Beruflich Dokumente
Kultur Dokumente
Cloud Computing
Hochgeladen von
vibhor1990Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Cloud Computing
Hochgeladen von
vibhor1990Copyright:
Verfügbare Formate
CLOUD COMPUTING
Congruent and Converging Forces
that compete
If you accept
There is an unquenchable thirst for
collaboration and sharing
We can work anywhere at any time highly
mobile workforce
You can work wherever you are at home,
traveling, etc.
Then
How do we achieve mission assurance on the same
network?
How do we ensure the network is there when we
need it?
What approach should we take?
Mission
Assurance
Work
Anywhere
at any
time
Sharing
Collaboration
Work
wherever
you are
Cloud Computing
Cloud means Internet. The computing takes place on the Internet
in place of the software you use executing on your desktop pc, its
hosted on the Internet on a server installed in a data centre usually
staffed by people who are experts in managing technology.
Gartner definition
a style of computing where massively scalable IT-enabled
capabilities are delivered as a service to external customers using
Internet technologies
Characteristics
It is sold on demand, typically by the minute or the hour;
it is elastic -- a user can have as much or as little of a service as they
want at any given time
the service is fully managed by the provider (the consumer needs
nothing but a personal computer and Internet access).
Significant innovations in virtualization and distributed computing,
as well as improved access to high-speed Internet and a weak
economy, have accelerated interest in cloud computing.
Private or Public?
A public cloud sells services to anyone on the Internet. (Currently,
Amazon Web Services is the largest public cloud provider.)
A private cloud is a proprietary network or a data center that
supplies hosted services to a limited number of people.
When a service provider uses public cloud resources to create their
private cloud, the result is called a virtual private cloud.
Private or public, the goal of cloud computing is to provide easy,
scalable access to computing resources and IT services.
Infrastructure-as-a-Service
Infrastructure-as-a-Service like Amazon Web Services provides
virtual server instance) to start, stop, access and configure their
virtual servers and storage.
In the enterprise, cloud computing allows a company to pay for
only as much capacity as is needed, and bring more online as soon
as required.
Because this pay-for-what-you-use model resembles the way
electricity, fuel and water are consumed, it's sometimes referred to
as utility computing.
Platform-as-a-service
Platform-as-a-service in the cloud is defined as a set of software and
product development tools hosted on the provider's infrastructure.
Developers create applications on the provider's platform over the
Internet.
PaaS providers may use APIs, website portals or gateway software
installed on the customer's computer. GoogleApps is an example.
Developers need to know that currently, there are not standards for
interoperability or data portability in the cloud. Some providers will
not allow software created by their customers to be moved off the
provider's platform.
Software-as-a-service
In the software-as-a-service cloud model, the vendor supplies the
hardware infrastructure, the software product and interacts with the
user through a front-end portal.
SaaS is a very broad market.
Services can be anything from Web-based email to inventory
control and database processing.
Because the service provider hosts both the application and the data,
the end user is free to use the service from anywhere.
Benefits
Reduced costs: You pay for what you use.
Scalability: You can scale your business storage needs seamlessly
rather than having to go out and purchase expensive programs or
hardware.
Automatic Updates: There is no need for IT to worry about paying
for your future updates in terms of software and hardware.
Remote Access: employees, partners and clients can access, and
update information wherever they are, rather than having to run
back the office.
Contd.
Disaster Relief: With your companys data safely stored on secure
data centers instead of your server room (previously known as your
storage closet), losing power due to hurricanes, earthquakes or a
construction worker cutting the power lines, you are back at work
as long as you have an internet connection.
Ease of Implementation: Your IT team (hopefully older than a 10
year old) may not like this, but implementing cloud services is as
easy as, well, setting up a LinkedIn page.
Skilled Vendors: Who would you rather manage and protect your
data? A company such as InfoStreet (with over 16 years experience
serving enterprise clients), IBM or Amazon or your IT staff.
Contd.
Response Time: Cloud computing accomplishes a better response
time in most cases than your standard server and hardware.
Even playing field for small firms: This allows small companies
to complete more effectively with some of the larger businesses,
balancing the playing field. Your small business can utilize the same
tools that Fortune 100 companies use and can do this because with
cloud computing, your business will only pay for what you need
Cloud Computing Challenges: Dealing with too many
issues
Scalability
Reliability
Billing
Utility & Risk
Management
Programming Env.
& Application Dev.
Software Eng.
Complexity
Uhm, I am not quite
clearYet another
complex IT paradigm?
