Beruflich Dokumente
Kultur Dokumente
Top 10 Website Security Myths Revealed
Hochgeladen von
Aca Aca AcaCopyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Top 10 Website Security Myths Revealed
Hochgeladen von
Aca Aca AcaCopyright:
Verfügbare Formate
Top 10 Website Security
Myths Revealed
An essential guide from Thawte
WHITE PAPER 2014
Contents:
Introduction 3
Myth #1: Hacking? It wont happen to me!
Myth #2: Security risks can be quantified
Myth #3: Looking after security practices? Thats the CISOs job
Myth #4: SSL is broken 5
Myth #5: I dont store credit card data, so I dont need SSL
Myth #6: All types of certificates issued by a CA are the same, arent they?
Myth #7: Only shady-looking websites are really dangerous. Mines safe and secure
Myth #8: I dont need SSL on all my web pages
Myth #9: I have great anti-virus software on my network, so my systems are safe
Myth #10: We use a firewall, so were well protected against attacks
Living in the Real World 8
More Information 9
About Thawte 9
Top 10 Website Security Myths Revealed
Top 10 Website Security Myths Revealed
Introduction
Protecting your website from hackers is no easy task. There are no days off. The battle is a never-ending one where
one false move, one careless decision or indecision, could mean your website is compromised and breached. And
the upshot of such an invasion? Best case: disruptions to your business while you remove the threats and try to
figure out what went wrong and how to prevent it happening again. Worst case? That your business is seriously
damaged and even put out of action. That is such a startling prospect that surely no one would fail to shore up their
defences to the max, would they? Sadly, they would and do.
In fact, many companies fail to put in place the most fundamental protections to keep themselves safe, often because of the misconceptions and security myths that still prevail around security. Either they believe the most basic
defences are sufficient to keep the enemy outside the gates; or they imagine that they do not have to worry about
hackers. Why? Because the thinking goes like this: No one would go after me! Ive got nothing of value and my business is just too small. Its the big guys the cyber gangs always target. And even if someone did attack my website,
Ive got the best anti-virus there is running on my system and pretty impressive BYOD policies in place, too. Ill be
fine.
The problem is that many businesses, while aware of online threats, have steeped themselves in the mythology that
surrounds website security and simply bury their heads when it comes to the dangers that EVERY business faces.
To be truly safe, they need to move from myth to reality, shoring up their defences, corporate policies, practices
and procedures to the point where they can honestly say: There is no more I can do and then look again and do
even more.
So, lets take a look at those myths and where they fall down.
Myth #1: Hacking? It wont happen to me!
Many people believe their website is such a small fish in the Internet Ocean that no respectable hackers would lower
themselves even to take a look. The problem is that they are now casting their net very wide indeed. If you assume
that your website is always being probed by hackers using scripts, you will be close to the truth.
Perhaps your website really doesnt have any value or maybe the underlying SQL database on your server is fertile
ground for identity theft information. The far more subtle risk to any website hack is the undetected changes the
hacker might make to your site without your knowledge.
Another line of attack that online criminals are now executing is spear phishing where they seek to gain unauthorised access to sensitive data, using faked, but highly credible, emails impersonating a colleague or a bank, for
instance, in order to trick their targets into sharing not only personal data, but also corporate and highly sensitive
information.
But whatever you do, do not believe the size of your business makes a difference to the hackers. The sharks have
you on their radar, however big or small you might be.
Top 10 Website Security Myths Revealed
Myth #2: Security risks can be quantified
This is the rule of thumb myth. You wet your digit, stick it in the air and hope to work out which way the security wind is
blowing. In other words, trying to quantify such risks is all but impossible. How, for example, can you know how much it
might cost you, if your website was to be hacked or your network badly infected? What price would you put upon sensitive
corporate or customer data falling into the wrong hands? How can you measure what the impact will be on your business
and how long it will be before you are back up on your feet after an incident? And what long-term price would anyone set
against a breach that leaves their customers disaffected and taking their business elsewhere?
