Beruflich Dokumente
Kultur Dokumente
Cryptoviral Extortion: A Virus Based Approach
Hochgeladen von
seventhsensegroup0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
17 Ansichten5 SeitenAs we know that traditionally,
"Cryptography" is used for information processing and
communications, it helps people to store information
securely and it is used very frequently for private
communications. but Cryptovirology is the study of
applications of cryptography to build the malicious
software (malware). It is an investigation, how modern
cryptographic tools and paradigms can be used to
strengthen, develop and improve new malware attacks.
This is a forward engineering discipline that can be
used for attacking rather than defending.
Originaltitel
Cryptoviral Extortion: A virus based approach
Copyright
© © All Rights Reserved
Verfügbare Formate
PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenAs we know that traditionally,
"Cryptography" is used for information processing and
communications, it helps people to store information
securely and it is used very frequently for private
communications. but Cryptovirology is the study of
applications of cryptography to build the malicious
software (malware). It is an investigation, how modern
cryptographic tools and paradigms can be used to
strengthen, develop and improve new malware attacks.
This is a forward engineering discipline that can be
used for attacking rather than defending.
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
17 Ansichten5 SeitenCryptoviral Extortion: A Virus Based Approach
Hochgeladen von
seventhsensegroupAs we know that traditionally,
"Cryptography" is used for information processing and
communications, it helps people to store information
securely and it is used very frequently for private
communications. but Cryptovirology is the study of
applications of cryptography to build the malicious
software (malware). It is an investigation, how modern
cryptographic tools and paradigms can be used to
strengthen, develop and improve new malware attacks.
This is a forward engineering discipline that can be
used for attacking rather than defending.
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 5
International Journal of Computer Trends and Technology (IJCTT) - volume4 Issue5May
ISSN: 2231-2803 http://www.ijcttjournal.org Page 1149
Cryptoviral Extortion: A virus based approach
S.Manoj Kumar
#
1, M.Ravi Kumar*2
#
Dept.of IT (MCA)
G M R Institute of Technology, Rajam, Andhra Pradesh, India
*Dept. of IT (MCA)
G M R Institute of Technology Rajam, Andhra Pradesh, India
Abstract As we know that traditionally,
"Cryptography" is used for information processing and
communications, it helps people to store information
securely and it is used very frequently for private
communications. but Cryptovirology is the study of
applications of cryptography to build the malicious
software (malware). It is an investigation, how modern
cryptographic tools and paradigms can be used to
strengthen, develop and improve new malware attacks.
This is a forward engineering discipline that can be
used for attacking rather than defending. In this paper
we present the clear process of how the crypto virus
can damage the victims system, based on Extortion
mechanism with showing the live scenario that causes
the loss of access to information, loss of control and loss
of money also. Here we discuss and explain some of the
latest events regarding to this cryproviral extortion like
GPcode and Conflicker. This paper also suggests some
of the countermeasures, mechanisms to defend and
prevent such attacks. Even if the attackers actions on
the host machine are being monitored, it cannot be
controlled the host system completely. By knowing that
the exact scenario what exactly hacker follow to spoil
our system or network using this cryptoviral Extortion
method .we can anticipate or guesses the opponent's or
attackers next move and can able to provide some of the
safe guards initially.
Keywordscryptovirus, snatching, public-key
cryptography, kleptography, cryptanalysis, Gpcode,
Malware, Deniable Password Snatching (DPS),
cryptoviral extortion.
I. INTRODUCTION
Cryptography has been used for defensive purposes.
In the public eye, the word cryptography is virtually
synonymous with security. It is a means to an end, a
way to send e-mail privately and purchase items
securely on-line. Ciphers defend against a passive
eavesdropper. Crypto virology extends beyond
finding protocol failures and design vulnerabilities. .
Public-key cryptography is very essential for the
attacks that based on cryptovirology. Crypto virology
attacks have been devised to: give malware enhanced
privacy and be more Robust against reverse-
engineering, give the attacker enhanced anonymity
when Communicating with deployed malware to
improve the ability to steal data, improve the ability
to carry out extortion, Enable new types of denial-of-
service; enable fault-tolerance in distributed crypto
viral attacks, and so on. This field also encompasses
covert attacks in which the attacker secretly steals
private information such as private keys.
