Beruflich Dokumente
Kultur Dokumente
CEHv8 Module 04 Enumeration PDF
Hochgeladen von
MehrdadOriginalbeschreibung:
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
CEHv8 Module 04 Enumeration PDF
Hochgeladen von
MehrdadCopyright:
Verfügbare Formate
Enumeration
Module 04
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
Enumeration
Module 04
Engineered by Hackers. Presented by Professionals.
CEH
Ethical H acking and C ounterm easures v8
Module 04: Enumeration Exam 312-50
Module 04 Page 435
Ethical Hacking and Countermeasures Copyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
solutions
news
October 20, 2012 11:28AM
write us
H a c k e rs A tta c k U S W e ath e r S e rv ic e
THE US National Weather Service computer network was hacked with a group from Kosovo claiming credit and posting sensitive data, security experts said Friday. Data released by the Kosovo Hackers Security group includes directory structures, sensitive files of the Web server and other data that could enable later access, according to Chrysostomos Daniel of the security firm Acunetix. "The hacker group stated that the attack is a protest against the US policies that target Muslim countries," Daniel said. "Moreover, the attack was a payback for hacker attacks against nuclear plants in Muslim countries, according to a member of the hacking group who said, "They hack our nuclear plants using STUXNET and FLAME-like malwares, they are bombing us 24-7, we can't sit silent hack to payback them." .
h ttp :/ / w w w . theaustralian. com . ou
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
N E W S
S ecurity New s Hackers Attack US Weather Service
Source: http://www.theaustralian.com.au
The US National W eather Service computer network was hacked with a group from Kosovo claiming credit and posting sensitive data, security experts said recently. Data released by the Kosovo Hackers Security group includes directory structures, sensitive files from the web server, and other data that could enable later access, according to Chrysostomos Daniel of the security firm Acunetix. "The hacker group stated that the attack is a protest against the US policies that target Muslim countries," Daniel said. Moreover, the attack was a payback for hacker attacks against nuclear plants in Muslim countries, according to a member of the hacking group who said, "They hack our nuclear plants using STUXNET and FLAME-like malwares, they are bombing us 24-7, we can't sit silent - hack to payback them."
Module 04 Page 436
Ethical Hacking and Countermeasures Copyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
Paul Roberts, writing on the Sophos Naked Security blog, said the leaked information includes a list of administrative account names, which could open the hacked servers to subsequent "brute force attacks." "Little is known about the group claiming responsibility for the attack," he said. "However, they allege that the weather.gov hack was just one of many US government hacks the group had carried out and that more releases are pending."
2011 CBS Interactive. All rights reserved.
http://www.theaustralian.com.au/australian-it/hackers-attack-us-weather-service/storye6frgakx-1226499796122
Module 04 Page 437
Ethical Hacking and Countermeasures Copyright by
EC-COUIlCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
M odule O bjectives
'J J J J J What Is Enumeration? Techniques for Enumeration Services and Ports to Enumerate NetBIOS Enumeration Enumerate Systems Using Default Passwords SNMP Enumeration t J J J J J J J UNIX/Linux Enumeration LDAP Enumeration NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing
CE H
----------
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
l&SJ I* =
~
M odule O b jectiv es
In the previous modules, you learned about foot printing and scanning networks. The
next phase of penetration testing is enumeration. As a pen tester, you should know the purpose of performing enumeration, techniques used to perform enumeration, where you should apply enumeration, what information you get, enumeration tools, and the countermeasures that can make network security stronger. All these things are covered in this module. This module will familiarize you with the following: W hat Is Enumeration?
9 9
UNIX/Linux Enumeration LDAP Enumeration NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing
Techniques for Enumeration Services and Ports to Enumerate NetBIOS Enumeration Enumerate Systems Using Default Passwords SNM P Enumeration
9
9 9 9 9
Module 04 Page 438
Ethical Hacking and Countermeasures Copyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
M odule Flow
CEH
4\
M odule Flow
In order to make you better understand the concept of enumeration, we have divided
the module into various sections. Each section deals with different services and ports to enumerate. Before beginning with the actual enumeration process, first we will discuss enumeration concepts. ^ Enumeration Concepts
^
-
NTP Enumeration ^ SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing
!t__^
NetBios Enumeration SNMP Enumertion Unix/Linux Enumeration LDAP Enumeration
This section briefs you about what enumeration is, enumeration techniques, and services and ports to enumerate.
Module 04 Page 439 Ethical Hacking and Countermeasures Copyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
What Is Enumeration?
J In the enumeration phase, attacker creates active connections to system and performs directed queries to gain more information about the target
CEH
J J
Attackers use extracted information to identify system attack points and perform password attacks to gain unauthorized access to information system resources Enumeration techniques are conducted in an intranet environment
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
W hat Is E n u m e ra tio n ?
Enumeration is defined as the process of extracting user names, machine names, network resources, shares, and services from a system. In the enumeration phase, the attacker creates active connections to the system and performs directed queries to gain more information about the target. The attacker uses the gathered information to identify the vulnerabilities or weak points in system security and then tries to exploit them. Enumeration techniques are conducted in an intranet environment. It involves making active connections to the target system. It is possible that the attacker stumbles upon a remote IPC share, such as IPC$ in W indows, that can be probed with a null session allowing shares and accounts to be enumerated. The previous modules highlighted how the attacker gathers necessary information about the target without really getting on the wrong side of the legal barrier. The type of information enumerated by attackers can be loosely grouped into the following categories:
Information Enumerated by Intruders:
9 9 Network resources and shares Users and groups
Module 04 Page 440
Ethical Hacking and Countermeasures Copyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
9 9 9 9 9
Routing tables Auditing and service settings Machine names Applications and banners SNM P and DNS details
Module 04 Page 441
Ethical Hacking and Countermeasures Copyright by
EC-COUIlCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
Techniques for Enumeration
CEH
IUkjI N M h M
Extract user names using email IDs
Extract information using the default passwords
Extract user names using SN M P
Extract user groups from Windows
Extract information using DNS Zone Transfer
T e c h n iq u e s for E n u m e ra tio n
^ In the enumeration process, an attacker collects data such as network users and group names, routing tables, and Simple Network Management Protocol (SNM P) information. This module explores possible ways an attacker might enumerate a target network, and what countermeasures can be taken. The following are the different enumeration techniques that can be used by attackers:
Extract u se r n am es usin g em ail IDs
In general, every email ID contains two parts; one is user name and the other is domain name. The structure of an email address is username@domainname. Consider abc@gmail.com; in this email ID "abc" (characters preceding the and "gmail.com" (characters proceeding the symbol) is the user name symbol) is the domain name.
Extract inform ation usin g the default passw ords
Many online resources provide lists of default passwords assigned by the manufacturer for their products. Often users forget to change the default passwords provided by the manufacturer or developer of the product. If users don't change their passwords for a long time, then attackers can easily enumerate their data.
Module 04 Page 442 Ethical Hacking and Countermeasures Copyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
Brute force Active D irectory
Microsoft Active Directory is susceptible to a user name enumeration weakness at the time of user-supplied input verification. This is the consequence of design error in the application. If the "logon hours" feature is enabled, then attempts to the service authentication result in varying error messages. Attackers take this advantage and exploit the weakness to enumerate valid user names. If an attacker succeeds in revealing valid user names, then he or she can conduct a brute-force attack to reveal respective passwords.
Extract u se r n am es usin g SNMP
Attackers can easily guess the "strings" using this SNM P API through which they can extract required user names.
Extract u se r groups from W indows
These extract user accounts from specified groups and store the results and also verify if the session accounts are in the group or not.
Extract inform ation usin g DNS Zone T ransfer
DNS zone transfer reveals a lot of valuable information about the particular zone you request. W hen a DNS zone transfer request is sent to the DNS server, the server transfers its DNS records containing information such as DNS zone transfer. An attacker can get valuable topological information about a target's internal network using DNS zone transfer.
Module 04 Page 443
Ethical Hacking and Countermeasures Copyright by
EC-COUIlCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
Services and Ports to Enum erate
T C P 53
DNS zone transfer
CEH
UDP 161
Simple Network Management protocol (SNMP)
T C P 135
Microsoft RPC Endpoint Mapper
TCP/UDP 389
Lightweight Directory Access Protocol (LDAP)
T C P 137
NetBIOS Name Service (NBNS)
TCP/UDP 3368
Global Catalog Service
T C P 139
NetBIOS Session Service (SMB over NetBIOS)
T C P 25
Simple Mail Transfer Protocol (SMTP)
T C P 445
SM B over TCP (Direct Host)
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
S ervices an d P o rts to E n u m e ra te
TCP 53: DNS zone tran sfer
O 6 DNS zone transfer relies on TCP 53 port rather than UDP 53. If TCP 53 is in use then it means that DNS zone transfer is in process. The TCP protocol helps to maintain a consistent DNS database between DNS servers. This communication occurs only between DNS servers. DNS servers always use TCP protocol for the zone transfer. The connection established between DNS servers transfers the zone data and also helps both source and destination DNS servers to ensure the data consistency by means of TCP ACK bit.
TCP 135: M icrosoft RPC E ndpoint M apper
!The RPC port 135 is used in client/server applications to exploit message services. To stop the popup you will need to filter port 135 at the firewall level. W hen trying to connect to a service, you go through this mapper to discover where it is located.
TCP 137: NetBIOS N am e Service (NBNS)
NBNS, also known as Windows Internet Name Service (WINS), provides name resolution service for computers running NetBIOS. NetBIOS Name Servers maintain a database
EC-C0UnCil
Module 04 Page 444
Ethical Hacking and Countermeasures Copyright by
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
of the NetBIOS names for hosts and the corresponding IP address the host is using. The job of NBNS is to match IP addresses with NetBIOS names and queries. The name service is usually the first service that will be attacked.
TCP 139: NetBIOS Session Service (SMB over NetBIOS)
NetBIOS session service is used to set up and tear down sessions between NetBIOScapable computers. Sessions are established by exchanging packets. The computer establishing the session attempts to make a TCP connection to port 139 on the computer with which the session is to be established. If the connection is made, the computer establishing the session then sends over the connection a "Session Request" packet with the NetBIOS names of the application establishing the session and the NetBIOS name to which the session is to be established. The computer with which the session is to be established will respond with a "Positive Session Response," indicating that a session can be established or a "Negative Session Response," indicating that no session can be established.
TCP 445: SMB over TCP (Direct Host)
By using TCP port 445 you can directly access the TCP/IP MS Networking without the help of a NetBIOS layer. You can only get this service in recent versions of Windows, such as Windows2K/XP. File sharing in Windows2K/XP can be done only by using Server Message Block (SM B) protocol. You can also run SM B directly over TCP/IP in Windows 2K/XP without using the help of extra layer of NetBT. They use TCP port 445 for this purpose.
UDP 161: Sim ple N etwork M an ag em en t protocol (SNMP)
You can use the SN M P protocol for various devices and applications (including firewalls and routers) to communicate logging and management information with remote monitoring applications. SNM P agents listen on UDP port 161; asynchronous traps are received on port 162.
TCP/UDP 389: L ightw eight D irectory A ccess Protocol (LDAP)
m
You can use LDAP (Lightweight Directory Access Protocol) Internet protocol, used my M S Active Directory, as well as some email programs to look up contact information from a server. Both Microsoft Exchange and NetMeeting install an LDAP server on this port.
TCP/UDP 3368: G lobal C atalog Service
You can use TCP port 3368, which uses one of the main protocols in TCP/IP a connection-oriented protocol networks; it requires three-way handshaking to set up end-toend communications. Only then a connection is set up to user data and can be sent bidirectionally over the connection. TCP guarantees delivery of data packets on port 3368 in the same order in which they were sent. You can use UDP port 3368 for non-guaranteed communication. It provides an unreliable service and datagrams may arrive duplicated, out of order, or missing without notice and error
Module 04 Page 445
Ethical Hacking and CountermeasuresCopyright by EC-COUIICil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Checking and correction is not necessary or performed in the application, avoiding the overhead of such processing at the network interface level. UDP (User Datagram Protocol) is a minimal message-oriented Transport Layer protocol. Examples that often use UDP include voice over IP (VoIP), streaming media, and real-time multiplayer games.
TCP 25: Sim ple M ail T ransfer Protocol (SMTP)
SMTP allows moving email across the Internet and across your local network. It runs on the connection-oriented service provided by Transmission Control Protocol (TCP), and it uses well-known port number 25. Telnet to port 25 on a remote host; this technique is sometimes used to test a remote system's SMTP server but here you can use this command-line technique to illustrate how mail is delivered between systems.
Module 04 Page 446
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
information through enumeration; now it's time to put them into practice. If you are trying to enumerate information of a target network, then NetBIOS is the first place from where you should try to extract as much information as possible.
Enumeration Concepts
| 3 | NetBios Enumeration
4 1 NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing
SNMP Enumertion Unix/Linux Enumeration LDAP Enumeration
This section describes NetBIOS enumeration and the information you can extract through enumeration, as well as NetBIOS enumeration tools.
Module 04 Page 447
Ethical Hacking and Countermeasures Copyright by EC-COUItCll All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
NetBIOS Enumeration
NetBIOS name is a unique 16 ASCII character string used to identify the network devices over TCP/IP; 15 characters are used for the device name and 16th character is reserved for the service or name record type N e tB IO S N a m e L is t Attackers use the NetBios enumeration to obtain:
8 List of computers that belong to a domain S List of shares on the individual hosts on the network Policies and passwords
Name NetBIOS Code Type
UN IQ UE <domain> <00> GROUP
CEH
WWW
Information Obtained
Hostnam e Domain nam e M essenger service running for th at com puter M essenger service running for th at in dividual logged-in user Server service running M aster brow ser nam e for the subnet Domain m aster brow ser name, identifies the PDC for th at domain
<hostname>
<03>
UN IQ UE
<username>
<03>
UN IQ UE
chost name>
<20>
UN IQ UE
<domain>
<1D>
GROUP
<domain>
<1B>
UN IQ UE
Note: NetBIOS name resolution is not supported by Microsoft for Internet Protocol Version 6 (IPv6)
C op yright b y IC -C c u n c il. All Rights Reserved. Rep rod u ctio n is Strictly Prohibited.
NetBIOS E n u m e ra tio n
The first step in enumerating a Windows machine is to take advantage of the NetBIOS API. NetBIOS stands for Network Basic Input Output System. IBM, in association with Sytek, developed NetBIOS. It was developed as an Application Programming Interface (API), originally to facilitate the access of LAN resources by the client's software. The NetBIOS name is a unique 16 ASCII character string used to identify the network devices over TCP/IP; 15 characters are used for the device name and the 16th character is reserved for the service or name record type. Attackers use the NetBIOS enumeration to obtain:
List of computers that belong to a domain and shares of the individual hosts on the network
Policies and passwords
If an attacker finds a Windows OS with port 139 open, he or she would be interested in checking what resources he or she can access, or view, on the remote system. However, to enumerate the NetBIOS names, the remote system must have enabled file and printer sharing. Using these techniques, the attacker can launch two types of attacks on a remote computer
Module 04 Page 448
Ethical Hacking and Countermeasures Copyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
that has NetBIOS. The attacker can choose to read/write to a remote computer system, depending on the availability of shares, or launch a denial-of-service.
NetBIOS Name List
Name
NetBIOS Code <00> <00> <03>
Type
Information Obtained
<host name> <domain> <host name>
UNIQUE GROUP UNIQUE
Hostname Domain name Messenger service running for that computer
<username>
<03>
UNIQUE
Messenger service running for that individual logged-in user
<host name> <domain> <domain>
<20> <1D> <1B>
UNIQUE GROUP UNIQUE
Server service running Master browser name for the subnet Domain master browser name, identifies the PDC for that domain
Note: NetBIOS name resolution is not supported by Microsoft for Internet Protocol Version 6
(IPv6).
