Beruflich Dokumente
Kultur Dokumente
Source Code Features: Malicious Url Is Detected by Using 3 Major Features
Hochgeladen von
Radha RamanOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Source Code Features: Malicious Url Is Detected by Using 3 Major Features
Hochgeladen von
Radha RamanCopyright:
Verfügbare Formate
Malicious Url is detected by using 3 major features:We score url on the set of features.
The urls matching maximum no of feature score will be classified as malicious .
Lexical Features
These features allow us to capture the property that malicious URLs tend to look different from benign URLs. For example, the appearance of the token .com in the URL www.ebay.com is not unusual. However, the appearance of .com in www.ebay.com.phishy.biz or phish.biz/www.ebay.com/ index.php could indicate an attempt by criminals to spoof the domain name of a legitimate commercial Web site. Similarly, we would like to capture the fact that there are certain red flag keywords that tend to appear in malicious URLs e.g., ebayisapi would appear frequently in the path of URLs attempting to spoof an eBay page.
Source code features
JavaScript exploits are typically obfuscated to prevent detection by automated or manual analysis. Attackers typically use special characters to encode script, either as direct ASCII or transformed by some simple character-to-character function: document.write(unescape(%3C%68%74%6D%6C%20 %6C%61%6E%67%3D%22%65%6E%22%20%6... Thus, we can use the ratio of special character subsequences (nonEnglish for en websites) to script length.
Network features
We have only captured payload size i.e size of the webscript . Executable can be arbitrarily long, and obfuscated script may add to payload size as well.
Forecasting Sales using Data Mining
A data mining algorithm is a set of heuristics and calculations that creates a data mining model from data. To create a model, the algorithm first analyzes the data you provide, looking for specific types of patterns or trends. The algorithm uses the results of this analysis to define the optimal parameters for creating the mining model. These parameters are then applied across the entire data set to extract actionable patterns and detailed statistics. The mining model that an algorithm creates from your data can take various forms, including: A set of clusters that describe how the cases in a dataset are related. A decision tree that predicts an outcome, and describes how different criteria affect that outcome. A mathematical model that forecasts sales. A set of rules that describe how products are grouped together in a transaction, and the probabilities that products are purchased together.
We can Association rule mining for sales forecasting.Where forecasting will be done by By analyzing the most frequent items present in the dataset. We can also use time series analysis for forecasting .As we analyze the previous years sales patterns for analyzing.
Das könnte Ihnen auch gefallen
- Numsense! Data Science For The LaymanDokument65 SeitenNumsense! Data Science For The Laymanjohn100% (3)
- Data Mining Algorithms (Analysis Services - Data Mining) : Choosing The Right AlgorithmDokument3 SeitenData Mining Algorithms (Analysis Services - Data Mining) : Choosing The Right AlgorithmsatishgwNoch keine Bewertungen
- How Do Search Engines Work?Dokument6 SeitenHow Do Search Engines Work?Suhaila IbrahimNoch keine Bewertungen
- My DocumentDokument7 SeitenMy Documentclash tvNoch keine Bewertungen
