Beruflich Dokumente
Kultur Dokumente
Performance Analysis of Location Based Adhoc Routing Protocols DSDV and Aodv
Hochgeladen von
ijsretOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Performance Analysis of Location Based Adhoc Routing Protocols DSDV and Aodv
Hochgeladen von
ijsretCopyright:
Verfügbare Formate
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 12 pp 857-863
March 2014
www.ijsret.org
ISSN 2278 0882
PERFORMANCE ANALYSIS OF LOCATION BASED ADHOC
ROUTING PROTOCOLS DSDV AND AODV
P. Malathi
PG Scholar
Dept of Computer Science & Engineering
P.S.R Rengasamy College of Engineering for Women,
Sivakasi-626 140
ABSTRACT
In many kind of mobile network environment,
nodes are communicated on the basis of their persistent
public identities. In some kind of suspicious MANET
settings, node identities should be kept as secret and
node movements must not be guessable. Since the nodes
need to communicate by only the way of their current
locations, it is necessary to construct a secure map of
locations. By using that current map, every node will
decide which other nodes it wants to communicate with.
ALARM takes advantage of anonymity and intractability
(tracking-resistance). Anonymous Location Aided
Routing protocol for Manets (ALARM) is the protocol
which uses their location and creates map for packet
transformation. In this paper, the goal is to analyze the
two ALARM protocols (DSDV & AODV) in the view
of node identity protection and performance. The aim is
to determine the performance measures like throughput,
packet delivery ratio and delay that are commonly used
in MANET by evaluating these ALARMS routing
protocols- DSDV & AODV
General Terms: MANET, DSDV, AODV
N.Chitra Devi
Assistant Professor
Dept of Computer Science & Engineering
P.S.R Rengasamy College of Engineering for Women,
Sivakasi-626 140
transmission range. More recently, location information
has become increasingly available through small and
inexpensive GPS receivers. Combining ad hoc
networking with location information facilitates some
appealing new applications, such as location-based
advertising and focused dissemination of critical
information.
In this paper a small analysis about what it takes
to provide a secure communication in hostile and
suspicious MANETs. The rest of the paper is organized
as follows: It is started by motivating the need for such a
routing scheme in section 2. Then the description of the
related work is given in section 3. The detail of the
analysis of routing protocols is given in section 4. The
presentation of the performance measures is illustrated in
section 5.The simulation results are presented by graphs
in section 6 and conclude the paper with a discussion of
remaining issues and future work is descripted in section
7.
2. AD-HOC ROUTING PROTOCOLS
1. INTRODUCTION
A. Location as Both Address and Identity
The envision a MANET setting with salient
features and requirements as follows:
A Mobile ad hoc network is a group of wireless
mobile computers (or nodes); in which nodes collaborate
by forwarding packets for each other to allow them to
communicate outside range of direct wireless
transmission. Ad hoc networks require no centralized
administration or fixed network infrastructure such as
base stations or access points, and can be quickly and
inexpensively set up as needed. Routing is the act of
moving information from a source to a destination in an
internetwork. At least one intermediate node within the
internetwork is encountered during the transfer of
information when the distance of separation exceeds the
[LOCATION] Universal availability of location
information each MANET node is equipped with a
device capable of obtaining positioning information,
e.g., GPS.
[MOBILITY] Sufficiently high mobility: A certain
minimum fraction (or number) of MANET nodes moves
periodically such that tracking a given node (which
moved) from one topology snapshot to the next is
contingent upon distinguishing it among all
nodes that have moved in the interim.
[PRIVACY] No public node identities or addresses:
Each MANET node is anonymous, i.e., its occurrences
IJSRET @ 2014
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 12 pp 857-863
March 2014
at different locations cannot be linked (we elaborate on
this below).
[SECURITY] Resistance to passive and active attacks
stemming from both outsiders and malicious (e.g.,
compromised) insider nodes.
B. Pro-Active / Table Driven:
Proactive MANET protocols are also called
as table driven protocols and will actively determine the
layout of the network. Through a regular exchange of
network topology information between the nodes of the
network, at every single node an absolute picture of the
network is maintained. There is hence minimal delay in
determining the route to be taken. This is especially
important for time critical traffic. When the routing
information becomes worthless quickly, there are many
short lived routes that are being determined and not used
before they turn invalid. Therefore, another drawback
resulting from the increased mobility is the amount of
traffic overhead generated when evaluating these
unnecessary routes.
