Beruflich Dokumente
Kultur Dokumente
Adhoc Network
Hochgeladen von
Manoj Kumar GOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Adhoc Network
Hochgeladen von
Manoj Kumar GCopyright:
Verfügbare Formate
Hacking Resistance Protocol for Securing
Passwords Using Personal Device
L. Shyamala Kumari
1
and P. Deepa Rani
2
Department of Computer Science and Engineering, Pandian Saraswathi Yadav Engineering College,
Arasanoor, Sivagangai Dt., Tamil Nadu, India
E-mail:
I
shyamala.cl@gmail.com;
2
deepa.murugan24@gmail.com
Abstract-Users passwords are prone to h stolen and
compromised under dierent threats and vulnerabilities.
Firstly, users often select weak passwords and reuse the
same passwords across diferent websites. An adversary
can launch several password stealing attacks to snatch
passwords, such as phishing, ke loggers and malware. In this
paper, we design a hacking resistance protocol for system
access (ogin) and other applications requiring authentication
that is secure against passive attacks based on replaying
captured reusable passwords. This protocol was evolved
from the SIKEY (SIKEY is a trademark of Bell core). The
authentication system described in this document uses a
secret pass-phrase to generate a sequence of one-time
passwords. With this system, the user's secret pass-phrase
never needs to cross the network at any time such as during
authentication or during pass-phrase changes. Thus, it is
not vulnerable to replay attacks. Added securit is provided
by the propert that no secret information need be stored on
any system, including the server being protected The securit
of the system is based on the non-invert abilit of a secure
hash function. Such a function must be tractable to compute
in the forward direction, but computationally infeasible to
invert. This protocol leverages a user's cell phone and
short message service to thwart password hacking.
Keyords: Network Securit, Hacking Resistance, Password
Stealing, One-Time Password, Hash Function.
I. INTRODUCTION
Generally, password-based user authentication can resist
brute force and dictionary attacks [10], [18] i users
select strong passwords to provide sufcient entropy.
However, password-based user authentication has a major
problem that humans are not experts in memorizing text
stings[3]. Tus, most users would choose easy-to-remember
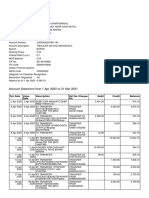
passwords [13]. Figure 1 shows the analysis of password
selection by user. Another problem is that users tend to
reuse passwords across various websites. Password reuse
causes users to lose sensitive information stored in diferent
websites if a hacker compromises one of their passwords
[14]. The above problems are caused by the negative
infuence of human factors. Therefore, it is important to
978-1-4673-4603-0/12/$31.00 2012 IEEE
take human factors into consideration when designing a
hacking resistance protocol. Up to now, researchers have
investigated a variety of technology to reduce the negative
infuence of human factors in the user authentication
procedure. Since humans a more adept in remembering
graphical passwords [15], [1] many graphical password
schemes were designed to address human's password
recall problem. Using password management tools is an
alternative. These tools automatically generate strong
passwords for each website, which addresses password
reuse and password recall problems. The advantage is that
users only have to remember a master password to access
the management tool. Despite the assistance of these two
technologies- graphical password [ 8] and password
management tool the user authentication system still
sufers fom some considerable drawbacks.
Some researches focus on the three-factor authentication
rather than password-based authentication to provide more
reliable user authentication. Three-factor authentication
[12] depends on what you know (e.g., password), what
you have (e.g., token), and who you are (e.g., biometric).
To pass the authentication, the user must input a password
and provide a pass code generated by the token (e.g.,
RSA SecureID), and scan her biometric feat ures (e.g.,
fingerprint or pupi l ). Three-factor authentication is a
comprehensive defense mechanism against password
stealing attacks, but it requires comparative high cost.
Although many banks support two-factor authentication
[6] [7], it still suffers fom the nonnegative infuence of
human factors, such as the password reuse attack. Users
have to memorize another four-digit PIN code to work
together with the token, for example RSA Secure ID. In
addition, users easily forget to bring the token. In this
paper, a hacking resistance protocol is proposed which
leverages a user's cell phone and short message service
(SMS) to prevent the password stealing and password
reuse attacks. It is difcult to thwart password reuse
attacks from any scheme where the users have to
remember something. The main cause of stealing
password attacks is when users type passwords to the
main concept of this protocol is fee users fom having to
remember or type any passwords into conventional
Hacking Resistance Protocol for Securing Passwords Using Personal Device 45
computers for authentication. Unlike generic and the
user authentication, this protocol involves a new
component, the cl phone, which is used to generate one
time passwords and a new communication channel used
to transmit messages.
