Beruflich Dokumente
Kultur Dokumente
Ijettcs 2015 02 19 85
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Ijettcs 2015 02 19 85
Copyright:
Verfügbare Formate
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 4, Issue 1, January-February 2015
ISSN 2278-6856
AN OVERVIEW OF VARIOUS BIOMETRIC
APPROACHES: ECG AS ONE OF ITS
TRAIT
Kavyashree .U1, K.N Deeksha2, Suma Ballal3, Vitina Mary Dsouza4, Rama Moorthy H5
1
Student, CSE, SMVITM-Bantakal, Karnataka, India
Student, CSE, SMVITM-Bantakal, Karnataka, India
Student, CSE, SMVITM-Bantakal, Karnataka, India
Student, CSE, SMVITM-Bantakal, Karnataka, India
Asst. Prof, CSE, SMVITM-Bantakal, Karnataka, India
Abstract
A Bio-metrics system is actually a pattern recognition system
that utilizes various patterns like iris, retina and biological
traits like fingerprint, voice recognition, facial geometry and
hand geometry. What makes Bio-metrics really attractive is
that the various security codes like passwords and ID cards
can be interchanged, stolen or duplicated. To enhance the
security and reliability of the system, physiological traits can
be used. This paper gives the overview of key bio-metric
technologies and basic techniques involved and their
drawbacks. Then the paper illustrates the working of ECG and
the various opportunities for ECG are also mentioned.
Key Words: Bio-metric, recognition methods, access
control, privacy, safety.
1. INTRODUCTION
Biometrics for authentication: Biometrics traits are the
strongest link between a person and his identity as it
cannot be easily shared, lost or duplicated. Hence it is
more resistant to social engineering attacks. This type of
system requires user to be present at the time of
authentication. It can deter user from making false claims.
Hence it can be incorporated in security applications. Law
enforcement agencies in world rely on fingerprints for
criminals and forensic identification. Biometric traits deal
with access control, checking for multiple access control,
international border crossing and secure identification
documents. Each biometric trait has its own advantages
and weak points. The technique of using biometric
methods for identification can be widely applied to
forensics, ATM banking, communication security,
attendance management systems, and access control. It
also plays an important role in enhancing homeland
security.Biometric techniques involve 'metrics' or
measurements of some kind, rather than depending merely
on familiar or hidden methods [8].
Taxonomy of Biometric Techniques given below:
Appearance - These are the physical descriptions like
color of skin or eyes, texture of hair, gender, race,
physical markings, height and weight.
Volume 4, Issue 1, January February 2015
Social behavior -these features correspond to style of
speaking, habituated actions and visible handicaps.
Bio-dynamics - the way, in which a person signs,
rhythm of speaking, keystroke dynamics, particularly
in relation to login-id and password.
Natural physiography These include patterns of
fingerprints, hand geometry, retina, iris, DNA,
earlobes and many more.
Imposed physical characteristics like dog-tags,
collars, bracelets and anklets, bar-codes, embedded
micro-chips [8].
2. BACKGROUND
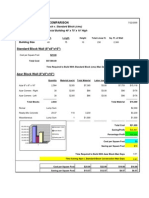
Biometric System: Biometric system is a computer that
implements biometric algorithms and makes use of
sensing, feature extracting and matching modules. The
sensing part captures the traits, feature extraction is done
to eliminate unnecessary information and the matching
modules match the traits with the references stored in the
database. There are two stages in the authentication
process. They are the enrollment and verification as
shown in Fig 2.1. Enrollment is the process of storing the
traits in the database and verification the process of
matching the extracted traits with references in stored in
database.
Fig 2.1: Biometric System [8]
Page 162
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 4, Issue 1, January-February 2015
ISSN 2278-6856
Classification of biometric identification systems:
Biometrics systems is broadly classified into two types
Physical biometrics: It is based on data derived from
direct measurements of parts of the human body.
Fingerprints, iris, retina, hand geometry and facial
recognition are some of the leading physiological
biometrics.
Behavioral characteristics: Identification of the person
is based on his unique behavioral characteristics.
These characteristics can be voice, speech, signature,
and rhythm of typing or an individual's walking style
(gait). Even though the behavioral biometrics is
dependent on the actions of an individual, it is also
influenced by the physical structure of the human
body.
