Beruflich Dokumente
Kultur Dokumente
HackMeCo PCI Compliance Presentation Outline
Hochgeladen von
Cesar Santiago Bolaño SalazarOriginalbeschreibung:
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
HackMeCo PCI Compliance Presentation Outline
Hochgeladen von
Cesar Santiago Bolaño SalazarCopyright:
Verfügbare Formate
HackMeCo, Incident Response
An approach to lecture #2
Weve been had, and it was all Georges fault.
If you recall from week 2
Finish the job
Already we:
Hopefully were prepared Detected and analyzed Contained, eradicated?? and recovered Post mortem analysis
Dont forget the follow-up
Prosecute? Re-visit our controls?
An approach
Multiple shades of red
Do we need to be XXX compliant? What does regulatory compliance mean to unregulated industries?
Regulatory and otherwise compliance
Industries treatment of information is often regulated to assure society that protections meet an agreed upon standard. In such cases, the regulations are published, well known and expertise is available for interpreting the legal language.
Health Insurance Portability and Privacy act (HIPAA): 355 pages in the federal register Sarbanes Oxley: 65 pages NERC Critical Infrastructure Protection 31 documents (but carefully read - $1 million / day fining authority)
Simple compliance
In the government regulatory scenario:
The rules are knowable Its reasonably clear who the rules apply to As written into law, the rules are usually pretty generic Its possible to know where you stand
Simple sort of
Payment Card Industry Data Security Standard (PCI DSS): Industry self-regulation, notable failures in ecommerce FFIEC guidance on Internet banking authentication
Guidance, not regulation, though Internet searches link pages which incorrectly refer to the guidance as regulation because US Courts are finding against banks which have not implemented the guidance citing it as best practice
Non regulatory, but still compliance
In the absence of regulation or authoritative controls, courts and the general population will still judge your actions based on a perception of good or best practices. The fact that there wasnt a law or regulation forcing you to do a good job is often moot. WEP encryption IS a way to encrypt wireless transactions, technically satisfying PCI DSS (at one time) but nobody would have defended TJX security practices as best ~= large fines
What!?!
Fines: Non compliance can result in regulatory authorities assigning fines.
These range from relatively minor to NERC CIP at $1,000,000 / day / incident back dated to the start of the non-compliant behavior Fines are typically assigned directly by the regulating body, no court action required
Penalties vary - regulatory
Legal: In some cases (some levels of HIPAA violation for example) non-compliance is criminal
Penalties include fines as well as potential jail time Criminal liability is, of course, individual an can be applied to directors, employees and officers of the company
Penalties vary - regulatory
PCI penalties are civil in nature, not criminal
Most levels include fines They can also decide not to allow you to accept credit cards anymore
Penalties vary civil
FFIEC Guidance has NO direct effect, but banks are losing in court (sometimes) based on it
Civil judgments against the bank, based on noncompliance Other standards may apply in the same way, keeps lawyers busy
Penalties vary civil
Security incidents these days can be noisy affairs
Organizational reputations are at stake Perception of shoddy infosec standards can cost you customers Umbrella laws like the Federal Trade Commissions Unfair Practices Act can be used to categorize poor behavior and levy fines in lieu of direct regulation
Penalties vary market
Many companies today have limited or no regulatory compliance issues with respect to IT security, but have customers / business partners with such requirements. In these cases, third party handling of information isnt always spelled out in law or regulation, but in some cases like HIPAA (Business Associate Agreements) the provisions are explicit
No such thing as unregulated
In cases like HIPAA where third party agreements are spelled out, it doesnt necessarily make it simpler
HIPAA is a legal requirement for the covered entity, but the BA agreements are civil While there is no private right of action against a covered entity (you cant sue them) under HIPAA, the contractual agreement may allow for civil action against third parties While you cannot contractually indemnify parties with respect to violations of the law (HIPAA violations) you CAN indemnify against contract breach
Sometimes there are no audit requirements, just penalties for breach or other evidence of noncompliance (e.g. state breach disclosure laws)
Complicated Landscape
Sometimes, as in the case of US States, regulation is regional
46 of 50 states have laws regarding notification in the case of breach of Personally Identifiable Information (PII.) Each of them are different, some are VERY different. Washington State provides a free pass if the breached entity was PCI Compliant at the time of the breach Global companies with information stored in multiple locations throughout the world have to deal with local law and regulation, wherever they may be
Whos in charge
Break 1
If your customer must comply, they will likely feel that you need to comply as well. EVERYONE tries to spread the liability around Even if folks arent spreading it around, sometimes liability spreads through court action Even without liability or regulatory mandate, being responsible for a breach can be painful
Business Realities
Sometimes, full compliance without the requirement is a marketing tool Even though you arent currently mandated by law, someone in local or federal government is thinking about regulating you count on it. If a customer has to choose between you, and a competitor that is compliant, you lose MOST government regulations regarding information security and assurance are just good sense guidelines, and fairly weak at that.
