Beruflich Dokumente
Kultur Dokumente
GPS Spoofing
Hochgeladen von
spunkettedivine0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
73 Ansichten5 SeitenPaper on GPS Spoofing
Copyright
© Attribution Non-Commercial (BY-NC)
Verfügbare Formate
PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenPaper on GPS Spoofing
Copyright:
Attribution Non-Commercial (BY-NC)
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
73 Ansichten5 SeitenGPS Spoofing
Hochgeladen von
spunkettedivinePaper on GPS Spoofing
Copyright:
Attribution Non-Commercial (BY-NC)
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 5
GPS Spoofing Attack on Time Synchronization in
Wireless Networks and Detection Scheme Design
Qi Zeng, Husheng Li and Lijun Qian
Abstract-In this paper, we introduce a GPS spoofing attack
on the time synchronization in wireless networks. As a case study,
the frequency hopping code division multiple access (FH-CDMA)
based ad hoc network relying on the GPS signal is investigated.
The GPS spoofing attack, which is more malicious than other
attacks such as jamming, could lead to the loss of network-wide
synchronization as well as the loss of synchronization in FH
code. The performance degradation in terms of symbol error
rate (SER) of the FH-CDMA based ad hoc network under
such an attack is evaluated. Then, to detect the spoofing attack
we propose to employ a quick detection technique,
i.e., CUSUM test algorithm, by observing the dynamic range of
the successful detection rate. Simulation results show that GPS
spoofing attack on network performance is a long-term impact
and more pernicious threat compared to the jamming; moreover,
our proposed CUSUM scheme is an effective method to detect
the GPS spoofing attack.
I. INTRODUCTION
Global position system (GPS) has been widely employed
in a variety of wireless applications, e.g., mobile ad hoc
network, cellular phone network, smart grid and so forth, since
it could provide many desired features, including localization,
navigation and time synchronization. However, GPS signals
are susceptible to jamming and spoofing attack. Compared
with jamming, the spoofing attack is a more pernicious attack
because it makes the GPS receivers in the attack range to
believe the fake GPS signals sent by the spoofer, without any
alert to suggest that an attack is underway.
GPS spoofing attack is becoming a hot topic in recent years.
In [1] and [2], the authors demonstrated a experiment and
a practical GPS spoofer to test how easily a civilian GPS
receiver could be spoofed, respectively. In [3], a low cost GPS
spoofer is designed and the performance effect on the carrier
and code level is analyzed. Besides civilian GPS receiver,
spoofing attack is also a critical problem for the military
GPS receiver. In [6], an attacker can manipulate the arrival
times of military GPS signals by pulse-delaying or replaying
individual navigation signals with a delay, although advanced
cryptography and new keying architecture are employed in the
modernized military GPS design known as "M code" [16].
Recently in [4], the requirements for successful GPS spoofing
attacks on the military GPS receiver are investigated. From the
Q. Zeng and H. Li are with the Department of Electrical Engineering
and Computer Science, the University of Tennessee, Knoxville, TN 37996
(email: qi.zeng82@gmail.com; husheng@eecs.utk.edu). L. Qian is with the
Department of Electrical and Computer Engineering, Prairie View A&M
University, Prairie View, TX 77446 (email: liqian@pvamu.edu).This work
was supported in part by the National Science Foundation under grants CCF-
0830451 and ECCS-0901425, and by the US Army Research Office under
grant W911NF-12-1-0054.
978-1-4673-3/12/$31.00 2013 IEEE
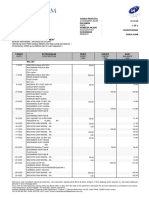
Fig. 1. The model of FH-CDMA based ad hoc network relying on the GPS
system.
view of countermeasures to the spoofing attack, the approaches
which range from the cryptographic authentication to modifi-
cations of the GPS signal or the infrastructure are proposed in
[5], [6]. However, such approaches are unlikely implemented
in the near future due to the high cost and the long deployment
cycles, and spoofing military GPS is nonetheless a concern in
addition to civilian GPS spoofing.
