Beruflich Dokumente
Kultur Dokumente
2600 Hacker Quarterly Volume 16 Number 4 Winter 1999-2000
Hochgeladen von
Kasi XswlCopyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
2600 Hacker Quarterly Volume 16 Number 4 Winter 1999-2000
Hochgeladen von
Kasi XswlCopyright:
Verfügbare Formate
I
"Hac(ng can ge you in a who(e (0+
ore +rout(e than you +hink and if a
cop(ee(y creepy +hing +0 do." - l
we
t
page aied a+ kidf +0 difcourage
hacking
Editor-In-Chief
Emmanuel Goldstein
lavoUI and Design
shapeSHIFTER
Cover Desin
snc. The Chopping lock Inc.
Ofice Manager
Tamprut
Wrilers:Bernie S .. Billst. Blue Whale.
Noam Chomski. Eric Corlev. Dr. Delam.
Derneval. Nathan Dortman. John Drake.
Paul Estev. Mr. French. Thomas Icom.
Joe630. Kingpin. Mm. Kevin Mitnick. The
Prophet. David Ruderman. Seraf. Silent
Switchman. Scott Skinner. Mr. Upsetter
Webmaslers:Kerrv. Macki
Nelwork Ooeralions:CSS.lzaac
Broadcasl Coordinalors: Juintz.
Shihlock. AbsoluteO. silicon. cnote.
Anakin
IRC Admins:autojack. ross
Insoiralional Music: Joe Strummer.
Svd Barrett. real earlv Flovd. Ron Geesin
ShoUI OUIS: Hippies From Hell. etov.
claudus. 112. The Stony Brook Press.
ww.indvmedia.org. Studio X. and
everyone who stood UP in Seallle
RIP: Krvstalia
Good luck: Nahali
2600(SSN 0749-3851) is publshed
quarterly by 2600 Enterprises Inc.
7 Stng's Lane, Setuket, NY 11733.
Second class postage permit paid at
Setauket, New York.
POSTMASTER: Send address
changes to
2600, P.O. Box 752, Middle Island. NY
11953-0752.
Copyright (c) 1999 2600 Enterprises. Inc.
Yearly subscription: U.S. and Canada -
$18 individual, $50 corporate (U.S. funds).
Overseas - $26 individual. $65 corporate.
Back issues available for 1984-1998 at $20
per year. $25 per year overseas.
Individual issues available from 1988 on
at $5 each. S6.25 each overseas.
ADDRESS ALL
SUBSCRIPTION
CORRESPONDENCE TO:
2600 Subscription Dept., P.O. Box 752.
Middle Island. NY 11953-0752
(subs@2600.com).
FOR LETTERS AND ARTICLE
SUBMISSIONS, WRITE TO:
2600 Editorial Dept., P.O. Box 99,
Middle Island, NY 11953-0099
(letters@2600.com,
articles@2600.com).
2600 Ofice Line: 516-751-2600
2600 FAX Line: 516-474-2677
l00h00. h08. l0Ilm8
could have gotten 15
i
lnstall
that's
r
do are
''."
'
.1,1.'
t
,'
D ODWS DSCIDD
OI !D QUIQOSS O DUCd!OD. lH dWdI
!DS QIOCDUI COUD D dDD HdS DD
USD !O CICUHVD! !D SCUI!y O dDy
VDDOWS N HdCDD WDCD !H USI DdS
QDySCd dCCSS !O. l DO DO! CODDOD !D
US O !DS DOIHd!OD OI Qd QUI
QOSS, DOI dH l ISQODSD OI dDy!DDQ
S!UQD dDyOD DOS W!H !DS DOIHd!OD.
N L SUQQOH D LDUX S S! L!d, IdD
DQ dDD COQyDQ IOH !D DIV S Sd,
DU! COQyDQ !O !D DIV S dD d! yOUI
OWD ISK d.