Good Sense
What if you have to comply with:
CIPA (Children's Internet Protection Act) CISP (Visa Cardholder Information Security Program) PA-DSS (Payment Application Data Security Standard) PCI DSS (Payment Card Industry Data Security Standard) Federal Circular A-123 FFIEC authentication in an electronic banking environment guidance FISMA (Federal Information Security Management Act) GLBA (Gramm-Leach Bliley Act) HIPAA (Health Insurance Portability and Accountability Act) Sarbanes-Oxley Act of 2002 (Public Company Accounting Reform and Investor Protection Act)
This is the SHORT and USA ONLY list
Compliance Costs
Direct Costs
New infrastructure (new firewalls, IDS, logging devices) Additional personnel Internal audit and compliance (time) ??? Opportunity costs Business model restrictions ???
Indirect costs
Compliance Costs (cont.)
Direct Benefit
Marketing Material Sales (base on new marketing) Customer audit readiness ??? Process improvement (CMM style improvements?) Risk reduction ???
Indirect Benefit
Compliance Benefits
Break 2
You are the Director of Security (reporting to the CFO) for HackMeCo subsidiary which HIPAA covered healthcare providers use to examine medical billings and payments for evidence of fraud. All of their billing information flows through you (but you dont do billing). You arent collecting this information, so assume that you are not required to adopt PCI (technically, this may not be true, but lets use that as a baseline assumption) You DID have to sign a Business Associate agreement (sample available) to get Protected Health Information (PHI)
Medicare Billing Fraud Reduction ASP
Nobody is demanding anything, we are operating performing the service we advertise. Customers have asked our salespeople if we are PCI compliant. Our salespeople said Gee, I expect that we are, but Ill ask The truth is, we are not PCI compliant, nor is there a legal requirement for it In a short email, we explained this to the salesperson, who then asked why not (and CCed the CIO and CEO) Not adversarial, just wants a discussion since she sees it as a potential negative.