Imagining you can quantify the impact of the risk to which your organisation is exposed will always be a guesstimate and
often wide of the mark. Moreover, knowing how secure you are can be something of a Catch 22: your security program can
only really be put to the test when a major attack takes place, yet this is something that the program has been designed to
prevent in the first place.
Any business needs some measure of how secure it is, of course, and the best approach is to build your security programs
from the ground up, so you have a comprehensive view of your estate, enabling the business to identify the security strategies and systems most suited to deliver the levels of protection it needs. From these solid foundations, all else can flow.
Myth #3: Looking after security practices? Thats the CISOs job
Its true that the Chief Information Security Officer (CISO) should be the senior-level executive within an organisation
responsible for establishing and maintaining the enterprise vision, strategy and program to ensure information assets
and technologies are adequately protected. But should it be his or her sole responsibility to define and enforce security
practices?
Unloading this responsibility onto one person is not a good idea. Instead, a company should build an information security strategy and process around the specific needs of the business and that means involving a multitude of people
and departments across the organisation.
In the early days of large-scale corporate use of the Internet, many basic technical precautions were not being taken
and the sheer scale of the work to be undertaken in IT seemed to require that Information Security specialisations
existed solely within IT.
However, Information Security is no longer solely a technical problem, but encompasses management of people, process, legal affairs, risk management, public relations, physical security, organisational change and many other areas,
alongside technical management of the threat.
It is also now clear that, with such a complex threat landscape, a risk-managed approach to Information Security is critical. The assessment of such risk requires the involvement of many stakeholders right across the business and, critically,
an individual to manage this process, who might well be the CISO.
Top 10 Website Security Myths Revealed
Myth #4: SSL is broken
The argument that has been going around in some quarters, for some time now, is that the Transport Layer Security
(TLS) or Secure Sockets Layer (SSL) system is indeed broken and past salvaging. That it has run its course, had its
day; simply outlived its usefulness. Many of the anti-SSL camp believe the time has come to replace SSL with a new
system that takes over the mantel of authenticating identities online. In fact, some have even argued that the use of
Certification Authorities (CAs) themselves should be done away with.
Yet this is surely a rush to judgement and rides roughshod over all of the benefits that SSL has delivered for so long.
SSL certificates are widely acknowledged as the worlds most dependable and scalable cryptographic system, so why
are the daggers suddenly out? Yes, there have been high-profile security failures involving SSL of late. But why did
these happen? The easiest scapegoat to point the finger at is SSL, whereas the reality is that these breakdowns were
often due to a lack of appropriate internal security controls at the end-entity level, rather than a system-wide failure.
The real failure to be considered here is the one that might happen if you havent ensured that the right SSL certificate
is taking care of your website. Then it certainly would be broken. They have proved to be a major factor in Internet
security for the best part of two decades and are still by far the most proven, reliable and scalable method to
protect web transactions.
The reality is that SSL is not broken, but very much a key part of any defence strategy.
Myth #5: I dont store credit card data, so I dont need SSL
So your business doesnt store credit card data. That of itself is a good thing, bearing in mind the levels of credit card
fraud that now take place and how often this is linked to identity theft. However, that doesnt automatically make you or
your customers safe. Not storing sensitive financial information might make you feel as though you are better protected
from cyber-attacks, but that is only one aspect of what keeps you secure online.
There are many other ways that cyber attackers can wreak damage on your organisation and its reputation, other than
by stealing financial data, and you need to have the highest levels of protection in place to keep them firmly at bay.
That means having safe and trusted areas for your customers where they know they are out of harms way, as well
as operating the highest levels of security for log-ins and passwords.
Secure areas: these are interactive and personalised portals on a website that provide customers with online
access to sensitive information in a secure and confidential environment. Moreover, this can be restricted to users
with electronic certificates, enforcing another powerful layer of security
Log-ins/Passwords: anyone logging in to your site should be using passwords that are at least 10 characters long
and contain multiple character types, including lowercase, uppercase, numbers and special characters. The harder
a password is to guess or crack with a brute force attack, the safer those customers will be. Login information,
including passwords, should always be unique and never reused across multiple web sites; once such details have
been compromised on one site, other accounts may also be hit and that could be the slippery path to financial loss
and identity theft.
