Beruflich Dokumente
Kultur Dokumente
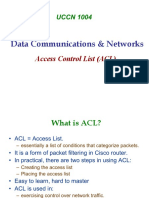
Configuring and Troubleshooting Acls: Access Control Lists
Hochgeladen von
ธนวรรณ โภคาอนนต์Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Configuring and Troubleshooting Acls: Access Control Lists
Hochgeladen von
ธนวรรณ โภคาอนนต์Copyright:
Verfügbare Formate
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.
06-1
Access Control Lists
Configuring and
Troubleshooting
ACLs
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-2
Testing Packets with
Numbered Standard IPv4 ACLs
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-3
Activates the list on an interface.
Sets inbound or outbound testing.
no ip access-group access-list-number {in | out} removes the ACL from the interface.
ip access-group access-list-number {in | out}
Uses 1 to 99 for the access-list-number.
The first entry is assigned a sequence number of 10, and successive entries
are incremented by 10.
Default wildcard mask is 0.0.0.0 (only standard ACL).
no access-list access-list-number removes the entire ACL.
remark lets you add a description to the ACL.
access-list access-list-number
{permit | deny | remark} source [mask]
RouterX(config)#
RouterX(config-if)#
Numbered Standard IPv4 ACL
Configuration
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-4
Permit my network only
Numbered Standard IPv4 ACL
Example 1
RouterX(config)# access-list 1 permit 172.16.0.0 0.0.255.255
(implicit deny all - not visible in the list)
(access-list 1 deny 0.0.0.0 255.255.255.255)
RouterX(config)# interface ethernet 0
RouterX(config-if)# ip access-group 1 out
RouterX(config)# interface ethernet 1
RouterX(config-if)# ip access-group 1 out
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-5
Deny a specific host
Numbered Standard IPv4 ACL
Example 2
RouterX(config)# access-list 1 deny 172.16.4.13 0.0.0.0
RouterX(config)# access-list 1 permit 0.0.0.0 255.255.255.255
(implicit deny all)
(access-list 1 deny 0.0.0.0 255.255.255.255)
RouterX(config)# interface ethernet 0
RouterX(config-if)# ip access-group 1 out
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-6
Deny a specific subnet
Numbered Standard IPv4 ACL
Example 3
RouterX(config)# access-list 1 deny 172.16.4.0 0.0.0.255
RouterX(config)# access-list 1 permit any
(implicit deny all)
(access-list 1 deny 0.0.0.0 255.255.255.255)
RouterX(config)# interface ethernet 0
RouterX(config-if)# ip access-group 1 out
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-7
Permits only hosts in network 192.168.1.0 0.0.0.255 to connect
to the router vty lines
access-list 12 permit 192.168.1.0 0.0.0.255
(implicit deny any)
!
line vty 0 4
access-class 12 in
Example:
access-class access-list-number {in | out}
Restricts incoming or outgoing connections between a particular
vty and the addresses in an ACL
RouterX(config-line)#
Standard ACLs to Control vty Access
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-8
Testing Packets with
Numbered Extended IPv4 ACLs
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-9
ip access-group access-list-number {in | out}
Activates the extended list on an interface
Sets parameters for this list entry
access-list access-list-number {permit | deny}
protocol source source-wildcard [operator port]
destination destination-wildcard [operator port]
[established] [log]
RouterX(config)#
RouterX(config-if)#
Numbered Extended IPv4 ACL
Configuration
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-10
Numbered Extended IPv4 ACL
Example 1
RouterX(config)# access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 21
RouterX(config)# access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 20
RouterX(config)# access-list 101 permit ip any any
(implicit deny all)
(access-list 101 deny ip 0.0.0.0 255.255.255.255 0.0.0.0 255.255.255.255)
RouterX(config)# interface ethernet 0
RouterX(config-if)# ip access-group 101 out
Deny FTP traffic from subnet 172.16.4.0 to subnet 172.16.3.0 out E0
Permit all other traffic
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-11