The Issue of the day
No legal requirement (remember, PCI is industry based, not legal regulation) Even the Payment Card Industry says we dont have to be compliant We have billing data from our clients regarding health care billing, which includes HIPAA protected data as well as credit card info and billing histories You suspect the sales person asking for this is the one stealing your lunch out of the fridge
Our Situation
So far, its just an email conversation but the CIO has called for a meeting of the COO, CIO, Director of Marketing, Director of Operations, You and the Salesperson to discuss. The CFO (your boss) has asked that you research the topic and present your findings to the meeting with your recommendations. Draft an outline of your presentation to the management team
Choose Your Response
Remember, just because you are not forced to comply doesnt mean its necessarily a bad idea Weigh the benefits and costs of compliance or lack of compliance Put a mousetrap in your lunchbox
Suggestions for the assignment
Das könnte Ihnen auch gefallen
- Yardi Commercial SuiteDokument52 SeitenYardi Commercial SuiteSpicyNoch keine Bewertungen
- Violation ProcessDokument16 SeitenViolation ProcessEduard O. NiteNoch keine Bewertungen
- Data Protection United StatesDokument10 SeitenData Protection United Statesaquinas03Noch keine Bewertungen
- Pharma Pathway SopDokument350 SeitenPharma Pathway SopDinesh Senathipathi100% (1)
- p2 - Guerrero Ch13Dokument40 Seitenp2 - Guerrero Ch13JerichoPedragosa88% (17)
- Forensic Accounting, Fraud Investigation And Fraud AnalyticsVon EverandForensic Accounting, Fraud Investigation And Fraud AnalyticsNoch keine Bewertungen
- 37 Operational Emergency and Abnormal ProceduresDokument40 Seiten37 Operational Emergency and Abnormal ProceduresLucian Florin ZamfirNoch keine Bewertungen
- BWT Septron Line 31-61 Rev01!08!05-18 Opm enDokument56 SeitenBWT Septron Line 31-61 Rev01!08!05-18 Opm enDavide Grioni100% (1)
- A. What Is Balanced/objective Review or Criticism?Dokument11 SeitenA. What Is Balanced/objective Review or Criticism?Risha Ann CortesNoch keine Bewertungen
- GDPR-standard data protection staff training: What employees & associates need to know by Dr Paweł MielniczekVon EverandGDPR-standard data protection staff training: What employees & associates need to know by Dr Paweł MielniczekNoch keine Bewertungen
- Information Security GovernanceDokument16 SeitenInformation Security Governancefawas hamdiNoch keine Bewertungen
- Basic Concepts in Legal, Regulations, Investigations, and ComplianceDokument22 SeitenBasic Concepts in Legal, Regulations, Investigations, and ComplianceAnonymous 97dbabE5Noch keine Bewertungen
- Compliance White Paper: Compliance and Computer ForensicsDokument7 SeitenCompliance White Paper: Compliance and Computer ForensicsEmily NelsonNoch keine Bewertungen
- Big Data Analytics in Accounting and Finance GDPR ComplianceDokument7 SeitenBig Data Analytics in Accounting and Finance GDPR ComplianceJavier Noel ClaudioNoch keine Bewertungen
- CISSP - 10 Legal, Regulations, Investigations & ComplianceDokument56 SeitenCISSP - 10 Legal, Regulations, Investigations & ComplianceVeli AnlamaNoch keine Bewertungen
- HIPAA Has Teeth: What Accountants, Lawyers, and Other Professionals Need To Know When Working With Clients in HealthcareDokument7 SeitenHIPAA Has Teeth: What Accountants, Lawyers, and Other Professionals Need To Know When Working With Clients in HealthcareJedidahCuevasNoch keine Bewertungen
