Beruflich Dokumente
Kultur Dokumente
Mobile Applications Security Android OS
Hochgeladen von
ghazi4uOriginalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Mobile Applications Security Android OS
Hochgeladen von
ghazi4uCopyright:
Verfügbare Formate
Mobile applications security Android OS (case study)
Maciej Olewiski
Cryptographic Seminar 16.05.2012r.
Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Presentations schedule
Mobile devices market
Smartphones domination is coming
Android basics
Main facts Architecture model
Applications security
On lower architectural layers Essential principles of higher layers design Android runtime as local web services environment Explicit data sharing Permissions mechanism Known vulnerabilities
Appendix Summary
2/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Smartphones growth
Smartphones on their way for mobile world domination
Huge popularity grow Popularization of mobile applications Smartphones replaces more and more devices: mp3 players, simple cameras etc. More and more sensitive data in small, portable devices
Market share
Main smartphones mobile platforms
Google Android Symbian iOS (Apple) BlackberryOS Windows Mobile/Windows Phone Bada
100% 80% 60% 40% 20% 0% 2010 2011 2012 2015 Others Windows Mobile/Phone Apple iOS Blacberry OS Symbian Google Android Mobile platforms market share in years 2010-2015 (prediction) - Gartner
3/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
What is Android?
Android is a software stack for mobile devices that includes an operating system, middleware and key applications
Created by Android Inc., a company acquired by Google in 2005 Developed under supervision of Open Handset Alliance (OHA) Released and open-sourced in 2008
Based on popular technologies
Linux Kernel Not a typical Linux distribution Java language Not a typical Java platform
The most popular smartphones OS in 2011
Also the fastest growing
4/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Android architecture the model
5/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Android architecture basic facts
All applications are equal (with small exceptions for Phone application)
System applications have no precedence over 3rd party software (with small exception for safe-mode)
All Android applications are written in Java programming language
Android SDK
Android is not a typical Java platform; it only uses the language
Custom implementation of Virtual Machine Dalvik VM (non-compliant with any Sun/Oracle solutions) Totally redesigned application lifecycle mechanisms, user interface principles and more Main packages set derived from Java SE platform (not from Java ME!) Removed desktop-typical packages (e.g. Swing, AWT etc.) Added mobile-typical packages (for telephony, location-based services, user interface and more)
Possibility to use native code in Android applications
Compiled C/C++ libraries can be used by Android applications using NDK (JNI) All Android security model principles are also applied to those libraries
Custom security model
Defined across the all architectural layers
Cryptographic Seminar| 16.05.2012r. 6/18
Maciej Olewiski | Android OS mobile applications security model
Applications security lower layers
A central design point of the Android security architecture is that no application, by default, has permission to perform any operations that would adversely impact other applications, the operating system, or the user Android Developers Android extensively use Linux-level security mechanisms
Even though each application package has its own instance of Dalvik Virtual Machine, it also gets its own Linux User ID (UID) and works in its own process Any data used by application is assigned to packages UID and is not accessible for other packages For any data sharing higher-level (Android specific) mechanisms should be used (full protection on Linux level); exposing all application data for other applications must be done explicitly
Applications signing for secure updates
Each application must be signed by developers certificate Certificate can be self-signed as it is only used to distinguish if the newer version of application can work under the same UID
7/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Applications the essentials (1)
All Android applications are build of 4 types of basic components
Activities Main user interface containers - an Activity represents one single screen visible by user Services Used for performing long-running, background operations Content Providers Used for sharing data between application explicit way for fully manageable exposing the data Broadcast Receivers Used for receiving broadcasts (something like Java listeners, but on higher level)
Querying Content Provider uses URIs and MIME types for RESTful-like interface Interaction between Activities, Services and Broadcast Receivers is driven by Intents
Intents are kind of asynchronous messages used for components activation
8/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Applications the essentials (2)
Intents the heart of Android
Intents can call specific components explicitly by defining target components class The real power lies in the fact that they can also define only required action and (optionally) data description (with MIME and URI), calling the components implicitly Runtime binding between components based on so called Intent Filters
Android Applications are typically not solid
Extensive use of runtime binding between components instead of compilation time binding (with Intents) Application are typically a set of independent components, rather than homogenous entity Anyway, it is possible to build solid application by using explicitly defined Intent targets
Android OS flexible, extensible environment of cooperating, distributed components
Typically, on almost all popular platforms one application can call another application On Android, because of Intents, one applications part can call a part of another application Applications dont have to be aware of each other; an OS resolves Intents dynamically Many Intent Filters defined by system applications
9/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Android runtime local web services"
Loosely coupled components works together by specifying contracts
The same idea that is used in web services and SOA principle
All components and their capabilities of specific applications are described in AndroidManifest.xml file (mandatory application descriptor for OS)
<manifest xmlns:android="http://schemas.android.com/apk/res/android" package="com.example.android.notepad"> <application android:icon="@drawable/app_notes" android:label="@string/app_name" > [...] <activity android:name="NotesList" android:label="@string/title_notes_list"> [...] <intent-filter> <action android:name="android.intent.action.VIEW" /> [...] <data android:mimeType="vnd.android.cursor.dir/vnd.google.note" /> </intent-filter> [...] </activity> [...] </application> </manifest>
Where is the security?
