Beruflich Dokumente
Kultur Dokumente
Chapter 5 Tracker
Hochgeladen von
kunalmaniyarCopyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Chapter 5 Tracker
Hochgeladen von
kunalmaniyarCopyright:
Verfügbare Formate
Torrents…..
Revolutionised Apportion
CHAPTER 5
TRACKERS
5.1 WHAT IS TRACKER?
A bittorrent tracker is a server that assists in the communication
between peers using the BitTorrent protocol. It is also, in the absence of extensions to the
original protocol, the only major critical point, as clients are required to communicate
with the tracker to initiate downloads. Clients that have already begun downloading also
communicate with the tracker periodically to negotiate with newer peers and provide
statistics; however, after the initial reception of peer data, peer communication can
continue without a tracker.A tracker should be differentiated from a BitTorrent index by
the fact that it does not necessarily list files that are being tracked. A BitTorrent index is a
list of .torrent files, usually including descriptions and other information. Trackers merely
coordinate communication between peers attempting to download the payload of the
torrents.Many BitTorrent websites act as both tracker and index. Sites such as these
publicize the tracker's URL and allow users to upload torrents to the index with the
tracker's URL embedded in them, providing all the features necessary to initiate a
download.
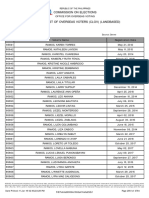
FIG 5.1 ROLE OF TRACKER
5.2 OPEN TRACKERS
Department of Computer Engg 14
AVCOE,Sangamner
Torrents…..Revolutionised Apportion
CHAPTER 5
Open trackers can be used by anyone by adding the tracker address to an existing
torrent, or they can be used by any newly created torrent.
Some of the most popular open trackers include OpenBitTorrent,The HiddenTracker,etc
5.3 PRIVATE TRACKERS
A private tracker is a BitTorrent tracker that restricts use, by requiring users to
register with the site. The method for controlling registration used amongst almost all
private trackers is an invitation system, in which active and contributing members are
given the ability to grant a new user permission to register at the site. Invitations,
typically sent via email or an invite code system, are normally granted to active users
who have uploaded a pre-determined amount or meet specific upload-to-download ratio
requirements. Trading invites for different sites is highly frowned upon in the private
BitTorrent community as it allows anti-piracy groups to infiltrate private trackers more
easily. Most private trackers monitor how much users upload or download, and in most
situations, enforce a minimum upload-to-download ratio.
Some of the allure of private tracker versus a public one are: higher speeds, a
tighter community, and safer downloads. Private trackers implement a strict set of rules,
so generally files containing malware are extremely uncommon. Many private trackers
keep in close contact with each other, so bad users (who trade invites or attempt to fake
their ratio) can be quickly blacklisted. Almost all private trackers implement a passkey
system, where each user is given a personalized announce URL so if there is
unauthorized distribution, it can be pinpointed to the user responsible. Some private
trackers have a higher level of security than others - many sites, such as, the late ScT,
only allow their users to refer to their site as an abbreviation, and never as the site's full
name or URL. Other trackers restrict invites to outstanding members, and many trackers,
to increase security, have gotten rid of the invite system altogether. An example of a
private tracker is pink, which was forcibly shut down in late 2007 by law enforcement
officials.
The downside is that some private trackers are little more than pyramid schemes
inviting donations to enable users to bypass the upload-to-download ratio. In a closed
community it can be mathematically impossible for all members to maintain the required
ratio. Competitions may be offered, with prizes of improved ratios, and forums may
suggest other complicated means of doing this. In the pyramid schemes, 'donations' turn
Department of Computer Engg 14
AVCOE,Sangamner
Torrents…..Revolutionised Apportion
CHAPTER 5
out to be the only way to continue downloading. Downloads can then be quite expensive.
On the other hand, if they are unobtainable elsewhere, they may be good value for
money. Some trackers use "free leech" systems to improve the users ratio. When
downloading a free leech torrent only the upload gets logged in, the download is ignored.
Usually popular (healthy) and large torrents are offered as free leech. Seeding to a ratio of
at least 1 is still recommended even for free leech torrents.
5.4 IMPROVING TORRENT RELIABILITY
Trackers are the primary reason for a damaged BitTorrent 'swarm'. (Other reasons
are mostly related damage or hacked clients uploading corrupt data.) The reliability of
trackers has been improved through two main innovations in the BitTorrent protocol.
