Beruflich Dokumente
Kultur Dokumente
Ijettcs 2014 05 29 062
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
13 Ansichten7 SeitenInternational Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org, editorijettcs@gmail.com
Volume 3, Issue 3, May-June 2014 ISSN 2278-6856, ISRA Journal Impact Factor:
3.258
Originaltitel
IJETTCS-2014-05-29-062
Copyright
© © All Rights Reserved
Verfügbare Formate
PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenInternational Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org, editorijettcs@gmail.com
Volume 3, Issue 3, May-June 2014 ISSN 2278-6856, ISRA Journal Impact Factor:
3.258
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
13 Ansichten7 SeitenIjettcs 2014 05 29 062
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org, editorijettcs@gmail.com
Volume 3, Issue 3, May-June 2014 ISSN 2278-6856, ISRA Journal Impact Factor:
3.258
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 7
International Journal of EmergingTrends & Technology in Computer Science(IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 3, Issue 3, May June 2014 ISSN 2278-6856
Volume 3, Issue 3 May June 2014 Page 58
Abstract: Mobile Adhoc NETwork is the self organized
infrastructure less network which is formed by a collection of
mobile nodes that communicate with each other via wireless
links directly or with the help of intermediate nodes. These
mobile nodes contain both transmitter and receiver in them.
In this paper we discuss the MANETs, Categories and various
IDS with their limitations.
Keywords: MANETs, IDS Credit Based Schemes,
Reputation Based Schemes, Acknowledgement schemes
1.INTRODUCTION
Routing protocols such as Dynamic Source Routing can
be used to determine the route from a node to another
node. Due to its nature of open medium, the MANETs
may have severe threats posed by attackers or malicious
node. Nodes in the network move rapidly and hence there
is no fixed network topology for MANETs.
There are two types of MANETs:
Closed MANETs
Open MANETs [1]
Closed MANETs: In close MANETs all the mobile
nodes work collaboratively to accomplish a common goal.
Eg: Military operations.
Open MANETs: In open MANETs all the nodes in the
network have their own goals, yet they share their
resources to accomplish some global activity.
Some resources in the network will be consumed very
quickly, such as battery power of mobile nodes. The nodes
in the network may sometimes act as misbehaving nodes
or sometimes behaves selfishly. For example, a node may
attempt to benefit the resources from other nodes in the
network but may refuse to share its own resources. Such
nodes are called Selfish nodes or Misbehaving nodes.
Another example is [2] a selfish node may refuse to
forward data packets to other nodes in the network so as
to conserve its energy.
2.INTRUSION DETECTION SYSTEMS
Intrusion Detection System is a security management
system that monitors network traffic to detect suspicious
activities attempted by nodes in the network. Various
schemes have been proposed to prevent selfishness in
MANETs. Intrusion Detection Systems are broadly
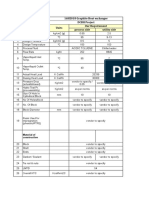
classified into three categories shown below:
1. Credit-based schemes.
2. Reputation-based schemes.
3. End-to-End Acknowledgement Scheme.
2.1 Credit-Based Schemes
In this category, a credit is given to every node so that
they can provide services to every other node in the
network. To achieve this, virtual currency system can be
set up. Every node in the network is paid for providing
services to other nodes in the network. Whenever a node
provides service it gets paid for it, and in turn pays the
credit when it requests other nodes to help it in
forwarding the packets [3], [4], [5], [6]. Buttyan [3] and
Hubaux [3] proposed a concept of nuggets or beans to be
paid by each node to the other nodes for helping them in
packet forwarding.
As a result two models were proposed by them [3]:
a) The Packet Purse Model
b) The Packet Trade Model
i) The Packet Purse Model:
In the Packet Purse Model, every packet is loaded with
the nuggets before it is forwarded to the next node. The
sender puts a certain number of nuggets on the data
packet to be sent. Each intermediate node that forwards
this packet gains nuggets from it. If the nuggets in the
packet are emptied before it reaches the destination and if
there are still the nodes prior to destination in the
transmission path then the packet will be dropped.
ii)The Packet Trade Model:
In the Packet Trade Model, each node actively does the
trading business. Each node buys the packet from
previous node for some nuggets and sells it to the next
node at a profit i.e. more nuggets. Therefore each
intermediate node earns some nuggets for forwarding the
packets to next node in the transmission path. The
destination node bears overall cost of forwarding the
packet.
Limitations of Credit Based Schemes:
Credit-Based schemes have a limitation that they require
additional hardware or credit payment system.