Personal details: such as names, email addresses, contact numbers and mailing addresses. If you collect enough
personal data, identity theft may become a plausible threat to your customers. Take the necessary precautions;
otherwise it can be devastating to your customer and the reputation of your business. More and more customers
are educated online shoppers nowadays and wont buy from you if you dont have an SSL certificate installed on
your website.
Remember: Even if you dont sell online, your customers will appreciate the care you take to protect their personal
data especially where you operate a secure access area on your site.
Top 10 Website Security Myths Revealed
Myth #6: All types of certificates issued by a CA are the same, arent they?
No, they are not. There are several types of certificate on offer and not all can be trusted to the same degree.
Here are the main ones:
Domain Validated (DV) The lowest cost means of securing a website, this does not provide authentication or
validation of the business behind the website.
Organisation Validation (OV) These certificates include full business and company validation from a certificate
authority using currently established and accepted manual vetting processes, but are still not validated to the highest
standards set by the CA/B Forum*.
Extended Validation (EV) EV certificates are fully validated to the meticulous guiding principles set by the CA/B
Forum, providing the highest levels of security and trust to end users.
Always opt for an SSL (Secure Socket Layer) certificate with EV from a globally recognised certificate authority, such as
Thawte. The entire address bar will turn green (for safe), if you are on a site using EV certification. These certificates
guarantee the business is legitimate, whereas many other types are only validated with respect to the domain, but not
the owners and operators of the domain.
With EV, you will know youve made a safe, secure connection to a website when the beginning of the URL changes
from HTTP to HTTPS (with the S standing for Secure). Also, a padlock will be displayed to the left of the address bar
(which will have turned green), showing your customers that the page is using an EV SSL certificate to encrypt all
communications between them and your website.
Trust marks/seals are another important means retailers use to reassure customers that it is safe to shop on your site,
demonstrating they have passed various security and privacy tests. The Thawte Trusted Site Seal, for example, gives
your web site instant credibility in the online world by visually reassuring customers that your sites identity has been
verified and that it is secured with SSL.
* CA/B Forum, an independent standards body that requires in-depth verification of the legality and probity of a company before it is issued with a certificate
Myth #7: Only shady-looking websites are really dangerous. Mines safe and secure
Its a given that, however much money, time and technology you have, your website will never be 100% secure.
Dont imagine what looks okay is okay. Its all about what lies beneath. Hackers are constantly seeking out and
discovering security flaws in systems that were once thought all but impregnable. The time between these discoveries
and the required patch software will make you highly susceptible to a full-on assault. One thing you need to be aware
of is that hackers have already probed your systems, checked out your software and are ready to take advantage of any
zero-day vulnerabilities that might open you up.
Even the simplest websites rely on software - and software is inherently flawed and contains errors or bugs. You should
know the components your website relies on to operate and keep tabs on the known issues, and releases of updates
and patches.
Its common practice to harden, or lock down, access to only the resources that need to be accessed. This should
include the operating system, web server and web application itself. And use strong passwords!
Even though total website security is a myth, the goal should always be to make yours as secure as possible. Attackers
are opportunists, seeking out the path of least resistance, and the harder you make it for them, the more likely they will
move on and find a site that is not as robust as yours is.
Top 10 Website Security Myths Revealed
Myth #8: I dont need SSL on all my web pages.
Many organisations use the SSL/TLS (Secure Socket Layer/ Transport Layer Security) protocol to encrypt the
authentication process when users log in to a website but then fail to encrypt subsequent pages during the users
session. This is not good practice, because intermittent use of SSL protection wont keep users safe in the face of
todays burgeoning online threats.
With the rise of Web 2.0 and social networking, people are spending more and more time online and logged in,
communicating much more than just their credit card numbers. This has seen a surge in cybercriminals targeting
consumers using an attack method called sidejacking that takes advantage of consumers visiting unencrypted HTTP
web pages after they have logged in to a site. Sidejacking allows hackers to intercept cookies (typically used to retain
user specific information such as username, password and session data) where they are transmitted without the
continuous protection of SSL encryption.