Is the security of lower Android architectures layers spoiled by higher layers?
10/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Android permissions
Permissions as the security boundary between components
All basic applications components (Activities, Services, Content Providers and Broadcast Services) can define specific permission that another component must have granted to use them Every application that uses components with defined permissions must have explicit admission granted by user during applications installation
Components define permissions that they require in AndroidManifest.xml
<permission android:name="com.example.android.notepad.permission.READING_NOTES" android:label="Czytanie danych notatek" android:description="Umoliwia czytanie danych notatek. Zoliwe aplikacje mog wysa te dane osobom trzecim" android:protectionLevel="dangerous" />
Application that want to use components which require permission declares that it uses permission in its AndroidManifest.xml
<manifest xmlns:android="http://schemas.android.com/apk/res/android" package="com.android.app.otherApp" > [...] <uses-permission android:name="com.example.android.notepad.permission.READING_NOTES" /> [...] </manifest>
11/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
How do permissions work?
Applications A component declares in its AndroidManifest.xml that it requires permission
Application B which wants to use applications A component declare in its AndroidManifest.xml file that it uses permissions During installation of application B, OS reads its AndroidManifest.xml file looking for uses-permission declarations. If found, it asks user for granting permission OS shows permission description defined in application A
Application can not to define uses-permission data, but it will cause runtime security error while trying to access protected components
In case of users refusal, OS stops an installation
In case of users acceptance, application is installed and can use capabilities that has just got granted
Problem no control if application uses it in secure way (driving licencse and no road police?) Result: with users acceptance even the malicious software can be installed But it can also be easily uninstalled
12/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Permissions summary
Easy and extensible mechanism for creating security boundary in distributed environment of applications components
Android is very security-strict in its lower layers Even though its higher layers define rich environment of independent, cooperating components
Fully Optional for exposing data/functionality Strictly required for using permissions-protected data/functionality Very convenient to use
Applications developer dont have to create any additional code Declaring permission name and description is sufficient Android OS is responsible for forcing security contract keeping
Perfect solution?
13/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Priviledge escalation attack (1)
Problem: Android OS does not provide transitive permissions checking Attack scenario (technical view)
Application A exposes data/functionality and requires permission P Application B uses As data/functionality and has permission P granted (it declares its usage in AndroidManifest.xml and user has accepted it during Bs installation) In the same time, application B exposes data/functionality that uses permissions-protected applications A data/functionality inside and does not require any permissions Application C does not have permission P to use applications A data/functionality directly Anyway, application C can use data/functionality exposed by application B because B does not require any permissions Application C can use applications A data functionality indirectly with no permissions granted!