2.2 Reputation-Based Schemes
In Reputation Based schemes [7], [8], all the nodes in the
network collaboratively work to detect and declare the
suspicious node as the misbehaving node. This
declaration is propagated to all the nodes in the network
so as to block the misbehaving node from rest of the
network.
i) Watchdog & Pathrater Scheme:
The watchdog [7][9][10][11][12] scheme is the IDS that
detect misbehaving nodes in the network formed by
mobile nodes. Watchdog is installed in all the nodes of
A SURVEY & COMPARISON OF
INTRUSION DETECTION SYSTEMS IN
MANETS
Ms. Rasagna Chinthireddy
1
and Dr. S Aravind
2
1
Dept. of CSE, CMRIT, Kandlakoya, Hyderabad
2
Professor & Head, CSE, CMRIT, Kandlakoya, Hyderabad
International Journal of EmergingTrends & Technology in Computer Science(IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 3, Issue 3, May June 2014 ISSN 2278-6856
Volume 3, Issue 3 May June 2014 Page 59
the MANET. Whenever a node forwards a packet to the
next node in the path to reach the destination, the
watchdog installed in the node ensures that the next node
in the path forwards the packet by overhearing the
transmission promiscuously.
Each node in the MANET does this to ensure the packets
are transmitted to next node in the path. Any node that
does not forward the packet which it receives is
considered to be a compromised and hence is marked as
misbehaving node by the previous node that sent packet
to this node. In such case the failure counter of this node
is incremented. A threshold is set prior to the
transmission begins in the network, and if any nodes
failure counter value exceeds this threshold such node is
tagged as malicious node and hence this node is blocked
for future transmissions. On overhearing the transmission
at next node if the previous node learns that the packet is
forwarded, then this next nodes trustworthiness is
increased. If the Watchdog node that detected the
misbehaving node is not the source node, then it sends a
message to the source node identifying the misbehaving
node. Watchdog is robust to most of the attacks as they
use only local information.
Suppose there exists a path from node A to D through the
intermediate nodes B and C. A transmits the packet to
node B and then promiscuously listens to node B's traffic.
Since a watchdog is installed in every node, A overhears
the operation of node B and can tell if B transmits the
packet to C. Figure 1 [13], shows the normal case of
forwarding packets from source A to destination D.
Fig 1: Normal overhearing of packets
Packet 1 is transmitted from A to B. B transmits packet
from B to C. Since A is within the transmission range of
B A can overhear Bs traffic, A also receives the same
packet that is transferred from B to C. With the
information received from B, node A can decide whether
B is malicious or not.
Figure 2 [13], shows the detection of malicious nodes in
the transmission path. Here B is a malicious node and
drops all packets instead of forwarding. Node A transmits
a packet to B, but it overhears that node B does not
forward the packet to next node in the path. Therefore A
decides B to be malicious node and increments its failure
count.
Fig 2: Malicious Node detection
In MANETs there exits more than one route to reach the
destination from source. Pathrater [14] works in
collaboration with the routing protocols in deciding
which path should be chosen to transmit the packets to
reach the destination. Every node uses the information
provided by watchdogs to rate neighbor nodes. Each node
in the network maintains the reliability rating for every
other node in the network. Pathrater calculates the rating
of each path from source to destination by taking the
average of ratings all the nodes involved in the path.
Since there may exist multiple paths between source and
destination in MANETs, the path that has the highest
reliability rating is chosen for transmission of data
packets.
The Routeguard [16] mechanism combines the watchdog
and Pathrater solutions to classify each neighbor node as
Fresh, Member, Unstable, Suspect or Malicious node.
Watchdog can only monitor the first node while the
second malicious node performs an attack.
Limitations of the watchdog mechanism:
Though the watchdog scheme is sufficient to identify the
malicious nodes and packet collisions, it is difficult for a
watchdog to differentiate whether the loss of a packet is
due to an attack or a collision.
The weaknesses of Watchdog scheme are namely, false
misbehavior, limited transmission power, and receiver
collision.
a) Receiver Collisions Problem:
Fig 3 [15] shows the receiver collisions problem that
persists in Watchdog Scheme. Source node S intends to
forward packet 1 to destination node D. It does so by
sending packet to A and overhears its transmission,
similarly A transmits packet to B. When B transmits
packet, A learns that B forwarded the packet but never
ensures if C received it. At the same time X tries to send
packet 2 to C. Therefore both packet 1 & 2 collides at
receiver C and hence both the packets are dropped.
Though C had not intentionally missed forwarding
packets both B and X assumes C to be malicious node and
inform the same to respective sources.
Fig 3: Receiver Collision Problem in Watchdog Scheme
b) False Misbehavior Report:
International Journal of EmergingTrends & Technology in Computer Science(IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 3, Issue 3, May June 2014 ISSN 2278-6856
Volume 3, Issue 3 May June 2014 Page 60
Figure 4 [15] shows the false misbehavior report
generated by node A, though node A overhears that the
packet is transmitted from node B to C. Node A
intentionally does this because it so happens when a node
in a network can be compromised and act as malicious
node.
Fig 4: False Misbehavior Report Problem in Watchdog
Scheme
c) Limited Transmission Power:
The nodes in the MANETs limit their transmission power
in order to protect their battery from getting drained soon.