LD O !D HdDy HSCODCQ!ODS
dDOU! VDDOWS NS !Dd! !S d SCUI
OQId!Dg SyS!H dDD !Dd! Dy OIHd!!DQ
d DSK WI!D lL dDD QIOQIy S!!DQ
QIHSSODS, DODODy CdD dCCSS !D D
OIHd!OD OD !Dd! DSK W!DOU! QIHSSOD
!O DO SO.
DI dI !WO QIODHS W!D !DS !D
OIy.lIS!, ! S wrng. LCODD, d ! Idy
UOS S HdK CIdSD ICOVIy HOI D
CU!. l W DSCID d H!DOD OI CICUH
VD!D_ NlL SCUI!y. USDQ d LDUX
DOO! DISK. DS CdD D USU D HdDy
WdyS. lIOH !D SyS!H dDHDS!Id!OIS
VW, !DS S dD XCD! Wdy !O Q! dC
CSS !O HQOI!dD! S OD d SyS!H !Dd!
DdS CIdSDD DOI OIHd!!DQ !D DdID
DIV dDD IDS!dDQ N lIOH !D
DdCKIS VW, ! QVS dCCSS !O !D SyS
!H S. m WOUD DO! DOIHdy DdV dC
CSS !O !D IQS!Iy, USI QIOS, L
llS, !C.
lD OIDI !O dCCOHQSD !DS yOU Wl
DD SOH KDOWDQ O LDUX. |! S QOS
SD !O DO !DS W!D d LLL DOO!dD
OQQy, DU! !D ODy NlL DIVIS dVdl
dD dI IdD ODy dDD !DIOI USSS
!O H. lD dl dIDSS, LDUX DdS !DS VU
DIdD!y dS W.
D IS! !DDQ yOU DD S d COQy O
!Dd!S!VISODOIDUX.DS S d
LDUX HD DS!IDU!OD DSQDD OI D!
WOIK dDHDS!Id!OD dDD ! DdS HdDy US
U d!UIS. |!S DS! d!UI !DOUQD S !S
dD!y !O DOO! IOH d OQQy OD VI!Udly
dD HdCDD WDCD DdS HOI !DdD 8 NL
O PN.
L! !WO DdDK OQQy DSKS, QO !O
WWW.!IDUX.OIQ, dDD OWDOdD !D OlOW
DQ S. DOO!.QZ, CdSSC.QZ, D!S.O, dDD
IdWI!.X. D CUIID! VISOD dS O !DS
WI!DQ S .Z, DOWVI US VISOD .J
dS !DI S DO! DOUQD IOOH OI X!Id
S OD !D .Z DOO! DSK. lOOW !D D
S!IUC!ODS OI UDZQQDQ dDD HdKDQ !D
DOO! DSK dDD !D Dd!d DSK. l yOU CdD!
Q! !DS dI, yOU DdV DO DUSDSS DODQ
S D !D IS! QdC.
VDD !DS S DOD, COQy D!S.O !O !D
DOO! DSK, D! !D NODUS , dDD !D
D D!S !O ! [DO QUO!S), dDD SdV !D
.P! !DS QOD! ! S DS! yOU DOO! !D
DSK d W !HS, IS! !O !S! ! dDD SC
ODD !O Q! dHdI W!D WDd! W DdQQD
dDD DOWIDUX W ISQODD !O COH
HdDDS QVD !. DS Wdy !DI dI DO
SUDISS.
WHtl
NOW !dK !D !WO OQQS !O !D Hd
CDD yOU WdD! !O dCCSS. LOO! !D IS!
DSK.VDD! dSKS yOU DdV d Dd!d DSK,
QU! D !D SCODD DSK dDD !yQ y !DD
D! I!UID. l! W !DD dSK yOU dQdD. yQ
D dDD D! I!UID.
VDD ! S DSDD DOO!DQ, yOU W
DdV d IDUX .J QIOHQ!. yQ DS
HOD D!S.O !DSOdDS !D NLSUQQOI!.
yQ HOUD! -! D!S /DV/DDdJ /HD!
!DS WlHOUD! !DIS!QdI!!ODOD!DIS!
DdIDDIV.DSdSSUHS!DIS!QdI!!OD
OD !D IS! DdID DIV S dD NlL QdI!
