Beruflich Dokumente
Kultur Dokumente
Decompiler - Reversing Compilation
Hochgeladen von
api-3728136Originalbeschreibung:
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Decompiler - Reversing Compilation
Hochgeladen von
api-3728136Copyright:
Verfügbare Formate
Decompiler:
Reversing Compilation
Written By,
Tushar B Kute,
Lecturer in Information Technology
(K. K. Wagh Polytechnic, Nashik – 3, Maharashtra, INDIA)
Email – tbkute@gmail.com
Decompiler: Reversing Compilation -1-
Protection from Decompilers
As every coin has two sides, Decompiler also can be used positively or
negatively. License agreements don’t offer any real protection from a programmer
that wants to decompile your code. So to avoid misuse of this concept, we need the
ways to avoid misuse of Decompiler. That is, need of protection if decompiler is
misused.
Use of Obfuscator:
An obfuscator acts like a filter, removing any useful information such as
variable names and line attributes and only allowing the bare minimum of information
to pass through. Essentially the obfuscator parses the constant pool to find and then
rename all variable names and parameters. It is only been marginally effective, it
allows the class-file to run as normal and it prevents the decompiled code from being
recompiled. However that is not the end of the story. True, it is more difficult to
understand and recompile and once a class-file has been through an obfuscator we
can never recover the original variable names, but we could have accomplished
some of that by compiling.
Using some Obfuscator as many methods as possible are renamed a using
overloading where ever possible. Overloaded methods have the same name but
have different numbers of parameters. True, the overloaded methods are difficult to
understand but they are not impossible to comprehend. They too can be renamed
into something easier to read.
Some obfuscators have a far more aggressive form of obfuscation known as
high mode obfuscation. For example, Zelix Klassmaster encrypts all strings in a
class-file and Neil Aggarwal’s Obfuscate adds extra invalid entries to the symbolic
table rather like a bytecode manipulator. Unfortunately while they do succeed in
mangling the symbolic names beyond all recognition, some decompilers such as
SourceAgain can substitute new strings automatically.
Selling source code with application by charging extra
Some companies are finding that if source code is so readily accessible then
why not just sell it at a higher price. JClass is available from the KL Group as both
class file and source code. The difference in price is so small that it just doesn’t
make any sense to decompile, given the time and energy that is sometimes required.
We’ve already talked about the possibility of giving away our code at a higher price.
If the price is not too high we could convince the decompiler to pay for the code as
programmer’s comments are usually very informative. This won’t be for everyone but
why not make some money on the fact that some people will decompile our code to
copy it, so why not try to gain some revenue on these otherwise illegal activities.
License agreement
License agreements don’t offer any real protection from a programmer that
wants to decompile our code.
Code Fingerprinting
Decompiler: Reversing Compilation - 14 -
In a court of law, one of the best ways of proving that an application or applet
was decompiled and recompiled is to show spurious code which has no function and
yet is in the original as well as the decompiled code.
However most decompilers will be able to spot spurious code put in there for
fingerprinting and it too will be ultimately useless, like stretching a watermarked
image to remove the watermark. Both JAD and SourceAgain can already search out
unexecuted code and remove it from the decompiled code.
IPR Protection Schemes
IPR protection schemes are one of the areas where real strides are likely to
be made in class-file protection. The logic behind IPR protection schemes with
respect to Java is that if we can’t get at the class-file then we cannot possibly
decompile it and to do that we need a secure browser cache.
Already secure browsers that don’t dump class-files, HTML or images to the
Internet Explorer or Netscape Navigator cache are on the market. Breaker
Technologies have a secure browser and IBM’s CryptoLive claims to have one and
no doubt there are others. For the moment this technology is in it’s infancy but
expect it to grow.
