Beruflich Dokumente
Kultur Dokumente
DWDM OTN
Hochgeladen von
neonetwirelessOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
DWDM OTN
Hochgeladen von
neonetwirelessCopyright:
Verfügbare Formate
JOURNAL OF INFORMATION SCIENCE AND ENGINEERING 25, 733-745 (2009)
The Multiple Path Protection
of DWDM Backbone Optical Networks*
WEN-PING CHEN, FU-HUNG SHIH AND WEN-SHYANG HWANG
Department of Electrical Engineering
National Kaohsiung University of Applied Sciences
Kaohsiung, 807 Taiwan
Primary transmission protection technology is based on the characteristics of
SONET/SDH protection mechanism which provides two fiber path rings. A serious
problem may arise in the architecture when two fiber links are simultaneously broken.
Mesh protection networks can support many protection paths to address above issue, but
the key components of optical cross-connect (OXC) or photonic cross-connect (PXC) are
expensive for network providers. Therefore, this study proposes a novel protection
mechanism with a low-cost equipment of optical protection switching (OPS) for building
a multiple path protection architecture on DWDM backbone network. The proposed
mechanism is named the double 8-type OPS back to back protection mechanism. It can
support eight protection paths to improve the issues of the low-path 1 + 1 dedicated ring
and expensive mesh protection networks. This experiment demonstrates the automatic
protection switching (APS) simulation tool, and the proposed mechanism could satisfy all
demands of protection standard (e.g., the protection switching within 50 ms).
Keyword: OPS, DWDM, multiple-path protection, SONET/SDH, ring network
1. INTRODUCTION
The transmission bandwidth of telecom networks has growing dramatically in recent years. With this growing bandwidth, and the growing number of subscribers, the
network restore forces are also growing and become more important. The large bandwidth
of optical fibers has made the fibers attractive for high-speed networks, and the use of
dense wavelength division multiplexing (DWDM) allows the aggregation of channels
onto a single fiber without the need of high-speed optoelectronic devices for end-users
[1-4]. It is the simplicity of this multiplexing scheme that permits relatively easy access
to the fibers bandwidth, which is the underlying reason for DWDM playing a major role
in the expansion of optical networks. However, the existence of many independent data
channels over the fiber infrastructure could lead to problems of failure, as the amount of
bandwidth lost by a component or cable failure is now much larger than what would
have been lost in a traditional network. This is why extra effort must be spent in analyzing optical DWDM networks and in finding ways to protect them against failures [5-8].
Currently the DWDM backbone network protection still adopts the traditional 1 + 1
dedicated path protection, which builds two fiber rings to increase the network survivability, i.e., working path and protection path [9-11]. The O-BLSR (MS-SPRING) or
O-UPSR (SNCP) of SONET/SDH protection can support two path fiber routing transReceived February 1, 2008; accepted November 28, 2008.
Communicated by Yau-Hwang Kuo, Pau-Choo Chung and Jar-Ferr Yang.
*
This research was supported by the National Science Council of Taiwan, R.O.C. project No. NSC 96-2221E-151-029.
733
734
WEN-PING CHEN, FU-HUNG SHIH AND WEN-SHYANG HWANG
missions to avoid an optical fiber from breaking off, however, sometimes two fiber paths
would break simultaneously in a network. The restoration and repair time of cut fibers is
lengthy. Although many researches of mesh protection [12, 13] have addressed the above
issue, the switch equipments (e.g., optical cross-connect (OXC), and photonic cross-connect (PXC)) are expensive for network providers.
Therefore, how to design a multiple-paths protection architecture with a low-cost
equipment to improve the 1 + 1 protection architecture of a DWDM backbone network is
a very important issue. In this paper, a low-cost and rapid multiple-path protection DWDM
backbone network is proposed and implemented. The OPS operation model for the proposed protection structure is presented in section 2. The DWDM general protection type
is described in section 3. Section 4 presents a multiple-path protection mechanism. Section 5 describes the simulations, testing results and further discusses the proposed architecture. Finally, a few concluding remarks are given in section 6.