Numbered Extended IPv4 ACL
Example 2
RouterX(config)# access-list 101 deny tcp 172.16.4.0 0.0.0.255 any eq 23
RouterX(config)# access-list 101 permit ip any any
(implicit deny all)
RouterX(config)# interface ethernet 0
RouterX(config-if)# ip access-group 101 out
Deny only Telnet traffic from subnet 172.16.4.0 out E0
Permit all other traffic
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-12
ip access-list {standard | extended} name
[sequence-number] {permit | deny} {ip access list test conditions}
{permit | deny} {ip access list test conditions}
ip access-group name {in | out}
Named IP ACL Configuration
Alphanumeric name string must be unique
If not configured, sequence numbers are generated automatically starting at 10 and
incrementing by 10
no sequence number removes the specific test from the named ACL
Activates the named IP ACL on an interface
RouterX(config {std- | ext-}nacl)#
RouterX(config-if)#
RouterX(config)#
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-13
Deny a specific host
Named Standard IPv4 ACL Example
RouterX(config)#ip access-list standard troublemaker
RouterX(config-std-nacl)#deny host 172.16.4.13
RouterX(config-std-nacl)#permit 172.16.4.0 0.0.0.255
RouterX(config-std-nacl)#interface e0
RouterX(config-if)#ip access-group troublemaker out
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-14
Deny Telnet from a specific subnet
Named Extended IPv4 ACL Example
RouterX(config)#ip access-list extended badgroup
RouterX(config-ext-nacl)#deny tcp 172.16.4.0 0.0.0.255 any eq 23
RouterX(config-ext-nacl)#permit ip any any
RouterX(config-ext-nacl)#interface e0
RouterX(config-if)#ip access-group badgroup out
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-15
Commenting ACL Statements
access-list access-list-number remark remark
ip access-list {standard|extended} name
Creates a named ACL comment
Creates a numbered ACL comment
RouterX(config {std- | ext-}nacl)#
RouterX(config)#
remark remark
RouterX(config)#
Creates a named ACL
Or
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-16
Monitoring ACL Statements
RouterX# show access-lists {access-list number|name}
RouterX# show access-lists
Standard IP access list SALES
10 deny 10.1.1.0, wildcard bits 0.0.0.255
20 permit 10.3.3.1
30 permit 10.4.4.1
40 permit 10.5.5.1
Extended IP access list ENG
10 permit tcp host 10.22.22.1 any eq telnet (25 matches)
20 permit tcp host 10.33.33.1 any eq ftp
30 permit tcp host 10.44.44.1 any eq ftp-data
Displays all access lists
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-17
Verifying ACLs
RouterX# show ip interfaces e0
Ethernet0 is up, line protocol is up
Internet address is 10.1.1.11/24
Broadcast address is 255.255.255.255
Address determined by setup command
MTU is 1500 bytes
Helper address is not set
Directed broadcast forwarding is disabled
Outgoing access list is not set
Inbound access list is 1
Proxy ARP is enabled
Security level is default
Split horizon is enabled
ICMP redirects are always sent
ICMP unreachables are always sent
ICMP mask replies are never sent
IP fast switching is enabled
IP fast switching on the same interface is disabled
IP Feature Fast switching turbo vector
IP multicast fast switching is enabled
IP multicast distributed fast switching is disabled
<text ommitted>
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-18
Troubleshooting Common ACL Errors
Error 1: Host 10.1.1.1 has no connectivity with 10.100.100.1.
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-19
Error 2: The 192.168.1.0 network cannot use TFTP to connect to
10.100.100.1.
Troubleshooting Common ACL Errors
(Cont.)
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-20
Error 3: 172.16.0.0 network can use Telnet to connect to 10.100.100.1,
but this connection should not be allowed.
Troubleshooting Common ACL Errors
(Cont.)
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-21
Error 4: Host 10.1.1.1 can use Telnet to connect to 10.100.100.1,
but this connection should not be allowed.
Troubleshooting Common ACL Errors
(Cont.)