Intellectual Property Rights (IPR) protection schemes such as IBM’s
Cryptolope Live or InterTrust’s DigiBox and Breaker Technologies’ SoftSEAL are
normally used to sell HTML documents or audio files on some pay-per-view basis or
pay-per-group scheme. However as they typically have built in trusted HTML viewers
they allow Java applets to be seen but not copied. Unfortunately IPR protection
schemes are not cheap. Worse still some of the clients are written in 100% pure
Java and can therefore be decompiled. Similar protection schemes in the future are
likely to provide the best chance of success in nailing the decompiler issue once and
for all.
Executables applications
The safest protection for Java applications is to compile them into
executables. This is an option on many Java compilers, for example SuperCede.
Your code will now be as safe as any C or C++ executables – read a lot safer – but
are no longer portable as they no longer use the JVM.
Keeping code on server side
The safest protection for applets is to hide all the interesting code on the web
server and only use the applet as a thin front end GUI. However this increases web
server load and goes against the Java methodology.
Decompiler developer’s develops obfuscator
Crema is the original obfuscator and was a complementary program to the
above mentioned Mocha. Of course we know Mocha was given away free but Crema
cost somewhere around $30 and to safeguard against Mocha we had to buy Crema.
It performs some rudimentary obfuscation as we’ll see later and it also has one
interesting side effect. It flags class files so that Mocha refuses to decompile any
applets or applications that had been previously run through Crema. However other
decompiler soon came onto the market which was not so Crema friendly. Now we
Decompiler: Reversing Compilation - 15 -
find obfuscators and decompilers are in what we could describe as a cold war
scenario without any entente cordiale. So far the decompilers are winning but that’s
not to say the climate won’t change.
Best Defense
It is said that perhaps the best defense is to provide a stable, useful
application with all the usual phone support and good documentation. The majority of
our customers will much prefer a supported application than an illegal copy that they
will have to support themselves. So before we start worrying too much about
decompilation, remember that people need someone to shout at when things go
wrong.
Drawbacks
• Functionality not user Friendly: Using Decompiler’s i.e. getting full use of
Functionality of Decompiler is not much user friendly, some times due to need
of technical background, lack of GUI.
• Presence of Larger Size of Source Code: It is harder to get source code back
from larger size of decompiled data. For e.g. Decompiling Office 97 using dcc
(A Decompiler) would create so much code that it is about as user friendly as
debug or a hexadecimal dump. Most modern commercial software’s source
code is so large that it becomes unintelligible without the design documents
and lots of source code comments. Let’s face it; many people’s C++ is hard
enough to read six months after they wrote it. So how easy would it be for
someone else to decipher C code that came from compiled C++ code without
any help even if the library calls aren’t traversed?
• No GUI for older ones: As older Decompiler’s where mainly used by
developers hence the lack GUI which is common for many softwares, hence
due to lack of GUI handling Decompiler becomes harder.
• Compiler Dependent: As Design of Decompiler depends on compiler for which
it is been developed. Hence change in compiler causes to write updated
Decompiler.
• Increasing Trend towards Stealing code: Habits of using Decompiler are
increasing trends towards stealing code other than for educational purpose.
• Giving Trusted Secrets to Competitors, Hackers: Using Decompiler the
competitors, hackers can get inside the product and can acquire Trusted
Secrets, which else was hard to known.
• Security holes Exposed: The security holes can be made public using
Decompilers in software developed.
Conclusion
• The future of decompilation and obfuscation techniques looks like being fairly
reminiscent of the Cold War. An arms race is brewing between the decompiler
developers and the obfuscator developers. Oddly enough these are often the
same companies trying to break a rival’s product and then sell there own
obfuscator as the only 100% secure solution.
• The Attitude towards Decompiler’s is needed to be changed, as there are
many positive uses of this concept, so more attention is needed to be given to
this concept.
Decompiler: Reversing Compilation - 16 -
• More research is required in executable to assembly code decompilation.
References
• Thesis paper by Cristina Confluents On “Decompiler Techniques”.