3. VARIOUS BIOMETRICS APPROACHES
Following section lists the various Behavioral Biometrics
approaches,
Keystroke or Typing Recognition:
Keystroke dynamics captures the manner or rhythm
in which a user types characters on keyboard. The
time in which key is pressed is called dwell time and
the time interval between key up and next key
down is called as flight time. This timing data is
recorded. It is then processed using neural algorithms,
which gives us the primary pattern used for future
comparisons.
Speaker or Voice Authentication:
A voice biometric is a numerical representation of the
sound, rhythm, and also pattern of an individuals
voice. A voice biometric or "voice print," is as unique
to an individual as any other biometric methods.
Voice authentication is a fairly simple process. To
register, a user records the sample of his voice and it
is stored in the authenticating system as voiceprint.
If the user wishes to access the resource, a sample of
their voice is given to the system. A comparison is
made
between the input and voiceprint to validate that the
right person is given the access to the resource.
Following section lists the various Physical Biometrics
approaches,
Fingerprint Identification or Recognition:
Fingerprint technology is also known as dactyloscopy.
It is a technique of identification where comparison is
made between two instances of fingerprints to
determine whether they are from same sources. This
technique requires comparing several features of
fingerprints that are found unique for an individual.
The ridges and minutia points are unique for an
individual. The ridges can be of three types: loop,
whirl and arch .Minutia points are specific points on
fingerprints which are critical for identification.
These features of fingers are captured as an image
with help of scanner and is enhanced and converted
to a template. The template is encrypted biometric key
or mathematical information. The image of the
fingerprint is not stored. The algorithm cannot
Volume 4, Issue 1, January February 2015
convert this template back to image. Hence it is
difficult to replicate fingerprints. Scientists have
discovered that the fingerprints are inherited. It is
possible to have a belief that the members of a family
share the same fingerprint pattern.
Hand or Finger Geometry Recognition:
Hand geometry identifies an individual based on the
unique features of the hand. The unique features may
be length of finger, its thickness, the distance between
the finger joints and overall structure of the bone. The
system consists of a camera which captures the image
of the hand. The necessary features are extracted,
processed and stored in the database. These stored
templates can be used later for the purpose of
verification.
Facial Recognition:
Face Recognition systems have the ability to identify
an individual based on the various features on the
face. Human face has several distinguishable features
called the nodal points. There are about 80 different
nodal points on the face. Some of which are the width
of the nose, distance between eyes, length of the
jawline, shape of the face based on cheek bones, depth
of the eye sockets and many more. The positions of
these nodal points are calculated using appropriate
algorithms like PCA and LDA. The emerging trend
in face recognition is 3D face recognition systems
which have better levels of accuracy when compared
to the older systems.
4. DRAWBACKS OF VARIOUS APPROACHES
Drawbacks of various biometric systems are given below:
Fingerprint:
Injuries, traumas, wounds or cuts can make the
fingerprint reading unidentifiable. Distortions due to
grease, dirt or contamination on finger tips have the
chances of the identification to be rejected. Todays
scanners are still not able to differentiate between real
and fake fingerprints. Fake fingerprints can be tricked
using gelatinized molds over real finger
Facial recognition:
Pose variations, ageing are still the limiting factors to
identify the person using face recognition. Use of 2D
scanners cant handle pose variations and are
sensitive to variations in light and shadows. The use
of 3D scanners eliminates these limitations but is
expensive and has time constraints.
Voice recognition:
These systems are susceptible to error in the presence
of noise and external sounds. The distance of the
microphone from the user also affects the accuracy
rates. Prerecorded voice can be used for malicious
access. These systems take time to adjust to the voice
of an individual and require large amount of memory
to store voice files.
Iris and retinal recognition:
The distance of the person from the camera affects the
performance of the system. Errors might occur due to
reflection caused by spectacles, eyelashes or lenses.
Page 163
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 4, Issue 1, January-February 2015
ISSN 2278-6856
During the scanning process the person is required to
remain still. The equipment used is expensive.
Hand geometry based recognition:
Complications might arise when used with certain
populations. There can be a perception of bio- hazard
due to spread of potential germs. Possible changes to
the shape of hands s can cause failure of the system.
