Beruflich Dokumente
Kultur Dokumente
Network and Computer Security Tutorial
Hochgeladen von
Sandeep Shrivastava0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
88 Ansichten26 SeitenNetwork and Computer Security Tutorial
Copyright
© © All Rights Reserved
Verfügbare Formate
DOC, PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenNetwork and Computer Security Tutorial
Copyright:
© All Rights Reserved
Verfügbare Formate
Als DOC, PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
88 Ansichten26 SeitenNetwork and Computer Security Tutorial
Hochgeladen von
Sandeep ShrivastavaNetwork and Computer Security Tutorial
Copyright:
© All Rights Reserved
Verfügbare Formate
Als DOC, PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 26
Network and Computer Security Tutorial
Version 0.4.0 April 16, 2001
ack!round
This computer security tutorial is written based on my experiences with computer
and network security along with my training and information I have read. The field of
security is constantly changing so I cannot guarantee that information in this
computer security tutorial will be current. This computer security tutorial will define
some basic security issues and give insight into what causes security to be a
constant issue. This computer security tutorial will help you decide what to protect
and provide some basic information about attacks that may be made against your
network, computer systems, or data. It will also provide computer and network
security recommendations for you or your organization. Although much useful
information can be derived from this document without the reader having
networking knowledge, to use this document in depth, I recommend that readers of
this computer security tutorial have a fundamental knowledge about networking.
The information contained in The CT! "etworking #uide contains the networking
documentation re$uired to understand this computer security tutorial.
"ntroduction
In this computer security tutorial, the terms computer security and network security
will be used often. %hen the term computer security is used, it specifically refers to
the security of one computer, although the overall security of each individual
computer is re$uired for network security. %hen the term network security is used, it
refers to the security of the network in general. This includes such issues as
password security, network sniffing, intrusion detection, firewalls, network structure
and so forth.
Security Violation #e$inition
Computer or network security has been violated when unauthorized access by any
party occurs.
%&y Security'
Computer security is re$uired because most organizations can be damaged by
hostile software or intruders. There may be several forms of damage which are
obviously interrelated. These include&
amage or destruction of computer systems.
amage or destruction of internal data.
'oss of sensitive information to hostile parties.
(se of sensitive information to steal items of monitary value.
(se of sensitive information against the organization)s customers which may
result in legal action by customers against the organization and loss of customers.
amage to the reputation of an organization.
*onitary damage due to loss of sensitive information, destruction of data,
hostile use of sensitie data, or damage to the organization)s reputation.
The methods used to accomplish these unscrupulous ob+ectives are many and
varied depending on the circumstances. This guide will help administrators
understand some of these methods and explain some countermeasures.
Security "ssues
Computer security can be very complex and may be very confusing to many people. It can even
be a controversial sub+ect. "etwork administrators like to believe that their network is secure and
those who break into networks may like to believe that they can break into any network. I believe
that overconfidence plays an important role in allowing networks to be intruded upon. There are
many fallacies that network administrators may fall victim to. These fallacies may allow
administrators to wrongfully believe that their network is more secure than it really is.
This guide will attempt to clarify many issues related to security by doing the following&
,elp you determine what you are protecting.
-reak computer security into categories.
.xplain security terms and methods.
!oint out some common fallacies that may allow administrators to be overconfident.
Categorize many common attacks against networks and computers.
.xplain some attack methods.
escribe tools that can be used to help make a network more secure.
Security "nterdependence
There are many different aspects to computer and network security as you will read in this
document. These different areas of computer security are interdependent on each other in order
for a network to be secure. If one or more areas of computer security are ignored, then the entire
security integrity of the organization)s network may be compromised. A clear example of this is in
the area of computer virus or worm protection. Computer virus protection programs can only filter
known viruses or worms. There are viruses or worms that are not yet recognized as virus
programs immediately after their release. The best way to make unrecognized virus or worm
programs less effective is by $uickly removing the vulneribilities that they use. /ome of these
vulnerabilities are operating system and application program errors. %hen security patches are
created for software, they should be $uickly applied. In this way the vulnerabilty to viruses is
minimized but not eliminated. There are other steps which may further reduce this vulnerability,
but it can never be completely eliminated.
Security (imitations and Applications
If you are reading this document and are thinking that you can get all the information re$uired to
make your network completely secure, then you are sadly mistaken. In many ways, computer
security is almost a statistical game. 0ou can reduce but not eliminate the chance that you may be
penetrated by an intruder or virus. This is mainly for one reason.
"o one can ever know all the software vulnerabilities of all software used on a system.
This is why even those who consider themselves hackers will say that the number one computer
security threat is the lack of $uality in the applications and operating systems. At this point, I could
talk about the various corporate entities that write software and why software lacks the $uality that
many of us believe that it should possess, but that sub+ect is not only way beyond the scope of
this document, but also way beyond the scope of this pro+ect.
The bottom line here is that unless you can remove all the application and operating system
problems that allow viruses and intruders to penetrate networks, you can never secure your
network. Additionally the users on your network are potentially a greater security risk than any
programs. 1bviously removing all vulnerabilities is impossible and will not secure your network
against user errors. I have even considered the possibility that an operating system without a
network interface can be completely secure, but even this cannot be guaranteed. (nknown
viruses or tro+an programs can creep in with applications on Cs or floppies. This has been known
to happen. Although an attacker may not be able to get data from the system, they can damage or
destroy data.
(ayered Security
The fact that complete security is impossible is the reason security experts recommend 2layered
security2. The idea is to have multiple ways of preventing an intrusion to decrease the chance that
intrusions will be successful. 3or example, you should have virus protection on your client
computers. To help layer this security you should also filter viruses at your email server. To help
even more, you should block the most dangerous types of email attachments to prevent
unrecognized viruses and other hostile software from entering your network. Another good
defense layer would also include educating your users about viruses, how they spread, and how
to avoid them.
)ackers
There are many documents that attempt to define the term hacker. I believe that the term hacker
is a connotative term. This means that it is more defined by people)s beliefs rather than by a
dictionary. /ome believe that a hacker is a very skilled computer person. 1thers believe that
hackers are those that perform unauthorized break ins to computer systems. The media and many
sources have caused many uninformed people to believe that a hacker is a threat to computer
and network security while this is not the case. A hacker is no more likely to break the law than
anyone else. I use the more accurate descriptive term, 2intruder2 to describe those who intrude
into networks or systems without authorization.
*&ysical Security
This guide will not talk about physical computer security beyond this paragraph. 0our organization
should be aware how physically secure every aspect of its network is because if an intruder gets
physical access, they can get your data. -e sure the your organization properly secures locations
and consider the following&
/ervers 4 Contain your data and information about how to access that data.
%orkstations 4 *an contain some sensitive data and can be used to attack other
computers.
5outers, switches, bridges, hubs and any other network e$uipment may be used as an
access point to your network.
"etwork wiring and media and where they pass through may be used to access your
network or place a wireless access point to your network.
.xternal media which may be used between organizational sites or to other sites the
organization does business with.
'ocations of staff who may have information that a hostile party can use.
/ome employees may take data home or may take laptops home or use laptops on the
internet from home then bring them to work. Any information on these laptops should be
considered to be at risk and these laptops should be secure according to proper policy when
connected externally on the network 6more on this later7.
Some Terms
This paragaph describes some commonly used computer security terms.
Protocol 4 %ell defined specification allowing computer communication.
Confidentiality 4 Information is available only to people with rightful access.
Integrity 4 Information can only be changed by authorized personnel. Integrity 4 The
receiver of the message should be able to tell the message was not modified. 5e$uires key
exchange.
Availability 4 Information is available to only those who need it.
Verification - nonrepudiation 4 There is proof that the sender sent the message
Authentification 4 The receiver of the message should be able to be sure of the origin of
the message. 5e$uires a digital signature 61ne way hash, public key algorithm, and symmetric
algorithm7 or a public key algorithm.
Spyware 4 A computer program whose purpose is to spy on your internet activities usually
for marketing purposes and usually done by a shady corporate entity.
Malware 4 A computer program with some evil intent. It may on the surface have a good or
useful intent, but may be a tro+an 6with a hidden purpose7 which can be used to gain unauthorized
access to your computer.
Computer Security +e,uirements
This page is about your computer security re$uirements and is intended to save many people
unnecessary reading. If you are an individual who is only concerned about the security needs of
your home computer and do not want to learn alot about computer security, then there are some
simple guidelines that you should read and you do not need to read this entire manual. 0ou should
read the ,ome Computer /ecurity Article on this site. *ost home computers re$uire the following&
A personal firewall when connecting to the internet over any type of connection.
Anti4virus software that is kept updated.
-ack up your data onto another computer, C451*, 8I! drive, or tape regularly.
