Beruflich Dokumente
Kultur Dokumente
Kern MMGT PDF
Hochgeladen von
VijayaLakshmiOriginalbeschreibung:
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Kern MMGT PDF
Hochgeladen von
VijayaLakshmiCopyright:
Verfügbare Formate
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
Gustavo Duarte (/gustavo/blog/)
brain food for hackers
How the Kernel Manages Your Memory
Feb 3rd, 2009
After examining the virtual address layout (http://duartes.org/gustavo/blog/post/anatomyof-a-program-in-memory) of a process, we turn to the kernel and its mechanisms for managing
user memory. Here is gonzo again:
1 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
Linux processes are implemented in the kernel as instances of task_struct (http://lxr.linux.no
/linux+v2.6.28.1/include/linux/sched.h#L1075), the process descriptor. The mm
(http://lxr.linux.no/linux+v2.6.28.1/include/linux/sched.h#L1129) eld in task_struct points to
the memory descriptor, mm_struct (http://lxr.linux.no/linux+v2.6.28.1/include/linux
/mm_types.h#L173), which is an executive summary of a programs memory. It stores the start
and end of memory segments as shown above, the number (http://lxr.linux.no/linux+v2.6.28.1
/include/linux/mm_types.h#L197) of physical memory pages used by the process (rss stands for
Resident Set Size), the amount (http://lxr.linux.no/linux+v2.6.28.1/include/linux
/mm_types.h#L206) of virtual address space used, and other tidbits. Within the memory
descriptor we also nd the two work horses for managing program memory: the set of virtual
memory areas and the page tables. Gonzos memory areas are shown below:
2 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
Each virtual memory area (VMA) is a contiguous range of virtual addresses; these areas never
overlap. An instance of vm_area_struct (http://lxr.linux.no/linux+v2.6.28.1/include/linux
/mm_types.h#L99) fully describes a memory area, including its start and end addresses, ags
(http://lxr.linux.no/linux+v2.6.28/include/linux/mm.h#L76) to determine access rights and
behaviors, and the vm_le (http://lxr.linux.no/linux+v2.6.28.1/include/linux/mm_types.h#L150)
eld to specify which le is being mapped by the area, if any. A VMA that does not map a le is
anonymous. Each memory segment above (e.g., heap, stack) corresponds to a single VMA, with
the exception of the memory mapping segment. This is not a requirement, though it is usual in
x86 machines. VMAs do not care which segment they are in.
A programs VMAs are stored in its memory descriptor both as a linked list in the mmap
(http://lxr.linux.no/linux+v2.6.28.1/include/linux/mm_types.h#L174) eld, ordered by starting
virtual address, and as a red-black tree (http://en.wikipedia.org/wiki/Red_black_tree) rooted at
the mm_rb (http://lxr.linux.no/linux+v2.6.28.1/include/linux/mm_types.h#L175) eld. The
red-black tree allows the kernel to search quickly for the memory area covering a given virtual
address. When you read le /proc/pid_of_process/maps, the kernel is simply going through
the linked list of VMAs for the process and printing each one (http://lxr.linux.no/linux+v2.6.28.1
/fs/proc/task_mmu.c#L201).
3 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
In Windows, the EPROCESS (http://www.nirsoft.net/kernel_struct/vista/EPROCESS.html) block is
roughly a mix of task_struct and mm_struct. The Windows analog to a VMA is the Virtual
Address Descriptor, or VAD (http://www.nirsoft.net/kernel_struct/vista/MMVAD.html); they are
stored in an AVL tree (http://en.wikipedia.org/wiki/AVL_tree). You know what the funniest thing
about Windows and Linux is? Its the little dierences.
The 4GB virtual address space is divided into pages. x86 processors in 32-bit mode support
page sizes of 4KB, 2MB, and 4MB. Both Linux and Windows map the user portion of the virtual
address space using 4KB pages. Bytes 0-4095 fall in page 0, bytes 4096-8191 fall in page 1, and
so on. The size of a VMA must be a multiple of page size. Heres 3GB of user space in 4KB pages:
The processor consults page tables to translate a virtual address into a physical memory
address. Each process has its own set of page tables; whenever a process switch occurs, page
tables for user space are switched as well. Linux stores a pointer to a process page tables in the
pgd (http://lxr.linux.no/linux+v2.6.28.1/include/linux/mm_types.h#L185) eld of the memory
descriptor. To each virtual page there corresponds one page table entry (PTE) in the page
tables, which in regular x86 paging is a simple 4-byte record shown below:
4 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
Linux has functions to read (http://lxr.linux.no/linux+v2.6.28.1/arch/x86/include
/asm/pgtable.h#L173) and set (http://lxr.linux.no/linux+v2.6.28.1/arch/x86/include
/asm/pgtable.h#L230) each ag in a PTE. Bit P tells the processor whether the virtual page is
present in physical memory. If clear (equal to 0), accessing the page triggers a page fault. Keep
in mind that when this bit is zero, the kernel can do whatever it pleases with the remaining
elds. The R/W ag stands for read/write; if clear, the page is read-only. Flag U/S stands for
user/supervisor; if clear, then the page can only be accessed by the kernel. These ags are used
to implement the read-only memory and protected kernel space we saw before.
