Beruflich Dokumente
Kultur Dokumente
Mitigating Blind Signature Attacks Using Daily Updated Quotes
Hochgeladen von
Editor IJRITCCCopyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Mitigating Blind Signature Attacks Using Daily Updated Quotes
Hochgeladen von
Editor IJRITCCCopyright:
Verfügbare Formate
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1495 1498
_______________________________________________________________________________________________
Mitigating Blind Signature Attacks Using Daily Updated Quotes (DUQ)
S.Kalaiselvi, B.Sathya (PG Student), Ms. A. Priyadharshini, (Assistant Professor)
Computer Science and Engineering,
Knowledge Institute of Technology, Salem,Tamilnadu,India.
Email Id: kalaislv12@gmail.com, sathyacse24@gmail.com, apcse@kiot.ac.in.
Abstract -- To ensure integrity of data, digital signature scheme is used.Blind signature is a popular approach where a third party is used to sign
the message. The blind signature scheme is more vulnerable to attack. If the signature is compromised then the whole system is exposed to the
attacker. In the previous digital signature schemes chakraborty-melta signature scheme is used to generate the blind signature. But the stamp of
the signature z in the algorithm is easy to compute. So there is possiblity for two attacks. Hence, we propose Daily Updated Quotes(DUQ)
Scheme that makes the stamp of the signature diffcult to find by the attacker. Hence, the blind signature is secured for further processing.
Keywords: Blind signature, Elliptic curve, Stamp
__________________________________________*****_________________________________________________
1.
INTRODUCTION
Blind signature scheme is introduced by David
Chaum [3].In a blind signature scheme the content of a
message is blinded before it is signed.
The user sends a message to signer. Then the signer
verifies the message and sends back to the user. After
unbinding, the message gives the blind signature and blind
message.
message
User
Signer
Signature on message
Unlinkable
Signer
The signers signature on message
Fig 1.Blind signature
In general signature generation and verification scheme the
user sends the message to the signature verifier. Message
will be blinded and attacker will crack the message by using
key that he have. Once the message is attacked then it is a
readable message. Finally verifier will verify whether it is
true or false. A secure blind signature scheme satisfies
following three properties:
1) Un-linkable: Attacker cannot get exact message
from the user.
2) Randomized: Enciphers message through randomly
choosing cipher text and it will give the greater
security and it eliminate plaintext attacks.
3) Message recoverable: when network or computer
failure occurs it would not interrupt the message
and it will surely deliver.
Because of the un-linkable and randomized properties
blind signature scheme has been working expansively in
confidentiality oriented applications, such as e-voting
system [5, 8].
Recently, Chakrabortyand Mehta [2] projected blind
signature security established on the elliptic curve discrete
logarithm problem. In this paper, easily A (y,z) can able to
copy and use signature on any message, and after getting a
signature from a signer, A also know the secret of the
signer. Therefore, Chakraborty and Mehta blind signature
scheme cannot be used in e-voting system because it is not
secure.
2.
RELATED WORK
2.1 Elliptic curve group
Let n>3 be a large prime and F n be a finite field.
An elliptic curve H over F n is the set of all points A=(y,z)
that satisfy the equation
z 2 = y 3 + sy + t(modn)
Here s,t F n are constants such that 4s 2 + 27t 2
0, together with an infinity point T. the elliptic curve H can
form a cyclic group under the point addition operation
C=A+B which is defined according to a chord-and-tangent
rule. Particularly, we define x. P=P+P+..+P(x times).
1495
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1495 1498
_______________________________________________________________________________________________
2.2 General security notations of digital signature
scheme
2.4 Cryptanalysis of Chakraborty-mehta signature
scheme
As mentioned previously, a digital signature scheme
must satisfy message recoverable. Here, we list all type of
forgeries of signature schemes:
2.4.1 Attack 1
1) Universal forgery: The creation of a valid
signature for any given message. An adversary
capable of universal forgery is able to sign
messages which he chose himself, messages chosen
at random or even specific messages provided by
an opponent.
2) Selective forgery : The creation of a
message/signature pair. Where message has been
chosen by the adversary prior to the attack.
3) Existential forgery: The creation of at least one
message/signature pair.The adversary need not
have any control over message.
If the malicious user A needs to get the signers
secret key y, then the attacker can do the following steps:
1)
2)
3)
A request a blind signature on a message M. Then
the signer will compute and output signature
(C,v,w) as a response.
After receiving, A computes
h (w).
Finally, the secrete key is obtained as y=v+ h (w).