5egular security updates to the operating system 6these are not as critical if a personal
firewall is installed, but this item is still important7.
5egular updates to the applications run on the system such as *icrosoft 1ffice.
-e aware of the following&
0ou should also be aware that most data that you send or receive on the internet can be
read by other people. Therefore you should be aware of the sensitivity of the data or information
you are sending. If you need to send confidential data you should only send it to sites that begin
with https&99 or use some software to encrypt your data.
-e careful when opening email attachments since they may contain hostile programs even
if your antivirus software has not detected it.
-e careful when downloading and installing programs on the internet. 0ou should scan any
programs for viruses that you get on the internet, but also be aware that some programs may be
spyware or other malware used to gain access to your system.
If you are someone who is responsible for your orgainzation)s security and9or you are learning
about computer security, then you should read this complete document.
#eterminin! w&at to protect
-efore you design your organization)s security plan and implement it, you must first
determine what to protect. Then you must determine what threats exist to what is
protected. This page will discuss how to determine what to protect and what its
value is. etermining the value to your organization of the data you are protecting
will help you determine how much it is worth spending to protect your data. This
information will both help you determine your security re$uirements and your
disaster recovery policy.
+ate -our #ata
-ased on your organization)s structure, you must determine what the importance
and value of your data is. This can most likely be broken down by department and
you may accomplish it by sending $uestionnaires to your department managers
through your management. %hat must be defined is the following&
%hat data you have.
%here it is stored 6%hat server or computer it is stored on and in what
directory7 4 The response may be it is in the I drive in some directory and it will be
up to you to determine the server location for the I drive.
Is it a database or a set of files:
The data importance should be defined in a manner similar to the method shown
below&
,ow well can you live without your data:
;. < 4 I don)t care
=. ; 4 I would like to have it
>. = 4 *ust have it
?. > 4 Can)t live without it
As an organization or department how long can you live without access to
your data 6for each data item specified7: This may be minutes, hours, days, weeks,
months, or years. This information will help you determine if your organization will
survive if this data is lost and whether this data is really vital to your organization. It
will also help you with creation of your disaster recovery plan and its re$uirements.
%hat is the maximum possible damage in monetary units if unauthorized
persons had access to your data and could use it against your organization:
%hat is the maximum possible damage in monetary units if unauthorized
persons incorrectly modified your data or your data was lost:
This information is best determined by department and depending on the type of
your organization, the data may be more or less valuable by department. 3or
example assume an organization with the following departments.
,uman 5esources
3inance
5esearch and .ngineering
'aw epartment
Consider which department)s data would be most important if the organization was any one of a
bank, law firm, or auto manufacturing company.
5ating your data and considering the potential monetary loss if the data is destroyed or
inaccessible for some period of time will also be instrumental in helping your organization develop
a disaster recovery plan.
Consider t&reats, risks, and possi.le dama!e
%hen evaluating how to defend your data, you will need to consider each threat and the degree of
vulnerability to that threat. This is the risk which e$uals threat times vulnerability. Then consider
the cost if the conse$uences of the threat are realized. This will help determine how much you
should spend to reduce your vulnerabilities to each threat.
Computer Security *olicy Cate!ories and
Types
1nce you have determined the value of your data, you need to develop a set of
policies to help protect it. These policies are called security policies and may apply
to users, the IT department, and the organization in general. %hen writing your
policies, consider&
;. %hat data may a user take home:
=. If a user works from home or remote offices and uses the internet to transmit
data, how secure must the data be when in transmission across the internet:
>. %hat policies, network structure, and levels of defenses are re$uired to
secure your data depending on its importance, value and the cost of defending it:
The first items that should be defined are the policies related to the use and and
handling of your data. This will help you determine defensive measures and
procedures. I have categorized policies into three different areas listed below&
(ser !olicies 4 efine what users can do when using your network or data
and also define security settings that affect users such as password policies.
IT !olicies 4 efine the policies of the IT department used to govern the
network for maximum security and stability.
#eneral !olicies 4 ,igh level policies defining who is responsible for the
policies along with business continuity planning and policies.
/ser *olicies
efine what users can and must do to use your network and organization)s
computer e$uipment. It defines what limitations are put on users to keep the
network secure such as whether they can install programs on their workstations,
types of programs they can use, and how they can access data. /ome policies
include&
!assword !olicies 4 This policy is to help keep user accounts secure. It
defines how often users must change their passwords, how long they must be,
complexity rules 6types of characters used such as lower case letters, upper case
letters, numbers, and special characters7, and other items.
!roprietary Information (se 4 Acceptable use of any proprietary information
owned by the company. efines where it can be stored and where it may be taken,
how and where it can be transmitted.
Internet (sage 4 (se of internet mail, (se of programs with passwords or
unencrypted data sent over the internet.
/ystem (se 4 !rogram installation, "o Instant *essaging, "o file sharing
such as @azaa, *orpheus. 5estrictions on use of your account or password 6not to
be given away7.
A!" and remote user system use 6remote access7 4 *ust be checked for
viruses9tro+ans9backdoors. *ust have firewall, must have AA.
Acceptable use of hardware such as modems 4 "o use of modems to
internet without a personal firewall.
"T *olicies
These policies include general policies for the IT department which are intended to
keep the network secure and stable.
Airus incident and security incident 4 Intrusion detection, containment, and removal. ;.
prepare 6policies, checklists9procedures7 = identify 6get evidence7 > contain 6pull off network,
modify passwords7 ? eradicate 6fix, determine cause, improve defenses, test for vulnerablilties7 B
recover 6validate the system, monitor for re4infection7 C lessons learned 6make recommendations
to prevent a similar incident7
-ackup policy 4 efine what to back up, who backs it up, where it is stored, how long it is
stored, how to test backups, what program is used to do backups.
Client update policies 4 (pdate clients how often and using what means or tools.
/erver configuration, patch update, and modification policies 6security7 4 5emove unneeded
services 6harden server7. %hat servers should have I/. ,ow is it determined to do an update:
%hat is done when someone works on the server:
3irewall policies 4 %hat ports to block or allow, how to interface to it or manage it, who has
access to the control console.
%ireless, A!", router and switch security, dmz policy, email retention, auto forwarded email
policy, ability for IT to audit and do risk assessment, acceptable encryption algorithms
0eneral *olicies
,igh level program policy 4 efines who owns other policies, who is responsible for them,
scope and purpose of policies, any policy exceptions, related documents or policies.
-usiness continuity plan 4 Includes the following plans&
o Crisis *anagement 4 %hat to do during the 6any7 crisis which may threaten the
organization.
o isaster 5ecovery 4 /ubfunctions&
/erver recovery
ata recovery
.nd4user recovery
!hone system recovery
.mergency response plan
%orkplace recovery
*olicy (e1els
!olicies can exist on many levels of the organization from a group or team level, to department
level, plant level, or global organizational level. some policies may only be effective on a local
level while others may be enterprise wide throughout the organization.
Computer Security *olicy +e,uirements
/ecurity policies are an excellent way to complement the hardware and software
security measures of your organization. /ecurity policies can determine the method
that both hardware and software are used. The policies will enable everyone in the
organization to be on the same track.
.very organization should have a stated security policy. It should be carefully
written and checked by an attorney to be sure it does not create unnecessary
liability.
+e,uirements o$ t&e *olicy
The policy must be consistant to be effective. There must be similar levels
of security in multiple areas such as physical security, remote access, internal
password policy policies, and other policies.
The policy statement should be assessable.
Issues should be clearly defined and when they apply to the policy. efine
services affected such as email.
Clearly define goals of the policy.
/taff and management must find the policy acceptable. This is why it is
important to justify each policy.
Define roles of the staff with respect to the policies and security issues.
The policy must be enforceable from the network and system controls.
!olicies must be set on servers to be sure domain passwords are reasonably
complex, not repeated, changed periodically, etc.
efine conseuences of security policy violation.
efine expected privacy for users.
!rovide contact information for those interested in more information about
the policy.
*olicy #e$initions
!olicies may define procedures to be used or limitations to what can and can not be
done in the organization. Items that policies should define may include&
%hy the policy exists or why a procedure is done and what it is.
%ho enforces the policy or performs the procedure and why.
%here is the policy effective or where is the procedure done.
%hen is the policy in effect or when is the procedure used.
The where and the when items define the policy scope.
*olicy %ordin! Su!!estions
If security policy is worded incorrectly, it can be ineffective or become a source of trouble. -e
careful not to imply guarantees over items you cannot fully control. 3or example, you cannot
guarantee that employees will be unable to view pornographic web sites from their workplace. It
may also be worth considering a disclaimer to the policy indicating that the policy is not created to
guarantee safety or circumvent accidental exposure of employees to ob+ectional material, but the
policy is intended to protect the organizational network from abuses from within and without. It
should be noted that the policy cannot guarantee that abuses cannot occur.