- Sample LIA Template: Part 1: Purpose TestDokument5 SeitenSample LIA Template: Part 1: Purpose TestNiranjan JeyakumarNoch keine Bewertungen
- Legal Ethics in The Digital Age.1Dokument25 SeitenLegal Ethics in The Digital Age.1Gerry SchulzeNoch keine Bewertungen
- California Consumer Protective ActDokument7 SeitenCalifornia Consumer Protective ActChristine Marie Wagan AlmanzaNoch keine Bewertungen
- Data Protection Act CourseworkDokument4 SeitenData Protection Act Courseworkbcqy65mx100% (2)
- CD Ws Security So 32672 e Guide 120310Dokument8 SeitenCD Ws Security So 32672 e Guide 120310Eduardo Martinez CoronaNoch keine Bewertungen
- Digital Data, Copyright, AIDokument26 SeitenDigital Data, Copyright, AIVishal LohareNoch keine Bewertungen
- Data Protection Act ThesisDokument5 SeitenData Protection Act Thesisafknoaabc100% (2)
- Ict Ethics NotesDokument5 SeitenIct Ethics NotesSharon AmondiNoch keine Bewertungen
- Jamshaid 59 4438 2 BE Session 3Dokument42 SeitenJamshaid 59 4438 2 BE Session 3Mahnoor BalochNoch keine Bewertungen
- Biancuzzo The Convergence of Law and Cybersecurity Nuix 3 7 2018Dokument3 SeitenBiancuzzo The Convergence of Law and Cybersecurity Nuix 3 7 2018vv2285307Noch keine Bewertungen
- ResearchDokument15 SeitenResearchEjhay OniaNoch keine Bewertungen
- Affirmative Defense Response System: Answer: Liability, Both Civil and CriminalDokument33 SeitenAffirmative Defense Response System: Answer: Liability, Both Civil and CriminalHavilah100% (1)
- Introduction To Information Systems (Chapter3&4)Dokument15 SeitenIntroduction To Information Systems (Chapter3&4)ezzeddin pNoch keine Bewertungen
- Hipaa Security ChecklistDokument2 SeitenHipaa Security ChecklistnicolepetrescuNoch keine Bewertungen
- Legal and Ethical Issues in Information SecurityDokument10 SeitenLegal and Ethical Issues in Information SecurityCarlRiveraNoch keine Bewertungen
- Social MediaDokument103 SeitenSocial MediaVipul PartapNoch keine Bewertungen
- Data Privacy LawDokument6 SeitenData Privacy LawJoan Magno MariblancaNoch keine Bewertungen
- Data Privacy LawsDokument5 SeitenData Privacy LawsShobhit ShuklaNoch keine Bewertungen
- Protect your data and avoid costly penaltiesDokument11 SeitenProtect your data and avoid costly penaltiesygupta01Noch keine Bewertungen
- Lecture 03 - Legal, Ethical & Professional-1Dokument68 SeitenLecture 03 - Legal, Ethical & Professional-1Umair AmjadNoch keine Bewertungen
- What To Expect in 2021 - An in House Perspective - revisedLIDokument3 SeitenWhat To Expect in 2021 - An in House Perspective - revisedLIEdieNoch keine Bewertungen
- Bana1 ReviwerDokument9 SeitenBana1 ReviwerCHOZAS, BEA NICOLE B.Noch keine Bewertungen
- Hipaa Research Paper TopicsDokument7 SeitenHipaa Research Paper Topicsafmcwxcuk100% (1)
- Module 4 Legal, Ethical, and Professional Issues in Information SecurityDokument27 SeitenModule 4 Legal, Ethical, and Professional Issues in Information Securityjosh melchorNoch keine Bewertungen
- Code of Conduct - July 2020Dokument18 SeitenCode of Conduct - July 2020GeorgeNoch keine Bewertungen
- DSG Security Newsletter Issue 1 July 1, 2009: What's Going On?Dokument6 SeitenDSG Security Newsletter Issue 1 July 1, 2009: What's Going On?api-14476259Noch keine Bewertungen
- DataSecurityandRisksinFranchiseSystem-1Dokument37 SeitenDataSecurityandRisksinFranchiseSystem-1tuccialexandre1Noch keine Bewertungen
- Lecture 03 - Legal, Ethical & Professional-3Dokument69 SeitenLecture 03 - Legal, Ethical & Professional-3snyderlola0Noch keine Bewertungen