In this paper, we investigate the impact of the GPS spoofing
attack on wireless communication networks. As a case study
for military communications, we focus on FH-CDMA based
ad hoc networks [7], [8], where all nodes usually need to
synchronize to an external clock, such as GPS signal. The
network infrastructure is shown in Fig. 1. In this network,
we propose to employ a novel general orthogonal FH code,
i.e., no-hit-zone code [13], to the neighboring nodes in order
to mitigate the interference, which is similar to the idea of
[8]. The impact of GPS-based synchronization degradation on
other cellular networks (i.e., CDMA, GSM and UMTS) could
be found in [17].
The network-wide time synchronization is extremely crucial
for successful transmission in FH-based ad hoc netowrks,
because it renders the transmission pair to simultaneously
switch to the next frequency channel. In order to achieve the
accurate network-wide time synchronization, we assume that
each node is equipped with a GPS receiver and is synchronized
to the GPS signal, Due to the GPS spoofing attack, the FH
codes of victim nodes will be out of synchronization, which
leads to the serious collision of hopping frequency. Therefore,
one of the issues in this paper is to evaluate the performance
degradation in terms of symbol error rate (SER) due to the
GPS spoofing attack.
It should be noted that jamming (or poor channel quality)
could result in performance degradations as well as the GPS
spoofing attack does, although there exist some critical dif-
ferences. Jamming only impacts a small portion of spectrums
due to the random hopping, which will lead to the short-term
impact on the performance. As to the GPS spoofing attack,
the transceivers cannot detect such an attack and still falsely
trust each other. Therefore, the spoofing attack is usually a
long-term and more pernicious threat. Thus, the other issue
in this paper is to find an efficient method to detect the GPS
spoofing attack and to distinguish from the jamming, To the
authors' best knowledge, there have not been any studies on
the GPS spoofing in communication networks.
Based on the idea similar to the quickest detection for
the abrupt changes, we adopt the well-known cumulative
sum (CUSUM) testing algorithm to detect the GPS spoofing
attack by observing the fluctuation range of the successful
detection rate [9]. The CUSUM detection method has been
extensively studied in a variety of applications, e.g., detecting
selfish occupancy of wireless resource [10], detecting the data
injection attack on smart grid [11] and so forth.
The remainder of this paper is organized as follows. The
system model and signal analysis are provided in Section II.
The CUSUM test for detecting the GPS spoofing is discussed
in Section III. Numerical simulations and conclusions are
provided in Sections IV and V, respectively.
II. SYSTEM MODEL AND SIGNAL ANALYSIS
In this section, we focus on FH-CDMA based ad hoc
wireless networks, where the network-wide time synchroniza-
tion is achieved by relying on the GPS system. Firstly, we
introduce the basic infrastructure of FH-CDMA based ad hoc
network and analyze the impact of GPS spoofing attack on FH
code synchronization. Then, we investigate the performance
degradation in terms of SER due to the GPS spoofing attack
on the time synchronization.
A. The System Model under the GPS Spoofing Attack
The structure of FH-CDMA based ad hoc network is shown
in Fig. 1. In this network, the nodes are distributed in the plane
according to a Poisson point process. Each node synchronizes
to an accurate clock which is provided by GPS. We only focus
on the next neighbor transmission to investigate the impact of
the spoofing attack on the system performance.
In the physical layer, all the co-located nodes in the neigh-
boring area are assumed to have been pre-assigned unique sig-
nature FH codes which they use to modulate their information
symbols. The signature FH code of node k is denoted by C
Ck
).
To mitigate the multiple access interference (MAl) resulting
from the neighborhood nodes, a novel general orthogonal FH
code, i.e., no-hit-zone (NHZ) code, is proposed for FH-CDMA
Fig. 2. The model of FH-CDMA transceiver.
based ad hoc networks in this paper. The reason for using such
an FH code is that NHZ code could improve the immunity to
the slight time imperfect synchronization due to its specific
Hamming correlation properties, compared with other FH
codes. Some design algorithms of general orthogonal codes
and their Hamming correlation properties could be found in
[13].