- Detect Phishing Websites Using MLDokument20 SeitenDetect Phishing Websites Using MLZac ryanNoch keine Bewertungen
- Module 3Dokument23 SeitenModule 3aashirwadmishra24Noch keine Bewertungen
- DSE 3 Unit 3Dokument4 SeitenDSE 3 Unit 3Priyaranjan SorenNoch keine Bewertungen
- SEO Terms & MeaningsDokument23 SeitenSEO Terms & MeaningsNehan HossainNoch keine Bewertungen
- Detecting Nepotistic Links Based On Qualified Link Analysis and Language ModelsDokument4 SeitenDetecting Nepotistic Links Based On Qualified Link Analysis and Language Modelssurendiran123Noch keine Bewertungen
- Search Engine Optimization - NOtesDokument8 SeitenSearch Engine Optimization - NOtesBounty HunterNoch keine Bewertungen
- Aioseo LojaalfastorecombrDokument11 SeitenAioseo Lojaalfastorecombrshahid iqbalNoch keine Bewertungen
- DM Merged PDFDokument51 SeitenDM Merged PDFSurabhi AgarwalNoch keine Bewertungen
- WARNINGBIRD A Near Real Time Detection System For Suspicious URLs in Twitter StreamDokument5 SeitenWARNINGBIRD A Near Real Time Detection System For Suspicious URLs in Twitter StreamManchireddy AnanthaNoch keine Bewertungen
- Lab 8.1 - Find String: CCIS2410: Hacker Techniques & ToolsDokument3 SeitenLab 8.1 - Find String: CCIS2410: Hacker Techniques & ToolsaderhabNoch keine Bewertungen
- Overall Score For:: Seositecheckup ReportDokument16 SeitenOverall Score For:: Seositecheckup ReportabhishekluvNoch keine Bewertungen
- Seositecheckup Analysis Report 2015 09 25 09 37 15 PDFDokument20 SeitenSeositecheckup Analysis Report 2015 09 25 09 37 15 PDFt.umeshNoch keine Bewertungen
- Detect Phishing Websites Using MLDokument6 SeitenDetect Phishing Websites Using MLHarikrishnan ShunmugamNoch keine Bewertungen
- Top 30+ Free Search Engine Optimization (SEO) ToolsDokument7 SeitenTop 30+ Free Search Engine Optimization (SEO) Toolssaliniprabha100% (2)
- Detection of Phishing Attacks: A Machine Learning ApproachDokument11 SeitenDetection of Phishing Attacks: A Machine Learning ApproachKiran MudaliyarNoch keine Bewertungen
- Working of Search Engines and How Search Engines Crawl the WebDokument13 SeitenWorking of Search Engines and How Search Engines Crawl the WebaviNoch keine Bewertungen
- What Is CorrelationDokument9 SeitenWhat Is CorrelationVõ HồngNoch keine Bewertungen
- How To Debug A Coremetrics ImplementationDokument20 SeitenHow To Debug A Coremetrics ImplementationBajji RajinishNoch keine Bewertungen
- Annotating Full DocumentDokument48 SeitenAnnotating Full DocumentkalyanNoch keine Bewertungen
- SEO BasicsDokument18 SeitenSEO BasicsAlexandra CiarnauNoch keine Bewertungen
- Ten Supplementary Analyses To Improve E-Commerce Web Sites: Ron Kohavi Rajesh ParekhDokument8 SeitenTen Supplementary Analyses To Improve E-Commerce Web Sites: Ron Kohavi Rajesh ParekhnightkamiNoch keine Bewertungen
- Phishing Detection WebsiteDokument7 SeitenPhishing Detection WebsiteSshatpu SshNoch keine Bewertungen
- Phishing Detection Website Base PaperDokument8 SeitenPhishing Detection Website Base PaperSshatpu SshNoch keine Bewertungen
- Benefits of Web Crawling and ScrapingDokument4 SeitenBenefits of Web Crawling and Scrapingjamiluisah26Noch keine Bewertungen
- How Google Analytics Collects DataDokument3 SeitenHow Google Analytics Collects DataRosalieNoch keine Bewertungen
- SEO Audit Report - Bizualized v2Dokument17 SeitenSEO Audit Report - Bizualized v2curiousEngineNoch keine Bewertungen
- SQL Server Data Mining ToolsDokument4 SeitenSQL Server Data Mining ToolsJulie RobertsNoch keine Bewertungen