- Customer Due Diligence ChecklistDokument5 SeitenCustomer Due Diligence ChecklistThomas T.R HokoNoch keine Bewertungen
- ICO Data Sharing CodeDokument59 SeitenICO Data Sharing CodeOllie EvansNoch keine Bewertungen
- Chp2 MoodleDokument2 SeitenChp2 MoodleNway Nway Wint AungNoch keine Bewertungen
- Privacy Definition of TermsDokument37 SeitenPrivacy Definition of TermsmarjNoch keine Bewertungen
- Boyd TestimonyDokument4 SeitenBoyd TestimonylcullenGTNoch keine Bewertungen
- Data Privacy: What Every Manager Needs To KnowDokument10 SeitenData Privacy: What Every Manager Needs To KnowSaswat SamantarayNoch keine Bewertungen
- Final Information SystemDokument7 SeitenFinal Information Systemshahrupasha902Noch keine Bewertungen
- Intro To CCPADokument7 SeitenIntro To CCPAJohn Henry AntonaNoch keine Bewertungen
- Module 7 AssignmentDokument10 SeitenModule 7 Assignmentapi-360051483Noch keine Bewertungen
- Case Study explores corporate ethics and IT's roleDokument2 SeitenCase Study explores corporate ethics and IT's roleNoviansyah PamungkasNoch keine Bewertungen
- DPA AssignmentDokument5 SeitenDPA Assignmentvaibhav kharbandaNoch keine Bewertungen
- A Accounting Ethics in The Digital AgeDokument5 SeitenA Accounting Ethics in The Digital AgeBrook KongNoch keine Bewertungen
- 03.2 Audit Legal Compliance Vs ISO 27001Dokument3 Seiten03.2 Audit Legal Compliance Vs ISO 27001digi devaNoch keine Bewertungen
- Module 6 Saq: Why Do We Monitor Transactions?Dokument10 SeitenModule 6 Saq: Why Do We Monitor Transactions?RANDANoch keine Bewertungen
- Ass. Ethics Breach - EditedDokument3 SeitenAss. Ethics Breach - EditedSamuel KamuriNoch keine Bewertungen
- CCSP Exam Cram Domain 6 HandoutDokument142 SeitenCCSP Exam Cram Domain 6 HandouttrojanbayaNoch keine Bewertungen
- AssignmentDokument4 SeitenAssignmentapi-561990701Noch keine Bewertungen
- Phpy PCNCLDokument3 SeitenPhpy PCNCLNATSOIncNoch keine Bewertungen
- What Is Data Privac - A GuideDokument2 SeitenWhat Is Data Privac - A GuideClarizaNoch keine Bewertungen
- Data Breaches and Legal LiabilityDokument5 SeitenData Breaches and Legal LiabilityParth RastogiNoch keine Bewertungen
- IJRAR19K3961Dokument8 SeitenIJRAR19K3961Cesar Santiago Bolaño SalazarNoch keine Bewertungen
- ALC PDH RADIO Technical Training Siae MiDokument141 SeitenALC PDH RADIO Technical Training Siae Mijavierignacio212446Noch keine Bewertungen
- 3G Alarm Impact To PerformanceDokument8 Seiten3G Alarm Impact To PerformanceMahamadou Ousseini BarkiréNoch keine Bewertungen
- DUW Software Upgrade ProcedureDokument2 SeitenDUW Software Upgrade ProcedureanwarNoch keine Bewertungen
- For - Rs.omm-002 Rutina de MantenimientoDokument157 SeitenFor - Rs.omm-002 Rutina de MantenimientoCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Ceragon-Fibeair Ip-10 Technical SpecsDokument15 SeitenCeragon-Fibeair Ip-10 Technical SpecsFarid BaskoroNoch keine Bewertungen
- Config Rep Comba Sr-1939Dokument5 SeitenConfig Rep Comba Sr-1939Cesar Santiago Bolaño SalazarNoch keine Bewertungen
- Ceragon 130624081358 Phpapp01 PDFDokument43 SeitenCeragon 130624081358 Phpapp01 PDFCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Innovations in Spectrum Efficiency: Hilik Shivek Vice President, Global Pre-SalesDokument34 SeitenInnovations in Spectrum Efficiency: Hilik Shivek Vice President, Global Pre-Salesy_m_algbaliNoch keine Bewertungen
- 3G Alarm Impact To PerformanceDokument8 Seiten3G Alarm Impact To PerformanceMahamadou Ousseini BarkiréNoch keine Bewertungen