Bits D and A are for dirty and accessed. A dirty page has had a write, while an accessed page
has had a write or read. Both ags are sticky: the processor only sets them, they must be
cleared by the kernel. Finally, the PTE stores the starting physical address that corresponds to
this page, aligned to 4KB. This naive-looking eld is the source of some pain, for it limits
addressable physical memory to 4 GB (http://www.google.com/search?hl=en&
q=2^20+*+2^12+bytes+in+GB). The other PTE elds are for another day, as is Physical Address
Extension.
A virtual page is the unit of memory protection because all of its bytes share the U/S and R/W
ags. However, the same physical memory could be mapped by dierent pages, possibly with
dierent protection ags. Notice that execute permissions are nowhere to be seen in the PTE.
This is why classic x86 paging allows code on the stack to be executed, making it easier to
exploit stack buer overows (its still possible to exploit non-executable stacks using returnto-libc (http://en.wikipedia.org/wiki/Return-to-libc_attack) and other techniques). This lack of a
5 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
PTE no-execute ag illustrates a broader fact: permission ags in a VMA may or may not
translate cleanly into hardware protection. The kernel does what it can, but ultimately the
architecture limits what is possible.
Virtual memory doesnt store anything, it simply maps a programs address space onto the
underlying physical memory, which is accessed by the processor as a large block called the
physical address space. While memory operations on the bus are somewhat involved
(http://duartes.org/gustavo/blog/post/getting-physical-with-memory), we can ignore that here
and assume that physical addresses range from zero to the top of available memory in one-byte
increments. This physical address space is broken down by the kernel into page frames. The
processor doesnt know or care about frames, yet they are crucial to the kernel because the
page frame is the unit of physical memory management. Both Linux and Windows use 4KB
page frames in 32-bit mode; here is an example of a machine with 2GB of RAM:
In Linux each page frame is tracked by a descriptor (http://lxr.linux.no/linux+v2.6.28/include
/linux/mm_types.h#L32) and several ags (http://lxr.linux.no/linux+v2.6.28/include/linux/pageags.h#L14). Together these descriptors track the entire physical memory in the computer; the
precise state of each page frame is always known. Physical memory is managed with the buddy
memory allocation (http://en.wikipedia.org/wiki/Buddy_memory_allocation) technique, hence a
6 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
page frame is free if its available for allocation via the buddy system. An allocated page frame
might be anonymous, holding program data, or it might be in the page cache, holding data
stored in a le or block device. There are other exotic page frame uses, but leave them alone for
now. Windows has an analogous Page Frame Number (PFN) database to track physical memory.
Lets put together virtual memory areas, page table entries and page frames to understand how
this all works. Below is an example of a user heap:
Blue rectangles represent pages in the VMA range, while arrows represent page table entries
mapping pages onto page frames. Some virtual pages lack arrows; this means their
corresponding PTEs have the Present ag clear. This could be because the pages have never
been touched or because their contents have been swapped out. In either case access to these
pages will lead to page faults, even though they are within the VMA. It may seem strange for the
VMA and the page tables to disagree, yet this often happens.
A VMA is like a contract between your program and the kernel. You ask for something to be
done (memory allocated, a le mapped, etc.), the kernel says sure, and it creates or updates
the appropriate VMA. But it does not actually honor the request right away, it waits until a page
7 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
fault happens to do real work. The kernel is a lazy, deceitful sack of scum; this is the
fundamental principle of virtual memory. It applies in most situations, some familiar and some
surprising, but the rule is that VMAs record what has been agreed upon, while PTEs reect what
has actually been done by the lazy kernel. These two data structures together manage a
programs memory; both play a role in resolving page faults, freeing memory, swapping
memory out, and so on. Lets take the simple case of memory allocation:
When the program asks for more memory via the brk() (http://www.kernel.org/doc/manpages/online/pages/man2/brk.2.html) system call, the kernel simply updates (http://lxr.linux.no
8 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
/linux+v2.6.28.1/mm/mmap.c#L2050) the heap VMA and calls it good. No page frames are
actually allocated at this point and the new pages are not present in physical memory. Once the
program tries to access the pages, the processor page faults and do_page_fault()
(http://lxr.linux.no/linux+v2.6.28/arch/x86/mm/fault.c#L583) is called. It searches
(http://lxr.linux.no/linux+v2.6.28/arch/x86/mm/fault.c#L692) for the VMA covering the faulted
virtual address using nd_vma() (http://lxr.linux.no/linux+v2.6.28/mm/mmap.c#L1466). If found,
the permissions on the VMA are also checked against the attempted access (read or write). If
theres no suitable VMA, no contract covers the attempted memory access and the process is
punished by Segmentation Fault.