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-22
Error 5: Host 10.100.100.1 can use Telnet to connect to 10.1.1.1,
but this connection should not be allowed.
A B
Troubleshooting Common ACL Errors
(Cont.)
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-23
Error 6: Host 10.1.1.1 can use Telnet to connect into router B, but
this connection should not be allowed.
B A
Troubleshooting Common ACL Errors
(Cont.)
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-24
Visual Objective 6-1: Implementing
and Troubleshooting ACLs
WG Router s0/0/0 Router fa0/0 Switch
A 10.140.1.2 10.2.2.3 10.2.2.11
B 10.140.2.2 10.3.3.3 10.3.3.11
C 10.140.3.2 10.4.4.3 10.4.4.11
D 10.140.4.2 10.5.5.3 10.5.5.11
E 10.140.5.2 10.6.6.3 10.6.6.11
F 10.140.6.2 10.7.7.3 10.7.7.11
G 10.140.7.2 10.8.8.3 10.8.8.11
H 10.140.8.2 10.9.9.3 10.9.9.11
SwitchH
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-25
Summary
Standard IPv4 ACLs allow you to filter based on source IP
address.
Extended ACLs allow you to filter based on source IP address,
destination IP address, protocol, and port number.
Named ACLs allow you to delete individual statements from
an ACL.
You can use the show access-lists and show ip interface
commands to troubleshoot common ACL configuration errors.
2007 Cisco Systems, Inc. All rights reserved. ICND2 v1.06-26
Das könnte Ihnen auch gefallen
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkVon EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNoch keine Bewertungen
- Network with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationVon EverandNetwork with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationNoch keine Bewertungen
- Exercices ACLDokument9 SeitenExercices ACLPapa NiangNoch keine Bewertungen
- Cisco Ccna Icnd PPT D20S06L02Dokument24 SeitenCisco Ccna Icnd PPT D20S06L02AMIT RAJ KAUSHIKNoch keine Bewertungen
- Lab 1.4.3 Introductory Lab 3 - Access Control List Basics and Extended PingDokument5 SeitenLab 1.4.3 Introductory Lab 3 - Access Control List Basics and Extended PingnickNoch keine Bewertungen
- Introducing ACL Operation: Access Control ListsDokument18 SeitenIntroducing ACL Operation: Access Control Listsธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Configuring and Troubleshooting Acls: Access Control ListsDokument25 SeitenConfiguring and Troubleshooting Acls: Access Control ListstuancoiNoch keine Bewertungen
- Sec 5Dokument54 SeitenSec 5mostafa elsayedNoch keine Bewertungen
- Experiment#7: Access Control List Basics and Extended Ping: ObjectiveDokument4 SeitenExperiment#7: Access Control List Basics and Extended Ping: ObjectiveqweqweNoch keine Bewertungen
- 26.2.2 Packet Tracer - Configure Extended IPv4 ACLs - Scenario 2 - ILMDokument4 Seiten26.2.2 Packet Tracer - Configure Extended IPv4 ACLs - Scenario 2 - ILMTRYST CHAMANoch keine Bewertungen
- CCNA 2 v5.0 Routing and SwitchingDokument9 SeitenCCNA 2 v5.0 Routing and SwitchingCarlos Castillo PalmaNoch keine Bewertungen
- CCNA Lab M4 5.5.1Dokument6 SeitenCCNA Lab M4 5.5.1vadancorneliuNoch keine Bewertungen
- Ccna Quick Revision NotesDokument49 SeitenCcna Quick Revision NotesPaul100% (3)
- Ccnas Chp4 Ptacta Acl InstructorDokument4 SeitenCcnas Chp4 Ptacta Acl InstructorAmine SahliNoch keine Bewertungen