II. BACKGROUND
Hacking resistance protocol adopts the one-time password
strategy therefore, the strategy is given later. We also
describe the secure features of SMS channel and explain
why SMS can be trusted. Finally, we introduce the security
of 3G connection used in the registration and recovery
phases.
Only upper cas
Only lower cse
Only numeric
Contins special chara(ers
FIG. 1: ANALYSIS OF PASSWORD SELECTION
A. One-Time Password
Te one-time passwords are generated by a secure one-way
hash function. With a given input, the set of one- time
passwords is established by a hash chain through multiple
hashing [16]. Assuming we wish to prepare one-time
passwords, the frst of these passwords is produced by
performing hashes on input c.
00= J(c) . . . (1)
The next one-time password is obtained by performing
N -1 hashes.
0, = J-'(c) ... (2)
Hence, the general formula is given as follows:
OJ=Jj(c) . . . (3)
For security reasons, we use these one-time passwords in
reverse order, i.e., using ON.'ON_2 ....... oo. If an old one-time
password is leaked, the attacker is unable to derive the next
one. Besides, the input c is derived fom a long-term
password (Pu), the identity of server (IDs), and a random
seed (<) generated by the server.
C = H(PuIIIDsll<) ... (4)
Note that function is a hash which IS ireversible in
general cryptographic assumption.
B. SMS Channel
A we know, SMS is a fndamental service of telecom,
which belongs to 3GPP standards [17]. SMS represents the
most successfl data transmission of telecom systems; hence,
it is the most wide- spread mobile service [11] in the world.
Besides the above advantages, we chose SMS channel
because of its security benefts. SMS represents the most
successful data transmission of telecom systems; hence, it is
the most wide spread mobile service in the world. Besides
the above advantages, we chose SMS channel because of
its security benefts. Unlike conventional authentication
protocols, users securely tansfer sensitive messages to servers
witout relying on untsted kiosks. Tis protocol resists
password stealing attacks since it is based on SMS chanels.
C. JO Connection
Te hacking resistance protocol utilizes the securit features of
3G connection [19] to develop te convenient account
registation ad recover procedures. Users can securely
tasmit ad receive inforation to the web site through a 3G
connection.
III. ARCHITECTURE AND ASSUMPTIONS
In this section we introduce the architecture of our hacking
resistat protocol system and make some reasonable
assumptions.
A. Architecture
For users to perfor secure login on an usted computer
(kiosk), the protocol consists of a tsted cell phone, a
browser on the kiosk, and a web server that users wish to
access. The user operates her cell phone and the untsted
computer directly to accomplish secure logins to the web
server. The communication between the cell phone and the
web server is through the SMS channel. The web browser
interacts with the web server via the Interet. In our
protocol design, we require the cell phone interact directly
with the kiosk. The general approach is to select available
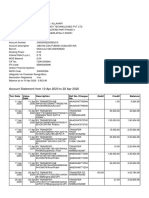
interfaces on the cell phone, Wi-Fi or Bluetooth. Fig. 2
shows the architecture of hacking resistance protocol.
r
,
L
+ S3S1.... l
"''.''
./" .....
FIG. 2: ARCHITECTURE OF HCKING RESISTANCE PROTOCOL
4b0 Proceedings of7
h
International Conference on Intelligent Systems and Control (ISCO 20!J)
B. Assumptions
Te assumptions in resistant protocol system are as follows:
Each web server possesses a unique phone number.
Via the phone nwnber, users can interact with each
website through an SMS channel.
The users' cell phones are malware-free. Hence, users
safely input the long-term passwords into cell phones.
The telecommunication service provider (TSP) will
participate in the registration and recovery phases. The
TSP is a bridge between subscribers and web servers. It
provides a service for subscribers to perform the
registation ad recovery progress with each web service.