It is worth making policy abuse statements at logon screens to indicate that anyone logging on to
a particular machine or domain who is not authorized may be prosecuted. This wording should be
done in a legal manner and those who create the policies should consider consulting with their
attorneys about the proper wording of these statements.
Access Control *olicy
An access control policy can be part ot the security policy document, or it may be separate.
Access control policy will define how access to the network is allowed and how it can be done. It
should also define how access to external resources such as the internet should be done. This
access policy should define how access to other business resources 6places that your
organization may regularly do business with or exchange data with7 is done. 3or example, this
access may be done over the internet using some form of Airtual !rivate "etworking 6A!"7, or it
may be done by modem. In any case, it should be covered in the policy to be sure these external
accesses, whether incoming or outgoing are secure.
1ne suggestion for this policy is to forbid employee access from inside the network to the internet
through any source other than the firewall. At the least, any access to the internet should be
through an approved secure interface.
This policy should state&
Allowed access across the network both inside and outside.
,ow services are to be routed both in and out, and whether they are accepted in specific
directions. /ome services of concern include ,TT!, 3T!, and mail.
Acceptable traffic should be specified and all other traffic should be blocked at the firewall
and at other possible locations in the network. Include&
o irection
o /ervice
o ,ost6s7 where re$uired to use service6s7.
o (sers 6where re$uired7 and acceptable times they can access resources.
Computer Security "ncident *rocedures
epending on your organization)s size and re$uirements, a computer security
incident response team may be re$uired or recommended. In any event, someone
in your organization should be in charge of performing the security incident
procedures. In addition, the personnel performing these procedures will re$uire a
certain level of authority so the organization)s management must support this effort.
If you have no security incident procedures an analysis should be done of the types
of security problems you are having. The following should be considered&
%hat types of incidents are occurring: Are they virus attacks, denial of
service, hacked systems, user account compromise, or other attacks:
,ow much of your IT staff time is being spent dealing with each type of
attack:
%hat is the damage in staff time and loss of productivity due to each type of
attack:
%hat is the damage to data due to each type of attack and what is the cost
of this:
%hat is the risk in damage to the organization due to compromised data or
lost data due to each type of attack:
%hat is the overall risk to the suvival of the organization due to each type of
attack:
The answers to the above $uestions will help your organization decide how much
effort should be put into defining the security response and how much should be
spent on computer security measures in general.
Computer Security "ncident *rocedure Steps
There are three main actions that must occur during a security incident. These are
intrusion detection, containment, and removal. The containment and removal
process are covered in the computer security incident procedure steps listed below
which are recommended by the /A"/ Institute and several government agencies.
These steps are based on the /A"/ Institute)s guide on 2Computer /ecurity
Incident ,andling& /tep4by4/tep2
;. !repare 4 Create your policies, checklists, and procedures. !erform and test
backups regularly in case data must later be restored. !ost warning banners on
against intruders. %hen writing policies and procedures consider outside
organizations that may be affected if you have a security incident. etermine who
handles the security incidents.
=. Identify 4 ,ave methods in place to detect an incident and provide a trail of
evidence. etermine if an incident really occurred and evaluate the evidence. "otify
and coordinate the appropriate incident handling personnel other appropriate
personnel and managers who may be affected.
>. Contain 4 Assess the situation in such a way the intruder does not know you
are aware of their presence until you are ready to implement your response. !ull
any critical data off the network that may yet be compromised. Take
countermeasures, possibly pull the affected system6s7 off the network and change
passwords.
?. .radicate 4 5emove malicious code or possibly re4install the system to be
sure to remove all back door or malicious code, and possibly restore from backups.
etermine the cause of the incident, analyze the intrusion method and vulnerability,
implement a protection techni$ue to prevent further intrusion, improve defenses,
and test for vulnerablilties.
B. 5ecover 4 Aalidate the system, monitor for re4infection, restore operations
when it is appropriate and the vulnerability has been removed.
C. 'essons learned 4 *ake recommendations to prevent a similar incident,
create an incident report, and modify your computer security incident procedure if
necessary.
In order to contain and remove an intruder, a very important part of the process
includes detection. 0our organization must have some mechanism in place to detect
a security incident. Therefore the following items are important to consider.
0our organization should have someone check your server status and logs on a regular
basis.
0ou should consider some type of intrusion detection device on your servers depending on
the importance of your data and cost of the intrusion detection device.
0ou should consider some type of intrusion detection device on your network 6search for
suspicious traffic7 depending on the importance of your data transmitted and stored on your
network with consideration for the cost of the intrusion detection device.
"ncident 2orm "tems
/everal items that should be included in your computer security incident form include&
Incident date and time
Computer system6s7 name and9or numbers affected.
Affected system location6s7
1perating system6s7 on the system affected.
Type of system affected 6workstation, mail server, file server, etc.7
Type of intrusion 6data compromise, virus incident, denial of service attack, etc.7
,ow the intrusion was discovered
.ffect of the intrusion
,ow the intrusion occurred
,ow the intrusion was removed
/teps taken to prevent the same type of intrusion again
%ho was notified about the intrusion.
Time spent handling the intrusion and cost of the intrusion to the organization
Security Cate!ories
This page outlines the various technical and management areas that comprise network and
computer system security. These categories include actions and areas of knowledge that will help
administrators in securing a network. %hen administrators have proper knowledge about intruder
attacks, networking, and security protocols, they can properly set up a network to be more secure.
Application and !perating syste" vulnerability control 4 Includes&
o Inventoring software used on your network including all server and client software
operating systems, applications, and services. The version number of each software component
should be recorded.
o %atching security bulletins for new discovered vulnerabilities on software in use on
your network.
o (pdating applications in a timely fashion when security vulnerabilities are found.
o /ervice monitoring 4 .very network administrator should know what services and
network ports are active on each system on the network. /ervice and port use should be limited to
only those that are necessary on each system.
o Approved /oftware 4 1nly software approved by the Information /ystems
department should be used in the organization. This is not to restrict someone)s rights, but to
protect the organization from potentially hostile software such as tro+an or spyware programs.
#etwor$ Manage"ent
o *anagement of network structure 4 %here routers, bridges and other devices are
used. %hat network transmission media are used. "etwork layoout can be used to increase the
network security.
o 3irewalls 4 Implementation, configuration, management, and monitoring.
o Intrusion detection 4 etermining when an intruder has penetrated or attempted
penetration of the network.
o Traps 4 Traps can be used to delay some intruders or prevent damage.
o !asswords 4 !asswords may have different methods of storage, transmittal, or
password policies. Aariations of these methods can affect the security of the passwords and the
network.
o /ecurity tools 4 Aarious tools can be used to check the security strength of the
network and various computers.
o (ser .ducation 4 .ducating users so they can be aware of what to do and what not
to do to help keep the network secure.
o Intruder attacks 4 An administrator should have some knowledge of the various types
of intruder attacks in order to better be able to structure the network and various systems to be
resistant to these attacks.
o ,ardware management 4 ,ardware devices which can connect to the network
indemendently of your normal connection such as modems should be managed to be sure they
are not used without approval and if used should be properly protected.
Virus Protection 4 Airus protection is used to identify and remove viruses from computer
systems and should be actively running on all systems on the network. ,owever, virus protection
will not defend against undocumented viruses.
Security policy 4 /ecurity policy outlines how the network is used and even may determine
wording of warnings. These warnings may state something like 2(nauthorized use is prohibited2.
/ecurity policy may be used to determine password policies, external connection policies, use of
the internet and so forth. The policy should also state how software will be used and only
approved software will be used.
Security protocols 4 @nowledge about various encryption protocols, their strengths and
weaknesses, and how they are best used can help administrators make networks much more
secure.
So$tware Vulnera.ility Control
A software vulnerablilty is some defect 6commonly called a 2bug27 in software which
may allow a third party or program to gain unauthorized access to some resource.
/oftware vulnerability control is one of the most important parts of computer and
network security for the following reasons.
Airus programs use vulnerabilities in operating system and application
software to gain unauthorized access, spread, and do damage.
Intruders use vulnerabilities in operating system and application software to
gain unauthorized access, attack other systems, and do damage.
/ome software itself may be hostile.
If software vulnerabilities did not exist, I believe that viruses would not exist and
gaining any unauthorized access to resources would be very difficult indeed. The
primary tools for unauthorized access would then become&
Tro+an horse programs 6described below7
"etwork sniffing.
!assword cracking through network sniffing.
*an in the middle attacks.
*ost unauthorized access would then most likely be done by employees of the
organization or the unauthorized access would be due to very sloppy firewall
administration or user error.