- Clase 17. Packet FilteringDokument70 SeitenClase 17. Packet FilteringKarolina GuamanNoch keine Bewertungen
- Session1e PTActA ACLDokument4 SeitenSession1e PTActA ACLKhông TrânNoch keine Bewertungen
- 4.4.1.2 Packet Tracer - Configure IP ACLs To Mitigate Attacks - InstructorDokument11 Seiten4.4.1.2 Packet Tracer - Configure IP ACLs To Mitigate Attacks - InstructorJohana GarcíaNoch keine Bewertungen
- UCCN1004 - Lect7 - ACL and Packet FilteringDokument40 SeitenUCCN1004 - Lect7 - ACL and Packet FilteringVickRam RaViNoch keine Bewertungen
- D 3 Challenge Acl LabDokument5 SeitenD 3 Challenge Acl LabAmadouMalickMouamfonMoumbagnaNoch keine Bewertungen
- Lab CCNA Security ACLDokument4 SeitenLab CCNA Security ACLAngel SczNoch keine Bewertungen
- Sybex CCNA 640-802 Chapter 12Dokument30 SeitenSybex CCNA 640-802 Chapter 12xkerberosxNoch keine Bewertungen
- Cisco IOS Threat DefenseDokument180 SeitenCisco IOS Threat DefenseLes Wise DavisNoch keine Bewertungen
- Lab 8 Packet Tracer VersionDokument6 SeitenLab 8 Packet Tracer VersionOsGuIsNoch keine Bewertungen
- 4.4.1.2 Packet Tracer - Configure IP ACLs To Mitigate Attacks - InstructorDokument14 Seiten4.4.1.2 Packet Tracer - Configure IP ACLs To Mitigate Attacks - InstructorMiguel JiménezNoch keine Bewertungen
- Basic Router ConfigurationDokument20 SeitenBasic Router ConfigurationLiêm Trần TrọngNoch keine Bewertungen
- Computer System Engineering Department ENCS413 Network Lab Access ListDokument13 SeitenComputer System Engineering Department ENCS413 Network Lab Access Listak akNoch keine Bewertungen
- 7.2.3.4 Lab - Configuring and Verifying VTY Restrictions Act 16Dokument8 Seiten7.2.3.4 Lab - Configuring and Verifying VTY Restrictions Act 16ErvinYanoNoch keine Bewertungen
- En Security Chp4 PTActA ACL InstructorDokument4 SeitenEn Security Chp4 PTActA ACL InstructorEdwin MarinNoch keine Bewertungen
- Boson Netsim Le Functionality and Supported CommandsDokument12 SeitenBoson Netsim Le Functionality and Supported CommandsMian DawoodNoch keine Bewertungen
- 5.4.13 Packet Tracer - Configure Extended IPv4 ACLs - Scenario 2Dokument4 Seiten5.4.13 Packet Tracer - Configure Extended IPv4 ACLs - Scenario 2WerrtyNoch keine Bewertungen
- Cisco Router Command Quick ReferenceDokument4 SeitenCisco Router Command Quick ReferenceWalter ValverdeNoch keine Bewertungen
- 7.2.3.4 Lab - Configuring and Verifying VTY Restrictions WB PDFDokument7 Seiten7.2.3.4 Lab - Configuring and Verifying VTY Restrictions WB PDFAriana Olea CortezNoch keine Bewertungen
- Lab 10 CCNDokument7 SeitenLab 10 CCNIsmail SheikhNoch keine Bewertungen
- 30 COMANDOS IOS (Modo de Compatibilidade)Dokument30 Seiten30 COMANDOS IOS (Modo de Compatibilidade)CarlosAugustoNoch keine Bewertungen
- Ccna: Semester 2 Configuring Acls: HostbDokument14 SeitenCcna: Semester 2 Configuring Acls: HostbFaby ReveloNoch keine Bewertungen
- Answer of CCNA DiscoveryGBDokument34 SeitenAnswer of CCNA DiscoveryGBChimdi KweksNoch keine Bewertungen
- ENSA - Module - 5-ACL LabDokument2 SeitenENSA - Module - 5-ACL LabJusten BiberNoch keine Bewertungen
- Chapter 2 Static RoutingDokument27 SeitenChapter 2 Static RoutingCalvin OhseyNoch keine Bewertungen