When a VMA is found (http://lxr.linux.no/linux+v2.6.28/arch/x86/mm/fault.c#L711) the kernel
must handle (http://lxr.linux.no/linux+v2.6.28/mm/memory.c#L2653) the fault by looking at the
PTE contents and the type of VMA. In our case, the PTE shows the page is not present
(http://lxr.linux.no/linux+v2.6.28/mm/memory.c#L2674). In fact, our PTE is completely blank (all
zeros), which in Linux means the virtual page has never been mapped. Since this is an
anonymous VMA, we have a purely RAM aair that must be handled by do_anonymous_page()
(http://lxr.linux.no/linux+v2.6.28/mm/memory.c#L2681), which allocates a page frame and
makes a PTE to map the faulted virtual page onto the freshly allocated frame.
Things could have been dierent. The PTE for a swapped out page, for example, has 0 in the
Present ag but is not blank. Instead, it stores the swap location holding the page contents,
which must be read from disk and loaded into a page frame by do_swap_page()
(http://lxr.linux.no/linux+v2.6.28/mm/memory.c#L2280) in what is called a major fault
(http://lxr.linux.no/linux+v2.6.28/mm/memory.c#L2316).
This concludes the rst half of our tour through the kernels user memory management. In the
9 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
next post, well throw les into the mix to build a complete picture of memory fundamentals,
including consequences for performance.
124 Comments (/gustavo/blog/comments/kernel-memory.html)
(//twitter.com(http://feeds.feedburner.com
(mailto:food4hackers@duartes.org)
/food4hackers)
/GustavoDuarte)
Posted by Gustavo Duarte
Feb 3rd, 2009
Internals (/gustavo/blog/category/internals/), Linux
(/gustavo/blog/category/linux/), Software Illustrated (/gustavo/blog/category/software-illustrated/)
Anatomy of a Program in Memory (/gustavo/blog/post/anatomy-of-a-program-in-memory/)
The Thing King (/gustavo/blog/post/the-thing-king/)
Recent Posts
Home Row Computing on Macs (/gustavo/blog/post/home-row-computing-on-mac/)
System Calls Make the World Go Round (/gustavo/blog/post/system-calls/)
What Does an Idle CPU Do? (/gustavo/blog/post/what-does-an-idle-cpu-do/)
When Does Your OS Run? (/gustavo/blog/post/when-does-your-os-run/)
Closures, Objects, and the Fauna of the Heap (/gustavo/blog/post/closures-objects-heap/)
10 of 11
Saturday 25 April 2015 06:12 PM
How the Kernel Manages Your Memory - Gustavo Duarte
http://duartes.org/gustavo/blog/post/how-the-kernel-manages-your...