This is especially altered when the network
size increases. The portion of the total control traffic that
consists of actual practical data is further decreased.
Lastly, if the nodes transmit infrequently, most of the
routing information is considered redundant. The nodes,
however, continue to expend energy by continually
updating these unused entries in their routing tables as
mentioned, energy conservation is very important in a
MANET system design. Therefore, this excessive
expenditure of energy is not desired. Thus, proactive
MANET protocols work best in networks that have low
node mobility or where the nodes transmit data
frequently.
C. Reactive (On Demand) protocols
Portable nodes- Notebooks, palmtops or
even mobile phones usually compose wireless ad hoc
networks. This portability also brings a significant issue
of mobility. This is a key issue in ad hoc networks. The
mobility of the nodes causes the topology of the network
to change constantly. Keeping track of this topology is
not an easy task, and too many resources may be
consumed in signalling. Reactive routing protocols were
intended for these types of environments. These are
based on the design that there is no point on trying to
have an image of the entire network topology, since it
will be constantly changing. Instead, whenever a node
needs a route to a given target, it initiates a route
discovery process on the fly, for discovering out a
pathway. Reactive protocols start to set up routes on
demand.
www.ijsret.org
ISSN 2278 0882
The routing protocol will try to establish
such a route, whenever any node wants to initiate
communication with another node to which it has no
route. This kind of protocols is usually based on flooding
the network with Route Request (RREQ) and Route
reply (RERP) messages. By the help of Route request
message the route is discovered from source to target
node; and as the target node gets a RREQ message it
send RERP message for the confirmation that the route
has been established. This kind of protocol is usually
very effective on single rate networks. It usually
minimizes the number of hops of the selected path.
However, on multi rate networks, the number of hops is
not as important as the throughput that can be obtained
on a given path.
3. RELATED WORK
Routing in MANETS has attracted a lot of
attention from the networking and security research
community. There are numerous proposals for secure
on-demand routing, such as SRDP [2], Ariadne [3], and
SEAD [4]. They focus mainly on securing route
discovery and route maintenance against node
impersonation, as well as modification and fabrication of
routing information. A comprehensive survey of secure
on demand ad-hoc routing techniques can be found in
[8] and [9].
It will not consider node privacy and
anonymity. Other research results have yielded
anonymous on demand routing protocols, such as
MASK [11], ANODR [12], ARM [14] and ODAR [15].
These protocols use pseudonyms for node identification
and addressing but none of them utilizes location
information for routing. Location-based routing
protocols mainly focus on improving the performance of
the routing protocol and minimizing overhead by
utilizing location information to deliver routing control
messages in MANETs without flooding the whole
network. Some notable techniques include [2], [17] and
[18]. To the best of our knowledge, there have been no
proposals for location-based proactive routing protocols
that preserve node anonymity and privacy.
4.
A.
DESTINATION
SEQUENCED
DISTANCE VECTOR ROUTING PROTOCOL
(DSDV)
Destination Sequenced Distance Vector Routing
(DSDV) is a table driven routing scheme for ad hoc
mobile networks based on the Bellman-Ford algorithm.
It was developed by C. Perkins and P.Bhagwat in 1994.
IJSRET @ 2014
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 12 pp 857-863
March 2014
The main contribution of the algorithm was to solve the
routing loop problem. Each entry in the routing table
contains a sequence number, the sequence numbers are
generally even if a link is present; else, an odd number is
used. The number is generated by the destination, and
the emitter needs to send out the next update with this
number. Routing information is distributed between
nodes by sending full dumps infrequently and smaller
incremental updates more frequently.
No assumptions about mobile hosts maintaining any sort
of time synchronization or about the phase relationship
of the update periods between the mobile nodes are
made. Following the traditional distance vector routing
algorithms, these update packets contain information
about which nodes are accessible from each node and the
number of hops necessary to reach them. Routes with
most recent sequence numbers are always the preferred
basis for forwarding decisions. Of the paths with same
sequence number, those with the smallest metric
(number of hops to destination) will be used.