- ACL (Access Control List)Dokument5 SeitenACL (Access Control List)RAKIB ভাইয়োNoch keine Bewertungen
- Lab#11 - Extended ACL CCNDokument6 SeitenLab#11 - Extended ACL CCNIsmail SheikhNoch keine Bewertungen
- Answer CCNA Discovery 3 Ver 4 0 Chapter 8 U Can Get 90 2%Dokument9 SeitenAnswer CCNA Discovery 3 Ver 4 0 Chapter 8 U Can Get 90 2%poentren100% (10)
- ACL Practice Lab 1Dokument8 SeitenACL Practice Lab 1LGBT Việt NamNoch keine Bewertungen
- SecurityDokument14 SeitenSecurityjokate6848Noch keine Bewertungen
- Standard Acces List: Ccna Managing Traffic With Access ListsDokument2 SeitenStandard Acces List: Ccna Managing Traffic With Access ListsRafik OudaoudNoch keine Bewertungen
- Practical 4Dokument11 SeitenPractical 4riyevas163Noch keine Bewertungen
- (CCNA) Cisco Commands Cheat Sheet #4 - Boubakr TechDokument3 Seiten(CCNA) Cisco Commands Cheat Sheet #4 - Boubakr TechJosé PedroNoch keine Bewertungen
- Cisco Training - 03 OSPFDokument23 SeitenCisco Training - 03 OSPFIrfan Irawan CbnNoch keine Bewertungen
- Introducing ACL Operation: Access Control ListsDokument38 SeitenIntroducing ACL Operation: Access Control Listsblue.jupiter9x154Noch keine Bewertungen
- 9.4.2.7 Lab - Troubleshooting ACL Configuration and PlacementDokument8 Seiten9.4.2.7 Lab - Troubleshooting ACL Configuration and PlacementEdward Octaviano III0% (5)
- SECS05L02 - Configuring Cisco IOS Classic FirewallDokument35 SeitenSECS05L02 - Configuring Cisco IOS Classic FirewallKhoa Huynh DangNoch keine Bewertungen
- Cisco Access Control Lists (ACL)Dokument54 SeitenCisco Access Control Lists (ACL)Paul100% (2)
- 9.2.1.11 Packet Tracer - Configuring Named Standard ACLs Luis SanchezDokument4 Seiten9.2.1.11 Packet Tracer - Configuring Named Standard ACLs Luis Sanchezrafael8214Noch keine Bewertungen
- Network Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityVon EverandNetwork Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityNoch keine Bewertungen
- Cisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3Von EverandCisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3Noch keine Bewertungen
- Next-Generation switching OS configuration and management: Troubleshooting NX-OS in Enterprise EnvironmentsVon EverandNext-Generation switching OS configuration and management: Troubleshooting NX-OS in Enterprise EnvironmentsNoch keine Bewertungen
- EDM Customer Journey DayMap DownloadDokument1 SeiteEDM Customer Journey DayMap Downloadธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Din Fiber Optic ConnectorsDokument1 SeiteDin Fiber Optic Connectorsธนวรรณ โภคาอนนต์Noch keine Bewertungen
- PMP Exam Prep SummaryDokument5 SeitenPMP Exam Prep SummaryAshenafi100% (8)
- PASOLINKNEODokument117 SeitenPASOLINKNEOAlejandro QuiejNoch keine Bewertungen
- 2.488Gbps SFP Optical Transceiver, 2km Reach: DS-SFP-FC-2G-LWDokument8 Seiten2.488Gbps SFP Optical Transceiver, 2km Reach: DS-SFP-FC-2G-LWtv_romeoNoch keine Bewertungen
- 2.488Gbps SFP Optical Transceiver, 300m Reach: DS-SFP-FC-2G-SWDokument8 Seiten2.488Gbps SFP Optical Transceiver, 300m Reach: DS-SFP-FC-2G-SWtv_romeoNoch keine Bewertungen
- Data Copper ProductsDokument3 SeitenData Copper Productsธนวรรณ โภคาอนนต์Noch keine Bewertungen
