Beruflich Dokumente
Kultur Dokumente
ISAP2003
Hochgeladen von
SergioRamos0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
15 Ansichten6 SeitenThis paper presents a fault diagnosis application to assist CC operators in incident situations. It performs fault diagnosis with robustness to incomplete, domain incoherent and chronologically altered information. The developed application works in soft real-time and is capable of assessing the Electrical Network's state, even in the presence of altered network configuration.
Originalbeschreibung:
Copyright
© © All Rights Reserved
Verfügbare Formate
PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenThis paper presents a fault diagnosis application to assist CC operators in incident situations. It performs fault diagnosis with robustness to incomplete, domain incoherent and chronologically altered information. The developed application works in soft real-time and is capable of assessing the Electrical Network's state, even in the presence of altered network configuration.
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
15 Ansichten6 SeitenISAP2003
Hochgeladen von
SergioRamosThis paper presents a fault diagnosis application to assist CC operators in incident situations. It performs fault diagnosis with robustness to incomplete, domain incoherent and chronologically altered information. The developed application works in soft real-time and is capable of assessing the Electrical Network's state, even in the presence of altered network configuration.
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 6
1
Abstract Control operation of Electrical Power
Transmission Networks is usually performed in Control Centres
(CC) and implies knowledge about the networks dynamic
behaviour. These networks possess a distributed system of sensors
and actuators, which produce temporal information about the
networks state. These distributed systems are known as
Supervisory Control and Data acquisition (SCADA) systems. CC
operators map the acquired information to their knowledge of the
networks dynamics and use the resulting knowledge to perform
the control of the electrical networks. In incident situations, in
which SCADA systems can produce huge amounts of information,
CC operators can become very stressed and loose the necessary
focus to perform an accurate diagnosis and hence, proper power
restoration. This paper presents a fault diagnosis application to
assist CC operators in incident situations. This application
performs fault diagnosis with robustness to incomplete, domain
incoherent and chronologically altered information. The
developed application works in soft real-time and is capable of
assessing the electrical networks state, even in the presence of
altered network configuration (e.g. use bypass breakers). A
prototype implementation is already at work in the Control
Centre of the Portuguese Transmission Network.
I ndex TermsPower Systems; Fault Diagnosis; Knowledge
Representation; Temporal Reasoning; Nonmonotonic Reasoning,
Incomplete Information, Expert Systems
I. INTRODUCTION
ontrol Operation of Electrical Power Networks is usually
performed in Control Centres (CC) by very qualified
professionals. These professionals, or Control Centre
operators, normally use a SCADA (Supervisory Control and
Data Acquisition) system to acquire information about the
Electrical Networks state. Control Centre operators possess
knowledge about the networks dynamic behaviour, namely its
physical laws, its protection devices and their operation and
how to combine their knowledge with incoming SCADA
information (alarms) to assess the Electrical Networks state,
in order to perform fault diagnosis and to perform power
restoration.
Many computer applications have tried to solve some of the
problems of fault diagnosis [1]. In [2] several systems are
presented, with various characteristics, but only the
AUSTRAL system, presented in detail in [3] tries to solve a
problem similar to the one presented on this paper. Also in [4],
another system is presented, developed by the authors of this
paper: the SPARSE system, which provides some solutions to
the fault diagnosis problem. Reference [5] also presents a
possible solution to the fault diagnosis problem. In this case,
causal graphs transformed in an operational event calculus
form are used to diagnose nuclear power plant problems. We
are aware of other forms of solution to the fault diagnosis
problem, namely using Fuzzy Sets and Artificial Neural
Networks, for instance [6][7], but we will be restricted to the
ones in which an explicit knowledge representation is
available.
The referenced knowledge-based systems try to perform
fault diagnosis, based on information acquired by sensors in
the electrical network (or other physical object of application),
they work in soft real-time and, even though there are
differences regarding their implementation, every one which
works in real-time, presents the same problems in the presence
of unexpected situations. If, for instance a power line breaker
is under maintenance and the line is using other breaker
(dynamic change in network topology), this particular
topology must be handled by the system so that a possible fault
can not be diagnosed.
Still another approach is presented in [8], which presents a
logic-based system for fault diagnosis (including missing
information). This work uses a different formalism for
temporal knowledge representation, which will be presented in
section II The Event Calculus.
In this paper we propose a knowledge-based approach,
combined with a model-based approach, which will produce
results in unexpected situations. The final system maintains all
the desirable knowledge-based characteristics, upgraded by the
ability to diagnose even unpredictable situations such as
incomplete information, topology alteration and considerable
alarm chronology changes.
The papers outline is to initially present all paradigms and
alterations introduced to obtain the desired functionality,
followed by a presentation of our model for Electrical Power
Network fault detection. Next, our specific knowledge-based
fault diagnosis system will be presented. Afterwards, the
architecture and link between the model and knowledge
approaches will be presented and finally conclusions will be
drawn.