The attack 1 is successful.we know that the
algorithm sign (v=y-h (w)). The signer secret key y will be
able to generate valid signature of any messages.
If h (w) is known then the secret key will be found.
2.4.2 Attack 2
2.3 Review of Chakraborty-mehta blind scheme
In this section, we briefly review ChakrabortyMehtablind signature scheme.
Let H be a elliptic curve group and A be a generator of H
with order b. The Chakraborty-Mehta blind signature
scheme run as follows.
Setup: Input H, A and b, the algorithm outputs a
cryptographic hash function.
H:{0,1} Zb The signer choose y Zb uniformly at random
and sets (B=yA,y) as its public/private secret key pair.
Blind: The user with message M wants to get a blind
signature on M. He first computes k= h (M) and d=kB, then
sends d to the signer.
Sign: On input d and the secret key y, the signer does the
following steps:
1
1) Compute d=y d=kA.
2) Generate a stamp of the blind signature
[nounce||date||place quote of the day].
3) Compute C=d+ h (w)P and v=y - h(w).
4) Output the signature (C,v,w).
w=
Verify: Input is the message M and the signature(C,v,w),
the verifier accepts the signature if and onlyif the equality
v(A)-B+C=h(m)A holds.
The correctness of the scheme can be verified as follows.
v(A) -B+C
= (y-h (w))A-B+d+h(w)A
=yA-B+d
=d
=h(M)A
If the mean user wants to get message M with valid
signature then, the following steps will be followed:
1) A first produce the signature w= (nounce|| date||
place)
2) Then A compute h(w) and h(M).
3) A selects vZq equally at random.
4) Finally, A computes C=h(M)A+B-v(A), where B is
the signers public key.
The copied signature on M is (C,v,w).
We can see that v (A)-B+C=v(A)-B+ h(M)A+Bv(A)=h(M)A
Therefore the signature (C,v,w) will pass the
verifier proving. That the signature (C,v,w) copied by A is
valid.
3.
PROMOTED WORK
3.1 Daily Updated Quotes(DUQ) Scheme
3.1.1 Selecting expiration dates and using sub keys
By default, a DSA master signing key and an
ElGamal encryption sub-key are generated when a new keypair is created. This is convenient, because the roles of the
two keys are different, therefore the keys need to have
different lifetimes. The master signing key is used to make
digital signatures, and it also collects the signatures of others
who have confirmed the identity. The encryption key is used
only for encrypting and decrypting the encrypted documents
1496
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1495 1498
_______________________________________________________________________________________________
sent to the receiver. To maintain the digital signature for
long period, a key needed to be framed too hard. On the
other hand, the encryption sub-key may be changed
periodically for extra security, since if an encryption key is
broken, the attacker can read all documents encrypted by
that key both in the future and from the past.
In most of the cases we would not use the master
key to expire and it has two reasons for choosing an
expiration date. First, you may intend the key to have a
limited lifetime. For example, it is being used for an event
such as a political campaign and will no longer be useful
after the campaign is over. Another reason is that if you loss
control of the key and do not have a revocation certificate
with which to revoke the key, having an expiration date on
the master key ensures that the key will eventually fall into
disuse.
Changing encryption sub-keys is straight forward
but with be inconvenient. If you generate a new key-pair
with expiration date on the sub-key, that sub-key will
eventually expire. Shortly before the expiration you will add
a new sub-key and publish your updated public key. Once
the sub-key expires, those who wish to correspond with you
must find your updated key since they will no longer be able
to encrypt the expired key. This may be inconvenient
depending on how you distribute the key. Since no extra
signatures are necessary the new sub-key will be signed with
your master signing key, which presumably has already
been validated by your correspondents.
The inconvenience may or may not be worth the
extra security. Just as you can, an attacker can still read all
documents encrypted to an expired sub-key. Changing subkeys only protects future documents. In order to read
documents encrypted to the new sub-key, the attacker would
need to mount a new attack using whatever techniques he
used against you the first time.
Finally, it only makes sense to have one valid
encryption sub-key on a key-ring. There is no additional
security gained by having two or more active sub-keys.
There may of course be any number of expired keys on a
key-ring so that documents encrypted in the past may still be
decrypted, but only one sub-key need to be active at any
given time.
A document's digital signature is the result of
applying a hash function to the document. To be useful,
however, the hash function needs to satisfy two important
properties. First, it should be hard to find two documents
that hash to the same value. Second, given a hash value it
should be hard to recover the documents that have produced
that value.