Selection of Route
If a router receives new information,
then it uses the latest sequence number. If the sequence
number is the same as the one already in the table, the
route with the better metric is used. Stale entries are
those entries that have not been updated for a while.
Such entries as well as the routes using those nodes as
next hops are deleted.
B.
AD-HOC ON DEMAND DISTANCE
VECTOR ROUTING PROTOCOL (AODV)
Ad hoc On Demand Distance Vector (AODV)
routing is a routing protocol for mobile ad hoc networks
and other wireless ad hoc networks. It is jointly
developed in Nokia Research Centre of University of
California, Santa Barbara and University of Cincinnati
by C. Perkins and S. Das. It is an on demand and
distance vector routing protocol, meaning that a route is
established by AODV from a destination only on
demand. AODV is capable of both unicast and multicast
routing. It keeps these routes as long as they are
desirable by the sources. Additionally, AODV creates
trees which connect multicast group members. The trees
are composed of the group members and the nodes
needed to connect the members. The sequence numbers
are used by AODV to ensure the freshness of routes. It is
loop free, self starting, and scales to large numbers of
mobile nodes. AODV defines three types of control
messages for route maintenance. RREQ- A route request
message is transmitted by a node requiring a route to a
www.ijsret.org
ISSN 2278 0882
node. As an optimization AODV uses an expanding ring
technique when flooding messages.
SOURCE
ADDRESS
BROADCAST
ID
SOURCE
SEQUENCE
NO.
DESTINATION
ADDRESS
DESTINATION
SEQUENCE NO.
HOP COUNT
Figure 1: RREQ message format
Every RREQ carries a time to live (TTL) value that
states for how many hops this message should be
forwarded. This value is set to a predefined value at the
first transmission and increased at retransmissions.
Retransmissions occur if no replies are received. Data
packets waiting to be transmitted (i.e. the packets that
initiated the RREQ). Every node maintains two separate
counters: a node sequence number and a broadcast id.
The RREQ contains the following fields as shown in
Figure 1
The pair <source address, broadcast ID> uniquely
identifies a RREQ. Broadcast id is incremented
whenever the source issues a new RREQ.
RREP- A route reply message is unicasted back to the
originator of a RREQ if the receiver is either the node
using the requested address, or it has a valid route to the
requested address. The reason one can unicast the
message back, is that every route forwarding a RREQ
caches a route back to the originator.
RERR- Nodes monitor the link status of next hops in
active routes. When a link breakage in an active route is
detected, a RERR message is used to notify other nodes
of the loss of the link. In order to enable this reporting
mechanism, each node keeps a precursor list, containing
the IP address for each its neighbours that are likely to
use it as a next hop towards each destination.
Figure 2 A possible path if A wishes to find a route to J
in AODV
Selection of Route
IJSRET @ 2014
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 12 pp 857-863
March 2014
AODV builds routes using a route request/route
reply query cycle. When a source node desires a route to
a destination for which it does not already have a route,
it broadcasts a route request (RREQ) packet across the
network. Nodes receiving this packet update their
information for the source node and set up backwards
pointers to the source node in the route tables. In
addition to the source node's IP address, current
sequence number, and broadcast ID, the RREQ also
contains the most recent sequence number for the
destination of which the source node is aware.
A node getting the RREQ may send a route
reply (RREP) if it is either the destination or if it has a
route to the destination with corresponding sequence
number greater than or equal to that contained in the
RREQ. If this is the case, it unicasts a RREP back to the
source. Otherwise, it rebroadcasts the RREQ. The Figure
2 describes the possible path if A wishes to find a route
to J indicating all the messages involved. Nodes keep
track of the RREQ's source IP address and broadcast ID.
If they receive a RREQ which they have already
processed, they discard the RREQ and do not forward it.
As the RREP message propagates back to
the source,
Total delay of sent and received packets
nodes set
up forward pointers to the destination. Once the source
node receives the RREP, it may begin to forward data
packets to the destination. If the source later receives a
RREP containing a greater sequence number or contains
the same sequence number with a smaller hop count, it
may update its routing information for that destination
and begin using the better route.
