Beruflich Dokumente
Kultur Dokumente
Comprehensive Study Effort in Cloud Computing Fog Computing Approach
Hochgeladen von
Editor IJRITCCCopyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Comprehensive Study Effort in Cloud Computing Fog Computing Approach
Hochgeladen von
Editor IJRITCCCopyright:
Verfügbare Formate
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 6
ISSN: 2321-8169
3553 - 3555
_______________________________________________________________________________________________
Comprehensive Study Effort in Cloud Computing : Fog Computing Approach
Azhar L. Inamdar
Prof.Pramod Jadhav
Dept.of Information Technology
BVDUCOEP
Pune, India
azharinamdar99@gmail.com
Dept.of Information Technology
BVDUCOEP
Pune, India
Pramodjadhav1408@gmail.com
Abstract Comprehensive Research work is Integration one more than one technique in securing cloud Environment. Comprehensive
methodology is future generation of approach in any software development or security approach in safeguarding private confidential stats on
cloud platform. Cloud safety is key challenging issue with numerous methods with pros and cons with no perfect methodology so a fusion
approach is been selected. Fog computing initiates s decisive computing mechanism which helps the safekeeping of private documents on cloud
server and a counterattack methodology is been proposed which in a divergent way attacks on attacker. The system integrates SHA1 algorithm
with cloud DeDup technique which keeps a unique copy of every file with better encryption applied other security Mechanics like OTP
generation and sms alert have been provided with set of ten security questions which safe guard the security birch. The proposed system works
for Audio video and document kind of files which is comprehensive plus extended research in base research scholar paper.
Keywordscloud Environment,Fog Computing,Decoy method
________________________________________________*****___________________________________________________
I. INTRODUCTION
Cloud computing is next level of platform technology where in
software and application would be placed on www and used
by numerous user. Cloud provides distributed computing
environment .the upload applications can be used as service or
even computing platforms or as an integrated Infrastructure
that is ISAS PAS & SAS. Today safety of information is
prime objective and goals of any software system. Cloud
numerous approaches and key technologies exists that provide
a fight back to particular security issues only .one technique
for one issue. So we need a technique that is methodology that
can act and provide security against a complete set of security
threats and in all achieve better security measures.
Fog is standard that spreads Cloud work out and
facilities to brink of web. Comparable Fog delivers statistics,
work out, stowage, and solicitation facilities to end-clients.
this section sumptuous incentive and compensations of Fog
and analyses its solicitations in sequence of actual situations,
That as Clever Network, clever transportation lights in
transportation systems and software demarcated systems. This
section elaborates the technology termed fog
Which is under similar canopy of cloud environment. Safety
and discretion subjects are additional revealed rendering to
existing Fog standard. As an instance, we education a
characteristic bout, human-in-central bout, for conversation of
safety in Fog. We explore furtive topographies of bout by
exploratory the environment.
drive Cloud classical develops an effectual substitute to
possessing and handling secluded statistics centers for clients
facing Web requests and collection dispensation. Cloud frees
Initiatives and their end clients from requirement of numerous
particulars that as storing capitals, totaling restraint and
network announcement price. Though, this ecstasy develops a
problematic for dormancy-subtle submissions, that necessitate
bulges in neighborhood to happen their interruption necessities
[5]. When practices and plans of IoT are receiving additional
complex in consumerss life, existing Cloud pattern can barely
content their necessities of flexibility provision, place
consciousness and little dormancy. Fog is planned to discourse
overhead delinquent [5]. As Fog is applied at superiority of
Set-up, it delivers low dormancy, position consciousness, and
Advances excellence-of-services (QoS) for gushing and
existent Period submissions.
II. NECESSITY OF FOG
In previous few decades, Cloud has delivered numerous
Occasions for originalities by subscription their clienteles a
variety of work out facilities. Present reimbursement-as-you-
FIG 1 : FOG AND ITS APPLICATION
3553
IJRITCC | June 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 6
ISSN: 2321-8169
3553 - 3555
_______________________________________________________________________________________________
III. LITERATURE SURVEY
Survey has been document in tabular format to study and
scrutinize the system and find scope and further research space
in domain. Keystone articles from which we form problem
definition are as following.
security questions have been added as security measure next
module sms and OTP generation is security measure been
integrated. User monitoring module with decoy methodology
is next modular development where the system supports in
working for development of text files only. the further module
is SHA1 and MD5 integration with cloud DEDUP
methodology integration from research scholar Pasquale
Puzio article which built better stowage system.
