Beruflich Dokumente
Kultur Dokumente
Vulnerability Management
Hochgeladen von
api-25902953Originalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Vulnerability Management
Hochgeladen von
api-25902953Copyright:
Verfügbare Formate
Vulnerability Management
IKON Corporate Security Services
datasheet
IKON Corporate Security Services provides organizations with the ability to reduce
exposure and manage threats by providing a comprehensive suite of security services,
designed to manage the Confidentiality, Integrity and Availability of your data and
services.
A comprehensive Vulnerability Management process involves identifying and quantifying
vulnerabilities across your systems, reducing these vulnerabilities and improving the
capacity to manage future incidents.
IKON Vulnerability Management automates the process of vulnerability management
and policy compliance throughout the enterprise, providing network discovery,
mapping, asset prioritization, vulnerability assessment reporting, remediation and
remediation tracking according to business risk.
Keross offers Corporate Security Services including Vulnerability Management in a
Software-as-a-Service model, allowing our customers to have the same state-of-the-
start enterprise level services at a fraction of the cost.
IKON VM is easily scalable to cover organizations of all sizes and distributed across
multiple geographical locations and sites.
Features
Automate vulnerability identification
Prioritize remediation based on risk to business operations
Document regulatory compliance via automated agent-less auditing
Comprehensive vulnerability KnowledgeBase incorporates thousands of unique checks
Six-sigma accuracy of detection
After-hours, scheduled remediation performed by certified experts
“ IKON VM provides Mondial Assistance Customized reporting & dashboarding
with a 24x7 visibility on security & availability Well defined SLAs and Service Management
of our data. The Keross SOC monitors and
manages our devices round the clock to Benefits
ensure that our systems are scanned,
patched and available securely throughout Manage, reduce & mitigate business risk
the day, while our team focusses on
”
Ensure compliance with laws, regulations and corporate security policies
strategic projects. Measurable ROI with lower OPEX and no CAPEX
— Frederic Jesupret Monthly reports with full status and service summary
Telecom & Security Manager Flexible customer-oriented pricing structure
Mondial Assistance, France Alignment of IT & core business objectives
Business Dashboards
For more information or a free trial, contact us: info@keross.com
© 2010 Keross LLC
datasheet
Vulnerability Management
IKON Corporate Security Services
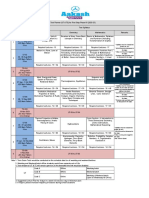
Executive Dashboards & Reports Automated Policy Management
• One quick view to govern real-time exposure • Manage auditing, reporting, compliance needs of PCI, ISO 27001, HIPAA,
• Automated vulnerability trend analysis & differential reports GLBA, SOX, etc
• Export reports to HTML, MHT, PDF, CSV and XML formats • Automated Self-Service Payment Card Industry
and more… • (PCI) compliance certification
24x7 Remediation Management Vulnerability Management Architecture
The Keross Security Operations Center (K-SOC) provides patch
management services to help remediate vulnerabilities and threats.
Automated patch management techniques suffer from a non-human Centralized IT Teams
View dashboards, reports
element and lack of roll back. The K-SOC: Customer Architecture
Receive alerts, remote control
On-site support
• Establishes patch management & mitigation plans
• Determins QA environment for first roll-out of patches
• Monitors QA devices to validate patches 6 AL
ERT
4
ORT S
• Rolls out patches to production S UP
P
• Provides 24x7 service with a pool of 20 experts 1 2 7 1
7 EXTERNAL IP SCANS
Probe + Scanner
Process Quality Management MITI
GATION S,
AL
ERT
S SOC Central Servers
(external VM scanners)
IKON PQM provides a portal for conducting online audit and reporting 5 RE
PORT 3
activities as well as managing and maintaining enterprise progress in End users Keross Security Operations Center
Report analysis, mitigation strategy
terms of regulations, policies and procedures. Progress and performance Remediation of vulnerabilities
can be measured against industry indices and benchmarking, supporting Level I, II, III Support
long-term risk mitigation. All K-SOC activity around Vulnerability
Management is provided within PQM to ensure:
1. Internal/External scanners run non-intrusive scans to detect vulnerabilities
• Enterprise wide monitoring of staff activities related to standards and 2. IKON Managed Services monitor all critical devices while awaiting remeditation
operating procedures 3. K-SOC analyze, provide filtered reports to the customer for validation
• Reporting, tailored to individual roles and functions 4. K-SOC provides mitigation strategy
• Collaborative task management 5. K-SOC remediates vulnerabilities, configuration and permissions, manages patches*
• Ability to publish policies and tasks in multiple languages 6. K-SOC, IT teams maintain availability of devices during remediation process
• Proactive quality assurance 7. Internal/External scanners run second report to validate remediation
Summary of Vulnerabilities Audit Results, Action item Summary
Additional Services
• Web Application Scanning • Mail Security, Archiving Services • Log Management
WAS provides automated crawling & testing for custom web IKON Email Security Services provide high protection IKON SIEM is a comprehensive digital security platform that
applications to identify most vulnerabilities such as those against E-mail, Spam, Virus alongwith Business Continuity uses alarms and indicators to manage & prevent security
in the OWASP Top 10 and WASC Threat Classification, with live archiving, Bandwidth management without risks by collecting & storing logs to analyse any type of
including SQL Injection and Cross-Site Scripting. hardware or software. event.