• http://www.riis.com/book
• http://www.debugmode.com/index.htm
• http://www.program-transformation.org
• http://www.itee.uq.edu.au/~csmweb/decompilation/
• http://www.decompiler.com/
• http://en.wikipedia.org/
• http://research.sun.com/research/people/cristina/index.html
• Google Groups at http://www.google.com/
• E-book On Building decompilers http://www.riis.com/book
• “C Column Collection” by Yeshwant Kanetkar
----------------
Decompiler: Reversing Compilation - 17 -
Das könnte Ihnen auch gefallen
- Software Defined Radio: The Software Communications ArchitectureVon EverandSoftware Defined Radio: The Software Communications ArchitectureNoch keine Bewertungen
- Reversing of A Protection Scheme Based On Drivers v11 by Shub-NigurrathDokument38 SeitenReversing of A Protection Scheme Based On Drivers v11 by Shub-NigurrathpepeNoch keine Bewertungen
- Foundation Course for Advanced Computer StudiesVon EverandFoundation Course for Advanced Computer StudiesNoch keine Bewertungen
- Y%!&' (Y) ' Y!" + Y,-, Y .Y%.) Ô.YDokument5 SeitenY%!&' (Y) ' Y!" + Y,-, Y .Y%.) Ô.YJoelton GomesNoch keine Bewertungen
- 11.3 Session Hijacking ToolsDokument20 Seiten11.3 Session Hijacking ToolsChristopher Agbagba100% (1)
- Ida Pro TutorialDokument18 SeitenIda Pro Tutorialapi-302590568Noch keine Bewertungen
- Olly DBG 2 HelpDokument77 SeitenOlly DBG 2 HelpSrinivasXesNoch keine Bewertungen
- Assembly For CrackersDokument4 SeitenAssembly For CrackersImran Khan100% (1)
- Chip8: A CHIP-8 / SCHIP Emulator by David Winter (Hpmaniac)Dokument14 SeitenChip8: A CHIP-8 / SCHIP Emulator by David Winter (Hpmaniac)Guy100% (1)
- Home Automation Using Telegram BOT (Id 36)Dokument8 SeitenHome Automation Using Telegram BOT (Id 36)chakravarthyNoch keine Bewertungen
- Photoshop CS6 AppleScript RefDokument271 SeitenPhotoshop CS6 AppleScript Reffireproof23Noch keine Bewertungen
- CDMA - Flexent Autoplex ECP Release 17 - 0 PDFDokument626 SeitenCDMA - Flexent Autoplex ECP Release 17 - 0 PDFrnesi100% (1)
- FxgeditorDokument11 SeitenFxgeditorroder76Noch keine Bewertungen
- DEFCON 21 Grand JTAGulator PDFDokument62 SeitenDEFCON 21 Grand JTAGulator PDFhisohisoNoch keine Bewertungen
- Hacking With WebSocketsDokument43 SeitenHacking With WebSocketsSony LazarusNoch keine Bewertungen
- Ethical Hacking Track: Certified Ethical Hacker: Programme OverviewDokument6 SeitenEthical Hacking Track: Certified Ethical Hacker: Programme OverviewTamirat WorkuNoch keine Bewertungen
- Frequently Asked Questions (And Answers) About Reverse EngineeringDokument15 SeitenFrequently Asked Questions (And Answers) About Reverse EngineeringAnonymous i3HHYO8Noch keine Bewertungen
- Sqlmap CASE STUDYDokument19 SeitenSqlmap CASE STUDYKumoulica KumoulicaNoch keine Bewertungen
- A Theory of Automated Market Makers in DeFiDokument34 SeitenA Theory of Automated Market Makers in DeFiBranden KeckNoch keine Bewertungen
- Johnny V. Perrez Bsit 1 - 3: Architectural Components 64-Bit Windows 32-Bit WindowsDokument1 SeiteJohnny V. Perrez Bsit 1 - 3: Architectural Components 64-Bit Windows 32-Bit Windowskirito gameNoch keine Bewertungen