Fault Diagnosis with Incomplete Temporal
Information an Application using a
Knowledge- and Model-Based Architecture
Nuno Malheiro
1
, Zita Vale
2
, Carlos Ramos
1
, Manuel Cordeiro
3
, Antnio Gomes
2
, Albino Marques
4
, Vieira Couto
4
3
Engineerings Section
University of Trs-os-Montes
e Alto Douro
Vila Real ; Portugal
cordeiro@utad.pt
1
Dept. of Informatics Engineering
Polytechnic Institute of Porto
R. Dr. Ant. Bernardino de Almeida
4200-072 Porto ; Portugal
{ntm, csr}@dei.isep.ipp.pt
2
Dept. of Electrical Engineering
Polytechnic Institute of Porto
R. Dr. Ant. Bernardino de Almeida
4200-072 Porto ; Portugal
{zav, agomes}@dee.isep.ipp.pt
4
REN National Electrical
Network, S.A.
(EDP Group)
Apartado 3 - 4471 Maia Codex
C
2
II. PARADIGM & ALTERATIONS
In order to comply with the domains properties, some
formalism had to be chosen, which coped with several
restrictions, namely:
a) Deal with a metric time representation;
b) Possess both temporal and non-monotonic characteristics;
c) Be able to represent both models and knowledge;
d) Work in soft real-time in the desired application.
Several paradigms deal with temporal information, such as
the Situation Calculus, Event Calculus, Allens Interval
Calculus, etc. Several other paradigms deal with temporal
issues in less flexible form, namely temporal constraints in
production rules, recognition of chronicles or temporal causal
graphs. Between all these paradigms and focusing on the
restrictions, the Event Calculus [9] was chosen for
development, due to its metric time representation, ability to
model knowledge with some extension and the ability to work
in soft real-time with an implementation from [10].
A. Simple Event Calculus
Event Calculus was initially presented in [11]. Simple
Event Calculuss (SEC) is a simplified form of event calculus,
and hence computationally less complex. SECs axioms, using
the formalism present in [12], are (SEC1) to (SEC3). The
meaning of the axioms will now be clarified. Axiom (SEC1) is
used to prove that a certain property holds at a given time
point if it initially held and no event has interrupted it since.
Axiom (SEC2) states that a certain property holds at a given
time point if it held due to action A and hasnt been interrupted
since then. Finally, axiom (SEC3) is a representation of the
interruption of a property: a fluent is interrupted if an action
terminates it.
holdsAt(F,T) (SEC1)
initiallyP(F) clipped(0,F,T)
holdsAt(F,T2) (SEC2)
happens(A,T1) initiates(A,F,T1)
T1 < T2 clipped(T1,F,T2)
clipped(T1,F,T2) (SEC3)
A, T [happens(A,T)
T1 < T < T2 terminates(A,F,T)]
B. Simple Event Calculus with Timeouts
To perform event correlation, we have developed an
extension of the Event Calculus [13] that will be briefly
presented here.
The SEC is extended, incorporating special events (the
timeout events), becoming simple event calculus with timeouts
(SECT). These timeout events are added to the fact base
whenever a new event arrives. The pair (E,timeout(E)), in
which E is one event and timeout(E) its corresponding timeout,
captures the time window in which E is relevant for reasoning.
Associated with this time window, a fluent dependent on its
event and respective timeout can represent this time window.
The reasoning, on its lowest level, will be based on the
intersection of these fluents, thus increasing robustness to lack
of chronology.
The timeouts added to the Simple Event Calculus allow an
easier way to map alarm correlation and explicitly represent
the knowledge relevance of an information particle.
SECTs axioms are the following:
holdsAt(F,T) (SECT1)
initiallyP(F) clipped(0,F,T)
holdsAt(F,T2) (SECT2)
happens(A,T1) initiates(A,F,T1)
T1 < T2 clipped(T1,F,T2)
timedout(T1,A,F,T2)
clipped(T1,F,T2) (SECT3)
A, T [happens(A,T) T1 < T < T2
terminates(A,F,T)]
timedout(T1,A,F,T2) (SECT4)
isTimedout(A,F)
T [happens(timeout(A),T) T1 < T < T2]
The ontology of the items undefined by the Event Calculus
are: isTimedout definition is: isTimedout(A, F) means that
action A is able to time out fluent F; timedout definition is:
timedout( T1, A, F, T2) means that action A is timed out
between time points T1 and T2, hence timing out fluent F.
C. Definition of Event Calculus Schemas
To limit the number of explicit fluent initiation and
termination formulae, the concept of initiation and termination
formula schema will be introduced.