This leads to limited transmission power problem to occur
in watchdog scheme. Node S is source node and Node D
is destination node, all the intermediate nodes in the path
between S and D involve in transmitting packets. It can
be seen in the Figure 5 [15], node A overhears that B
transmitted packet successfully but C did not receive
packet as Bs transmission range is limited.
Fig 5: Limited Transmission Power Problem in
Watchdog Scheme
d) Ambiguous Collisions Problem:
Ambiguous collisions prevent the nodes from overhearing
next node. From the figure 6 [15], it can be observed that
collision occurred at node A while it is in a process of
overhearing the next node transmissions.
Fig 6: Ambiguous collisions problem in Watchdog
scheme
The node A will not be able to decide if collision occurred
because B forwarded the packet to next node or if B
never forwarded the packet and the collision was caused
due to some other neighboring node of A (in this case S).
ii)CONFIDANT Protocol:
This protocol proposed by Buchegger and Le Boudec[8] is
also a reputation-based scheme. It is made up of four
components. These components watch their neighbor
nodes, rate them, rate the path and also send and receive
the alarm messages.
The four components of CONFIDANT protocol are:
a) The Monitor:
Every node in the network continuously monitors the
behavior of the node next to it. If any suspicious event is
detected, the details of such event are passed to the next
component i.e. Reputation System.
b) The Reputation System:
The rating of the suspected node is modified (either
incremented or decremented) based on the details such as
frequency of the suspicious event and also significance of
such event.
c) The Path Manager:
When the node rating crosses the predefined threshold the
control is passed to this component by the Reputation
System. This system then controls the route cache.
d) The Trust Manager:
This component propagates the alarm message to all the
nodes in the network.
Limitations of CONFIDANT protocol:
The monitor component in this scheme works same as
that of the watchdog scheme in which it observes and
overhears the next nodes transmission. Hence this
scheme also has the same limitations as that faced by the
watchdog scheme.
2.3 End-to-End Acknowledgment Schemes
There are several schemes that use end-to-end
acknowledgments (ACKs) to detect routing misbehavior
or malicious nodes in wireless networks.
i) 2 ACK SCHEME
The watchdog scheme [7][9][10][11][12] suffers from
several problems such as ambiguous collisions, receiver
collisions, and limited transmission power and false
misbehavior report. The major problem is that the
successful reception of packets can only be determined at
the receiver of the next hop link, but the watchdog
scheme only monitors the sender of next hop link.
Since the next hop links sender or receiver can be a
misbehaving node, therefore it is necessary to detect
misbehaving links instead of the misbehaving nodes. The
2ACK scheme proposed by Liu et al.[17] is a network-
layer technique to detect misbehaving links. The 2ACK
scheme detects misbehavior through using
acknowledgment packet namely 2ACK. This packet is
sent by a node to two nodes down the line along the route.
Fig. 7 illustrates the operation of the 2ACK scheme.
From the figure it can be seen that N1, N2, and N3 are
three consecutive nodes along the transmission path.
Fig 7: 2ACK schemes
International Journal of EmergingTrends & Technology in Computer Science(IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 3, Issue 3, May June 2014 ISSN 2278-6856
Volume 3, Issue 3 May June 2014 Page 61
The routing protocol DSR determines the route from
source node S to destination node D in the Route
Discovery Phase. N1 sends data packet to N2 and then N2
sends the data packet to N3, but N1 cannot ensure
whether N3 receives the data packet or not. This happens
even when no nodes in the path are misbehaving nodes.
This problem becomes severe when the nodes misbehave
in MANETs. Hence to overcome this problem the 2ACK
scheme ensures that each node sends an
acknowledgement packet two hops down the line along
the route in opposite direction i.e. Node N3 on successful
reception of data packet must send the acknowledgement
2ACK to N1 via N2. This acknowledgment 2ACK
contains ID of the corresponding data packet received by
N3.
This 2ACK transmission takes place for every set of three
nodes. Therefore, only the first node next to source will
not send the 2ACK packet and only the last node just
before destination & destination node both will not
receive the 2ACK packets. Each node in the transmission
path maintains the list of IDs of packets that are sent from
it for a predefined time say T seconds. If the 2ACK is
received within T seconds, then the ID of that packet
which is received successfully by third node (node that
sends acknowledgement) will be deleted from list at the
node receiving 2ACK. Otherwise the ID is deleted from
the list after T seconds and failure count will be
incremented.
The 2ACK scheme overcomes the watchdog scheme
limitations as mentioned below:
a) Ambiguous Collisions: In watchdog scheme
ambiguous collisions may occur at node N1. Sometimes it
may be possible that N2 forwards the packet to N3 and
still the node N1 cannot overhear N2s transmission due
to collision at N1 by other nodes transmission of packet to
it. This limitation of watchdog can be solved by 2ACK,
where 2ACK scheme insists node N3 to send 2ACK
packet to N1.
b) Receiver Collisions: In watchdog scheme, N1
forwards packet to N2 and overhears N2s transmission.