web www.keross.com twitter @keross
news keross.com/news.html blog keross.com/synchronicity
© 2010 Keross LLC
San Francisco • Paris • Dubai • Kolkata
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Your Free Buyer Persona TemplateDokument8 SeitenYour Free Buyer Persona Templateel_nakdjoNoch keine Bewertungen
- Lite Touch. Completo PDFDokument206 SeitenLite Touch. Completo PDFkerlystefaniaNoch keine Bewertungen
- (Dan Stone) The Historiography of The HolocaustDokument586 Seiten(Dan Stone) The Historiography of The HolocaustPop Catalin100% (1)
- Kormos - Csizer Language Learning 2008Dokument29 SeitenKormos - Csizer Language Learning 2008Anonymous rDHWR8eBNoch keine Bewertungen
- Focus Charting of FDokument12 SeitenFocus Charting of FRobert Rivas0% (2)
- Poet Forugh Farrokhzad in World Poetry PDokument3 SeitenPoet Forugh Farrokhzad in World Poetry Pkarla telloNoch keine Bewertungen
- 576 1 1179 1 10 20181220Dokument15 Seiten576 1 1179 1 10 20181220Sana MuzaffarNoch keine Bewertungen
- Nahs Syllabus Comparative ReligionsDokument4 SeitenNahs Syllabus Comparative Religionsapi-279748131Noch keine Bewertungen
- Large Span Structure: MMBC-VDokument20 SeitenLarge Span Structure: MMBC-VASHFAQNoch keine Bewertungen
- Simple Future Tense & Future Continuous TenseDokument2 SeitenSimple Future Tense & Future Continuous TenseFarris Ab RashidNoch keine Bewertungen
- Term-2 - Grade 8 Science (Biology) Mock Paper-2Dokument3 SeitenTerm-2 - Grade 8 Science (Biology) Mock Paper-2bhagat100% (1)
- Paediatrica Indonesiana: Sumadiono, Cahya Dewi Satria, Nurul Mardhiah, Grace Iva SusantiDokument6 SeitenPaediatrica Indonesiana: Sumadiono, Cahya Dewi Satria, Nurul Mardhiah, Grace Iva SusantiharnizaNoch keine Bewertungen
- Unified Power Quality Conditioner (Upqc) With Pi and Hysteresis Controller For Power Quality Improvement in Distribution SystemsDokument7 SeitenUnified Power Quality Conditioner (Upqc) With Pi and Hysteresis Controller For Power Quality Improvement in Distribution SystemsKANNAN MANINoch keine Bewertungen
- Mathsnacks05 InfiniteDokument1 SeiteMathsnacks05 Infiniteburkard.polsterNoch keine Bewertungen
- SassigbmentDokument7 SeitenSassigbmentFurkaan Ali KhanNoch keine Bewertungen
- SHS11Q4DLP 21st CentFinalDokument33 SeitenSHS11Q4DLP 21st CentFinalNOEMI DE CASTRONoch keine Bewertungen
- Great Is Thy Faithfulness - Gibc Orch - 06 - Horn (F)Dokument2 SeitenGreat Is Thy Faithfulness - Gibc Orch - 06 - Horn (F)Luth ClariñoNoch keine Bewertungen
- Article 1156 Gives The Civil Code Definition of Obligation, in Its Passive Aspect. Our Law MerelyDokument11 SeitenArticle 1156 Gives The Civil Code Definition of Obligation, in Its Passive Aspect. Our Law MerelyFeir, Alexa Mae C.Noch keine Bewertungen
- Motion To Strike BasedDokument16 SeitenMotion To Strike BasedForeclosure Fraud100% (1)
- Problem ManagementDokument33 SeitenProblem Managementdhirajsatyam98982285Noch keine Bewertungen
- Hedonic Calculus Essay - Year 9 EthicsDokument3 SeitenHedonic Calculus Essay - Year 9 EthicsEllie CarterNoch keine Bewertungen
- Calendar of Cases (May 3, 2018)Dokument4 SeitenCalendar of Cases (May 3, 2018)Roy BacaniNoch keine Bewertungen
- Best-First SearchDokument2 SeitenBest-First Searchgabby209Noch keine Bewertungen
- Influencing Factors Behind The Criminal Attitude: A Study of Central Jail PeshawarDokument13 SeitenInfluencing Factors Behind The Criminal Attitude: A Study of Central Jail PeshawarAmir Hamza KhanNoch keine Bewertungen
- UT & TE Planner - AY 2023-24 - Phase-01Dokument1 SeiteUT & TE Planner - AY 2023-24 - Phase-01Atharv KumarNoch keine Bewertungen
- Time Interest Earned RatioDokument40 SeitenTime Interest Earned RatioFarihaFardeenNoch keine Bewertungen
- A Photograph (Q and Poetic Devices)Dokument2 SeitenA Photograph (Q and Poetic Devices)Sanya SadanaNoch keine Bewertungen
- In Mein KampfDokument3 SeitenIn Mein KampfAnonymous t5XUqBNoch keine Bewertungen
- OglalaDokument6 SeitenOglalaNandu RaviNoch keine Bewertungen
- Atul Bisht Research Project ReportDokument71 SeitenAtul Bisht Research Project ReportAtul BishtNoch keine Bewertungen