personnel
are not permitted to do so intentionally or disclose or otherwise
use what they have seen. One exception, however, is that of
Systems Administrator who may need to inspect email when re-
routing or disposing of otherwise undeliverable email. This
exception is limited to the least invasive level of inspection
required to perform such duties. Furthermore, this exception
does not exempt Systems Administrator from the prohibition
against disclosure of personal and confidential information,
except insofar as such disclosure equates with good faith
attempts to route the otherwise undeliverable email to the
intended recipient. Re-routed mail normally should be
accompanied by notification to the recipient that the email has
been inspected for such purposes
1.7 Even though the sender and recipient have
discarded their copies of an electronic mail record,
there may be back-up copies that can be retrieved.
Systems may be "backed-up" on a routine or
occasional basis to protect system reliability and
integrity, and to prevent potential loss of data. The
back-up process results in the copying of data onto
storage media that may be retained for periods of
time and in locations unknown to the originator or
recipient of electronic mail. The practice and
frequency of back-ups and the retention of back-up
copies of email vary from system to system.
PURPOSE
This paper is aimed to:
2.1 Establish a policy for effective and way of
communication through the proper use of email.
2.2 Identify limitations and prohibitions in the use
of company email facility.
2.3 Define new policy and procedures where
existing policies do not specifically address issues
particular to the use of electronic mail.
2.4 Minimize disruptions in the use of company’s
electronic mail and other services and activities.
SCOPE
• This policy applies to all employees of
iWebmasters.com, Inc.
POLICY
1. Each user is subject to 50 megabytes
quota space only.
2. Only IT personnel is authorized to issue
email account to each employee of iWeb.
3. Each employee will only be provided with
one email account, additional email account
can be accommodated provided approved by
IT Manager and COO.
4. Use of company email is limited to official
use only. Use of company email for private
business activities, personal activities,
amusement/entertainment purposes, or other
non-job related communications is
discouraged.
5. Email services may be used for incidental
personal purposes provided that, in addition to the
foregoing constraints and conditions, such use
does not
5.1 Directly or indirectly interfere with the
company’s operation of computing facilities or
electronic mail services;
5.2 Burden the company with noticeable
incremental cost;
5.3 Interfere with the email user's employment
or other obligations to the company. Email records
arising from such personal use may, however, be
subject to full disclosure under the presumption
that such are company records
such as MS Outlook maybe allowed provided
approved by IT Manager and COO.
8. All email messages should be
downloaded. No copy of messages will be
stored in the email server.
9. Email accounts of resigned employees are
automatically deleted on their last working
day.
PENALTIES
• Employees are accountable for their use of electronic
communications just as they are for other conduct and
communications in the workplace. Violations of policies
governing the use of email may result in restriction of
access to the company’s computing access. In addition,
Corrective Action may be applicable under the company’s
Code of Conduct specifically the following provisions:
• Article 1 Section 4.1
• Article 1 Section 4.2
• Article 1 Section 5.25
• Article 2 Section 2.19
• Article 2 Section 2.21
• Article 3 Section 1.1
• Article 3 Section 1.22
In addition to the above existing provisions in our
Code of Conduct, the following will be added:
OFFENSES RELATED TO EMAIL USE
DESCRIPTION of OFFENSE TYPE of OFFENSE
• Theft or other abuse of C
computing facilities.
• Unauthorized entry, use, C
transfer, and tampering with
the accounts and files of
others
• Interference with the work of
others and with other B
computing facilities
• Use of email for unlawful
activities C
• Use of email commercial B
purposes not under the
auspices of the company
OFFENSES RELATED TO EMAIL USE
DESCRIPTION of OFFENSE TYPE of OFFENSE
• Use of email for personal C
financial gain (except as
permitted under applicable
policies)
• Use of email for personal use B
inconsistent with policies
regarding intellectual property,
or regarding sexual or other
forms of harassment.