Users connect to the TSP via 3G connections [19] to
protect the transmission.
The TSP and the web server establish a secure sockets
layer (SSL) tunnel. Via SSL protocol, the TSP can
verif the server by its certifcate to prevent phishing
attacks. With the aid of TSP, the server can receive
the correct Tsent from the subscriber.
If a user loses her cell phone, she can notif her
TSP t disable her lost SIM card and apply a new
cad wit te sae phone nwnber. Terefore, the user can
perform the recovery phase using a new cell phone.
IV. HCKING RESISTANCE PROTOCOL
I this section, we present a protocol fom the user perspective
to show operation fows. This protocol consists of
registration, login, and recovery phases. We introduce the
details of these three phases respectively.
A. Overview
Te protocol utilizes a user's cell phone as a authentication
token and SMS as a secure channel. Diferent fom regular
login processes, additional steps are required for the protocol.
In the registration phase, a user starts the protocol program
to register her new account on the website. Unlike
conventional registration, the server requests for te user's
account id and phone number, instead of password.
The program automatically sends a registration SMS
message to the server for completing the registation procedure.
Te protocol also designed a recovery phase to fx problems
in some conditions, such as losing one's cell phone. The
login procedure in protocol does not require users to type
passwords into an un trusted web browser. Finally, the cell
phone receives a response message from the server and
shows a success message on her screen if the server is
able to verify her identity.
B. Registration Phase
The aim of this phase is to allow a user and a server to
negotiate a shared secret to authenticate succeeding logins
for this user. The user begins by opening the protocol
program installed on her cell phone. She enters ID
(account id she prefers) and ID (usually the website URL
or domain name) to the program. Once the TSP received
the ID ad the ID, it can tace the user's phone number based
on user's SIM card. The TSP also plays the role of third
part to distibute a shaed key between the user and the server.
The cell phone computes a secret credential by the
following operation:
c= J
(Pu
II
ID
sll<
) (5)
To prepare a secure registration SMS the cell phone
encrypted the computed credential c with the key Ksd and
generates the corresponding MAC. Then, the cell phone
sends an encrypted registration SMS to the server by phone
number as follows:
CcIIp!onc
ss s:
Iu, {CIl4}K.d,IV
HMAC
C. Login Phase
|)
The protocol starts when user u wishes to log into her
favourite web server S (already registered). However, u
begins the login procedure by accessing the desired website via
a browser on an un trusted kiosk. The browser sends a
request to S with u's account IDu .. Next server S supplies
the IDs and a fesh nonce 1 time password for OJ for current
login is recommended using the following operations:
c = ((Pu III
D
s 114
^, " (l-iCC).
(8)
The next action on the cell phone is sending the following
SMS message to server:
!! -- I!, {ndllns}6i,IV
^
(9)
Afer receiving the login sms the server recomputes OJ, to
decrypt and verif the authenticity of the login sms.
D. Recovery Phase
Te protocol is able to recover the setting on her new cell
phone asswning she still uses the same phone number (apply
a new SIM card with old phone number).Once user u
installs the protocol program on her new cellphone, she can
launch the program to send a recovery request with her
account IDu and requested server IDs to predefmed TSP
through a 3G connection. As we mentioned before, ID can be
the domain name or U link of server S.
Once server S receives the request, S probes the account
inforation in its database to conf if account u is
registered or not. If account IDu exists, the information used
Hacking Resistance Protocol for Securing Passwords Using Personal Device 4b1
to compute the secret credential c will be fetched and be
sent back to the user. The server S generates a fesh nonce
1 and replies a message which consists of ID, <, Ts, i, and
1.This message includes all necessary elements for
generating the next one-time passwords to the user u. When
the mobile program receives the message, like registration,
it forces the user u to enter her long-term password to
reproduce the correct one-time password o,, (assuming the
last successful login before u lost her cell phone is o,).
During the last step, the user's cell phone encrypts the
secret credential c and server nonce 1 to a cipher text. The
recovery SMS message is delivered back to the server S for
checking. Similarly, the server S computes o, and decrypts
this message to ensure that user u is already recovered. At
this point, her new cell phone is recovered and ready to
perform further logins. For the next login, one-time
password o,_will be used for user authentication.