Multi-tracker torrents
Multi-tracker torrents feature multiple trackers in a single torrent file. This provides
redundancy in the case that one tracker fails, the other trackers can continue to maintain
the swarm for the torrent. One disadvantage to this that it becomes possible to have
multiple unconnected swarms for a single torrent where some users can connect to one
specific tracker while being unable to connect to another. This can create a disjoint set
which can impede the efficiency of a torrent to transfer the files it describes.
Trackerless torrents
The original BitTorrent client was the first to offer decentralized,distributed tracking
using a distributed hash table (DHT), making torrents more independent from the tracker.
Later, Vuze, rTorrent, µTorrent, BitComet and KTorrent adopted this feature. Vuze's
"Distributed Database" feature uses its own form of DHT (Kademlia) which is
incompatible with the official BitTorrent client's implementation; however, support for
the official implementation can be added through the Mainline DHT plugin. Most other
clients support the official DHT implementation.
5.5 DISTRIBUTED HASH TABLE(DHT)
Department of Computer Engg 15
AVCOE,Sangamner
Torrents…..Revolutionised Apportion
CHAPTER 5
Distributed hash tables (DHTs) are a class of decentralized distributed
systems that provide a lookup service similar to a hash table: (key, value) pairs are stored
in the DHT, and any participating node can efficiently retrieve the value associated with a
given key. Responsibility for maintaining the mapping from keys to values is distributed
among the nodes, in such a way that a change in the set of participants causes a minimal
amount of disruption. This allows DHTs to scale to extremely large numbers of nodes
and to handle continual node arrivals, departures, and failures.
DHTs form an infrastructure that can be used to build more complex services, such
as distributed file systems, peer-to-peer file sharing and content distribution systems,co-
operative caching, multicast, anycast, domain name services, and instant messaging.
Notable distributed networks that use DHTs include BitTorrent's distributed tracker,
the Kad network, the Storm botnet, YaCy, and the Coral Content Distribution Network.
DHTs characteristically emphasize the following properties:
Decentralization: the nodes collectively form the system without any central
coordination.
Scalability: the system should function efficiently even with thousands or millions of
nodes.
Fault tolerance: the system should be reliable (in some sense) even with nodes
continuously joining, leaving, and failing
Department of Computer Engg 15
AVCOE,Sangamner
Das könnte Ihnen auch gefallen
- Bit TorrentDokument15 SeitenBit TorrentHari NathNoch keine Bewertungen
- Cohen - Incentives Build Robustness in BitTorrentDokument5 SeitenCohen - Incentives Build Robustness in BitTorrentanon-355439100% (2)
- Blockchain for Beginners: Understand the Blockchain Basics and the Foundation of Bitcoin and CryptocurrenciesVon EverandBlockchain for Beginners: Understand the Blockchain Basics and the Foundation of Bitcoin and CryptocurrenciesBewertung: 4.5 von 5 Sternen4.5/5 (7)
- Bit TorrentDokument15 SeitenBit Torrentkbrahmateja5940Noch keine Bewertungen
- Bittorrent (Protocol) : File SharingDokument14 SeitenBittorrent (Protocol) : File SharingPremendra YadawNoch keine Bewertungen
- Wolchok PDFDokument9 SeitenWolchok PDFNitin G. TodiNoch keine Bewertungen
- Name Sundas Fatima Id F2017065292 Section W3 Part#1Dokument6 SeitenName Sundas Fatima Id F2017065292 Section W3 Part#1SUNDAS FATIMANoch keine Bewertungen
- Crawling Bittorrent Dhts For Fun and Profit: Scott Wolchok and J. Alex HaldermanDokument9 SeitenCrawling Bittorrent Dhts For Fun and Profit: Scott Wolchok and J. Alex HaldermanreddituserNoch keine Bewertungen