If trust is the foundation of the Internet economy, then you need end-to-end security that can help protect every web
page your users visit, not just login pages and shopping carts. Always On SSL is a fundamental, cost-effective security
measure for websites that helps protect the entire user experience from start to finish, making it safer to search,
share and shop online. It is supported as best practice by leading industry players such as Google, Microsoft, PayPal,
Symantec, Facebook and Twitter.
Any company that is serious about protecting their customers and their business reputation will follow their lead and
implement Always On SSL, with SSL certificates from a trusted Certificate Authority.
Myth #9: I have great anti-virus software on my network, so my systems are safe.
Your anti-virus software may well be excellent of itself but that isnt enough of itself. Anyone who thinks AV is still all
they need is, quite bluntly, living in the past. The world has changed and attackers (and malware threats) have moved
on apace, with far too many variants now flying around for traditional signature-based anti-virus products to cope.
As always, while security vendors, IT administrators and end users adapt new measures to block security threats,
attackers are constantly creating new, sophisticated ways to get through their defences. However good your AV might
be, they will target a weakness in the system, network or indeed end users themselves in their mission to break
through.
With brute force threats designed to target different weaknesses on different systems, never using the same technique
twice, its no surprise that AV products, used as the sole or main means of defence, are increasingly failing, causing
costly downtime, clean-up efforts and data loss.
A successful attack can now be the passport to significant revenue streams, and the resources and skills employed to
undermine security defences are formidable, so you can be certain that the tenacity and guile of the cybercriminals will
only increase, too.
For all of these reasons, AV-only is not enough. Companies need comprehensive attack prevention that integrates the
full range of security technologies.
Top 10 Website Security Myths Revealed
Myth #10: We use a firewall, so were well protected against attacks.
This is a myth still rife across many corporations and seems to be based more on some feel good fantasy than fact.
Firewalls are of real value and positioned in front of a web server will certainly control traffic to that server. But that
server will need to see web requests, so these cannot be filtered. Equally, web application firewalls can assist in
protecting known vulnerabilities and unusual traffic, but they cannot normally provide protection against business logic
vulnerabilities, custom code vulnerabilities, valid use that corrupts data and zero day attacks. And while they can be
useful in temporarily filtering traffic when a vulnerability is discovered, they need to be thought of as a temporary fix,
rather than a permanent repair.
Take SQL injections, for example: one the most potent threats to computer security and notoriously hard to detect. They
are popular with hackers, as they can be used to exploit weak security measures in database applications or software,
inputting rogue commands that can tell the application to do something it shouldnt. The most effective of these
injections can wreak havoc on website security, because they can bypass typical login firewalls and send SQL queries
to formerly protected databases.
Whats the answer? Organisations need to utilise more comprehensive security measures that can offer support from
data leaks and awareness, where a threat or system breach occurs. In fact, beyond singular reliance on a firewall,
technologies for perimeter protection are essential to deliver an effective layered defence strategy around security
management.
Living in the Real World
Why do we believe in these myths? Mainly because they make us feel comfortable and are the easy option. No hacker
would bother with little us, Our AV is all we need, Nobody gets past our firewall! is how the thinking goes. But the
false sense of security this rose-tinted view of the world affords is a dangerous thing, as believing in the myth means
taking little or even no further action to shore up your defences, leaving your systems wide open to cyber-attack.
Against the myths, you must set the reality. For example:
In 2013, the personal information of one of every 13 people in the world 552 million was exposed in
cyber-attacks (using 7.16 billion as current world population estimate Symantec Internet Security Threat
Report Vol. 19). Stealing data is big business and protection requires layered security.
Mega Data Breaches - where more than 10 million identities were exposed - went from 1 in 2012 to 8 in
2013 this marks a shift in behaviour from years past
Targeted attacks increased by 91% from 2012.
Meanwhile, the security steps that might once have kept you safe from online threats no longer offer the same levels
of protection. The cybercriminals have moved on at staggering speed. The attack systems they employ are highly
refined and potentially devastating. You need to update your defences as often as the criminals update their attack
mechanisms, because this is a battle for supremacy that can never be won. You can only keep the enemy at bay one
day at a time.