2. THE OPS OPERATION MODEL
In this proposed protection architecture, each node is installed an optical protection
switching (OPS) for building the protection policy. The structure of OPS mainly divides
two parts: transmitter side and receiver side. The description of them is as follows:
Transmitter-side
The transmitter-side structure of the OPS is shown in Fig. 1. When an optical signal
comes from the upstream nodes, a small portion of incoming optical power (INcom) is
separated into the photo diode (PD). The small portion of optical power is converted to
be an electronic signal for detecting the incoming optical power value. The INcom signal
and optical supervisory channel (OSC) signal are combined into the fiber with a coupler
to connect the working path (OUTw) and protection path (OUTp).
Fig. 1. The transmitter-side structure of OPS.
TS0: FAS (Frame alignment signal)
TS2: F1 (User define channel)
TS15: E2 (Order wire channel)
TS1: E1 (Order wire channel)
TS3 ~ TS14: D1 ~ D12 (DCC Channel)
TS16 ~ TS31: Reserve channels
Fig. 2. The frame format of OSC.
To support the protection policy, a frame format of OSC is shown in Fig. 2. The
FAS field is confirmed for the signal synchronization. The TS1 and TS15 fields are used
THE MULTIPLE PATH PROTECTION OF DWDM BACKBONE OPTICAL NETWORKS
735
for voice communication channels. The F1 field is a free channel for users. D1 ~ D12
fields represent the data communication channels. Finally, the TS16 ~ TS31 fields are
the reserved channels.
Receiver-side
The receiver-side structure of the OPS is shown in Fig. 3. The incoming optical
power signal (INw) can be detected by the OSC in real-time. When its optical power is
lower than the initial threshold, the optical switch port is switched to the protection path
(INp) to guarantee the network reliability. It is worth noting that the detection time of the
lower optical power signal (INw) must be sustained for 50 ms according to the protection
standards, to void an error decision in switching.
Fig. 3. The receiver-side structure of OPS.
Here, there are three different kinds of operation modes in OPS that can be selected
for the network management. These operation modes are described as follows:
y AUTO: this model is an auto reserve type. When the signal loss of INw is large, the
unusual time is more than 50 ms, and the optical switch is able to switch the INp port.
When the working fiber has been reconstructed, the optical switch will return to connect the INw port.
y SEMI-AUTO: this model is a semi-automatic switch type. This model can automatically switch to INp port when the working path is cut, however, the optical switch cannot return to connect the INw port, even if the working fiber has been repaired.
y MANUAL: this model is a manual operation type. When the working path is cut or
repaired, the network management must operate the optical switch port to select received the incoming optical signal of INp or INw via SNMP management.
The operation configuration of OPS is shown in Fig. 4. The significance of input/
output symbols and the system parameters range of OPS are listed in Tables 1 and 2. The
insertion loss of OPS only consumes about 1.2 dB by power meter.
3. DWDM GENERAL PROTECTION TYPE
When the loss of incoming optical power (INw port) of OPS or the optical signal
power is seriously degraded for some important channels, these irregular phenomena can
be detected by the OSC channel. Once a fault is detected the optical switch switches
736
WEN-PING CHEN, FU-HUNG SHIH AND WEN-SHYANG HWANG
Fig. 4. The OPS operation configuration.
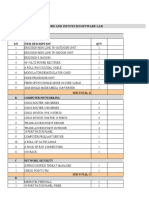
Table 1. The significance of input/output symbols of OPS.
Symbol
OUTcom
INcom
INw
INp
OUTw
OUTp
Significance
Local optical receiver plug
Local optical transmission plus
Receiver remote optical transmission (working path) plug
Receiver remote optical transmission (protection path) plug
Transmission to remote receiver (working path) plug
Transmission to remote receiver (protection path) plug
Table 2. The system parameter ranges of OPS.
Transmitter-side
Receiver-side
Item
Operating wavelength (nm)
Input power range (dBm)
OSC wavelength (nm)
Operating wavelength (nm)
Input power range (dBm)
Switch level (dBm)
Setting range (Res = 1)
Restoration time (ms)
Min
Typical
Max
1310 20 & 1550 20
15
3
1595
1625
1655
1310 20 & 1550 20
35
1
29
5
50
form the INw port to the INp port for executing network protection. In addition, to ensure the OPS has a correct protection mechanism, there are many important system parameters requirements necessary to conform. They are listed as follows:
y Switch over time within 50 ms to minimize the impact to the service.
y Both the working path and protection path are supervised by the OSC channel in realtime.
y DWDM side (MUX/DMUX): the received power is set at power ranges (0 ~ 18 dB).
y Client side: the received power of optical transponder unit (OTN) is set at power
ranges ( 3 ~ 18 dB).
y OPS switching level: the value is set according to the OUT and client equipment sensitivity.