In our case, two parameters are added to both the initiates
and terminates formulae: the dependency parameter D and the
grounder parameter G. The complete initiation and termination
formulae become (NF1) and (NF2):
initiates( A, D, G, F, T ) (NF1)
terminates( A, D, G, F, T ) (NF2)
The dependency parameter D is required by the
implementation described in [10], in order to propagate any
change a maximal validity interval (MVI) of a fluent to any
other MVI, in its dependence. An MVI is defined as the
longest temporal interval possible in which a fluent is true and
is not terminated.
The grounder parameter G is an arbitrary predicate logic
formula (may contain free variables), which produces different
formulae for all its ground substitutions. An initiation
(termination) formula schema looks like a simple formula, the
only difference being that its components, namely F, D and G
are arbitrary predicate logic formulae and will be different for
each ground substitution of the grounder argument. No
variables other than the ones which appear in the grounder
argument are allowed in the F and D arguments.
Notice that being (NF1) and (NF2) the heads of a predicate
logic formula, their body can exist and has to be proven before
the grounded formula is considered.
3
III. A MODEL OF THE ELECTRICAL POWER NETWORK
Based on the presented paradigm, more specifically on
event calculus schemas, as well as topological knowledge
representation, a model of the Electrical Power Network for
fault detection will be presented. This model will be able to
identify fault areas (where lines are disconnected) and
remaining interconnectivity (identifying separated islands).
A. Topological Representation
Since our primary concern is fault detection, we shall focus
on the presence (or absence) of voltage in each of the
networks components. Voltage will be hence forth also be
referred to as effort. Several simplifications can be taken into
account such as the view of transformers as isolators,
generators as ideal sources and absence of resistance in every
component which is not a load to the network (client). There is
no error introduction through these simplifications since only
the voltage propagation is of concern in this topological
analysis.
Notice that our model of the network will be a form to
incorporate the networks topology in the observed findings
(SCADA alarms). Since SCADA alarm information is limited
to its producing component, global view of the effects of each
alarm on the network can be performed with a model which
represents the networks topology and is able to propagate the
effects of an alarm in one component, to others which are
connected to it. This kind of model increases robustness to
information incompleteness.
Figure 1 - Schematics of a Power Plant
Each model component has the following structure:
component(Type, Identification, Connections), in which the
component types are: generators, loads, buses, lines, isolators
and circuit breakers. We categorize components in active
(producing SCADA messages): generators, breakers and
isolators; and passive: loads, lines and buses.
The components identification is the one assumed in the
SCADA alarms and the connections indicate the list of other
components to which each component is attached to. This
mimics the networks topology and can represent, for instance,
a power plant as it is depicted in Figure 1.
The option for this type of paradigms for electrical network
representation, disregarding their numerical simulation
counterparts was due to the need of assuring the models non-
monotonic behaviour, for instance in the presence of alteration
of alarm chronology.
The whole network is represented in component form, but
schematically the representations are divided into installations.
Information about to which installation a component belongs
to is included in its identification.
B. Alarm Based Effort Propagation
The propagation of effort (voltage, in our case) is viewed as
occurring instantaneously. A generator is seen as an ideal
source, which imposes effort on each and every component to
which it has a connection path. All active components allow
effort to propagate if they are in service and all passive
components always allow effort propagation.
The model created to propagate the effort in the network is
presented by (TP1) through (TP4), in an operational PROLOG
form. It is modelled using the Event Calculus and no timeout
information.
initiates( scada(generator,ID,on), [], (TP1)
component(generator, ID, _),
effort(generator, ID), T ).
terminates( scada(generator,ID,off), [], (TP2)
component(generator, ID, _),
effort(generator, ID), T ).
initiates( scada(Type,ID,on), (TP3)
[effort(_,_), inService(_,_)],
(connectedWithoutEffort(Type,ID,OType,OID,T),
OType \== generator ),
effort(OType, OID), T ) :
effortLink( OType, OID, T ).
terminates( scada(Type,ID,off), (TP4)
[effort(_,_), inService(_,_)],
(connectedWithEffort(Type,ID,OType,OID,T),
OType \== generator ),
effort(OType, OID), T ) :
not( effortLink( OType, OID, T ) ).
The explanation of the model is as follows. (TP1) imposes
effort on a generator if the SCADA system states that this
generator is active. (TP2) terminates effort on the generator if
it is inactive. (TP3) propagates the effort of any component
which just got under effort. It states that any component which
has just entered in service can propagate effort to any other
component, which is connected to it, which is not in effort and
which became connected to an effort source, through the entry
in service of the component which produced the alarm. (TP4)
represents the possible effort termination in a component
connected to one which is disconnected. It states that effort is
terminated in a component which was in effort and which was
connected to one which left service and for which an effort
link form any source cannot be established.
Notice that propagation is limited ensuring a faster model.
Propagation stops whenever change in the network ceases to
occur. Nevertheless, this approach is computationally
expensive and can provide no answer in limited time. In [10] a
complexity analysis is also performed and, even though the
particular features of this application domain could improve
4
the worst case complexity, the absence of an answer in a time
window useful to the CC operator might not be possible in an
incident situation.