Module 04 Page 449
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
NetBIOS Enumeration
(Contd)
Nbtstat displays NetBIOS over TCP/IP (NetBT) protocol statistics, NetBIOS name tables for both the local computer and remote computers, and the NetBIOS name cache
CE H
Run nbtstat command "nbtstat. exe -a < NetBIOS Name of remote machine>"to get the NetBIOS name table of a remote computer
Run nbtstat command "nbstat.exe - c " t o display the contents of the NetBIOS name cache, the table of NetBIOS names, and their resolved IP addresses
C:\Windows\system32\cmd.exe
Users\Adnin)nbtstat .exe -a\:2 *a
l H
C:\Wi ndows\system 32\cmd .exe
S.U 8 c 1*0 'sfl d m in ) n b t 8 1 a t . c
Ethernet: *lode IpAddress : (192.168 .168.170 Scope Id: M
NetBIOS Renote Cache Nane Table
NetBIOS Renote flachine Nane Table Nane < <
Ml t
Type <00> <00> <1C> <20> <1B> UNIQUE GROUP GROUP UNIQUE UNIQUE 05
Status Registered Registered Registered Registered Registered
DM
M
"* MAC Address - m 2:MJ sers\Adin>
* Ut *
http://technet.microsoft.com
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
NetBIOS E n u m e ra tio n (C ontd)
x Source: http://technet.microsoft.com Nbtstat displays NetBIOS over TCP/IP (NetBT) protocol statistics, NetBIOS name tables for both the local computer and remote computers, and the NetBIOS name cache. Nbtstat allows a refresh of the NetBIOS name cache and the names registered with Windows Internet Name Service (WINS). Used without parameters, Nbtstat displays help. Run the nbtstat command "nbtstat.exe -a < NetBIOS Name of remote machine>" to get the NetBIOS name table of a remote computer.
Module 04 Page 450
Ethical Hacking and Countermeasures Copyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
C:\Windows\system32\cmd.exe
C:\Users\Admin)nbtstat.exe -a Ethernet: Mode IpAddress: [192.168 .168.170] Scope Id: U NetBIOS Renote Machine Nane Table Name <00> <00> <1c> <20> >1B < : Type UNIQUE GROUP GROUP UNIQUE UNIQUE !* 05 Status Registered Registered Registered Registered Registered
MAC Address = C:\Users\Adnin> B
FIGURE 4.1: Enumeration Screenshot
Run the nbtstat command "nbstat.exe
-c" to display the contents of the NetBIOS name
cache, the table of NetBIOS names, and their resolved IP addresses. S3
C:\Windows\system32\cmd.exe
2:\Users\Admi1Cnbtstat exe -c Ethernet: 40de IpAddress: [192.168.168.170] Scope Id: []
NetBIOS Remote Cache Name Table Name <20> <20> i:\Users\Admin> Type UNIQUE UNIQUE Host Address Life [sec]
1 9 2.168.168.170 192.168.168.1
FIGURE 4.2: Enumeration Screenshot
Module 04 Page 451
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
NetBIOS E n u m e ra tio n Tool: S uperS can
SuperScan is a connect-based TCP port scanner, pinger, and hostname resolver
SuperScar! 4.0
Goan | Hosl end Soivce Discovery | Scon Options] Tods Hostnarae/IP/UHl W1 ndv*eEnun*f*liar| Aocul |
CEH
L= ll
fenurefate^ 3pbons._ | Q ea> |
A
Features:
10.D02
S 8
m
Enuneratbn Type
Nerbios lnromaticn cn 10.0.0.2 3 name m cable GROUP UH1QCJE UNIQ'JE WcricstaTioa service naze Horkscafioa service atec Server services naze
Support for unlimited IP ranges Host detection by multiple ICMP methods TCP SYN and UDP scanning
Simple HTML report generation
m m
Source port scanning
0 n n 0 n Q Q n 0 Q
NetBIOS Name Tabic NULL Session MAC Addresses Workstation t y p e User? Groups RFCEnc^oirt Dunp Account P o l i c i e s Shares Domains Remote Time0 1Day Logon Sesiicnj D r i v e s Trusted Domains Seivbcs R e g i i t r y
WORKGROUP 00 WIK-MSS2LCK4K41 00 W:N-.HS :LCK4K41 20 MAC addcess 0: Uaora on 10.0.0.2 Totsi Users: 4 .
Admin , *Adnd.niscrator" m m Full Ks m : 31.11i .-1q a count ror administering System Comnent: the camD-iter/donsin* Last logon: Password expires: Password changed: Locked out: Disabled Nunber of logons: 3ac p a ss ve rd count: *Jset
"H u n t*
Fast hostname resolving
B
m
rri Aug 17 93:27:14 2012 (0 lays ago) Never 9 days age No No 1 te 0
Extensive banner grabbing
Extensive W indow s host enumeration
00:02
Saved log file
Liv k O
|TCP open: 0
[UOPopenTO
|1 / 1 done
http ://www. mcafee. com
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
NetBIOS E n u m e ra tio n Tool: SuperS can
Source: http://www.mcafee.com SuperScan is a connect-based TCP port scanner, pinger, and hostname resolver. It performs ping sweeps and scans any IP range with multithreading and asynchronous techniques. You can restore some functionality by running the following at the Windows command prompt before stating SuperScan: 0 0 0 0 0 0 0 0 0 Support for unlimited IP ranges Host detection using multiple ICMP methods TCP SYN , UDP, and source port scanning Hostname resolving IP and port scan order randomization Extensive Windows host enumeration capability Extensive banner grabbing Source port scanning Simple HTML report generation
Ethical Hacking and Countermeasures Copyright by
Module 04 Page 452
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
SuperScan 4.0
Scan | Host and Service Discovery | Scan Options | Tools Hostname/I P/URL 1 10.0.0.2 Enumeration Type 0 0 NetBIOS Name Table NULL Session MAC Addresses Workstation type Users Groups RPC Endpont Dum p Account Policies Shares Domains Remote Time of Day Logon Sessions Drives Trusted Domains Services Registry Windows Enunciation | About | Enumerate | Qptions | lea!
NetBIOS information on 10.0.0.2 3 nazr.es in table WORKGROUP 00 WIN-MSSELCK4K41 0 0 WIN-MSSELCK4K41 2 0 MAC address 0 :
GROUP Workstation service UNIQUZ Workstation service UNIQUZ Server services name
name name
Users on 10.0.0.2 Total Users: 4
1 / . 1 /
Admin Administrator" Full Naxne: "" System Comment: Built-in account for administering the computer/domain User Coxzsaent: " Last logon: Fri Aug 17 0 9 : 2 7 : 1 4 2 0 1 2 (0 days ago) Password expires: Never Password changed: 8 days ago Locked out: No Disabled: No Number of logons: 1 58 Bad password count: 0 User Guest"
3
TCP open: 0 UDP open: 0 1/1 done
0002
Saved log file
Live: 0
FIGURE 4.3: SuperScan Screenshot
Module 04 Page 453
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
NetBIOS Enumeration Tool: Hyena
Hyena is GUI product for managing and securing Microsoft operating systems. It shows shares and user logon names for Windows servers and domain controllers It displays graphical representation of Microsoft Terminal Services, Microsoft Windows Network, Web Client Network, etc.
S e r v i c e 9e*\\mCV
%a E* M m T m* nap 1-4 > ^ j
V '!
X + : : ie
od y *< 5
j j t ra u
J_bs2----------------- 1
Artw D irecto ryW ebS ervices A pp licatio nE x p e rien ce AppfcaticnHo# H elp erService A p p licatio nId en tity Sto p p e d A p p A ca fco nWormjton Sto p p ed (A ppficatcnUinrjriryr ASPiiETStateService A 'etd ow sA ud io(ndpeeit Bu ild er Sto p p e d W indow sA u d io Sto p p ed 8eseF*enngEn9 rv e B o e1q ro u rv( :!tellqert T ran sferService Sto p p ed C om putrr Bro w ser Sto p p e d C ertificatePro p ag atio n Wrosoft J4ETFrtrrtew & lcN G ENv2 A 5 C ?2 7 _X *6 Sto p p e d M icro so ftMgT Framed N GfN2 .0 J0 7 2 7 _X 4 Sto p p e d M crosoft .N ETFram wkNO tNv 410 3 W 1 9 .X S 6 **SVrosoft .N ETFr1m erkN G C N A030319J CO M * SystemA p p licatio n C !> p to g ra p *cSer.ices DC O MServerPro cesslat*1c t1e r D ali O rfrag m en tar DfSMamewce O FSR ep licatio n DHCPCUrt D M 5ferret D N SC lient )W eedA atoConfl D iag n o stic Pdky Seroce C item ib leA r/th en b cstio nPro to co l ne{ < * ) 11ngFileSystem(IK Andowi Event log Service(O w nP ro cess) Service(ScaredP ro cess) Servite(C h o nProem ) Service(Sh aredP ro cess) Soviet (Sh aredP ro cess) Service(Sh aredP *o e e sa ) Service(Sh o redProem ) Service(O w nP ro cess) Service(Sh aredProem ) Service(Sh aredProem ) Service(SharedPro cessJ Service(Sh aredP ro cess) Service !;S h a re dProem ) Service(Sh aredP ro cess) Service(O w nP ro cess) Service(O w nProem ) Service(O w nP ro cess) Service(O w nPro cessJ Service(O w nProem ) Service(Sh aredP ro cess) Service(Sh aredP ro cess) Service(O w nProem ) Service(O w nProem ! Service(O w nP ro cess) Service(Sh aredProem ) Service(O w nPro cml Service(Sh aredProem )
* JJ le iU e itfo in d tC e fe jtc o n a e id rfo ro fp iu n 9 j )M a cse f.k fca 1 jcS te M C )1 & 4 s
-1 2 1Mirages Ser-iceAccoists(Man* car^intt 3 EJ ) 3 LZ ] Macscf: uJiar.je Sjiar- C fc je c ts * 21 Q uotasiQ.ctaspecAcabensccwCaK-e':
* Cl P '0 9 r r nC a te.O e * a U tkxrtoif( C w rjre f g Cl System systemsettv^s
5 jjj Cwla-itsOX
J Uiei Crfadl ec * farup grad edu ser a c
sflnww
- 0 1iM tl H mj *Sflress C > P r ogn~\ fdes**crcso/TE M rnj A3**NS r: /ft-so w s: (S.JCSICW B mj dew-lead t AMtadl jCSOA} : mj tKhenyeCAl C'M yiin FWcs'Mcx s 1 U 0 * <C\1M-**SV9r0L\w* TJ C\Pra fW e sM ew T *J yrSVOt.(C .*nr->SWOl\oyw
elr.optrtiiatien.viOJ0 7 2 7 .3 2 41e !_o p e ac*sn_*2JJ0727jM e&c)r.optmjat.c.v4J)J03I9J2 At1r.opem .at1on.1A0J0Jl9.64 *COMSytApp c-.pt',.:
4 l0 c o m L a u K t1
*"-
Sto p p e d
Service(Sh aredProcml Service (Sh o redP ro cess) Serv.ce(Sh aredProeeu) Service(Sh aredProem ) Service (Sh aredProem ) Service(Sh aredP ro cess)
h ftp ://w w w . system too ls.co m Copyright ffi by IC-Cmcil. All Rights Reserved. Reproduction is Strictly Prohibited.
NetBIOS E n u m e ra tio n Tool: H yena
Source: http://www.systemtools.com Hyena is GUI product for managing and securing any Windows operating system such as Windows NT, Windows 2000, Windows XP/Vista, Windows 7, or Windows Server 2003/2008 installation. It uses an Explorer-style interface for all operations and to manage users, groups (both local and global), shares, domains, computers, services, devices, events, files, printers and print jobs, sessions, open files, disk space, user rights, messaging, exporting, job scheduling, processes, and printing. It shows shares and user logon names for Windows servers and domain controllers. It displays a graphical representation of the web client network, Microsoft terminal services, and Windows network.
Module 04 Page 454
Ethical Hacking and Countermeasures Copyright by
EC-COUItCll
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
H h*
* 0 m lea N*
O i T ^ A J .2 J 1* Q JjU L -
Y -! * X 5* : : E
ArtOeodetyWe* Wm(1
S#rw* |Qm1 P1MM4) Service(Own PlCKtlt) Semcr (Vxred>twml Seevire(Uu*od Pw m i NT *UThOWTViIm Mmm iwrftysiem NT k* r K t CAttMtaiH lxK)H> w NT AUTMOtfnriMrftortu NT AUThO CSTV U m rlU C IM m i M oomUMT caw i 0% (.M M m 'V n 1 rK t
Lfmnci
AepUceton layer Gateway Service **heat* M o t HaiderService
W >X (hj*dP*<m) Mm m I
t J J Ifc W i titfw y 1 1 <o 0>)W g J M M Qmw <QvU 1oe< 1n1 m M y w r ft 1H t 1n < Service C e < t1f-c*t Prefa'ater' MKiOKft X T frarv.< *N i(N W C.XW .tH UemoD NIT lre<e*NO<N*JC.M7;7.tt4 MkmsA X T f,*r**kNCtM viC K M -M Mirttno* NIT hn1<M1lrNMN^t.l01n.ll4 COM SyMeraAfffcceUen i* f f (Omi hwm) WvKt (Vxt<tV<ml Service (SheeedProeeM)
!N r iM i
taw |Wm < N < )
Service(SHeredProeen) Servtcr (Slured Proem! Service (lKjd Proem) Seme* (Own Picccm) Service (Omi h t(M | Service(Own tocot) Service(Own Pk*m<) W1X1 (Own Piwcm) Servicf (UuwdProem) Service (SfctretfhKM | 5nx (Own Preceu) W<(Own Prc<) Service (Own Pioceu) Smite Itawd Proem) W vki (Own Pieceu) W>1c* (ViMd Pt m l Service lu*ed Pn) itmcc (ShercdProem) W\x1 (SkerodProem) Service(SK4dProem) Service(Uiwd Proem) Service (SK**dProem) Service(SheiedProem) Service(SkwedProeew) Service(SharedProea*) Service (SharedProem)
4V 1 M M IX jD C n N n r-
3, , v
O M M M 'M w M t M r ( ', M M ' l l M M l M n C\0fc* > !* BoxfcMT c w M U < M r
8 j A4*0m C f4t.lAuceo* I M mj 1 M M (CNWWidcan)
Crfptoy*phtt icM tn
SeJC SfC A J
m
9 * j briM ^KUS <CProgramMr 'M ck t j CkxM*x> (C A-iy ?in'Ate* !C-,ttbe i i ' i ' i t iJbi
JaCM
e j afWBU C x .n i il
KOMSnPrMmUyn<N' DakC ef> a m e n ce r [>i Narweifeee
Stooped
DfSM m iw
O M C PCIM M DNSSorver DNSCSart
( -.H ko ~ <yOT^<*. C W > 7 1> ,* * 1 0 .'C T?
C M M M iy iM U U K lI C A-4*m
0 4
aO N IU O G O N ifS Y S X X V jy r a jl lO ^ yn F lo N M o ra a J S V S M X(O .* .d e .i'S V S V d ie y ^ Q
EiKryptan^f 4cSyilem (US) AmtoMbwilef COM- tvy Sjnt Witicwrt fibre ChannelPlatformfegiiticticn S_ tuwebe* 0*cowy Provide*M o e *
FIGURE 4.4: Hyena Screenshot
Module 04 Page 455
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
http ://www. winfingerprin t.com
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
NetBIOS E n u m e ra tio n Tool: W in F in g erp rin t
Source: http://www.winfingerprint.com WinFingerprint is an administrative network resource scanner that allows you to scan machines on your LAN and returns various details about each host. This includes NetBIOS shares, disk information, services, users, groups, and more. WinFingerprint is an administrative network resource scanner that allows you to scan machines on your LAN and returns various details about each host. This includes NetBIOS shares, disk information, services, users, groups, and more. You can choose to perform a passive scan or interactively explorer network shares, map network drives, browse HTTP/FTP sites and more. Scans can be run on a single host or the entire network neighborhood.
Module 04 Page 456
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Winfingerprint 0.6.2
Input Options C IP Range
(
C IP List
Scan Options ( Domain
W
C Active Directory
C WMI API
W
Single Host C Neighborhood IP Address: I 10.0.0.3
Win32 OS Version W Users Null IPC$ Sessions P Services NetBIOS Shares Date and Time Ping Host(s) P Disks I Groups RPC Bindings
Patch Level
1
W W W
[7 MAC Address f7 Sessions I Event Log Show Help
V Traceroute Host
General Options
\~
TCP Portscan Range:
Timeout for TCP/UDP/ICMP/SNMP: Retries: [3 Max Connections:
f~ UDP Portscan Range: P SNMP Community String: public
Pinging 10.0.0.3 with 44 bytes of data: Reply from 10.0.0.3 0 ms (id* 1, seq* 1) IP Address: 10.0.0.3 WINDOWS8 Computername: WORKGROUP\WINDOWS8 MAC Addresses: 00155da86e06 Scan completed in 0.27 seconds Done.
httD ://w infinQ erprint.s o u rc e fo ra e .n e t m a1 lto:vacu u m < au sers.s o u rc e fo ro e .n e t
Winfingerprint 0.6.2
In p u t Options S c a n O ptions
< I P R a n g e ( "S in g le
| 192
I P List
(* D o m ain
I* f7 [*
C" A c tiv e D ire c to ry W U s e rs
C WMI API W Patch Le v e l
f ? M AC A d d res s p Se ss io n s
Host C N e ighborhood S ta rtin g I P A d d re s s : . 168 . 168 !