- 8 Channel VideoDokument1 Seite8 Channel Videoธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Huihong Technologies Limited: 64 Channel Fiber Optic Video TransceiverDokument2 SeitenHuihong Technologies Limited: 64 Channel Fiber Optic Video Transceiverธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Blockless PLC SplitterDokument1 SeiteBlockless PLC Splitterธนวรรณ โภคาอนนต์Noch keine Bewertungen
- CWDM - SFPDokument8 SeitenCWDM - SFPtv_romeoNoch keine Bewertungen
- 100G Seminar - Bangkok - July 2014Dokument50 Seiten100G Seminar - Bangkok - July 2014ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Huihong Technologies Limited: 2 Channel Fiber Optic Video TransceiverDokument1 SeiteHuihong Technologies Limited: 2 Channel Fiber Optic Video Transceiverธนวรรณ โภคาอนนต์Noch keine Bewertungen
- ICND210S03L01Dokument31 SeitenICND210S03L01ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- ICND210S05L02Dokument9 SeitenICND210S05L02ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- FTTH W-P-1Dokument64 SeitenFTTH W-P-1ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- CD PMD Osa-1Dokument38 SeitenCD PMD Osa-1ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- FNMM Overview BKK2014Dokument59 SeitenFNMM Overview BKK2014ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- ICND210S05L01Dokument27 SeitenICND210S05L01ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Module Summary: © 2007 Cisco Systems, Inc. All Rights Reserved. ICND2 v1.0 - 6-1Dokument2 SeitenModule Summary: © 2007 Cisco Systems, Inc. All Rights Reserved. ICND2 v1.0 - 6-1ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Module Summary: Show Ip Eigrp Neighbor, Show Ip Eigrp Topology, Show Ip Eigrp Interface, and Show Ip RouteDokument2 SeitenModule Summary: Show Ip Eigrp Neighbor, Show Ip Eigrp Topology, Show Ip Eigrp Interface, and Show Ip Routeธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Transitioning To Ipv6: Address Space ManagementDokument30 SeitenTransitioning To Ipv6: Address Space Managementธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Introducing VPN Solutions: LAN Extension Into A WANDokument21 SeitenIntroducing VPN Solutions: LAN Extension Into A WANธนวรรณ โภคาอนนต์Noch keine Bewertungen
- ICND210S07L01Dokument26 SeitenICND210S07L01ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Module Summary: © 2007 Cisco Systems, Inc. All Rights Reserved. ICND2 v1.0 - 7-1Dokument2 SeitenModule Summary: © 2007 Cisco Systems, Inc. All Rights Reserved. ICND2 v1.0 - 7-1ธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Establishing A Point-to-Point WAN Connection With PPPDokument14 SeitenEstablishing A Point-to-Point WAN Connection With PPPธนวรรณ โภคาอนนต์Noch keine Bewertungen
- Establishing A WAN Connection With Frame RelayDokument22 SeitenEstablishing A WAN Connection With Frame Relayธนวรรณ โภคาอนนต์Noch keine Bewertungen
- E Marketing I KolokvijDokument5 SeitenE Marketing I KolokvijsamhagartNoch keine Bewertungen
- كتاب كامل في علم التدريب الرياضي هام جدا لكل مدرب - الكابتن جلال فاضلDokument1.264 Seitenكتاب كامل في علم التدريب الرياضي هام جدا لكل مدرب - الكابتن جلال فاضلSalim Derradji0% (1)
- FalguniDokument2.752 SeitenFalguniKaran VirNoch keine Bewertungen