- Ceragon-Fibeair Ip-10 Technical SpecsDokument30 SeitenCeragon-Fibeair Ip-10 Technical SpecsCesar Santiago Bolaño SalazarNoch keine Bewertungen
- RTN 380 V100R002 Quick Installation Guide 03Dokument35 SeitenRTN 380 V100R002 Quick Installation Guide 03Cesar Santiago Bolaño SalazarNoch keine Bewertungen
- Modulacion PDFDokument4 SeitenModulacion PDFCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Linear Circuits: An Introduction To Linear Electric Components and A Study of Circuits Containing Such DevicesDokument7 SeitenLinear Circuits: An Introduction To Linear Electric Components and A Study of Circuits Containing Such DevicesCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Introductory Astronomy: Week 7: Galaxies Clip 1: Introduc On: Finding The Milky WayDokument5 SeitenIntroductory Astronomy: Week 7: Galaxies Clip 1: Introduc On: Finding The Milky WayCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Introductory Astronomy: Week 7: Galaxies Clip 5: Bulge and CoreDokument4 SeitenIntroductory Astronomy: Week 7: Galaxies Clip 5: Bulge and CoreCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Lab 4Dokument10 SeitenLab 4Cesar Santiago Bolaño SalazarNoch keine Bewertungen
- Ceragon - FibeAir Outdoor EnclosureDokument2 SeitenCeragon - FibeAir Outdoor Enclosurecapulina1234+Noch keine Bewertungen
- Circuits Docs Labs Lab3 First and Second Order ResponsesDokument8 SeitenCircuits Docs Labs Lab3 First and Second Order ResponsesCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Linear Circuits: An Introduction To Linear Electric Circuit Elements and A Study of Circuits Containing Such DevicesDokument10 SeitenLinear Circuits: An Introduction To Linear Electric Circuit Elements and A Study of Circuits Containing Such DevicesCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Linear Circuits: An Introduction To Linear Electric Circuit Elements and A Study of Circuits Containing Such DevicesDokument15 SeitenLinear Circuits: An Introduction To Linear Electric Circuit Elements and A Study of Circuits Containing Such DevicesCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Lab 0Dokument3 SeitenLab 0Cesar Santiago Bolaño SalazarNoch keine Bewertungen
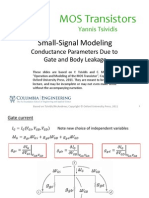
- Lecture - Slides Small Signal Modeling 8 2Dokument5 SeitenLecture - Slides Small Signal Modeling 8 2Cesar Santiago Bolaño SalazarNoch keine Bewertungen
- Linear Circuits: An Introduction To Linear Electric Components and A Study of Circuits Containing Such DevicesDokument4 SeitenLinear Circuits: An Introduction To Linear Electric Components and A Study of Circuits Containing Such DevicesCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Linear Circuits Frequency Spectrum Lab DemoDokument8 SeitenLinear Circuits Frequency Spectrum Lab DemoCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Circuits & Electronics: An Introduction to Electric ElementsDokument11 SeitenCircuits & Electronics: An Introduction to Electric ElementsCesar Santiago Bolaño SalazarNoch keine Bewertungen
- 2-10 Systematic Solution Methods Part 2Dokument12 Seiten2-10 Systematic Solution Methods Part 2Cesar Santiago Bolaño SalazarNoch keine Bewertungen
- Introductory Astronomy: Week 8: Cosmology Clip 7: Big Bang NucleosynthesisDokument8 SeitenIntroductory Astronomy: Week 8: Cosmology Clip 7: Big Bang NucleosynthesisCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Cosmology and the evolution of the early universeDokument5 SeitenCosmology and the evolution of the early universeCesar Santiago Bolaño SalazarNoch keine Bewertungen
