Beruflich Dokumente
Kultur Dokumente
AuthShield - One Click VPN Solution Providers India
Hochgeladen von
AuthShield LabCopyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
AuthShield - One Click VPN Solution Providers India
Hochgeladen von
AuthShield LabCopyright:
Verfügbare Formate
IN N EFU L ab s is a research oriented Information Security consulting group specializing in
meeting the Information Security needs of the consumer via specialized products and services. We believe in innovating and creating the latest technologies to combat the rapidly grow-
TM
ing menace of hacking and reduce dependency on human factors. We offer a complete gamut of Information Security services under one roof which includes our patented and patent pending products like 99% Secure - Cyber Cafe Surveillance, Tactical Internet Interception, Multi Factor Authentication, Link Analysis and Pattern Matching and services like complete corporate security
Two Factor Authentication
process management, web application security and managed security services.
Cred ent ials
Empanelled with DRDO Labs for multiple indigenous products.
A strong Board of Advisor consisting of former Army officers and academicians
Only Indian company to have developed an indigenous Two Factor Authentication (Hard token,
Push Token
USB Token, Image based login)
Only Indian company to have developed and deployed an independent Internet Monitoring System across an entire region
Successfully tracked ring of cyber criminals operating from within India as well as from outside
Served key clients in Private and Public sector for more than four years
Management with combined experience of more than 5000 Hours in information security
Largest trained manpower for Cyber Intelligence with a Private company in India
Multiple patent pending technologies including Cyber Caf surveillance, Tactical Internet Monitoring System, Multifactor Authentication
ARE YOU STILL USING THE
90s TECHNOLOGY OR
HAVE MOVED ON
TO THE LATEST
ONE!
Inf orm ati on S ec uri ty at Its best
Corp Add:- 8th Floor, Unit 876
Aggarwal Cyber Plaza II,
Netaji Subhash Palace , Delhi -110034, India
+91-11-47065866 / 27356211-12 ,
+91-9313050131
E-mail: info@innefu.com
website: www.innefu.com
Hard Token
USB Token
The Problem
Different Token Types from AuthShield
OTP-based authentication definitely adds
an extra step to your log-in process. However, depending on the form factor and the
vendor you chose it can be a minor inconvenience or a major pain. Much also depends on your users patience and your
willingness to spend the extra time to ensure a higher level of security. Users find
it difficult to enter OTPs in devices.
In this scenario, Innefu has launched a
revolutionary concept to use smart phones
as a medium for Two factor Authentication. One Touch Authentication bypass
the standard One Time Passwords, and
brings a truly Two Factor Authentication
experience which beats all hacking mechanisms including Key Logger
Token Type
It generates a new
password a er xed
intervals of me.
The user enters the
password generated
by the hard token as
a secondary form of
authen ca on.
Description
The Solution: AuthShield One Click TM
AuthShield One-Touch Authentication is the latest innovation
in Two factor Authentication. Once a user is registered for One
Touch Authentication he receives a Push Notification on his
smart phone every time he attempts to log in. The user just has
to Approve or Deny the request by a Single One Touch
Authentication on his device to log in or reject the attempt.
Mobile token is
convenient form
factor installed on
the smart phone
itself . OTP is generated in the Smart
Phone itself
In SMS token
One Time Password is generated and sent to
the registered
mobile phone of
the user.
All OATH
Compliant
tokens
Platforms
AuthShield so
token is a convenient form
factor installed
on the laptop /
desktop itself.
The user enters
the password
generated by
so token.
All Phones
With SMS
One Click Authentication Architecture
Requires Mobile
Operator
Connec vity
Offline Usage?
Seamless integra on with
Financial transac ons
Web applica ons
VPN
Mail solu ons
Remote server
Ac ve Directory Login
Cloud
ERP solu ons
ADVANTAGES
Doesnt slow you down while logging-in
Doesnt require any extra hardware tokens
Uses asymmetric cryptography to sign and verify communica ons
Delivered over a mutually-authen cated secure transport
An a acker cant breach as it is based on Public-private key infrastructure
Operating Systems
Au
hie
S
h
t
ld
va
Ad
s
ge
a
t
n
Unparalleled Support
Indigenous Technology
Competitive Advantage
Au
th
Sh
iel
dA
dv
an
tag
e
Robust and Proven Technology
Simple and Easy Integration
Our Expertise in dealing with various Government Agencies
USB token is based
on Public Key Infrastructure PKI Technology. It enables
the use of digital
signature, digital
receipt, encryp on
and permissions
management services.