This field was actually introduced with the
observation that the public-key cryptography can be
used to break the symmetry between what an
antivirus analyst knows regarding a virus and what
the virus writer. The former can only see a public key
whereas the latter can see a public key and
corresponding private key as well. The first attack
that was identified in this field is the "cryptoviral
extortion". The field includes hidden attacks in which
the attacker
secretly steals
private
information like
private keys. In
the cryptoviral
extortion attack
a malware
hybrid encrypts
the plaintext
from the
victims system
using the public
key of the
attacker. The attacker demands some form of
payment from the victim as ransom in return for the
plaintext that is held hostage. In the public eye, the
word cryptography is virtually synonymous with
security. It is a means to an end, a way to send e-mail
privately and purchase items securely on-line.
To reduce the risk of being get attacked or infected
by a cryptovirus, some of the counter measures are
described in this paper. Many of the attacks described
in this paper can be avoided with existing antiviral
mechanisms and a tool, since cryptoviruses propagate
in the similarly as traditional viruses does.
Fig 1 Skeletal of Crypto Virus
International Journal of Computer Trends and Technology (IJCTT) - volume4 Issue5May
ISSN: 2231-2803 http://www.ijcttjournal.org Page 1150
II. BACKGROUND
A. Cryptography
"Cryptography" is used to information processing and
communications, because it allows people to store
information securely and conduct private
communications over long distances. There are
mainly two aspects in cryptography algorithms and
the key used [5]. The important encryption
techniques are symmetric, asymmetric, hash function
algorithms. Symmetric-key cryptography refers to
encryption methods in which both the sender and
receiver share the same key of decryption. In
asymmetric key cryptography, the encryption key is
the public and decryption key is the private key or
secret key individually.
B. Cryptovirology
Cryptovirology is the study of the applications of
cryptography for implementation of malicious
software [5]. It is about, how modern cryptographic
paradigms and tools can be used to strengthen,
improve, and develop new malicious software
attacks. Cryptovirology attacks have been
categorized to: give enhanced privacy to the malware
and be more robust against reverse-engineering,
secondly give the attacker enhanced anonymity while
communicating with deployed malware.
C. Kleptography
"Kleptography" is the study of stealing the
information more securely. A kleptographic attack is
an attack in which a malware designer deploys an
asymmetric backdoor. In this attack, there is an
explicit distinction between confidentiality of the
messages and awareness of the attack is taking place.
A secure kleptographic attack is truly undetectable as
long as the cryptosystem is a black-box [2]. A
kleptographic attack is an asymmetric backdoor
attack that can only used by the designer that carries
out the attack. If reverse engineering detects the key
generation code then he or she will get known that a
kleptographic attack is underway.
D. Cryptanalysis
Cryptography is the science of making the secret
unintelligible and cryptanalysis is the science of
retrieving the secret from that unintelligible data for
the further use [2].
E. Crypto virus
In computer security, a crypto virus is defined as a
computer virus that contains and uses a public key.
Usually the public key belongs to the author of the
virus, though there are other possibilities as well. For
instance, a virus or
worm may generate and
use its own Key pair at
run-time [5]. Crypto
viruses may utilize
secret sharing to hide
information and may
communicate by
reading posts from
public bulletin boards.
Crypto Trojans and
crypto worms are the
same as crypto viruses, except they are Trojan horses
and worms, respectively.
III. ATTACKING METHODOLOGY OF CRYPTO VIRUS
A. Cryptoviral Extortion [4]
Crypto viral extortion is mechanism for the
encrypted viruses which uses public key
cryptography, in a denial of resources (DoR) attack
which can be introduced by the crypto virus. It is a
three-round protocol which is carried out by an
attacker against the victim. The attack is generally
carried out via a cryptovirus that uses a hybrid
cryptosystem to encrypt data while deleting or
overwriting the original data in the infecting process.
The virus notifies its victim that the attack has
occurred and states that the asymmetric cipher-text
will be needed to restore the original data. If the
victim ready to pay the ransom and transmitting the
asymmetric cipher-text to the virus author then the
virus author decrypts the cipher-text using the private
key that only the virus author has. The virus author
sends that symmetric key and corresponding
initialization vector to the victim. These are then used
to restore the data that was held ransom. The attack
will be is ineffective if the data can be recovered
from backups of victims computer.