Signature
These kinds of systems have the limitation factor of
inconsistent signature. A person without a constant
signature may not be recognized or an individual with
muscular illness may face difficulties in proving their
identification. The quality of ink and paper may also
account for rejections.
Keystroke:
The major drawback is low accuracy rates due to the
varying rhythms of typing. These variations may be
due to injury, fatigue, distractions, and mood or due
to the side effects of drugs, medications or
consumption of alcohol.
DNA recognition:
As it is a very new technology, may not be very
accurate among close relatives and hence less popular
in public. Requires time to process and establish
identity. Requires expensive equipment for processing
and analyzing the samples.
5. ECG AS BIOMETRIC TRAIT
ECG based biometric is a recent topic for research. The
ECG record is a graphical record of electrical impulses of
heart. Electrical activity of the heart is represented by
ECG signal. Capturing the ECG signal without the
cooperation from the person is a difficult task. Hence
cannot be copied easily to provide fake identity. One of the
most important strengths of ECG is that it accounts for the
vitality of a person. Hence it requires that the person has
to be necessarily present at the time of authentication.
All these factors assure better security when compared to
other biometric traits which were discussed earlier. Hence
ECG can become the most promising biometrics in the
near future.
Description of ECG waveforms: The ECG is
characterized by five different segments of the waveform:
the P, Q, R, S and T Waves. [9] The analysis of each
segment gives information about different events of the
cardiac cycle as shown in fig 5.1.
P-wave: It is a small voltage deflection caused due to
atrial depolarization.
QRS-complex: It is the largest amplitude portion of ECG.
It is caused to the currents generated in ventricular
depolarization. It is made of three closely related waves: Q
wave, R wave and the S wave.
T-Wave: It represents ventricular repolarization.
P-Q interval: It is the time interval between the
beginning of P wave and the beginning of QRS complex.
Volume 4, Issue 1, January February 2015
Fig 5.1 ECG cycle with different segments
Features that make ECG unique:
ECG is unique as the morphology and the amplitudes of
the cardiac cycle are dependent on the size, shape and
position of the heart. The most variable factor of heart is
the heartbeat. The normal heart beat of a person is around
60-80 beats/min. This may rise to 200beats/min under
pressure or excitement. This variation may reduce the
diastole duration and ventricular depolarization. It may
also cause the attenuation of the R wave amplitude. But
the duration of QRS complex does not vary significantly.
Generally the raw ECG signal is contaminated by noise
and hence requires preprocessing to remove the
disturbances. Once preprocessing is done, Feature has to
be extracted for the purpose of authentication. The
features that can be extracted are:
Angle features: The angle between PQR, QRS and RST
in the ECG signal can be used.
Interval features: The time interval between two R peaks
can also be used as one of the features. The others are the
time difference between a peak and a valley or between
two peaks or two valleys.
Amplitude features: The difference between the
amplitudes of two peaks or two valleys or one peak and a
valley can be the features extracted for authentication.
The feature to be extracted has to be selected carefully
based on feasibility, consistency and accuracy rates. The
angle and interval features are not constant .This because
of the fact of the heart beat rate changes from a child to an
adult. Hence these features are not suitable. But the
amplitude features do not change with age and remain
almost constant. Hence the amplitude features may be
more suitable for the purpose of authentication.
6. APPLICATIONS OF ECG AS A BIOMETRIC
TRAIT
We have listed following areas where we can have an
authentication process via. ECG.
In attendance management systems usually ID cards
are used for validating the presence of an individual.
It is possible for a person to forget his ID at home but
very unlikely to forget his heart at home. It is also
difficult to make proxy attendance using ECG.
In e-voting machines, ECG can be used as key factor
of single vote. A person can cast single vote. Addition
Page 164
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 4, Issue 1, January-February 2015
ISSN 2278-6856
of fake votes or multiple votes can easily be identified
and rejected.
In locking systems present in mobile phones, house
doors, bank lockers, vehicles etc.
It can be used in the field of telemedicine to monitor a
patients health over long distances using ECG as
identifying factor.
Used in application involving financial transactions
like net banking, ATM systems, online shopping
systems etc.
Used as digital signature to file income tax returns,
eProcurement, eTendering, sending and receiving
encrypted mails etc.