Fig 2: literature table
IV. PROPOSED SYSTEM: IMPLEMENTATION
Fig 4: Better Cloud Stowage scheme
V. RESULTS AND CONCLUSION
Fig 3: Generalized Fog Computing architecture
Proposed system encompasses numerous techniques in
safekeeping
cloud
environment
the
base
model
implementation has been research work of year 2012 and of
research scholar Salvatore J. Stolfo .the cloud environment
we implement a replication strategy that in holds best for loose
of data in cloud environment against insider attack the
research article of author Pasquale Puzio [7] has been
integrated in implementation. The SHA1 algorithm
implementation has been compared in MD5 to implement
better encryption. This proposed work is Fusion f where
F= {integration of all best Techniques at dynamic} to provide
in best security measures to cloud environment. The
implementation sis been divide in seven modules where the
base implementation module starts from development of
Virtual machine environment the user registration and file
uplaoad are base module to be developed ,next module
Fig3 Login screen1
The concluding remark stands that current system which we
have developed is better in so far but we need some
comparative parameters for assessment of system which would
tell us how better is system in terms of what factors and what
is scope of next or changes in same scheme. The system is
been developed in incremental lifecycle with flexibility and
3554
IJRITCC | June 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 6
ISSN: 2321-8169
3553 - 3555
_______________________________________________________________________________________________
scalability in software scheme which makes the system
platform compatible and not dependent on any specific
hardware or software require which is the most important
keystone we achieve after this research work.
Acknowledgment
Special thanks to my guide prof P.A.Jadhav and utterly thanks
to prof.Y.C.kulkarni for kind cooperation and help ultimately
its been light of path shown by head of department
prof.S.Z.Gawali and ultimately Prof.Ananad Balearo thanks to
all of them and by friends and family and all mighty God
References
[1] M. Van Dijk and A. Juels, On the impossibility of cryptography
alone for privacy-preserving cloud computing, in Proceedings
of the 5th USENIX conference on Hot topics in security, ser.
HotSec10. Berkeley, CA, USA: USENIX Association, 2010,
pp. 18
[2] P. Allen, Obamas Twitter password revealed after french
hacker arrested for breaking into U.S. presidents account,
March 2010.
Fig 4: registration window
[3] IM. Ben-Salem and S. J. Stolfo, Modeling user search-behavior
for masquerade detection, in Proceedings of the 14th
International Symposium on Recent Advances in Intrusion
Detection. Heidelberg: Springer, September 2011, pp. 120..
[4] Cloud Security Alliance, Top Threat to Cloud Computing
V1.0,March2010.Available:https://cloudsecurityalliance.org/to
pthreats/csathreats.v1.0.pdf
[5] Sheng Wen Fog Computing Paradigm: Scenarios and Security
Issues Proceedings of the Federated Conference onComputer
Science and Information Systems2014.
[6] Salvatore J. Stolfo, Malek Ben Salem, Angelos D. Keromytis
Fog Computing: Mitigating Insider Data Theft Attacks in the
Cloud, IEEE SYMPOSIUM ON SECURITY AND PRIVACY
WORKSHOP (SPW) YEAR2012.
Fig 5 File upload
[7] ClouDedup: Secure Deduplication with Encryption by Refik
Molva IEEE2013.