Top 10 Website Security Myths Revealed
Protect data in transit with an SSL certificate
More Information
from Thawte today.
If you have further questions,
or would like to speak with a Sales Advisor,
Not All SSL Is the Same
please feel free to contact us:
We make SSL our business in order to protect
yours. Thawte online security is trusted by
Via phone
millions of people around the world. Here are
US toll-free:
+1 888 484 2983
just a few reasons to switch to Thawte:
UK:
+44 203 450 5486
South Africa: +27 21 819 2800
High- assurance digital certificates
Germany:
+49 69 3807 89081
Global reputation for uncompromised reliability
France:
+33 1 57 32 42 68
Up to 256-bit SSL encryption
World-class, multilingual support
New, lower prices that are within your
sales@thawte.com
security budget
Thawte Trusted Site seal
Visit our website at https://www.thawte.com/ssl
Protect your data, safeguard your business,
and translate trust to your customers with
high-assurance, digital certificates from Thawte.
BUY
TRY
LEARN MORE
Protect your business and translate trust to your customers with high-assurance digital certificates from Thawte, the worlds first international
specialist in online security. Backed by a 17-year track record of stability and reliability, a proven infrastructure, and world-class customer support,
Thawte is the international partner of choice for businesses worldwide.
2014 Thawte, Inc. All rights reserved. Thawte, the Thawte logo, and other trademarks, service marks, and designs are registered or
unregistered trademarks of Thawte, Inc. and its subsidiaries and affiliates in the United States and in foreign countries. All other trademarks
are property of their respective owners.
Das könnte Ihnen auch gefallen
- The Purpose of DreamsDokument8 SeitenThe Purpose of DreamsAca Aca AcaNoch keine Bewertungen
- ScieChimiche GeoMap-WMinfoDokument115 SeitenScieChimiche GeoMap-WMinfoemoscribdNoch keine Bewertungen
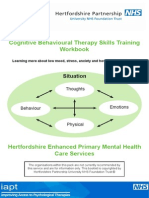
- CBT Workshop Booklet WebDokument52 SeitenCBT Workshop Booklet WebRough Black100% (1)
- NASA Weather Modification 1966Dokument97 SeitenNASA Weather Modification 1966bootlegsaintNoch keine Bewertungen
- Advanced Cybercrime Terrorism ReportDokument14 SeitenAdvanced Cybercrime Terrorism ReportAca Aca AcaNoch keine Bewertungen
- A Link Between Black Holes and The Golden RatioDokument10 SeitenA Link Between Black Holes and The Golden RatioAca Aca AcaNoch keine Bewertungen
- Byod Security That WorksDokument12 SeitenByod Security That WorksAca Aca AcaNoch keine Bewertungen
- Universal Biometric DeviceDokument2 SeitenUniversal Biometric DeviceAca Aca AcaNoch keine Bewertungen
- FDA SecretsDokument16 SeitenFDA SecretsgeorgegeeNoch keine Bewertungen
- A Golden Opportunity For Stock Market InvestorsDokument7 SeitenA Golden Opportunity For Stock Market InvestorsDonlic CarvalhoNoch keine Bewertungen
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Us06-201 843 01 01 02 PDFDokument12 SeitenUs06-201 843 01 01 02 PDFF2CANALESNoch keine Bewertungen
- LG LCD CH La73a 47lc7df UbDokument62 SeitenLG LCD CH La73a 47lc7df UbvideosonNoch keine Bewertungen
- Department of Electrical Engineering: Riphah College of Science & Technology Faculty of Engineering & Applied SciencesDokument5 SeitenDepartment of Electrical Engineering: Riphah College of Science & Technology Faculty of Engineering & Applied SciencesAafaqIqbalNoch keine Bewertungen