- BIT TorrentDokument15 SeitenBIT TorrentHari NathNoch keine Bewertungen
- Bit TorrentDokument5 SeitenBit Torrentapi-26183726Noch keine Bewertungen
- Torrent DownloadDokument41 SeitenTorrent Downloadkingkumar442Noch keine Bewertungen
- Bit Torrent Full N FinleDokument29 SeitenBit Torrent Full N Finle169Yash GhadiyaNoch keine Bewertungen
- It Torrent Echnology: Done By: Swathi Raman 08D2754Dokument17 SeitenIt Torrent Echnology: Done By: Swathi Raman 08D2754Laxmi DeviNoch keine Bewertungen
- Jss Academy of Technical Education, Noida: Seminar On BittorrentDokument12 SeitenJss Academy of Technical Education, Noida: Seminar On BittorrenthimanshiNoch keine Bewertungen
- Bittorrent Bittorrent: A Peer To Peer File Sharing Protocol A Peer To Peer File Sharing ProtocolDokument35 SeitenBittorrent Bittorrent: A Peer To Peer File Sharing Protocol A Peer To Peer File Sharing ProtocolJay PatelNoch keine Bewertungen
- Bit Torrent Technology: Presentation By: Arya JayachandranDokument29 SeitenBit Torrent Technology: Presentation By: Arya Jayachandransreehari321Noch keine Bewertungen
- Bittorrent: Prepared by Harsh B. BrahmbhattDokument33 SeitenBittorrent: Prepared by Harsh B. Brahmbhattchuck1993Noch keine Bewertungen
- Attacks On Bittorrent: Presented by Andrew SprouseDokument42 SeitenAttacks On Bittorrent: Presented by Andrew SprouseAtul SrivastavaNoch keine Bewertungen
- Technical Presentation On BittorrentDokument29 SeitenTechnical Presentation On BittorrentLaxmi DeviNoch keine Bewertungen
- Bit Torrent REPORTDokument28 SeitenBit Torrent REPORTmehul dholakiyaNoch keine Bewertungen
- How Torrent Downloading WorksDokument2 SeitenHow Torrent Downloading Workstsultim bhutiaNoch keine Bewertungen
- Freenet ReportDokument25 SeitenFreenet ReportArjun JayachandranNoch keine Bewertungen
- BitTorrent DHT Security Assessment Ntms11Dokument6 SeitenBitTorrent DHT Security Assessment Ntms11mehralsmenschNoch keine Bewertungen
- Optimize BitTorrent To Outwit Traffic Shaping ISPsDokument4 SeitenOptimize BitTorrent To Outwit Traffic Shaping ISPsKunal Bhatt100% (6)
- Bit - Torrent.pex IEEE p2pDokument8 SeitenBit - Torrent.pex IEEE p2pdustydiamondNoch keine Bewertungen
- Bittorrent: Presented By: Seminar Guide: Ashish Kumar Ms. Preetha M Kurup Roll No.: 17 Cs - A 'Dokument23 SeitenBittorrent: Presented By: Seminar Guide: Ashish Kumar Ms. Preetha M Kurup Roll No.: 17 Cs - A 'Chinna ParsiNoch keine Bewertungen
- BitTorrent PresentationDokument43 SeitenBitTorrent PresentationNilesh Kumar ParjapatiNoch keine Bewertungen
- Glossary of BitTorrent TermsDokument4 SeitenGlossary of BitTorrent TermsarseniorodNoch keine Bewertungen
- BitTorrent SeminarDokument27 SeitenBitTorrent SeminarjstkiddinNoch keine Bewertungen
- Bit TorrentDokument17 SeitenBit TorrentBiswajit BeheraNoch keine Bewertungen
- Ntorrent: Peer-To-Peer File Sharing in Named Data NetworkingDokument10 SeitenNtorrent: Peer-To-Peer File Sharing in Named Data NetworkingFaisal AlviNoch keine Bewertungen
- Csc523: Analysis of The P2P Bittorrent Protocol: Abram Hindle 0020755 April 16, 2004Dokument19 SeitenCsc523: Analysis of The P2P Bittorrent Protocol: Abram Hindle 0020755 April 16, 2004bluestar25Noch keine Bewertungen
- Lecture 8 (Peer-to-Peer Applications)Dokument11 SeitenLecture 8 (Peer-to-Peer Applications)Abdullah AnwaarNoch keine Bewertungen
- Bit Torrent Protocol) - InformationDokument16 SeitenBit Torrent Protocol) - InformationVinay SinghNoch keine Bewertungen
- BIT TORRENT Dsad.Dokument1 SeiteBIT TORRENT Dsad.Padman MukharjeeNoch keine Bewertungen
- SlideshowDokument14 SeitenSlideshowsawanNoch keine Bewertungen
- The Torrent Guide For Everyone - 24 Pages PDFDokument24 SeitenThe Torrent Guide For Everyone - 24 Pages PDFGlen GadowskiNoch keine Bewertungen
- TorrentDokument16 SeitenTorrentshekharssharmaNoch keine Bewertungen
- BitTorrent-ChainWhitepaper ENDokument8 SeitenBitTorrent-ChainWhitepaper ENMarcos QuadroNoch keine Bewertungen