W in 3 2 O S V ersio n
Null I P C S Se ss io n s W S e r v ic e s N e tB IO S S h a r e s D a te and T im e
En ding I P A d d ress: | 192 . 168 . 168 . 4
W D is k s W G ro u p s
f*
W E v e n t Log
Show E rro rs Help
f N e tm a s k
f Ping H o s t(s )
wR P C r Bin din gs
G e n e r a l Options | B ro a d co m N e tU n k (T M ) G ig a b it E th e rn e t T im e o u t fo r T C P / U D P / IC M P / S N M P : R e trie s : f3 M ax C o n n e c tio n s : [5 | 1024
31
f~ T C P P o rtsca n R a n g e :
U D P P o rtsca n R a n g e : S N M P C o m m u n ity Strin g : public
I P A d d re s s : 192.168.168.1 C o m p u te rn a m e :
1A
T rac in g rou te to 192.168.168.1 1 0 ms 0 ms 0 m s 192.168.168.1 X M A C A d d re s s e s : 5 R P C Bin d in g s: n c a c n _ip _tc p U U ID A d d re s s 192.168.168.1 E n d P o in t 49158 n c a c n _ ip _ tc p U U ID ncacn_1 p _tcp U U ID ncacn_1 p _tcp U U ID ncacn_1 p _tcp U U ID n c a c n _ip _tc p U U ID ncacn_1 p _tcp U U ID A d d re s s 192.168.168.1 E n d P o in t 49219 A d d re s s 192.168.168.1 En d P o in t 49219 A d d re s s 192.168.168.1 E n d P o in t 49219 A d d re s s 192.168.168.1 En d P o in t 49219 A d d re s s 192.168.168.1 En d P o in t 49190 A d d re s s 192.168.168.1 En d P o in t 49181
FIGURE 4.5: Winfingerprint Screenshots
Module 04 Page 457
Ethical Hacking and Countermeasures Copyright by EC-COIillCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
NetBIOS E n u m e ra tio n Tool: N etBIOS E n u m e ra to r
CEH
iijjA ^1 .
i ? ?
]WORKGROUP[ 10.0.0.7 ?
W1N-MSSB.OC4M1J[ 10.0.0.2 ?
Scamwo from: 10 .0 0 1 to: 10.0 0 5 0
s?
% % % %
R e a d y
$ 131 NetBIOS '< (
1)14 5(j)
SCimrg Von: li.ao 1 to: 10.0X50
WINDOWS8I[ 10.0.0.3 10.0.0.5 [WW-UQr0WR3R9< 1 [
m t X M U -R Serve Sowe
WINDOWS Watetaton s t a WORKGROUP Cwran Kane WORKGROUP - PotenSa Masto 3r WORKGRCXP - Master frowse _0 6_ mmoS Username: (No one logged on] =
**V
2 O o m a n :W O R K G R O U P ! G f R0l l T rpT in * PTT): 1 TT oU
g
? 10.0.0.7 [WORKGRCXf]
B J S NetBIOS Na w (3) ( S . vvoRKGROl^ * Doman Name
Do w K G O JP
so u rc e fo rg e -n e t
http://btenum Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
NetBIOS E n u m e ra tio n Tool: NetBIOS E n u m e ra to r
, M Source: http://nbtenum.sourceforge.net This application is recommended when you want to determine how to use remote network support and how to deal with some other interesting web techniques, such as SM B.
Module 04 Page 458
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
NetBIOS Enumerator
f!y IP range to scan from:| 10.0.0.1 to: | 10.0.0.50 Scan Your local ip: 10.0.0.7
W
Settings
Clear
[1...254]
Debug window Scanning from: 10.0.0.1 to: 10.0.0.50 Ready!
10.0.0.4 [WINDOWS8] S S ? ? 10.0.0.7 [WORKGROUP] 10.0.0.2 [WIN-MSSELCK4K41] 10.0.0.3 [WINDOWS8] 10.0.0.5 [WIN-LXQN3WR3R9M] ? ?
J
NetBIOS Enumerator
- fs j IP range to scan --from:| 10.0.0.1 to: 10.0.0.50 Scan Your local ip: 10.0.0.7
W
Clear
Settings
[1...254]
Debug window Scanning from: 10.0.0. 1 to: 10.0.0.50 Ready!
B ?
10.0.0.4 [WINDOWS8]
*I
B m NetBIOS Names (6) 1 S p WINDOWS8 -File Server Service WINDOWS8 -Workstation Service | % I j % I 3 WORKGROUP Domain Name WORKGROUP - Potential Master Bro WORKGROUP Master Browser MSBROWSE Master Br!
!Q Username: (No one logged on)
|
B
? 6
Domain: WORKGROUP Round Trip Time (RTT): 1ms-Time To Li NetBIOS Names (3) WORKGROUP -Domain Name
[ i
10.0.0.7 [WORKGROUP]
j D o m a i n : WORKGROUP 1 Ef Round Trip Time (RTT): 0 ms -Time To Li v
III I >
WIN-D39MR 5HL9E4 -Workstation S WIN O39MR 5HL9E4 -File Server Se
| J J ; Username: (No one logged on)
i f
FIGURE 4.6: Enumeration Screenshot
Module 04 Page 459
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Enumerating User Accounts
PsExec
h ttp ://technet.m icrosoft.com
CEH
PsList
h ttp ://technet.m icrosoft.com
PsFile
http ://te ch ne t.m icro soft.co m
PsLoggedOn
h ttp ://te ch n e t. microsoft. com
PsGetSid
http ://te ch ne t.m icro soft.co m
PsLogList
h ttp ://te ch n e t. microsoft. com
PsKill
L^V
h ttp ://technet.m icrosoft.com
PsPasswd
http ://te ch ne t.m icro soft.co m
Pslnfo
h ttp ://technet.m icrosoft.com
y/
PsShutdown
h ttp ://te ch n e t. microsoft. com
Copyright C by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
E n u m e ra tin g U ser A ccounts
PsExec
Source: http://technet.microsoft.com PsExec is a command-line tool used for telnet-replacement that lets you execute processes on other systems and console applications, without having to manually install client software. W hen you use a specific user account, PsExec passes credentials in the clear to the remote workstation, thus exposing the credentials to anyone who happens to be listening in.
PsFile
Source: http://technet.microsoft.com PsFile is a command-line utility that shows a list of files on a system that is opened remotely, and it also allows you to close opened files either by name or by a file identifier. The default behavior of PsFile is to list the files on the local system that are open by remote systems. Typing a command followed by " displays information on the syntax for the command.
Module 04 Page 460
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
PsGetSid
f
Source: http://technet.microsoft.com PsGetsid allows you to translate SIDs to their display name and vice versa. It works on built-in accounts, domain accounts, and local accounts. It also allows you to see the SIDs of user accounts and translates a SID into the name that represents it and works across the network so that you can query SIDs remotely.
PsKill
Source: http://technet.microsoft.com PsKill is a kill utility that can kill processes on remote systems and terminate processes on the local computer. You don't need to install any client software on the target computer to use PsKill to terminate a remote process.
Pslnfo
Source: http://technet.microsoft.com Pslnfo is a command-line tool that gathers key information about the local or remote Windows NT/2000 system, including the type of installation, kernel build, registered organization and owner, number of processors and their type, amount of physical memory, the install date of the system and, if it is a trial version, the expiration date.
PsList
^ Source: http://technet.microsoft.com PsList is a command-line tool that administrators use to view information about process CPU and memory information or thread statistics. The tools in the Resource kits, pstat and pmon, show you different types of data but display only the information regarding the processes on the system on which you run the tools.
jjpjF PsLoggedO n
Source: http://technet.microsoft.com PsLoggedOn is an applet that displays local and remote logged users. If you specify a user name instead of a computer, the PsLoggedOn tool searches all the computers in the network neighborhood and tells you if the user is currently logged on PsLoggedOn's definition of a locally logged on user is one that has their profile loaded into the Registry, so PsLoggedOn determines who is logged on by scanning the keys under the HKEY_USERS key.
PsLogList
Source: http://technet.microsoft.com
The default behavior of PsLogList is to show the contents of the System Event Log on the local computer, with visually-friendly formatting of Event Log records. Command-line options let you
Module 04 Page 461
Ethical Hacking and CountermeasuresCopyright by EC-C0lMCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
view logs on different computers, use a different account to view a log, or to have the output formatted in a string-search friendly way.
PsPassw d
Source: http://technet.microsoft.com sPasswd is a tool that enables the administrator to create batch files that run PsPasswd on the network of computers to change the administrator password as a part of standard security practice.
J PsShutdown
|*jc . Source: http://technet.microsoft.com PsShutdown is a command-line tool that allows you to remotely shut down the PC in networks. It can log off the console user or lock the console (locking requires Windows 2000 or higher). It does not require any manual installation of client software.
Module 04 Page 462
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
E num erate S ystem s U sing D efault P assw ord s
Devices like switches, hubs, routers, access points might still be enabled with a "default password"
CE H
Attackers gain unauthorized access to the organization computer network and information resources by using default and common passwords
3COM 3COM 3COM 3COM 3COM 3COM
L A T 'P te X
LANpiex LinkSwitch NetbuiWer NetBuider Ottnc Conncct ISDW Roiicrs
2 D O O
2500 2000/2700
Ortwg teen tech
PASSWORD
Aann
h ttp://www. vims. org/default_passwds
Enterprise Network
Default Username/Pwd Ex: admin/synnet
Router
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
E n u m e ra te S ystem s U sing D efault P a ssw o rd s
Source: http://www.defaultpassword.com Devices such as switches, hubs, routers, and access points usually come with "default passwords." Not only network devices but also a few local and online applications have built-in default passwords. These passwords are provided by vendors or application programmers during development of the product. Most users use these applications or devices without changing the default passwords provided by the vendor or the programmer. If you do not change these default passwords, then you might be at risk because lists of default passwords for many products and applications are available online. Once such example is http://www.virus.org/default_passwds; it provides verified default login/password pairs for common networked devices. The logins and passwords contained in this database are either set by default when the hardware or software is first installed or are in some cases hardcoded into the hardware or software.
Module 04 Page 463
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
S earch
Sear[ ^
vendor
Product
Model
2 | 3 | A | B | C | D | E | F | G | H | I | J | K | L | M | N | 0 | P | Q | R | S | T | U | V | W |X |Z |All Vendor 2w1re 3COM 3COM 3COM 3COM 3COM 3COM 3COM 3COM 3COM 3COM Product W iF i Routers CellPlex CoreBuiider CoreBuilder HiPerARC LANptex LANplex LinkSwitch NetBuikler NetBuilder Office Connect ISDN Routers Model\Rev1slon 7000 7000/6000/3500/2500 7000/6000/3500/2500
V4 I X
2500 2500 2000/2700
Login (none) tech debug tech adm debug tech tech
Password Wireless tech synnet tech (none) synnet tech tech ANYCOM ILMI PASSWORD
A ccess Level Admin
snmp-read snmp-read Admin
5x0
n/a
FIGURE 4.7: Enumeration Screenshot
Attackers take advantage of these default passwords and the online resources that provide default passwords for various products and application. Attackers gain unauthorized access to the organization computer network and information resources by using default and common passwords.
Router
FIGURE 4.8: Enumeration Screenshot
Module 04 Page 464
Ethical Hacking and Countermeasures Copyright by
EC-COUIlCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
M odule Flow
CEH
Enumeration Concepts
NetBIOS Enumeration
HP
Enumeration Pen Testing
UNIX/Linux Enumeration
SMTP Enumeration
DNS Enumeration
Enumeration Counterm easures
is
Copyright C by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
M odule Flow
This section describes the UNIX/Linux commands that can be used for enumeration and Linux enumeration tools.
Enumeration Concepts t__J| NetBios Enumeration
SN M P Enumertion
y" NTP Enumeration
SMTP Enumeration DNS Enumeration Enumeration Countermeasures _^ Enumeration Pen Testing
Unix/Linux Enumeration LDAP Enumeration
Module 04 Page 465
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
SNMP (Sim ple N etw ork M an ag em en t Protocol) E n u m eratio n
J a target system using SN M P J SN M P consists of a manager and an agent; agents are embedded on every network device, and the manager is installed on a separate computer
CEH
SN M P enumeration is a process of enumerating user accounts and devices on
SN M P holds tw o passwords to access and configure the SN M P agent from the management station Read community string: It is public by default, allows to view the device or system configuration 6 Read/write community string: It is private by default, allows to edit or alter configuration on the device
Attacker uses these default com munity strings to extract information about a device
= =
Attackers enumerate SN M P to extract information about network resources such as hosts, routers, devices, shares, etc. and network information such as ARP tables, routing tables, traffic statistics, device specific information, etc.
Copyright C by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
SNMP (Sim ple N etw ork M a n a g e m e n t Protocol) E n u m e ra tio n
SNM P (Simple Network Management Protocol) is an application layer protocol that runs on UDP, and is used to maintain and manage routers, hubs, and switches on an IP network. SN M P agents run on Windows and UNIX networks on networking devices. SN M P enumeration is the process of enumerating the user's accounts and devices on a target computer using SNMP. Two types of software components are employed by SNM P for communicating. They are the SN M P agent and SNM P management station. The SN M P agent is located on the networking device whereas the SNM P management station is communicated with the agent. Almost all the network infrastructure devices such as routers, switches, etc. contain an SNM P agent for managing the system or devices. The SNM P management station sends the requests to the agent; after receiving the request the agent sends back the replies. Both requests and replies are the configuration variables accessible by the agent software. Requests are also sent by SN M P management stations for setting values to some variables. Trap let the management station know if anything has happened at the agent's side such as a reboot or interface failure or any other abnormal event.
Module 04 Page 466
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
SNM P contains two passwords that you can use for configuring as well as for accessing the SNM P agent from the management station. The two SNM P passwords are: Read community string:
o o
Configuration of the device or system can be viewed with the help of this password These strings are public
Read/write community string:
o o
Configuration on the device can be changed or edited using this password These strings are private
W hen the community strings are left at the default setting, attackers take the opportunity and find the loopholes in it. Then, the attacker can uses these default passwords for changing or viewing the configuration of the device or system. Attackers enumerate SN M P to extract information about network resources such as hosts, routers, devices, shares, etc. and network information such as ARP tables, routing tables, device specific information, and traffic statistics. Commonly used SNM P enumeration tools include SN M PU til and IP Network Browser.