- Reverse Engineering Cheat SheetDokument3 SeitenReverse Engineering Cheat SheetTorve TrogNoch keine Bewertungen
- Understanding Linear Feedback Shift Registers - The Easy WayDokument3 SeitenUnderstanding Linear Feedback Shift Registers - The Easy WayrockymaxdeemannNoch keine Bewertungen
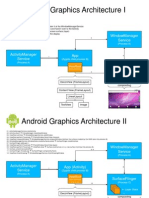
- Android Graphics ArchitectureDokument19 SeitenAndroid Graphics Architectureavinashjha99Noch keine Bewertungen
- Parallela Cluster by Michael Johan KrugerDokument56 SeitenParallela Cluster by Michael Johan KrugerGiacomo Marco ToigoNoch keine Bewertungen
- Netx Insiders GuideDokument261 SeitenNetx Insiders GuideMapuka MuellerNoch keine Bewertungen
- Tor Masternode Setup GuideDokument17 SeitenTor Masternode Setup GuideWilliam EC0% (1)
- Lecture 2.4.2 - SolidityDokument14 SeitenLecture 2.4.2 - SolidityShiv RogersNoch keine Bewertungen
- Praktikum Ethical HackingDokument144 SeitenPraktikum Ethical HackingKido KaindeNoch keine Bewertungen
- Important Github Repositories For Security: Created TagsDokument5 SeitenImportant Github Repositories For Security: Created TagsTechnical SupportNoch keine Bewertungen
- SIM800 Series at Command Manual V1.07Dokument370 SeitenSIM800 Series at Command Manual V1.07henry2109Noch keine Bewertungen
- Practical SS7, Part 3Dokument7 SeitenPractical SS7, Part 3MITHUNLALUSNoch keine Bewertungen
- Secure Data Exchange Via HSMDokument3 SeitenSecure Data Exchange Via HSMLayer7TechNoch keine Bewertungen
- Qt6book With FrontpageDokument728 SeitenQt6book With FrontpagesatyakambaruahNoch keine Bewertungen
- Design of Digitalised Vending Machine Using VerilogDokument24 SeitenDesign of Digitalised Vending Machine Using VerilogRohan SNoch keine Bewertungen
- Create A Dangerous Virus Using NotepadDokument6 SeitenCreate A Dangerous Virus Using NotepadHafiz FadzilNoch keine Bewertungen
- Student Coin: Ethereum - Waves Bridge ManualDokument8 SeitenStudent Coin: Ethereum - Waves Bridge ManualALK Student CoinNoch keine Bewertungen
- Cyber Security Project: Password CrackingDokument42 SeitenCyber Security Project: Password CrackingDiksha PanditNoch keine Bewertungen
- Chat GPT2Dokument1 SeiteChat GPT2mklitabeNoch keine Bewertungen
- Static Keyword in JavaDokument3 SeitenStatic Keyword in JavaCHANDRA BHUSHANNoch keine Bewertungen
- System Verilog IntroductionDokument20 SeitenSystem Verilog IntroductionRamakrishnaRao SoogooriNoch keine Bewertungen
- Olly ScriptDokument5 SeitenOlly Scriptj_humbsNoch keine Bewertungen
- Writing Simple Automation Scripts With PythonDokument3 SeitenWriting Simple Automation Scripts With Pythonnaveen_nageshNoch keine Bewertungen
- Smart CardsDokument19 SeitenSmart CardsRakesh BelakudNoch keine Bewertungen
- Dizzying But Invisible Depth: Jean-Baptiste QueruDokument40 SeitenDizzying But Invisible Depth: Jean-Baptiste QueruevandrixNoch keine Bewertungen
- The openCV Installed With The Jetpack Does Not Have CUDA Supported PDFDokument11 SeitenThe openCV Installed With The Jetpack Does Not Have CUDA Supported PDFseul aloneNoch keine Bewertungen
- SR-201 Network Relay Quick Start GuideDokument7 SeitenSR-201 Network Relay Quick Start GuideiakapoNoch keine Bewertungen