- Ontario Sunshine List: Electricity 2013Dokument247 SeitenOntario Sunshine List: Electricity 2013Gillian GraceNoch keine Bewertungen
- 11.6.6 Lab Calculate IPv4 Subnets ILMDokument4 Seiten11.6.6 Lab Calculate IPv4 Subnets ILMale_romero1994Noch keine Bewertungen
- CMTS NSI Config GD CMD Reference R7.2.4.2!08!28 2017Dokument866 SeitenCMTS NSI Config GD CMD Reference R7.2.4.2!08!28 2017Silvio Macias100% (1)
- Room Number Subnet Mask Network ID Individual IP Address of Each Computer Broadcast IDDokument3 SeitenRoom Number Subnet Mask Network ID Individual IP Address of Each Computer Broadcast IDGlenn BonafeNoch keine Bewertungen
- Ccna Intro: Chapter - 2Dokument9 SeitenCcna Intro: Chapter - 2Amritpal SinghNoch keine Bewertungen
- MVPN Overview ShortDokument23 SeitenMVPN Overview ShortSaptarshi B.Noch keine Bewertungen
- 201 0722 QPDokument4 Seiten201 0722 QPAsyiqin MohdNoch keine Bewertungen
- ECE 151 Syllabus AY1819s2Dokument2 SeitenECE 151 Syllabus AY1819s2AntonNoch keine Bewertungen
- Network Layer: Computer Networking: A Top Down ApproachDokument157 SeitenNetwork Layer: Computer Networking: A Top Down ApproachVijay GadichaNoch keine Bewertungen
- Netdev 0x12 Ipsec FlowDokument32 SeitenNetdev 0x12 Ipsec FlowRichard CrothersNoch keine Bewertungen
- CCNA Particular Book (CCNAX)Dokument75 SeitenCCNA Particular Book (CCNAX)shakill44Noch keine Bewertungen
- Extended Access-List Example On Cisco RouterDokument1 SeiteExtended Access-List Example On Cisco RouterSamuel HOUNGBEMENoch keine Bewertungen
- TL-R470T (UN) 6.0 DatasheetDokument4 SeitenTL-R470T (UN) 6.0 DatasheetGustavo VeraNoch keine Bewertungen
- MCnew 2Dokument8 SeitenMCnew 2Harvey EguilosNoch keine Bewertungen
- Isp Anti DetectDokument2 SeitenIsp Anti DetectMhine Kho100% (1)
- Ospf Routing ProtocolDokument31 SeitenOspf Routing ProtocolAbhishrkNoch keine Bewertungen
- Konfigurasaun Router Rua Ba Dhcpserver (Yusuf - 2120261251)Dokument25 SeitenKonfigurasaun Router Rua Ba Dhcpserver (Yusuf - 2120261251)Yusuf FaisalNoch keine Bewertungen
- Ip Spoofing Seminar ReportDokument36 SeitenIp Spoofing Seminar ReportHarsha Srinivas100% (3)
- Test Bank For Mike Meyers Comptia Network Guide To Managing and Troubleshooting Networks Lab Manual Exam n10 007 5th Edition by Mike Meyers Jonathan WeissmanDokument23 SeitenTest Bank For Mike Meyers Comptia Network Guide To Managing and Troubleshooting Networks Lab Manual Exam n10 007 5th Edition by Mike Meyers Jonathan WeissmanJamesBoltongdbes100% (30)
- 1.3.1.3 Packet Tracer - Skills Integration Challenge InstructionsDokument4 Seiten1.3.1.3 Packet Tracer - Skills Integration Challenge InstructionsCorie White17% (6)
- Btech Cs 6 Sem Computer Network rcs601 2019Dokument2 SeitenBtech Cs 6 Sem Computer Network rcs601 2019Temp MailNoch keine Bewertungen
- Computer Networking - Free Courses - UdacityDokument9 SeitenComputer Networking - Free Courses - UdacityMike MikkelsenNoch keine Bewertungen
- Laboratory Journal-Network BasicsDokument18 SeitenLaboratory Journal-Network BasicsJosué Claver MANAMOUNoch keine Bewertungen
- MTCRE Soal TestDokument4 SeitenMTCRE Soal TestRidho BonggaNoch keine Bewertungen
- The Application LayerDokument15 SeitenThe Application LayerRahulNoch keine Bewertungen
- Chap 17Dokument142 SeitenChap 17Mo LêNoch keine Bewertungen