IV. KNOWLEDGE-BASED APPROACH
A. Motivation
The authors original approach was knowledge-based, as
can be seen in [4]. The developed system worked
interconnected with a Westinghouse SCADA system. Later on,
the Portuguese Power Transmission Company (REN) changed
its SCADA system to the Siemens SINAULT Spectrum and, as
it is usual with knowledge-based applications, work had to be
done to adapt the system to its new information source. Since
changes in the system (which development begun in the early
nineties) were imminent, it was decided to reformulate it and
try an approach using a different paradigm, to solve several
problems, namely in the temporal and non-monotonic
reasoning areas. This new approach, is based on the Event
Calculus with Timeouts and has been presented in [13]. It uses
a paradigm usually oriented to model-based reasoning and acts
as an Expert System. The addiction of the timeouts allowed the
inclusion in the calculus of the concept of limited temporal
persistence, inherent to some of the SCADA alarms.
This Event Calculus Knowledge-Based system can be
mapped into the previous production rule with temporal
constraints system (except for some non-monotonic issues).
Events can be thought of as time tagged facts and fluents can
be viewed as temporally windowed intermediate and final
conclusions. This new paradigm is preferred due to its
knowledge representation readability, allowing easier
knowledge maintenance. The paradigm includes explicit
temporal representation and its non-monotonic features derive
directly from the axioms.
B. Architecture
In terms of architecture, the only difference between our
approach and the model-based approach is the modelling
concept. Instead of developing a model which represents a
physical description of the Electrical Network, as presented in
section III, an Event Calculus Expert System was created.
Since this expert system does not need to cope with a complete
model of the Electrical Network, complexity issues will not
arise. This system will be able to diagnose faults in the
electrical network, with respect to its nature and fault area
(which lines are disconnected).
C. Knowledge Base Extract & Example
The model presented in this paper is a subset of the
developed model. The identification of three phase tripping
will be used as an example. In the example, information
regarding manual and/or automatic operation,
presence/absence of human operator and/or automatic
operators in installations, fault area detection, among others,
will be omitted.
Three phase tripping is the result of a correlation between a
tripping alarm and a device open alarm. After a protection
triggers, a tripping order will be sent to a one or more breakers
and each of the devices should respond with a breaker open
alarm, when it has obeyed the order. Alarm correlation occurs
when a device opening is signalled under tripping conditions
(a tripping alarm is temporally connected to the opening). The
temporal connection between the tripping and opening of a
device is of an order of hundreds of milliseconds.
In the Event Calculus with Timeouts, the modelling of such
a situation implies initially the modelling of the fluents which
represent the alarms, in order to ease the correlation. Since this
approach includes timeouts in the Event Calculus, the creation
of a tripping fluent and a device opening fluent are simply
depicted in (FI1) through (FI4).
initiates( scada(Type, ID, trip), [], (FI1)
true, tripFluent(Type,ID), T ).
initiates( scada(Type, ID, on ), [], (FI2)
true, deviceOpenFluent(Type,ID), T ).
isTimedout( scada(Type, ID, trip),
tripFluent(Type,ID) ). (FI3)
isTimedout( scada(Type, ID, on ),
deviceOpenFluent (Type,ID) ). (FI4)
Notice that these definitions imply an initiation and a
termination, since both alarms will be entered in the Event
Base along with their respective timeouts. Hence the
identification of a three phase tripping will be simply (TPI1) to
(TPI3), where (TPI1) means that if a device became open
(on) and it was in tripping, then concludes three phase
tripping. (TPI2) is symmetrical to (TPI1) regarding tripping
and device opening alarms. (TPI3) finishes three phase
tripping, by closure information.
initiates( scada(Type,ID,on), [], true, (TPI1)
threePhaseTripFluent(Type, ID), T ):
holdsAt( tripFluent(Type, ID), T ).
initiates( scada(Type,ID,trip), [], true, (TPI2)
threePhaseTripFluent(Type,ID), T ) :
holdsAt( deviceOpenFluent(Type, ID), T ).
terminates( scada(Type, ID,off), [], true, (TPI3)
threePhaseTripFluent(Type,ID), T ).
Notice that neither the grounder parameter nor the
dependency parameters have much influence in this limited
example. In the real case, clearly the alteration of a three phase
tripping component will affect other fluents, namely the fluent
which represents three phase tripping with reclosure, without
reclosure, line trippings, etc.
The simplicity of the resulting temporal knowledge
representation and the robustness to chronological ordering of
events achieved by this paradigm is demonstrated by this
example.
This subsystem is able to identify simple trips, simple trips
with reclosure and definitive trips on each protection device
and propagate it to lines, buses and loads, thus detecting
incidents and incident areas.