Attack scenario (real-life view)
An attacker offer useful application X that uses sensitive data/functionality User grants all permissions to application X; he/she does not know that application X exposes the data/functionality further without requiring any permissions An attacker encourage user to install another application Y that does not need any permissions to be granted User accepts application Y; after installation it can stole/corrupt data
14/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Priviledge escalation attack (2)
Solution (official) Android designers has known about this problem
Explicit, runtime checking permissions mechanism is also present in Android platform Checking must be done by application that uses and exposes data/functionality in the same time (it means application B in naming convention used in this presentation) Very, very bad solution when we expose data/functionality in our application, we must trust the developers of external applications They must not to expose our data/functionality further, or they must check in runtime if other applications using their interfaces has the permission to our application granted We dont have any control of this! The main cause of described problem lies outside of our
Solution (good practices)
application; though, we must rely on a good design of external applications which may be (intentionally or not) spoiled
The most obvious tip: we should not to expose any data/functionality if we really dont have to We can use android:exported property to all application components in our AndroidManifest.xml If set to false for a specific component, it disables external access to this component We can resign for dynamic Intents resolving, defining target components explicitly by class name
Conclusion
Event though there are some traps, building secure Android applications is possible
15/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Security appendix
Cryptography in Android
Full standard packages set from Java SE ready to use with Android SDK Two independent sets of HTTP packages: native Java SE and taken from Apache Foundation All good security coding practices from Java SE can be directly used in Android Java SE cryptography code is fully portable (only performance aspects should be considered) BouncyCastle for Java SE can also be used directly by importing it to project No need for any changes in library no need for separate Android version
Android and malware
Most of the malware must be explicitly installed by user (psychology aspects important for attackers) Only a few vulnerabilities caused by errors in platform itself Unfortunately, updates are Achilles heel of Android There is always the possibility to simply uninstall the whole application (in worst case with safe mode)
The biggest question Google and privacy
Gmail, Calendar, Contacts synchronized with Google Account by default Rich location-based services Voice recognition mechanisms, Face Unlock etc.
Cryptographic Seminar| 16.05.2012r.
16/18
Maciej Olewiski | Android OS mobile applications security model
Summary
Mobile devices are becoming more and more popular
In the same time, they store more and more sensitive, personal data They are very attractive as an attack target Conflicting requirements: environment flexibility, convenient usage and strict security
Android is designed to face those problems and it does it
All applications are sandboxed Very strict security solutions on lower architecture layers Rich, flexible and distributed environment of higher levels Security requirements are met because of two basic mechanisms Explicit data sharing Permissions