When N1 learns that N2 forwarded packet to N3 it rests
assure that packet is sent, but it may sometimes happen
that the data packet may not be received by N3 due to
collision at N3. Again, the 2ACK scheme overcomes this
problem with the help of acknowledgement packets i.e.
2ACK packets.
c) Limited Transmission Power: In MANETs the nodes
limit their transmission power to protect their battery
from getting drained soon. In the watchdog scheme when
a node say N2 limits its transmission power such a way
that node N1 can overhear its transmission when data
packet is sent from it, but it misbehaves (by limiting its
transmission power) such that data can never be reached
to N3. 2ACK acknowledgement packet is the solution for
such problem.
d) Limited Overhearing Range: In MANETs the nodes
limit their overhearing range to protect their battery from
getting drained soon. In watchdog scheme this may lead
to a limitation. Though the node N2 transfers the packet
successfully to N3, the node N1 may not be able to
overhear the transmission because of its limiting
overhearing range. This is again solved by the 2ACK
acknowledgement packets.
Limitations of 2ACK Scheme:
The 2ACK scheme solves the above mentioned problems
but at the same time creates network overhead. This
overhead is due to the fact that acknowledgement packets
are generated for every triplet.
ii)TWOACK Scheme:
The TWOACK scheme [19] is and End-End
acknowledgment scheme which can be implemented on
top of any source routing protocol like DSR. This scheme
works on the basis of special type of acknowledgment
packets called TWOACK packets which are sent back to
two hops in the direction opposite to that of the arrival of
data packets.
Fig 1: TWOACK Scheme
Figure 1 [19], shows the working of the TWOACK
scheme. Suppose that the DSR protocol has discovered a
route from source node S to destination node D as [S
N1 N2 N3 D]. Now assume node N1
should transfer a data packet to N2, and this packet is to
be transferred to node N3, Node N1 has no way to
determine whether the packet is delivered to N3
successfully or not. Listening to the next nodes
transmission as in overhearing schemes will only lead to
determining the nodes transmission but not the reception
of packet at next node. Hence it may even result in false
reports. The TWOACK scheme is designed to solve these
problems: when a node N3 receives a data packet, it sends
out a TWOACK packet over two hops back to N1 via N2.
The TWOACK packet contains the packet ID of that
packet which is received at N3. The backward route i.e.
[N3 N2 N1] via which the TWOACK packet is sent
is extracted from the data packet which is received at N3
that contains the route of source. The goal of this
TWOACK packet is to inform the source i.e. N1 that
node N3 received the data packet is received successfully.
This procedure is carried out by every three consecutive
nodes called as triplets.
The TWOACK and 2ACK schemes differ in the
following ways:
1) TWOACK packets are sent for every data packet
received whereas the 2ACK packets are sent for only
fraction of data packets received. Acknowledging only a
International Journal of EmergingTrends & Technology in Computer Science(IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 3, Issue 3, May June 2014 ISSN 2278-6856
Volume 3, Issue 3 May June 2014 Page 62
fraction of received data packets yield better performance
of 2ACK as this reduces network overhead due to more
number of acknowledgement packets compared to
TWOACK.
2) The 2ACK scheme uses an authentication mechanism
to ensure that the acknowledgement packets are genuine.
iii) The S-TWOACK Scheme
The TWOACK scheme results in generating two
TWOACK packets for every hop of data packet being
forwarded. Each TWOACK packet is a unique one and
hence causes congestion in the network. To overcome this
problem of network overhead of TWOACK, S-TWOACK
(Selective TWOACK) scheme [19] is proposed. Unlike
TWOACK scheme, S-TWOACK does not send
acknowledgement packet each time a data packet is
received. Instead it waits for the reception of certain
number of packets and then with a single
acknowledgement packet acknowledges all the packets
received so far.
Limitations of S-TWOACK Scheme:
a) It is expensive to avoid the problem of network
overhead.
b) False-alarm problems.
iv) Adaptive Acknowledgement Scheme (AACK):
Sheltami et al [12] proposed AACK scheme. This is also
an acknowledgement based network layer scheme and it
is a combination of two existing schemes such as
TWOACK and ACK. AACK scheme could reduce the
network overhead but could not improve the network
throughput. The figure 7 [15], below shows the ACK
scheme.
Fig 7: ACK (An End- End Acknowledgement)
It can be noticed that node S forwards the packet to the
destination via the intermediate nodes such as A, B, C
and X. The intermediate nodes forward this packet till the
destination node receives it. When the destination node
receives this packet it in turn sends an acknowledgement
packet via all the intermediate nodes down the line to the
source in an opposite direction. If the ACK is not received
within the predefined time period, then the data transfer
between source and destination node is not successful,
otherwise it is considered to be successful.
If the data transfer is not successful, the source node
switches from ACK mode to TACK mode by sending
TACK packet. This way of adopting hybrid technique of
combining both ACK and TACK scheme results in
reduced network overhead.