May be used in Aadhar cards. Aadhar is 12 digits
unique ID issued to every citizen of India. This single
source of truth will help in financial inclusions, with
deeper penetration of financial institutions and
smooth error free distributions of governmental
schemes. It card has fingerprints and irises captured.
It is likely to fake these biometric factors. But if ECG
based identification is used it is difficult to clone the
uniqueness of a person.
Can be used as factor of identification of a person in
international border crossing and henceforth avoid
the illegal trespassing, smuggling activities and other
anti-social activities.
Gain access control over data files and computer
programs which contain personal and crucial
information which is of importance to the military,
investigations bureaus, revenue, defense and other
government organizations. It is very important to
maintain secrecy for these agencies.
[4] Nicos
Maglaveras,
TelemachosStamkopoulos,
Konstantinos Diamantaras, Costas Pappas, Michael
Strintzis ECG pattern recognition and classification
using non-linear transformations and neural
networks: A review, International Journal of Medical
Informatics 52 (1998) 191-208
[5] Fahim Sufi, Ibrahim Khalil, and Jiankun Hu, ECGBased Authentication, Chapter 17, Handbook of
Information and Communication Security (Eds.)
[6] [Biometric
authentication]
found
at,
http://www.scholarpedia.org/article/Biometric_authen
tication
[7] Abhishek Kumar Sinha, Financial Transactions get
personalized and secure with biometrics, Digital
Transformation.
[8] P. Sasikala and Dr. R.S.D. Wahidabanu,
Identification
of
Individuals
using
Electrocardiogram, IJCSNS International Journal of
Computer Science and Network Security, VOL.10
No.12, December 2010
[9] Dr.Neil
Townsend,
Medical
Electronics,
Michaelmas Term 2001 found at pno 7
[10] Steven A. Israel, John M. Irvine, Andrew Cheng,
MarkD.Wiederhold, Brenda K. Wiederhold ECG to
identify individuals, PatternRecognition, The journal
of pattern recognition society.
7. CONCLUSION
This paper has evaluated the purpose of using ECG
enabled biometric authentication system. Unlike
conventional biometrics that is neither secure nor robust
enough against falsification, ECG is inherited to an
individual is highly secure and impossible to be forged.
The most important feature of ECG is its real-time feature
of vitality. This ensures that ECG cannot be acquired from
a dead person and compulsorily requires the presence of
the person at the time of authentication. ECG is the most
promising biometric feature due to its uniqueness,
universality and acceptability. The characteristic of
permanence is also a key factor for it to emerge as an
excellent biometric system in the near future
Reference
[1] [Drawbacks of Various Approaches] Found at,
http://biometrics.pbworks.com/w/page/14811349/Adv
antages%20and%20disadvantages%20of%20technolo
gies
[2] [Drawbacks of Various Approaches] Found at,
https://sites.google.com/a/cortland.edu/biometrics/dis
advantages
[3] B Rodger Jamieson, Ph.D., CA, Greg Stephens and
Santhosh Kumar Fingerprint Identification: An Aid
to the Authentication Process, Information Systems
Audit and Control Association.