• Mis-representation. Giving the B
impression that employee is
representing, giving opinions,
or otherwise making
statements on behalf of the
company unless appropriately
authorized (explicitly or
implicitly) to do so
OFFENSES RELATED TO EMAIL USE
DESCRIPTION of OFFENSE TYPE of OFFENSE
• Failure to write an explicit
disclaimer at the bottom
of the email unless it is
clear from the context
that the author is not
representing the B
company. An appropriate
disclaimer is: “The
opinions or statements
expressed hereon are my
own and should not be
taken as a position,
opinion, or endorsement
of the company.
OFFENSES RELATED TO EMAIL USE
DESCRIPTION of OFFENSE TYPE of OFFENSE
• Use of email that will Interfere with
the company’s email services that
could reasonably be expected to
cause, directly or indirectly,
excessive strain on any computing
facilities, or unwarranted or
unsolicited interference with others'
use of email or email systems .
Such uses include, but are not
limited to, the use of email services
to:
• i. Send or forward email chain
letters;
B
• ii "Spam", that is, to exploit list
servers or similar broadcast
systems for purposes beyond their
intended scope to amplify the
widespread distribution of
unsolicited email;
• Iii. “Letter-bomb", that is, to re-send
the same email repeatedly to one or
more recipients to interfere with the
recipient's use of email.
OFFENSES RELATED TO EMAIL USE
DESCRIPTION of OFFENSE TYPE of OFFENSE
• Excessive use of email for A
Personal Use.
• Failure to exercise extreme
caution in using email to B
communicate confidential
sensitive matters.
• Failure to take necessary
precautions to protect the B
confidentiality of personal or
confidential information
encountered in the
performance of their duties or
otherwise in the use of email
facilities
EFFECTIVITY AND VALIDITY
• This policy paper shall take effect
immediately after approval and should be
reviewed annually or as need arises.
Das könnte Ihnen auch gefallen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Acknowledgement of Debt 2 PDFDokument5 SeitenAcknowledgement of Debt 2 PDFzoopy zodzkNoch keine Bewertungen
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- Mauri-Crown-Royal-Decree Declaration Judgment 13Dokument9 SeitenMauri-Crown-Royal-Decree Declaration Judgment 13api-536617451Noch keine Bewertungen
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Defendants' Opposition To Hikma Pharmaceuticals USA Inc.'s Motion To Int...Dokument74 SeitenDefendants' Opposition To Hikma Pharmaceuticals USA Inc.'s Motion To Int...Anonymous C3i3MTaS1QNoch keine Bewertungen
- Re-Hiring Policy: "A Leap To Endless Possibilities"Dokument9 SeitenRe-Hiring Policy: "A Leap To Endless Possibilities"Ninoyz™Noch keine Bewertungen
- Legal Consequences of The Construction of A Wall in The Occupied Palestinian TerritoryDokument2 SeitenLegal Consequences of The Construction of A Wall in The Occupied Palestinian TerritoryElaiza Jamez PucateNoch keine Bewertungen
- Do's and Dont's During PregnancyDokument11 SeitenDo's and Dont's During PregnancyNinoyz™100% (2)
- Aldaba v. Comelec DigestDokument3 SeitenAldaba v. Comelec Digestkathrynmaydeveza100% (2)
- Policy On Floating StatusDokument19 SeitenPolicy On Floating StatusNinoyz™100% (5)
- Dimagiba v. Montalvo - DigestDokument2 SeitenDimagiba v. Montalvo - DigestMaria Jennifer Yumul Borbon50% (2)