3555
IJRITCC | June 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
Das könnte Ihnen auch gefallen
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Importance of Similarity Measures in Effective Web Information RetrievalDokument5 SeitenImportance of Similarity Measures in Effective Web Information RetrievalEditor IJRITCCNoch keine Bewertungen
- A Review of Wearable Antenna For Body Area Network ApplicationDokument4 SeitenA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCNoch keine Bewertungen
- Channel Estimation Techniques Over MIMO-OFDM SystemDokument4 SeitenChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNoch keine Bewertungen
- Regression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeDokument7 SeitenRegression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeEditor IJRITCCNoch keine Bewertungen
- A Review of 2D &3D Image Steganography TechniquesDokument5 SeitenA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNoch keine Bewertungen
- Channel Estimation Techniques Over MIMO-OFDM SystemDokument4 SeitenChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNoch keine Bewertungen
- Comparative Analysis of Hybrid Algorithms in Information HidingDokument5 SeitenComparative Analysis of Hybrid Algorithms in Information HidingEditor IJRITCCNoch keine Bewertungen
- IJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Dokument3 SeitenIJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Editor IJRITCCNoch keine Bewertungen
- Performance Analysis of Image Restoration Techniques at Different NoisesDokument4 SeitenPerformance Analysis of Image Restoration Techniques at Different NoisesEditor IJRITCCNoch keine Bewertungen
- A Study of Focused Web Crawling TechniquesDokument4 SeitenA Study of Focused Web Crawling TechniquesEditor IJRITCCNoch keine Bewertungen
- A Review of 2D &3D Image Steganography TechniquesDokument5 SeitenA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNoch keine Bewertungen
- A Review of Wearable Antenna For Body Area Network ApplicationDokument4 SeitenA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCNoch keine Bewertungen
- Diagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmDokument5 SeitenDiagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmEditor IJRITCCNoch keine Bewertungen
- Modeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleDokument4 SeitenModeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleEditor IJRITCCNoch keine Bewertungen
- Network Approach Based Hindi Numeral RecognitionDokument4 SeitenNetwork Approach Based Hindi Numeral RecognitionEditor IJRITCCNoch keine Bewertungen
- Fuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewDokument4 SeitenFuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewEditor IJRITCCNoch keine Bewertungen
- Efficient Techniques For Image CompressionDokument4 SeitenEfficient Techniques For Image CompressionEditor IJRITCCNoch keine Bewertungen
- 41 1530347319 - 30-06-2018 PDFDokument9 Seiten41 1530347319 - 30-06-2018 PDFrahul sharmaNoch keine Bewertungen
- Prediction of Crop Yield Using LS-SVMDokument3 SeitenPrediction of Crop Yield Using LS-SVMEditor IJRITCCNoch keine Bewertungen
- Itimer: Count On Your TimeDokument4 SeitenItimer: Count On Your Timerahul sharmaNoch keine Bewertungen
- 45 1530697786 - 04-07-2018 PDFDokument5 Seiten45 1530697786 - 04-07-2018 PDFrahul sharmaNoch keine Bewertungen
- Predictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth KotianDokument3 SeitenPredictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth Kotianrahul sharmaNoch keine Bewertungen
- 44 1530697679 - 04-07-2018 PDFDokument3 Seiten44 1530697679 - 04-07-2018 PDFrahul sharmaNoch keine Bewertungen
- Hybrid Algorithm For Enhanced Watermark Security With Robust DetectionDokument5 SeitenHybrid Algorithm For Enhanced Watermark Security With Robust Detectionrahul sharmaNoch keine Bewertungen
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDokument3 SeitenSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaNoch keine Bewertungen
- A Clustering and Associativity Analysis Based Probabilistic Method For Web Page PredictionDokument5 SeitenA Clustering and Associativity Analysis Based Probabilistic Method For Web Page Predictionrahul sharmaNoch keine Bewertungen
- Vehicular Ad-Hoc Network, Its Security and Issues: A ReviewDokument4 SeitenVehicular Ad-Hoc Network, Its Security and Issues: A Reviewrahul sharmaNoch keine Bewertungen
- Image Restoration Techniques Using Fusion To Remove Motion BlurDokument5 SeitenImage Restoration Techniques Using Fusion To Remove Motion Blurrahul sharmaNoch keine Bewertungen