As long as the route remains active, it will
continue to be maintained. A route is considered active
as long as there are data packets periodically travelling
from the source to the destination along that path. Once
the source stops sending data packets, the links will time
out and eventually be deleted from the intermediate node
routing tables. If a link break occurs while the route is
active, the node upstream of the break propagates a route
error (RERR) message to the source node to inform it of
the now unreachable destinations. After receiving the
RERR, if the source node still desires the route, it can
reinitiate route discovery.
5. PERFORMANCE MEASURES
The performance measures are used to evaluate
the effectiveness of Ad hoc routing protocols. It includes
Throughput, Packet Delivery Ratio (PDR), End to End
Delay and Routing Protocol Overhead. The Routing
Protocol providing high throughput, high Packet
www.ijsret.org
ISSN 2278 0882
Delivery Ratio, less Delay and less Routing Overhead is
always preferred. Before the real implementation of the
routing protocols, simulations are important in finding
the effectiveness of the Routing Protocols under
different mobility models. The performance metrics
defining the effectiveness of routing protocol are
discussed below.
5.1 Throughput
Total no of received packets in bits
Throughput = -----------------------------------------Total Simulation time in seconds
Throughput is defined as the average number of
bits arrived per second at each destination node. This
metric can be used to figure out the suitability of the
protocol for applications requiring high throughput. It
depends on the input data rate at the application level. In
the output trace file there are different levels of received
packets such as the RTR or AGT level. The packets
received by the node in its AGT level will be the real
received packets.
5.2 Packet Delivery Ratio
No of received packets in Destination
Ratio = ----------------------------------------------No of packets generated at the source
Packet Delivery Ratio is the ratio of the data packets
delivered to the destinations to those generated by the
sources. Lower value reflects a larger number of packets
being dropped due to link failures or network
congestion.
5.3 Average End To End Delay
No of received packets in Destination
Average Delay =
Total no of received packets
Average End to End Delay is defined as the time
a packet takes from its sending till its arrival at the
destination.
It
includes
buffering,
queuing,
retransmission and propagation delays. The end-to-end
delay is important because today many applications need
a low latency to deliver usable result.
These performance metrics can be calculated
from the trace files by using AWK program. The trace
file comprises of about few hundreds to thousands of
lines of information.
IJSRET @ 2014
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 12 pp 857-863
March 2014
www.ijsret.org
ISSN 2278 0882
6. SIMULATION RESULTS
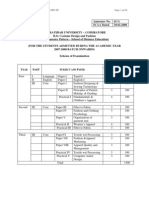
Experimental Results of DSDV
DSDV requires a regular update of its routing
tables, which uses up battery power and a small amount
of bandwidth even when the network is idle. This limits
the number of nodes that can join the network.
Whenever the topology of the network changes, a new
sequence number is necessary before the network re
converges and DSDV is unstable until update packets
propagate through the network. For this reason DSDV is
not suitable for highly dynamic networks.
Figure 5 : Packet Delivery ratio of DSDV
DSDV is effective for creating ad hoc networks of small
populations of mobile nodes. Even if the number of
nodes is higher, DSDV can perform well if the topology
does not change quickly.
Experimental Results of AODV
The main advantage of AODV protocol is that
routes are established on demand and destination
sequence numbers are used to find the latest route to the
destination. The connection setup delay is less.
Figure 3 : Delay of DSDV
Figure 6 : Delay of AODV
Figure 4 : Throughput of DSDV
IJSRET @ 2014
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 12 pp 857-863
March 2014
www.ijsret.org
ISSN 2278 0882
Both DSDV, AODV supports anonymous
location-based routing in certain types of suspicious
MANETS. In this work, performance of the routing
protocols (DSDV & AODV) are Simulated. The results
have shown the performance of AODV provides higher
throughput and packet delivery than DSDV. The average
delay for AODV protocol is observed to be less than
DSDV. DSDV periodically transmits updates to
maintain routing tables. There are also event triggered
routing table exchanges through incremental dumps.
Continuous updates contribute to a relatively stable
overhead and hence DSDV has higher delay and routing
overhead in transmitting packets successfully. Future
study should be focused on the study of the identity
protection of routing protocols.
The node identity protection and the performance
of the two location based protocols are evaluated. Both
of them cannot provide the intractability of routing
nodes. Future work includes developing an efficient
location based routing protocols that hide the routing
node identities from the outside observers with low cost.