For the ad hoc network investigated in this paper, a spoofer,
which is placed near the target nodes, receives the genuine
GPS signal and forges the fake one. The victim nodes could
falsely track to the forged GPS signal via the spoofing attack
method stated in [2]. We assume that the time synchronization
of nodes within a certain area near the spoofer, which is shown
as the dashed circle in Fig.l, is affected by this spoofer. The
size of such area depends on the power of the spoofer. The
area of neighbor transmission, which is denoted by the solid
circle in Fig.l, contains the nodes suffering or not suffering
from the spoofing attack. Each paired source-destination node
employs the unique NHZ code to reduce the MAL
The paired transceiver structure for source-destination nodes
in the physical layer is shown in Fig.2. The wireless channel
between two arbitrary nodes is assumed to be a slow Rayleigh
fading. In the transmitter, the information bits are firstly
modulated by l'v1-ary FSK and the central frequency of MFSK
symbol then hops to the designated frequency slot according
to the pre-assigned FH code. In the receiver, the received
signal is orderly processed through the dehopper, non-coherent
demodulator and decoder. The non-coherent demodulator for
the MFSK signal is specified in detail in [14].
B. Signal Analysis for SER performance
In this subsection, the expressions of SER analysis are
derived for the FH-CDMA based ad hoc network with l'v1-ary
FSK modulation. By using these expressions, semi-analytic
Monte Carlo simulations are then performed to estimate the
impact on error probability due to the GPS spoofing attack.
Before we analyze the signal model, some definitions of the
notations are firstly listed as follows.
K: the total number of source nodes in the neighboring
area, including the nodes which are synchronized to the
genuine GPS signal and the victim nodes which are
synchronized to the fake one.
d
C
k) ( n): one l'v1-arysymbol transmitted by the k- th node
during the n-th symbol interval.
c ~ ~ : one frequency hopping slot used by the k-th node
during the n-th symbol interval, which depends on the
assigned NHZ FH code set.
1]: the complex additional white Gaussian noise (AWGN)
with the two-sided power spectral density of N
o/2.
J2S(k): the received signal amplitude of the k-th node
under the independent Rayleigh fading channel with the
mean square value 20.
'Tk: the time offset of the k-th node caused by the GPS
spoofing attack. Actually, 'Ti is restricted by the maximum
value D which depends on the resolution of the crystal
oscillator of the local clock [2].
For the simplicity of analysis, it is assumed that one AI-
ary FSK symbol is sent per hop in this paper. In order
to mitigate the inter-symbol interference, the frequency of
signals maintains the orthogonality by setting the minimum FH
frequency spacing to AI ITs, where T; denotes the duration of
one AI-ary symbol. Then, the complex received signal during
the n-th symbol interval can be written as
r(t) = V2SCk)F
T s
(t-Tk -nT,) exp[j(21Tde';;n) t
+271" +",. (1)
A non-coherent demodulator is adopted in the paper. Then,
in the receiver of the destination node, the decision variable in
the l-th branch of the AI matched filters (l == 0, 1, ... ,AI -1)
observed during the n-th interval is computed as follows [15].
f dCk)=l
IWl(n)I==) ",K (k)() I (k) , (2)
l Lk:=l;k;fS I
l
ri +Vl , d =l=-l
where reS) follows i.i.d. Rayleigh distribution with PDF
frCk) (:) == 2: exp( _:2) for k == 1,2, , K. \7,\S) ==
8( , Pk+8( (1 - Pk), which the
impact of GPS attack on the desired signal. The maximum
time offset D caused by GPS spoofing attack is equal to
NkT+PkTs, where Ni. is an integer and Pk follows a uniform
distribution within [0,1]. For the special case when there does
not exist any GPS attack and all nodes are well synchronized to
genuine GPS signals, is constantly equal to 1. fl>k == rt+Nk
is the symbol interval index of the k-th interfering node after
suffering from the spoofing attack, which depends on the
maximum time offset D. The function (z , y) == 1 for a: == y;
otherwise, ()(:, y) == O. Vl is a complex AWGN with mean zero
and variance Nol E
s
and the average energy of one symbol
E; == Tn. The total MAl Il(k) due to the k-th interfering node
could be rewritten as
(3)
where
(k} (k) (k) . . .