- Fake UrlDokument64 SeitenFake UrlChaitan BruceNoch keine Bewertungen
- Data Mining FunctiDokument6 SeitenData Mining Functiparthasarathy_vinayaNoch keine Bewertungen
- Supplementary AnalysesDokument8 SeitenSupplementary AnalysessonisandeepmNoch keine Bewertungen
- Association Rule MiningDokument13 SeitenAssociation Rule MininggayatrikhasiramNoch keine Bewertungen
- Crawling Deep Web Entity Pages: Yeye He Heyeye@cs - Wisc.edu Dong Xin Venkatesh Ganti Sriram Rajaraman Nirav ShahDokument10 SeitenCrawling Deep Web Entity Pages: Yeye He Heyeye@cs - Wisc.edu Dong Xin Venkatesh Ganti Sriram Rajaraman Nirav ShahTarun ChoudharyNoch keine Bewertungen
- Application of Regular Expression in Search Engine OptimizationDokument12 SeitenApplication of Regular Expression in Search Engine OptimizationDevanshu AgarwalNoch keine Bewertungen
- Digital Marketing PDFDokument10 SeitenDigital Marketing PDFGokula priyaNoch keine Bewertungen
- Seo GuideDokument25 SeitenSeo Guideradwa.talaatNoch keine Bewertungen
- Do Businesses Actually Need SEODokument6 SeitenDo Businesses Actually Need SEOacharyamalvikaNoch keine Bewertungen
- IoT Domain Analyst Digital Assignment E-R Model and Predictive AnalysisDokument6 SeitenIoT Domain Analyst Digital Assignment E-R Model and Predictive AnalysisharshithNoch keine Bewertungen
- How Do Search Engines WorkDokument25 SeitenHow Do Search Engines WorkRemonda SaiedNoch keine Bewertungen
- DCS802DataMiningProject PDFDokument10 SeitenDCS802DataMiningProject PDFDavid UlmerNoch keine Bewertungen
- How to Web Scrape with Python in 4 MinutesDokument12 SeitenHow to Web Scrape with Python in 4 Minutesvicearellano100% (1)
- Free Traffic SecretsDokument30 SeitenFree Traffic Secretsoszkar69Noch keine Bewertungen
- TorrentsDokument19 SeitenTorrentskunalmaniyarNoch keine Bewertungen
- N P Singh's guide to business intelligence and data analyticsDokument28 SeitenN P Singh's guide to business intelligence and data analyticsBhawna KhoslaNoch keine Bewertungen
- SeminDokument8 SeitenSeminMomin Mohd AdnanNoch keine Bewertungen
- Using Naive Bayes To Detect Spammy Names in Social Networks: David Mandell FreemanDokument10 SeitenUsing Naive Bayes To Detect Spammy Names in Social Networks: David Mandell FreemanArdani RohmanNoch keine Bewertungen
- Search Engine Student DocumentsDokument6 SeitenSearch Engine Student DocumentsMrHeerenTeachesNoch keine Bewertungen
- Stock Market Analysis Using Supervised Machine LearningDokument6 SeitenStock Market Analysis Using Supervised Machine LearningAbishek Pangotra (Abi Sharma)Noch keine Bewertungen
- Web Scraping by Using RDokument3 SeitenWeb Scraping by Using RVijay ChandarNoch keine Bewertungen
- Spam Url Attribute MethodDokument3 SeitenSpam Url Attribute MethodHieun kongNoch keine Bewertungen
- Data Mining Using SAS Enterprise Miner - A Case Study ApproachDokument134 SeitenData Mining Using SAS Enterprise Miner - A Case Study ApproachRohita MaddipatiNoch keine Bewertungen
- Data - Collection PythonDokument40 SeitenData - Collection PythonZADOD YASSINENoch keine Bewertungen
- Association RulesDokument9 SeitenAssociation Rulesadarsh barodNoch keine Bewertungen
- IWT Lab ManualDokument26 SeitenIWT Lab ManualPushpendra KumarNoch keine Bewertungen
- Techniques for Advanced Search Engine Optimization: On Autopilot, Increase Your Traffic and Profits!Von EverandTechniques for Advanced Search Engine Optimization: On Autopilot, Increase Your Traffic and Profits!Noch keine Bewertungen