Das könnte Ihnen auch gefallen
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (894)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- KieselDokument38 SeitenKieselNEWS CENTER Maine100% (1)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- 3HE17250AAAATQZZA - V1 - NSP NFM-P 21.3 XML API Developer GuideDokument366 Seiten3HE17250AAAATQZZA - V1 - NSP NFM-P 21.3 XML API Developer Guidedd100% (1)
- CIS Red Hat Enterprise Linux 5 Benchmark v2.2.1Dokument437 SeitenCIS Red Hat Enterprise Linux 5 Benchmark v2.2.1Julio Cesar PrincipeNoch keine Bewertungen
- TCS associates must protect sensitive informationDokument15 SeitenTCS associates must protect sensitive informationABHISHEK TIDKE67% (6)
- Auth Shield Case Study-Better User Security For Enterprises Powered by SAP ERPDokument8 SeitenAuth Shield Case Study-Better User Security For Enterprises Powered by SAP ERPAuthShield LabNoch keine Bewertungen
- AuthShield 2FA Integration With Checkpoint One Click VPN SolutionDokument16 SeitenAuthShield 2FA Integration With Checkpoint One Click VPN SolutionAuthShield LabNoch keine Bewertungen
- AuthShield - Trusted Authentication Partner For Your Enterprise SolutionDokument2 SeitenAuthShield - Trusted Authentication Partner For Your Enterprise SolutionAuthShield LabNoch keine Bewertungen
- Authshield-Web Application Security SolutionsDokument11 SeitenAuthshield-Web Application Security SolutionsAuthShield LabNoch keine Bewertungen
- AuthShield-ERP Solution Providers IndiaDokument12 SeitenAuthShield-ERP Solution Providers IndiaAuthShield LabNoch keine Bewertungen
- Auth Shield Lab - Mobile One Touch Authentication SolutionsDokument12 SeitenAuth Shield Lab - Mobile One Touch Authentication SolutionsAuthShield LabNoch keine Bewertungen
- Save Your Information by Auth Shield Two Factor AuthenticationDokument29 SeitenSave Your Information by Auth Shield Two Factor AuthenticationAuthShield LabNoch keine Bewertungen
- AuthShield - Information Security Solution Provider For Banking Sector in IndiaDokument33 SeitenAuthShield - Information Security Solution Provider For Banking Sector in IndiaAuthShield LabNoch keine Bewertungen
- AuthShield Lab-Hard Token Authentication SolutionDokument8 SeitenAuthShield Lab-Hard Token Authentication SolutionAuthShield LabNoch keine Bewertungen
- Authshield-OTP Solution For UninorDokument14 SeitenAuthshield-OTP Solution For UninorAuthShield LabNoch keine Bewertungen
- Authshield Lab-2 Factor Authentication SolutionsDokument31 SeitenAuthshield Lab-2 Factor Authentication SolutionsAuthShield LabNoch keine Bewertungen
- Auth Shield - MFID - Secure Access and Authentication SolutionDokument46 SeitenAuth Shield - MFID - Secure Access and Authentication SolutionAuthShield LabNoch keine Bewertungen
- AuthShield-ERP Solution Providers IndiaDokument12 SeitenAuthShield-ERP Solution Providers IndiaAuthShield LabNoch keine Bewertungen
- AuthShield - Two Factor AuthenticationDokument23 SeitenAuthShield - Two Factor AuthenticationAuthShield LabNoch keine Bewertungen
- AuthShield-Information Security Solution ProviderDokument29 SeitenAuthShield-Information Security Solution ProviderAuthShield LabNoch keine Bewertungen
- Auth Shield - Two Factor Authentication Solution Provider Company IndiaDokument2 SeitenAuth Shield - Two Factor Authentication Solution Provider Company IndiaAuthShield LabNoch keine Bewertungen
- AuthShield - Two Factor AuthenticationDokument23 SeitenAuthShield - Two Factor AuthenticationAuthShield LabNoch keine Bewertungen