Limitations of AACK Scheme:
a) Fails to detect the malicious nodes in the presence
of false misbehavior report.
b) Fails to detect the malicious nodes in the presence
of forged acknowledgement packets.
v) EAACK- Enhanced Adaptive Acknowledgement:
This is also an acknowledgement based scheme. This
scheme was proposed by Elhadi M. Shakshuki et al. [15]
All the end-end acknowledgement schemes deal with
acknowledgement packets which need to be
authenticated.
EAACK consists three major parts:
End End Acknowledgement Scheme (ACK)
Secured Acknowledgement Scheme (S- ACK)
Misbehavior Report Authentication (MRA)
a) ACK Scheme
ACK is an end-to-end acknowledgment scheme which is
part of hybrid scheme of EAACK. ACK aims at reducing
the network overhead caused due to acknowledgement
packets.
Fig 8: ACK scheme
Fig. 8 [15], illustrates the operational details of ACK
mode, node S forwards a data packet P
ad1
to
destination node D. All the nodes in the transmission
path collaboratively work to forward the data packets
to D. On successful reception of data packet P
ad1
, the
destination node D responds back to source node by
sending it an acknowledgement packet P
ak1
in the
opposite direction. If the source node receives the
acknowledgement packet within the time set before
the data transfer between source and destination is
considered to be successful. Otherwise the source node
switches itself to the S-ACK mode by forwarding an
SACK packet to detect the misbehaving nodes in the
transmission path.
b) S- ACK mode:
The S-ACK scheme as proposed by Liu et al. [17] is an
improved version of the TWOACK scheme. The goal of
SACK scheme is to let every three consecutive nodes i.e.
every triplet to actively participate in identifying the
misbehaving nodes. The third node in the triplet has to
send an S-ACK acknowledgement packet back to the
node that is two hops away from it in opposite direction.
International Journal of EmergingTrends & Technology in Computer Science(IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 3, Issue 3, May June 2014 ISSN 2278-6856
Volume 3, Issue 3 May June 2014 Page 63
Fig 9: S-ACK mode
Fig 9 shows the operational details of S-ACK mode.
Suppose that the data need to be transferred from the
source node S to destination node D. Consider the three
consecutive nodes (say A, B, and C) as intermediate
nodes in the path from S to D. These nodes work
collaboratively to detect the misbehaving nodes in the
network. Node A forwards the S-ACK data packet P
sad1
to
the node B, Node B in turn forwards the same to node C.
As node C is the third node in the triplet, on successful
reception of this SACK packet, the node C now needs to
send the S-ACK acknowledgement packet P
sack1
back to
the first node in the triplet i.e A via B in an opposite
direction. If the first node in the triplet does not receive
the S-ACK acknowledgement packet P
sack1
in the
predefined time period node A reports both B and C as
malicious nodes. Therefore node A generates a
misbehavior report and sends to node S which is source
node.
The difference between TWOACK [19] scheme and
EAACK [15] is that in the former a source node trusts the
misbehavior report even in case of false misbehavior
report. Whereas in EAACK the source node on receipt of
misbehavior report switches to MRA mode, and verifies if
the received misbehavior report is true or false. The S-
ACK scheme was introduced in order to detect the
misbehaving nodes even in the presence of receiver
collisions or limited transmission power.
c) MRA
The overhearing techniques discussed in the Reputation
Based Schemes fail to detect misbehaving nodes with the
presence of false misbehavior report. The false
misbehavior reports are the ones which are generated by
malicious nodes in order to falsely report the innocent
node as a malicious node. This causes a severe problem
when the attackers try to divide the network into parts
attacking nodes in it. When a node sends a false
misbehavior report to the source node indicating loss of
some packet, the source node instead of trusting this
report sends an MRA packet via some alternative path to
the destination. This alternative route is chosen from its
local knowledge base, if the alternative path is not
available Dynamic Source Routing is used to determine
new route between source and destination. The
destination node now compares the packet ID mentioned
in MRA packet and the packet IDs of its local knowledge
base. If a match is found it, then the destination node
acknowledges back the source node indicating that the
packet said to be lost is actually received by it. Otherwise
the source will conclude that the report received is a false
one and hence marks the reporter as the malicious node.
Fig 9: Flowchart of operational details of EAACK
components
The figure 9 [15] shows the flow of control between the
three parts of EAACK.
d) Digital Signatures
EAACK is an End - End Acknowledgment scheme i.e. all
the above discussed components of EAACK operate based
on acknowledgement packets. Using these packets the
EAACK components identify the misbehavior nodes. It
may even happen such that these packets might be forged.
Hence it is necessary to ensure that these packets are
authentic. EAACK uses an additional methodology such
as Digital Signature Algorithm (DSA) [20] and RSA [20]
digital signature schemes to digitally sign the
acknowledgement packets.
3.CONCLUSION
With the increasing use and demand of MANETs,
security of MANETs has become the major concern.
Prevention alone is not the solution for this; hence
Intrusion Detection Systems have come into focus.
Various existing IDS were discussed in this paper. Every
IDS has its own limitations.