THE MULTIPLE PATH PROTECTION OF DWDM BACKBONE OPTICAL NETWORKS
737
Fig. 5. When the working path fiber is cut, the DWDM site-A and DWDM site-B of OPS are
switched to the protection path. (Channel Protection)
Fig. 6. When the working tributary card has a failure, OPS1 and OPS2 are switched to the protection tributary card. (Client Protection)
738
WEN-PING CHEN, FU-HUNG SHIH AND WEN-SHYANG HWANG
There are four different kinds of protection mechanisms that can be selected in this
protection architecture, such as channel protection, client protection, channel/client protection, and fiber protection. These protection mechanisms are described as follows:
Channel Protection Mechanism
In this mechanism, the DWDM side has two MAX/ DMAX, as shown in Fig. 5.
When the working path fiber is cut, the DWDM site-A and DWDM site-B OPS are
switched to the protection path for achieving a good communication quality for traffic
load.
Client Protection Mechanism
In this client protection mechanism (see Fig. 6), the DWDM site has one path, one
MUX/DMUX, and are two tributary cards. When the working tributary card fails, the
OPS1 and OPS2 are simultaneously switched to the protection tributary card to ensure
communication reliability.
Channel/Client Protection Mechanism
In the channel/client protection, both the DWDM side and tributary side have working and protection cards to execute the protection mechanism as shown in Fig. 7. This
protection mechanism has two protection methods. In the channel protection mechanism,
the DWDM site-A of OPS and DWDM site-B of OPS are simultaneously switched to the
protection path when the working path fiber is cut. In the client protection mechanism,
Fig. 7. When the working path fiber is cut or working tributary card has a failure, OPS switches to
the protection path and the protection tributary card. (Channel/client protection)
THE MULTIPLE PATH PROTECTION OF DWDM BACKBONE OPTICAL NETWORKS
739
the DWDM site-A of OPS and DWDM site-B of OPS can be switched to the protection
tributary card to avoid the traffic load being broken.
Fiber Protection Mechanism
In the fiber protection mechanism, if the working fiber is cut, the traffic can be
automatically switched to the protection fiber. This protection mechanism is able to protect all channels to guarantee the communication quality. Here, the characteristic of protection fiber in length and power budget is similar the working fiber [14] to avoid error
detection of all OPS. Naturally, the influence of the insertion loss in OPS is also considered. The illustration of protection mechanism is show in Fig. 8.
Fig. 8. When the working fiber is cut, the traffic can be switched to the protection fiber automatically. (Fiber protection)
Fig. 9. 8-type OPS back to back connection protection.
740
WEN-PING CHEN, FU-HUNG SHIH AND WEN-SHYANG HWANG
4. MULTIPLE-PATH PROTECTION
In the general protection mechanism, there are two fiber paths or two tributary cards
for protection of the working fiber or the working tributary card. However, this protection only provides two paths protection. Therefore, in order to increase the protection
paths, the above protection mechanism could be extended to a multiple-path protection
mechanism. This multiple-path protection mechanism has two different kinds of protection architectures, the descriptions of protection action are as follows:
8-Type OPS back to back Protection Mechanism
An OPS back to back connection protection is accomplished as shown in Fig. 9 to
support four routing protection paths as follows:
(1) DWDM side-A path1 DWDM side-C path2 DWDM side-B.
(2) DWDM side-A path1 DWDM side-C path4 DWDM side-B.
(3) DWDM side-A path3 DWDM side-C path2 DWDM side-B.
(4) DWDM side-A path3 DWDM side-C path4 DWDM side-B.
This 8-type back to back OPS connection can provide double protection capacity
over the traditional 1 + 1 protection mechanism.
Double 8-Type OPS back to back Protection Mechanism
The double 8-type protection mechanism consists two 8-type OPS back to back protection networks, with parallel connections. The illustration of protection mechanism is
show in Fig. 10. It can support eight protection paths, as follow:
(1) DWDM side-A path1 DWDM side-C path2 DWDM side-B.
(2) DWDM side-A path1 DWDM side-C path4 DWDM side-B.
(3) DWDM side-A path3 DWDM side-C path2 DWDM side-B.
(4) DWDM side-A path3 DWDM side-C path4 DWDM side-B.
(5) DWDM side-A path5 DWDM side-C path6 DWDM side-B.