- ACCP D8 7020 Trim1 PracticalPaper Set1 SolnDokument2 SeitenACCP D8 7020 Trim1 PracticalPaper Set1 SolnRadha RamanNoch keine Bewertungen
- KNNDokument11 SeitenKNNRadha RamanNoch keine Bewertungen
- SkdnssecDokument10 SeitenSkdnssecRadha RamanNoch keine Bewertungen
- File Zilla FTPDokument3 SeitenFile Zilla FTPRadha RamanNoch keine Bewertungen
- The Basic Concepts of Algorithms: 2.1 The Minimal Spanning Tree ProblemDokument32 SeitenThe Basic Concepts of Algorithms: 2.1 The Minimal Spanning Tree ProblemManjunath KurubaNoch keine Bewertungen
- Display Images in ASPDokument4 SeitenDisplay Images in ASPRadha RamanNoch keine Bewertungen
- Black and WhiteDokument66 SeitenBlack and WhiteRadha RamanNoch keine Bewertungen
- Page Replacement Algorithms Important Donot DeleteDokument10 SeitenPage Replacement Algorithms Important Donot DeletesabirsvcmNoch keine Bewertungen
- 1.convert An Audio/video File in Array of Bytes. 2.use A Cryptographic Algorithm To Encrypt/decryptDokument2 Seiten1.convert An Audio/video File in Array of Bytes. 2.use A Cryptographic Algorithm To Encrypt/decryptRadha RamanNoch keine Bewertungen
- AbstractDokument1 SeiteAbstractRadha RamanNoch keine Bewertungen
- Nfa DfaDokument13 SeitenNfa DfaRadha RamanNoch keine Bewertungen
- E Libary SynopsisDokument7 SeitenE Libary SynopsisRadha RamanNoch keine Bewertungen
- Format GridviewDokument2 SeitenFormat GridviewRadha RamanNoch keine Bewertungen
- Format GridviewDokument2 SeitenFormat GridviewRadha RamanNoch keine Bewertungen
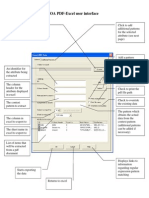
- Woa PDF-XL User InterfaceDokument2 SeitenWoa PDF-XL User InterfaceRadha RamanNoch keine Bewertungen
- Black and WhiteDokument66 SeitenBlack and WhiteRadha RamanNoch keine Bewertungen
- MI0041 AnswerDokument15 SeitenMI0041 AnswerRadha RamanNoch keine Bewertungen
- Content: Chapter Title Page NoDokument3 SeitenContent: Chapter Title Page NoRadha RamanNoch keine Bewertungen
- MI0038 AnswerDokument13 SeitenMI0038 AnswerRadha RamanNoch keine Bewertungen
- Perform The Following Conversion: (3+3 Marks) A. (ABE) Ans: (101010111110)Dokument3 SeitenPerform The Following Conversion: (3+3 Marks) A. (ABE) Ans: (101010111110)Radha RamanNoch keine Bewertungen
- Class Path SettingDokument1 SeiteClass Path SettingRadha RamanNoch keine Bewertungen
- OsDokument7 SeitenOsRadha RamanNoch keine Bewertungen
- AstarDokument22 SeitenAstarRadha RamanNoch keine Bewertungen
- PaperDokument4 SeitenPaperRadha RamanNoch keine Bewertungen
- 17 11 11Dokument5 Seiten17 11 11Radha RamanNoch keine Bewertungen
- Context DFDDokument1 SeiteContext DFDRadha RamanNoch keine Bewertungen
- Compare AStar DijkshitraDokument5 SeitenCompare AStar DijkshitraRadha RamanNoch keine Bewertungen
- Database Snapshot: Read-Only View for ReportingDokument8 SeitenDatabase Snapshot: Read-Only View for ReportingRadha RamanNoch keine Bewertungen
-  Œdental Patient Management SystemâDokument13 Seiten Œdental Patient Management SystemâRadha RamanNoch keine Bewertungen
- Dmbi FileDokument31 SeitenDmbi Fileharnek singhNoch keine Bewertungen
- AStudyon Dataminingtechniquestoimprovestudentsperformancein Higher EducationDokument7 SeitenAStudyon Dataminingtechniquestoimprovestudentsperformancein Higher Educationddol36899Noch keine Bewertungen
- Association of Symptoms With Eating Habits and Food Preferences in Chronic Gastritis Patients A CrossSectional StudyDokument11 SeitenAssociation of Symptoms With Eating Habits and Food Preferences in Chronic Gastritis Patients A CrossSectional StudyDayanne WesllaNoch keine Bewertungen