Even though there are some known issues, building secure applications are possible and easy
17/18 Cryptographic Seminar| 16.05.2012r.
Maciej Olewiski | Android OS mobile applications security model
Thank you for your attention
Questions, comments?
Cryptographic Seminar| 16.05.2012r.
Das könnte Ihnen auch gefallen
- Android Programming For Beginners: The Ultimate Android App Developer's GuideVon EverandAndroid Programming For Beginners: The Ultimate Android App Developer's GuideNoch keine Bewertungen
- Lamw Framework FundamentalDokument23 SeitenLamw Framework FundamentaljmpessoaNoch keine Bewertungen
- Analysis and Research of System Security Based On AndroidDokument4 SeitenAnalysis and Research of System Security Based On AndroidelvictorinoNoch keine Bewertungen
- Android: An Open Handset Alliance ProjectDokument28 SeitenAndroid: An Open Handset Alliance Projectvishal176Noch keine Bewertungen
- Minds-On: Android: Paulo Baltarejo SousaDokument34 SeitenMinds-On: Android: Paulo Baltarejo SousaJulio Pincay EspinozaNoch keine Bewertungen
- Unit One For Mobile ProgrammingDokument25 SeitenUnit One For Mobile ProgrammingMotiNoch keine Bewertungen
- AndroidDokument47 SeitenAndroidwaeel idreesNoch keine Bewertungen
- Android Sec TutorialDokument36 SeitenAndroid Sec Tutorialnam5Noch keine Bewertungen
- Android Seminar PresentationDokument24 SeitenAndroid Seminar PresentationRajkiran k nNoch keine Bewertungen
- M1 ABCDE-Android IntroductionDokument66 SeitenM1 ABCDE-Android IntroductionAlroy AlmeidaNoch keine Bewertungen
- Android Operating System: by Rajmane Aarti P. (3409) Nandgave Ankita D. (3404)Dokument15 SeitenAndroid Operating System: by Rajmane Aarti P. (3409) Nandgave Ankita D. (3404)aarti1420.scjiotNoch keine Bewertungen
- L4Android: A Generic Operating System Framework For Secure SmartphonesDokument39 SeitenL4Android: A Generic Operating System Framework For Secure SmartphonesirfanzsheikhNoch keine Bewertungen
- Mobile App AssignmentDokument14 SeitenMobile App AssignmentReuben FredrickNoch keine Bewertungen
- Android: An Open Handset Alliance ProjectDokument24 SeitenAndroid: An Open Handset Alliance ProjectMusaab QamarNoch keine Bewertungen
- AndroidDokument23 SeitenAndroidLokesh PaduchuriNoch keine Bewertungen
- What Is Android?: Open Handset AllianceDokument8 SeitenWhat Is Android?: Open Handset AllianceSreenivas Reddy BNoch keine Bewertungen
- What Is AndroidDokument13 SeitenWhat Is AndroidHarshad Dhirajlal SatraNoch keine Bewertungen
- Android Mobile App Pentesting PDFDokument22 SeitenAndroid Mobile App Pentesting PDFGihan AragãoNoch keine Bewertungen
- Introduction To Mobile Computing With Android: Prof. Manish Kumar Joshi, Assistant ProfessorDokument29 SeitenIntroduction To Mobile Computing With Android: Prof. Manish Kumar Joshi, Assistant Professorprincewarrior035Noch keine Bewertungen
- Android The Developers GuideDokument388 SeitenAndroid The Developers GuideKaushal KunalNoch keine Bewertungen
- OSY-Microproject V VDokument20 SeitenOSY-Microproject V VComputer ActivityNoch keine Bewertungen
- Android App DevelopmentDokument191 SeitenAndroid App DevelopmentMallikarjun RaoNoch keine Bewertungen
- 18 Android Secure App DevDokument106 Seiten18 Android Secure App DevnhiNoch keine Bewertungen
- AndroidDokument12 SeitenAndroidSergio Darío LópezNoch keine Bewertungen
- Android Architecture and FrameworkDokument32 SeitenAndroid Architecture and Frameworkmahrukhkhan702Noch keine Bewertungen
- Android Operating System ExampleDokument27 SeitenAndroid Operating System Exampleagas_96panda0% (1)