!OD. lDO!, !D OOWDQ!dDWQVyOU
dD Dd O DOW !O HOUD! !D QIOQI DIV.
DS dI OI lLL DIVS.
/DV/DDdJ
/DV/DDdZ SCODD QdI!!OH OD !D IS!
DIV
/DV/DDDJ IS! QdI!!OD OD !D SCODD
DdID DIV
/DV/DDDZ SCODD QdI!!OD OD !D SC
ODD DdID DIV
`OU Q! !D Dd. NOW yOU SDOUD
DdVdCCSS!O!DDIV.`OUCdDDOWQU!
d !DID OQQy D !D DIV dDD !yQ HOUD!
! HSDOS /DV/D /OQQy. DS QVS yOU
dCCSS !O !D OQQy SO yOU DdV SOH
QdC !O SdV S !O. P!IDd!y, yOU
dI Idy CVI yOU COUD Q! !D QIOQI
HODUS OI ZQ DIV SUQQOI! WDCD COD
DC!S !O !D L QOI! [SCSO dDD QQd.O),
WDCD WOUD QV yOU HOI XD!y D
COQyDQ S.
l WOUD K !O QV CId!V CID! !O
LN, WDO CDdDQD H !O DD d Wdy !O
dCCSS dD NlL SyS!H IOH d OQQy
DSK.
2000
N
2000
a 10
s,
o
Microsof Networking
Y
C:\net view \Iip addressl
7
o
md sl
*
*SM
*SMSERVER
AM$
C:\net use i: \\Iip address)\[share name)
N
c I:
t
U. s
"d.
b
b
b If;
d
t ru de"),
t
b
"r"
Utte
I
N
Lon
m sb
U
d
NAT (etwork Audit Tool
I wl
a
LphtCrack N
AGENT SM T
Password Crack
A
N i1
d
t b
a h
ay D
N
ac
N
e.)
u
E, p
t d
ing. So before you devise a vile pla t put DOS
6.22 ad dosrboot.exe onto your tet, ad
chage te boot.ini, look aud for backup copies
of s._. It's not ue of to fd a old copy in
some like "C:\winnt\pdc\pair".
A, if you prfer to crack passwords with UNI,
you'll have to convert the hive to a U passwd
file (cut and paste te hashes).
F
Te closest thing a hacker ca do to telnettng in to
a NT machine is connecting via FTP. The prb
lem is tt just because a accout exists on te
machine doesn't mea t it's allowed FTP ac
cess. So get te password hashes, crck them, and
to it tem all.
If te sys tinks he's sma, he'll rname te
Adminisator (root) account. Either way, if you
crack te pasword, you'll have FTP access with
astrative privileges. You ca now defce web
pages, get more passwords for oter computers on
te netwo
r
k, upload tojas, e. Here's a tick:
copy te Event Viewer progrm to a shard direc
tor, then Net View to it. You now have access to
all logs on tat machine.
Elte Tactcs
Okay, let's prend you have access. The prb
lem is, you ca't execute prgs or do anyting
else tt's any f. The answer - a tja. Oet one
t allows you complete filesystem access, allows
for se hots of your tet computer, and lets
you open ad kill active windows (NetBus does all
of ts). But how do you r te toja once you
upload it? You have a few options. Put it in te au
toexec.bat or autoexec.nt file, and force it into r
booting (possibly wit a DoS a ck), or just wait
until someone rboots it. Anoter ploy, if te ma
chine is a web server: upload te toja into a COl
dr (cgi-win, cgi-dos, cgi-shl, e.), ten r
quest te toja wit a browser. If you ste the path
corctly, te web service will spawn (lanch) te
tja for you. Now just connect wit your client,
ad you have complete contl of te computer.
Her's another so. Let's say you wat to hack
teir web page. You have a few passwors, but te
FTP service has been disabled. Well, if te web
pages reside in a shae (unlikely) you ca use MS-
DOS EDIT t edit te defult.ht or index.ht
fle. Otherise, you ca always use HTPto up
load your file. Netscape ad Intet Explorr bot
have clients to upload htl files via HIP - just
use te user names ad paswords you cracked.