(6) DWDM side-A path5 DWDM side-C path8 DWDM side-B.
(7) DWDM side-A path7 DWDM side-C path6 DWDM side-B.
(8) DWDM side-A path7 DWDM side-C path8 DWDM side-B.
This protection mechanism can maintain eight protection paths for DWDM backbone networks to more communication reliability. The flow chart of a double 8-type
OPS back to back protection connection action is shown in Fig. 11.
5. SIMULATION AND TESTING RESULTS
To test the proposed protection mechanism, the simulation software named automatic protection switching (APS) in the ACTERNA ANT20 is used. The channel speed
is operated at 2.5 Gb/s in the DWDM backbone network.
THE MULTIPLE PATH PROTECTION OF DWDM BACKBONE OPTICAL NETWORKS
Fig. 10. Double 8-type OPS back to back connection protection.
Fig. 11. The flow chart of a double 8-type OPS back to back protection connection.
741
742
WEN-PING CHEN, FU-HUNG SHIH AND WEN-SHYANG HWANG
(a)
(b)
Fig. 12. (a) The test result of the switching time with the OPS manual switching; (b) The test result
of switching time when the OPS fiber is cut.
(a)
(b)
Fig. 13. (a) The ES test result with the OPS manual switching by the APS of ACTERNA ANT20;
(b) The test result of ES when the OPS fiber is cut.
Manual Switch Testing
The test uses the manual switching mode to examine the protection capacities of
Figs. 5 to 10. Here, the INw port is switched to the INp port by SNMP management. The
test results of the switching time, and the error seconds (ES), are shown in Figs. 12 (a)
and 13 (a). The simulation results show that the switching time and ES are only about 2
ms and 1 (ES). This represents that this proposed mechanism can provide a rapid and
low error protection system.
Fiber Cut Switch Testing
In the test simulation, the OPS is operated as automatic models to understand the
influence of fibers being cut, as shown in Figs. 5 to 10. The test results are shown in Figs.
12 (b) and 13 (b). From the figures display the switching time and ES is only 6 ms and 1
ES.
The above discussion makes it clear that double 8-type back to back connection
protection mechanism has a more perfect protection capacity than do other protection
mechanisms. The feature comparisons of these proposed protection mechanisms are
summarized in Table 3. The proposed protection mechanism exhibits excellent protection capacity and low-cost equipment to maintain the communication reliability and
quality for widespread users or important customers.
THE MULTIPLE PATH PROTECTION OF DWDM BACKBONE OPTICAL NETWORKS
743
Table 3. Comparison of general DWDM backbone protection and double 8-Type back to
back connection protection mechanism.
Protection Type
1 + 1 dedicated protection
Channel protection
Client protection
Channel and client protection
8-type back to back connect
Double 8-type back to back connection
Path numbers
2
2
1
2
4
8
Tributary numbers
1
1
2
2
1 or 2
1 or 2
6. CONCLUSION
Optical communications provide a huge bandwidth capacity on DWDM backbone
networks, therefore, if the working fiber is suddenly cut, it is a serious problem for communication quality. Hence, how to enhance the network survivability is still a very important issue in DWDM backbone networks. This paper proposes a double 8-type back
to back connection protection mechanism to improve the 1 + 1 dedicated protection
mechanism (with only two protection paths) on DWDM backbone networks. The protection architecture requires simplified, rapid, and low-cost equipment with some passive
optical components. It can support eight protection paths to more ensure communication
reliability and quality. The simulation results also show that, the switching demands of
this proposed protection mechanisms can satisfy protection standards, regardless of the
system being operated as an automation or manual operation model. This protection
mechanism can provide multiple-paths with a low-cost equipment to improve the disadvantages of the low-path 1 + 1 dedicated ring protection and expensive mesh protection
mechanisms.
REFERENCES
1. J. H. Ho, W. P. Chen, W. S. Hwang, and C. K. Shieh, CSMA/ID MAC protocol for
IP over WDM ring network, International Journal of Communication Systems, Vol.
21, 2008, pp. 1155-1170.
2. W. P. Chen, W. F. Wang, and W. S. Hwang, A novel bandwidth reservation MAC
protocol for OBS metro ring networks, Journal of High-Speed Networks, Vol. 17,
2008, pp. 59-72.