Figure 7 : Throughput of AODV
REFERENCES
Figure 8 : Packet Delivery ratio of AODV
One of the drawbacks of this protocol is that
intermediate nodes can lead to inconsistent routes if the
source sequence number is very old and the intermediate
nodes have a higher but not the latest destination
sequence number, thereby having stale entries. Also
multiple Route Reply packets in response to a single
Route Request packet can lead to heavy control
overhead. Another disadvantage of AODV is that the
periodic beaconing leads to unnecessary bandwidth
consumption.
[1] C. Maihofer, A Survey of Geocast Routing
Protocols, IEEE Communications Surveys &
Tutorials, vol. 6, no. 2, pp. 32-42, 2004.
[2] J. Kim and G. Tsudik, SRDP: Securing Route
Discovery in DSR, The Second Annual
International Conference on Mobile and Ubiquitous
Systems: Networking and Services (MobiQuitous
2005), 2005.
[3] Y.-C. Hu, A. Perrig and D. B. Johnson, Ariadne: A
Secure On- Demand Routing Protocol for Ad Hoc
Networks, Proceedings of the Eighth Annual
International Conference on Mobile Computing and
Networking (MobiCom 2002), 2002.
[4] Y.-C. Hu, D. B. Johnson and A. Perrig, SEAD:
secure efficient distance vector routing for mobile
wireless ad hoc networks, Fourth IEEE Workshop
on Mobile Computing Systems and Applications
(WMCSA 02), 2002.
[5] G. Acs, L. Buttyn and I. Vajda,Provably Secure Ondemand Source Routing in Mobile Ad Hoc
Networks, IEEE Transactions on Mobile
Computing, vol. 5, no. 11, November 2006.
[6] M. G. Zapata and N. Asokan, Securing ad hoc
routing protocols, Proceedings of the 3rd ACM
workshop on Wireless security (WiSE 02), 2002.
[7] Y.-C. Hu and A. Perrig, A Survey of Secure
Wireless Ad Hoc Routing, IEEE Security And
Privacy Magazine, vol. 2; no. 3, pp. 28-39, 2004.
7. CONCLUSION AND FUTURE WORK
IJSRET @ 2014
International Journal of Scientific Research Engineering & Technology (IJSRET)
Volume 2 Issue 12 pp 857-863
March 2014
[8] P. Argyroudis and D. OMahony,Secure Routing for
Mobile Ad- Hoc Networks,To appear in IEEE
Communications Surveys and Tutorials.
[9] S. Carter and A. Yasinsac, Secure Position Aided
Ad Hoc Routing, Proceedings of the IASTED
International Conference on Communications and
Computer Networks (CCN02), pp. 329- 334, Nov. 46, 2002.
[10] B. Zhu, Z. Wan, M. Kankanhalli, F. Bao, and R.
Deng, Anonymous Secure Routing in Mobile AdHoc Networks, Proceedings of the 29th Annual
IEEE International Conference on Local Computer
Networks (LCN 2004), 2004.
[11] Y. Zhang, W. Liu, W. Lou and Y. Fang, MASK:
anonymous on demand routing in mobile ad hoc
networks, IEEE Transactions on Wireless
Communications, vol.5, no.9, pp.2376-2385, 2006.
[12] J. Kong and X. Hong, ANODR: ANonymous On
Demand Routing with Untraceable Routes for
Mobile Ad-hoc Networks, Proceedings of ACM
MOBIHOC03, pp. 291302, 2003.
[13] L. Yang, M. Jakobsson and S. Wetzel, Discount
Anonymous On Demand Routing for Mobile Ad
hoc Networks, SECURECOMM 06, 2006.
[14] S. Seys and B. Preneel, ARM: Anonymous
Routing Protocol for Mobile Ad hoc Networks,
Proceedings of the 20th International Conference
on Advanced Information Networking and
Applications (AINA06), 2006.
[15] D. Sy, R. Chen and L. Bao, ODAR: On-Demand
Anonymous Routing in Ad Hoc Networks, In
Proceedings of The Third IEEE International
Conference on Mobile Ad-hoc and Sensor Systems
(MASS), 2006.