Netork snifers ca also be put into place. LOpht
Crack comes wit 5M Packet Cat, a decent
snifer. Seah te net for oter N, Etheret, or To
ken Ring snifers. The point here is t if ter is
even one Wmdows 9.x machine on the netwo
r
k, it
sends cieaext (ASCII) passwors when autenti
cating, so a snifer will always catch tem.
There a also a huge variet of exploits for N.
The tick is weeding tugh te DoS sploits ad
the local ones. One remot exploit,
iishack.eseliishack.asm (www.eeye.com) theoreti
cally will upload ay fle (in your c, a toja)
right thrugh lIS's HTP daemon. lIS ships wit
most NT Seler packes, ad comes wit one of
the ealier seIice packs. Even if the machine in
question isn't a web seler, it prbably has l I S in
stalled. One popula web SeIer for N is WebSite
P, which has a vulnerbilit in its packaged COl
executables. Specifically, uploader.exe allows you
to upload fles to te computer - witout pass
wors.
Now, when I said that you ca't log on to a NT
Seler over the Interet, tt was paially wrg.
The only way to log int an N network is to be a
member of the domain. So you'll have to mae
your computer a member. How? Hack te POC
( Domain Contoller) or a BDC (Backup
Domain Contller). Now, chances a if you've
gott f enough "in" to make yourself a member
of te domain, you prbably have all the permis
sions you could ever wat. If not, lauch te pro
g called User Manager for Domains ad add
yourself wit your IP address.
I Summar
Ain all, N is a very difernt environment t
U or VMS. It also demads ver diferent
skills ad techniques to hack. Doing so is just as r
waing as breaing into a SPARC sttion, ad will
provide you wit all kinds of new ad usefl infor
mation. Tis is, a all, why we do what we do.
9
The most prevalent information on tele
phone counter-surveillance has been foat
ing around for at least 15 years. Short the
pair at the demark and measure resistance.
Open the pair at the demark and measure
the resistance. Abnormally high or low re
sistances indicate a phone tap. Forrest
Ranger wrote about it in text fles, M.L.
Shannon and Paul Brookes included it in
their books, and an untold number of phone
phreaks have employed this technique. De
spite its popularity, the technique has its
shortcomings: it fails to detect devices in
stalled in the outside plant, split pairs are
undetected, and transmitters built into the
phone are not tested for.
What you'll need:
I) Access to a local DATU.
2) A multimeter with high impedance
scales (several meters that measure into the
giga-ohm range are available) and a capac
itance meter.
3) An induction probe.
4) A fequency counter or near feld de
tector.
5) Something that makes continuous
noise, like a tape player.
6) Ancillary tools (screwdrivers, a can
wrench, etc.).
First, call the phone company to ask
about your line's readiness for ISDN or
DSL. High-speed services demand a line
with no loading coils and a minimum
amount (less than 2500 f.) of bridged taps.
Either will cause inaccurate measurements.
Begin by taking the phone of hook and
turing on your tape player (to tum on
voice activated transmitters). Now give
your phone a pass with your near feld de
tector or frequency counter. Transmitters in
the phone will hopeflly be picked up at
this point. (Note: some speakerphones are
prone to normal RF leakage.) Next, mea
sure the capacitance of the line, dividing
the value by .83 (the average mutual capac
itance for a mile of phone line). This is
roughly the length of your line. Write it
down, you'll need it later. Remember that
.83 is an average value, which can range
fom .76 to .90 depending on line condi
tions. To get a more accurate measurement
you can fne tune your fgure by comparing
capacitance measurements on a section of
plant cable of a known length, or use a
TDR.
Disconnect all the phones from the line
you want to test. Go to your demark and
disconnect your pair on the customer ac
cess side. Short the pair and measure the re
sistance of the line fom the farthest jack
with the meter set to its lowest scale. Re
verse the polarity of the meter and measure
again. If either resistance is more than a
few ohms, it would suggest a series device
wired into the line somewhere on your
property. Now retur to your demark, open
the pair, and cover the ends in electrical
tape. Measure the resistance of the pair
with the meter set to its highest scale. A less
than infnite resistance would suggest a de
vice wired in parallel to your line.