Module 04 Page 467
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures
Enumeration
Exam 312-50 Certified Ethical Hacker
Working of SNMP
CEH
itktjl H..U1
Active Session Information (No. of sessions: 2, Comm: Complnfo, IP: 10.10.2.15) Host X (SN M P M anager) Community String: IP: 10.10.2.12 If the community string does not match with the string stored in the MIB database, host Y will send a community string to a pre configured SNMP manager indicating the error Host Y (SN M P Agent)
&
Host Z (SN M P Manager)
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
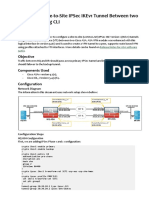
W orking of SNMP
MIB
Community String: Complnfo Software version hard drive space session table r
Community String: Comf Comm unity String: Alarm
IP: 10.10.2.1
Sends request for active session (Community String: Complnfo, IP: 10.10.2.15)
IP: 10.10.2.15
Active Session Information (No. of sessions: 2, Comm: Complnfo, IP: 10.10.2.15)
Host X (SNMP Manager)
Host Y (SNMP Agent)
If the community string does not match with the string stored in the M IB database, host Y will send a community string to a pre-configured I
SNMf^nanagenndicatin^h^rroi^
Host Z (SNMP Manager) FIGURE 4.9: SNMP Screenshot
Module
04 Page 468
Ethical Hacking and CountermeasuresCopyright by
EC-C0UnCil
All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
M an agem en t Inform ation B ase (MIB)
M IB is a virtual database containing can be managed using SNMP
CE H
The M IB database is hierarchical and each managed object in a M IB is addressed through object identifiers (OIDs)
Two types of managed objects exist: 9 Scalar objects that define a single object instance e Tabular objects that define multiple related object instances that are grouped in MIB tables The OID includes the type of M IB object such as counter, string, or address, access level such as not-accessible, accessible-for-notify, read-only or read-write, size restrictions, and range information
SNMP uses the MIB's hierarchical namespace containing object identifiers (OIDs) to translate the OID numbers into a human-readable display
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
M a n a g e m e n t In fo rm atio n B ase (MIB)
M IB is a virtual database containing a formal description of all the network objects that can be managed using SNMP. M IB is the collection of hierarchically organized information. It provides a standard representation of the SN M P agent's information and storage. M IB elements are recognized using object identifiers. Object ID is the numeric name given to the object and begins with the root of the M IB tree. The object identifier can uniquely identify the object present in the M IB hierarchy. MIB-managed objects include scalar objects that define a single object instance and tabular objects that define group of related object instances. The object identifiers include the object's type such as counter, string, or address, access level such as read or read/write, size restrictions, and range information. M IB is used as a codebook by the SNM P manager for converting the OID numbers into a human-readable display. The contents of the M IB can be accessed and viewed using a web browser either by entering the IP address and Lseries.mib or by entering DNS library name and Lseries.mib. For example, http://IP.Address/Lseries.mib or http://library_name/Lseries.mib. Microsoft provides the list of MIBs that are installed with the SN M P Service in the Windows resource kit. The major ones are:
Module 04 Page 469
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Q 9 9 e
DHCP.MIB: Monitors network traffic between DHCP servers and remote hosts HOSTMIB.MIB: Monitors and manages host resources LNMIB2.MIB: Contains object types for workstation and server services W IN S.M IB: For Windows Internet Name Service
Module 04 Page 470
Ethical Hacking and Countermeasures Copyright by EC-C0l1ncil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
SNMP Enum eration Tool: OpUtils
OpUtils with its integrated set of tools helps network engineers to monitor, diagnose, and troubleshoot their IT resources
U rtrfi * Itb K jl
C EH
Copyright by
IC-Council. All
Rights Reserved. Reproduction is Strictly Prohibited.
SNMP Enum eration Tool: OpUtils
Source: http://www.manageer 1Rine.com OpUtils is a collection of tools using which network engineers can monitor, diagnose, and troubleshoot their IT resources. You can monitor the availability and other activities of critical devices, detect unauthorized network access, and manage IP addresses. It allows you to create a custom SNMP tools through which you can monitor M IB nodes.
Module 04 Page 471
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Module 04 Page 472
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
SNMP Enumeration Tool: SolarWinds IP Network Browser
Sola.Wintls Oe Tata VWw Oev*n rterluen Gadqm f *ffral Tools Help kspace studio U4rw 9< 5HMOCrdf'I^K Q KUnqt Ttintl'&H Credentials *^Settings9* ^0 . *S4tup. {JNvT*b *Hi SaveSeated Tbs Tftnft/$SH tg inttrfxt Chart / TnccRoul(
CEH
1 4 216a1 6 a3 - 4J-63 1S3S PC 13216a 168x fc 152.16a168 32 . ~ T 132.168168 35 **
mm ....
WindowsNTWiykSttton er System M J"* System Nam ** 0 i SystemDescrpBon J1 Location sys0t!ec30 1.181.41311.1.1.1 F J Lasttoo; 8 1 2 1 4 0 1 29.6766AM 0O SI Services v Interfaces 2interlaces US TCP looptacfc 1 n tn 9 c g} 0 Reaitek RTLB16a811 0Family Gig to 5 *C*S(60) Accounts It ARP Tawe ODR Routes I Snares It! SMrrt onottfi feTCmPNtfwo'ts l, TCPC0nnctl(K*S 3 13 2 .1 6 8 1 6 842 1 3 21 6 8 .1 6 8 .4 2 3 13 2 .1 6 8 1 6 84 3 I 3 13 2 .1 6 8 1 6 85 0 1 3 21 6 8 .1 6 8 .5 0
IP Network Browser performs network discovery on a single subnet or a range of subnets using ICMP and SNMP It scans a single IP, IP address range, or subnet and displays network devices discovered in real time, providing immediate access to detailed information about the devices on network
,nUor-ttmc'cch
SW7c, 1
Pass * 5 f t 1a Q ..: j 5teU Q v ,*-P
iS ^
http://www.solarwinds.com
Copyright ffl by
IC-Ctuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
c. j
SNMP Enum eration Tool: SolarW inds IP Network Browser
Source: http://www.solarwinds.com IP Network Browser from SolarWinds is a network discovery application. It collects information via ICMP and SNMP locally or on a remote network. It scans a single IP, IP address range, or subnet and displays network devices as they are discovered in real time, providing you with immediate access to detailed information about the devices on your network. It is easy for the attacker to discover information about the target network after performing scanning of the entire subnet. Using IP Network Browser, an attacker can gather information from a poorly configured Windows system. The information that can be gathered includes server name, operating system version, SNMP contact and location information, list of services and network interfaces, list of all user accounts, machine date/time, etc. For example, on a Cisco router, Solar Winds IP Network Browser will determine the current IOS version and release, as well as identify which cards are installed into which slots, the status of each port, and ARP tables. When the IP Network Browser discovers a Windows server, it returns information including interface status, bandwidth utilization, services running, and even details of software that is installed and running.
Module 04 Page 473
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
SolarWinds
I I File Tab< V1 w In t d f x K Gadget* External Tool* H#lp Setting j... Setup... ?Add Nen Device-. Martagc SNMP Credcrteh Q Manage Telnet/SSHCredential!
Studio
,jJNewTeb c jSave SelectedTabs
I 3 Switch Port Mapper Trtrwt/SSH *J rtertace Chart / TraeeRoute I Explorer IP Nerwert Growter * ^ g 192 163 168 1
*" Gadgets
1 /P3 Monitoring
d;Ca C P Ja ro Mewocy Ml interface onr O ! erfaceGawse dt 1 rte<face~atoe * | Respont# TneCnart fft Response T*e Gauge & Ratpoma T Telia - , n Took * C3 Ad ess Manatraert
a 1921631533 0 ( 1 192163163 5 ls>g 192163168 30 j ^ 3 192 163 15332 19216316336
...
f C
!r|hTT68:3r
i f WircovisNT Aorujtanon : SyiUnMlS .P) Sst None. -** ! | Systan Description: i
Contact d a Location sysCfcjectC: 1.3.6.1 4.1.311.1.1.31.1 JTj lattboor 3/210012 367-MAM tt 0 9 Service* 2interfaces (/ % MS TCP Loopback interface *>9 Raaltefc RTL81SWM10 Fain ly Gigabit Etharret NIC - Packet Scheduler Miniport
1i> Q C u Tool*
>r3 ConngTaas -
C a5 * fiW * :T j3 6
3sco^ar> Tccb > a < =littAOrc Browser t.7 W O F !< 3e t ? 'Js gnbo* Wap Ang Sweep RajleYtavef $. Snnp Sweep ^ Srten Port Mapper T:aceRou:e / AMI B ro w r +
in te rfa c e s
1 Serv cesGC)
Lt. Accounts *. ARPTaWe t Routes C1 CR Routes , . Snares *. Snared Pr rtacs 1. *CP^P Networks 1* TCPComecaons
*, 7 MonrtoinjTook 2
tZ2 SNVPTools+
i f 15 AetoGedgets word Generator***
3en re Stated
O More Help V u j *centy Used
^3 1 9 2 1 6 3 1 6 3 4 21 9 2 .1 6 3 .1 6 3 .4 2 ^a 1 - - -4 3 1 6 3 1 5 3 03 1 9 2 1 6 3 1 5 3 5 0:1 9 2 .1 6 8 .1 6 3 .5 0
*3 .
>
D ray 2
: second'
FIGURE 4.11: SNMP Enumeration Tool Screenshot
Module 04 Page 474
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
S N M P E n u m e r a tio n T o o ls
Getif
h tt p :/ / w w w . wtcs. org h tt p :/ / w w w . softperfect.com
C EH
SoftPerfect Network Scanner
OiDViEW SN M P M IB Browser
h tt p :/ / w w w . oidvie w . com
SN M P Informant
h ttp ://w w w .s n m p -in fo rm a n t.c o m
iReasoning M IB Browser
h ttp ://tll.ire a so n in g .c o m
Net-SNMP
http ://ne t-sn m p .sou rce fo rge.n et
SNScan
h ttp ://w w w .m c a fe e .c o m
Nsauditor Network Security Auditor
h tt p :/ / w w w . nsauditor. com
SN M P Scanner
h ttp ://w w w .se cu re -b yte s.co m
-
Spiceworks
h tt ttD p :/ ://w /www w.soice . spiceworks.com
Copyright by
IC-Ccuncil. All
Rights Reserved. Reproduction is Strictly Prohibited.
SNMP Enum eration Tools
In addition to OpUtils and SolarWind's are listed as follows: Q Q Q e Q Q e e 9 6 Getif available at http://www.wtcs.org OiDViEW SNMP MIB Browser available at http://www.oidview.com iReasoning MIB Browser available at http://tll.ireasoning.com SNScan available at http://www.mcafee.com SNMP Scanner available at http://www.secure-bytes.com SoftPerfect Network Scanner available at http://www.softperfect.com SNMP Informant available at http://www.snmp-informant.com Net-SNMP available at http://net-snmp.sourceforge.net Nsauditor Network Security Auditor available at http://www.nsauditor.com Spiceworks available at http://www.spiceworks.com
IP Network Browser, a few more SNMP tools
Module 04 Page 475
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Module Flow
Enumeration Concepts
NetBIOS Enumeration
SNMP Enumeration
SMTP Enumeration
DNS Enumeration
Enumeration Countermeasures
Enumeration Pen Testing
i s
Copyright C by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
M odule Flow
This section describes the UNIX/Linux commands that can be used for enumeration and Linux enumeration tools. Enumeration Concepts t__J| NetBios Enumeration SNMP Enumertion ^ Unix/Linux Enumeration LDAP Enumeration
1
y" NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures _^ Enumeration Pen Testing
Module 04 Page 476
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
UNIX/Linux Enum eration C om m ands
o Enumerates the user and the host Enables you to view the user's home directory, login time, idle times, office location, and the last time they both received or read mail
EH
[root$] finger -1 0target.hackme.com
Helps to enumerate Remote Procedure Call protocol RPC protocol allows applications to communicate over the network
[root] rpcinfo -p 19x.16x.xxx.xx
Using rpcclient we can enumerate user names on Linux and
OSX
[root $] rpcclient $> netshareenum
Finds the shared directories on the machine
[root $] showmount -e 19x.l6x. xxx.xx
Copyright by
IC-Ccuncil. All
Rights Reserved. Reproduction is Strictly Prohibited.
U N IX /Linux E n u m e ra tio n C o m m a n d s
Commands used to enumerate UNIX network resources are as follows: showmount, finger, rpcinfo (RPC), and rpcclient.
finder command is used for enumerating the users on the remote machine. It The finger enables you to view the user's home directory, login time, idle times, office location, and the last time they both received or read mail. The syntax for finger is: finger [-b] [-f] [-h] [-i] [1 ] [-m] [-p] [-q] [-s] [w] [username] O p tio n s: -b
-f Suppresses printing the user's home directory and shell in a long format printout. Suppresses printing the header that is normally printed in a non-long format printout.___________ I Suppresses printing of the .project file in a long format printout. Forces "idle" output format, which is similar to short format except that only the login name, terminal, login time, and idle time are printed.
Finger:
h
-I
Module 04 Page 477
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Forces long output format. Matches arguments only on the user's name. Suppresses printing of the .plan file in a long format printout. Forces quick output format, which is similar to short format except that only the login name, terminal, and login time are printed. Forces short output format. Suppresses printing the full name in a short format printout.
q
-s -w
For example, if the command root$] finger-1 (target.hackme.com is executed, then you can get the list of users on the target host.
IfS
^ 1
rpcinfo (R PC )
rpcinfo (RPC) helps you to enumerate Remote Procedure Call protocol. This in turn allows the applications to communicate over the network. The syntax for rpcinfo follows:
rpcinfo [-m | -s ] [ host ]
rpcinfo P [ host ] rpcinfo -T transport host prognum [ versnum ] rpcinfo -1 [ -T transport ] host prognum versnum rpcinfo rpcinfo ] n portnum ] -u host prognum [ versnum ] ] n portnum ] -t host prognum [ versnum ] ? transport prognum [ versnum
rpcinfo -a serv address
rpcinfo -b [ -T transport ] prognum versnum rpcinfo -d [ -T transport ] prognum versnum
O p tio n s:
-m Displays a table of statistics of rpcbind operations 011 the given host. The table shows statistics for each version of rpcbind (versions 2, 3 and 4), giving the number of times each procedure was requested and successfully serviced, the number and type of remote call requests that were made, and information about RPC address lookups that were handled. This is useful for monitoring RPC activities 011 the host. Displays a concise list of all registered RPC programs on host. If host is not specified, it defaults to the local host. Probes rpcbind on host using version 2 of the rpcbind protocol, and display a list of all registered RPC programs. If host is not specified, it defaults to the local host. Note that version 2 of the rpcbind protocol was previously known as the portmapper protocol. Makes a RPC call to procedure 0 of prognum on the specified host using TCP, and report whether or not a response was received. This option is made obsolete by the -T option as shown in the third synopsis.
-s
-P
-t
Module
04 Page 478
Ethical Hacking and CountermeasuresCopyright by EC-C0IM Cil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Displays a list of entries with a given prognum and versnum 011 the specified host. Entries are returned for all transports in the same protocol family as that used to contact the remote rpcbind. Makes a RPC broadcast to procedure 0 of the specified prognum and versnum and report all hosts that respond. If transport is specified, it broadcasts its request only on the specified transport. If broadcasting is not supported by any transport, an error message is printed. Use of broadcasting should be limited because of the potential for adverse effect on other systems. Deletes registration for the RPC service of the specified prognum and versnum. If transport is specified, unregister the service on only that transport; otherwise, unregister the service on all the transports on which it was registered. Only the owner of a service can delete a registration, except the superuser, who can delete any service. Makes an RPC call to procedure 0 of prognum on the specified host using UDP, and report whether or not a response was received. This option is made obsolete by the -T option as shown in the third synopsis.
-b
-d
-u
-a serv_address
Uses serv_address as the (universal) address for the service on transport to ping procedure 0 of the specified prognum and report whether or not a response was received. The -T option is required with the -a option. If versnum is not specified, rpcinfo tries to ping all available version numbers for that program number. This option avoids calls to remote rpcbind to find the address of the service. The serv_address is specified in universal address format of the given transport.
-n p o rtn u m
Uses portnum as the port number for the -t and -u options instead of the port number given by rpcbind. Use of this option avoids a call to the remote rpcbind to find out the address of the service. This option is made obsolete by the -a option. Specifies the transport on which the service is required. If this option is not specified, rpcinfo uses the transport specified in the NETPATH environment variable, or if that is unset or NULL, the transport in the netconfig database is used. This is a generic option, and can be used in conjunction with other options as shown in the SYNOPSIS. Specifies host of rpc information required.
-T tra nsp o rt
Host
For example, if the command [root] rpcinfo -p 19x.16x.xxx.xx is executed, then you can get the rpc information of the host you are currently connected to.
rpcclient
rpcclient is used to enumerate usernames on Linux and OS X. The syntax for rpcclient follows: rpcclient [-A authfile] [-c ccommand string>] [-d debuglevel] [-h] [1 logdir] [-N] [-s <smb config file>] [-U username[%password]] [-W workgroup] [1 destinationIP] {server} O p tio n s:
c
Execute semicolon-separated commands.
Module 04 Page 479
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
-I
IP address is the address of the server to connect to. It should be specified in standard "a.b.c.d" notation.