The EAACK scheme proposed by Elhadi et al. in [15]
successfully detects the malicious nodes in conditions
such as False Misbehavior Report and secures the
acknowledgement packets. Digital Signatures are used to
digitally sign the Acknowledgement packets.
REFERENCES
[1] H. Miranda and L. Rodrigues, Preventing
Selfishness in Open Mobile Ad Hoc Networks, Proc.
Seventh CaberNet Radicals Workshop, Oct. 2002.
International Journal of EmergingTrends & Technology in Computer Science(IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 3, Issue 3, May June 2014 ISSN 2278-6856
Volume 3, Issue 3 May June 2014 Page 64
[2] L.M. Feeney and M. Nilsson, Investigating the
Energy Consumption of a Wireless Network Interface
in an Ad Hoc Networking Environment, Proc. IEEE
INFOCOM, 2001.
[3] L. Buttyan and J.-P. Hubaux, Enforcing Service
Availability in Mobile Ad-Hoc WANs, Proc.
MobiHoc, Aug. 2000.
[4] J.-P. Hubaux, T. Gross, J.-Y. LeBoudec, and M.
Vetterli, Toward Self-Organized Mobile Ad Hoc
Networks: The Terminodes Project, IEEE Comm.
Magazine, Jan. 2001.
[5] L. Buttyan and J.-P. Hubaux, Stimulating
Cooperation in Self- Organizing Mobile Ad Hoc
Networks, ACM/Kluwer Mobile Networks and
Applications, vol. 8, no. 5, 2003.
[6] M. Jakobsson, J.-P. Hubaux, and L. Buttyan, A
Micropayment Scheme Encouraging Collaboration in
Multi-Hop Cellular Networks, Proc. Financial
Cryptography Conf., Jan. 2003.
[7] S. Marti, T. Giuli, K. Lai, and M. Baker,
Mitigating Routing Misbehavior in Mobile Ad Hoc
Networks, Proc. MobiCom, Aug. 2000.
[8] S. Buchegger and J.-Y. Le Boudec, Performance
Analysis of the CONFIDANT Protocol: Cooperation
of Nodes, Fairness in Dynamic Ad-Hoc
Networks,Proc. MobiHoc, June 2002.
[9] J.-S. Lee, A Petri net design of command filters for
semiautonomous mobile sensor networks, IEEE
Trans. Ind. Electron., vol. 55, no. 4, pp. 18351841,
Apr. 2008.
[10] J. Parker, J. Undercoffer, J . Pinkston, and A. Joshi,
On intrusion detection and response for mobile ad
hoc networks, in Proc. IEEE Int. Conf. Perform.,
Comput., Commun., 2004, pp. 747752.
[11] A. Patcha and A. Mishra, Collaborative security
architecture for black hole attack prevention in
mobile ad hoc networks, in Proc. Radio Wireless
Conf., 2003, pp. 7578.
[12] T. Sheltami, A. Al-Roubaiey, E. Shakshuki, and A.
Mahmoud, Video transmission enhancement in
presence ofmisbehaving nodes inMANETs, Int. J.
Multimedia Syst., vol. 15, no. 5, pp. 273282, Oct.
2009.
[13] Charlie Obimbo#1, Liliana Maria Arboleda-Cobo*2
An Intrusion Detection System for MANET
Communications in Information Science and
Management Engineering(CISME) Vol.2 No.3 2012
PP.1-5 www.jcisme.org 2011-2012 World Academic
Publishing.
[14] Sergio Marti, T. J. Giuli, Kevin Lai, and Mary Baker.
Mitigating routing misbehavior in mobile ad hoc
networks. In Mo- biCom '00: Proceedings of the 6th
annual international conference on Mobile
computing and networking, pages 255_265, New
York, NY, USA, 2000. ACM.
[15] Elhadi M. Shakshuki, Senior Member, IEEE, Nan
Kang, and Tarek R. Sheltami, Member, IEEE,
EAACKA Secure Intrusion-Detection System for
MANETs IEEE TRANSACTIONS ON
INDUSTRIAL ELECTRONICS, VOL. 60, NO. 3,
MARCH 2013
[16] Hasswa, A., Zulkernine, M., and Hassanein, H.
Routeguard: an intrusion detection and response
system for mobile ad hoc networks. In Wireless And
Mobile Computing, Networking And
Communications, 2005. (WiMob'2005), volume 3,
pages 336_343. IEEE, August 2005.
[17] K. Liu, J. Deng, P. K. Varshney, and K.
Balakrishnan, An acknowledgment-based approach
for the detection of routing misbehavior in
MANETs, IEEE Trans. Mobile Comput., vol. 6, no.
5, pp. 536550, May 2007.
[18] L. Zhou and Z.J. Haas, Securing Ad Hoc
Networks, IEEE Network Magazine, vol. 13, no. 6,
Nov./Dec. 1999.
[19] K. Balakrishnan, J. Deng, and P.K. Varshney,
TWOACK: Preventing Selfishness in Mobile Ad
Hoc Networks, Proc. IEEE Wireless Comm. and
Networking Conf. (WCNC 05), Mar. 2005.