Testing in the outside plant should be
conducted fom the telco side of the de
mark point in order to avoid measurement
error fom the station protector circuit. Call
that DATU and short the pair, then measure
the resistance of the line. Compare the
value you got for your line's length with the
fgures below:
Note: 5ESS switches incorporate a "test
bus" that will add about 500 ohms to the
shorted pair.
These fgures will vary with tempera
ture, splices, wet sections, and a host of
other reasons. Large deviations could (but
don't necessarily) suggest something wired
in series with the line. This measurement
may be supplemented by either a resistance
to ground measurement of both sides of the
pair and a capacitance balance test or a
voltage measurement. A resistive imbal
ance of more than 10 ohms or a noticeable
drop in off-hook voltage calls for further
inspection.
To test for parallel devices in the outside
plant, open the line with the DATU and re-
Wire Gauge Loaded Pair Unloaded Pair
2
833 833
2
52. 51.
22 33.7 329
19 17. 1610
peat the parallel test as described above.
Testng for telehone hook-switch compro
mises requires an induction probe. Recon
nect your pair at the demark and plug aU
your phones back in. Tur your tape player
back on and put it near your phone. Now
probe all the lines coming through your
demark point. If you hear the tape player
through the probe, your phone's hook
switch has been compromised.
Checking for splits on your linc requires
an induction probe and access to a plant
wiring cabinet. Add a tone to either lead of
your pair with the DATU. Probe all the
conductors in the binder pair, listening for
the trace tone. If you hear the tone on more
than two leads (the ones connected to the
line you're checking) your line has been
split. This can be either a bad splicing job,
or someone intentionally hooking a pair up
to your line.
If any of the above tests suggests that
there is something on your line, remember
that there are plenty of innocent reasons a
test could tur up positive, so a detailed
physical search is in order. Disassembling
the phone in question and comparing the
innards to a schematic would be a wise idea
at this point. Take the covers of your
phone jacks, dig around in your demark
point, peek inside wiring cabinets if you
can, and so on. There are some places that
are likely out of your reach, but keep in
mind that they're likely out of reach to
many wiretappers as well.
BUY 2600 ONIINE!
I
Yes . it
.
s true. You can fnally buy 2600 and 2600
accessories without having to waste valuable energy
getting out of your chair or licking a stamp! Best of
all . you can get a lifetime subscription and pay for it
over the course of your entire lifetime . all through the
magic of credit cards. We will also be ofering online
registration for H2K to avoid waiting on line once you
get there! No more writing check or pacing the halls
for week waiting for your stuf to arrive - online
orders usually ship in one week. Check in ofen for new
items and special ofers.
.!11. C!m
The Tool of the New A e
byMMX
Most of tis acle is ac ondensed fm te
administon manua. But b honest wit yourself b
for crticizing me f "sting" ts acle. When w
the last tme you caled Has ad SE'd it out of tem?
Huh? Didn't tink so bitch.