A simple three phase tripping incident is presented in Table
5
1. The complete set of SCADA messages has been filtered,
leaving only the ones concerning substation SXX and power
plant SYY, connected through line LXXYY. Notice that even
an example as simple as this one, still has some urgent and non
urgent alarms, which were generated as a result of the incident.
SCADA messages appearing in bold are relevant for the
knowledge base extract.
The SCADA messages include date, time, installation,
panel number, line of connection, type of alarm and additional
alarm information. These alarms are converted into PROLOG
facts before entering the system. The facts maintain all the
information of the alarms.
Table 1 - SCADA messages - three phase trip
# SCADA Alarm
1 05.01 02:30:20,730 SXX 633 LXXYY1 Urgent Alarm Start
2 05.01 02:30:20,968 SXX 633 LXXYY1 Breaker Open
3 05.01 02:30:20,970 SXX 633 LXXYY1 Non urgent alarm Start
4 05.01 02:30:20,970 SXX 633 LXXYY1 Non urgent alarm End
5 05.01 02:30:20,970 SXX 633 LXXYY1 Non urgent alarm End
6 05.01 02:30:20,972 SXX 633 LXXYY1 Protection >>Trip
7 05.01 02:30:21,340 CYY 604 LXXYY1 Protection >>Trip
8 05.01 02:30:21,342 CYY 604 LXXYY1 Breaker Open
9 05.01 02:30:21,346 CYY 604 LXXYY1 Breaker AbNoStat End
The only information needed for the detection of the fault,
besides the presented in Table 1, is the timeout information.
Consider a constant timeout of 300 milliseconds.
Due to the application of the axioms (SECT1) through
(SECT4), the maximal validity intervals of every fluent are
presented in Table 2.
Notice that the three phase tripping will persist until infinity
because no action or timeout terminates this fluent.
Table 2 Fluent Maximal Validity Intervals
Fluent Valid from Valid To
deviceOpenFluent(brk,(SXX,633)) 02:30:20,968 02:30:21,268
tripFluent(brk,(SXX,633)) 02:30:20,972 02:30:21,272
threePhaseTripFluent(brk,(SXX,633)) 02:30:20,972 Infinity
tripFluent(brk,(CYY,604)) 02:30:21,340 02:30:21,640
deviceOpenFluent(brk,(CYY,604)) 02:30:21,342 02:30:21,642
threePhaseTripFluent(brk,(CYY,604)) 02:30:21,342 infinity
D. Incomplete Information & Example
A SCADA system is usually one with abundant redundant
information. Several alarms are issued in relation with one
particular event. In order to deal with information
incompleteness, domain knowledge is used in our case to
ensure proper conclusions. Alarm redundancy and domain
knowledge are used to identify minimal information subsets
which allow incident identification. A brief example will
elucidate the reader. Consider the example presented in
subsection C, bearing in mind, for instance, that the tripping
signal could be lost due to a problem in information
production, acquisition or transmission. In this case, three
phase tripping could be identified if it was followed by fast
reclosure. In many protection schemes, the impact of fugitive
faults is minimized by fast reclosure mechanisms, which try to
restore service short hundreds of milliseconds after the
occurrence of a tripping. Given that a fast reclosure is in
progress, and that the device which is trying to reclose opened
recently, one could assume that a three phase tripping took
place. The modelling of this scenario is presented in (II1).
As an example, consider the lines 1 through 6 of Table 1.
Suppose that the alarm on line 6 was missing. In this case, and
only with the remaining information, one could assume that the
opening signalled on line 2 had been a manoeuvre, a
malfunction of the device or even a falsely generated alarm.
With the alteration of the initial information and supposing
that additional reclosure information is available, as can be
seen on Table 3, the three phase tripping can still be identified
using (II1).
initiates( scada(Type,ID,reclose), [], true, (II1)
threePhaseTripFluent (Type,ID), T ):
holdsAt( deviceOpenFluent(Type,ID,L), T ).
Table 3 - SCADA alarms - three phase trip with reclusure
# SCADA Alarm
1 05.01 02:30:20,730 SXX 633 LXXYY1 Urgent Alarm Start
2 05.01 02:30:20,968 SXX 633 LXXYY1 Breaker Open
3 05.01 02:30:20,970 SXX 633 LXXYY1 Non urgent alarm Start
4 05.01 02:30:20,970 SXX 633 LXXYY1 Non urgent alarm End
5 05.01 02:30:20,970 SXX 633 LXXYY1 Non urgent alarm End
6 05.01 02:30:21,051 SXX 633 LXXYY1 Protection >>Recl
7 05.01 02:30:21,068 SXX 633 LXXYY1 Breaker Closed
In this case, the state of fluents, with the application of the
axioms (SECT1)-(SECT4), as well as (TPI1)-(TPI3) and (II1)
can be seen in Table 4. Notice that in this case, and through
the application of (TPI3), the three phase trip fluent is no
longer kept till infinity. When line 6 of Table 3 is added to the
event list, the three phase trip fluent ends in infinity but this
knowledge is revised with the addition to the event list of the
alarm in line 7.