Il_\n)== t1
h
r sznc(Pk(}l-)Pk exp(J (7rPk(}l_+cp(k))),(4)
(n) r(k) sinc((}l+ (1-Pk)) (l-Pk)
X exp(j (1r(}l+(Pk+1)+cp(k)))_ (5)
Fig. 3. The impact on SERperformance due to the jamming and the GPS
spoofing attack.
I (4) d (5) A (k) _ (S))_ (k)
n an ,u
h
-uC'h ,Cn ,(}l-==ri (nk)-land
(}l+ == ri(k) (nk + 1)-l. The function sinc(:) == sin(71"X) I (7rx)
if a: =I=- 0 and sinc(:) == 1 if a: == O. The detailed derivations
of (3)-(5) are similar to the work in [12], which is omitted in
this paper due to the limited space.
In order to demonstrate the performance difference between
the GPS spoofing attack and the jamming, the SERs of FH-
based ad hoc network with AI-ary FSK modulation for AI == 4
and 8 are shown in Fig. 3. We assume that the GPS spoofing
attack occurs at the time instant t == 100 and the jamming
occurs at t == 50. Besides, the number of victim nodes is equal
to 5 and the maximum time offset D due to GPS spoofing
attack is assumed to be 3 chip-slots. From the simulation
results, it is obtained that the system performance under
jamming is temporarily degraded, then will likely get better in
the next time slot due to the fact that frequency is hopped from
the jammed channel into the good one. However, under the
GPS spoofing attack, the system consistently remains at the
poor performance level. The symbol detection rate obtained
from the simulation is utilized as the observation in CUSUM
testing algorithm in the next section.
III. DETECTION OF GPS SPOOFING
The CUSUM algorithm is a promising method to quickly
find abrupt changes in a process when there is an unknown
parameter in the post-change distribution and this parameter
may be varying during the detection process. Due to the
abrupt GPS spoofing attack, the time when the GPS spoofing
attack occurs, which is denoted by to, is unknown. The other
parameter, i.e., the probability of frequency collisions (hit-rate)
() after spoofing, is unknown as well. The nodes which suffer
from the attack are out of the FH code synchronization. It will
result in the increase for MAl and the abrupt degradation for
performance.
For the simplicity of analysis in detection scheme, it is
The standard statistical approach is to use the maximum
likelihood estimates of these two parameters, which leads to
the decision function given by
By using the proposed CUSUM testing algorithm, the net-
work will raise the alarm at the to-th time instant to inform that
the network is attacked by GPS spoofer. Also, the estimated
value of another parameter () after change is denoted by {}I,
which can be obtained from (10).
IV. SIMULATION RESULTS
In this section, we present the simulation results to demon-
strate the performance of the proposed detection scheme. In
the FH-CDMA based ad hoc network, the NHZ FH code
set, which is designed via the algorithm in [13], is pre-
assigned to the neighboring nodes and binary FSK modulation
is considered. In all the following results, it is assumed that
the GPS spoofing attack occurs at the lOOth observation (i.e.,
to== 100) and the time offset due to the spoofing attack could
go beyond the no hit zone. The performance for the proposed
detection scheme is considered in terms of the false alarm rate
and detection delay.
Fig. 4 shows the false alarm rate versus the CUSUM
decision threshold (h) for the various signal-to-noise ratios
(SNRs). As observed from the figure, with the fixed SNR in
each curve, the false alarm rate deceases when h increases. It
is also found that, as the false alarm rate is fixed, the detection
scheme for the system with large SN R needs a lager threshold
h than that for the small SNR system. It is due to the fact
that the system with large SN R results in the increase of gk
in (10), thus increases the threshold h as well.
Fig. 5 shows the relation between the threshold hand SNR
for some given false alarm rates (0.01 and 0.001). From this
figure, we could obtain the optimal threshold for the CUSUM
scheme corresponding to the SNRs so that the false alarm
rate reaches the expected level. For the given SNR, the false
alarm rate will become a smaller value with increase of h;
however, it will result in the degradation of another detection
performance, i.e., average detection delay, of which results will
be specified in Fig.6.