B. The Secret Sharing Virus
This type of attack shows how to implement a virus
that is a very close approximation to the highly
servile virus. Where as in the above attack the virus
author managed the keys and owned the private key
and the virus itself will manage its private key. Since
a virus holding a public key and managing its private
key can be get analysed by antivirus analyst and
could lose its power [6].
C. Deniable Password Snatching
In the DPS attack, the attacker first seeks to install a
crypto Trojan into a target computer. Already it
seems possible that the attacker is at the high risk of
getting caught and most probably if he has installs the
crypto Trojan manually. The attack is generally
Fig 2 Cryptovirus
International Journal of Computer Trends and Technology (IJCTT) - volume4 Issue5May
ISSN: 2231-2803 http://www.ijcttjournal.org Page 1151
carried out by using a custom crypto virus designed
by the attacker. The purpose of this whole is to allow
the attacker to indirectly run code of his own Trojan
without being blamed for installing it.
Among these above attacking techniques we
mainly concentrate on the first technique
i.e.,Cryptoviral Extortion the complete methods
and tasks included in these techniques can be
illustrated in following sections:
1) Cryptoviral Extortion Attack Scenarios:
Scenario 1 is a cryptoviral extortion protocol
performed by encryption of the victims data as
ransom.
Scenario 2 is same as to Scenario 1 except for that the
virus writer also demands the victims encrypted text
for decryption along with the ransom.
Scenario 3 explains a secret sharing cryptovirus. The
attack works on network with infected hosts. In this
attack asymmetric private key is divided into parts
and shared among all infected network host.
Scenario 4 states the involvement of a cryptovirus in
a Deniable Password Snatching (DPS) attack.
IV. LATEST EVENTS
A. Gpcode [6]
This Trojan modifies data on the victim system so
that the victim cannot use the data or it prevents the
computer from functioning correctly. Once the data
has been encrypted, the user will receive demand for
ransom. The ransom demand states to send the
money to the attacker, on the receipt of this, the virus
writer will send a program to the victim to restore the
original data or restore his computers performance.
Gpcode is one of the classic cryptovirus. Another
classic cryptovirus is Virus.Win32.Gpcode.ag. It
partially uses the version of 660-bit RSA (RSA
private key) and encrypts files in many different
extensions and overwrites or removes the original
one. It tells victim to email a given mail ID if the he
desires the decryptor of data to regain the original
data. If attacker contacted by email, the victim will be
asked to pay a certain amount of money as ransom in
return for the decryptor of data.
Virus uses cryptography for extortion.
Files in the infected computer are
encrypted.
Asks for a fee to decrypt the files.
Virus spreads through email.
1) How Gpcode spreads...:
Email message:
Dear customer!
We are very much glad to be as our customer. We are
really thankful to you for choosing our service. We
need your valuable feedback about out services this
will really helpful to providing better services further.
Thats why please fill out the attached feedback form
based on your views and opinions related to our
services and send that form.
Sincerely,
Shanon fedo
Head of the Marketing Dept
Armway Home needs Agency Pvt.Ltd
Fig 3 How the cryptovirus attaching to the actual code
This email has an MS word .doc file called
feedback.doc attached. File contains a
malicious program called Trojan-
Dropper.MSWord.Tored.a.
On opening that feedback.doc file, a
malicious macro installs another Trojan
Trojan Downloader.Win32.Small.crb on the
victim machine.
This Trojan then downloads Gpcode from
[skip].msk.ru/services.txt and installs it to
the victim machine.
2) How GPcode attacks the victims system:
Scans all accessible directories and encrypts files
with certain extensions such as .txt, .xls, .rar, .doc,
.html, .pdf etc. Also encrypts mail client databases.
Gpcode and the other Trojans self destruct. Leave
behind a file in each directory which has an
encrypted file with README.txt.
3) Cryptanalysis:
Initially 56-bit RSA key was used.
660-bit key was cracked by Kaspersky Labs.
The technique used was never published
(trade secret!)
Now, GPcode uses 1024-bit.