Z'-p
This number is the TCP port number used when making connections to the server. The standard TCP port number for an SMB/CIFS server is 139, which is the default. debuglevel is an integer from 0 to 10. The default value if this parameter is not specified is 0 . Prints the program version number. The file specified contains the configuration details required by the server.
-d
-V
-s
Base directory name for log/debug files. The extension ".progname" will be appended (e.g. log.smbdient, log.smbd, etc...). The log file is never removed by the client. If specified, this parameter suppresses the normal password prompt from the client to the user. This is useful when accessing a service that does not require a password. This option allows you to specify a file from which to read the username and password used in the connection. Sets the SMB user name or user name and password. Set the SMB domain of the use rname.
-N
-A -U -W
Print a summary of command-line options.
For example, if the command root $] rpcclient $> netshareenum is executed, then it displays all the user names.
showmount
showmount identifies and lists the shared directories available on a system. The clients that are remotely mounted on a file system from a host are listed by showmount. mountd is an RPC server that replies to the NFS access information and file system mount requests. The mountd server on the host maintains the obtained information. The file /etc/rmtab saves the information from crashing. The default value for the host is the value returned by hostname
( 1).
The syntax for the mountd:/usr/lib/nfs/mountd [-v]
[-r] [hostname]
The syntax for Showmount: /usr/sbin/showmount [-ade]
Module 04 Page 480
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
O p tio n s:
-a
-d -e
Print all remote mounts in the format.
List directories that have been remotely mounted by clients. Print the list of shared file systems.
For example, if the command [root $] showmount -e 19x.l6x. xxx.xx is executed, then it displays the list of all shared directories that are mounted by a host.
Module 04 Page 481
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Linux Enum eration Tool: Enum41inux
sh-3.2S enum41inux.pl r 192.168.2.55 Starting enum41inux vO.8.2 ( http://labs.portcullis.co.uk/applic11tion/enura41inux/ ) on Wed Apr 2 14:14:35 20( ---- Target information ----Target ................. 192.168.2.55 RID Range ............ 500-550.1000-1050 Uscmane ............. * Password.............. * Known Usernames .. adm inistrator, guest, krbtgt, domain admins, root, bin, none Enuraerating Workgroup/Domain on 192.168.2.55 [ * ] Got domain/workgroup name: W ORKGRO UP ---- Getting domain SID for 192.168.2.55 ---Donain Nane: W O RKG RO UP Donain Sid: S-0-0 [+] Host is part of a workgroup (not a domain) Session Check on 192.168.2.55 [ ] Server 192.168.2.55 allows sessions using username , password Users on 192.168.2.55 via RID cycling (RIDS: 500-550,1000-1050) [ I] Assuming that user "adm inistrator" exists Got SID: S - l - 5 - 2 1 7 2 5 3 4 5 5 4 3 1801674531 1482476501 using username " , password S-l-5-21-1801674531-1482476501-725345543-500 W2KSQL\Administrator (Local User) S-l-5-21-1801674531-1482476501-725345543-501 W2KSQL\Guest (Local User) S-l-5-21-18016745311482476501-725345543-513 W2KSQL\N0ne (Domain Group) S-l-51801674531-1482476501-725345543-1000 21 W2KSQL\TsInternetUser (Local User) S-l-5-21-1801674531-1482476501-725345543-1001 W2KSQL\IUSR_PORTCULLIS (Local User) S-1-5-21-1801674531-1482476501-725345543-1002 W2KSQL\IWAM_P0RTCULLIS (Local User) S-1-5-21-1801674531-1482476501-725345543-1004 W2KSQL\mark (Local User) S-l-5-21-1801674531-1482476501-725345543-1005 W2KSQL\blah (Local User) S-l-5-21-1801674531-1482476501-725345543-1006 W2KSQL\basic (Local User)
[j
cnun411nux complete on Wed Apr 2 14:14:40 2008
http://labs,portcullis,co.uk
Copyright C by
IC-Ccuncil. All
Rights Reserved. Reproduction is Strictly Prohibited.
Linux Enum eration Tool: Enum41inux
Source: http://labs.portcullis.co.uk
Enum4linux is a tool that allows you to enumerate information from samba, as well as Windows systems. Features: Q RID Cycling (When RestrictAnonymous is set to 1 on Windows 2000) e User Listing (When RestrictAnonymous is set to 0 on Windows 2000)
Q Listing of Group Membership Information 9 Share Enumeration e e Detecting if host is in a Workgroup or a Domain Identifying the remote Operating System
9 Password Policy Retrieval (using polenum)
Module 04 Page 482
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
s h -3 .2 J e riu M Iin u x :p r r :1 9 2 .1 6 8 .2 .5 V : S ta r t in g enum41inux v0.8.;2 ( h t t p : / / l a b s . p o r t c u l l l s . c o u k /a p p lic a tio n /e n u m 4 1 in u x / ) on Ned Apr --------- . T a rg e t in fo rm a tio n -------T arg et ........................................................................................ SS. 1 9 2 .1 6 8 .2 RID Range ;................ 500-550.1000-1050 U sernaae J ........................................................................................ Known Usernames . . a d m in is tr a to r , g u e st k r b tg t , domain adm ins, ro o t, b in . none
2 14:14:35 2(X
m woM ;...;...:....... : .................
------- Enum erating Workgrciup/Domain on 1 9 2 .1 6 8 .2 .5 5 (] Got dom ain/w orkgroup name: W ORKGROUP ------- G e ttin g domain SID tor 1 9 2 .1 6 8 .2 .$ S --------D e ta in Name: W ORKGROUP ; D oaain S id : S -0 -0 [+] Host i s p a r t o f a workgroup (n o t a domain) .......... S e ssio n Check on 1 S 2 .1 6 8 .2 .5 S [] S e rv e r 1 9 2 .1 6 8 .2 .SS a llo w s s e s s io n s u sin g username ' ' . passw ord * U sers on 192:168.2.;S5 viar RID c y c lin g (RIDS: SO0-SSO;1000-1050) [X] Assuming t h a t u s e r " a d m in is tra to r" e x i s t s [ ] Cot SID: S - l- 5 - 2 1 - 1801674531-14824765O1-725345543 vising username f . passw ord S-1-S-21-I801674S31-1482476SO1-72534S543-S00 W 2KSQL\Adrtinistrator (L o ta l U ser) S-1-S-21-1801674531-1482476501-72534SS43-501 W2KSQL\Guest (L ocal U ser) S-1-S-21-1801674S31-1482476S01-72S34SS43-S13 W2KSQL\None (Domain Group) S-1-S-21-I801674531-1482476501-72S345543-1000 W2KSQL\TsInternetUser ( lo c a l U ser) S -l-S -2 1 -l8 0 i674531j 1432476501-72S345543j 1001 #2KSQL\IUSR_PORTCULLIS (L ocal U ser) S - l - 5-21-1801674531-1482476501-725345543-1002 W2KSQL\IWAM_PORTCULLIS (L ocal U ser) S-1-S-21-1801674S31-1482476S01-725345543-1004 W2KSQL\mark (L ocal U ser) S-1-S-21-1801674531-1482476501-72S34S543-100S W2KSQL\blah (L ocal U ser) S -l-S -2 1 -1 8 0 1 6 7 4 S 3 1 -1482476501-725345543-1006 W2KSQL\basic (L ocal U ser) enum-JlinuX com plete on W<d Apr 2 1 4 :1 4 '4 0 2008
FIGURE 4.11: Enum4linux Tool Screenshot
Module 04 Page 483
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Module Flow
CEH
Enumeration Concepts
NetBIOS Enumeration
SNMP Enumeration
UNIX/Linux Enumeration
SMTP Enumeration
DNS Enumeration
Enumeration Countermeasures
Enumeration Pen Testing
i s
Copyright by
IC-Ccuncil. All
Rights Reserved. Reproduction is Strictly Prohibited.
M odule Flow
To enable communication and manage data transfer between network resources, various protocols are employed. All these protocols carry valuable information about network resources along with the data to be transferred. If any external user is able to enumerate that information by manipulating the protocols, then he or she can break into the network and may misuse the network resources. LDAP is one such protocol intended to access the directory listings. Enumeration Concepts !t__5 NetBios Enumeration SNMP Enumertion ! NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures
IfF v
Unix/Linux Enumeration LDAP Enumeration
Enumeration Pen Testing
This section focuses on LDAP enumeration and LDAP enumeration tools
Module 04 Page 484
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
LDAP E num eration
Lightweight Directory Access Protocol (LDAP) is an Internet protocol for accessing distributed directory services
CEH
Itfc tu l N k w
t t
-**
Directory services may provide any organized set of records, often in a hierarchical and logical structure, such as a corporate email directory
A client starts an LDAP session by connecting to a Directory System Agent (DSA) on TCP port 389 and sends an operation request to the DSA
Information is transmitted between the client and the server using Basic Encoding Rules (BER)
Attacker queries LDAP service to gather information such as valid user names, addresses, departmental details, etc. that can be further used to perform attacks
Copyright by
IC-Ccuncil. All
Rights Reserved. Reproduction is Strictly Prohibited.
n>
LDAP Enum eration
The Lightweight Directory Access Protocol (LDAP) is used to access directory listings within an Active Directory or from other directory services. A directory is compiled in hierarchical or logical form, slightly like the levels of management and employees in a company. It is suitable to attach with the Domain Name System (DNS) to allow quick lookups and fast resolution of queries. It usually runs on the port 389 and other similar protocols. You can anonymously query the LDAP service. The query will disclose sensitive information such as user names, addresses, departmental details, server names, etc., which can be used by the attacker for launching the attack.
Module 04 Page 485
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
LDAP Enumeration Tool: Softerra LDAP Administrator
UrlA H
EH c1
ItbKJl HMkM
HT ML V i e w
LDAP Adrn'nistrator
hf(P'' '1
Copyright C by
IC-Ccuncil. All
Rights Reserved. Reproduction is Strictly Prohibited.
LDAP Enum eration Tool: Softerra LDAP Adm inistrator
Source: http://www.ldapadministrator.com Softerra LDAP Administrator is a LDAP administration tool that allows you to work with LDAP servers such as Active Directory, Novell Directory Services, Netscape/iPlanet, etc. It generates customizable directory reports with information necessary for effective monitoring and audit. Features: It provides directory search facilities, management facilities, etc. bulk update operations, group membership
It supports LDAP-SQL, which allows you to manage LDAP entries using SQL-like syntax
Module 04 Page 486
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
CN=Franko Barucci.OU =HR Department.DC=example,DC= com -Softerra LDAP Administrator 2011.1
11* drt '*w Fjvontes Sfer Entry dtf Schema Refiorts !ools Window Hf lP
* J s i -JM - X
Scope Pane
X -u4 '* 3
.'iff i '"JJ' -J i; K?-2JI \ M J-EfI
"
w 9
3 S i OU -HR Department I E 2 CN - Aaron Dorben | S) CN-Alexander Lemming I IS CN-Alexander McDoughal I E CN-Andrew Anderson : S CN-Andrew Wfe ! f i CN Andrew Wfcon | ! j j E E $ $ ft E B ft ft ft ft (S ft ft ft E ? 5 CN=Ann Doe CN-Anny Hobbs CN-Aron Piersoi CN Aurora Namuia CN Clarence Bulwmkei CN C 0ns1dting Department CN David Morris CN=Oavid Smith CN David Watson CN=Oerrxs Martin CN-Szabeth Johnson CN=EMEA Group CN Cordon Summer CN Gregory Murrey CN Henry Richards CN-HR Managers C N -IT Department CN James Garfield CN*Jason Guard CN -le e dark
Franko Barucci
U F.Barucci(j>Example.com Planning Manager Paris
*331 587 268 45
-331 587 268 48
Organization Franko Barucci
Telephones
Address
Account
Franko Barucci Planning Manager Paris
ft a E
Telephone Number
+ 331 587 268 45
.; :
examples [example.com:389] -Softerra LDAP Administrator 2011.1
Entry Schema Recorts Iools Window tjelp ^
I * * J ; !
Scope Pane
jtlew- 3 ^ x
? x Name
| I J
Value
\ a) K? ;
Configuration Schema DomatnDnsZones example ForestDnsZones 20110620130837.0Z CN-NTDS Settings,CN *SERVER 1,CN... DC example,DC com CN Schema,CN Configuration,DC*... DC example ,DC com MaxPoolThreads MaxDatagramRecv MaxReceiveBuffer InitRecvTimeout MaxConnections MaxConnldleTime MaxPageSize MaxQueryDuration MaxTempTableSize MaxResultSetSize MaxNotficationPerConn MaxValRange 28907 server 1 .example.com
O k
Type Entry Entry Entry Entry Entry Attribute Attnbute Attribute Attribute Attribute Attribute Attnbute Attribute Attnbute Attribute Attribute Attribute Attribute Attribute Attribute Attnbute Attribute Attnbute Attribute Attnbute Size unknown unknown unknown unknown unknown 17 109 17 44 34 17 14 15 16 15 14 15 11 16 16 16 22 11 5 ____________19
Softerra LDAP Admrtrator ajJ Internet Pubk Servers $ 0 Adressen der Bundesverwaltu f f l - y Came^e Melon University Colorado State University J Debian 0 ffl 0 Deutsche Telekom AG DTrustCAs New York University 0 Trust Center h 0 University of MKhigan ft g VeriSign Local Servers $ ufj Mcrosoft Exchange Servers -j 0 ^ Testing Servers
13CN L3CN 5JDC 3 DC 3DC
H currentTme l*J dsServiceName
S S
defaultNamingContext
&J schemaNamingContext & J rootDomainNamingContext S supportedLDAPPobaes E supportedLDAPPoliaes (=J supportedLDAPPobaes S supportedLDAPPobaes (=J supportedLDAPPobaes supportedLDAPPobaes C = J supportedLDAPPobaes (=] supportedLDAPPobaes C * J supportedLDAPPobaes (=J supportedLDAPPobaes H supportedLDAPPobaes (=J supportedLDAPPobaes highestCommittedUSN (*J dnsHostName d H List View X
configurabonNamingContext CN Configuration,DC =example,DC=...
i .. j
3 CN=Config1 ration & S 3 CN Schema f t 3 DC=DomainDnsZones j ftSJ DC example f t |3 DC ForestDnsZones f t - 0 rainbow f t - Q umbrella E 0 AD i - 0 CA Directory 4 9 Planet
HTML View
B Output C Basket S subnodes
FIGURE 4.12: Softerra LDAP Administrator tool Screenshot
Module 04 Page 487
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
LDAP E num eration Tools
JXplorer
h ttp ://w w w .jx p lo re r.o rg h ttp ://technet.m icrosoft.com
CEH
Active Directory Explorer
LDAP Admin Tool
h tt p :/ / w w w . Idapsoft. com
LDAP Administration Tool
http ://sou rce fo rge.n et
LDAP Account Manager
h ttp ://w w w .ld a p -a cco u n t-m a n a g e r.o rg
LDAP Search
http ://secu rityxp lo de d .com
fi ^
m
LEX-The LDAP Explorer
h ttp ://w w w .ld a p e x p lo re r.co m
n-
Active Directory Domain Services Management Pack
h ttp ://w w w .m icro so ft.co m
LDAP Admin
h ttp ://w w w .ld a p a d m in .o rg
LDAP Browser/Editor
h ttp ://w w w .n o v e ll.c o m
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
LDAP Enum eration Tools
There are many LDAP enumeration tools that can be used to access the directory listings within Active Directory or from other directory services. Using these tools attackers can enumerate information such as valid user names, addresses, departmental details, etc. from different LDAP servers. A few LDAP enumeration tools are listed as follows: Q JXplorer available at http://www.ixplorer.org Q LDAP Admin Tool available at http://www.ldapsoft.com Q LDAP Account Manager available at http://www.ldap-account-manager.org Q LEX - The LDAP Explorer available at http://www.ldapexplorer.com e e e 9 t? 9 LDAP Admin available at http://www.ldapadmin.org Active Directory Explorer available at http://technet.microsoft.com LDAP Administration Tool available at http://sourceforge.net LDAP Search available at http://securitvxploded.com Active Directory Domain Services Management Pack available at http://www.microsoft.com LDAP Browser/Editor available at http://www.novell.com
Module 04 Page 488
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Module Flow
C EH
M odule Flow
Often, the NTP server is overlooked in terms of security. But, if queried properly, it can also provide a lot of valuable network information to the attackers. Therefore, it is necessary to test what information an attacker can enumerate about your network through NTP enumeration. Enumeration Concepts t__5 NetBios Enumeration SNMP Enumertion Unix/Linux Enumeration
If* ->
^jr^ NTP Enumeration ^ SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing
LDAP Enumeration
This section describes what is NTP, what information can be extracted through NTP enumeration, and NTP enumeration commands
Module 04 Page 489
Ethical Hacking and CountermeasuresCopyright by EC-C0l1nCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
NTP E num eration
a
Network Time Protocol (NTP) is designed to synchronize clocks of networked computers It uses as its primary means of communication
CEH
Rip
ggi
S S
It can achieve accuracies of or better in local area networks under ideal conditions
NTP can maintain time to within 1 0 milliseconds ( 1 / 1 0 0 seconds)over the public Internet
Attacker queries NTP server to gather valuable information such as:
List of hosts connected to NTP server Clients IP addresses in a network, their system names and OSs Internal IPs can also be obtained if NTP server is in the DMZ
Cbpyright C by I C C c u n c i l . All RightsJteServfci Reproduction is Strictly Prohibited.