- Matric Tech Class 9th IoT Software Development - 2Dokument181 SeitenMatric Tech Class 9th IoT Software Development - 2HamzaZahidNoch keine Bewertungen
- MCSL 034 Lab Manual Session - 1: Scope of The Railway Reservation SystemDokument62 SeitenMCSL 034 Lab Manual Session - 1: Scope of The Railway Reservation SystemUjjwal SharmaNoch keine Bewertungen
- DI-604 Cable/DSL Router With 4-Port SwitchDokument2 SeitenDI-604 Cable/DSL Router With 4-Port SwitchRobert VicuñaNoch keine Bewertungen
- 1 - PDFDokument19 Seiten1 - PDFHikka JayasingheNoch keine Bewertungen
- SSH Client and Server GuideDokument12 SeitenSSH Client and Server GuideGhelmez MihaelaNoch keine Bewertungen
- Find and Download Archived Versions of Adobe AIR SDKDokument1 SeiteFind and Download Archived Versions of Adobe AIR SDKFrancisco Javier Andrade CorreaNoch keine Bewertungen
- PSSPI Work Flow: Approved Drawings (Single Line, Schematic Drawings and Required Settings)Dokument1 SeitePSSPI Work Flow: Approved Drawings (Single Line, Schematic Drawings and Required Settings)Noel SantosNoch keine Bewertungen
- Siemens HiPath 4000Dokument6 SeitenSiemens HiPath 4000Rolando MarquesNoch keine Bewertungen
- Event Report Cyber SecurityDokument50 SeitenEvent Report Cyber SecurityEhtisham KhattakNoch keine Bewertungen
- W. Robert-Der Traum Als Naturnothwendigkeit Erklärt-Dertraumalsnatu00unkngoogDokument61 SeitenW. Robert-Der Traum Als Naturnothwendigkeit Erklärt-Dertraumalsnatu00unkngoogLas TorresNoch keine Bewertungen
- Microcomputer Components: 8-Bit CMOS Single-Chip MicrocontrollerDokument62 SeitenMicrocomputer Components: 8-Bit CMOS Single-Chip MicrocontrollerJose CNoch keine Bewertungen
- Dxdiag LumionDokument41 SeitenDxdiag Lumionexodus exodusNoch keine Bewertungen
- MobiKEY Technology Overview Version 4.2.1Dokument10 SeitenMobiKEY Technology Overview Version 4.2.1hxsxaxNoch keine Bewertungen
- Fortinet SMB Vs SonicWALL TZ Series - Talking PointsDokument2 SeitenFortinet SMB Vs SonicWALL TZ Series - Talking PointsMonNoch keine Bewertungen
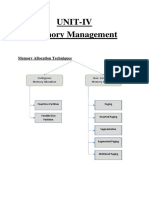
- UNIT 4 Memory ManagementDokument31 SeitenUNIT 4 Memory ManagementMohit SharmaNoch keine Bewertungen
- Pega Admin 1Dokument5 SeitenPega Admin 1Cricket Live StreamingNoch keine Bewertungen
- Mobile IP Overview ExplainedDokument8 SeitenMobile IP Overview ExplainedMaumita ChattopadhyayNoch keine Bewertungen
- Zero-Knowledge Proofs ExplainedDokument22 SeitenZero-Knowledge Proofs ExplainedLyan AnNoch keine Bewertungen
- 1.2 LECTURE Intoduction To ES (ES Component) EC702 ESDokument40 Seiten1.2 LECTURE Intoduction To ES (ES Component) EC702 ESVimoli MehtaNoch keine Bewertungen
- 1 - Database System (Introduction) PDFDokument42 Seiten1 - Database System (Introduction) PDFAllahn GonzalesNoch keine Bewertungen
- BlueCoat PacketShaper 11.10 GuideDokument1.596 SeitenBlueCoat PacketShaper 11.10 GuideArnoldNoch keine Bewertungen
- How Watsco Is Building A New Business Model With Iot: Case StudyDokument8 SeitenHow Watsco Is Building A New Business Model With Iot: Case StudyJasonNoch keine Bewertungen
- MODELS: WEB-600, WEB-600-O, WEB-600-US, WEB-600-O-US: FeaturesDokument4 SeitenMODELS: WEB-600, WEB-600-O, WEB-600-US, WEB-600-O-US: FeaturesJulio SantosNoch keine Bewertungen
- Ed7 NotesDokument2 SeitenEd7 NotesKate FampulmeNoch keine Bewertungen
- AIA Final exam notes summaryDokument4 SeitenAIA Final exam notes summaryViraj Dissanayake100% (1)
- JNTUA IoT TextDocDokument11 SeitenJNTUA IoT TextDocAmbarkar SupriyaNoch keine Bewertungen