- How To Write A Smart-Contract For Your ICO - An Ultimate Guide - The Ultimate Crypto How-To GuidesDokument12 SeitenHow To Write A Smart-Contract For Your ICO - An Ultimate Guide - The Ultimate Crypto How-To Guidesasset68Noch keine Bewertungen
- Software Cracking and PatchingDokument19 SeitenSoftware Cracking and Patchingjigsaw55555100% (2)
- CCB DeveloperDokument7 SeitenCCB DeveloperHaneef Ali SadiqNoch keine Bewertungen
- Aelf Blockchain Development Process: 1) Development Environment Preparation & Contract WritingDokument5 SeitenAelf Blockchain Development Process: 1) Development Environment Preparation & Contract WritingEdwin OngNoch keine Bewertungen
- Using Open Source Tools For AT91SAM7S Cross Development Revision C PDFDokument198 SeitenUsing Open Source Tools For AT91SAM7S Cross Development Revision C PDFducchinh1001Noch keine Bewertungen
- Lab Wireshark Packet Capture Assignment TutorialDokument8 SeitenLab Wireshark Packet Capture Assignment TutorialHaseeb RazaNoch keine Bewertungen
- BlackHat Europe 09 Damele A G Advanced SQL Injection WhitepaperDokument37 SeitenBlackHat Europe 09 Damele A G Advanced SQL Injection WhitepaperPradeep ChauhanNoch keine Bewertungen
- Test Design Specifications: Automated Teller Machine System (ATMS) Independent Verification and ValidationDokument17 SeitenTest Design Specifications: Automated Teller Machine System (ATMS) Independent Verification and ValidationEmmaNoch keine Bewertungen
- Android Material DocumentDokument203 SeitenAndroid Material DocumentParitala RamcNoch keine Bewertungen
- Analysis of AlgorithmDokument43 SeitenAnalysis of AlgorithmAzeemNoch keine Bewertungen
- LoicDokument4 SeitenLoicRa-v ChaxNoch keine Bewertungen
- Step by Step Backtrack 5Dokument29 SeitenStep by Step Backtrack 5X Hai HoangNoch keine Bewertungen
- p64 - 0x06 - Attacking The Core - Kernel Exploitation Notes - by - Twiz & SgrakkyuDokument94 Seitenp64 - 0x06 - Attacking The Core - Kernel Exploitation Notes - by - Twiz & SgrakkyuabuadzkasalafyNoch keine Bewertungen
- BeEF - DeepSec - AttackDokument36 SeitenBeEF - DeepSec - AttackAaaaaaaNoch keine Bewertungen
- Management Information SystemDokument11 SeitenManagement Information Systemapi-3728136Noch keine Bewertungen
- Question Bank CPR Practical No.5Dokument1 SeiteQuestion Bank CPR Practical No.5api-3728136Noch keine Bewertungen
- Question Bank CPR Practical No.2Dokument1 SeiteQuestion Bank CPR Practical No.2api-3728136Noch keine Bewertungen
- Question Bank CPR Practical No.7Dokument1 SeiteQuestion Bank CPR Practical No.7api-3728136Noch keine Bewertungen
- Unicode - Language of UniverseDokument15 SeitenUnicode - Language of Universeapi-3728136Noch keine Bewertungen
- Question Bank: Programming in C' (9017) Class: FYIF Chapter No. 05 PointersDokument2 SeitenQuestion Bank: Programming in C' (9017) Class: FYIF Chapter No. 05 Pointersapi-3728136Noch keine Bewertungen
- Question Bank CPR Practical No.2Dokument1 SeiteQuestion Bank CPR Practical No.2api-3728136Noch keine Bewertungen
- Question Bank CPR Practical No.2Dokument1 SeiteQuestion Bank CPR Practical No.2api-3728136Noch keine Bewertungen