NTP Enumeration
Before beginning with NTP enumeration, let's first discuss what NTP is. NTP is a network protocol designed to synchronize clocks of networked computer systems. NTP is important when using Directory Services. It uses UDP port 123 as its primary means for communication. NTP can maintain time to within 10 milliseconds (1/100 seconds) over the public Internet. It can achieve accuracies of 200 microseconds or better in local area networks under ideal conditions. Through NTP enumeration, you can gather information such as lists of hosts connected to NTP server, IP addresses, system names, and OSs running on the client systems in a network. All this information can be enumerated by querying the NTP server. If the NTP server is in the DMZ, then it can also be possible to obtain internal IPs.
Module 04 Page 490
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
NTP E n u m era tio n C o m m a n d s
ntptrace
& Traces a chain of NTP servers back to the primary source
6 < 40 vlrt jal-marMnt- vlrtM l* 1w c M M :S ntpdc ntpdc* / ntpdc connands: aridp*1r control key fudge aridrefcloefc ctls ta ts help addtorvof debug host add rap delay hostnanes outhlnfo deW estrlct Ifrrloed broadcast disable U s u is elkbug dnpeers lostats clockstat enable kerplnfo clrtrap exit keyld ntpdc* nonlist renote address port local *44 keytype
CEH
CeflrfWd IU k j I N a*h a tlnerstats
5 ntptrace [ -vdn ] [ -r retries ] [ t timeout ] [ server ]
ntpdc
Monitors operation of the NTP daemon, ntpd
looplnfo "* * H t * m llit passed peers preset pstets
ltK*r*
r**Ay(
rqv* 1 tky est r n llt t r e s tric t shMpter systnfo t y t U it s
trap!
W T M trU t untrastedkey versto* lit t n t
6 /usr/bin/ntpdc tn] [-v] hostl I IPaddressl...
curoplun.canonical.ton 123 J9J.1C0 125.02.193.121 123 ]92.168. 1 2 0 1 0 *46 83 . sni tZl . hn123 192.168. se0ent119-226 .s lfy.n 123 192.168. ns3.nel - .con 123 192.168. ntpdc* |
25 28 27 26
4 4 4 4
4 4 4 4
ntpq
9 Monitors NTP daemon ntpd operations and determines performance
ntpdc: monlist query
m -vlr tual-nachlne:-J ntpq 1tpq> . itpq connands:
e ntpq [-inp]
[-c
co m m and ]
[host]
[ I
:learvara :lo ckllst keyld keytype passoclatlons passwd save<onfl9 showers .onflg-fron-rile lopeeis poll version :ooked ipassoclatlons pstatus w rite lls t :v Ipeers quit rltevar lebug nreadllst raw _ tpq> readllst issoctdaO status>061S leap none. sync_ntp. 1 event, clock sync, rerston-ntpd 4 7 ftpigi Tue lun . ?:17:11 UTC ?81? (1 )*. irocettor-"1696 , syctem-*llnux/3.2. 23 generic-pae*, leap, itratun-3, precision 22, rootdelay-141.734, rootdlsp-1!.34, cr1d-120.0e.46.10, eftlned3cl9d3d.elOcM7B r r l , Aug 24 2012 11:37:09.MO, ;locked3el9e4r.ac34l2cc r r l . Aug 24 2012 12:91:43.072, peer304, tc*o. iln tc O , orrset04.020, frequency80 . 008 . sys Jlt t e r a r s .179, :Ik )ltter-83.672, elk wander-9.28d
ntptrace
ntpq: readlist query
Copyright C by IC-Ctuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
EB NTP Enum eration C om m ands
NTP enumeration can be performed using the NTP suite command-line tool. NTP Suite is used for querying the NTP server to get desired information from the NTP. This command-line tool includes the following commands:
Q ntptrace ntpdc ntpq
These commands will help you extract the data from the NTP protocol used in the target network. ntptrace: This command helps you determine from where the NTP server updates its time and traces the chain of NTP servers from a given host back to the prime source.
Syntax: ntptrace [-vdn] [-r retries ] [-t timeout] [servername/IP_address]
Example:
# ntptrace localhost: stratum 4, offset 0.0019529, synch distance 0.143235
Module 04 Page 491
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
192.168.0.1: 192.168.1.1:
stratum 2, offset 0.0114273, synch distance 0.115554 stratum 1, offset 0.0017698,
-virtual-machine: -
synch distance 0.011193
-vlrtual-machlne:~$ ntptrace localhost: stratum 3, offset -0.057878, synch distance 0.095064 120.88.46.10: tlned out, nothing received ***Request tlned out - m - -vlrtual-machlne:-$ |
FIGURE 4.13: NTP Enumeration Tool Screenshot
ntpdc:
This command will help you to query the ntpd daemon about its current state and to request changes in that state.
Syntax: ntpdc [-ilnps] [-c command] [hostname/!P_address]
europium.canonical.con 125.62.193.121 126-88-46-16.snat21.hn segnent-119-226.stfy .n ns3.ne1 *.con ntpdc> |
123 123 123 123 123
192.168.18.134 192.168.18.134 192.168.18.134 192.168.18.134 192.168.18.134
28 26 28 27 26
4 4 4 4 4
4 4 4 4 4
Ida ld0 ldO lde ldO
67 72 67 76 72
44 54 54 56 60
FIGURE 4.14: NTP Enumeration Tool Screenshot
ntpq:
This command will help you to monitor NTP daemon ntpd operations and determine performance.
ntpq [-inp] [-c command] [host/!P_address]
Module 04 Page 492
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Example:
ntpq> version ntpq 4.2.0 a @ l .1196-r Mon May 07 14:14:14 EDT 2006 ntpq> host current host is 192.168.0.1
al-machlne: chine:-$ ntpq
(1)
elay xit elp ost ostnanes eytd eytype associations opeers passociations peers readlist
mrea nrl nrv ntpv opee pass pass peer poll psta quit raw
615 leap_none, sync_ 6p3$l.2296-0 Tue Jun system"Linux/3.2.0o n 2 2 - , rootdelay=16 1608878 Fri, Aug 24 412cc Fri, Aug 24 2 .626, frequency86.8 elk wander=9.206
FIGURE 4.15: NTP Enumeration Screenshot
Module 04 Page 493
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Module Flow
Enumeration Concepts
NetBIOS Enumeration
SNMP Enumeration
UNIX/Linux Enumeration
DNS Enumeration
Enumeration Countermeasures
Enumeration Pen Testing
Copyright by
IC-Ccuncil. All
Rights Reserved. Reproduction is Strictly Prohibited.
M odule Flow
So far, we discussed what enumeration is and enumeration techniques to extract information related to network resources. Now it's time to discuss an enumeration technique that can extract information related to valid users on SMTP server, i.e., SMTP enumeration Enumeration Concepts t__5 NetBios Enumeration SNMP Enumertion Unix/Linux Enumeration
Ipc- V
! -
NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing
LDAP Enumeration
This section will familiarize you with how to get a list of valid users on the SMTP server and the tools that can test the process of sending email through the SMTP server
Module 04 Page 494
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
SMTP E num eration
CEH
SMTP Enum eration
SMTP Enumeration allows you to determine valid users on the SMTP server. This is accomplished with the help of three built-in SMTP commands. The three commands are: > VRFY -This command is used for validating users > EXPN -This command tells the actual delivery address of aliases and mailing lists > RCPT TO - It defines the recipients of the message SMTP servers respond differently to VRFY, EXPN, and RCPT TO commands for valid and invalid users. Thus, by observing the SMTP server response to these commands, one can easily determine valid users on the SMTP server. The attacker can also directly communicate with the SMTP server though the telnet prompt as follows: Using the SMTP VRFY Command
$ telnet 192.168.168.1 25 Trying 192.168.168.1... Connected to 192.168.168.1. Escape character is IA] 1.
Module 04 Page 495
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
220 NYmailserver ESMTP Sendmail 8.9.3 HELO 501 HELO requires domain address HELO x 250 NYmailserver Hello [10.0.0.86], pleased to meet you VRFY Jonathan 250 Super-User <Jonathan0NYmailserver> VRFY Smith 550 Smith... User unknown
Using the SMTP EXPN Command
$ telnet 192.168.168.1 25 Trying 192.168.168.1... Connected to 192.168.168.1. Escape character is 'A] '. 220 NYmailserver ESMTP Sendmail 8.9.3 HELO 501 HELO requires domain address HELO x 250 NYmailserver Hello [10.0.0.86], pleased to meet you EXPN Jonathan 250 Super-User <Jonathan@NYmailserver> EXPN Smith 550 Smith... User unknown
Using the SMTP RCPT TO Command
$ telnet 192.168.168.1 25 Trying 192.168.168.1 ... Connected to 192.168.168.1. Escape character is 'A] ' . 220 NYmailserver ESMTP Sendmail 8.9.3 HELO 501 HELO requires domain address HELO x 250 NYmailserver Hello [10.0.0.86], pleased to meet you MAIL FROM:Jonathan 250 Jonathan... Sender ok RCPT TO:Ryder 250 Ryder... Recipient ok RCPT TO: Smith 550 Smith... User unknown
Module 04 Page 496
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
1
Copyright by
I
EC-Council. All
http://www.netscontools.com
Rights Reserved. Reproduction is Strictly Prohibited.
SMTP Enum eration Tool: NetScanTools Pro
Source: http://www.netscantools.com NetScanTool Pro's SMTP Email Generator tool allows you to test the process of sending an email message through an SMTP server. You can extract all the common email header parameters including confirm/urgent flags. You can log the email session to the log file and then view the log file showing the communications between NetScanTools Pro and the SMTP server. NetScanTool Pro's Email Relay Testing Tool allows you to perform relay test by communicating with an SMTP server. The report includes a log of the communications between NetScanTools Pro and the target SMTP server.
Module 04 Page 497
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
1345803851 - NetScanTools Pro Demo Version Build 8-17-12 based on version 11.19
File Edit Accessibility View IPv6 Help
sA
a -j a 1a
Welcome Automated Tools Manual Tools (all)
*
Manual Tools SMTP Server Tests ^ Use this tool to send test SMTP messages and to check servers for email relaying. Jump To Automated SMTP mail server name (server.domarj.com or IP address requred) smtp. yourDomanNameGoesHere.com Reports Add to Favontes
Service Lookup
Send Test Message Stop Sendng Test Message Test Message Settings Global Test Settings HELO login ID SMTP Port 25 DELL| Network Timeout (sec) 15
Email Relay Testing Tests to run Your Sending Domain Name yourdomar.com Start SMTP Relay Test Stop Relay Test 01 02 03 04 05 06 07 View Relay Test Results 08 09 O vie w Results as Text () View Results in Web Browser dear Al Tests Set Al Tests 010 011 012 013 014 015 016 017
Sim ple Services
S
-
SMTP Server Tests
Favorite Tools Actrve Discovery Tools Passive Discovery Tools
View SMTP Log File Delete SMTP Log File
Packet Level Tools External Tools Program Info For Help, press F1
FIGURE 4.1: NetScanTools Pro Screenshot
Module 04 Page 498
Ethical Hacking and CountermeasuresCopyright by EC-C0lMCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Module Flow
Enumeration Concepts
NetBIOS Enumeration
SNMP Enumeration
UNIX/Linux Enumeration
SMTP Enumeration
Enumeration Countermeasures
Enumeration Pen Testing
i s
Copyright C by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
M odule Flow
So far, we have discussed enumeration concepts, how to enumerate NetBIOS, SNMP, UNIX/Linux, LDAP, NTP, SMTP, and what information you can get from those enumeration processes. Now we will discuss DNS enumeration and the information you can get from it. Enumeration Concepts t__1! NetBios Enumeration SNMP Enumertion Unix/Linux Enumeration LDAP Enumeration
1 ~ NTP Enumeration
SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing
w Ei
Iffc- V
Module 04 Page 499
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
This section describes DNS zone transfer enumeration and tools that can be used to extract DNS records.
Module 04 Page 500
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
DNS Zone Transfer Enumeration Using NSLookup
J It is a process of locating the DNS server and the records of a target network J An attacker can gather valuable network information such as DNS server
names, hostnames, machine names, user names, IP addresses of the potential targets, etc.
c EH
itfcM l M k M
J In a DNS zone transfer enumeration, an attacker tries to retrieve a copy of the
entire zone file for a domain from a DNS server
Command Prompt
C :\>nslookup
Default Server: nsl. example. com Address: 10.219.100.1
> server 192.168.234.110
Default Server: corp-dc.example2.org Address: 192.168.234.110 > Set type-any
> Is -d example2.org
[[192.168.234.110]] example2.org. SGA corp-dc.example2.org admin. example2.org. A 192.168.234.110 exa^ple2.org. NS corp-dc.example2.org g c . t c p SKV priority=0, weight=100, port=3268, corp-dc.exan*>le2.org _kerberos._tcp SRV priority=0, weight=100, port=88, corp-dc.exa1 9 le2 .org kpasswd. tcp SRV priority=0, weight=100, port=464, corp-dc.exanple2.org
Copyright C by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited
DNS Zone Transfer Enum eration U sing nslookup
The attacker performs DNS zone transfer enumeration for locating the DNS server and records of the target organization. Through this process, an attacker gathers valuable network information such as DNS server names, hostnames, machine names, user names, and IP addresses of potential targets. To perform DNS zone transfer enumeration, you can use tools such as nslookup, DNSstuff, etc. These tools enable you to extract the same information that an attacker gathers from the DNS servers of target organization. To perform a DNS zone transfer, you need to send a zone transfer request to the DNS server pretending to be a client; the DNS server then sends a portion of its database as a zone to you. This zone may contain a lot of information about the DNS zone network. To perform a DNS zone transfer, you need to send a zone transfer request to the DNS server pretending to be a client. In reply to your request, the DNS server transfers DNS records containing a lot of valuable network information, including IP address. The following screenshot shows how to perform DNS zone transfer using nslookup:
Module 04 Page 501
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Command Prompt C : \>nslookup
Default Server: nsl.example.com Address: 10.219.100.1
> server 192.168.234.110
Default Sarvar: eorp-de.axampla2.org Address: 192.168.234.110 > Set type-any
> Is
-d example 2 .org
t[192.168.234.110 example2.org. SOA corp-dc.example2.org admin. example2.org. A 192.168.234.110 example2.org. NS corp-dc.example2.org _gc._tcp SRV priority=0, weight=100, port=3268, corp-dc.example2.org _kerberos._tcp SRV priority=0, weight=100, port=88, corp-dc.example2.org _kpa.sswd._tcp SKV priority=0, weight=100, port=464, corp-dc.example2.org
FIGURE 4.17: DNS zone Transfer Screenshot
Module 04 Page 502
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Module Flow
Enumeration Concepts
NetBIOS Enumeration
SNMP Enumeration
UNIX/Linux Enumeration
SMTP Enumeration
DNS Enumeration
Enumeration Countermeasures
Enumeration Pen Testing
i s
Copyright by
IC-Ccuncil. All
Rights Reserved. Reproduction is Strictly Prohibited.