- Seminar On:: A Peer-To-Peer Network SystemDokument24 SeitenSeminar On:: A Peer-To-Peer Network SystemChinna ParsiNoch keine Bewertungen
- Decentralized File SharingDokument5 SeitenDecentralized File SharingNikhil SahuNoch keine Bewertungen
- Assignment # 3Dokument4 SeitenAssignment # 3Muhammad Tariq Ali NCBA&ENoch keine Bewertungen
- How To Cheat Bittorrent and Why Nobody Does: David Hales Simon PatarinDokument11 SeitenHow To Cheat Bittorrent and Why Nobody Does: David Hales Simon PatarinNirgal SarNoch keine Bewertungen
- TorrentDokument5 SeitenTorrentalysonmicheaalaNoch keine Bewertungen
- Department of Computer Science, Delft University of Technology, The NetherlandsDokument6 SeitenDepartment of Computer Science, Delft University of Technology, The NetherlandsNghĩa ZerNoch keine Bewertungen
- What Are Torrents and How They WorkDokument3 SeitenWhat Are Torrents and How They WorkHelloNoch keine Bewertungen
- Torrent File - Wikipedia, The Free EncyclopediaDokument5 SeitenTorrent File - Wikipedia, The Free EncyclopediaakochaNoch keine Bewertungen
- Torrent ProjectDokument18 SeitenTorrent ProjectRahulNoch keine Bewertungen
- Effective and Secure Content Retrieval in Unstructured P2P Overlay Networks Using Bloom Cast TechniqueDokument6 SeitenEffective and Secure Content Retrieval in Unstructured P2P Overlay Networks Using Bloom Cast TechniqueInternational Journal of computational Engineering research (IJCER)Noch keine Bewertungen
- Enabling Peer Cooperation in Private Local Area Networks Using BittorrentDokument8 SeitenEnabling Peer Cooperation in Private Local Area Networks Using BittorrentKshitij KumarNoch keine Bewertungen
- BittorrentDokument36 SeitenBittorrentSachin AgarwallaNoch keine Bewertungen
- About TorrentsDokument1 SeiteAbout TorrentsthchyNoch keine Bewertungen
- ReadmeDokument3 SeitenReadmePantera IonutNoch keine Bewertungen
- Do Incentives Build Robustness in Bittorrent?Dokument14 SeitenDo Incentives Build Robustness in Bittorrent?Salem Ben NasrNoch keine Bewertungen
- Compromising Tor Anonymity Exploiting P2P Information LeakageDokument11 SeitenCompromising Tor Anonymity Exploiting P2P Information LeakageAnonymous fQSumzNoch keine Bewertungen
- Bit TorrentDokument20 SeitenBit TorrentDaniel BelascuNoch keine Bewertungen
- Solution To Complete Your Torrent Download After The Tracker Goes Down by (Achwaq Khalid)Dokument8 SeitenSolution To Complete Your Torrent Download After The Tracker Goes Down by (Achwaq Khalid)Anurag AgrawalNoch keine Bewertungen
- Blockchain: Real-World Applications And UnderstandingVon EverandBlockchain: Real-World Applications And UnderstandingBewertung: 4 von 5 Sternen4/5 (11)
- Group A14 - AI Parking SystemDokument5 SeitenGroup A14 - AI Parking SystemkunalmaniyarNoch keine Bewertungen
- AbstactDokument1 SeiteAbstactkunalmaniyarNoch keine Bewertungen
- Be Computer Seminar: A Seminar On Biometrics Security SystemDokument22 SeitenBe Computer Seminar: A Seminar On Biometrics Security SystemkunalmaniyarNoch keine Bewertungen
- Outline 1Dokument23 SeitenOutline 1kunalmaniyarNoch keine Bewertungen
- TorrentsDokument19 SeitenTorrentskunalmaniyarNoch keine Bewertungen
- Search EngineDokument20 SeitenSearch EnginekunalmaniyarNoch keine Bewertungen
- Chapter 6 ClientsDokument3 SeitenChapter 6 ClientskunalmaniyarNoch keine Bewertungen
- Chapter 4 TechnicalityDokument5 SeitenChapter 4 TechnicalitykunalmaniyarNoch keine Bewertungen
- Seminar On TorrentsDokument1 SeiteSeminar On TorrentskunalmaniyarNoch keine Bewertungen
- Chapter 2 OperationDokument4 SeitenChapter 2 OperationkunalmaniyarNoch keine Bewertungen
- AcknowledgementDokument1 SeiteAcknowledgementkunalmaniyarNoch keine Bewertungen
- TorrentsDokument1 SeiteTorrentskunalmaniyarNoch keine Bewertungen
- JURNAL - Fis - IIP.59 18 Wid PDokument15 SeitenJURNAL - Fis - IIP.59 18 Wid PDina kartika rayaNoch keine Bewertungen