3. S. V. Kartalopoulos, Elastic bandwidth: Optical-fiber communication, IEEE Circuits and Devices Magazine, Vol. 18, 2002, pp. 8-13.
4. Y. Frignac, G. Charlet, W. Idler, R. Dischler, P. Tran, S. Lanne, S. Borne, C. Martinelli, G. Veith, A. Jourdan, J. P. Hamaide, and S. Bigo, Transmission of 256 wavelength-division and polarization-division-multiplexed channels at 42.7 Gb/s (10.2
Tb/s capacity) over 3 100 km of Teralight fiber, in Optical Fiber Communication
Conference and Exhibit, 2002, pp. FC5-1-FC5-3.
5. S. Ramamurthy and B. Mukherjee, Survivable WDM mesh networks, Journal of
Lightwave Technology, Vol. 21, 2003, pp. 870-883.
744
WEN-PING CHEN, FU-HUNG SHIH AND WEN-SHYANG HWANG
6. A. Fumagalli, I. Cerutti, M. Tacca, and F. Masetti, Survivable networks based on
optimal routing and WDM self-healing rings, in Proceedings of the 18th Annual
Joint Conference of the IEEE Computer and Communications Societies, Vol. 2, 1999,
pp. 726-733.
7. S. Arakawa, M. Murata, and H. Miyahara, Design methods of multilayer survivability in IP over WDM networks, Optical Networking and Communications, Vol.
4233, 2000, pp. 279-290.
8. O. Gerstel and R. Ramaswami, Optical layer survivability: An implementation perspective, IEEE Journal on Selected Areas in Communications, Vol. 18, 2000, pp.
1885-1899.
9. D. Levy, K. Solomon, and S. Korotky, Loss-less bridging in 1 + 1 optical protection using a modified transmitter and receiver, IEEE Photos Technology Letters,
Vol. 15, 2003, pp. 485-487.
10. R. Iraschko, R. Sharma, M. Ngyuen, J. Mar, and G. Parker, An optical 4-fiber bidirectional line-switched ring, in Proceedings of International Conference on Integrated Optics and Optical Fiber Communication, Vol. 1, 1999, pp. 154-156.
11. Z. Wang, C. Lin, and C. Chan, Demonstration of a single-fiber self-healing CWDM
metro access ring network with unidirectional OADM, IEEE Photonics Technology
Letters, Vol. 18, 2006, pp. 163-165.
12. S. Kim, X. J. Zhang, and S. S. Lumetta, Rapid and efficient protection for
all-optical WDM mesh networks, IEEE Journal on Selected Areas in Communications, Vol. 25, 2007, pp. 68-82.
13. E. Bouillet and J. F. Labourdette, Distributed computation of shared backup path in
mesh optical networks using probabilistic methods, IEEE/ACM Transactions on
Networking, Vol. 12, 2004, pp. 920-930.
14. K. Hogari, S. Tetsutani, J. Zhou, F. Yamamoto, and K. Sato, Optical-transmission
characteristics of optical-fiber cables and installed optical-fiber cable networks for
WDM systems, Journal of Lightwave Technology, Vol. 21, 2003, pp. 540-545.
Wen-Ping Chen () received the B.S. degree in Electrical Engineering from National Taiwan Institute of Technology,
Taiwan in 1992, the M.S. degree in Electrical Engineering from
National Sun Yat-sen University, Taiwan in 2000 and the Ph.D.
degree in Electrical Engineering from National Kaohsiung University of Applied Sciences in 2003. He is an Assistant Professor
of the Electrical Engineering of National Kaohsiung University
of Applied Sciences. His current research interests include metro
networks and PON networks.
THE MULTIPLE PATH PROTECTION OF DWDM BACKBONE OPTICAL NETWORKS
745
Fu-Hung Shih () received the B.S. degree in Electronic Engineering from National Yunlin Institute of Technology,
Taiwan in 1994, and the M.S. degree in Electrical Engineering
from National Kaohsiung University of Applied Sciences, Taiwan in 2008. He is an Associate Manager of private network
company. His research focuses on optical protection and network
management.
Wen-Shyang Hwang () received B.S., M.S. and
Ph.D. degrees in Electrical Engineering from National Cheng
Kung University, Taiwan, in 1984, 1990 and 1996, respectively.
He is a Professor of Electrical Engineering and the chairman of
Department of Computer Science and Information Engineering in
National Kaohsiung University of Applied Sciences, Taiwan. His
current research interests are in the fields of high speed networks,
performance evaluation, Internet QoS, storage area networks and
multimedia wireless communications.