M odule Flow
So far, we have discussed what enumeration is, how to perform various types of enumeration, and what type of information an attacker can extract through enumeration. Now it's time to examine the countermeasures that can help you to keep attackers away from enumerating sensitive information from your network or host. Enumeration Concepts t__1 NetBios Enumeration SNMP Enumertion u Unix/Linux Enumeration LDAP Enumeration
NTP Enumeration SMTP Enumeration DNS Enumeration Enumeration Countermeasures Enumeration Pen Testing
This section focuses on how to avoid information leakage through SNMP, DNS, SMTP, LDAP, and SMB.
Module 04 Page 503
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Enum eration C ounterm easures
C EH
SN M P
9 R em ove th e S N M P agent or turn off the S N M P service If shutting off S N M P is not an option, then change the default "p u b lic " com m u n ity's nam e e Upgrade to S N M P 3 , which encrypts passwords and messages e Im plem ent the Group Policy security option called "A d d itio nal restrictions for anonym ous con n ectio n s" e Access to null session pipes, null session shares, and IPSec filtering should also be restricted
r
e
DNS
-V--
Disable the DNS zone transfers to the untrusted hosts
Make sure that the private hosts and their IP addresses are not published into DNS zone files of public DNS server
Use premium DNS registration services that hide sensitive information such as HINFO from public
Use standard network admin contacts for DNS registrations in order to avoid social engineering attacks
C-
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
Enum eration C ounterm easures
You can apply the following countermeasures to prevent information leakage through various types of enumeration.
'41
Q
SN M P Enum eration Counterm easures:
6 Remove the SNMP agent or turn off the SNMP service from your system. If shutting off SNMP is not an option, then change the default "public" community's name.
Upgrade to SNMP3, which encrypts passwords and messages. Implement the Group Policy security option called anonymous connections." "Additional restrictions for
Q Q S
Restrict access to null session pipes, null session shares, and IPSec filtering. Block access to TCP/UDP ports 161. Do not install the management and monitoring Windows component unless it is required.
Module 04 Page 504
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
IJ
Encrypt or authenticate using IPSEC.
DNS Enumeration Countermeasures:
S Configure all name servers not to send DNS zone transfers to unreliable hosts.
Check the publicly accessible DNS server's DNS zone files and ensure that the IP addresses in these files are not referenced by non-public hostnames. Q Q Make sure that the DNS zone files do not contain HINFO or any other records. Provide standard network administration contact details in Network Information Center Databases. This helps to avoid war-dialing or social engineering attacks.
Prune DNS zone files to prevent revealing unnecessary information.
Module 04 Page 505
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Enum eration C ounterm easures
( C o n t d)
UrlA H
c 1EH
ItbKJl
SMTP
J Configure SMTP servers to:
Q Q Ignore em ail messages to unknown recipients Not include sensitive mail server and local host inform ation in mail responses Q Disable open relay feature
LDAP
J
Use N TLM or basic authentication to limit access to known users only By default, LDAP traffic is transm itted unsecured; use SSL techn o lo gy to encrypt the traffic J Select a user nam e different from your em ail address and enable account lockout
Copyright C by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
Enum eration C ounterm easures (Contd)
(MSS SM TP:
Configure SMTP servers to: S Ignore email messages to unknown recipients. Not include sensitive mail server and local host information in mail responses. Q Disable open relay feature configuring SMTP servers. Ignore emails to unknown recipients by
LD AP:
Use NTLM or basic authentication to limit access to known users only. By default, LDAP traffic is transmitted unsecured; use SSL technology to encrypt the traffic. Select a user name different from your email address and enable account lockout.
Module 04 Page 506
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
SMB Enum eration C ou n term easu res
D isab lin g SMB
Ethernet Properties
CEH
Go to Eth ern et Prop erties
Networking Connect usng: j* Broadcom Netbnk (TM) Gigattf Ethernet
Select the Client for Microsoft K ' Networks and File and Printer Sharing for Microsoft Networks check boxes
This connection uses the folowng terns:
Configure
1 * <.
* F3c-:e:
|* File and Printer Shanng for Mcrosoft Networks | U ^- Microsoft Network Adapter Mubptexor Protocol 0 A - MKTosoft LLDP Protocol Driver 0 0 Link-Layer Topology Discovery Mapper 1/0 Driver *Link-Layer Topology Discovery Responder
Click Uninstall
Description
Allows your computer to access resources on a fAcrosoft
Follow th e uninstall steps
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
w SMB Enum eration C ounterm easures
Common sharing services or other unused services may prove to be doorways for attackers to break into your security. Therefore, you should disable these services to avoid information leakage or other types of attacks. If you don't disable these services, then you can be vulnerable enumeration. Server Message Block (SMB) is a service intended to provide shared access to files, serial ports, printers, and communications between nodes on a network. If this service is running on your network, then you will be at high risk of getting attacked. Therefore, you should disable it if not necessary, to prevent enumeration. Steps to disable SMB: 1. Go to Ethernet Properties. 2. Select the Client for M icrosoft N etw orks and File and Printer Sharing for M icrosoft N etw orks check boxes. 3. Click Uninstall. 4. Follow the uninstall steps.
Module 04 Page 507
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Ethernet Properties
N etw orking Connect using:
Broadcom N etLink (TM) Gigabit Ethernet Configure...
This connection uses the follow ing item s:
IHg Client for Microsoft Networks |
[0 A
M JHQ 0 S Packet Scheduler________________
File and Printer Sharing for M icrosoft Netw orks M icrosoft Netw ork Adapter M ultiplexor Protocol M icrosoft LLDP Protocol D river Link-Layer Topology Discovery M apper I/O D river Link-Layer Topology Discover) Responder
In stall.
U ninstall
Properties
D escription Allow s your com puter to access resources on a M icrosoft network.
OK
Cancel
FIGURE 4.18: Ethernet properties Screenshot
Module 04 Page 508
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Module Flow
CEH
Enumeration Concepts
NetBIOS Enumeration
SNMP Enumeration
UNIX/Linux Enumeration
SMTP Enumeration
DNS Enumeration
Enumeration Countermeasures
Copyright C by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
M odule Flow
This section describes the importance of enumeration pen testing, the framework of pen testing steps, and the tools that can be used to conduct pen testing.
Enumeration Concepts I 1 NetBios Enumeration
_
NTP Enumeration SMTP Enumeration
/A
SNMP Enumertion Unix/Linux Enumeration
b ^ ' DNS Enumeration Enumeration Countermeasures
is: >
LDAP Enumeration
Enumeration Pen Testing
Module 04 Page 509
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
E num eration Pen Testing
Used to identify valid user accounts or poorly protected resource shares using active connections to systems and directed queries
CEH
The information can be users and groups, network resources and shares, and applications
Used in combination with data collected in the reconnaissance phase
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
Enum eration Pen Testing
Through enumeration, an attacker may gather sensitive information of organizations if the security is not strong. He or she may then use that sensitive information to hack and break into the organization's network. If an attacker breaks into the organization, then the organization potentially faces huge losses in terms of information, service, or finance. Therefore, to avoid these kinds of attacks, every organization must test its own security. Testing the security of an organization legally against enumeration is called enumeration pen testing. Enumeration pen testing is conducted with the help of the data collected in the reconnaissance phase. As a pen tester, conduct enumeration penetration tests to check whether the target network is revealing any sensitive information that may help an attacker to perform a well-planned attack. Apply all types of enumeration techniques to gather sensitive information such as user accounts, IP address, email contacts, DNS, network resources and shares, application information, and much more. Try to discover as much information as possible regarding the target. This helps you determine the vulnerabilities/weaknesses in the target organization's security.
Module 04 Page 510
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
E num eration Pen Testing
( Co nt d)
^
- *
S TA R T
r nr
Use tools such as W hois Lookup
v
Calculate the subnet mask
...<
Use Subnet Mask Calculators In order to enumerate important servers, Use tools such as Nmap (nmap sPcnetworkrange>) find the network range using tools such as W hois Lookup Calculate the subnet mask required for the IP range as an input to many of the ping sweep and port scanning tools by using Subnet Mask Calculators Find the servers connected to the Internet using tools such as Nmap Perform port scanning to check for the open ports on the nodes using tools such as Nmap
V
Undergo host discovery
V
Perform port scanning
' Use tools such as Nmap (nmap sS<networkrange>)
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
You should conduct all possible enumeration techniques to enumerate as much information as possible about the target. To ensure the full scope of the test, enumeration pen testing is divided into steps. This penetration test includes a series of steps to obtain desired information. Stepl: Find the network range If you want to break into an organization's network, you should know the network range first. This is because if you know the network range, then you can mask yourself as a user falling within the range and then try to access the network. So the first step in enumeration pen testing is to obtain information about network range. You can find the network range of target organization with the help of tools such as Whois Lookup. Step 2: Calculate the subnet mask Once you find the network rage of the target network, then calculate the subnet mask required for the IP range using tools such as Subnet Mask Calculator. You can use the calculated subnet mask as an input to many of the ping sweep and port scanning tools for further enumeration, which includes discovering hosts and open ports.
ua
Enum eration Pen T esting (Contd)
Module 04 Page 511
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Step 3: Undergo host discovery Find the important servers connected to the Internet using tools such as Nmap. The Nmap syntax to find the servers connected to Internet is as follows: nmap - sP <network-range>. In place of the network range, enter the network range value obtained in the first step. Step 4: Perform port scanning It is very important to discover the open ports and close them if they are not required. This is because open ports are the doorways for an attacker to break into a target's security perimeter. Therefore, perform port scanning to check for the open ports on the nodes. This can be accomplished with the help of tools such as Nmap.
Module 04 Page 512
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
E num eration Pen Testing
(C o n td)
J
CEH
M
Perform DNS enumeration
V
Use W indow s utility NSLookup
Perform DNS enumeration using Windows utility NSLookup
Perform NetBIOS enumeration using tools such as SuperScan, Hyena, and Winfingerprint
J
Use tools such as SuperScan, Hyena, and Winfingerprint
Perform SNM P enumeration using tools such as OpUtils Network Monitoring Toolset and SolarWinds IP Network Browser
Perform NetBIOS enumeration
V
.....
Perform Unix/Linux enumeration using tools such as Enum4linux
Perform SNMP enumeration
V
....
Use tools such as OpUtils and Solarwinds IP Network Browser
Perform Unix/Linux enumeration
Use tools such as Enum4linux
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
Enum eration Pen T esting (Contd)
Step 5: Perform DNS enumeration Perform DNS enumeration to locate all the DNS servers and their records. The DNS servers provide information such as system names, user names, IP addresses, etc. You can extract all this information with the help of the Windows utility nslookup. Step 6: Perform NetBIOS enumeration Perform NetBIOS enumeration to identify the network devices over TCP/IP and to obtain a list of computers that belong to a domain, a list of shares on individual hosts, and policies and passwords. You can perform NetBIOS enumeration with the help of tools such as SuperScan, Hyena, and WinFingerprint. Step 7: Perform SNMP enumeration Perform SNMP enumeration by querying the SNMP server in the network. The SNMP server may reveal information about user accounts and devices. You can perform SNMP enumeration using tools such as OpUtils and SolarWinds IP Network Browser.
Module 04 Page 513
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
Step 8: Perform Unix/Linux enumeration Perform Unix/Linux enumeration using tools such as Enum4linux. You can use commands such as showmount, Finger, rpfinfo (RPC), and rpcclient etc.to enumerate UNIX network resources.
Module 04 Page 514
Ethical Hacking and Countermeasures Copyright by EC-COUIlCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
E num eration Pen Testing
(C o n td)
CEH
Perform LDAP enumeration
Use tools such as Softerra LDAP Administrator
Perform LDAP enumeration using tools such as Softerra LDAP Administrator 8 Perform NTP enumeration using commands such as ntptrace, ntpdc, and ntpq Perform SMTP enumeration using tools such as NetScanTools Pro
V Perform NTP enumeration
Use commands such as ntptrace, ntpdc, and ntpq
# ^
Use tools such as NetScanTools Pro
ttwt
Perform SMTP enumeration
Copyright by IC-Ccuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
Enum eration Pen T esting (Contd)
Step 9: Perform LDAP enumeration Perform LDAP enumeration by querying the LDAP service. By querying the LDAP service you can enumerate valid user names, departmental details, and address details. You can use this information to perform social engineering and other kinds of attacks. You can perform LDAP enumeration using tools such as Softerra LDAP Administrator. Step 10: Perform NTP enumeration Perform NTP enumeration to extract information such as host connected to NTP server, client IP address, OS running of client systems, etc. You can obtain this information with the help of commands such as ntptrace, ntpdc, and ntpq. Step 11: Perform SMTP enumeration Perform SMTP enumeration to determine valid users on the SMTP server. You can use tools such as NetScanTools Pro to query the SMTP server for this information. Step 12: Document all the findings The last step in every pen test is documenting all the findings obtained during the test. You should analyze and suggest countermeasures for your client to improve their security.
Module 04 Page 515 Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Ethical Hacking and Countermeasures Enumeration
Exam 312-50 Certified Ethical Hacker
M odule Sum m ary
Enumeration is defined as the process of extracting user names, machine names, network resources, shares, and services from a system Simple Network Management Protocol (SNMP) is a TCP/IP protocol used for remote monitoring and managing hosts, routers, and other devices on a network
CEH
MIB is a virtual database containing formal description of all the network objects that can be managed using SNMP Devices like switches, hubs, and routers might still be enabled with a "default password" that enables an attacker to gain unauthorized access to the organization computer network
Attacker queries LDAP service to gather information such as valid user names, addresses, departmental details, etc. that can be further used to perform attacks Network Time Protocol (NTP) is designed to synchronize clocks of networked computers
Copyright ffi by IC-Cuncil. All Rights Reserved. Reproduction is Strictly Prohibited.
y' X
^ M odule Summary
Q Enumeration is defined as the process of extracting usernames, machine names, network resources, shares, and services from a system. Simple Network Management Protocol (SNMP) is a TCP/IP protocol used for remote monitoring and managing hosts, routers, and other devices on a network. 6 MIB is a virtual database containing formal description of all the network objects that can be managed using SNMP. Devices like switches, hubs, and routers might still be enabled with a "default password" that enables an attacker to gain unauthorized access to the organization computer network.
Q Attacker queries LDAP service to gather information such as valid usernames, addresses, departmental details, etc. that can be further used to perform attacks. Q Network Time Protocol (NTP) is designed to synchronize clocks of networked computers.
Module 04 Page 516
Ethical Hacking and Countermeasures Copyright by EC-C0UnCil All Rights Reserved. Reproduction is Strictly Prohibited.