Some public-key ciphers could be used to sign
documents. The signer encrypts the document with his
private key. Anybody who is willing to check the signatures
can that see the document simply uses the signer's public
key to decrypt the document. This algorithm satisfies the
two properties needed for a good hash function, but in
practice, this algorithm is too slow to be useful.
An alternative is to use hash functions designed to
satisfy these two important properties.
SHA-512(Secure Hash Algorithm)
The SHA loas developed by NIST& published as a
federal information processing standard(FIPS 180) in 1993,
a revised version was issued as FIPS 180-1 in 19952 is
generally to as SHA-1.
SHA-512 is the version of SHA with a 512bitmessage digest. The algorithm takes as input a message
with a maximum length of less than 2128 bits and produces
as output a 512 bit message digest .The input is processed in
1024 bit blocks.
MD5 (Message Digest Version 5)
Using such an algorithm, a document is signed by
hashing it, and the hash value is the signature. Another
person can check the signature by also hashing their copy of
the document and comparing the hash value they got with
the hash value of the original document. If the two hash
values match, it is almost certain that the documents are
identical.
MD5 has been developed by Ron Rivest .It provide
more security MD5 has been Developed. The algorithm
takes as input a message of 512-bit blocks& produces as
output a 128-bit message digest.
4.
CONCLUSION
3.1.2 HASH FUNCTION
A hash function maps an input a variable length
message into a fixed length value, which is called as
message digest or hash value.
Digital signature scheme is more powerful
authentication mechanism and it also addresses integrity
problems. But blind signature scheme is vulnerable to
attack. We proposed a Daily Updated Quotes(DUQ) scheme
which makes the Stamp z of the signature more secure as
1497
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 2 Issue: 6
ISSN: 2321-8169
1495 1498
_______________________________________________________________________________________________
the stamp is encrypted. Hence the blind signature is free
from attacks.
REFERENCES
[1]
[2]
[3]
[4]
[5]
[6]
[7]
[8]
J. Camenisch, J. Piveteau, and M. Stadler, Blind
signatures based on the discrete logarithm problem," in
Eurocrypt '94, LNCS 950, pp. 428-432, Springer-Verlag,
1995.
K. Chakraborty and J. Mehta, A stamped blind signature
scheme based on elliptic curve discrete logarithm
problem," International Journal of Network Security, vol.
14, no. 6, pp. 316-319, 2012.
D. Chaum, Blind signatures for untraceable payments,
in Crypto '82, pp. 199-203, 1983.
S. Goldwasser, S. Micali, and R. Rivest, A digital
signature scheme secure against adaptive chosen
message attacks, SIAM Journal of Computing, vol. 17,
no. 2, pp. 281-308, 1988.
I. Lin, M. Hwang, and C. Chang, Security enhancement
for anonymous secure e-voting over a network,
Computer Standards and Interfaces, vol. 25, no. 2, pp.
131-139, 2003.
T. Okamoto, Efficient blind and partially blind
signatures without random oracles,in The 3rd Theory of
Cryptography Conference, LNCS 3876, pp. 80-99,
Springer-Verlag, 2006.
M. Ruckert, Lattice-based blind signatures, in Asiacrypt '10, LNCS 6477, pp. 413-430, Springer-Verlag,
2010.
F. Rodrguez-Henrquez, D. Ortiz-Arroyo, and C.GarcaZamora, Yet another improvement over the MuVaradharajan
e-voting protocol," Computer Standards
and Interfaces, vol. 29, no. 4, pp. 471-480, 2007.