(/gustavo/blog/about/)
(//twitter.com
(http://feeds.feedburner.com
(mailto:food4hackers@duartes.org)
/food4hackers)
/GustavoDuarte)
Copyright 2008-2014 Gustavo Duarte - Powered by Octopress (http://octopress.org)
11 of 11
Saturday 25 April 2015 06:12 PM
Das könnte Ihnen auch gefallen
- Ext4 Fast FSCK Ted TsoDokument24 SeitenExt4 Fast FSCK Ted TsoVijayaLakshmiNoch keine Bewertungen
- Curtiswrite MC PDFDokument4 SeitenCurtiswrite MC PDFVijayaLakshmiNoch keine Bewertungen
- Android For Work Security White Paper PDFDokument18 SeitenAndroid For Work Security White Paper PDFVijayaLakshmiNoch keine Bewertungen
- Solaris10 Security Dive 20061024Dokument71 SeitenSolaris10 Security Dive 20061024VijayaLakshmiNoch keine Bewertungen
- Macos Kernel in SecurityDokument33 SeitenMacos Kernel in SecurityVijayaLakshmiNoch keine Bewertungen
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- UBD01 - FundamentalsDokument3 SeitenUBD01 - FundamentalsBerce Emanuel-ViniciusNoch keine Bewertungen
- Module1ImplementingServerVirtualizationwithHyper V PDFDokument43 SeitenModule1ImplementingServerVirtualizationwithHyper V PDFMaria PiliNoch keine Bewertungen
- Ultrasonic Glasses For Blinds 3Dokument19 SeitenUltrasonic Glasses For Blinds 3shradha anandNoch keine Bewertungen
- ABX00087 SchematicsDokument2 SeitenABX00087 Schematicsdilip.sharma2005Noch keine Bewertungen
- File DelDokument9 SeitenFile DelGabrielNoch keine Bewertungen
- Bus Impedance Matrix Building Algorithm Illustrated With An ExampleDokument3 SeitenBus Impedance Matrix Building Algorithm Illustrated With An ExampleLangelihle Xaba KingNoch keine Bewertungen
- 820 6551Dokument610 Seiten820 6551Helga TarisznyasNoch keine Bewertungen
- FreeBSD Cheat SheetDokument2 SeitenFreeBSD Cheat Sheetcemerlang satuNoch keine Bewertungen
- Philips 190x6 - 170x6 Service ManualDokument105 SeitenPhilips 190x6 - 170x6 Service ManualzeljavalybiNoch keine Bewertungen
- Micro-Controller Lesson-1Dokument1 SeiteMicro-Controller Lesson-1Engr Shehzad HaneefNoch keine Bewertungen
- FortiSandbox-3.2.2-JSON API ReferenceDokument59 SeitenFortiSandbox-3.2.2-JSON API Reference양현석Noch keine Bewertungen
- Kubernetes 1Dokument3 SeitenKubernetes 1AymenNoch keine Bewertungen
- 7.sap - Abap 2Dokument15 Seiten7.sap - Abap 2mlp mlpNoch keine Bewertungen
- User Guide: Mk5 Gateway Module As Profibus InterfaceDokument27 SeitenUser Guide: Mk5 Gateway Module As Profibus InterfaceErnesto Sta AnaNoch keine Bewertungen
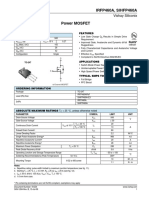
- Vishay IRFP460APBF Datasheet PDFDokument8 SeitenVishay IRFP460APBF Datasheet PDFkamel keddarNoch keine Bewertungen
- Online Complaint Management System PDFDokument67 SeitenOnline Complaint Management System PDFshekhar24Noch keine Bewertungen
- Kumpulan Serial Number Windows XPDokument4 SeitenKumpulan Serial Number Windows XPIbnu Habibi Abdulah MutaqinNoch keine Bewertungen
- Catalogue 2022 r02Dokument22 SeitenCatalogue 2022 r02EmilioGastónNoch keine Bewertungen
- Labsheet 1Dokument4 SeitenLabsheet 1KarthikNoch keine Bewertungen
- Rsa Authentication Manager 8.5 Setup Config GuideDokument120 SeitenRsa Authentication Manager 8.5 Setup Config GuideELias ELNoch keine Bewertungen
- Shenzhen Noridc - BLE Sensor AppDokument54 SeitenShenzhen Noridc - BLE Sensor AppAlina AnaNoch keine Bewertungen
- HomeWork - 05Dokument12 SeitenHomeWork - 05ShantanuNoch keine Bewertungen
- Presonus-Studio One 5 - EffectsDokument6 SeitenPresonus-Studio One 5 - Effectsebursic100% (1)
- Python MCQDokument123 SeitenPython MCQAbhishek Gunjal0% (1)
- Cics Abend CodesDokument825 SeitenCics Abend Codesjoshna30Noch keine Bewertungen
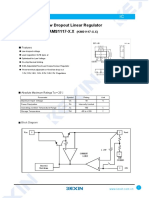
- SMD Type IC: Low Dropout Linear Regulator AMS1117-X.XDokument3 SeitenSMD Type IC: Low Dropout Linear Regulator AMS1117-X.XcarlosmarciosfreitasNoch keine Bewertungen
- Course Instructor Dr.M.K.Kavitha Devi, Professor/CSE, TCEDokument43 SeitenCourse Instructor Dr.M.K.Kavitha Devi, Professor/CSE, TCEbaby sivakumarNoch keine Bewertungen
- HP Compaq Elite 8100Dokument63 SeitenHP Compaq Elite 8100Daniel MoránNoch keine Bewertungen
- Eee PC 1225b Service Manual PDFDokument2 SeitenEee PC 1225b Service Manual PDFaldi 88Noch keine Bewertungen
- ??????? ??? ?????? ?? ???????? ???????? ????? ?????Dokument206 Seiten??????? ??? ?????? ?? ???????? ???????? ????? ?????Abhishek MishraNoch keine Bewertungen