- Factura 1 2022Dokument188 SeitenFactura 1 2022La Primera La Sonrisa SeNoch keine Bewertungen
- SSL Tls HttpsDokument32 SeitenSSL Tls HttpsShivansh PundirNoch keine Bewertungen
- Ias101 Midterm Lab-Activity-1 PDFDokument2 SeitenIas101 Midterm Lab-Activity-1 PDFCarlo RosallosaNoch keine Bewertungen
- Computer Security and Penetration Testing: Hacking Network DevicesDokument36 SeitenComputer Security and Penetration Testing: Hacking Network DevicesOsei SylvesterNoch keine Bewertungen
- Setup A Taskwarrior ServerDokument14 SeitenSetup A Taskwarrior ServerpolettixNoch keine Bewertungen
- Accounting Information Systems: Fifteenth EditionDokument19 SeitenAccounting Information Systems: Fifteenth Editionsyafiq rossleyNoch keine Bewertungen
- 03-Classical EncryptionDokument43 Seiten03-Classical Encryption6alal Ush100% (1)
- Chapter 11 Security Part 1Dokument29 SeitenChapter 11 Security Part 1AfifaNoch keine Bewertungen
- Question 5 Digital Rights and ResponsibilitiesDokument3 SeitenQuestion 5 Digital Rights and Responsibilitiesapi-320448591Noch keine Bewertungen
- Encryption MethodsDokument14 SeitenEncryption MethodsJaya SudhaNoch keine Bewertungen
- An Effective Mechanism of Access Control With The Ability of Attribute Update and Outsourcing For Cloud ComputingDokument9 SeitenAn Effective Mechanism of Access Control With The Ability of Attribute Update and Outsourcing For Cloud ComputingPraveen KumarNoch keine Bewertungen
- My Research On Cryptographic Protocols: Sreekanth MalladiDokument60 SeitenMy Research On Cryptographic Protocols: Sreekanth MalladiShashank SonarNoch keine Bewertungen
- Cara Hack FBDokument2 SeitenCara Hack FBRoha Sinaga100% (2)
- Network SecurityDokument4 SeitenNetwork SecurityJhansen Feliciano /JHAZPRINT/Noch keine Bewertungen
- Threats To Information SystemDokument26 SeitenThreats To Information SystemswampmasherNoch keine Bewertungen
- Why Organisations Should Be Wary of Maze RansomwareDokument2 SeitenWhy Organisations Should Be Wary of Maze RansomwareNeenu SukumaranNoch keine Bewertungen
- PDF Mutu Pangan Spektral DDDokument14 SeitenPDF Mutu Pangan Spektral DDRafi RidatullahNoch keine Bewertungen
- Chapter Four: E-Commerce Security and CryptographyDokument21 SeitenChapter Four: E-Commerce Security and Cryptographyiyasu ayenekuluNoch keine Bewertungen
- CS361 - CRNS - 22-23 - OBE Format - PracticalListDokument2 SeitenCS361 - CRNS - 22-23 - OBE Format - PracticalListhelloNoch keine Bewertungen
- 4739 1570796983Dokument242 Seiten4739 1570796983JAVIER E. PAREDES B.Noch keine Bewertungen
- Developer Https Asset Pedulilindungi Id CertDokument7 SeitenDeveloper Https Asset Pedulilindungi Id CertIkhsan Dwirana MoetaqienNoch keine Bewertungen
- Kne Twgur Ngns CribdDokument1 SeiteKne Twgur Ngns CribdpolegeNoch keine Bewertungen
- RFC 3647 - Internet X.509 Public Key Infrastructure Certificate Policy and Certification Practices FrameworkDokument93 SeitenRFC 3647 - Internet X.509 Public Key Infrastructure Certificate Policy and Certification Practices FrameworkmohammedNoch keine Bewertungen
- Midterm ITERADokument8 SeitenMidterm ITERAismael delosreyesNoch keine Bewertungen
- ABU DHABI PE R To S - Landbased PDFDokument370 SeitenABU DHABI PE R To S - Landbased PDFRizza CornejoNoch keine Bewertungen
- IronPort PresentationDokument58 SeitenIronPort PresentationVkrishna SoladmNoch keine Bewertungen
- Cisco 700-765 Free Practice Exam & Test Training - ITExams - Com Page1Dokument6 SeitenCisco 700-765 Free Practice Exam & Test Training - ITExams - Com Page1Dark HorizonNoch keine Bewertungen
- Finals Exam in Information Assurance and SecurityDokument3 SeitenFinals Exam in Information Assurance and SecurityJovanna Lagradilla OcampoNoch keine Bewertungen
- MIT15 S12F18 Ses23Dokument20 SeitenMIT15 S12F18 Ses23teo2005Noch keine Bewertungen