- Object-Oriented Programming (OOP) Lecture No. 4Dokument26 SeitenObject-Oriented Programming (OOP) Lecture No. 4Muhammad ZeeshanNoch keine Bewertungen
- Portable Spirometer Using Air Pressure Sensor MPX5500DP Based On Microcontroller Arduino UnoDokument10 SeitenPortable Spirometer Using Air Pressure Sensor MPX5500DP Based On Microcontroller Arduino UnoBiomed TNoch keine Bewertungen
- Digital Platforms PI4 - Planning IntroductionDokument40 SeitenDigital Platforms PI4 - Planning IntroductionMANUEL ANTONIO AVALOS ROSASNoch keine Bewertungen
- Ict in Language TeachingDokument25 SeitenIct in Language TeachingJulie Ann GernaNoch keine Bewertungen
- The Designer's Guide To VHDL (Systems On Silicon)Dokument737 SeitenThe Designer's Guide To VHDL (Systems On Silicon)wagnerprates1608100% (2)
- WT60 Spare PartsDokument11 SeitenWT60 Spare PartsimedNoch keine Bewertungen
- Coal Mine Road Way Support System HandbookDokument76 SeitenCoal Mine Road Way Support System HandbookRANGEROADNoch keine Bewertungen
- Solution Manual For Miller and Freunds P PDFDokument4 SeitenSolution Manual For Miller and Freunds P PDFKuttyNoch keine Bewertungen
- Enable Jumbo Frames For iSCSIDokument1 SeiteEnable Jumbo Frames For iSCSIrshandyNoch keine Bewertungen
- EBSR122 SecurityDokument34 SeitenEBSR122 SecurityrkvenkiNoch keine Bewertungen
- Interpolation Of: Course No: CEE137 Course Name: Numerical AnalysisDokument4 SeitenInterpolation Of: Course No: CEE137 Course Name: Numerical AnalysisMishkat Ahmed NaoshadNoch keine Bewertungen
- Sch-225-E-scd-gen-019 - Cms Rtu 5409 Digital Output Module DatasheetDokument1 SeiteSch-225-E-scd-gen-019 - Cms Rtu 5409 Digital Output Module DatasheetDelshad DuhokiNoch keine Bewertungen
- Network Video Recorder - Quick Start Guide - V1.0.0-EngDokument33 SeitenNetwork Video Recorder - Quick Start Guide - V1.0.0-EngRichard Mark FreoNoch keine Bewertungen
- Automine For Trucks Brochure EnglishDokument4 SeitenAutomine For Trucks Brochure EnglishJH Miguel AngelNoch keine Bewertungen
- DSA ProjectDokument3 SeitenDSA ProjectTARUN SAINoch keine Bewertungen
- Hyg042n10ns1p Hyg042n10ns1bDokument10 SeitenHyg042n10ns1p Hyg042n10ns1brennybenitezNoch keine Bewertungen
- Multi-Label Long Short-Term Memory-Based Framework To Analyze Drug Functions From Biological PropertiesDokument6 SeitenMulti-Label Long Short-Term Memory-Based Framework To Analyze Drug Functions From Biological PropertiesInternational Journal of Innovative Science and Research TechnologyNoch keine Bewertungen
- Use of Data Analytics in Project ManagementDokument12 SeitenUse of Data Analytics in Project ManagementPraful PawarNoch keine Bewertungen
- Mit AcpuDokument30 SeitenMit AcpuThanhtung DangNoch keine Bewertungen
- Restaurant Software BrochureDokument2 SeitenRestaurant Software BrochureKetan ShahaNoch keine Bewertungen
- 7-1B Systems of Linear Equations GraphingDokument23 Seiten7-1B Systems of Linear Equations GraphingDimas HakriNoch keine Bewertungen
- Oracle Exam. 1z0-063.by - Me.249q v.10Dokument97 SeitenOracle Exam. 1z0-063.by - Me.249q v.10Viswa TejaNoch keine Bewertungen
- 7701821350PL AvayaDokument830 Seiten7701821350PL AvayaVincent NormanNoch keine Bewertungen
- Choker Brute - Pathfinder - OGCDokument2 SeitenChoker Brute - Pathfinder - OGCdnddownloaderNoch keine Bewertungen
- Cambridge International A Level: Mathematics 9709/32 May/June 2020Dokument13 SeitenCambridge International A Level: Mathematics 9709/32 May/June 2020redwanNoch keine Bewertungen
- b1b FactbookDokument23 Seitenb1b Factbook连富兴Noch keine Bewertungen