Countermeasures
There are several countermeasures that may help ensure that unauthorized and
possibly hostile virus or tro+an software does not run on your systems. These
countermeasures also limit the scope of the vulnerability. Countermeasures include&
5un virus scan software on every organizational computer and update the
virus scan database at least twice per week. !erform a full scan at least once per
week.
@eep software security patches updated 4 #et on computer security advisory
mailing lists and update applicable software. %ith some systems such as %indows
systems you can set up a server to automatically update systems on your network.
1ne way to do thin in %indows =<<< systems and above is to use a systems
update server 6/(/7 and set your %indows domain policies to have all computers
regularly updated with approved updates as they are released by *icrosoft.
1nly allow approved software to be run on your computer systems so hostile
tro+an programs are not run. This may involve locking your users down so they
cannot install software on their computer systems.
'imit services on all servers and workstations to the minimum re$uired. -e
sure the network administrator is aware of all operating services especially on all
servers.
5un vulnerability scanners both inside and outside your network to find
computers with vulnerabilities so you will know which ones need patched. The cost
of this should be weighed against the security need.
+unnin! Virus Scan So$tware
Airus scan software should be run on every computer within the organization. This will detect
known viruses when they attempt to infiltrate the system if the virus scan software is setup
correctly. @eep in mind however that virus scan software will only detect viruses in its database,
so there are two concerns&
(nknown viruses will not be stopped by the scanner 4 This is why patching applications is
very important. !atching applications will help eliminate the vulnerabilities that virus programs will
exploit.
The virus database must be updated at least weekly so as new viruses are discovered,
they will be found by your virus scanner programs. these updates may be downloaded from the
maker of the virus scan software. They are normally executable files which update the database
on the client computers. The executable file can be placed in the user)s network login script
program so it will run when they boot their system. In some cases it may be best to test the virus
update before runing it on the entire system.
To be most effective, virus scanner programs should be set up to do the following&
!erform regular weekly or monthly scans of the entire computer system)s local drives.
/can all files when a scan is performed and don)t allow any exclusions of any directories
such as the recycle bin.
-e sure to prompt for user action when a virus is found. this way the user is more likely to
be aware of where the virus came from and they can call your IT staff.
/et the system to scan files when a file is run, copied, renamed or created.
/et up e4mail scanning to scan e4mail attachments. this can also be done at the firewall,
but should be done at least either at the firewall or on all client computers. /canning at both
locations may be a good idea if it is feasible.
0ou may also want to scan web content for hostile content either at the firewall or client
computer depending on your setup. 0ou should know that scanning for hostile e4mail or web
content on the firewall may overburden your firewall. *any firewall organizations recommend that
the scanning be done on a separate computer. ,ow this is done will depend on your situation, but
you should at least determine the process load on the firewall before adding this capability.
All virus incidents should be logged for future reference.
/pdate So$tware Security *atc&es
This process involves several steps which include&
;. @now your software configuration on all systems. This can be most easily done with a
database with information about all computers and software in the organization. The following
information is re$uired to have the ability to update software with security patches&
o %hat each computer is used for.
o The version of the operating system and the maker of the operating system.
o The last update to the operating system.
o The maker and version of all applications run on the system.
o The last update to each application.
o A list of or knowledge of services running on each system. A service is performed by
a particular program on the system. an example is a service that allows network logons to the
system.
o A list of, or knowledge of network ports on each computer system that may be active
and any associated service. A network port is a number which is used for networking to direct a
network transmission to a particular program to be processed.
=. #et on computer security advisory mailing lists and update applicable software. /ome of
the websites associated with these lists can be found in the 2websites2 area of the security section
of the Computer Technology ocumentation !ro+ect.
>. .valuate security advisory bulletins 4 %hen security advisories come in, they will mention
security vulnerabilities in operating systems or application software. *any of these vulnerabilities
may be associated with web browser programs or *icrosoft operating systems or applications.
/ometimes the vulnerability is associated with a service on a platform such as (nix or 'inux. The
administrator must evaluate whether your organization is using this software and whether the
vulnerability is a security risk to your organization. The steps at this point should be similar to&
o The administrator determines whether there is risk.
o The administrator should determine the amount of risk and possible damage. This
may be presented to management. If management is involved in this decision process, some
methodology must be worked out between the administrator and management which allows the
risk to be categorized. This will allow more sound decision making. In order for the network to be
secure, the decision to apply the patch cannot be left strictly to non4technical management.
o If necessary the administrator and management will decide whether to apply the
patch
o If the security vulnerability is a threat, the patch should be applied as soon as
possible.
This is not an endorsement of *icrosoft or %indows =<<<, but as a certified engineer, I am aware
that making patches to applications is much simpler when running a %indows =<<< network.
!atches may be applied on the server and the updates can be loaded the next time users boot or
use the applications. This can save a vast amount of time for systems administrators allowing
them to concentrate on their +obs more fully.
Appro1ed So$tware
1nly approved software should be operated on the organization)s network. This is so hostile
programs cannot gain access to the network. ,ostile programs may be written with some useful
functionality, but may perform a hidden task that the user is not aware of. This type of hostile
program is normally called a 2Tro+an ,orse2. The ways to help determine whether a program is
hostile may include&
oes the progam come from a reliable source:
Is there proof that the program came from the source such as a digital signature:
If the source code is available for the program, the code may be checked to be sure there
is no hostile content.
A reliable third party may be able to check out the software and certify that it is safe.
oes the creater of the program attempt to hide their identity: If the creator of the program
attempts to hide their identity then there may be reason for suspicion. If the program creater does
not hide their identity and can be reached, it is less likely that the program is a hostile program.
,as this program been run by other people or organizations for some period of time with no
adverse conse$uences:
/ome of the above issues are not proof that a program is safe, but are merely indicators. As
mentioned earlier, computer security is not an exact science and it is a matter of reducing the
chance of an intrusion. !robably the best method of being sure of the reliability of a program is to
allow a reliable third party to check the program. I believe it is likely that these kind of services
may become more popular in the future. !rogram writers may even send source code to these
service providers for certification with source code covered by a nondisclosure agreement.
)ostile So$tware
,ostile software programs may have several different types of functions. These
functions may cause damage or allow unauthorized access to be gained allowing
the program to be spread or information may be compromised. These are some
functions that hostile software may perform&
amaging operating systems.
amaging or destroying data.
/niffing the network for any data or passwords.
Installing itself or some other hostile software on computer systems for later
use.
Ac$uisition of unencrypted passwords on the network.
3orwarding compromised information to hostile parties through the firewall.
,arvesting e4mail addresses.
!utting unsolicited advertisements on infected computer systems. These
programs are called adware and may come with other 2useful2 applications.
/pyware 4 A type of program that usually comes with a useful application but
sends information to its creator about what the computer user is doing on the
internet. /ome of these programs creators actually tell the user that the program
comes with ability to see what the user is doing on the internet. 1thers do not.
0ou should be aware that all types of hostile programs such as viruses and tro+ans
can perform any of the above functions. There is a tendency for viruses to only
damage systems or data, and tro+an programs to send compromised data to other
parties, but either type of program can perform any of the functions. This is why all
unauthorized programs are a very serious matter.
Viruses
Airuses reproduce themselves by attaching themselves to other files that the used
does not realize are infected. Airuses are spread today mainly through .4mail
attachments. The attachment may be a file that is a legitimate file but the virus may
be attached as a macro program in the file. An example is a *icrosoft word file.
These files can contain macro programs which can be run by *icrosoft %ord. A
virus may infect these files as a macro and when they get on the next user)s
computer, they can infect other files. These virus programs normally take advantage
of a security vulnerability of the running application. In the case of this example a
*icrosoft %ord macro permission security vulnerability is exploited. Airuses can
directly affect executable files or ynamic 'ink 'ibrary 6'' 7 files that the operating
systems and applications use to run.
(sually the virus will spread before it will do anything that may alert the user to its
presence.
The countermeasure to prevent virus programs from infiltrating your organization is
to implement the countermeasures in the section titled 2/oftware vulnerability
Control2. 5unning virus scanning software on every computer in the organization is
a primary step in minimizing this step.
Tro3an )orse So$tware
The name 2Tro+an horse2 comes from the historical incident where the #reeks built a horse statue
as a tool to take the city of Troy. They hid soldiers inside. The people of Troy thought that they
were victorious and the gods had given them the horse as a gift, they pulled the horse inside the
city. At night the soldiers inside the horse snuck out and opened the gates of the city letting the
main #reek army into the city.
Tro+an horse software is software that appears to have some useful function, but some hidden
purpose awaits inside. This purpose may be to send sensitive information from inside your
organization to the author of the software.