- Android Application DevelopmentDokument32 SeitenAndroid Application DevelopmentAmi VermaNoch keine Bewertungen
- Unit-1 Hardik Sir SPUDokument57 SeitenUnit-1 Hardik Sir SPUgohar khanNoch keine Bewertungen
- Android Seminar PresentationDokument24 SeitenAndroid Seminar PresentationPiyuSh JainNoch keine Bewertungen
- Android SystemDokument3 SeitenAndroid SystemEdwin NfehNoch keine Bewertungen
- Android Application Development Tutorial: by Chau Ngo EEL 6788-Advanced Topics in Wireless NetworksDokument61 SeitenAndroid Application Development Tutorial: by Chau Ngo EEL 6788-Advanced Topics in Wireless Networksjagdishmehta_onlineNoch keine Bewertungen
- T.Aditya: An Open Handset Alliance ProjectDokument28 SeitenT.Aditya: An Open Handset Alliance ProjectVikram ReddyNoch keine Bewertungen
- Android Vulnerability To Impersonate Trusted ApplicationsDokument4 SeitenAndroid Vulnerability To Impersonate Trusted ApplicationssanjuNoch keine Bewertungen
- Android Security Model That Provide A Base Operating SystemDokument8 SeitenAndroid Security Model That Provide A Base Operating SystemJournal of TelecommunicationsNoch keine Bewertungen
- Android Coexist A Not HerosDokument10 SeitenAndroid Coexist A Not HerosParveen JainNoch keine Bewertungen
- 1.ITU 08104 ModuleDokument14 Seiten1.ITU 08104 Modulesabrina sadickNoch keine Bewertungen
- Android Mobile Operating SystemDokument10 SeitenAndroid Mobile Operating SystemHari RamNoch keine Bewertungen
- 18ai63 Module4Dokument40 Seiten18ai63 Module4Varshini RavikumarNoch keine Bewertungen
- R20EP094Dokument25 SeitenR20EP094King KingNoch keine Bewertungen
- Mad Part 1 NotesDokument10 SeitenMad Part 1 NotesVeeresh NikeeNoch keine Bewertungen
- Debremarkos Institute of Technology Mobile Programming History and Overview of Mobile Application DevelopmentDokument38 SeitenDebremarkos Institute of Technology Mobile Programming History and Overview of Mobile Application DevelopmentAmi NegnNoch keine Bewertungen
- A Short Introduction To Android: 95-702 Distributed SystemsDokument38 SeitenA Short Introduction To Android: 95-702 Distributed SystemsSasi KiranNoch keine Bewertungen
- Strategies in Improving Android SecurityDokument16 SeitenStrategies in Improving Android SecurityJaxon JaitlyNoch keine Bewertungen
- Introduction To Android DevelopmentDokument22 SeitenIntroduction To Android DevelopmentKainda Charlie DakaNoch keine Bewertungen
- Andriod OSDokument19 SeitenAndriod OSعلي محمود علي عاصيNoch keine Bewertungen
- What Is Android?Dokument13 SeitenWhat Is Android?Bharat HazarikaNoch keine Bewertungen
- A Review On Android Security Threats: Abhishek Tiwari, Mansi Mishra Pragya KamalDokument4 SeitenA Review On Android Security Threats: Abhishek Tiwari, Mansi Mishra Pragya KamalAbhishek TiwariNoch keine Bewertungen
- What Is An Android Operating SystemDokument3 SeitenWhat Is An Android Operating Systemdina.haziahmetova2000Noch keine Bewertungen
- Paper Presentation On AndriodDokument8 SeitenPaper Presentation On AndriodVenkat VeeraNoch keine Bewertungen
- Technical Seminar ReportDokument25 SeitenTechnical Seminar ReportVinod KoolNoch keine Bewertungen
- MAD All Chapter Q and ADokument169 SeitenMAD All Chapter Q and Aminari9400Noch keine Bewertungen
- Assignment On Android OSDokument28 SeitenAssignment On Android OSFahad KhanNoch keine Bewertungen
- Unit I PDFDokument13 SeitenUnit I PDFGopalNoch keine Bewertungen
- AndroidDokument14 SeitenAndroidVenkat CharyNoch keine Bewertungen
- Moblie Application DeveopmentDokument66 SeitenMoblie Application DeveopmentRashmee NavodaNoch keine Bewertungen