[16] M. Mauve, J.Widmer, and H. Hartenstein, A
Survey on Position- Based Routing in Mobile Ad
Hoc Networks, IEEE Network Magazine,
15(6):3039, November 2001.
[17] F. Arajo and L. Rodrigues, Survey on PositionBased
Routing,
University
of
Lisbon
TechnicalReport,
http://www.minema.di.fc.ul.pt/papers.html,
Jan.
2006,.
[18] Johnson, Maltz and Hu, The Dynamic Source
Routing Protocol for Mobile Ad Hoc Networks
(DSR), Internet Draft, 2003.
[19] C. Perkins and E. Royer, Ad hoc On-Demand
Distance Vector Routing, Proceedings of the 2nd
IEEE Workshop on Mobile Computing Systems
and Applications, pp. 90-100, 1999.
www.ijsret.org
ISSN 2278 0882
[20] J. Kurose and K. Ross, Computer Networks: A
Top Down Approach Featuring the Internet,
Pearson Addison Wesley.
[21] D. Chaum and E. Van Hejst, Group Signatures,
Advances in Cryptology EUROCRYPT 91, D.W.
Davies (Ed.), Springer-Verlag, pp. 257-265 .
[22] D. Boneh, X. Boyen and H. Shacham, Short Group
Signatures, In proceedings of Crypto 04, LNCS
3152, pp. 41-55, 2004.
[23] J. Camenisch and A. Lysyanskaya, Signature
Schemes and Anonymous Credentials from Bilinear
Maps, In Advances in Cryptology - Crypto 2004,
Springer Verlag, 2004.
IJSRET @ 2014
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Thermal Analysis On Characterization of Polycaprolactone (PCL) - Chitosan Scaffold For Tissue EngineeringDokument5 SeitenThermal Analysis On Characterization of Polycaprolactone (PCL) - Chitosan Scaffold For Tissue Engineeringijsret100% (1)
- A Review On Data De-Duplication Techniques For Managing Data Into CloudDokument4 SeitenA Review On Data De-Duplication Techniques For Managing Data Into CloudijsretNoch keine Bewertungen
- A Systematic Literature Review On Network Attacks, Classification and Models For Anomaly-Based Network Intrusion Detection SystemsDokument7 SeitenA Systematic Literature Review On Network Attacks, Classification and Models For Anomaly-Based Network Intrusion Detection SystemsijsretNoch keine Bewertungen
- Design and Manufacture of Carbon-Free CarDokument3 SeitenDesign and Manufacture of Carbon-Free CarijsretNoch keine Bewertungen
- A Review of Large-Scale RDF Document Processing in Hadoop MapReduce FrameworkDokument4 SeitenA Review of Large-Scale RDF Document Processing in Hadoop MapReduce FrameworkijsretNoch keine Bewertungen
- Consruction of A Direct Solar Dryer For Perishable Farm ProductsDokument9 SeitenConsruction of A Direct Solar Dryer For Perishable Farm ProductsijsretNoch keine Bewertungen
- A Review of Matrix Multiplication in Multicore Processor Using Interconnection NetworkDokument6 SeitenA Review of Matrix Multiplication in Multicore Processor Using Interconnection NetworkijsretNoch keine Bewertungen
- A Distinct Method To Find The Critical Path and Total Float Under Fuzzy EnvironmentDokument5 SeitenA Distinct Method To Find The Critical Path and Total Float Under Fuzzy EnvironmentijsretNoch keine Bewertungen
- A Review On Natural Fibre Polymer CompositesDokument6 SeitenA Review On Natural Fibre Polymer CompositesijsretNoch keine Bewertungen
- An Augmented Anomaly-Based Network Intrusion Detection Systems Based On Neural NetworkDokument6 SeitenAn Augmented Anomaly-Based Network Intrusion Detection Systems Based On Neural NetworkijsretNoch keine Bewertungen
- An Approach To Bug Triage: A ReviewDokument4 SeitenAn Approach To Bug Triage: A ReviewijsretNoch keine Bewertungen
- Comparative Study and Review On Object Oriented Design MetricsDokument4 SeitenComparative Study and Review On Object Oriented Design MetricsijsretNoch keine Bewertungen