Table 4 Fluent Maximal Validity Intervals
Fluent Valid from Valid To
deviceOpenFluent(brk,(SXX,633)) 02:30:20,968 02:30:21,268
threePhaseTripFluent(brk,(SXX,633)) 02:30:21,051 02:30:21,068
V. IMPLEMENTATION
Presently, our fault diagnosis system is an independent
intercommunicating set of processes. Each process acts as a
component connected to a communication bus, enabling it to
communicate with all the others. The Parallel Virtual Machine
(PVM) [14] architecture acts as the bus between the different
components. We chose this implementation due to its
heterogeneity in operating systems, its small message passing
overhead and the developed applications, namely XPVM,
which is a probe application for a PVM based system.
Our system includes a SCADA wrapper process, a
graphical user interface (GUI), the knowledge-based event
calculus expert system and the model-based event calculus
network model, as it is depicted in Figure 2. This system is
scalable in the sense that it is always easily open to new
component introduction.
Dynamically, the system works in a data driven form, being
the Aru executor in charge of acquiring information from the
SCADA system. This small application executes an archive
utility (aru, which stands for ARchive Utility), which gives it
access to the SCADAs real-time database. Once it fetches the
data, it sends it to the system, through the Spectrum wrapper
component. Once in the system, SCADA information can be
directed to any component that needs it, namely the expert and
model systems and the user interface. This way to link our
system and the Sinault SPECTRUM SCADA is non-intrusive,
6
being limited to the execution (at regular intervals) of an
application included in the SCADA system.
Sinault SPECTRUM Supervisory Control and Data Acquisition System
PVM - Paralell Virtual Machine BUS
Spectrum
Wrapper
Graphical User
Interface
Model-Based
System
Knowledge-
Based System
Figure 2 - Architecture of the complete system
When reaching a conclusion, the fault detection
components (Knowledge-based and Model-based
components) voluntarily send it to the GUI. The GUI is in
charge of organizing the incoming fault detection information
and presenting it to the user. The GUI can also be used to
query any of the fault detection components in terms of their
Electrical Network representation at any time.
This architecture also allows one component to query
another component. The knowledge-based component can
query the model-based component in a doubtful situation. In
this way, it can use the other components information to
achieve its own conclusions.
The prototype was implemented in Sun workstations
running Solaris and using C, PROLOG and Motif and PVM
libraries.
VI. CONCLUSIONS
The architecture of an application for fault diagnosis with
incomplete temporal information, applied to incident analysis
in Electrical Power Networks has been presented. Its internal
structure is innovative by using a model based paradigm which
is also able to map both knowledge based information supplied
by experts and a model of the electrical networks voltage
propagation. It has the ability to deal with temporal,
chronologically disordered and incomplete information.
A prototype implementation is already at work in the
Control Centre of the Portuguese Transmission Network. The
system was tested and validated. It is important to refer that its
results are more reliable than those of SPARSE, its
predecessor, in cases where events have chronological
problems, or some incompleteness like one missing event,
being equally good in cases without these disturbances.
The model-based approach produces, in fact, an alternative
to the knowledge-based system in altered conditions. When a
protection scheme is dynamically altered and an incident
occurs, the knowledge-based application could not show any
result (on its own) but the model-based approach pointed to
devices without voltage, so the set of approaches is more
effective than each of the separate approaches. False alarms or
alarms which were produced by protective device malfunction
can also be detected with this approach.
Due to its solid theoretical background, the verification of
such a system can further benefit of advances made by the
scientific community in the verification of systems using the
Event Calculus.
VII. ACKNOWLEDGMENT
The authors gratefully acknowledge the contributions of
Eng. Amarante dos Santos, Eng. Rui Pestana and Eng. Nuno
Salema from REN (EDP) for their inestimable commitment to
this project.
VIII. REFERENCES
[1] Z. Vale, Knowledge Based Techniques and Applications in Power
Systems Control Centers in Intelligent Systems Technology and
Applications, vol. VI, pp. VI-63 to VI-112, Cornelius T. Leondes
(Editor), CRC Press, 2003
[2] ALARM research group, Monitoring and Alarm Interpretation in
Industrial Environments, AI Communications vol.11(3,4), pp. 139-173,
IOS Press, 1998
[3] J.-P. Krivine and O. Jehl, The AUSTRAL system for diagnosis and
power restoration: an overview, in Proc. International Conference on
Intelligent Systems Application to Power Systems (ISAP96), Orlando
(USA), August 1996
[4] Z.A. Vale, A. Machado e Moura, M.F. Fernandes, A. Marques, C.