- Syllabus of Mobile Application DevelopmentDokument8 SeitenSyllabus of Mobile Application DevelopmentSufyan HassanNoch keine Bewertungen
- Android SecurityDokument18 SeitenAndroid Securitymloveyou250% (2)
- Android NotesDokument10 SeitenAndroid NotesMuhammad hamza0% (1)
- Google Android A Comprehensive Security Assessment From IEEEDokument10 SeitenGoogle Android A Comprehensive Security Assessment From IEEEgreg788Noch keine Bewertungen
- Android DescriptionDokument19 SeitenAndroid DescriptionpranithNoch keine Bewertungen
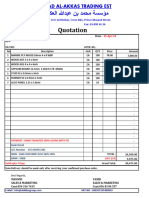
- CatalogDokument22 SeitenCatalogghazi4uNoch keine Bewertungen
- QTN - 1843Dokument1 SeiteQTN - 1843ghazi4uNoch keine Bewertungen
- receipt (4)Dokument1 Seitereceipt (4)ghazi4uNoch keine Bewertungen
- receipt (14)Dokument5 Seitenreceipt (14)ghazi4uNoch keine Bewertungen
- GE THN3364R Specification SheetDokument2 SeitenGE THN3364R Specification Sheetghazi4uNoch keine Bewertungen
- Sa09c2 Jve 04 XX DR Ce 00002Dokument15 SeitenSa09c2 Jve 04 XX DR Ce 00002ghazi4uNoch keine Bewertungen
- Sa09c2 Jve 27 XX DR Ce 00002Dokument9 SeitenSa09c2 Jve 27 XX DR Ce 00002ghazi4uNoch keine Bewertungen
- EL-004 Rev 01Dokument1 SeiteEL-004 Rev 01ghazi4uNoch keine Bewertungen
- Ithra - Projector Room - Civil-TOWER 06-TOWER 05 - Transformer fond-TOWER 05 - CivilDokument1 SeiteIthra - Projector Room - Civil-TOWER 06-TOWER 05 - Transformer fond-TOWER 05 - Civilghazi4uNoch keine Bewertungen
- Sa09c2 Jve 33 XX DR Ie 00002 1Dokument12 SeitenSa09c2 Jve 33 XX DR Ie 00002 1ghazi4uNoch keine Bewertungen
- Ithra - Projector Room - Civil-TOWER 06Dokument1 SeiteIthra - Projector Room - Civil-TOWER 06ghazi4uNoch keine Bewertungen
- El 004Dokument1 SeiteEl 004ghazi4uNoch keine Bewertungen
- El 005Dokument1 SeiteEl 005ghazi4uNoch keine Bewertungen
- Revised CGHS Rates For Empanelled Hospitals Under CGHS AhmedabadDokument28 SeitenRevised CGHS Rates For Empanelled Hospitals Under CGHS Ahmedabadghazi4uNoch keine Bewertungen
- Revised AIS Rule Vol I Rule 13 PDFDokument209 SeitenRevised AIS Rule Vol I Rule 13 PDFghazi4uNoch keine Bewertungen
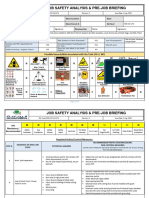
- Risk Assessment P3 Permanent Power Provision at IthraDokument2 SeitenRisk Assessment P3 Permanent Power Provision at Ithraghazi4uNoch keine Bewertungen
- Blackmagic Design DeckLink Studio 2 BDL-BDLKSTUDIO2 - N2142 B&HDokument5 SeitenBlackmagic Design DeckLink Studio 2 BDL-BDLKSTUDIO2 - N2142 B&Hghazi4uNoch keine Bewertungen
- Invoice of ConduitDokument1 SeiteInvoice of Conduitghazi4uNoch keine Bewertungen
- Government of NCT of Delhi Delhi Subordinate Services Selection Board Fc-18, Institutional Area, Karkardooma, DelhiDokument3 SeitenGovernment of NCT of Delhi Delhi Subordinate Services Selection Board Fc-18, Institutional Area, Karkardooma, Delhighazi4uNoch keine Bewertungen
- JSA-174.Confined Space EntryDokument3 SeitenJSA-174.Confined Space Entryghazi4u100% (1)
- 20PLUS Share Stock MarketDokument6 Seiten20PLUS Share Stock Marketghazi4uNoch keine Bewertungen
- Payslip 042018Dokument1 SeitePayslip 042018ghazi4uNoch keine Bewertungen
- Letterhead Template 13Dokument1 SeiteLetterhead Template 13ghazi4uNoch keine Bewertungen
- Letterhead Template 01Dokument1 SeiteLetterhead Template 01ghazi4uNoch keine Bewertungen
- BMSOverview PDFDokument15 SeitenBMSOverview PDFHafizah EzaniNoch keine Bewertungen
- Air Testing Formats (Banas Dairy)Dokument11 SeitenAir Testing Formats (Banas Dairy)ghazi4uNoch keine Bewertungen
- MEP Lead Engineer 150517Dokument50 SeitenMEP Lead Engineer 150517ghazi4uNoch keine Bewertungen