The Ha s Dirt Access Test Unit Remot Ti
nal extnds te field technician's testing capailites of
subscribr lines
Das könnte Ihnen auch gefallen
- WRTH2020 International Radio Supplement A20S Chedules RevisedDokument67 SeitenWRTH2020 International Radio Supplement A20S Chedules RevisedKasi XswlNoch keine Bewertungen
- Kelly Book ForensicDokument25 SeitenKelly Book ForensicKasi XswlNoch keine Bewertungen
- Sex and Broadcasting.oDokument356 SeitenSex and Broadcasting.oKasi XswlNoch keine Bewertungen
- WRTH 2020 International Radio Supplement2 - A20 SchedulesDokument66 SeitenWRTH 2020 International Radio Supplement2 - A20 SchedulesKasi Xswl100% (1)
- Frendx - 1985-05Dokument56 SeitenFrendx - 1985-05Kasi XswlNoch keine Bewertungen
- Frendx: Radio AustraliaDokument60 SeitenFrendx: Radio AustraliaKasi XswlNoch keine Bewertungen
- Frendx - 1985-06Dokument60 SeitenFrendx - 1985-06Kasi XswlNoch keine Bewertungen
- Frendx: Eg Department of Commerce Radio Station InvvvhDokument52 SeitenFrendx: Eg Department of Commerce Radio Station InvvvhKasi XswlNoch keine Bewertungen
- Frendx: E MisorasDokument60 SeitenFrendx: E MisorasKasi XswlNoch keine Bewertungen
- Frendx: George JacobsDokument60 SeitenFrendx: George JacobsKasi XswlNoch keine Bewertungen
- Frendx 1983 12Dokument60 SeitenFrendx 1983 12Kasi XswlNoch keine Bewertungen
- Frendx 1984 01Dokument60 SeitenFrendx 1984 01Kasi XswlNoch keine Bewertungen
- Frendx 1984 03Dokument56 SeitenFrendx 1984 03Kasi XswlNoch keine Bewertungen
- Frendx: September 1983Dokument56 SeitenFrendx: September 1983Kasi XswlNoch keine Bewertungen
- Frendx: ISSN 0160 - 1989Dokument60 SeitenFrendx: ISSN 0160 - 1989Kasi XswlNoch keine Bewertungen
- Frendx: Radio's Greatest Thrill IsDokument60 SeitenFrendx: Radio's Greatest Thrill IsKasi XswlNoch keine Bewertungen
- Frendx: ANARC 1983Dokument56 SeitenFrendx: ANARC 1983Kasi XswlNoch keine Bewertungen
- FR Endx: OdoçsesDokument60 SeitenFR Endx: OdoçsesKasi XswlNoch keine Bewertungen
- Frendx 1983 05Dokument60 SeitenFrendx 1983 05Kasi XswlNoch keine Bewertungen
- Frendx: AnarcDokument60 SeitenFrendx: AnarcKasi XswlNoch keine Bewertungen
- Frendx 1983 02Dokument56 SeitenFrendx 1983 02Kasi XswlNoch keine Bewertungen
- Frendx: 2) EluxeDokument60 SeitenFrendx: 2) EluxeKasi Xswl100% (1)
- Frendx 1982 12Dokument56 SeitenFrendx 1982 12Kasi XswlNoch keine Bewertungen
- DSWCI Short Wave News Last IssueDokument40 SeitenDSWCI Short Wave News Last IssueKasi XswlNoch keine Bewertungen
- DSWCI Tropical Bands Survey 2017Dokument3 SeitenDSWCI Tropical Bands Survey 2017Kasi XswlNoch keine Bewertungen
- Frendx: Radio CairoDokument60 SeitenFrendx: Radio CairoKasi XswlNoch keine Bewertungen
- Frendx: '44 Ab 7tel:DVIDokument60 SeitenFrendx: '44 Ab 7tel:DVIKasi XswlNoch keine Bewertungen
- Frendx 1982 08Dokument56 SeitenFrendx 1982 08Kasi XswlNoch keine Bewertungen
- World Radio TV Handbook 2017 Supplement Including A17schedulesDokument75 SeitenWorld Radio TV Handbook 2017 Supplement Including A17schedulesKasi Xswl100% (1)
- Domestic Broadcasting Survey, 19th Edition 2017 (FINAL EDITION)Dokument17 SeitenDomestic Broadcasting Survey, 19th Edition 2017 (FINAL EDITION)Kasi XswlNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Komunikasi Data: TEE 843 - Sistem TelekomunikasiDokument69 SeitenKomunikasi Data: TEE 843 - Sistem Telekomunikasi1A R. Moch Rizky Sunandar SaputraNoch keine Bewertungen