[20] R. Rivest, A. Shamir, and L. Adleman, A method
for obtaining digital signatures and public-key
cryptosystems, Commun. ACM, vol. 21, no. 2, pp.
120126, Feb. 1983.
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- An Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewDokument9 SeitenAn Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- THE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSDokument7 SeitenTHE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Customer Satisfaction A Pillar of Total Quality ManagementDokument9 SeitenCustomer Satisfaction A Pillar of Total Quality ManagementInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Experimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterDokument7 SeitenExperimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Study of Customer Experience and Uses of Uber Cab Services in MumbaiDokument12 SeitenStudy of Customer Experience and Uses of Uber Cab Services in MumbaiInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Detection of Malicious Web Contents Using Machine and Deep Learning ApproachesDokument6 SeitenDetection of Malicious Web Contents Using Machine and Deep Learning ApproachesInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Analysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyDokument6 SeitenAnalysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- THE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSDokument7 SeitenTHE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Analysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyDokument6 SeitenAnalysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- Study of Customer Experience and Uses of Uber Cab Services in MumbaiDokument12 SeitenStudy of Customer Experience and Uses of Uber Cab Services in MumbaiInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Customer Satisfaction A Pillar of Total Quality ManagementDokument9 SeitenCustomer Satisfaction A Pillar of Total Quality ManagementInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Synthetic Datasets For Myocardial Infarction Based On Actual DatasetsDokument9 SeitenSynthetic Datasets For Myocardial Infarction Based On Actual DatasetsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Detection of Malicious Web Contents Using Machine and Deep Learning ApproachesDokument6 SeitenDetection of Malicious Web Contents Using Machine and Deep Learning ApproachesInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Experimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterDokument7 SeitenExperimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Staycation As A Marketing Tool For Survival Post Covid-19 in Five Star Hotels in Pune CityDokument10 SeitenStaycation As A Marketing Tool For Survival Post Covid-19 in Five Star Hotels in Pune CityInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The Mexican Innovation System: A System's Dynamics PerspectiveDokument12 SeitenThe Mexican Innovation System: A System's Dynamics PerspectiveInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- Soil Stabilization of Road by Using Spent WashDokument7 SeitenSoil Stabilization of Road by Using Spent WashInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Impact of Effective Communication To Enhance Management SkillsDokument6 SeitenThe Impact of Effective Communication To Enhance Management SkillsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Digital Record For Privacy and Security in Internet of ThingsDokument10 SeitenA Digital Record For Privacy and Security in Internet of ThingsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Design and Detection of Fruits and Vegetable Spoiled Detetction SystemDokument8 SeitenDesign and Detection of Fruits and Vegetable Spoiled Detetction SystemInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Performance of Short Transmission Line Using Mathematical MethodDokument8 SeitenPerformance of Short Transmission Line Using Mathematical MethodInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Challenges Faced by Speciality Restaurants in Pune City To Retain Employees During and Post COVID-19Dokument10 SeitenChallenges Faced by Speciality Restaurants in Pune City To Retain Employees During and Post COVID-19International Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Deep Learning Based Assistant For The Visually ImpairedDokument11 SeitenA Deep Learning Based Assistant For The Visually ImpairedInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- An Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewDokument9 SeitenAn Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- A Comparative Analysis of Two Biggest Upi Paymentapps: Bhim and Google Pay (Tez)Dokument10 SeitenA Comparative Analysis of Two Biggest Upi Paymentapps: Bhim and Google Pay (Tez)International Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Secured Contactless Atm Transaction During Pandemics With Feasible Time Constraint and Pattern For OtpDokument12 SeitenSecured Contactless Atm Transaction During Pandemics With Feasible Time Constraint and Pattern For OtpInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Advanced Load Flow Study and Stability Analysis of A Real Time SystemDokument8 SeitenAdvanced Load Flow Study and Stability Analysis of A Real Time SystemInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Predicting The Effect of Fineparticulate Matter (PM2.5) On Anecosystemincludingclimate, Plants and Human Health Using MachinelearningmethodsDokument10 SeitenPredicting The Effect of Fineparticulate Matter (PM2.5) On Anecosystemincludingclimate, Plants and Human Health Using MachinelearningmethodsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (120)