- Letterhead Template 22 FBG01Dokument1 SeiteLetterhead Template 22 FBG01ghazi4uNoch keine Bewertungen
- Bootstrap 4 - Quick Guide - Tutorialspoint PDFDokument25 SeitenBootstrap 4 - Quick Guide - Tutorialspoint PDFSupriyo PalNoch keine Bewertungen
- b0193mq MDokument148 Seitenb0193mq MReinaldo Andres Castillo JopiaNoch keine Bewertungen
- Handling Examination QuestionsDokument12 SeitenHandling Examination QuestionsBricious Mulimbi100% (1)
- Intellecta Design Free Fonts LicenseDokument88 SeitenIntellecta Design Free Fonts LicenseMapan58Noch keine Bewertungen
- (How To) MSI True Color Installation GuideDokument4 Seiten(How To) MSI True Color Installation GuideStereo PodNoch keine Bewertungen
- User Instructions For This CD-ROMDokument1 SeiteUser Instructions For This CD-ROMErick OlavarriaNoch keine Bewertungen
- User Manual: Ingest SchedulerDokument80 SeitenUser Manual: Ingest SchedulerTenNoch keine Bewertungen
- 12 - Create ISE Guest Account As A Sponsor - Part 3Dokument1 Seite12 - Create ISE Guest Account As A Sponsor - Part 3Nguyen LeNoch keine Bewertungen
- Archana Verma: Mobile: +91-8860609753 Carrier ObjectiveDokument2 SeitenArchana Verma: Mobile: +91-8860609753 Carrier Objectivevibha sharmaNoch keine Bewertungen
- Gems Release NotesDokument8 SeitenGems Release NotesTessfaye Wolde GebretsadikNoch keine Bewertungen
- Licensing Brief PLT Microsoft Qualified Devices and Qualified UsersDokument4 SeitenLicensing Brief PLT Microsoft Qualified Devices and Qualified UsersShahimNoch keine Bewertungen
- Exercises GIT Basics PDFDokument14 SeitenExercises GIT Basics PDFCosticã Pardaillan LupuNoch keine Bewertungen
- Uploading Data From Access To SQL ServerDokument12 SeitenUploading Data From Access To SQL ServerExpert TutorNoch keine Bewertungen
- SJ BoyDokument4 SeitenSJ Boyrimon420Noch keine Bewertungen
- Sameer Kumar Web FileDokument50 SeitenSameer Kumar Web Filejoy8193kNoch keine Bewertungen
- Cisco Jabber - MRA and SSODokument16 SeitenCisco Jabber - MRA and SSOkepke86Noch keine Bewertungen
- Webuser - 28 June 2012Dokument76 SeitenWebuser - 28 June 2012Demir SolakNoch keine Bewertungen
- Personal Details: Yogita R. KanawadeDokument4 SeitenPersonal Details: Yogita R. Kanawadeyogita shelkeNoch keine Bewertungen
- Read MeDokument13 SeitenRead MeHaiDangNoch keine Bewertungen
- Group 7 PresentationDokument32 SeitenGroup 7 PresentationSushma VegesnaNoch keine Bewertungen
- ONVIF Profile G Specification RCDokument20 SeitenONVIF Profile G Specification RCOscar Orlando Sánchez FlórezNoch keine Bewertungen
- NVS Getting Access To On Premises Apps and Resources With Microsoft TunnelDokument15 SeitenNVS Getting Access To On Premises Apps and Resources With Microsoft TunnelSubash AcharyaNoch keine Bewertungen
- Cloud Security and Virtualized-HimaniDokument19 SeitenCloud Security and Virtualized-HimanimanishNoch keine Bewertungen
- Retouching GuidelinesDokument8 SeitenRetouching GuidelinesDc Lovensky JnNoch keine Bewertungen
- Hummingbird Deployment Wizard: User's GuideDokument72 SeitenHummingbird Deployment Wizard: User's GuideFrancoHermosillaFerreiraNoch keine Bewertungen
- ADVANCED SEO Syllabus (Course Start Soon) PDFDokument9 SeitenADVANCED SEO Syllabus (Course Start Soon) PDFmaniNoch keine Bewertungen
- EvoTv Quick Start GuideDokument24 SeitenEvoTv Quick Start GuideRakesh SharmaNoch keine Bewertungen
- Presentasi APP1Dokument14 SeitenPresentasi APP1Quintari WuriastutiNoch keine Bewertungen
- Reporting SamplesDokument7 SeitenReporting SamplesSamuel Vanger0% (1)
- Easy Mikrotik HotSpot SetupDokument5 SeitenEasy Mikrotik HotSpot SetupBoy EloadNoch keine Bewertungen