Reasons to Consider Avoiding Cloud Computing
Security
Data Location & Privacy
Internet Dependency, Performance & Latency
Current Enterprise Applications Can't Be Migrated Easily
Many Cloud Offerings: Good, but new issues-vendor lock in,
scaling across clouds
IBM Cloud
Manjrasoft Aneka
Complex decisions
to make?
Threats, vulnerabilities, and enemies
Goal
Learn the cloud computing threat model by examining the assets,
vulnerabilities, entry points, and actors in a cloud
Technique
Apply different threat modeling schemes
Basic components
Attacker modeling
Choose what attacker to consider
Attacker motivation and capabilities
Assets / Attacker Goals
Vulnerabilities / threats
Who is the attacker?
Insider?
Malicious employees at client
Malicious employees at Cloud provider
Cloud provider itself
Outsider?
Intruders
Network attackers?
Attacker Capability: Malicious Insiders
At client
Learn passwords/authentication information
Gain control of the VMs
At cloud provider
Log client communication
Attacker Capability: Cloud Provider
What?
Can read unencrypted data
Can possibly peek into VMs, or make copies of VMs
Can monitor network communication, application patterns
Attacker motivation: Cloud Provider
Why?
Gain information about client data
Gain information on client behavior
Sell the information or use itself
Why not?
Cheaper to be honest?
Why? (again)
Third party clouds?
Attacker Capability: Outside attacker
What?
Listen to network traffic (passive)
Insert malicious traffic (active)
Probe cloud structure (active)
Launch DoS
Attacker goals: Outside attackers
Intrusion
Network analysis
Man in the middle
Cartography
Assets (Attacker goals)
Confidentiality
Data stored in the cloud
Configuration of VMs running on the cloud
Identity of the cloud users
Location of the VMs running client code
Assets (Attacker goals)
Integrity
Data stored in the cloud
Computations performed on the cloud
Assets (Attacker goals)
Availability
Cloud infrastructure
SaaS/ PaaS
Organizing the threats using STRIDE
Spoofing identity
Tampering with data
Repudiation
Information disclosure
Denial of service
Elevation of privilege
Das könnte Ihnen auch gefallen
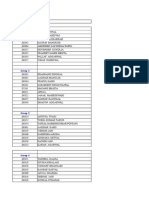
- Group 1: Group / Roll No. NameDokument8 SeitenGroup 1: Group / Roll No. Namevibhor1990Noch keine Bewertungen
- IbsDokument4 SeitenIbsvibhor1990Noch keine Bewertungen
- Cloud ComputingDokument27 SeitenCloud Computingvibhor1990100% (1)
- Ratings Terms You Need To Know FINAL 030509Dokument6 SeitenRatings Terms You Need To Know FINAL 030509vibhor1990Noch keine Bewertungen
- Blue Ocean Red OceanDokument8 SeitenBlue Ocean Red Oceanvibhor1990Noch keine Bewertungen
- TL End Term CaseDokument1 SeiteTL End Term Casevibhor1990Noch keine Bewertungen
- IPL - A Group 9 - FinalDokument8 SeitenIPL - A Group 9 - Finalvibhor1990Noch keine Bewertungen
- Gender Inequality at WorkplacesDokument27 SeitenGender Inequality at Workplacesvibhor1990Noch keine Bewertungen
- Voda India DistributionDokument19 SeitenVoda India Distributionvibhor1990Noch keine Bewertungen
- Marketing Google Case StudyDokument14 SeitenMarketing Google Case Studyvibhor1990Noch keine Bewertungen
- How Maruti Identified A Smart Supply Chain SystemDokument2 SeitenHow Maruti Identified A Smart Supply Chain Systemvibhor1990Noch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Empowerment Technologies: Quarter 1 - Module 2Dokument28 SeitenEmpowerment Technologies: Quarter 1 - Module 2Bernadette Falceso100% (5)
- Explaining WSTR in C RuntimeDokument1 SeiteExplaining WSTR in C RuntimeTiwa MoNoch keine Bewertungen
- Chapter-11 - Designing Effective Output Handout-UpdatedDokument6 SeitenChapter-11 - Designing Effective Output Handout-UpdatedAshique RasoolNoch keine Bewertungen