- Impact of Covid-19 On Employment Opportunities For Fresh Graduates in Hospitality &tourism IndustryDokument8 SeitenImpact of Covid-19 On Employment Opportunities For Fresh Graduates in Hospitality &tourism IndustryInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Anchoring of Inflation Expectations and Monetary Policy Transparency in IndiaDokument9 SeitenAnchoring of Inflation Expectations and Monetary Policy Transparency in IndiaInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- AMS BreakerDokument4 SeitenAMS Breakerkuttu9703Noch keine Bewertungen
- UbnfilelDokument3 SeitenUbnfilelJorge LorenzoNoch keine Bewertungen
- Blender 04Dokument38 SeitenBlender 04Ana Maria100% (1)
- AcaDokument3 SeitenAcasweetunannuNoch keine Bewertungen
- Unit-I Introduction To Erp Enterprise Resource Planning (ERP) Is An Integrated Computer-Based SystemDokument51 SeitenUnit-I Introduction To Erp Enterprise Resource Planning (ERP) Is An Integrated Computer-Based Systemchandru5g100% (4)
- Predictive Analytics in Warranty ClaimsDokument6 SeitenPredictive Analytics in Warranty ClaimsRaj SharmaNoch keine Bewertungen
- Concrete Pumping Cop 2005 PDFDokument27 SeitenConcrete Pumping Cop 2005 PDFShoaib HassanNoch keine Bewertungen
- Tkinter GUI Programming by ExampleDokument374 SeitenTkinter GUI Programming by ExampleArphan Desoja100% (5)
- Installation & Stock Detail of Ignition Modules & Magnetos of Gas Compressor Units (All Fields)Dokument4 SeitenInstallation & Stock Detail of Ignition Modules & Magnetos of Gas Compressor Units (All Fields)Atiq_2909Noch keine Bewertungen
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Ebara Pump Brochure DML-DMLFDokument15 SeitenEbara Pump Brochure DML-DMLFkutecoolNoch keine Bewertungen
- Est-Pergola Octogonal 21-03-2022Dokument1 SeiteEst-Pergola Octogonal 21-03-2022Victor MuñozNoch keine Bewertungen
- Lec 2 - Tall Building Criteria and Loading-2003Dokument30 SeitenLec 2 - Tall Building Criteria and Loading-2003JibonGhoshPritomNoch keine Bewertungen
- C ElanchezhianDokument8 SeitenC ElanchezhiankeshavuvceNoch keine Bewertungen
- Evaporator Design CalculationDokument58 SeitenEvaporator Design CalculationManoj BNoch keine Bewertungen
- KN3906Dokument3 SeitenKN3906ingucvNoch keine Bewertungen
- 16HE018 Graphite Heat Exchanger DCBH Project Sr. No. Particulars Units Our Requirement Process Side Utility SideDokument2 Seiten16HE018 Graphite Heat Exchanger DCBH Project Sr. No. Particulars Units Our Requirement Process Side Utility SideBhaumik BhuvaNoch keine Bewertungen
- DIS2116 ManualDokument88 SeitenDIS2116 ManualHưng Tự Động HoáNoch keine Bewertungen
- Wireless NetworkingDokument200 SeitenWireless NetworkingVamsikrishna PanugantiNoch keine Bewertungen
- Manual Safety Relays 3SK2 en-USDokument352 SeitenManual Safety Relays 3SK2 en-USKarina Ospina100% (3)
- SAS Hot Fix Analysis Download and Deployment ToolDokument11 SeitenSAS Hot Fix Analysis Download and Deployment ToolAdrian GallegosNoch keine Bewertungen
- Etic HackDokument31 SeitenEtic HackJOrdi CrespoNoch keine Bewertungen
- Thinker Thought Sara HendrenDokument1 SeiteThinker Thought Sara HendrenNathaniel RiversNoch keine Bewertungen
- Barrett Light 50Dokument23 SeitenBarrett Light 50Zayd Iskandar Dzolkarnain Al-HadramiNoch keine Bewertungen
- Texture Formats Used by CFS3Dokument2 SeitenTexture Formats Used by CFS3Hillmen HussinNoch keine Bewertungen
- Swiss FCM Ordinance - EuPIA QDokument6 SeitenSwiss FCM Ordinance - EuPIA Qiz_nazNoch keine Bewertungen
- FSP 851Dokument3 SeitenFSP 851RICHINoch keine Bewertungen
- Vatufeku Longman Writing Academic English Xufex PDFDokument4 SeitenVatufeku Longman Writing Academic English Xufex PDFNZAR AREFNoch keine Bewertungen
- Duty Engineer: Grand Mercure & Ibis Yogyakarta Adi SuciptoDokument1 SeiteDuty Engineer: Grand Mercure & Ibis Yogyakarta Adi Suciptoali maulana yuthiaNoch keine Bewertungen
- A01 04 Assessmentk UndercarriageDokument7 SeitenA01 04 Assessmentk UndercarriageMARIO DEL PINO MUÑOZNoch keine Bewertungen
- 1169a AopDokument12 Seiten1169a AopBAYARD BernardNoch keine Bewertungen
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNVon EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNBewertung: 5 von 5 Sternen5/5 (1)
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsVon EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsBewertung: 5 von 5 Sternen5/5 (1)
- Hacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.Von EverandHacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.Bewertung: 5 von 5 Sternen5/5 (2)
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsVon EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsNoch keine Bewertungen
- Unlock Any Roku Device: Watch Shows, TV, & Download AppsVon EverandUnlock Any Roku Device: Watch Shows, TV, & Download AppsNoch keine Bewertungen