Das könnte Ihnen auch gefallen
- TutsGalaxy.comDokument1 SeiteTutsGalaxy.comSamyuktha SridharNoch keine Bewertungen
- Solution Id 25Dokument23 SeitenSolution Id 25Kaye CatotalNoch keine Bewertungen
- Pre-Created Practice Lab For The Practice of DHCP Server: S: and - Both Network S Are Connect Ed To The Router'sDokument20 SeitenPre-Created Practice Lab For The Practice of DHCP Server: S: and - Both Network S Are Connect Ed To The Router'sneonetwirelessNoch keine Bewertungen
- Profile Neonet 2Dokument32 SeitenProfile Neonet 2neonetwirelessNoch keine Bewertungen
- Profile NeonetDokument27 SeitenProfile NeonetneonetwirelessNoch keine Bewertungen
- DHCP Internet ConfigDokument1 SeiteDHCP Internet ConfigneonetwirelessNoch keine Bewertungen
- Pre-Created Practice Lab For The Practice of DHCP ServerDokument5 SeitenPre-Created Practice Lab For The Practice of DHCP ServerneonetwirelessNoch keine Bewertungen
- Profile Neonet 2Dokument34 SeitenProfile Neonet 2neonetwirelessNoch keine Bewertungen
- Memorandum of Understanding (Mou) : Neonetwireless Nig LTD Translog Global ResourceDokument2 SeitenMemorandum of Understanding (Mou) : Neonetwireless Nig LTD Translog Global ResourceneonetwirelessNoch keine Bewertungen
- Neonet Training Proformer Invoice Training Sita NewDokument1 SeiteNeonet Training Proformer Invoice Training Sita NewneonetwirelessNoch keine Bewertungen
- Neonet Training Proformer Invoice Training Sita NewDokument1 SeiteNeonet Training Proformer Invoice Training Sita NewneonetwirelessNoch keine Bewertungen
- Neonet Training Proformer Invoice Training Sita NewDokument1 SeiteNeonet Training Proformer Invoice Training Sita NewneonetwirelessNoch keine Bewertungen
- Boq For Telecoms and Infotech/Software LabDokument4 SeitenBoq For Telecoms and Infotech/Software LabneonetwirelessNoch keine Bewertungen
- Profile Neonet 2Dokument34 SeitenProfile Neonet 2neonetwirelessNoch keine Bewertungen
- Neonet Training Proformer Invoice Training Sita NewDokument1 SeiteNeonet Training Proformer Invoice Training Sita NewneonetwirelessNoch keine Bewertungen
- Boq For Telecoms and Infotech/Software LabDokument4 SeitenBoq For Telecoms and Infotech/Software LabneonetwirelessNoch keine Bewertungen
- GSM Archtecture and TransmissionDokument2 SeitenGSM Archtecture and TransmissionneonetwirelessNoch keine Bewertungen
- Projects and PlanningDokument19 SeitenProjects and PlanningChristopher GauciNoch keine Bewertungen
- Huawie Microwave Radio Transmission Exam QuestionsDokument5 SeitenHuawie Microwave Radio Transmission Exam Questionsneonetwireless100% (2)
- Neonetwireless Registration FormDokument1 SeiteNeonetwireless Registration FormneonetwirelessNoch keine Bewertungen
- MICROWAVE RADIO COURSE 40KDokument4 SeitenMICROWAVE RADIO COURSE 40KneonetwirelessNoch keine Bewertungen
- SpieDokument12 SeitenSpieneonetwirelessNoch keine Bewertungen
- Onyemenam Ugochukwu George ResmeDokument4 SeitenOnyemenam Ugochukwu George ResmeneonetwirelessNoch keine Bewertungen
- Neonet MW Training Proformer InvoiceDokument1 SeiteNeonet MW Training Proformer InvoiceneonetwirelessNoch keine Bewertungen
- FIBER OPTICS TRANSMISSION ENGINEERING SlideDokument12 SeitenFIBER OPTICS TRANSMISSION ENGINEERING Slideneonetwireless100% (1)
- Ibeji Chukwuemeriwo's WirelessDokument4 SeitenIbeji Chukwuemeriwo's WirelessneonetwirelessNoch keine Bewertungen
- Ip Camera Course OutlineDokument2 SeitenIp Camera Course OutlineneonetwirelessNoch keine Bewertungen