The countermeasure to prevent tro+an horse programs from infiltrating your organization is to
implement the countermeasures in the section titled 2/oftware vulnerability Control2. Allowing only
approved software with proper testing to be run in the organization will minimize the threat of
these programs. The organizational security policy can help ensure that all members of the
organization operate in compliance with this countermeasure.
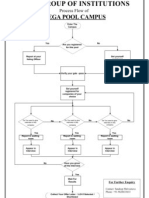
Network (ayout
The network layout has much influence over the security of the network. The
placement of servers with respect to the firewall and various other computers can
affect both network performance and security. There may even be areas of the
network that are more secure than others. /ome of these areas may be further
protected with an additional firewall. A typical network is shown below.
In this network, the box labeled 2I/2 is an intrusion detection system which may be
a computer or deviced designed to log network activity and detect any suspicious
activity. In this diagram it is shown outside the firewall, on the semi4private network
and protecting the servers on the private network. It may be a good idea to place an
I/ +ust inside the firewall to protect the entire private network since an attack may
be first launched against a workstation before being launched against a server. The
I/ protecting the servers could be moved to protect the entire private network, but
depending on cost and re$uirements it is also good to protect your servers,
especially the mail server.
The semi4private network is commonly called a 2*82 6for e*ilitarized 8one7 in
many security circles. In this diagram the semi4private network contains a mail relay
box to increase security since the mail server is not directly accessed. The mail relay
box routes mail between the internet and the mail server.
1ther network e$uipment used includes&
5outers 4 (sed to route traffic between physical networks. *any routers
provide packet filtering using access control lists 6AC's7. This can enhance network
security when configured properly. 5outers can be configured to drop packets for
some services and also drop packets depending on the source and9or destination
address. Therefore routers can help raise the security between different segments on
a network and also help isolate the spread of viruses.
/witches 4 A switch is used to regulate traffic at the data link layer of the 1/I
network model. This is the layer which uses the *edia /ccess Control 6*AC7
address. It is used to connect several systems to the network and regulates network
traffic to reduce traffic on the network media. This can reduce collisions.
*edia 4 The physical cable that carries the signal for the network traffic.
5outers can be set up to perform packet filtering to enhance network security.
Network4/ser 2unctions
The consideration of how each computer system on the network is used is a very
important part of computer and network security. These considerations can even be
used to enhance cost savings where neccessary.
*any times when security vulnerabilities are published, an older version of software
may not be supported by the manufacturer. This may re$uire an operating system
upgrade or an additional license to be purchased to upgrade specific software. This
may be very cost prohibitive to many organizations. %hen dealing with these
situations, it is important to consider your network layout and how it is used.
1ne consideration that should be kept in mind when dealing with network security is
what users can perform what functions and what computers these users can use.
3or example the following situation may exist in an organization&
/ome users can receive and send both internal and external e4mail while others can only
send and receive internal e4mail.
(ser)s who can only send and receive internal e4mail will not have users on their systems
who can use external e4mail.
Considering this situation, the computers that can only receive internal e4mail are less of a
security risk than those who can receive external e4mail. *any viruses spread with e4mail. If
computers that send and receive external email do not get the virus, then it is not likely to spread
to those computers that only deal with internal e4mail. Therefore it is more important to fix
application vulnerabilities on computers that deal with external e4mail than on those that do not. In
this way, a virtual perimeter of protection may be established in an organization. This may not be
the most secure network configuration, but it is much more secure than not updating any
computers at all.
Tra$$ic 2ilterin!
Traffic filtering is a method used to enhance network security by filtering network traffic based on
many types of criteria.
*acket 2ilterin!
!acket filtering is a method of enhancing network security by examining network packets as they
pass through routers or a firewall and determining whether to pass them on or what else to do with
them. !ackets may be filtered based on their protocol, sending or receiving port, sending or
receiving I! address, or the value of some status bits in the packet. There are two types of packet
filtering. 1ne is static and the other is dynamic. ynamic is more flexible and secure as stated
below.
Static *acket 2ilterin!
oes not track the state of network packets and does not know whether a packet is the first, a
middle packet or the last packet. It does not know if the traffic is associated with a response to a
re$uest or is the start of a re$uest.
#ynamic *acket 2ilterin!
Tracks the state of connections to tell if someone is trying to fool the firewall or router. ynamic
filtering is especially important when (! traffic is allowed to be passed. It can tell if traffic is
associated with a response or re$uest. This type of filtering is much more secure than static
packet filtering.
Source +outin!
In source routing, packets contain header information describing the route they are to take to the
destination. /ource routing is a security concern when an attacker may gain access to a network
that has access to yours without going through your firewall.
/ource routing should be disabled on network routers, especially at the network perimeters.
,ackers may be able to break through other friendly but less secure networks and get access to
your network using this method.
5ail and Security
*any attempts to intrude on organizational networks are made either through the
organization)s email server or through sending mail directly to users of the network.
There are several steps which should be taken to reduce the chance of penetration
success in this area.
-lock many dangerous email attachments on your mail server or at your
firewall. *any attachment types may contain code that can be run on workstations
or servers and create a method for an outsider to gain control of that machine. If an
executable attachment is sent to one of your users and they double click on the
attachment, it is likely that the code will run and the attack will succeed. The only
defense in this case is your antivirus software on the machine. ,owever consider
the possibility that the virus program may not recognize the attachment as hostile
code either because it was not detected yet or because a hacker specifically wrote
the code to penetrate your network. %e block the following attachments because
they either can point to dangerous code, are dangerous code or can contain
dangerous code&
;. Dade 4 *icrosoft Access pro+ect extension can contain executable
code.
=. Dadp 4 *icrosoft Access pro+ect can contain executable code.
>. Dapp 4 *icrosoft 3ox!ro application is executable code.
?. Dasp 4 Active server pages
B. Dasx 4
C. bas 4 -asic program source code is executable code.
E. bat 4 -atch file which can call executable code.
F. Dchm 4 Compiled ,T*' help file can contain executable code.
G. cmd 4 %indows "T command script file is executable code.
;<. com 4 Command file program is executable code.
;;. cpl 4 Control panel extension
;=. Dcrt
;>. Dcsh
;?. 4dll 4 ynamic link library is executable code. Could be placed on your
system then run by the system later.
;B. exe 4 -inary executable program is executable code.
;C. Dfxp 4 *icrosoft 3ox!ro is executable code.
;E. Dhlp 4 ,elp file
;F. Dhta 4 ,T*' program
;G. Dinf 4 /etup information
=<. Dins 4 Internet naming service
=;. Disp 4 Internet communication settings
==. +s 4 Hava/cript file
=>. +se 4 Hava/cript encoded file
=?. Dksh 4 (nix shell file
=B. Dlnk 4 'ink file
=C. Dmda 4 *icrosoft Access add4in program
=E. Dmdb 4 *icrosoft Access program
=F. Dmde 4 *icrosoft Access *. database
=G. Dmdt 4 *icrosoft Access file
><. Dmdw 4 *icrosoft Access file
>;. Dmdz 4 *icrosoft Access wizard program
>=. Dmsc 4 *icrosoft Common Console document
>>. msi 4 *icrosoft windows installer package
>?. Dmsp 4 %indows Installer patch
>B. mst 4 Aisual Test source files
>C. Dops 4 3ox!ro file
>E. pcd 4 2!hoto C image or *icrosoft Aisual Test compiled script2
>F. pif 4 2/hortcut to */41/ program2
>G. Dprf 4 2*icrosoft 1utlook !rofile /ettings2
?<. Dprg 4 23ox!ro program source file2
?;. reg 4 5egistry files
?=. Dscf 4 2%indows .xplorer Command file2
?>. scr 4 /creen saver
??. sct 4 %indowsI script component
?B. Dshb 4 ocument shortcut
?C. Dshs 4 /hell scrap ob+ect
?E. Durl 4 Internet address
?F. vb 4 Aisual -asic file
?G. vbe 4 Aisual -asic encoded script file
B<. vbs 4 Aisual -asic file
B;. Dvsd
B=. Dvss
B>. Dvst
B?. Dvsw
BB. wsc 4 %indows script component
BC. wsf 4 %indows script file
BE. wsh 4 %indows script host settings file
BF. xsl 4 J*' file may contain executable code
*icrosoft 1utlook blocks these above attachments by default in 1utlook =<<> as noted at
Attachment 3ile Types 5estricted by 1utlook =<<>.
2irewall *rotection
2irewall
3irewalls are used to protect an organization)s internal network from those on the outside
6internet7. It limits and regulates the access from the outside to the internal network and also
regulates traffic going out. It is used to keep outsiders from gaining information to secrets or from
doing damage to internal computer systems. 3irewalls are also used to limit the access of
individuals on the internal network to services on the internet along with keeping track of what is
done through the firewall.