TABLE 1: NOTATIONS
Name Description
IDx Identity of entity x.
Ty Entity y's phone number
0 Random seed
N Pre-defne length of hash chain ({ 00 o,).
n
z
Nonce generated by entity z.
P
u
User u 's long-term password.
Ksd Shared secret key between cell phone and the server.
c Secret shared credential between cell phone and the
a,
server
''
ith one-time password.
{
`
Concatenate operation.
/.|
Symmetric encryption) with key k.
IV
Hash function with input o.
HMAC1
Initialization vector of AES-CBC.
HMAC2
The HMAC-SHAI digest of IDIIIIIVII {c110 }ksd under
the Ksd
HMAC3
The HMAC-SHA 1 digest of IIII IIVI I {ndlln,}ai under
the ai.
The HMAC-SHA 1 digest of IIII IIVI I {clln,}ai+ 1
under the a,+ I.
I Symmetric encryption algorithm in protocol is AES-256.
2 Hash fnction is SHA-256.
V. EXPERIMENT DESIGN
We implemented a prototype and conducted a user study
to analyze the performance and usability.
/. Prototype Implementation
The prototype consists of three components: a mobile
program running on Android smart phones (Android OS
v2.1); an extension on Firefox browser; and a web server.
Te server ofers a web service by an Apache server rg
on a workstation with Windows XP, and SMS service
wit a GSM modem connected to itself Te communication
interface between the phone and the brwser extension is
based on a client/server model.
The client program is developed on Android OS due to its
populaity ad generalit. I the web server implementation,
we developed a server program which consists of main server
codes (PHP) and setup scripts for database (MYSQL).
Server program can be installed ad perfored on a Apache
HTTP server. On te oter had, capacit of sending/receiving
SMS via a GSM modem relies on an open source library
SMS Lib. For simulating TSP, partial PHP codes and
related information were also established by the database.
B. User Study
Before starting the study, participants are to be first asked to
complete a demographics questionnaire. They then to be
introduced to the protocol system. Then they would be
setting up the system, registering an account, and logging
in via a cell phone. Further, they have to be instructed t
choose a strong long-ter password that should be at least
eight digits long. They then have to proceed to complete a
formal test which consisted of the following steps:
1. Setting up the System: Different from the ordinary user
authentication system, users should install cell phone
sofware and a browser extension to setup the
protocol system.
2. Registering for an Account: Users frst open the
registration sofware on the cell phone. Users then fll
out a for, which includes an account id, a website's
id, and a long-term password, and submit it to the
website.
3. Logging into the Website: Users frst enter their
account id into the browser on the kiosk and submit
it to the server. Users then type their long-term
password into m cell- phone and submit to the server.
The login succeeds if a success message is shown on
the screen of cell phone. If login fails, participants
should try again until they are successful.
VI. RELATED WOR
A number of previous researchers have proposed to
protect user credentials from phishing attacks in user
authentication. The proposed systems leverage variable
technologies, f o r example, mobile devices, trusted
platfor module (TPM), or public key infastcture (PKI).
However, these solutions were short of considering the
negative infuence of human factors, such as password
4b2 Proceedings of7
h
International Conference on Intelligent Systems and Control (ISCO 2013)
reuse ad wea password problems. To stengthen password
based authentication in untrusted environment [9], MP
Auth forces the input of a long- term secret (typically a
user's text password) through a trusted mobile device.
Before sending the password to an untrusted kiosk, the
password is encrypted by a pre installed public key on
a remote server. MP-Auth is intended to guard passwords
fom attacks raised by untsted kiosks, including key loggers
and malware. On the other hand, some literature represents
different approaches to prevent phishing attacks [2]. Session
Magnifer enables an extended browser on a mobile device
and a regular browser on a public computer to
collaboratively secure a web session.
/. Comparisons between Resistance Protocol
and Other Systems
Many of proposed systems require user involvement in
certifcate confrmation (UICC) in order to setup a secure
SSL tunnel. However, prior research concluded that users
do not understand SSL and ofen ignore the SSL warings
caused by illegal certifcates [4], [5]. Consequently, users
ofen accept the received certifcates without verifcation.