- Question Bank CPR Practical No.2Dokument1 SeiteQuestion Bank CPR Practical No.2api-3728136Noch keine Bewertungen
- Question Bank CPR Practical No.2Dokument1 SeiteQuestion Bank CPR Practical No.2api-3728136Noch keine Bewertungen
- Program 2.23 Calling Sequence of ConstructorsDokument4 SeitenProgram 2.23 Calling Sequence of Constructorsapi-3728136Noch keine Bewertungen
- CPR Notes - Chapter 01 Basics of CDokument20 SeitenCPR Notes - Chapter 01 Basics of Capi-3728136Noch keine Bewertungen
- CPR - QB Chapter 02 NewDokument2 SeitenCPR - QB Chapter 02 Newapi-3728136Noch keine Bewertungen
- CPR - QB Chapter 04 NewDokument2 SeitenCPR - QB Chapter 04 Newapi-3728136Noch keine Bewertungen
- CPR MSBTE - Summer 2008Dokument3 SeitenCPR MSBTE - Summer 2008api-3728136Noch keine Bewertungen
- CPR MSBTE - Winter 2008Dokument2 SeitenCPR MSBTE - Winter 2008api-3728136Noch keine Bewertungen
- CPR - QB Chapter 03 NewDokument1 SeiteCPR - QB Chapter 03 Newapi-3728136Noch keine Bewertungen
- CPR - QB Chapter 01 NewDokument2 SeitenCPR - QB Chapter 01 Newapi-3728136Noch keine Bewertungen
- Program 2.16 Defining A Class Inside A MethodDokument5 SeitenProgram 2.16 Defining A Class Inside A Methodapi-3728136Noch keine Bewertungen
- ProjectsDokument2 SeitenProjectsapi-3728136Noch keine Bewertungen
- CPR Notes - Chapter 02 Decision Making and BranchingDokument24 SeitenCPR Notes - Chapter 02 Decision Making and Branchingapi-37281360% (1)
- JPR 01Dokument4 SeitenJPR 01api-3728136Noch keine Bewertungen
- Sessional Test-I Core Java 2007-2008Dokument1 SeiteSessional Test-I Core Java 2007-2008api-3728136Noch keine Bewertungen
- Sessional Test-II JPR 2007-2008Dokument1 SeiteSessional Test-II JPR 2007-2008api-3728136Noch keine Bewertungen
- Sample Class Test IDokument1 SeiteSample Class Test Iapi-3728136Noch keine Bewertungen
- Sessional Test-I JPR 2007-2008Dokument1 SeiteSessional Test-I JPR 2007-2008api-3728136Noch keine Bewertungen
- JPR Sample Question Paper - 1Dokument2 SeitenJPR Sample Question Paper - 1api-3728136Noch keine Bewertungen
- Sessional Test-II JPR 2006-2007Dokument1 SeiteSessional Test-II JPR 2006-2007api-3728136Noch keine Bewertungen
- Java Programming Sample Paper 5th Semester MSBTE DiplomaDokument2 SeitenJava Programming Sample Paper 5th Semester MSBTE DiplomaSanjay Dudani100% (7)
- 20 Marks Sample Test PaperDokument2 Seiten20 Marks Sample Test PaperSagar KachareNoch keine Bewertungen
- Gigabyte z97pd3 ManualDokument40 SeitenGigabyte z97pd3 ManualRiccardoFlaskNoch keine Bewertungen
- Improving Data Generation Process For A Printer of Holographic StereogramsDokument28 SeitenImproving Data Generation Process For A Printer of Holographic StereogramsLeandro BertoluzziNoch keine Bewertungen
- SPRB 176 AdDokument27 SeitenSPRB 176 AdMADDYNoch keine Bewertungen
- EJ Unit 4Dokument39 SeitenEJ Unit 4Yexo KajNoch keine Bewertungen
- Module-1: Chapter-1 Parallel Computer ModelsDokument42 SeitenModule-1: Chapter-1 Parallel Computer ModelsprajNoch keine Bewertungen
- SP Ait LMDokument19 SeitenSP Ait LMNemishNoch keine Bewertungen