International Journal of Computer Trends and Technology (IJCTT) - volume4 Issue5May
ISSN: 2231-2803 http://www.ijcttjournal.org Page 1152
B. Conflicker
Conficker is also nicknamed as Downup, Downadup
and Kido, is a computer worm targeted to the
Microsoft Windows operating systems that was
detected in November 2008 for first time. It makes
use of the flaws in Windows software and make
Dictionary attack on administrator passwords to co-
opt system and link them into a virtual computer that
can be commanded remotely by attacker. Conficker
has since spread very rapidly into what is now known
as the largest computer worm infection since the
2003 SQL Slammer, with more than seven million
government, business and home computers in over
two hundred countries now in its control. The worm
has been usually difficult to detect because of its
combined use of many advanced malware tools and
techniques [7] [6].
1) TimeLine:
Win32/Conficker.A -November 21, 2008.
Win32/Conficker.B - December 29, 2008.
Win32/Conficker.C - February 20, 2009.
Win32/Conficker.D - March 4, 2009.
Win32/Conficker.E - April 8, 2009.
2) Initial Infection:
Variants A, B, C and E exploit vulnerability in the
Server Service on Windows computers. In the source
computer, the worm runs an HTTP server on a port
between 1024 and 10000. The target shell code
connects back to this HTTP server to download a
copy of the worm in DLL form, which it then
attaches to a running service.
3) Payload Propagation
Variant A generates a list of 250 domain
names every day across five TLDs (top
level domains).
Variant B increases the number of TLDs to
eight
Variant C creates a named pipe, over which
it can push URLs for downloadable
payloads to other infected hosts on a local
area network.
Variant D generates a daily pool of 50000
domains across 110 TLDs, from which it
randomly chooses 500 to attempt for that
day.
Variants D and E create an ad-hoc peer-to-
peer network to push and pull payloads over
the wider Internet.
4) Domain Name Generation:
Conficker implements its own random number
generator. Selectively chooses between its own
function generate _random () and system rand()
function. A top-level domain (TLD) suffix chosen
randomly between .com, .net, .org, .info, and .biz is
then appended to the domain name. Conficker B
includes additional TLD suffixes (.ws, .cn, .cc).
V. Countermeasures
There are several measures that can be taken to
immensely reduce the risk of being get attacked or
infected by a cryptovirus. Many of the attacks
described in here can be avoided with existing
antiviral mechanisms and a tool, since cryptoviruses
propagate in the similarly as traditional viruses does.
The first step toward this is, implementing
mechanisms and schemes to detect viruses before
infection or may be immediately following system
infiltration [6].
1. Only passwords are weak to authenticate a
host. Two level authentications, first with
the biometric entity such as the users
fingerprint, iris scan and second using the
password.
2. Use of up-to-date anti-virus mechanism, as
the crypto viruses spread similar to normal
viruses does.
3. Provide an access control mechanism to
cryptographic tools and APIs of the system.
This will helps virus analyst or the system
administrator to identify suspicious
cryptographic usage of the system
component.
4. The direct memory monitoring is needed to
catch self polymorphic encrypting,
cryptoviruses.
5. Use of intrusion detection System and
firewall to protect host in the network
system and the stand alone systems. Use
patches as they are made available to make
system more secure.
6. On-line proactive anti-viral measures
theoretic for now.
7. Access control to cryptographic tools
If strong crypto ciphers and random number
generators are available to user processes,
then they are available to viruses.
8. Backups
International Journal of Computer Trends and Technology (IJCTT) - volume4 Issue5May
ISSN: 2231-2803 http://www.ijcttjournal.org Page 1153
VI. CONCLUSIONS
We have shown how Cryptography can be used to
implement viruses that are able to perform extortion-
based attacks on their hosts. Public-key cryptography
is very much essential in enabling the virus-author to
get an advantage over the victimsystem. We also
suggested a set of counter measures that can be taken
to minimize some sort of possibility to reduce the
risks posed by the crypto virological attacks such as
latest events like Gpcode and Conflicker. Finally,
Cryptographic techniques and tools can be used to
create a new class of viruses: Cryptoviruses in which
the virus/Trojan writer need not be aware of all the
cryptography tools and use of available functions
(like APIs) and a victims point of view also, it is
better to know the different types of attacks by the
attacker to keep some of the safeguards to protect
their system and networks from attacker. The goal of
cryptanalysis is not to undo the honourable work of
others, but to find vulnerabilities and fix them.