This inattentive behavior causes users to suffer fom
potential attacks, such as MITM and DNS spoofng attacks.
From previous literature, users should pay attention to
confrming server certifcate validities by themselves. The
signifcant diference between resistance protocol and other
related schemes is that protocol reduces the negative impact
of user misbehaviors as much as possible.
In the protocol system, the SSL tunnel is established
between a TSP and a web site server. From the perspective
of users, they feel comfortable since there is no frther
need to verif the server certifcate by themselves. In
other words, overhead on verifying seer certifcates for
users is switching to the TSP. The TSP acts as a users'
agent to validate server certifcates and also establish SSL
tunnels correctly. Therefore, this protocol still resists
phishing attacks even if users misbehave.
VII. CONCLUSION
In this paper, hacking resistance protocol is developed
which leverages the cell phones and SMS to thwart
password stealing and password reuse attacks. It is assumed
that each website possesses a unique phone number. Also
assume that a telecommunication service provider
participates in the registration and recovery phases.
The design principle of this protocol is to eliminate the
negative as much as possible. Through protocol, each
user only needs to remember a long-term password which
has been used to protect her cell phone. Users are fee
fom typing any passwords into untrusted computers for
login on all websites. Compared with previous schemes,
this resistance protocol is the frst user authentication
protocol to prevent password stealing (i.e., phishing,
key logger, and malware) and password reuse attacks
simultaneously. The reason is that it adopts the one-time
password approach to ensure independence between each
login. To make the protocol fully functional, password
recovery is also considered and supported when users lose
their cell phones. They can recover our protocol system
with reissued SIM cards and long-tenn passwords.
A prototype of resistance protocol is also implemented to
measure its performance. The average time spent on
registration and login is 21.8 and 21.6 s, respectively.
According to the result, SMS delay occupies more than
40% of total execution time. The delay could be shorter by
using advanced devices. Besides, the perfonnance of
login of the protocol is better than graphical password
schemes, for example, Pass faces. The login time of Pass
faces is from 14 to 88s, which is longer than resistance
protocol. Therefore, we believe te prtol Lacceptable and
reliable for users. Most participants could easily operate all
procedures of the prot ocol system. The login success
rate is over 90%, except for a few typing errors.
Consequently, this protocol is more secure than the original
login system. Certainly, the participants prefer this
resistance protocol to the original system.
REFERENCES
[I] P. van Oorschot, A. Salehi-Abari, and J. Thorpe, "Purely
automated attacks on pass points-style graphical passwords,"
IEEE Trans. Information Forensics Security, vol. 5, no. 3,
pp. 393-405, Sep. 2010.
[2] B. Paro, C. Kuo, and A. Perig, "Phoolproof phishing
prevention", Financial Cryptography Data Security, pp. 1-19,
2006.
[3] Shepard, R.N., 1967. Recognition memory for words, sentences,
and pictures. Journal of Verbal Learning and Verbal
Behavior 6, 156-163.
[4] D. Wendlandt, D. G. Andersen, and A. Perrig, "Perspectives:
Improving ssh-style host authentication with multi-path
probing," in Proc. USENIX 2008 Annu. Tech. Conf.,
Berkeley, CA, 2008, pp. 321-334, USENIX Association.
[5] S. E. Schechter, R. Dhamia, A. Ozment, and I. Fischer,
"Emperor's new security indicators: An evaluation of
website austhentication and the effect of role playing on
usability studies," in Proc. 2007 IEEE Symp. Security
Privacy, 2007.
[6] K. J. Hole and V. Moen and T. Tjostheim. Case Study: Online
banking Security. IEEE Security & Privacy Magazine, 2006.
[7] Zviran, M. & Haga, W. J. Password Security: An Empirical
Study. Journal of Management Information Systems 15, 4
(1999), 161-185
[8] M Zviran, WJ Haga, "A comparison of password techniques for
multilevel authentication mechanisms", in Computer Journal
v 36 no 3 (93) pp 227{237
[9] M. Mannan and P. van Oorschot, "Using a personal device
to strengthen password authentication from an untrusted
computer," Financial Crptography Data Security, pp. 88-103,
2007.