Fig. 4. The false alarm rate versus the CUSUM decision threshold h for the
various S N Rs.
(9)
(7)
(12)
(10)
unknown OI , (8)
to == n1in{k: s h}.
Ho
reasonable to assume that the detection for a packet is failed if
the frequency hit occurs during the packet interval; otherwise,
the detection is successful. With this assumption, we can
obtain the acceptable level of detection performance. Denote
by Y'i E {O, I}(i == 1,2, ..., N) the independent observation of
detection for packet at the i-th time slots in the FH-CDMA
based ad hoc network, where
{
I , successful detection
Y'i == 0, failed detection (6)
The probability of Y'i, which is denoted by PO(Y'i), belongs
to an unknown hit-rate () with a space 8. The space 8
is determined by both the pre-assigned FH code and the
maximum time offset D.
NHZ FH code has the capability to combat the slight time
offset, which leads to hit-free (() == 0); however, as the GPS
spoofing attack occurs, it will result in the severe hit-rate due
to fact that the time offset exceeds the no-hit zone. When
spoofing attack occurs, the hit-rate is denoted by ()I. As stated
above, the probability densities PO(Y'i) for these two cases
could be written as, respectively,
{
Poo(l) == PT
()o == 0 ,
POo(O) == 1 - PT
{
POI (1) == (1 - OI)PT
POI (0) == 1 - (1 - OI)PT
where PT denotes as the rate of correct detection when there
is hit-free (0
0
== 0), which depends on the fading channel
and noise. Actually, the value of PT depends on the channel
condition, the characteristic of the spoofer and so forth, which
is obtained by observing the symbol detection rate in the
real testing or the experiment. From the above equations, we
assume the distribution of Y'i is changed from 0
0
to (}I at the
unknown time instant to, where (}I is unknown as well but lies
in the space 8. We propose to adopt the CUSUM algorithm to
estimate the unknown parameters to and (}I. Correspondingly,
we compute the log-likelihood ratio with the CUSUM method
for the observation Y'i from time j up to time k, which is given
by
gk == max sup S](OI)'
I::;j::;k 8
1
ES
Then the decision rule is written as
{
Ho chosen; " gk < h (11)
HI IS chosen; If s h
where h is a pre-determined threshold. The alarm time for
the GPS spoofing attack is obtained by the following stopping
rule:
Fig. 5. The relation between the threshold hand SNR for some false alarm
rates (0.01 and 0.001).
Fig. 6. The The average detection delay of our proposed scheme under
different threshold hs.
The average detection delays of our scheme under different
thresholds are shown in Fig. 6 for the various SNR==5, 10,15
and 20dB. In the simulations, the average delay is defined as
E{lio-tol}. It is observed that, for the small SNR( <15dB),
the detection delay increases with the threshold; however, for
a larger SNR(> 15dB), the average detection delay is only
marginally dependent on the threshold. It should be noted that
the above phenomenon should exclude the range of small h
(h < 1).
v. CONCLUSIONS
In this paper, we have studied the impact of GPS spoofing
attack on the performance of FH-CDMA ad hoc network.
This network relies on the GPS signal to realize the network-
wide synchronization. The GPS spoofing attack is a type of
malicious threat, which leads to the loss of the network-
wide synchronization. Under such an attack, our investigated
network suffers from more severe performance degradation
than the jamming does. Then, we have proposed the CUSUM
detection scheme for determining the occurrence of GPS
spoofing attack as quickly as possible. Finally, we presented
simulation results that demonstrate the performance of the
CUSUM based detection scheme. It should be noted that the
proposed CUSUM scheme and framework of analysis are still
available for other wireless communication systems which are
vulnerable to the GPS spoofing attack, not limited to FH-
CDMA based ad hoc network. Based on the results obtained
in this paper, the countermeasure to the GPS spoofing attack
will be studied in our future works.
REFERENCES
[1] J. S. Warner and R. G. Johnston, ''A simple demonstration that the global
positioning system (GPS) is vulnerable to spoofing", Journal of Security
Administration, pp.1-9, 2002.