3irewalls filter traffic based on their protocol, sending or receiving port, sending or receiving I!
address, or the value of some status bits in the packet. There are several types of firewalls which
include packet filtering, circuit level relay, and application proxy.
If your organization does not have a firewall, get one. At least implement a packet filtering firewall
on a 'inux based computer, if money is the concern.
The firewall should filter e4mail, 3T! file transfers, and web content traffic for potential
harmful or hostile code and viruses.
"o computer should be directly connected to the internet without going through an I/
approved firewall. This means independent modem connections to the internet should be
forbidden.
2irewall *olicy
/et up a 2spoofing filter2 on your firewall 4 on)t allow traffic from the internet that indicates
a source I! address matching any of your internal network addresses. This keeps attackers from
2spoofing2 your machines and possibly causing them to crash.
!revent spoofing from your network 4 !lace an outbound filter 6for addresses inside your
network attempting outside access7 on the firewall that only allows traffic from valid internal
network addresses to be serviced. This should prevent attacks against other networks from being
originated in your network.
Network "ntrusion #etection
0our network should have some network intrusion detection system. %ith that said,
the method of detecting intrusions, how to monitor, and how to interpret the data is
a complex sub+ect.
"ntrusion #etection Types
"etwork 4 (sed to protect the network or a large part of it. It listens to all
available network packets and tries to find any intrusion pattern based on the
information in the packets. %here this type of I/ is placed on the network is
important since it cannot analyze all packets behind routers, bridges, or switches.
/ystem 4 (sed to protect a specific host such as a webserver. This kind of
intrusion system can be especially effective when a server is in an area off the
firewall such that it is neither on the internet or on the internal network K @nown as a
emilitarized zone 6*87 L. These kinds of intrusion detection systems can usually
only protect one service well.
"ntrusion #etection +e,uirements
The intrusion detection re$uirements mentioned in this section are generally for
network intrusion detection systems rather than system intrusion detection systems.
The re$uirements mentioned here are general and will depend on the size of your
network, traffic load on your network, and the type of intrusion detection software
you install. 5ead the manufacturers instructions for specific recommendations.
Intrusion detection systems typically consist of two parts which are an engine and a
control console. These two parts are usually on separate computers. 1bviously
the console is used to control and make changes to the behavior of the intrusion
detection engine. The engine analyzes the network traffic and takes appropriate
action if an intrusion is detected.
/ince network intrusion detection systems must process a lot of network data in a
short time, these systems re$uire a good deal of processing power. They also
re$uire much 5A* for high performance, and may re$uire much hard drive space to
store log information.
"ntrusion #etection 2eatures
Attack patterns are saved in a database.
ata packet reassembly 4 /ome may or may not re4assemble I! packets the
same way a receiving system would reassemble them. *ost I/ do not reassemble
the packets in this manner. %ithout reassembling the packets as the receiver, some
attacks may go unnoticed.
Checksum verification 4 A good I/ will verify packet checksums to be sure
the packet has not been tampered with.
"ntrusion #etection Actions
'og intrusion information or save raw packets.
/end an alert to an administrator using email or another method.
Interfere with the attack. There are several actions that may be taken&
o /ession disruption 4 The I/ can send AC@43I" packets to both ends of a
connection 6by I! spoofing each computer7 to close a session. This may be done if a hacker
appears to be gaining unauthorized access.
o *odify the firewall or router behavior during an attack.
Network *ort Scanners
!ort scanners are used to help increase the security of your network. !orts are mapped to specific
services. -y running a software program that tests to see what ports a specific computer responds
on, a network administrator 6or potential hacker7 can get some indication about the types of
services running on a particular machine. !ort scanning can be done inside your network to test
various servers and workstation or it can be done from outside your network to determine what
services can be accessed from the internet through your firewall.
0oals o$ *ort Scannin!
To determine services that a computer is running and shut down services not being used to
increase the security of the computer being scanned.
To determine the vulnerabilities of the services that are being run in the computer being
scanned. The vulnerabilities can then be patched once they are identified.
"nternal and 67ternal *ort Scannin!
There are some security service providers that will scan your network from the internet to test for
open ports and vulnerabilities on your servers. They may provide a printed or electronic report on
the results outlining your vulnerabilities and giving recommendations about how to fix them. *any
of these services are very useful especially since they stay current with current vulnerability
information and update their software regularly to test for new vulnerabilities.
.ven if you hire someone to scan your network from the outside, you should still scan your
network with your own scanning tools from the inside. !lease note that before scanning or sniffing
your network, even as a network administrator, you should always get written permission from
your management first up to the level of your CI1. This to avoid prosecution should someone
decide they do not like information being scanned. Also be sure you do not scan when system
crashes due to scans could cause loss of data or interfere with work.
If you scan your network, you should scan specific parts of your network rather than the whole
network at one time. I would recommend that you scan and secure your servers first, but do not
do this during normal business hours when your server usage is at a peak. Also you may want to
warn your users before a scan is done that some service interruption may occur due to system
preventative maintenance.
*ort Scanners
There are many port scanner types some of which may identify vulnerabilities along with ports that
are being serviced. 'inks to port scanners can be found at
http&99www.techtutorials.info9nsectools.html
Computer Security Tools
1ther network tools include&
,oney !ots 4 (sed to fool a hacker into believing that a target exists which really does not
exist. It may be uset to keep a hacker in a virtual environment which does not really exist as a
means of caputer or to prevent the attacker from attacking a real target.
(tilities that can be used to analyze log files 4 *akes administrator +obs easire by scanning
log files to locate attempted unauthorized entry or suspicious activity.
"etwork /niffers 4 Can be used to sniff and log network traffic which can help
administrators find traffic on the network which may be suspicious or contain information which
should be encrypted.
-andwidth Testers 4 Tests the available bandwidth across certain network lines or between
two points on your network.
!assword cracking programs 4 !rograms that take an encrypted or hashed value of a
password and guess at the password until they find the unencrypted password.
*asswords
!asswords are a primary piece of information that intruders will try to ac$uire in
order to gain unauthorized access to systems or networks.
*assword Stora!e
%hen users enter passwords for the network or operating system, they or some
facsimile of them must be stored so there is something to compare user login
attempts to. There are three primary choices for password storage&
Clear text
.ncrypted password
,ash value of a password 4 (sed by (nix and %indows "T
The storage locations may be&
5oot or administrator readable only
5eadable by anyone.
!asswords are more secure when they can only be read by the administrator or
root account. Also the best password storage security is to store the hashed value
of a password.
Typical )as&in! 2unctions
("IJ 4 Algorithm similar to ./ with BC bit key. There are two random
characters 6salt7 are added to the algorithm so two password values are not stored
the same even if they are the same.
%indows "T 4 *? is used to generate a ;=F bit value.
*assword *rotection and Crackin!
!asswords should be chosen wisely and a dictionary word should never be used.
This is because if an attacker can get the hashed or encrypted value of a password,
they can run password guessing programs to eventually guess the password by
comparing the encryped result of the guess to the actual encrypted password. The
easiest password attack is a dictionary attack where dictionary words are used to
guess the password. 1ther attacks include a brute force attack which can take
much longer than a dictionary attack. This is why passwords should have a
minimum length and a minimum degree of complexity. The complexity re$uirements
should include three of four of the following four types of characters&
'owercase
(ppercase
"umbers
/pecial characters such as MNOPQRSD67KLTU
3or help in choosing passwords wisely see the article Tips for choosing !asswords that can be
easily remembered, but are secure
*rotocols to send passwords
!A! 4 !assword Authentication !rotocol 4 (sed with !oint to !oint !rotocol 6!!!7. The
password is sent in the clear.
C,A! 4 Challenge handshake authentication protocol is preferred rather than !A! since
the actual password is not sent across the internet or network.
Security Attacks
This page lists types of security attacks. This document will address security issues, measures,
and policies which take these types of attacks into consideration.
o/4 enial of /ervice
Tro+an ,orse 4 Comes with other software.
Airus 4 5eproduces itself by attaching to other executable files.
%orm 4 /elf4reproducing program. Creates copies of itself. %orms that spread using e4mail
address books are often called viruses.
'ogic -omb 4 ormant until an event triggers it 6ate, user action, random trigger, etc.7.
)acker Attacks
I use the term 2hacker attacks2 to indicate hacker attacks that are not automated by programs
such as viruses, worms, or tro+an horse programs. There are various forms that exploit weakneses
in security. *any of these may cause loss of service or system crashes.
I! spoofing 4 An attacker may fake their I! address so the receiver thinks it is sent from a
location that it is not actually from. There are various forms and results to this attack.
o The attack may be directed to a specific computer addressed as though it is from
that same computer. This may make the computer think that it is talking to itself. This may cause
some operating systems such as %indows to crash or lock up.