Hacking Resistance Protocol for Securing Passwords Using Personal Device 4bJ
[10] S. Bellovin and M. Merritt. Encrypted key exchange:
password-based protocols secure against dictionary attacks.
In Proc. IEEE Security and Privacy Symposium, pages 72-S4.
IEEE Computer Society, 1992.
[11] I. T. Report, ITU Internet Rep. 2006: Digital. Life [Online].
Available: http://www.itu.inti
[12] L. O'Goran, "Comparing passwords, tokens, and biometrics
for user authentication," Proc. IEEE, vol. 91, no. 12, pp. 2021-
2040, Dec. 2003.
[13] D. Florencio and C. Herley, "A large-scale study of web
password habits," in WWW '07: Proc. 16th Int. Conf World
Wide Web., New York, 2007, pp. 657-666, ACM.
[14] S. GAW and E.W. Felten, "Password management strategies for
online accounts," in SOUPS '06: Proc. 2nd Symp. Usable
Privacy. Security, New York, 2006, pp. 44-55, ACM.
[15] I. Jermyn, A. Mayer, F. Monrose, M. K. Reiter, and A. D.
Rubin, "The design and analysis of graphical passwords," in
SSYM'99: Proc. Sth Conf USENIX Security Symp.,
Berkeley, CA, 1999, pp. 1-1, USENIX Association.
[16] A. Perig and D. Song, "Hash visualization: A new technique to
improve real-world security," in Proc. Int. Workshop
Cryptographic Techniques E-Commerce, Citeseer, 1999, pp.
131-13S.
[17] TS 23.040: Technical Realization Short Message Service
(SMS) 3GPP [Online]. Available: http://www.3gpp.org/
[I S] B. Pinkas and T. Sander, "Securing passwords against
dictionary attacks," in CCS '02: Proc. 9th ACM Conf
Computer Communications Security, New York, 2002,
pp. 161-170, ACM.
[19] TS 35.202: Specifcation 3GPP Confdentialit Integrit
Algorithms Document 2: KASUMI Specifcation 3GPP
[Online]. Available: http://www.3gpp.org
Das könnte Ihnen auch gefallen
- Info Theory LecturesDokument75 SeitenInfo Theory LectureschikyipNoch keine Bewertungen
- Network Simulator 2 - To Implement A New ProtocolDokument14 SeitenNetwork Simulator 2 - To Implement A New ProtocolManoj Kumar GNoch keine Bewertungen
- WSNS: Sensor Management: Ad Hoc Wireless Networks: Architectures and Protocols Wireless Sensor NetworksDokument32 SeitenWSNS: Sensor Management: Ad Hoc Wireless Networks: Architectures and Protocols Wireless Sensor NetworksManoj Kumar GNoch keine Bewertungen
- WSNS: Localization: Ad Hoc Wireless Networks: Architectures and ProtocolsDokument8 SeitenWSNS: Localization: Ad Hoc Wireless Networks: Architectures and ProtocolsManoj Kumar GNoch keine Bewertungen
- WSNS: Mac: Ad Hoc Wireless Networks: Architectures and Protocols IEEE Personal Communications Wireless Sensor NetworksDokument12 SeitenWSNS: Mac: Ad Hoc Wireless Networks: Architectures and Protocols IEEE Personal Communications Wireless Sensor NetworksManoj Kumar GNoch keine Bewertungen
- Reading: - "Wireless Lans and Pans," in Ad Hoc Wireless NetworksDokument49 SeitenReading: - "Wireless Lans and Pans," in Ad Hoc Wireless NetworksManoj Kumar GNoch keine Bewertungen
- Name Contactperson Mobile Address Phone Fax E-MailDokument1 SeiteName Contactperson Mobile Address Phone Fax E-MailManoj Kumar GNoch keine Bewertungen
- SRS SampleDokument21 SeitenSRS SampleManoj Kumar GNoch keine Bewertungen
- Blackboard 9.1 - Course FilesDokument17 SeitenBlackboard 9.1 - Course FilesManoj Kumar GNoch keine Bewertungen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Postal Ballot Notice 2023Dokument35 SeitenPostal Ballot Notice 2023Pratheesh .PNoch keine Bewertungen