- ECE270: Embedded Logic Design Mid-Semester Exam (15 Marks) : Date: 16/10/2020 Deadline: 11 AM (Read It As 10.45 Am)Dokument2 SeitenECE270: Embedded Logic Design Mid-Semester Exam (15 Marks) : Date: 16/10/2020 Deadline: 11 AM (Read It As 10.45 Am)Ankit GargNoch keine Bewertungen
- Multitasking With Raspberry Pi by Dogan IbrahimDokument232 SeitenMultitasking With Raspberry Pi by Dogan IbrahimrvpilotNoch keine Bewertungen
- CS Project 5Dokument38 SeitenCS Project 5AbhiNoch keine Bewertungen
- DDCA Ch6Dokument129 SeitenDDCA Ch6Dheer MehrotraNoch keine Bewertungen
- How To Convert Relational Data To XML - MelbourneDokument56 SeitenHow To Convert Relational Data To XML - Melbournesp40694Noch keine Bewertungen
- HP IP Console Viewer User GuideDokument339 SeitenHP IP Console Viewer User GuideGeorgSchreiberNoch keine Bewertungen
- The Art and Science of Detecting Cobalt Strike: by Nick MavisDokument29 SeitenThe Art and Science of Detecting Cobalt Strike: by Nick MavisCoibaNoch keine Bewertungen
- 8086 MicroprocessorDokument21 Seiten8086 MicroprocessorPinki KumariNoch keine Bewertungen
- Booting and Shutting Down Oracle Solaris 11.4 SystemsDokument88 SeitenBooting and Shutting Down Oracle Solaris 11.4 Systemserrr33Noch keine Bewertungen
- Tugas KeysDokument3 SeitenTugas KeysIVa LatifahNoch keine Bewertungen
- GSM Communicator For Fire Alarm Control Panels G17F: Installation ManualDokument33 SeitenGSM Communicator For Fire Alarm Control Panels G17F: Installation Manualosmani moncadaNoch keine Bewertungen
- Linux Practicals Final Updated 14-10-2011Dokument227 SeitenLinux Practicals Final Updated 14-10-2011ymr606Noch keine Bewertungen
- Data Flow Diagram of ARM: 1 39v10 The ARM ArchitectureDokument7 SeitenData Flow Diagram of ARM: 1 39v10 The ARM ArchitectureMohnishNoch keine Bewertungen
- Hardware: Computer Hardware Is A Collective Term Used To Describe Any of The Physical Components of AnDokument4 SeitenHardware: Computer Hardware Is A Collective Term Used To Describe Any of The Physical Components of AnkalNoch keine Bewertungen
- Gameloft Job Application FormDokument2 SeitenGameloft Job Application FormdvkieuNoch keine Bewertungen
- Eem 15 MT BookDokument420 SeitenEem 15 MT BookVellore Dinesh KumarNoch keine Bewertungen
- 6ES75152AN030AB0 Datasheet enDokument8 Seiten6ES75152AN030AB0 Datasheet enkalpana kadamNoch keine Bewertungen
- Ds NV Quadro k620 Jul24 Us Pny R LRDokument1 SeiteDs NV Quadro k620 Jul24 Us Pny R LRrafa260560Noch keine Bewertungen
- Text FileDokument104 SeitenText FileVictor TanasescuNoch keine Bewertungen
- LAN Switching & Wireless Networks: Suez Canal University - Faculty of Computers & Informatics - Cisco Local AcademyDokument29 SeitenLAN Switching & Wireless Networks: Suez Canal University - Faculty of Computers & Informatics - Cisco Local AcademyAbdullah AmmarNoch keine Bewertungen
- 小 SLK-TS100 LEAFLET (ENG)Dokument2 Seiten小 SLK-TS100 LEAFLET (ENG)Alan Perez EspinozaNoch keine Bewertungen
- Request Letter For ComputerDokument3 SeitenRequest Letter For ComputerLiza Marie NeryNoch keine Bewertungen
- E800 - High-Performance RTK Receiver - Esurvey GNSSDokument1 SeiteE800 - High-Performance RTK Receiver - Esurvey GNSSKray TharaNoch keine Bewertungen