1498
IJRITCC | June 2014, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
Das könnte Ihnen auch gefallen
- Regression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeDokument7 SeitenRegression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeEditor IJRITCCNoch keine Bewertungen
- A Review of 2D &3D Image Steganography TechniquesDokument5 SeitenA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNoch keine Bewertungen
- Channel Estimation Techniques Over MIMO-OFDM SystemDokument4 SeitenChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNoch keine Bewertungen
- Comparative Analysis of Hybrid Algorithms in Information HidingDokument5 SeitenComparative Analysis of Hybrid Algorithms in Information HidingEditor IJRITCCNoch keine Bewertungen
- Performance Analysis of Image Restoration Techniques at Different NoisesDokument4 SeitenPerformance Analysis of Image Restoration Techniques at Different NoisesEditor IJRITCCNoch keine Bewertungen
- A Review of Wearable Antenna For Body Area Network ApplicationDokument4 SeitenA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCNoch keine Bewertungen
- IJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Dokument3 SeitenIJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Editor IJRITCCNoch keine Bewertungen
- Channel Estimation Techniques Over MIMO-OFDM SystemDokument4 SeitenChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNoch keine Bewertungen
- Efficient Techniques For Image CompressionDokument4 SeitenEfficient Techniques For Image CompressionEditor IJRITCCNoch keine Bewertungen
- A Review of Wearable Antenna For Body Area Network ApplicationDokument4 SeitenA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCNoch keine Bewertungen
- Importance of Similarity Measures in Effective Web Information RetrievalDokument5 SeitenImportance of Similarity Measures in Effective Web Information RetrievalEditor IJRITCCNoch keine Bewertungen
- Network Approach Based Hindi Numeral RecognitionDokument4 SeitenNetwork Approach Based Hindi Numeral RecognitionEditor IJRITCCNoch keine Bewertungen
- Diagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmDokument5 SeitenDiagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmEditor IJRITCCNoch keine Bewertungen
- A Review of 2D &3D Image Steganography TechniquesDokument5 SeitenA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNoch keine Bewertungen
- Modeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleDokument4 SeitenModeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleEditor IJRITCCNoch keine Bewertungen
- Itimer: Count On Your TimeDokument4 SeitenItimer: Count On Your Timerahul sharmaNoch keine Bewertungen
- Fuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewDokument4 SeitenFuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewEditor IJRITCCNoch keine Bewertungen
- A Study of Focused Web Crawling TechniquesDokument4 SeitenA Study of Focused Web Crawling TechniquesEditor IJRITCCNoch keine Bewertungen
- 41 1530347319 - 30-06-2018 PDFDokument9 Seiten41 1530347319 - 30-06-2018 PDFrahul sharmaNoch keine Bewertungen
- Prediction of Crop Yield Using LS-SVMDokument3 SeitenPrediction of Crop Yield Using LS-SVMEditor IJRITCCNoch keine Bewertungen
- Predictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth KotianDokument3 SeitenPredictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth Kotianrahul sharmaNoch keine Bewertungen
- Image Restoration Techniques Using Fusion To Remove Motion BlurDokument5 SeitenImage Restoration Techniques Using Fusion To Remove Motion Blurrahul sharmaNoch keine Bewertungen
- 44 1530697679 - 04-07-2018 PDFDokument3 Seiten44 1530697679 - 04-07-2018 PDFrahul sharmaNoch keine Bewertungen
- 45 1530697786 - 04-07-2018 PDFDokument5 Seiten45 1530697786 - 04-07-2018 PDFrahul sharmaNoch keine Bewertungen
- Hybrid Algorithm For Enhanced Watermark Security With Robust DetectionDokument5 SeitenHybrid Algorithm For Enhanced Watermark Security With Robust Detectionrahul sharmaNoch keine Bewertungen
- Vehicular Ad-Hoc Network, Its Security and Issues: A ReviewDokument4 SeitenVehicular Ad-Hoc Network, Its Security and Issues: A Reviewrahul sharmaNoch keine Bewertungen
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDokument3 SeitenSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaNoch keine Bewertungen
- Space Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud DataDokument12 SeitenSpace Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud Datarahul sharmaNoch keine Bewertungen