VII. ACKNOWLEDGMENT
We are thankful to GMR Institute of Technology,
Rajam, AP, India and all our faculty members of
Information Technology Department for their
encouragement and whole hearted cooperation. I
would like to thank Asst. Prof. M.Balajee for his
guidance and valuable suggestions time to time. We
are lucky to have god like Parents, they provided me
very excellent moral support and Friends for their
encouragement during this work.
VIII. REFERENCES
[1] Malicious Cryptography Exposing Cryptovirology by
AdamYoung Moti Yung , Wiley Publishing, Inc.
[2] http://en.wikipedia.org
[3] Shafiqul Abidin, Rajeev Kumar, Varun Tiwari, A
Review Report on Cryptovirology and Cryptography
International J ournal of Scientific & Engineering
Research, Volume 3, Issue 11, November-2012 1 ISSN
2229-5518
[4] AdamYoung and Moti Yung, Cryptovirology:
Extortion-Based Security Threat and Countermeasures,
Proceedings of the1996 IEEE Symposiumon Security
and Privacy.
[5] Cryptovirology.comFAQ:
http://www.cryptovirology.com/
[6] ShivaleSaurabh Anandrao, Cryptovirology: Virus
Approach International J ournal of Network Security &
Its Applications (IJNSA), Vol.3, No.4, J uly 2011
[7] http://www.viruslist.com/en/viruses/encyclopedia?virus
id=313 444
Das könnte Ihnen auch gefallen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (890)
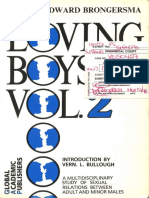
- Edward Brongersma - Loving Boys Vol. 2Dokument258 SeitenEdward Brongersma - Loving Boys Vol. 2RaymondGraciaNoch keine Bewertungen
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Constitutional Limitations on Congress' Power to Define and Punish CrimesDokument4 SeitenConstitutional Limitations on Congress' Power to Define and Punish CrimesMaya Sin-ot ApaliasNoch keine Bewertungen
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Security Proposal in Word FileDokument25 SeitenSecurity Proposal in Word FileAjay GuptaNoch keine Bewertungen
- People Vs Catubig (2001)Dokument6 SeitenPeople Vs Catubig (2001)Zan BillonesNoch keine Bewertungen
- 9.3 Data Breach Notification Form To The Supervisory Authority Preview enDokument1 Seite9.3 Data Breach Notification Form To The Supervisory Authority Preview enBogdan CorneaNoch keine Bewertungen
- Double Jeopardy Bar to Second Prosecution for Serious InjuryDokument97 SeitenDouble Jeopardy Bar to Second Prosecution for Serious InjuryKevin Ampuan0% (1)
- Non-Linear Static Analysis of Multi-Storied BuildingDokument5 SeitenNon-Linear Static Analysis of Multi-Storied Buildingseventhsensegroup100% (1)
- People V SayoDokument17 SeitenPeople V SayobogoldoyNoch keine Bewertungen
- Timoteo Garcia Vs SandiganbayanDokument1 SeiteTimoteo Garcia Vs SandiganbayanGen Jore67% (3)
- Criminal Psychology SyllabusDokument15 SeitenCriminal Psychology Syllabuspaleoman8Noch keine Bewertungen
- Comparison of The Effects of Monochloramine and Glutaraldehyde (Biocides) Against Biofilm Microorganisms in Produced WaterDokument8 SeitenComparison of The Effects of Monochloramine and Glutaraldehyde (Biocides) Against Biofilm Microorganisms in Produced WaterseventhsensegroupNoch keine Bewertungen
- Fabrication of High Speed Indication and Automatic Pneumatic Braking SystemDokument7 SeitenFabrication of High Speed Indication and Automatic Pneumatic Braking Systemseventhsensegroup0% (1)
- Experimental Investigation On Performance, Combustion Characteristics of Diesel Engine by Using Cotton Seed OilDokument7 SeitenExperimental Investigation On Performance, Combustion Characteristics of Diesel Engine by Using Cotton Seed OilseventhsensegroupNoch keine Bewertungen
- Comparison of The Regression Equations in Different Places Using Total StationDokument4 SeitenComparison of The Regression Equations in Different Places Using Total StationseventhsensegroupNoch keine Bewertungen