#aining access through source routing. ,ackers may be able to break through other
friendly but less secure networks and get access to your network using this method.
*an in the middle attack 4
o /ession hi+acking 4 An attacker may watch a session open on a network. 1nce
authentication is complete, they may attack the client computer to disable it, and use I! spoofing
to claim to be the client who was +ust authenticated and steal the session. This attack can be
prevented if the two legitimate systems share a secret which is checked periodically during the
session.
/erver spoofing 4 A C=*0A88 utility can be run on %indows GB stations to re$uest
'A"*A" 6in the clear7 authentication from the client. The attacker will run this utility while acting
like the server while the user attempts to login. If the client is tricked into sending 'A"*A"
authentication, the attacker can read their username and password from the network packets
sent.
"/ poisoning 4 This is an attack where "/ information is falsified. This attack can
succeed under the right conditions, but may not be real practical as an attack form. The attacker
will send incorrect "/ information which can cause traffic to be diverted. The "/ information
can be falsified since name servers do not verify the source of a "/ reply. %hen a "/ re$uest
is sent, an attacker can send a false "/ reply with additional bogus information which the
re$uesting "/ server may cache. This attack can be used to divert users from a correct
webserver such as a bank and capture information from customers when they attempt to logon.
!assword cracking 4 (sed to get the password of a user or administrator on a network and
gain unauthorized access.
Some #oS Attacks
!ing broadcast 4 A ping re$uest packet is sent to a broadcast network address where there
are many hosts. The source address is shown in the packet to be the I! address of the computer
to be attacked. If the router to the network passes the ping broadcast, all computers on the
network will respond with a ping reply to the sttacked system. The attacked system will be flooded
with ping responses which will cause it to be unable to operate on the network for some time, and
may even cause it to lock up. The attacked computer may be on someone else)s network. 1ne
countermeasure to this attack is to block incoming traffic that is sent to a broadcast address.
!ing of death 4 An oversized IC*! datagram can crash I! devices that were made before
;GGC.
/murf 4 An attack where a ping re$uest is sent to a broadcast network address with the
sending address spoofed so many ping replies will come back to the victim and overload the
ability of the victim to process the replies.
Teardrop 4 a normal packet is sent. A second packet is sent which has a fragmentation
offset claiming to be inside the first fragment. This second fragment is too small to even extend
outside the first fragment. This may cause an unexpected error condition to occur on the victim
host which can cause a buffer overflow and possible system crash on many operating systems.
Security *rotocol /se
(se services that send passwords only in encrypted form. Avoid telnet and 3T!.
SN5*
Avoid the use of /"*! on routers since information for this protocol is not encrypted and can
provide hackers with useful information about your network. (se /"*!v= is /"*! use is
necessary.
2T*
3T! uses port =; for commands and =< for data.
There are two types of 3T!&
/tandard 3T! 4 All inbound ports above ;<=> must be open.
!assive 3T! 4 All outbound ports above ;<=> must be open.
If 3T! must be supported, the most secure way to support it through the firewall is to support
passive 3T!.
Security 6ntry *oints
Consider some of the following issues when designing your security and setting up your network,
systems, and application programs.
,ow will you deal with a hostile takeover at one of your sites:
o o users have limited access to only what they need:
o Can we disable user access $uickly if necessary:
*odems
Airuses through e4mail attachments
,ostile programs installed by your users
Security Cost
Vuantify the cost of your security effort versus the cost of recovery from damage. o the following
to help determine worthwhile security policy&
Vuantify assets
Analyze worth
.stimate recovery costs.
Application (e1el *rotection
In order to avoid Tro+an ,orses, only I/ approved software should be allowed to be
installed on any computers in the organization.
@eep operating system and application program security patches updated. Therefore to
support this effort, the following must be in place&
;. /oftware architectures on all machines must be defined. This can be done by
department or individual computer or combination thereof. This policy is especially important for all
server computers.
The operating system on all computers must be defined along with all
applications that are run on them.
The latest security patches for all operating systems and applications must be
tracked and it must be known if each department or computer has the latest security patches.
5eliable patch sources for all operating systems and each application used in
the organization must be determined. These sources must be regularly used when new patches
are made available.
Turn on *acro Airus !rotection in *icrosoft applications such as %ord. /elect 2Tools2,
21ptions2, select the 2#eneral2 tab, and select 2*acro Airus !rotection2. In some later *icrosoft
Applications, this feature is always on and there is no checkbox to turn it on.
Turn the auto4execute feature off in *icrosoft applications.
Turn off scripts in 1utlook.
68mail
/end 5ich Text 3ormat 6.5T37 email attachments rather than *icrosoft %ord 6.1C7 email
attachments. 5ich Text 3ormat files cannot contain %ord macro programs which may contain
viruses. %hen opening the file, first open it in a plain text editor such as "otepad 6%ordpad won)t
work7 to be sure it is really a text file 6/ome viruses can disguise a 1C file as a 5T3 file7.
Turn off 2Auto !review2 in 1utlook 6not 1utlook .xpress7.
System *rotection
"o networked computer without operating virus detection software shall be operated. Airus
detection software shall be updated a minimum of once per month and a complete system scan
for viruses shall be done at least once per month.
"o unprotected shares
isable ActiveJ code in all web browsers.
/tandard settings on web browsers for Hava and Havascript code.
/ystems should be set not to hide file extensions for known file types. If hiding extensions
for known file types is allowed, an attacker can disguise a file with a name like
235I."'03I'..TJT.exe2. This file will appear to be a text file to a user. If the user attempts to
open it, it can be run in their system, and... To set this correctly, do the following&
;. 1pen 2*y Computer2.
=. 1n the menu, select 2Aiew2 and 23older 1ptions2.
>. /elect the 2Aiew2 tab.
?. (ncheck 2,ide file extensions for known file types2.
isable9remove %indows /cripting ,ost 6%/,7
;. Click on 2/ettings2
=. /elect 2Control !anel2
>. Click 2Add95emove2
?. Click on the 2%indows /etup2 tab.
B. Click 2Accessories2.
C. (ncheck 2%indows /cripting ,ost2 and click 21@2.
/ser Security "ssues
/ser 6ducation
(se caution opening e4mails. o not open mail from unknown originators.
*ake users aware of ability for hackers to hide executable files as text or other harmless
file types.
(sers must be educated not to use the same passwords at work that they may use over
unsecured connections on the internet.
*assword *olicies
'ogon passwords must be changed at least every G< days 6><4C< days recommended7.
*inimum password age policy 4 B days.
!asswords must be at least F characters long and use at least two numbers.
1n %indows omain networks in the 2omain /ecurity !olicy2 tool, select 2/ecurity
/ettings2, 2Account !olicies2, and 2!assword !olicy2. .nable the 2passwords must meet
complexity re$uirements2 rule. This means at least one character from three of the following
categories must be included&
o lowercase
o uppercase
o numbers
o special characters such as MNOPQRSD67KLTU
!asswords must be kept secret and not written down.
on)t let programs save passwords.
'ock account after > failed logon attempts within ;B minutes.
Account lockout should be reset by an administrator.
"o clear text passwords that can allow access to any sensitive information should be sent
through any unsecured network such as the internet.
The use of clear text passwords that can allow access to any sensitive information on a
secure network should be avoided. This means that the use of 3T! programs 6unless over A!"7
should be avoided. /ecure /hell 6//,7 programs can be used to perform the same function with
encrypted passwords.
!asswords should not be stored using reversible encryption.
Account *olicy
5emote users should be disconnected on "T domains after ;4? hours of inactivity. This
keeps users logged off after business hours so attackers can)t use an open account to launch an
attack from. Also any open files are closed and the tape backup program can backup all files.
1pen files are not backed up.
/et the account policy 2(sers must log on in order to change password2.
Ser1er *olicies on %indows #omains
on)t rename the Administrator Account, but don)t allow it to access the domain controller
computer6s7 from the network. Create a new account with the same or similar privileges as the
administrator and give this account an ability to access the domain controllers over the network.
%hen someone tries to log onto the administrator account over the network, it can be flagged as
an attempted security violation.
asic Security +ecommendations
+estoration
1f course important data should be periodically backed up. 1ne additional protection mechanism
is to use software such as "orton (tilities to take a snapshot of your system. It can record disk
partition information to a floppy, and this can be used to restore a system if a virus destroys
computer system disk partition information.
9r!ani:ational *olicies
evelop an organizational security policy and educate all users about the policy. %rite a virus
procedure to be implemented when a virus is discovered.
Security Terms
Ciphertext 4 Text or data that has been enciphered such that unauthorized persons should
be unable to read it.
Cipher 4 A mathematical function that is used to perform encryption or decryption.