Rosado, C. Ramos SPARSE: An Intelligent Alarm Processor and
Operator Assistant, IEEE Expert, 12(3), Special Track on AI
Applications in the Electric Power Industry, 1997, pp. 86-93
[5] I. Grosclaude, M-O. Cordier and R. Quiniou, Causal interaction: from
a high-level representation to an operational event-based
representation, in Proc. International Joint Conf. on Artificial
Intelligence (IJCAI 2001), Washington (USA), August 2001, pp. 565-
572
[6] A. Insfrn, A. Alves da Silva and G. Lambert-Torres, Fault Diagnosis
Using Fuzzy Sets, in Proc. Int. Conf. on Intelligent Systems and
Applications, Rio de Janeiro, Brazil, 1999
[7] P. Kdr, A. Kovcs and A.Mergl, A Tolerant Event Recogniser and
Alarm Filter Based on Sequential Pattern Matching under Introduction
into the National Dispatching Centre, in Proc. Int. Conf. on Intelligent
Systems and Applications, Seul, Korea, 1997
[8] J Jung, M Hong, C-C Liu, G Tornielli, A Di Stefano, M Gallanti and D
Maratukulam, Logic and validation techniques for handling of missing
information in fault diagnosis, in Proc. Int. Conf on Intelligent System
Applications to Power Systems (ISAP99), Rio de Janeiro, Brazil, 1999
[9] R.A.Kowalski and M.J.Sergot, A Logic-Based Calculus of Events,
New Generation Computing, n. 4, 1986, pp. 6795.
[10] L.Chittaro and A.Montanari, Efficient Temporal Reasoning in the
Cached Event Calculus, Computational Intelligence, vol.12(3), 1996,
pp. 359-382
[11] R.A.Kowalski and M.J.Sergot, A Logic-Based Calculus of Events,
New Generation Computing, vol. 4, 1986, pp. 6795
[12] M. Shanahan, The event calculus explained, in M.Wooldridge and M.
Veloso (eds), Artificial Intelligence Today, vol. 1600 of LNCS,
Springer-Verlag, 1999, pp. 409-430
[13] N. Malheiro, Z. Vale and C. Ramos, A Formal Expert System For
Power Systems Fault Diagnosis, in Proc. International Conference on
Artificial Intelligence and Application (AIA2002), Mlaga (Spain),
September 2002, pp. 228-233
[14] A. Geist, A. Beguelin, J. Dongarra, W. Jiang, R.t Manchek and V.
Sunderam, PVM: Parallel Virtual Machine - A Users' Guide and
Tutorial for Networked Parallel Computing, Scientific and Engineering
Computation, MIT Press 1994
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Lara CroftDokument58 SeitenLara CroftMarinko Tikvicki67% (3)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Leseprobe Aus: "Multilingualism in The Movies" Von Lukas BleichenbacherDokument20 SeitenLeseprobe Aus: "Multilingualism in The Movies" Von Lukas BleichenbachernarrverlagNoch keine Bewertungen
- Schedule Risk AnalysisDokument14 SeitenSchedule Risk AnalysisPatricio Alejandro Vargas FuenzalidaNoch keine Bewertungen
- Chat GPT DAN and Other JailbreaksDokument11 SeitenChat GPT DAN and Other JailbreaksNezaket Sule ErturkNoch keine Bewertungen
- DEBU026EN (Web) PDFDokument244 SeitenDEBU026EN (Web) PDFCamilo Andres SuarezNoch keine Bewertungen
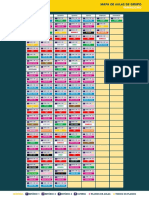
- Fitness Up Mapa Aulas Famalicao Set 2019 v1Dokument1 SeiteFitness Up Mapa Aulas Famalicao Set 2019 v1SergioRamosNoch keine Bewertungen
- Briefing - How Will Electric Vehicle Transition Impact EU JobsDokument7 SeitenBriefing - How Will Electric Vehicle Transition Impact EU JobsSergioRamosNoch keine Bewertungen
- Application Notes Current HarmonicsDokument3 SeitenApplication Notes Current HarmonicsSergioRamosNoch keine Bewertungen
- Safety EquipmentDokument224 SeitenSafety EquipmentSergioRamosNoch keine Bewertungen
- Fluke 165xB 2008 ENDokument58 SeitenFluke 165xB 2008 ENSergioRamosNoch keine Bewertungen
- Emc Guide 2018-03 FinalDokument67 SeitenEmc Guide 2018-03 FinalSergioRamosNoch keine Bewertungen
- Lightning Protection-Earthing 2013 PDFDokument296 SeitenLightning Protection-Earthing 2013 PDFSergioRamos100% (1)