- An Efficient Model of Detection and Filtering Technique Over Malicious and Spam E-MailsDokument4 SeitenAn Efficient Model of Detection and Filtering Technique Over Malicious and Spam E-MailsseventhsensegroupNoch keine Bewertungen
- Optimal Search Results Over Cloud With A Novel Ranking ApproachDokument5 SeitenOptimal Search Results Over Cloud With A Novel Ranking ApproachseventhsensegroupNoch keine Bewertungen
- Extended Kalman Filter Based State Estimation of Wind TurbineDokument5 SeitenExtended Kalman Filter Based State Estimation of Wind TurbineseventhsensegroupNoch keine Bewertungen
- Design, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)Dokument7 SeitenDesign, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)seventhsensegroupNoch keine Bewertungen
- High Speed Architecture Design of Viterbi Decoder Using Verilog HDLDokument7 SeitenHigh Speed Architecture Design of Viterbi Decoder Using Verilog HDLseventhsensegroupNoch keine Bewertungen
- A Multi-Level Storage Tank Gauging and Monitoring System Using A Nanosecond PulseDokument8 SeitenA Multi-Level Storage Tank Gauging and Monitoring System Using A Nanosecond PulseseventhsensegroupNoch keine Bewertungen
- Color Constancy For Light SourcesDokument6 SeitenColor Constancy For Light SourcesseventhsensegroupNoch keine Bewertungen
- FPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorDokument4 SeitenFPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorseventhsensegroupNoch keine Bewertungen
- Implementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationDokument6 SeitenImplementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationseventhsensegroupNoch keine Bewertungen
- Application of Sparse Matrix Converter For Microturbine-Permanent Magnet Synchronous Generator Output Voltage Quality EnhancementDokument8 SeitenApplication of Sparse Matrix Converter For Microturbine-Permanent Magnet Synchronous Generator Output Voltage Quality EnhancementseventhsensegroupNoch keine Bewertungen
- Ijett V5N1P103Dokument4 SeitenIjett V5N1P103Yosy NanaNoch keine Bewertungen
- Design and Implementation of Height Adjustable Sine (Has) Window-Based Fir Filter For Removing Powerline Noise in ECG SignalDokument5 SeitenDesign and Implementation of Height Adjustable Sine (Has) Window-Based Fir Filter For Removing Powerline Noise in ECG SignalseventhsensegroupNoch keine Bewertungen
- The Utilization of Underbalanced Drilling Technology May Minimize Tight Gas Reservoir Formation Damage: A Review StudyDokument3 SeitenThe Utilization of Underbalanced Drilling Technology May Minimize Tight Gas Reservoir Formation Damage: A Review StudyseventhsensegroupNoch keine Bewertungen
- An Efficient and Empirical Model of Distributed ClusteringDokument5 SeitenAn Efficient and Empirical Model of Distributed ClusteringseventhsensegroupNoch keine Bewertungen
- Ijett V4i10p158Dokument6 SeitenIjett V4i10p158pradeepjoshi007Noch keine Bewertungen
- An Efficient Encrypted Data Searching Over Out Sourced DataDokument5 SeitenAn Efficient Encrypted Data Searching Over Out Sourced DataseventhsensegroupNoch keine Bewertungen
- An Efficient Expert System For Diabetes by Naïve Bayesian ClassifierDokument6 SeitenAn Efficient Expert System For Diabetes by Naïve Bayesian ClassifierseventhsensegroupNoch keine Bewertungen
- A Comparative Study of Impulse Noise Reduction in Digital Images For Classical and Fuzzy FiltersDokument6 SeitenA Comparative Study of Impulse Noise Reduction in Digital Images For Classical and Fuzzy FiltersseventhsensegroupNoch keine Bewertungen
- Review On Different Types of Router Architecture and Flow ControlDokument4 SeitenReview On Different Types of Router Architecture and Flow ControlseventhsensegroupNoch keine Bewertungen
- Separation Of, , & Activities in EEG To Measure The Depth of Sleep and Mental StatusDokument6 SeitenSeparation Of, , & Activities in EEG To Measure The Depth of Sleep and Mental StatusseventhsensegroupNoch keine Bewertungen