- NCLT Convened Meeting NoticeDokument36 SeitenNCLT Convened Meeting NoticeAkash SinghNoch keine Bewertungen
- E Invoice Relyon Softech LTDDokument13 SeitenE Invoice Relyon Softech LTDvovope1174Noch keine Bewertungen
- Handbook On DIGITAL Products 20210815125103Dokument29 SeitenHandbook On DIGITAL Products 20210815125103Neos EonsNoch keine Bewertungen
- BITS User ManualDokument57 SeitenBITS User Manualanju dixitNoch keine Bewertungen
- OTP Verification ServicesDokument8 SeitenOTP Verification ServicesOtp Service Provider in IndiaNoch keine Bewertungen
- Rsfi - Annual - Regn - 2021-22Dokument1 SeiteRsfi - Annual - Regn - 2021-22parth waghNoch keine Bewertungen
- User ManualDokument27 SeitenUser ManualMritunjay kumarNoch keine Bewertungen
- Experience Guide Finbooster Credit Card PDFDokument11 SeitenExperience Guide Finbooster Credit Card PDFChirag GandhiNoch keine Bewertungen
- E-Statement of Account: Hans Rudolf Begonte TamidlesDokument4 SeitenE-Statement of Account: Hans Rudolf Begonte TamidlesKal LymNoch keine Bewertungen
- Online Voting SystemDokument4 SeitenOnline Voting SystemIJRASETPublicationsNoch keine Bewertungen
- Accelerex IT ReportDokument37 SeitenAccelerex IT ReportVincentNoch keine Bewertungen
- Arc IbDokument44 SeitenArc Ibgasay sinhtoNoch keine Bewertungen
- Up To Date Templates - ReviewedDokument39 SeitenUp To Date Templates - ReviewedRadu CristianNoch keine Bewertungen
- Account Statement From 1 Apr 2020 To 31 Mar 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDokument9 SeitenAccount Statement From 1 Apr 2020 To 31 Mar 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceRohit AgarwalNoch keine Bewertungen
- Ramayana VishavrukshamDokument2 SeitenRamayana VishavrukshamSRIDHAR allhari0% (1)
- Man3000 User ManualDokument68 SeitenMan3000 User ManualliviuisrNoch keine Bewertungen
- HDFC Net Banking & E StatementDokument17 SeitenHDFC Net Banking & E StatementgoanfidalgosNoch keine Bewertungen
- Account Statement From 5 Apr 2023 To 5 Oct 2023: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDokument8 SeitenAccount Statement From 5 Apr 2023 To 5 Oct 2023: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceAman guptaNoch keine Bewertungen
- Cor Dirin Gudstndngas 31 March 16Dokument449 SeitenCor Dirin Gudstndngas 31 March 16bissauNoch keine Bewertungen
- 411 SQP Banking & InsuranceDokument3 Seiten411 SQP Banking & InsuranceJanavi M SNoch keine Bewertungen
- fortitoken-2FA SolutionDokument7 Seitenfortitoken-2FA Solutionelpatron nachoNoch keine Bewertungen
- Rules and RegulationsDokument5 SeitenRules and RegulationsAyushNoch keine Bewertungen
- User Guide enDokument56 SeitenUser Guide enaldeachristian0Noch keine Bewertungen
- CYBERSECURITYDokument41 SeitenCYBERSECURITYDominique EijansantosNoch keine Bewertungen
- RBL Application Form1680992689896 - 9540523355Dokument5 SeitenRBL Application Form1680992689896 - 9540523355Vikram SharmaNoch keine Bewertungen
- Labour Commissionerate: User ManualDokument82 SeitenLabour Commissionerate: User ManualnirmalyagNoch keine Bewertungen
- Star TokenDokument34 SeitenStar Tokenashish_avm3042Noch keine Bewertungen
- Citizen Manual FOR National Cybercrime Reporting Portal: Ministry of Home AffairsDokument92 SeitenCitizen Manual FOR National Cybercrime Reporting Portal: Ministry of Home AffairsveenaNoch keine Bewertungen
- Social Dilemma Is A LieDokument3 SeitenSocial Dilemma Is A Lieinfo trafficboostNoch keine Bewertungen