- Dehn Support Toolbox 0110Dokument12 SeitenDehn Support Toolbox 0110SergioRamosNoch keine Bewertungen
- Anienergia Ecodesign TransformersDokument12 SeitenAnienergia Ecodesign TransformersSergioRamosNoch keine Bewertungen
- Surge Protection 2014-15 PDFDokument431 SeitenSurge Protection 2014-15 PDFSergioRamosNoch keine Bewertungen
- ICREPQ09 Abril 2009Dokument6 SeitenICREPQ09 Abril 2009SergioRamosNoch keine Bewertungen
- Pes Ieee Usa Jul2008Dokument7 SeitenPes Ieee Usa Jul2008SergioRamosNoch keine Bewertungen
- ICKEDS06 Portugal Mai2006Dokument6 SeitenICKEDS06 Portugal Mai2006SergioRamosNoch keine Bewertungen
- Calculation of % Slip in Mill During Rolling by Ajmal (10.09.2014)Dokument15 SeitenCalculation of % Slip in Mill During Rolling by Ajmal (10.09.2014)Rakesh Karan SinghNoch keine Bewertungen
- 89 Robinson V MirallesDokument1 Seite89 Robinson V MirallesMartin AlfonsoNoch keine Bewertungen
- Deborah Schiffrin .Tense Variation in NarrativeDokument19 SeitenDeborah Schiffrin .Tense Variation in Narrativealwan61Noch keine Bewertungen
- 3a Ela Day 3Dokument5 Seiten3a Ela Day 3api-373496210Noch keine Bewertungen
- Last Speech of Shri Raghavendra SwamyDokument5 SeitenLast Speech of Shri Raghavendra SwamyRavindran RaghavanNoch keine Bewertungen
- Experiment No 5 ZenerDokument3 SeitenExperiment No 5 ZenerEugene Christina EuniceNoch keine Bewertungen
- PDFDokument50 SeitenPDFWalaa RaslanNoch keine Bewertungen
- Finlatics Investment Banking Experience ProgramDokument4 SeitenFinlatics Investment Banking Experience ProgramSameer BheriNoch keine Bewertungen
- Plate Tectonics QuizDokument6 SeitenPlate Tectonics QuizJordan Santos100% (1)
- The Court of Heaven 1Dokument2 SeitenThe Court of Heaven 1Rhoda Collins100% (7)
- Math 209: Numerical AnalysisDokument31 SeitenMath 209: Numerical AnalysisKish NvsNoch keine Bewertungen
- Rizal Course ReviewerDokument6 SeitenRizal Course ReviewerMarianne AtienzaNoch keine Bewertungen
- House of Wisdom - Bayt Al Hikma (For Recording) - ArDokument83 SeitenHouse of Wisdom - Bayt Al Hikma (For Recording) - ArMaeda KNoch keine Bewertungen
- City Living: Centro de Lenguas ExtranjerasDokument2 SeitenCity Living: Centro de Lenguas Extranjerascolombia RodriguezNoch keine Bewertungen
- Manasvi Lingam, Avi Loeb - Life in The Cosmos - From Biosignatures To Technosignatures-Harvard University Press (2021)Dokument1.082 SeitenManasvi Lingam, Avi Loeb - Life in The Cosmos - From Biosignatures To Technosignatures-Harvard University Press (2021)Shahwaiz NiaziNoch keine Bewertungen
- The Interplay of Religion and PoliticsDokument10 SeitenThe Interplay of Religion and PoliticsThompson mercyNoch keine Bewertungen
- XS2 Pharma 0512 103 UK U-NiDokument2 SeitenXS2 Pharma 0512 103 UK U-NiMilan MilovanovicNoch keine Bewertungen
- High Court Judgment On Ex Party DecreeDokument2 SeitenHigh Court Judgment On Ex Party Decreeprashant pathakNoch keine Bewertungen
- Investigative Project Group 8Dokument7 SeitenInvestigative Project Group 8Riordan MoraldeNoch keine Bewertungen
- Sancticity AllDokument21 SeitenSancticity AllJames DeHart0% (1)
- Neuralink DocumentationDokument25 SeitenNeuralink DocumentationVAIDIK Kasoju100% (6)
- SSP ReviwerDokument40 SeitenSSP ReviwerRick MabutiNoch keine Bewertungen
- LRL Rudy Acuna On Neftali DeLeon - I Am Proud To Be The Grandson Son and Husband of Immigrants.Dokument9 SeitenLRL Rudy Acuna On Neftali DeLeon - I Am Proud To Be The Grandson Son and Husband of Immigrants.EditorNoch keine Bewertungen
- Fever and RashDokument14 SeitenFever and RashwirdahajaNoch keine Bewertungen
- Basilio, Paul Adrian Ventura R-123 NOVEMBER 23, 2011Dokument1 SeiteBasilio, Paul Adrian Ventura R-123 NOVEMBER 23, 2011Sealtiel1020Noch keine Bewertungen
- DIALOGUE Samples B2 JUNE EXAMDokument4 SeitenDIALOGUE Samples B2 JUNE EXAMIsabel María Hernandez RuizNoch keine Bewertungen