- A Content Based Region Separation and Analysis Approach For Sar Image ClassificationDokument7 SeitenA Content Based Region Separation and Analysis Approach For Sar Image Classificationrahul sharmaNoch keine Bewertungen
- Space Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud DataDokument12 SeitenSpace Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud Datarahul sharmaNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (894)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Manual Hampton Bay Ceiling FanDokument16 SeitenManual Hampton Bay Ceiling FanRafael GarciaNoch keine Bewertungen
- Legal Aspects of Business Communication Call CentersDokument2 SeitenLegal Aspects of Business Communication Call CentersRaj SharmaNoch keine Bewertungen
- MegaMek Scenario DescriptionsDokument5 SeitenMegaMek Scenario Descriptionsrgamer7Noch keine Bewertungen
- Pradeep Kumar: From Nov. 2009Dokument3 SeitenPradeep Kumar: From Nov. 2009Pradeep KumarNoch keine Bewertungen
- الرهن الرسمي العقاري يوسف افريلDokument385 Seitenالرهن الرسمي العقاري يوسف افريلEl MourabitNoch keine Bewertungen
- Dodge Journey 2017 - Owner's ManualDokument510 SeitenDodge Journey 2017 - Owner's Manualandres camachin100% (1)
- Expert Veri Ed, Online, Free.: Custom View SettingsDokument2 SeitenExpert Veri Ed, Online, Free.: Custom View SettingsxaninNoch keine Bewertungen
- Junos Release Notes 12.1Dokument235 SeitenJunos Release Notes 12.1omo-obaNoch keine Bewertungen
- 1.3.1.3 Packet Tracer - Skills Integration Challenge InstructionsDokument2 Seiten1.3.1.3 Packet Tracer - Skills Integration Challenge InstructionsAndrewNoch keine Bewertungen
- Assignment 8Dokument3 SeitenAssignment 8Doris LiuNoch keine Bewertungen
- Textile Wax FF-B NewDokument0 SeitenTextile Wax FF-B NewMuhammad Aasim HassanNoch keine Bewertungen
- San Francisco International Airport and Quantum Secure's SAFE For Aviation SystemDokument20 SeitenSan Francisco International Airport and Quantum Secure's SAFE For Aviation SystemCsarssjNoch keine Bewertungen
- Prinsip Kerja PSVDokument4 SeitenPrinsip Kerja PSVkaltumanikNoch keine Bewertungen
- Queue Tree + MangleDokument2 SeitenQueue Tree + MangleKrisno PratamaNoch keine Bewertungen
- Annexure 7 - Extract of Annual Return: Form No. MGT-9 Registration and Other DetailsDokument1 SeiteAnnexure 7 - Extract of Annual Return: Form No. MGT-9 Registration and Other DetailsJittu Elsa JoseNoch keine Bewertungen
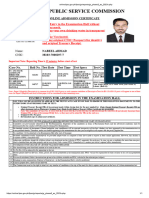
- FPSC (Fia Test)Dokument1 SeiteFPSC (Fia Test)Nabeel AhmadNoch keine Bewertungen
- SSLStrip On Windows-White PaperDokument6 SeitenSSLStrip On Windows-White PaperNilesh KumarNoch keine Bewertungen
- Cisco 800 SeriesDokument8 SeitenCisco 800 SeriesCami DragoiNoch keine Bewertungen
- Cracking and Patching by CHETAN SONIDokument29 SeitenCracking and Patching by CHETAN SONIchetansonihackerNoch keine Bewertungen
- How to apply for an Australian Maritime Crew VisaDokument3 SeitenHow to apply for an Australian Maritime Crew VisaChloe Luiz100% (2)
- Assignment 1 - AWS CLOUDGOAT Iam - Privesc - RollbackDokument2 SeitenAssignment 1 - AWS CLOUDGOAT Iam - Privesc - RollbackKipngeno MosesNoch keine Bewertungen
- Trading in a Global Environment: ISPS Code ImplementationDokument10 SeitenTrading in a Global Environment: ISPS Code ImplementationIkoy Setyawan Keren100% (1)
- Integrating Control and Safety: Where To Draw The Line.: Robin Mccrea-Steele, Invensys-Premier Consulting ServicesDokument6 SeitenIntegrating Control and Safety: Where To Draw The Line.: Robin Mccrea-Steele, Invensys-Premier Consulting ServicesIndranil HatuaNoch keine Bewertungen
- Escalator A17-1 Category 1 TestDokument1 SeiteEscalator A17-1 Category 1 TestUswatun HasanahNoch keine Bewertungen
- D500 GSM ConfigurationDokument20 SeitenD500 GSM ConfigurationCris_eu09Noch keine Bewertungen
- The Untold Story of Silk Road, Part 1Dokument42 SeitenThe Untold Story of Silk Road, Part 1HeartwalkerNoch keine Bewertungen
- U.C. Berkeley Engages FireEye For Advanced Malware ProtectionDokument2 SeitenU.C. Berkeley Engages FireEye For Advanced Malware ProtectionFireEyeNoch keine Bewertungen
- Vivares vs. STC, G.R. No. 202666, September 29, 2014Dokument11 SeitenVivares vs. STC, G.R. No. 202666, September 29, 2014Lou Ann AncaoNoch keine Bewertungen
- Click To Get Netflix Cookies #10Dokument23 SeitenClick To Get Netflix Cookies #10kmkmkmNoch keine Bewertungen
- Cyber Security: Quick Reference GuideDokument3 SeitenCyber Security: Quick Reference GuidesbahourNoch keine Bewertungen