- Land Bank Vs DumlaoDokument2 SeitenLand Bank Vs DumlaoTrek Alojado100% (2)
- Araneta Vs Bank of AmericaDokument1 SeiteAraneta Vs Bank of Americasabrina gayoNoch keine Bewertungen
- DIGEST - D.M. CONSUNJI, INC. vs. CADokument3 SeitenDIGEST - D.M. CONSUNJI, INC. vs. CADae JosecoNoch keine Bewertungen
- Rule 4 (Outline, Case Digest & Fulltext)Dokument61 SeitenRule 4 (Outline, Case Digest & Fulltext)to be the greatestNoch keine Bewertungen
- Summary of Attendance - August 2010Dokument4 SeitenSummary of Attendance - August 2010Ninoyz™Noch keine Bewertungen
- Government Mandated Benefits PolicyDokument13 SeitenGovernment Mandated Benefits PolicyNinoyz™100% (2)
- Policy On Request For Change of Work ScheduleDokument7 SeitenPolicy On Request For Change of Work ScheduleNinoyz™100% (1)
- Ninoyz ResumeDokument3 SeitenNinoyz ResumeNinoyz™Noch keine Bewertungen
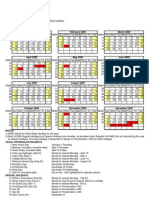
- 2009 CalendarDokument1 Seite2009 CalendarNinoyz™100% (1)
- Comm Sample MCQ - PortiaDokument14 SeitenComm Sample MCQ - Portiacmv mendozaNoch keine Bewertungen
- The Civil Code of The PhilippinesDokument208 SeitenThe Civil Code of The PhilippinesJOHN SPARKSNoch keine Bewertungen
- Class Action Maryland Oct 2010Dokument46 SeitenClass Action Maryland Oct 2010dean6265Noch keine Bewertungen
- GEMS Constitution and by LawsDokument7 SeitenGEMS Constitution and by Lawsmarie ellaine solisNoch keine Bewertungen
- Hunter MooreDokument20 SeitenHunter MoorenicholasdeleoncircaNoch keine Bewertungen
- @ItsKahuna John Anthony Borell PACER Discovery SealDokument6 Seiten@ItsKahuna John Anthony Borell PACER Discovery SealOccupyUnmaskedNoch keine Bewertungen
- Hunter Water To DPC - SO52 LHWSP PDFDokument2 SeitenHunter Water To DPC - SO52 LHWSP PDFMatthew KellyNoch keine Bewertungen
- James Egan QuestionnaireDokument6 SeitenJames Egan QuestionnaireStatesman JournalNoch keine Bewertungen
- Cariaga vs. LTBDokument5 SeitenCariaga vs. LTBMirzi Olga Breech SilangNoch keine Bewertungen
- Third Division: PEOPLE OF THE PHILIPPINES, Plaintiff-Appellee, V S - JOSE BRONIOLA at "ASOT", Accused-AppellantDokument7 SeitenThird Division: PEOPLE OF THE PHILIPPINES, Plaintiff-Appellee, V S - JOSE BRONIOLA at "ASOT", Accused-AppellantChoi ChoiNoch keine Bewertungen
- Predominance of Legal SpiritDokument4 SeitenPredominance of Legal SpiritpraharshithaNoch keine Bewertungen
- Commission On Human Rights (Philippines) : HistoryDokument6 SeitenCommission On Human Rights (Philippines) : Historyadonis.orillaNoch keine Bewertungen
- CIR V Mindanao II Geothermal PartnershipDokument2 SeitenCIR V Mindanao II Geothermal PartnershipGwynneth Grace LasayNoch keine Bewertungen
- Custodial DeathDokument8 SeitenCustodial Deathanuc07100% (2)
- Civil Procedure Cases 1Dokument30 SeitenCivil Procedure Cases 1Felip MatNoch keine Bewertungen
- The Police Order, 2002Dokument83 SeitenThe Police Order, 2002gladiatorranaNoch keine Bewertungen
- Edilon CaseDokument28 SeitenEdilon CaseAL Babaran CanceranNoch keine Bewertungen
- Bildner Vs IlusorioDokument30 SeitenBildner Vs IlusorioLawrence SantiagoNoch keine Bewertungen
- Doj Vs Liwag (Full Case)Dokument7 SeitenDoj Vs Liwag (Full Case)Awe SomontinaNoch keine Bewertungen
- Judicial Review-Quick Guide On AuthoritiesDokument22 SeitenJudicial Review-Quick Guide On AuthoritiesShahrin NordinNoch keine Bewertungen