- A Clustering and Associativity Analysis Based Probabilistic Method For Web Page PredictionDokument5 SeitenA Clustering and Associativity Analysis Based Probabilistic Method For Web Page Predictionrahul sharmaNoch keine Bewertungen
- A Content Based Region Separation and Analysis Approach For Sar Image ClassificationDokument7 SeitenA Content Based Region Separation and Analysis Approach For Sar Image Classificationrahul sharmaNoch keine Bewertungen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- PAN OS 6.0 Admin GuideDokument522 SeitenPAN OS 6.0 Admin GuideawaraarawaNoch keine Bewertungen
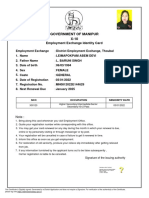
- Government of Manipur X-10: Employment Exchange Identity CardDokument1 SeiteGovernment of Manipur X-10: Employment Exchange Identity CardNongmaithem Bilash SinghNoch keine Bewertungen
- IAPP Certification Foundation Study Guide OverviewDokument13 SeitenIAPP Certification Foundation Study Guide OverviewRenato Leite Monteiro33% (3)
- Gujarath University - 5 Yr Integrated Program in Animation (B.SC & M.SC) DSNKDokument20 SeitenGujarath University - 5 Yr Integrated Program in Animation (B.SC & M.SC) DSNKVivek AdajaniaNoch keine Bewertungen
- VPN JUNIPER-FORTI v2Dokument5 SeitenVPN JUNIPER-FORTI v2Alberto Huamani CanchizNoch keine Bewertungen
- Itu-T: Technical SpecificationDokument18 SeitenItu-T: Technical SpecificationgbungerNoch keine Bewertungen
- 1.3.6 Packet Tracer Configure SSHDokument4 Seiten1.3.6 Packet Tracer Configure SSHleon MuñozNoch keine Bewertungen
- Web Services Security Chapter 8Dokument36 SeitenWeb Services Security Chapter 8Aishwarya RautNoch keine Bewertungen
- Critical Infrastructure Security and ResilienceDokument311 SeitenCritical Infrastructure Security and ResilienceOmotayo Joseph OladapoNoch keine Bewertungen
- Sample Report Email Risk AssessmentDokument10 SeitenSample Report Email Risk AssessmentTarmin AbdulghaniNoch keine Bewertungen
- Implementing A Real-Time Cyber-Physical System Test Bed in RTDS and OPNETDokument6 SeitenImplementing A Real-Time Cyber-Physical System Test Bed in RTDS and OPNETBo ChenNoch keine Bewertungen
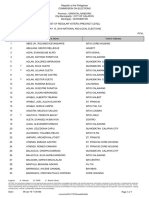
- Philippine voter list for Guinobatan precinctDokument74 SeitenPhilippine voter list for Guinobatan precinctAngelika CalingasanNoch keine Bewertungen
- Lab Exercise - Lesson 7Dokument2 SeitenLab Exercise - Lesson 7Corrales Briyan JoyNoch keine Bewertungen
- ITSY 2401 - Firewalls and Network Security - Network Security Plan ProjectDokument7 SeitenITSY 2401 - Firewalls and Network Security - Network Security Plan ProjectKyle LaPatoNoch keine Bewertungen
- Nouveau Document TexteDokument6 SeitenNouveau Document Texteamal mallouliNoch keine Bewertungen
- Alfresco Security Best Practices - Guide PDFDokument55 SeitenAlfresco Security Best Practices - Guide PDFWilliam SilvaNoch keine Bewertungen
- A Steganography LSB Technique For Hiding Image Within Image Using Blowfish Encryption AlgorithmDokument6 SeitenA Steganography LSB Technique For Hiding Image Within Image Using Blowfish Encryption AlgorithmInternational Journal of Research in Engineering and ScienceNoch keine Bewertungen
- Advantages and Disadvantages of Authentication ToolsDokument2 SeitenAdvantages and Disadvantages of Authentication Toolsnayr44100% (1)
- RRS DFD Diagrams FinalDokument7 SeitenRRS DFD Diagrams FinalYesu RajNoch keine Bewertungen
- CSOE Certification Steps 1 PDFDokument3 SeitenCSOE Certification Steps 1 PDFApoorva BadolaNoch keine Bewertungen
- Jku X5uDokument58 SeitenJku X5uCrystal PruebaNoch keine Bewertungen
- Oracle E-Business (General)Dokument11 SeitenOracle E-Business (General)hydersdNoch keine Bewertungen
- Security and Privacy Issues: A Survey On Fintech: (Kg71231W, Mqiu, Xs43599N) @pace - EduDokument12 SeitenSecurity and Privacy Issues: A Survey On Fintech: (Kg71231W, Mqiu, Xs43599N) @pace - EduthebestNoch keine Bewertungen
- Crack The User Data On Blackphone: Proof of ConceptDokument4 SeitenCrack The User Data On Blackphone: Proof of ConceptGilbert Laszlo KallenbornNoch keine Bewertungen
- Cybersecurity Fundamentals Course OutlineDokument4 SeitenCybersecurity Fundamentals Course Outlinem3lw1nNoch keine Bewertungen
- Black Tulip UpdateDokument101 SeitenBlack Tulip UpdatedefropiNoch keine Bewertungen
- Fundamental Areas of Cyber Security On Latest TechnologyDokument3 SeitenFundamental Areas of Cyber Security On Latest TechnologyEditor IJTSRDNoch keine Bewertungen
- Report FirewallDokument27 SeitenReport FirewallAbas WaniNoch keine Bewertungen
- EmtechDokument13 SeitenEmtechrichNoch keine Bewertungen
- SSH Overview for Linux UsersDokument16 SeitenSSH Overview for Linux UsersLev LafayetteNoch keine Bewertungen