- Oracle Machine Learning SQL Users GuideDokument188 SeitenOracle Machine Learning SQL Users GuideHarish NaikNoch keine Bewertungen
- DMDW-Solution For Unit 1-5Dokument20 SeitenDMDW-Solution For Unit 1-5Manish Arya50% (2)
- Association Rule Mining of Relational GraphsDokument1 SeiteAssociation Rule Mining of Relational GraphsSrinivasNoch keine Bewertungen
- The Optimization of Apriori Algorithm Based On Array and Its Application in The Analysis of Insurance ClientsDokument4 SeitenThe Optimization of Apriori Algorithm Based On Array and Its Application in The Analysis of Insurance Clientsulfadiyah kumalasariNoch keine Bewertungen
- Data Mining and Knowledge Discovery Assignment 2Dokument13 SeitenData Mining and Knowledge Discovery Assignment 2tzeloNoch keine Bewertungen
- ML Lab Manual AIML FinalDokument61 SeitenML Lab Manual AIML Finalsushankreddy0712Noch keine Bewertungen
- R Data AnalyticsDokument96 SeitenR Data AnalyticsShruti Jamsandekar100% (1)
- Apriori Algorithm in Data Mining Implementation With ExamplesDokument13 SeitenApriori Algorithm in Data Mining Implementation With Examplesaarthi devNoch keine Bewertungen
- 04 Frequent Patterns AnalysisDokument37 Seiten04 Frequent Patterns Analysisaanaon0Noch keine Bewertungen
- Unit 4 AiDokument13 SeitenUnit 4 Aimr yashNoch keine Bewertungen
- Weka Final Lab-KpswDokument137 SeitenWeka Final Lab-KpswchatlamalleshwarNoch keine Bewertungen
- DATA MINING ASSOCIATION RULESDokument96 SeitenDATA MINING ASSOCIATION RULESshilpa veeruNoch keine Bewertungen
- Data Mining - Lab - ManualDokument20 SeitenData Mining - Lab - ManualvarmamNoch keine Bewertungen
- WEKA Lab SessionDokument88 SeitenWEKA Lab SessionGUTAMA KUSSE GELEGLONoch keine Bewertungen
- What is Frequent Itemset MiningDokument7 SeitenWhat is Frequent Itemset MiningMonikaNoch keine Bewertungen
- Data WarehouseDokument41 SeitenData WarehouseAditya Mishra100% (2)
- CSD479 Data Mining: Lecture # 2 Chapter # 1 of The Text BookDokument14 SeitenCSD479 Data Mining: Lecture # 2 Chapter # 1 of The Text BookKhizar ShahidNoch keine Bewertungen
- AprioriTID Algorithm Improved From Apriori AlgorithmDokument5 SeitenAprioriTID Algorithm Improved From Apriori AlgorithmChadZs Arellano MutiaNoch keine Bewertungen
- Mining Various Kinds of Association RulesDokument11 SeitenMining Various Kinds of Association RulesJay MehtaNoch keine Bewertungen
- Academic Council Proceedings and Course on Data Mining and Business IntelligenceDokument2 SeitenAcademic Council Proceedings and Course on Data Mining and Business Intelligencenetgalaxy2010Noch keine Bewertungen
- ADBMS Lab ManualDokument26 SeitenADBMS Lab Manualanand_gudnavarNoch keine Bewertungen
- Machine Learning and Web Scraping Lesson02Dokument29 SeitenMachine Learning and Web Scraping Lesson02patrice mvogoNoch keine Bewertungen
- Unit-5: Concept Description and Association Rule MiningDokument39 SeitenUnit-5: Concept Description and Association Rule MiningNayan PatelNoch keine Bewertungen
- Lecture - 9 Unsupervised Learning (K-Means, Association Analysis and Frequuent Items)Dokument73 SeitenLecture - 9 Unsupervised Learning (K-Means, Association Analysis and Frequuent Items)ABDURAHMAN ABDELLANoch keine Bewertungen
- Data Warehousing MCQDokument71 SeitenData Warehousing MCQYash SulkahaNoch keine Bewertungen
- Data Mining Course IntroductionDokument39 SeitenData Mining Course IntroductionRaiza AnancaNoch keine Bewertungen