- Lks Bahasa Inggris Kelas Vii Semester 1 Dan 2Dokument6 SeitenLks Bahasa Inggris Kelas Vii Semester 1 Dan 2ꓰꓡꓡꓰꓠ.ꓓꓰꓖꓰꓠꓰꓣꓰꓢꓢ.Noch keine Bewertungen
- Control Systems Engineering by S C Goyal U A Bakshi PDFDokument3 SeitenControl Systems Engineering by S C Goyal U A Bakshi PDFShubham SinghNoch keine Bewertungen
- 8086 Microprocessor: J Srinivasa Rao Govt Polytechnic Kothagudem KhammamDokument129 Seiten8086 Microprocessor: J Srinivasa Rao Govt Polytechnic Kothagudem KhammamAnonymous J32rzNf6ONoch keine Bewertungen
- Chapter One: Business Studies Class XI Anmol Ratna TuladharDokument39 SeitenChapter One: Business Studies Class XI Anmol Ratna TuladharAahana AahanaNoch keine Bewertungen
- Course Handbook MSC Marketing Sept2022Dokument58 SeitenCourse Handbook MSC Marketing Sept2022Tauseef JamalNoch keine Bewertungen
- UntitledDokument4 SeitenUntitledMOHD JEFRI BIN TAJARINoch keine Bewertungen
- Divide Fractions by Fractions Lesson PlanDokument12 SeitenDivide Fractions by Fractions Lesson PlanEunice TrinidadNoch keine Bewertungen
- CONNECTIFYDokument3 SeitenCONNECTIFYAbhishek KulshresthaNoch keine Bewertungen
- © 2020 Lippincott Advisor Nursing Care Plans For Medical Diagnoses - Coronavirus Disease 2019 (COVID 19) PDFDokument7 Seiten© 2020 Lippincott Advisor Nursing Care Plans For Medical Diagnoses - Coronavirus Disease 2019 (COVID 19) PDFVette Angelikka Dela CruzNoch keine Bewertungen
- What Is Chemical EngineeringDokument4 SeitenWhat Is Chemical EngineeringgersonNoch keine Bewertungen
- Liu030 Nepal Bans Solo Mountain ClimbersDokument2 SeitenLiu030 Nepal Bans Solo Mountain Climberssanti.miranda.parrillaNoch keine Bewertungen
- Beyond B2 English CourseDokument1 SeiteBeyond B2 English Coursecarlitos_coolNoch keine Bewertungen
- The Patient Self-Determination ActDokument2 SeitenThe Patient Self-Determination Actmarlon marlon JuniorNoch keine Bewertungen
- Yamaha RX-A3000 - V3067Dokument197 SeitenYamaha RX-A3000 - V3067jaysonNoch keine Bewertungen
- Efficient Power Supply for Inductive LoadsDokument7 SeitenEfficient Power Supply for Inductive LoadsMary AndersonNoch keine Bewertungen
- Developmen of Chick EmbryoDokument20 SeitenDevelopmen of Chick Embryoabd6486733Noch keine Bewertungen
- FRABA - Absolute - Encoder / PLC - 1 (CPU 314C-2 PN/DP) / Program BlocksDokument3 SeitenFRABA - Absolute - Encoder / PLC - 1 (CPU 314C-2 PN/DP) / Program BlocksAhmed YacoubNoch keine Bewertungen
- CM Template For Flora and FaunaDokument3 SeitenCM Template For Flora and FaunaJonathan Renier Verzosa0% (1)
- Classification of Methods of MeasurementsDokument60 SeitenClassification of Methods of MeasurementsVenkat Krishna100% (2)
- A Development of The Test For Mathematical Creative Problem Solving AbilityDokument27 SeitenA Development of The Test For Mathematical Creative Problem Solving AbilityanwarNoch keine Bewertungen
- Funny Physics QuestionsDokument3 SeitenFunny Physics Questionsnek tsilNoch keine Bewertungen
- Questions - TrasportationDokument13 SeitenQuestions - TrasportationAbhijeet GholapNoch keine Bewertungen
- Evolution BrochureDokument4 SeitenEvolution Brochurelucas28031978Noch keine Bewertungen
- Introduction To Global Positioning System: Anil Rai I.A.S.R.I., New Delhi - 110012Dokument19 SeitenIntroduction To Global Positioning System: Anil Rai I.A.S.R.I., New Delhi - 110012vinothrathinamNoch keine Bewertungen