- Study On Fly Ash Based Geo-Polymer Concrete Using AdmixturesDokument4 SeitenStudy On Fly Ash Based Geo-Polymer Concrete Using AdmixturesseventhsensegroupNoch keine Bewertungen
- Key Drivers For Building Quality in Design PhaseDokument6 SeitenKey Drivers For Building Quality in Design PhaseseventhsensegroupNoch keine Bewertungen
- A Review On Energy Efficient Secure Routing For Data Aggregation in Wireless Sensor NetworksDokument5 SeitenA Review On Energy Efficient Secure Routing For Data Aggregation in Wireless Sensor NetworksseventhsensegroupNoch keine Bewertungen
- Free Vibration Characteristics of Edge Cracked Functionally Graded Beams by Using Finite Element MethodDokument8 SeitenFree Vibration Characteristics of Edge Cracked Functionally Graded Beams by Using Finite Element MethodseventhsensegroupNoch keine Bewertungen
- Performance and Emissions Characteristics of Diesel Engine Fuelled With Rice Bran OilDokument5 SeitenPerformance and Emissions Characteristics of Diesel Engine Fuelled With Rice Bran OilseventhsensegroupNoch keine Bewertungen
- Anthropometry IntroductionDokument35 SeitenAnthropometry Introductioninhee633Noch keine Bewertungen
- BALBUENA's GROUPDokument2 SeitenBALBUENA's GROUPNicanilanena BalbuenaNoch keine Bewertungen
- 4 types of abuse against women and childrenDokument10 Seiten4 types of abuse against women and childrenRebecca JordanNoch keine Bewertungen
- South Carolina Constitution 1895Dokument96 SeitenSouth Carolina Constitution 1895Demetrius New El100% (1)
- CADAC Ordinance Establishes Bacolod City Anti-Drug CouncilDokument4 SeitenCADAC Ordinance Establishes Bacolod City Anti-Drug CouncilRey PerezNoch keine Bewertungen
- TortsDokument5 SeitenTortsȘova AngelicaNoch keine Bewertungen
- Bar Questions Answers. Set 34Dokument3 SeitenBar Questions Answers. Set 34cjadapNoch keine Bewertungen
- Advantages and Disadvantages of Social MediaDokument5 SeitenAdvantages and Disadvantages of Social MediaAbubakar SohailNoch keine Bewertungen
- The ICT Lounge: Dangers of Online CommunicationDokument6 SeitenThe ICT Lounge: Dangers of Online CommunicationJedediah PhiriNoch keine Bewertungen
- Municipal Resolution For CIRDokument2 SeitenMunicipal Resolution For CIRBjustb LoeweNoch keine Bewertungen
- Political Mysteries (Malkani, K R) (Z-Library)Dokument110 SeitenPolitical Mysteries (Malkani, K R) (Z-Library)SUYASH DIXITNoch keine Bewertungen
- Auditor warns of phishing scamDokument3 SeitenAuditor warns of phishing scamFDEFNoch keine Bewertungen
- Worksheet Answer Key: Philip ProwseDokument2 SeitenWorksheet Answer Key: Philip ProwsefthtlNoch keine Bewertungen
- Washoe County District Attorney's Office Releases Report On Fatal Officer-Involved Shooting in SparksDokument28 SeitenWashoe County District Attorney's Office Releases Report On Fatal Officer-Involved Shooting in SparksReno Gazette JournalNoch keine Bewertungen
- Donald Ogman, Government MemoDokument38 SeitenDonald Ogman, Government MemomtuccittoNoch keine Bewertungen
- Legal Ethics DigestDokument16 SeitenLegal Ethics DigestMarivicTalomaNoch keine Bewertungen
- Felipe Jimenez, A046 294 792 (BIA March 4, 2015)Dokument11 SeitenFelipe Jimenez, A046 294 792 (BIA March 4, 2015)Immigrant & Refugee Appellate Center, LLCNoch keine Bewertungen
- Luis A Garavito TextDokument3 SeitenLuis A Garavito TextMarranNoch keine Bewertungen
- GBV Me HandoutsDokument19 SeitenGBV Me HandoutsamimuNoch keine Bewertungen
- PNP organizational structureDokument5 SeitenPNP organizational structureHarla Jane Ramos FlojoNoch keine Bewertungen
- State v. Myers - 76-CF-00912 - Petition For CompensationDokument194 SeitenState v. Myers - 76-CF-00912 - Petition For CompensationAnne SchindlerNoch keine Bewertungen