Volume 4, Issue 1, January February 2015
Page 165
Das könnte Ihnen auch gefallen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Experimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterDokument7 SeitenExperimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- The Mexican Innovation System: A System's Dynamics PerspectiveDokument12 SeitenThe Mexican Innovation System: A System's Dynamics PerspectiveInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (894)
- THE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSDokument7 SeitenTHE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Detection of Malicious Web Contents Using Machine and Deep Learning ApproachesDokument6 SeitenDetection of Malicious Web Contents Using Machine and Deep Learning ApproachesInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- An Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewDokument9 SeitenAn Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Customer Satisfaction A Pillar of Total Quality ManagementDokument9 SeitenCustomer Satisfaction A Pillar of Total Quality ManagementInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- An Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewDokument9 SeitenAn Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Customer Satisfaction A Pillar of Total Quality ManagementDokument9 SeitenCustomer Satisfaction A Pillar of Total Quality ManagementInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Study of Customer Experience and Uses of Uber Cab Services in MumbaiDokument12 SeitenStudy of Customer Experience and Uses of Uber Cab Services in MumbaiInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Experimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterDokument7 SeitenExperimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Detection of Malicious Web Contents Using Machine and Deep Learning ApproachesDokument6 SeitenDetection of Malicious Web Contents Using Machine and Deep Learning ApproachesInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Design and Detection of Fruits and Vegetable Spoiled Detetction SystemDokument8 SeitenDesign and Detection of Fruits and Vegetable Spoiled Detetction SystemInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Analysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyDokument6 SeitenAnalysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- THE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSDokument7 SeitenTHE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- Study of Customer Experience and Uses of Uber Cab Services in MumbaiDokument12 SeitenStudy of Customer Experience and Uses of Uber Cab Services in MumbaiInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Soil Stabilization of Road by Using Spent WashDokument7 SeitenSoil Stabilization of Road by Using Spent WashInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Staycation As A Marketing Tool For Survival Post Covid-19 in Five Star Hotels in Pune CityDokument10 SeitenStaycation As A Marketing Tool For Survival Post Covid-19 in Five Star Hotels in Pune CityInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- Analysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyDokument6 SeitenAnalysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Challenges Faced by Speciality Restaurants in Pune City To Retain Employees During and Post COVID-19Dokument10 SeitenChallenges Faced by Speciality Restaurants in Pune City To Retain Employees During and Post COVID-19International Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Performance of Short Transmission Line Using Mathematical MethodDokument8 SeitenPerformance of Short Transmission Line Using Mathematical MethodInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Impact of Effective Communication To Enhance Management SkillsDokument6 SeitenThe Impact of Effective Communication To Enhance Management SkillsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Digital Record For Privacy and Security in Internet of ThingsDokument10 SeitenA Digital Record For Privacy and Security in Internet of ThingsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Comparative Analysis of Two Biggest Upi Paymentapps: Bhim and Google Pay (Tez)Dokument10 SeitenA Comparative Analysis of Two Biggest Upi Paymentapps: Bhim and Google Pay (Tez)International Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Synthetic Datasets For Myocardial Infarction Based On Actual DatasetsDokument9 SeitenSynthetic Datasets For Myocardial Infarction Based On Actual DatasetsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Advanced Load Flow Study and Stability Analysis of A Real Time SystemDokument8 SeitenAdvanced Load Flow Study and Stability Analysis of A Real Time SystemInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Deep Learning Based Assistant For The Visually ImpairedDokument11 SeitenA Deep Learning Based Assistant For The Visually ImpairedInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Secured Contactless Atm Transaction During Pandemics