Das könnte Ihnen auch gefallen
- CEHv8 Module 05 System HackingDokument620 SeitenCEHv8 Module 05 System HackingAboubacar Beckham CamaraNoch keine Bewertungen
- CEHv8 Module 02 Footprinting and Reconnaissance PDFDokument171 SeitenCEHv8 Module 02 Footprinting and Reconnaissance PDFMehrdad88% (8)
- CEHv8 Module 13 Hacking Web Applications PDFDokument263 SeitenCEHv8 Module 13 Hacking Web Applications PDFMehrdadNoch keine Bewertungen
- CEHv8 Module 17 Evading IDS, Firewalls, and Honeypots PDFDokument142 SeitenCEHv8 Module 17 Evading IDS, Firewalls, and Honeypots PDFMehrdad100% (3)
- CEHv8 Module 12 Hacking Webservers PDFDokument123 SeitenCEHv8 Module 12 Hacking Webservers PDFMehrdadNoch keine Bewertungen
- CEHv8 Module 03 Scanning NetworksDokument172 SeitenCEHv8 Module 03 Scanning NetworksMiles GelidusNoch keine Bewertungen
- CEHv8 ReferencesDokument82 SeitenCEHv8 ReferencesMiles GelidusNoch keine Bewertungen
- CEH v8 Labs Module 09 Social Engineering PDFDokument28 SeitenCEH v8 Labs Module 09 Social Engineering PDFMehrdadNoch keine Bewertungen
- ETHICAL HACKING TECHNIQUESDokument12 SeitenETHICAL HACKING TECHNIQUESmani3686Noch keine Bewertungen
- CEHV8 Module 01 Introduction To Ethical Hacking PDFDokument90 SeitenCEHV8 Module 01 Introduction To Ethical Hacking PDFMehrdad100% (5)
- DOS AttackDokument54 SeitenDOS Attacksrinut31100% (3)
- CEHv8 Module 06 Trojans and Backdoors PDFDokument179 SeitenCEHv8 Module 06 Trojans and Backdoors PDFMehrdad100% (3)
- Cyber Forensics and Ethical HackingDokument27 SeitenCyber Forensics and Ethical HackingLeandro LisaNoch keine Bewertungen
- CEHV8 Module 01 Introduction To Ethical HackingDokument90 SeitenCEHV8 Module 01 Introduction To Ethical HackingCh Mohammad ZiaNoch keine Bewertungen
- A Presentation On Ethical HackingDokument30 SeitenA Presentation On Ethical Hackingʚĩɞ IkRàm AkCha ʚĩɞ100% (1)
- CEHv8 Module 11 Session Hijacking PDFDokument97 SeitenCEHv8 Module 11 Session Hijacking PDFMehrdad100% (1)
- Portals 0 Images CEH-brochureDokument12 SeitenPortals 0 Images CEH-brochureAnOop KaUshalNoch keine Bewertungen
- CEHv8 Module 19 Cryptography PDFDokument90 SeitenCEHv8 Module 19 Cryptography PDFMehrdad100% (2)
- Ethical Hacking and Countermeasures Threats and Defense Mechanisms PDFDokument2 SeitenEthical Hacking and Countermeasures Threats and Defense Mechanisms PDFJonathan0% (1)
- SQL Injection Attack LabDokument9 SeitenSQL Injection Attack Labmadhucisco madhuNoch keine Bewertungen
- CEHv8 Module 08 SniffingDokument180 SeitenCEHv8 Module 08 SniffingMiles GelidusNoch keine Bewertungen
- CEHv6 Module 01 Introduction To Ethical HackingDokument69 SeitenCEHv6 Module 01 Introduction To Ethical HackingfaliqulaminNoch keine Bewertungen
- Cehv10 Version Change DocumentDokument62 SeitenCehv10 Version Change DocumentVijay GopalNoch keine Bewertungen
- What Is Ethical Hacking..?Dokument13 SeitenWhat Is Ethical Hacking..?RayeesNoch keine Bewertungen
- Ethical Hacking: BSC Computer ScienceDokument31 SeitenEthical Hacking: BSC Computer SciencePawan MahalleNoch keine Bewertungen
- Ethical HarkingDokument18 SeitenEthical HarkingMakinde Yung FreemanNoch keine Bewertungen
- Preventing Successful Spear Phishing Attacks: Defense-In-DepthDokument2 SeitenPreventing Successful Spear Phishing Attacks: Defense-In-Depthlazaro MouraNoch keine Bewertungen
- Introduction To HackingDokument8 SeitenIntroduction To HackingvasugtkNoch keine Bewertungen
- CEH v8 Labs Module 00 PDFDokument4 SeitenCEH v8 Labs Module 00 PDFMehrdadNoch keine Bewertungen
- DemoPasswordManager v1.0Dokument28 SeitenDemoPasswordManager v1.0Rajesh1146Noch keine Bewertungen
- CISEv2-Learn Ethical HackingDokument6 SeitenCISEv2-Learn Ethical HackingDinesh Chauhan100% (1)
- Writing Alphanumeric ShellcodeDokument20 SeitenWriting Alphanumeric ShellcodeVasileXXL5Noch keine Bewertungen
- CEH v8 Labs Module 14 SQL Injection PDFDokument37 SeitenCEH v8 Labs Module 14 SQL Injection PDFMehrdadNoch keine Bewertungen
- The Cyber Crime Hall of Fame - The Phone Masters Case, by Asad SyedDokument12 SeitenThe Cyber Crime Hall of Fame - The Phone Masters Case, by Asad SyedAsad SyedNoch keine Bewertungen
- CEHv8 Module 00 PDFDokument26 SeitenCEHv8 Module 00 PDFMehrdad100% (1)
- Ethical Hacking PDFDokument127 SeitenEthical Hacking PDFPrudhvi MaheshwaramNoch keine Bewertungen
- Introduction To Ethical Hacking - Foot Printing and Reconnaissance - Scanning Networks - Enumeration - System Hacking - Malware Threats - SniffingDokument40 SeitenIntroduction To Ethical Hacking - Foot Printing and Reconnaissance - Scanning Networks - Enumeration - System Hacking - Malware Threats - Sniffingjaya prasanna100% (1)
- Computer Virus (Trojan Horse & Salami Attack)Dokument9 SeitenComputer Virus (Trojan Horse & Salami Attack)Muhammad Faiz50% (2)
- Windows XP Privilege Escalation ExploitDokument3 SeitenWindows XP Privilege Escalation Exploitgauth92Noch keine Bewertungen
- Cyber Awareness 2 0 2 1: BY Ayokunle OlaniyiDokument31 SeitenCyber Awareness 2 0 2 1: BY Ayokunle OlaniyiOludare OgunkoyaNoch keine Bewertungen
- CS409 Cryptography and Network SecurityDokument2 SeitenCS409 Cryptography and Network Securityjikku thomasNoch keine Bewertungen
- Cyber Security Unit - VDokument67 SeitenCyber Security Unit - VDeepak kumarNoch keine Bewertungen
- Cyber Security Essentials ReportDokument34 SeitenCyber Security Essentials Reportharika sweety100% (1)
- Ethical Hacking Unit 1 - Full NotesDokument87 SeitenEthical Hacking Unit 1 - Full NotesDineshNoch keine Bewertungen
- Up-To-Date 312-50 Eccouncil Certified Ethical Hacker v10 (2019) PDF Exam DemoDokument5 SeitenUp-To-Date 312-50 Eccouncil Certified Ethical Hacker v10 (2019) PDF Exam DemoDavidEButlerNoch keine Bewertungen
- Kyrion Ethical Hacking Workshop Handouts PDFDokument43 SeitenKyrion Ethical Hacking Workshop Handouts PDFKaran MehtaNoch keine Bewertungen
- Ethical Hacking IbmDokument20 SeitenEthical Hacking Ibmsviggnesh_hpNoch keine Bewertungen
- Dark Hotel APTDokument21 SeitenDark Hotel APTAnupam TiwariNoch keine Bewertungen
- Writing Sample On Cyber Defense OrganizationDokument21 SeitenWriting Sample On Cyber Defense Organizationgarret021Noch keine Bewertungen
- CEHv8 Module 09 Social Engineering PDFDokument110 SeitenCEHv8 Module 09 Social Engineering PDFMehrdad100% (5)
- CEH v5 Module 01 Introduction To Ethical HackingDokument43 SeitenCEH v5 Module 01 Introduction To Ethical HackingNghia Tran VanNoch keine Bewertungen
- Ethical Hacking DefinitionDokument8 SeitenEthical Hacking DefinitionMilton CuencaNoch keine Bewertungen
- Ethical Hacking Choosing The Right Pathway Whitepaper 1Dokument7 SeitenEthical Hacking Choosing The Right Pathway Whitepaper 1Tony PresNoch keine Bewertungen
- Analyzing and Implementing of Network Penetration TestingDokument48 SeitenAnalyzing and Implementing of Network Penetration TestingEngr. Md Yusuf MiahNoch keine Bewertungen
- CEH Sample Questions - Vamsi Krishna PDFDokument7 SeitenCEH Sample Questions - Vamsi Krishna PDFvamsi krishnaNoch keine Bewertungen
- Insecure Mag 47Dokument81 SeitenInsecure Mag 47DimitarNoch keine Bewertungen
- Phishing Detection And Response A Complete Guide - 2019 EditionVon EverandPhishing Detection And Response A Complete Guide - 2019 EditionNoch keine Bewertungen
- Cyber threat intelligence A Complete Guide - 2019 EditionVon EverandCyber threat intelligence A Complete Guide - 2019 EditionNoch keine Bewertungen
- Trends in Cloud ComputingDokument56 SeitenTrends in Cloud ComputingLiene LoNoch keine Bewertungen
- CloudDokument152 SeitenCloudMuh AkbarNoch keine Bewertungen
- Christopher Human Reality - Unlocked PDFDokument616 SeitenChristopher Human Reality - Unlocked PDFFrater CattusNoch keine Bewertungen
- CEHv8 Module 20 Penetration Testing PDFDokument104 SeitenCEHv8 Module 20 Penetration Testing PDFMehrdad100% (1)
- CEHV8 Module 01 Introduction To Ethical Hacking PDFDokument90 SeitenCEHV8 Module 01 Introduction To Ethical Hacking PDFMehrdad100% (5)
- CEHv8 Module 19 Cryptography PDFDokument90 SeitenCEHv8 Module 19 Cryptography PDFMehrdad100% (2)
- CEHv8 Module 14 SQL Injection PDFDokument148 SeitenCEHv8 Module 14 SQL Injection PDFMehrdad100% (2)
- CEHv8 Module 16 Hacking Mobile Platforms PDFDokument157 SeitenCEHv8 Module 16 Hacking Mobile Platforms PDFMehrdad100% (2)
- CEHv8 Module 11 Session Hijacking PDFDokument97 SeitenCEHv8 Module 11 Session Hijacking PDFMehrdad100% (1)
- CEHv8 References PDFDokument82 SeitenCEHv8 References PDFMehrdadNoch keine Bewertungen
- CEHv8 Module 06 Trojans and Backdoors PDFDokument179 SeitenCEHv8 Module 06 Trojans and Backdoors PDFMehrdad100% (3)
- CEHv8 Module 10 Denial of Service PDFDokument101 SeitenCEHv8 Module 10 Denial of Service PDFMehrdadNoch keine Bewertungen
- CEHv8 Module 15 Hacking Wireless Networks PDFDokument258 SeitenCEHv8 Module 15 Hacking Wireless Networks PDFMehrdadNoch keine Bewertungen
- CEHv8 Module 07 Viruses and Worms PDFDokument106 SeitenCEHv8 Module 07 Viruses and Worms PDFMehrdad100% (1)
- CEHv8 Module 18 Buffer Overflow PDFDokument91 SeitenCEHv8 Module 18 Buffer Overflow PDFMehrdadNoch keine Bewertungen
- CEH v8 Labs Module 19 Cryptography PDFDokument52 SeitenCEH v8 Labs Module 19 Cryptography PDFMehrdadNoch keine Bewertungen
- CEHv8 Module 05 System Hacking PDFDokument310 SeitenCEHv8 Module 05 System Hacking PDFMehrdadNoch keine Bewertungen
- CEHv8 Module 03 Scanning Networks PDFDokument172 SeitenCEHv8 Module 03 Scanning Networks PDFMehrdad100% (2)
- CEHv8 Module 00 PDFDokument26 SeitenCEHv8 Module 00 PDFMehrdad100% (1)
- CEHv8 Module 09 Social Engineering PDFDokument110 SeitenCEHv8 Module 09 Social Engineering PDFMehrdad100% (5)
- CEH v8 Labs Module 13 Hacking Web Applications PDFDokument20 SeitenCEH v8 Labs Module 13 Hacking Web Applications PDFMehrdadNoch keine Bewertungen
- CEH v8 Labs Module 12 Hacking Webservers PDFDokument31 SeitenCEH v8 Labs Module 12 Hacking Webservers PDFMehrdadNoch keine Bewertungen
- CEH v8 Labs Module 15 Hacking Wireless Networks PDFDokument28 SeitenCEH v8 Labs Module 15 Hacking Wireless Networks PDFMehrdad100% (1)
- CEH v8 Labs Module 18 Buffer Overflow PDFDokument13 SeitenCEH v8 Labs Module 18 Buffer Overflow PDFMehrdadNoch keine Bewertungen
- CEH v8 Labs Module 07 Viruses and Worms PDFDokument55 SeitenCEH v8 Labs Module 07 Viruses and Worms PDFMehrdad100% (1)
- Intermec SR30 PDFDokument56 SeitenIntermec SR30 PDFAlex RaduNoch keine Bewertungen
- TNZ Visitor Experience Monitor - 2011-12Dokument45 SeitenTNZ Visitor Experience Monitor - 2011-12Stewart HaynesNoch keine Bewertungen
- VSAT ManualDokument170 SeitenVSAT Manualchuchomat87Noch keine Bewertungen
- UH5300Dokument16 SeitenUH5300Merck Millipore Brasil - Lab Supply BrasilNoch keine Bewertungen
- GCTC Public Wifi BlueprintDokument74 SeitenGCTC Public Wifi BlueprintepraetorianNoch keine Bewertungen
- Module 1.1 Connecting To An SIUE Oracle Server Using PuTTYDokument21 SeitenModule 1.1 Connecting To An SIUE Oracle Server Using PuTTYkamakom780% (1)
- Mohammed Zahed - CVDokument4 SeitenMohammed Zahed - CVrash_babaNoch keine Bewertungen
- NCR Hp6592Dokument2 SeitenNCR Hp6592k19ajayNoch keine Bewertungen
- Allot SNMP Integration (16.5 and NW-S 15.3) v10 b9Dokument238 SeitenAllot SNMP Integration (16.5 and NW-S 15.3) v10 b9Ale CNoch keine Bewertungen
- Resolving Common Citrix IssuesDokument4 SeitenResolving Common Citrix IssuesHaraprasad MahapatroNoch keine Bewertungen
- Software-Defined NetworkingDokument11 SeitenSoftware-Defined NetworkingAhmed Zehara (IDPP)Noch keine Bewertungen
- PDH SDH PresentationDokument67 SeitenPDH SDH PresentationDanish Ahmed100% (2)
- ASA NAT Cheat Sheet For 8.2 and 8.4 UpdateDokument5 SeitenASA NAT Cheat Sheet For 8.2 and 8.4 UpdateSachin GudaNoch keine Bewertungen
- Configure A Site-To-Site UsingVTI On ASADokument6 SeitenConfigure A Site-To-Site UsingVTI On ASATapan DoshiNoch keine Bewertungen
- Product Data Sheet AMS Trex Device CommunicatorDokument9 SeitenProduct Data Sheet AMS Trex Device CommunicatorSardar PerdawoodNoch keine Bewertungen
- Bluetooth audio board schematicDokument1 SeiteBluetooth audio board schematicMoises CastroNoch keine Bewertungen
- CCNA Cisco Network Fundamentals Final Exam-Practice (Ver 4.0)Dokument23 SeitenCCNA Cisco Network Fundamentals Final Exam-Practice (Ver 4.0)sabriel69100% (1)
- Basic Principles of WCDMA System PDFDokument250 SeitenBasic Principles of WCDMA System PDFAli Abbas100% (1)
- TLE-Test-6 First Quarter 2017Dokument3 SeitenTLE-Test-6 First Quarter 2017Joy Angelique JavierNoch keine Bewertungen
- Manuals or User Guides HP LaserJet Pro MFP M225 PDFDokument146 SeitenManuals or User Guides HP LaserJet Pro MFP M225 PDFdragan44Noch keine Bewertungen
- Modulation Schemes (ERAN12.1 04)Dokument142 SeitenModulation Schemes (ERAN12.1 04)CosminD100% (1)
- 2012 LED/LCD TV Engineering Guide: XXLM760S-ZBDokument69 Seiten2012 LED/LCD TV Engineering Guide: XXLM760S-ZBWmadNoch keine Bewertungen
- iQBC Course SyllabusDokument5 SeiteniQBC Course SyllabusNinoNoch keine Bewertungen
- WGU Program Guidebook - BSCLSA (Bachelor of Science, Cloud and Systems Administration)Dokument21 SeitenWGU Program Guidebook - BSCLSA (Bachelor of Science, Cloud and Systems Administration)jwawaNoch keine Bewertungen
- 10.2.1.9 Lab - Configure A Site-To-Site IPsec VPN Using ISR CLI and ASA 5505 ASDMDokument22 Seiten10.2.1.9 Lab - Configure A Site-To-Site IPsec VPN Using ISR CLI and ASA 5505 ASDMerojasNoch keine Bewertungen
- USA Raymarine Brochure 2016 LowDokument92 SeitenUSA Raymarine Brochure 2016 LowJANAKIRAMANNoch keine Bewertungen
- 4.1 Data CenterDokument26 Seiten4.1 Data CenterPramod PawarNoch keine Bewertungen
- ERNW Checklist Tomcat7 HardeningDokument13 SeitenERNW Checklist Tomcat7 HardeningKarthikNoch keine Bewertungen
- Empowerment TechnologyDokument18 SeitenEmpowerment TechnologyLorenzo Cagula Jr.Noch keine Bewertungen
- IAD (DV-2010) : USER ManualDokument46 SeitenIAD (DV-2010) : USER ManualStein ChenNoch keine Bewertungen