- Chapter - 3: Loaders & LinkersDokument85 SeitenChapter - 3: Loaders & Linkersswathi SNoch keine Bewertungen
- 2.3.8 Lab - Navigate The IOS by Using Tera Term For Console Connectivity - ILMDokument7 Seiten2.3.8 Lab - Navigate The IOS by Using Tera Term For Console Connectivity - ILMMichael Isael Altamirano CuevaNoch keine Bewertungen
- Pros and Cons of Cryptography, Steganography and Perturbation TechniquesDokument6 SeitenPros and Cons of Cryptography, Steganography and Perturbation Techniquesparitosh chandrakapureNoch keine Bewertungen
- Format of ResumeDokument2 SeitenFormat of Resumeutkarsh_choudhary_1Noch keine Bewertungen
- Motorola G24 Connector Signals (Pinout)Dokument6 SeitenMotorola G24 Connector Signals (Pinout)Руслан МайбородаNoch keine Bewertungen
- Yota PCRF 3.5.2 Product DescriptionDokument37 SeitenYota PCRF 3.5.2 Product Descriptionarun_sakreNoch keine Bewertungen
- Dorks TodayDokument56 SeitenDorks TodayJoao SantosNoch keine Bewertungen
- Kognitio Configuration and Maintenance Manual: Data Classification - PUBLICDokument117 SeitenKognitio Configuration and Maintenance Manual: Data Classification - PUBLICGova Govardhan ReddyNoch keine Bewertungen
- GU 04 Global Supply Chain SecurityDokument2 SeitenGU 04 Global Supply Chain SecurityTanmayNoch keine Bewertungen
- PC Support and Maintenance 1Dokument19 SeitenPC Support and Maintenance 1Kangogo PettNoch keine Bewertungen
- Managing in The Digital World: Chapte RDokument41 SeitenManaging in The Digital World: Chapte RAnoo IamanidzeNoch keine Bewertungen
- It Workshop Lab Manual: Csi Wesley Institute of Tech &SCDokument82 SeitenIt Workshop Lab Manual: Csi Wesley Institute of Tech &SCmr copy xeroxNoch keine Bewertungen
- ISCA MCQs Chapter - 8 Emerging TechnologiesDokument13 SeitenISCA MCQs Chapter - 8 Emerging Technologiesgovarthan1976Noch keine Bewertungen
- Plant SCADA 2020 R2 - Installation GuideDokument159 SeitenPlant SCADA 2020 R2 - Installation GuideD4CONoch keine Bewertungen
- Kali Linux CookbookDokument25 SeitenKali Linux CookbookRob MitchellNoch keine Bewertungen
- Certified List of Candidates: Ilocos Sur - Santa Maria Ilocos Sur - Santa MariaDokument2 SeitenCertified List of Candidates: Ilocos Sur - Santa Maria Ilocos Sur - Santa MariaRussel RamosNoch keine Bewertungen
- ISO 17799 2005.audit ChecklistDokument42 SeitenISO 17799 2005.audit ChecklistDexter TadeoNoch keine Bewertungen
- Cit 0513 Assignment Format - 2Dokument7 SeitenCit 0513 Assignment Format - 2Marco DelarioNoch keine Bewertungen
- Learn PHP From Beginner To Advanced in 6 MonthsDokument3 SeitenLearn PHP From Beginner To Advanced in 6 Monthsajay kumarNoch keine Bewertungen
- Technical Manual: IEI Industrial PC IPC-016Dokument27 SeitenTechnical Manual: IEI Industrial PC IPC-016Mohammed Murtala MohammedNoch keine Bewertungen
- PacFactory User Manual of INGESYSDokument170 SeitenPacFactory User Manual of INGESYSAgung Chrisyancandra MobonguniNoch keine Bewertungen
- Configuration Standart Wifi Office Lt3Dokument3 SeitenConfiguration Standart Wifi Office Lt3M-Rizal Ar AssafNoch keine Bewertungen
- Rust Web ProgrammingDokument395 SeitenRust Web ProgrammingDoug100% (7)
- Dilla University: Industrial Internship ReportDokument53 SeitenDilla University: Industrial Internship Reportanteneh mekonenNoch keine Bewertungen
- Cisco ASA Series Syslog Messages PDFDokument68 SeitenCisco ASA Series Syslog Messages PDFmasterone1810Noch keine Bewertungen
- NSA: Security Highlights of Windows 7Dokument2 SeitenNSA: Security Highlights of Windows 7Brad BeckettNoch keine Bewertungen
- Ubiquitous Computing All AssignmentsDokument6 SeitenUbiquitous Computing All Assignmentsdawokel726Noch keine Bewertungen