- Source Identification For Anonymous Attacks With Deterministic Packet MarkingDokument4 SeitenSource Identification For Anonymous Attacks With Deterministic Packet MarkingijsretNoch keine Bewertungen
- A Review On Fingerprint Detection and Recognization TechniquesDokument4 SeitenA Review On Fingerprint Detection and Recognization TechniquesijsretNoch keine Bewertungen
- A Review On Face Detection and Recognization TechniquesDokument4 SeitenA Review On Face Detection and Recognization TechniquesijsretNoch keine Bewertungen
- Solving A Decision Making Problem Using Weighted Fuzzy Soft MatrixDokument5 SeitenSolving A Decision Making Problem Using Weighted Fuzzy Soft MatrixijsretNoch keine Bewertungen
- Mechanical and Fracture Toughness Analysis of Woven Carbon Fibre Reinforced Epoxy CompositesDokument6 SeitenMechanical and Fracture Toughness Analysis of Woven Carbon Fibre Reinforced Epoxy CompositesijsretNoch keine Bewertungen
- CHANGES IN ANTI OXIDANT ENZYME ACTIVITIES IN Pseudomonas Syringae PV Syringae (BACTERIAL BROWN SPOT) INFECTED SEEDLINGS OF Vigna Radiata L.Dokument5 SeitenCHANGES IN ANTI OXIDANT ENZYME ACTIVITIES IN Pseudomonas Syringae PV Syringae (BACTERIAL BROWN SPOT) INFECTED SEEDLINGS OF Vigna Radiata L.ijsretNoch keine Bewertungen
- Echo Cancellation System in VOIP Using MATLABDokument3 SeitenEcho Cancellation System in VOIP Using MATLABijsretNoch keine Bewertungen
- Augmentation Heat Transfer in A Circular Tube Using Conical Ring and Twisted Tape InsertDokument8 SeitenAugmentation Heat Transfer in A Circular Tube Using Conical Ring and Twisted Tape InsertijsretNoch keine Bewertungen
- Comparative Study and Review On Object Oriented Design MetricsDokument4 SeitenComparative Study and Review On Object Oriented Design MetricsijsretNoch keine Bewertungen
- Automated Personalized Face Detection Using Viola DetectorDokument5 SeitenAutomated Personalized Face Detection Using Viola DetectorijsretNoch keine Bewertungen
- Demographic Differences in Postgraduate Students' Attitudes and Use of ICT Facilities in Rivers State University of Science and Technology, Port HarcourtDokument6 SeitenDemographic Differences in Postgraduate Students' Attitudes and Use of ICT Facilities in Rivers State University of Science and Technology, Port HarcourtijsretNoch keine Bewertungen
- Comparison of Workpiece Geometry and Its Effects On ECAP Process by FEADokument5 SeitenComparison of Workpiece Geometry and Its Effects On ECAP Process by FEAijsretNoch keine Bewertungen
- Experimental Investigation and Numerical Simulation of Marble Dust Filled Aramid Fibre Reinforced Epoxy Composite For Wind Turbine Blade ApplicationDokument9 SeitenExperimental Investigation and Numerical Simulation of Marble Dust Filled Aramid Fibre Reinforced Epoxy Composite For Wind Turbine Blade ApplicationijsretNoch keine Bewertungen
- Numerically Investigating Effects of Channel Angle, Friction and Ram Velocity On Strain Homogeneity in EcapDokument4 SeitenNumerically Investigating Effects of Channel Angle, Friction and Ram Velocity On Strain Homogeneity in EcapijsretNoch keine Bewertungen
- Blending Behavior of Cotton and Polyester Fibers On Different Spinning Systems in Relation To Physical Properties of Blended YarnsDokument11 SeitenBlending Behavior of Cotton and Polyester Fibers On Different Spinning Systems in Relation To Physical Properties of Blended YarnsijsretNoch keine Bewertungen
- Content Based Image Retrieval Using Color FeatureDokument6 SeitenContent Based Image Retrieval Using Color FeatureijsretNoch keine Bewertungen