Cryptoanalysis 4 The practice of analyzing ciphertext with the intent of breaking it.
Cryptography 4 /cience dealing with keeping messages secure.
Cryptology 4 The section of mathematics that deals with cryptography and cryptoanalysis.
ecipher 4 The act of taking text that is enciphered so unauthorized persons cannot read it
and processing it into plain text or data that can be read or used.
ecryption 4 The process of turning an encrypted message 6ciphertext7 back into plaintext.
.ncipher 4 The act of taking plain text or data nnd processing it into ciphertext so
unauthorized personnel cannot read it or use it.
.ncryption 4 The process of hiding the contents of a message.
1ne way hash functions 4 A function that can be easily performed one way but is difficult or
impossible to reverse.
!laintext 4 "ormal text or data, before the enciphering process or after the deciphering
process.
/alting 4 Adding random data to a password prior to performing a one way hash on it. This
is a means of stopping a dictionary attack.
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Project File Should Include The FollowingDokument2 SeitenProject File Should Include The FollowingSandeep ShrivastavaNoch keine Bewertungen
- NetworkingDokument49 SeitenNetworkingSandeep ShrivastavaNoch keine Bewertungen
- Akestech Infotech PVT LTD: Features of SLICKPOSDokument4 SeitenAkestech Infotech PVT LTD: Features of SLICKPOSSandeep ShrivastavaNoch keine Bewertungen
- Steam Id ResetDokument1 SeiteSteam Id ResetSandeep ShrivastavaNoch keine Bewertungen
- Candidate List ElectionDokument1 SeiteCandidate List ElectionSandeep ShrivastavaNoch keine Bewertungen
- Administrator's Guide EnglishDokument19 SeitenAdministrator's Guide EnglishSandeep ShrivastavaNoch keine Bewertungen
- Akestech Infotech PVT LTD: Targeted BusinessesDokument3 SeitenAkestech Infotech PVT LTD: Targeted BusinessesSandeep ShrivastavaNoch keine Bewertungen
- Department of Home - EGovernance RoadmapDokument91 SeitenDepartment of Home - EGovernance RoadmapSandeep ShrivastavaNoch keine Bewertungen
- POM Unit 1Dokument16 SeitenPOM Unit 1Sandeep ShrivastavaNoch keine Bewertungen
- Complaint Management SystemDokument7 SeitenComplaint Management SystemSandeep Shrivastava0% (1)
- Must ReadmeDokument1 SeiteMust ReadmeSandeep ShrivastavaNoch keine Bewertungen
- ISCL Case Study 1Dokument3 SeitenISCL Case Study 1Sandeep ShrivastavaNoch keine Bewertungen
- Electronic Payment SystemDokument17 SeitenElectronic Payment SystemSandeep Shrivastava0% (1)
- ProductivityDokument2 SeitenProductivitySandeep ShrivastavaNoch keine Bewertungen
- Technical Considerations For Internet Service Blocking and FilteringDokument27 SeitenTechnical Considerations For Internet Service Blocking and FilteringSandeep ShrivastavaNoch keine Bewertungen
- Question On Quantitative Aptitude For Management Competition 30sep2013Dokument3 SeitenQuestion On Quantitative Aptitude For Management Competition 30sep2013Sandeep ShrivastavaNoch keine Bewertungen
- The Target Masses Consisted of All Indian IT Service Society Due To The MarketDokument1 SeiteThe Target Masses Consisted of All Indian IT Service Society Due To The MarketSandeep ShrivastavaNoch keine Bewertungen
- Concepts of Industrial ManagementDokument9 SeitenConcepts of Industrial ManagementSandeep Shrivastava50% (2)
- Role of The Nafed in The Agricultural MarketingDokument4 SeitenRole of The Nafed in The Agricultural MarketingSandeep ShrivastavaNoch keine Bewertungen
- Linux Stars in Mission CriticalDokument2 SeitenLinux Stars in Mission CriticalSandeep ShrivastavaNoch keine Bewertungen
- Retail Scenario in India: Unlimited OpportunityDokument20 SeitenRetail Scenario in India: Unlimited OpportunitySandeep ShrivastavaNoch keine Bewertungen
- Complete ProcessDokument1 SeiteComplete ProcessSandeep ShrivastavaNoch keine Bewertungen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Robot Operating SystemDokument11 SeitenRobot Operating SystemAbdullah Abbas100% (1)
- Json CacheDokument10 SeitenJson Cachebenjaminmishael20Noch keine Bewertungen
- Adrian - Borbe - CHAPTER 1 5 1Dokument149 SeitenAdrian - Borbe - CHAPTER 1 5 1ecilaborbe2003Noch keine Bewertungen
- Sachin S. Pawar: Career ObjectivesDokument3 SeitenSachin S. Pawar: Career ObjectivesSachin PawarNoch keine Bewertungen
- Answer Sheet A2Dokument3 SeitenAnswer Sheet A2Alba FernándezNoch keine Bewertungen
- CSProxyCache DLLDokument36 SeitenCSProxyCache DLLRadient MushfikNoch keine Bewertungen
- RAN3308: Flexi RFM 3T6R 2100Dokument2 SeitenRAN3308: Flexi RFM 3T6R 2100Reza BordbarNoch keine Bewertungen
- 1 - 2 - 1 RTSX Message ProcessingDokument67 Seiten1 - 2 - 1 RTSX Message ProcessingMichael Omodeyinde Robbin-CokerNoch keine Bewertungen
- The Paper Doctor TEXTODokument101 SeitenThe Paper Doctor TEXTOondasdeforma67% (3)
- Sensors and TransducersDokument9 SeitenSensors and TransducersPra BhuNoch keine Bewertungen
- Power BI DesktopDokument7 SeitenPower BI DesktopZaklina TrajkovskaNoch keine Bewertungen
- Introduction To IOTDokument8 SeitenIntroduction To IOTAKASH S RNoch keine Bewertungen
- HRS Funding Opportunities BulletinSeptember222017Dokument24 SeitenHRS Funding Opportunities BulletinSeptember222017SyedNoch keine Bewertungen
- Implementation With Ruby Features: One Contains Elements Smaller Than V The Other Contains Elements Greater Than VDokument12 SeitenImplementation With Ruby Features: One Contains Elements Smaller Than V The Other Contains Elements Greater Than VXyz TkvNoch keine Bewertungen
- MT6582 Android ScatterDokument5 SeitenMT6582 Android ScatterSharad PandeyNoch keine Bewertungen
- Setup and Deployment in Visual Basic 2010Dokument15 SeitenSetup and Deployment in Visual Basic 2010meongkuNoch keine Bewertungen
- Simple 4k Wallpaper - Google SearchDokument1 SeiteSimple 4k Wallpaper - Google SearchElix3rNoch keine Bewertungen
- Akun SiswaDokument10 SeitenAkun Siswagame advenNoch keine Bewertungen
- Mine Ventilation Using CFDDokument5 SeitenMine Ventilation Using CFDmitevNoch keine Bewertungen
- 29-CHT06 Honda Steering Wheel ControlDokument4 Seiten29-CHT06 Honda Steering Wheel Controlalexandre fleureauNoch keine Bewertungen
- Aspire Company Profile:, Aspire Exam Cracking KITDokument17 SeitenAspire Company Profile:, Aspire Exam Cracking KITChandrasekhar Uchiha100% (1)
- SAPDokument19 SeitenSAPdzulfatuhNoch keine Bewertungen
- Chapter 2 - The Origins of SoftwareDokument26 SeitenChapter 2 - The Origins of Softwareلوي وليدNoch keine Bewertungen
- Home Visit Record (HVR) #1Dokument2 SeitenHome Visit Record (HVR) #1Nicole Arriana ResumaNoch keine Bewertungen
- SSS - R1A - Form (EDocFind - Com)Dokument40 SeitenSSS - R1A - Form (EDocFind - Com)percy_naranjo_20% (1)
- HettichDokument74 SeitenHettichomkarniranjanNoch keine Bewertungen
- Dorma Automatic DoorDokument4 SeitenDorma Automatic DoorClef GonadanNoch keine Bewertungen
- RRU1861 UHF RFID Reader User's Manual V2.0Dokument39 SeitenRRU1861 UHF RFID Reader User's Manual V2.0Krishnamoorthy HegdeNoch keine Bewertungen
- Brochure CAT Advanced series-B-CATADV-112-ENDokument21 SeitenBrochure CAT Advanced series-B-CATADV-112-ENSelk CLNoch keine Bewertungen
- Semi-Automatic Digital Micro Vickers Hardness Testing Machine (Tester) DVS-1XYDokument8 SeitenSemi-Automatic Digital Micro Vickers Hardness Testing Machine (Tester) DVS-1XY周记伟Noch keine Bewertungen