[2] T. E. Humphreys, B. M. Ledvina, M. L. Psiaki and et al., "Assessing the
spoofing threat: development of a portable GPS", in Proc. of the ION
GNSS Conference, The Institute of Navigation, Savanna, Georgia, Sept.
2008.
[3] B. Motella, M. Pini, M. Fantino and et al., "Performance assessment of
low cost GPS receivers under civilian spoofing attacks", in Proc. of ESA
Workshop on Satellite Navigation Technologies and European Workshop
on GNSS Signals and Signal Processing, Noordwijk, Dec. 2010.
[4] N. O. Tippenhauer, C. Popper, K. B. Rasmussen and et al., "On the
requirements for successful GPS spoofing attacks", in Proc. of the ACM
Conference on Computer and Communications Security, Chicago, IL, Oct.
2011.
[5] B. M. Ledvina, W. J. Bencze, B. Galusha and et al., "An in-line anti-
spoofing device for legacy civil GPS receivers", in Proc. of the ION
international Technical Meeting, San Diego, CA, 2010.
[6] M. G. Kuhn, ''An asymmetric security mechanism for navigation signals",
in Proc. of the International Information Hiding Workshop, Toronto,
Canada, 2004.
[7] T. Vanninen, M. Raustia, H. Saarnissaari and et al., "Frequency hopping
mobile Ad hoc and sensor network synchronization", in Proc. of IEEE
Military Communications Conference (Milcom 2008), San Diego, CA ,
Nov. 2008.
[8] J. Elsner, R. Tanbourgi and F. K. Jondral, "Multiple access interference
mitigation through multi-level locally orthogonal FH-CDMA", in Proc.
of IEEE Military Communications Conference (Milcom 2011), Baltimore,
MD, Nov. 2011.
[9] M. Basseville, I. V. Nikiforov, Detection of Abrupt Changes: Theory and
Application, Prentice Hall, New Jersey, 1993.
[10] C. Liu, O. W.W.Yang, Y. Shu and et al., "Sliding window non-parametric
cumulative sum: a quick algorithm to detect selfish behavior in wireless
networks", lET Commun., Vol.5, no.15, pp.230-2140, 2010.
[11] Y. Huang, H. Li, K. A. Campbell and et al., "Defending false data
injection attack on smart grid network using adaptive CUSUM test", in
Proc.of Conferece on Information Sciences and Systems (CISS 2011),
Baltimore, ML, Mar. 2011.
[12] Q. Zeng, D. Peng and X. Wang, "Performance of a novel MFSKfFHMA
system employing no-hit zone sequence set over Rayleigh fading chan-
nel," IEICE Trans. Commun., vol. E94-B, no.2, pp. 526- 532, Feb. 2011.
[13] W. X. Ye, P. Z. Fan and E. M. Gabidulin, "Construction of non-repeating
frequency-hopping sequences with no-hit zone," Electronics Lett., vol. 42,
no. 12, pp. 681-682, Jan. 2006.
[14] M. K. Simon, J.K. Omura and R. A. Scholtz and et al. Spread Spectrum
Communications Handbook, McGraw-Hill, New York, 2001.
[15] K. Choi and K. Cheun, "Performance of asynchronous slow frequency-
hop multiple-access networks with MFSK modulation," IEEE Trans.
Commun., vol. 48,no. 2 pp.298-307, Feb. 2000.
[16] B. Barker, J. Betz and et al. "Overview of the GPS M code signal,"
Proceedings of the 2000 National Technical Meeting of The Institute of
Navigation, pp.542-549, Anaheim, CA, Jan. 2000.
[17] F. A. Khan and A. G. Dempster, "Impact of GPS-based synchronization
degradation on cellular networks," Symposium of the 2007 International
Global Navigation Satellite Systems (IGNSS 2007), pp.1-11, Sydney,
Austrilia, Dec. 2007.