- Pass KV-123Dokument31 SeitenPass KV-123vidamorjuniorNoch keine Bewertungen
- l9000 Led Light Source User Guide (English Only Version)Dokument37 Seitenl9000 Led Light Source User Guide (English Only Version)ismael0% (2)
- CAN BusDokument7 SeitenCAN BusMihnea DobreNoch keine Bewertungen
- Fluke 8846A - 6.5 Digit Precision MulitmeterDokument8 SeitenFluke 8846A - 6.5 Digit Precision MulitmeterFaqir Khan JadoonNoch keine Bewertungen
- Huawei eLTE Rapid System OverviewDokument10 SeitenHuawei eLTE Rapid System OverviewsolihinNoch keine Bewertungen
- RF Interview Questions and AnswersDokument2 SeitenRF Interview Questions and Answerskiran patraNoch keine Bewertungen
- Karel MS48 User ManualDokument69 SeitenKarel MS48 User ManualTheresa Ann Middleton GreenNoch keine Bewertungen
- Module 1 It Application Tools in Business - CompressDokument38 SeitenModule 1 It Application Tools in Business - CompressJames Ryan AlzonaNoch keine Bewertungen
- GB Interface Detailed Planning - FinalDokument63 SeitenGB Interface Detailed Planning - FinalMichel SilvaNoch keine Bewertungen
- 6502 - Guideline To Reverse Engineering v1.0Dokument7 Seiten6502 - Guideline To Reverse Engineering v1.0Boris IvanovNoch keine Bewertungen
- Accessory Cable GuideDokument9 SeitenAccessory Cable GuideCarmelo BayonNoch keine Bewertungen
- Course Manual - NGNDokument12 SeitenCourse Manual - NGNjugulkNoch keine Bewertungen
- OSI OverviewDokument14 SeitenOSI OverviewhekNoch keine Bewertungen
- MRBIOS Beep and Error Codes PDFDokument2 SeitenMRBIOS Beep and Error Codes PDFtm5u2rNoch keine Bewertungen
- Mobile Phone CloningDokument38 SeitenMobile Phone CloningDevansh KumarNoch keine Bewertungen
- VIBROTECTOR Vibration Transmitters: MeasurementDokument1 SeiteVIBROTECTOR Vibration Transmitters: MeasurementRioEstikaNoch keine Bewertungen
- Goodwe Smart MeterDokument2 SeitenGoodwe Smart MeterZakiNoch keine Bewertungen
- MGW R5Dokument2 SeitenMGW R5Tonya HowardNoch keine Bewertungen
- Lecture 1 Auxiliary Transformer SizingDokument9 SeitenLecture 1 Auxiliary Transformer Sizingelec.highest.euphratesNoch keine Bewertungen
- Tait Specifications TP8100 USDokument4 SeitenTait Specifications TP8100 USepitaNoch keine Bewertungen
- EE 201 - HW 1 Solutions W2007Dokument11 SeitenEE 201 - HW 1 Solutions W2007mrm3zaNoch keine Bewertungen
- Clúster KnoppixDokument10 SeitenClúster Knoppixxiber_paridesNoch keine Bewertungen
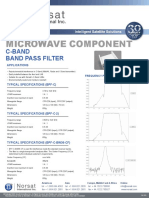
- Microwave Component: C-Band Band Pass FilterDokument1 SeiteMicrowave Component: C-Band Band Pass FilterFelipe DeleonNoch keine Bewertungen
- AntenaDokument4 SeitenAntenaMarcos MontesNoch keine Bewertungen
- How To Make Arduino On Breadboard - Step by Step Instructions - Homemade Circuit Projects PDFDokument12 SeitenHow To Make Arduino On Breadboard - Step by Step Instructions - Homemade Circuit Projects PDFKuldeep SinghNoch keine Bewertungen
- Juniper ACX DatasheetDokument7 SeitenJuniper ACX Datasheetmach75Noch keine Bewertungen
- 7 N 65Dokument2 Seiten7 N 65Aris RomdoniNoch keine Bewertungen
- 803MRF de PDFDokument92 Seiten803MRF de PDFanantiaNoch keine Bewertungen
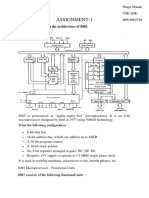
- MPMC Assignment-1Dokument7 SeitenMPMC Assignment-113Panya CSE2Noch keine Bewertungen