With Feasible Time Constraint and Pattern For OtpDokument12 SeitenSecured Contactless Atm Transaction During Pandemics With Feasible Time Constraint and Pattern For OtpInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Anchoring of Inflation Expectations and Monetary Policy Transparency in IndiaDokument9 SeitenAnchoring of Inflation Expectations and Monetary Policy Transparency in IndiaInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Impact of Covid-19 On Employment Opportunities For Fresh Graduates in Hospitality &tourism IndustryDokument8 SeitenImpact of Covid-19 On Employment Opportunities For Fresh Graduates in Hospitality &tourism IndustryInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Predicting The Effect of Fineparticulate Matter (PM2.5) On Anecosystemincludingclimate, Plants and Human Health Using MachinelearningmethodsDokument10 SeitenPredicting The Effect of Fineparticulate Matter (PM2.5) On Anecosystemincludingclimate, Plants and Human Health Using MachinelearningmethodsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Cotta Transfer Case Lube PlanDokument3 SeitenCotta Transfer Case Lube PlanMatias Alfredo Contreras KöbrichNoch keine Bewertungen
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- EZ-THUMP™ Series: Portable Fault Location SystemsDokument2 SeitenEZ-THUMP™ Series: Portable Fault Location Systemsriyad abdulhafeedNoch keine Bewertungen
- As 4123.4-2008 Mobile Waste Containers Containers With Four Wheels With A Capacity From 750 L To 1700 L WithDokument7 SeitenAs 4123.4-2008 Mobile Waste Containers Containers With Four Wheels With A Capacity From 750 L To 1700 L WithSAI Global - APACNoch keine Bewertungen
- Cyber Security Research Proposal - SandboxingDokument23 SeitenCyber Security Research Proposal - SandboxingAnonymous Sa6jc83D100% (4)
- 3.17. Creep EquationsDokument10 Seiten3.17. Creep Equationsruchit solankiNoch keine Bewertungen
- Wacker Neuson-Dpu - 25 KNDokument3 SeitenWacker Neuson-Dpu - 25 KNMilutin BožovićNoch keine Bewertungen
- AZAR Block CostcomparisonDokument8 SeitenAZAR Block CostcomparisontckittuNoch keine Bewertungen
- DC DC DC DC Iiii 6 6 6 6: Spec Spec Spec SpecDokument12 SeitenDC DC DC DC Iiii 6 6 6 6: Spec Spec Spec SpecarsolNoch keine Bewertungen
- MI MetadataDokument310 SeitenMI MetadataMatthew McCreadyNoch keine Bewertungen
- FG - BDER-78 Technical Catalogue - Technical - UNDokument8 SeitenFG - BDER-78 Technical Catalogue - Technical - UNAnh Le NgocNoch keine Bewertungen
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- 50TJDokument56 Seiten50TJHansen Henry D'souza100% (2)
- UI Sample ResumeDokument6 SeitenUI Sample ResumenazeerNoch keine Bewertungen
- TMC 421 PDFDokument82 SeitenTMC 421 PDFJamie MooreNoch keine Bewertungen
- 2:4 Decoder: DECODER: A Slightly More Complex Decoder Would Be The N-To-2n Type Binary Decoders. These TypesDokument6 Seiten2:4 Decoder: DECODER: A Slightly More Complex Decoder Would Be The N-To-2n Type Binary Decoders. These TypesPavithraRamNoch keine Bewertungen
- Parts List 8198417 RevCDokument12 SeitenParts List 8198417 RevCSonaina KhanNoch keine Bewertungen
- Strength and Insulating Properties of Building Blocks Made From Waste MaterialsDokument7 SeitenStrength and Insulating Properties of Building Blocks Made From Waste Materialsmjrobust05Noch keine Bewertungen
- GD&T Training Levels and ServicesDokument1 SeiteGD&T Training Levels and ServicesdramiltNoch keine Bewertungen
- Installing RegCM4.3rc Training Session IDokument11 SeitenInstalling RegCM4.3rc Training Session Ijmatias765428100% (1)
- Previews AGA XQ9902 PreDokument6 SeitenPreviews AGA XQ9902 PreAldrin HernandezNoch keine Bewertungen
- How To Install GmtsarDokument24 SeitenHow To Install GmtsardedetmixNoch keine Bewertungen
- Manual Service Aoc - E943fwskDokument51 SeitenManual Service Aoc - E943fwskEduardo BentoNoch keine Bewertungen
- Galvanize Galvanize Business Unit: Trust Us To GalvanizeDokument6 SeitenGalvanize Galvanize Business Unit: Trust Us To GalvanizeAdet WildanNoch keine Bewertungen
- ITU ISUP Release Cause CodesDokument5 SeitenITU ISUP Release Cause Codesdelgado08Noch keine Bewertungen
- Java Topics To Cover in InterviewsDokument5 SeitenJava Topics To Cover in InterviewsHemanth KumarNoch keine Bewertungen
- Technical Presentation - Arik Ethan Kinajil (25231)Dokument5 SeitenTechnical Presentation - Arik Ethan Kinajil (25231)Arik EthanNoch keine Bewertungen
- JUS StandardsDokument28 SeitenJUS StandardsgarejkaNoch keine Bewertungen
- Catalog Advantys AS-I IP20-IP67 - 803510 - DIA3ED2040909EN - 200408Dokument30 SeitenCatalog Advantys AS-I IP20-IP67 - 803510 - DIA3ED2040909EN - 200408Jean MarzanNoch keine Bewertungen
- WATCHDokument9 SeitenWATCHGANTORONoch keine Bewertungen
- Confinement (Book #1 in the Love and Madness series)Von EverandConfinement (Book #1 in the Love and Madness series)Noch keine Bewertungen
- The Voice of God: Experience A Life Changing Relationship with the LordVon EverandThe Voice of God: Experience A Life Changing Relationship with the LordNoch keine Bewertungen