Das könnte Ihnen auch gefallen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (120)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- WCF TutorialDokument104 SeitenWCF TutorialBozsóki IstvánNoch keine Bewertungen
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Home Security Alarm System Using Arduino Project Report PDFDokument17 SeitenHome Security Alarm System Using Arduino Project Report PDFprassanth jaiNoch keine Bewertungen
- Diffentian Transformer ProtectionDokument227 SeitenDiffentian Transformer ProtectionHuget St100% (3)
- Omron PLC & Remote Io - Cat2014Dokument40 SeitenOmron PLC & Remote Io - Cat2014Awidhi KresnawanNoch keine Bewertungen
- Aci sp-215-2003Dokument446 SeitenAci sp-215-2003Abigael Valles RamirezNoch keine Bewertungen
- 7 ITIL 4 FN GlossaryDokument9 Seiten7 ITIL 4 FN Glossarypavithra chinniNoch keine Bewertungen
- Synthesis PaperDokument12 SeitenSynthesis Paperapi-446695789Noch keine Bewertungen
- Remote Access - Students PDFDokument2 SeitenRemote Access - Students PDFMae RupidoNoch keine Bewertungen
- TBQ C Evaluation Requirement (Consultant) - Uni VersionDokument2 SeitenTBQ C Evaluation Requirement (Consultant) - Uni VersionAmanda MohNoch keine Bewertungen
- Mausam: Project Proposal OnDokument14 SeitenMausam: Project Proposal OnHyy NepalNoch keine Bewertungen
- ProjectDokument12 SeitenProjectOmkar TerkhedkarNoch keine Bewertungen
- Introduction To Managemenet Information System: Unit - 4Dokument22 SeitenIntroduction To Managemenet Information System: Unit - 4Vinodh Kumar LNoch keine Bewertungen
- Anna University Tiruchirappalli Tiruchirappalli - 620 024: Regulations 2007 Curriculum M.E. Software EngineeringDokument31 SeitenAnna University Tiruchirappalli Tiruchirappalli - 620 024: Regulations 2007 Curriculum M.E. Software EngineeringRevathy GmNoch keine Bewertungen
- Types of ComputerDokument41 SeitenTypes of ComputerAngelita CapagalanNoch keine Bewertungen
- Dibaj Azhar Nano AssignmentDokument4 SeitenDibaj Azhar Nano Assignmentdiba azharNoch keine Bewertungen
- Mini Project EEE PDFDokument7 SeitenMini Project EEE PDFAmit Kr SinghNoch keine Bewertungen
- 700 RTU User ManualDokument81 Seiten700 RTU User ManualSunny Jun PaclibarNoch keine Bewertungen
- 3-Channel Differential Line Driver Ic - VXDokument11 Seiten3-Channel Differential Line Driver Ic - VXAlphaNoch keine Bewertungen
- My Computer TerDokument33 SeitenMy Computer Terwahyudi eka putraNoch keine Bewertungen
- MXTDokument18 SeitenMXTMaxey HigginbothamNoch keine Bewertungen
- Uah 2018 PDR PresentationDokument84 SeitenUah 2018 PDR PresentationAdarshNoch keine Bewertungen
- Blinc 360 and Ajna TechDokument14 SeitenBlinc 360 and Ajna TechAlkame IncNoch keine Bewertungen
- Electrical Properties Antenna SpecificationsDokument7 SeitenElectrical Properties Antenna SpecificationsМиланNoch keine Bewertungen
- S. No. Name Test/Lab Onsite DateDokument11 SeitenS. No. Name Test/Lab Onsite Daterajat.telecomNoch keine Bewertungen
- An107 - Implementing 16-Bit PWM Using The PCADokument18 SeitenAn107 - Implementing 16-Bit PWM Using The PCAMot. Schutzen '90Noch keine Bewertungen
- El Iec61215-2 2016Dokument6 SeitenEl Iec61215-2 2016Venkataramanan SNoch keine Bewertungen
- VU - Software Testing March 21Dokument17 SeitenVU - Software Testing March 21Srikanth MarepalliNoch keine Bewertungen
- Expt 8 - Satellite Communication Audio and VideoDokument4 SeitenExpt 8 - Satellite Communication Audio and VideosamarthNoch keine Bewertungen
- Estatement-202310 20240118082918Dokument3 SeitenEstatement-202310 20240118082918jooamir70Noch keine Bewertungen
- POM ReportDokument164 SeitenPOM ReportShalemRajNoch keine Bewertungen