- Strategies of Effective Teaching and Learning Practical Skills in Technical and Vocational Training Programmes in NigeriaDokument6 SeitenStrategies of Effective Teaching and Learning Practical Skills in Technical and Vocational Training Programmes in NigeriaijsretNoch keine Bewertungen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Gender Representation in The Media Lesson PlanDokument2 SeitenGender Representation in The Media Lesson Planapi-250065413Noch keine Bewertungen
- Adbms New ProductDokument23 SeitenAdbms New ProductPinkNoch keine Bewertungen
- Introduction To Global MarketingDokument16 SeitenIntroduction To Global Marketing27usmanNoch keine Bewertungen
- BillboardsDokument6 SeitenBillboardsmainaka100% (1)
- Consumer Behaviour Towards E-Marketing: A Study of Jaipur ConsumersDokument12 SeitenConsumer Behaviour Towards E-Marketing: A Study of Jaipur ConsumersArun PrasaathNoch keine Bewertungen
- Cosmetic DentistryDokument52 SeitenCosmetic DentistryPaul Chen60% (5)
- B.SC SubjectsDokument24 SeitenB.SC Subjectsranju93Noch keine Bewertungen
- CH 3Dokument64 SeitenCH 3Tuan Anh Nguyen100% (2)
- Chapter 11Dokument24 SeitenChapter 11Samina KhanNoch keine Bewertungen
- Mario Moretti Polegato Is The CEO of GEOXDokument4 SeitenMario Moretti Polegato Is The CEO of GEOXkhanriskyNoch keine Bewertungen
- New Media AdvertisingDokument13 SeitenNew Media Advertisingbiggb4352Noch keine Bewertungen
- What Type of Tourism Should Be Developed in Rio de JaneiroDokument41 SeitenWhat Type of Tourism Should Be Developed in Rio de JaneiroRazvanNoch keine Bewertungen
- Aisha Ali Management Consultancy Profile PDFDokument25 SeitenAisha Ali Management Consultancy Profile PDFFarrukh TouheedNoch keine Bewertungen
- Solution Manual - RANTE COST ACCDokument127 SeitenSolution Manual - RANTE COST ACCray57% (7)
- Final ProjectDokument64 SeitenFinal ProjectAneesh Chorode0% (2)
- Final LuxDokument54 SeitenFinal LuxAnkit JainNoch keine Bewertungen
- The Emirates GroupDokument23 SeitenThe Emirates GroupSahlKhanNoch keine Bewertungen
- Directory Booking Form & Media KitDokument14 SeitenDirectory Booking Form & Media KitInexpo GroupNoch keine Bewertungen
- Online Consumer Behavior, Market Research, and AdvertisementDokument40 SeitenOnline Consumer Behavior, Market Research, and AdvertisementJenneey D Rajani100% (1)
- GSTDokument14 SeitenGSTsatwikaNoch keine Bewertungen
- Kurkure: CC CCDokument8 SeitenKurkure: CC CCDivya Chawhan0% (1)
- Brand Finance Journal Issue 2Dokument36 SeitenBrand Finance Journal Issue 2wilsonjoaoNoch keine Bewertungen
- Pemeriksaan Fisik Neonatus: PEMBIMBING: Dr. Gunawan Sugiarto, Sp.ADokument13 SeitenPemeriksaan Fisik Neonatus: PEMBIMBING: Dr. Gunawan Sugiarto, Sp.ALatifa Syifa SafitriNoch keine Bewertungen
- Dissertation NikhilDokument43 SeitenDissertation NikhilSourabh BansalNoch keine Bewertungen
- Ascott Limited enDokument13 SeitenAscott Limited enĐức TrọcNoch keine Bewertungen
- Impact of AdvertisementDokument14 SeitenImpact of AdvertisementRahulKrishnanNoch keine Bewertungen
- A Complete PR Plan of Skinny JeansDokument3 SeitenA Complete PR Plan of Skinny Jeansdarshand_2Noch keine Bewertungen
- A Sample Cell Phone Repair Business Plan TemplateDokument18 SeitenA Sample Cell Phone Repair Business Plan TemplateGibo100% (2)
- Marketing Plan Final555.Doc55Dokument48 SeitenMarketing Plan Final555.Doc55Moona Khan0% (1)
- The Brazilian Milk Fraud Scandal Involving The Italian Food Conglomerate Parmalat.Dokument12 SeitenThe Brazilian Milk Fraud Scandal Involving The Italian Food Conglomerate Parmalat.igabas21100% (1)