- Integration Processes in The Telecommunication Sector in EuropeDokument14 SeitenIntegration Processes in The Telecommunication Sector in EuropeneonetwirelessNoch keine Bewertungen
- Time Table For All The CoursesDokument2 SeitenTime Table For All The CoursesneonetwirelessNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5784)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (890)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (72)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Triband Eight-Port Antenna: Opa65R-Ke4D Data SheetDokument13 SeitenTriband Eight-Port Antenna: Opa65R-Ke4D Data SheetGuillermoNoch keine Bewertungen
- Multistage AmplifierDokument22 SeitenMultistage AmplifierVijay AnandhNoch keine Bewertungen
- En Functional SafetyDokument52 SeitenEn Functional Safetyvalentin barnedaNoch keine Bewertungen
- Traction Motor Type Tm4907Bz: Technical DataDokument12 SeitenTraction Motor Type Tm4907Bz: Technical DataPratibha Patel100% (1)
- Register Transfer Methodology: PracticeDokument54 SeitenRegister Transfer Methodology: PracticeSrinivas CherukuNoch keine Bewertungen
- Railway Track Crack DetectionDokument24 SeitenRailway Track Crack Detectionraghuveertrilochan100% (1)
- 1 s2.0 S001999586590241X MainDokument48 Seiten1 s2.0 S001999586590241X MainNestor GlezNoch keine Bewertungen
- 15 Panel FabricationDokument36 Seiten15 Panel FabricationhkshahNoch keine Bewertungen
- Electrical Transformer Losses GuideDokument4 SeitenElectrical Transformer Losses GuidesauravNoch keine Bewertungen
- 1MW Rooftop Solar PV Power Plant Permit PDFDokument9 Seiten1MW Rooftop Solar PV Power Plant Permit PDFPadmanathan Kasinathan KNoch keine Bewertungen
- Objective Question - 1 (Information Theory and Coding)Dokument11 SeitenObjective Question - 1 (Information Theory and Coding)suganyamachendran66% (32)
- FAN7387 SMDDokument17 SeitenFAN7387 SMDHung KdNoch keine Bewertungen
- Knee Point Voltage of Current Transformer PS ClassDokument6 SeitenKnee Point Voltage of Current Transformer PS ClassNitesh patyalNoch keine Bewertungen
- UNIT5-Ground Wave Propagation PDFDokument44 SeitenUNIT5-Ground Wave Propagation PDFRameshbabu SadineniNoch keine Bewertungen
- RFP50N05LDokument6 SeitenRFP50N05LNegru P. PlantatieNoch keine Bewertungen
- Course: Manufacturing Science Lecture No.: 15 Arc Welding Power SourceDokument10 SeitenCourse: Manufacturing Science Lecture No.: 15 Arc Welding Power SourcezombieNoch keine Bewertungen
- Electronic dice displays random numbersDokument15 SeitenElectronic dice displays random numbersRoshan SuvarnaNoch keine Bewertungen
- AMPHENOL Series 3Dokument36 SeitenAMPHENOL Series 3PTCNoch keine Bewertungen
- Simple Tuned Adaptive PI Controller For Conical Tank ProcessDokument6 SeitenSimple Tuned Adaptive PI Controller For Conical Tank ProcessSadagopan RajaNoch keine Bewertungen
- Equipment Cross Reference GuideDokument22 SeitenEquipment Cross Reference GuideizmitlimonNoch keine Bewertungen
- SRT6KXLI Product Data SheetDokument4 SeitenSRT6KXLI Product Data Sheet3maligeNoch keine Bewertungen
- Pickup Wiring 1 ConductorDokument5 SeitenPickup Wiring 1 ConductorJD HNoch keine Bewertungen
- Acer Aspire 5720 5720G Service GuideDokument108 SeitenAcer Aspire 5720 5720G Service GuidejaggveNoch keine Bewertungen
- Ste Electronics Q1 Module 4-1Dokument21 SeitenSte Electronics Q1 Module 4-1aime jane abiadaNoch keine Bewertungen
- Inv Str-All AlarmCode&Troubleshooting en Rev.2012!05!06Dokument18 SeitenInv Str-All AlarmCode&Troubleshooting en Rev.2012!05!06Lucas NascimentoNoch keine Bewertungen
- Marantz SR 5004 Service Manual PDFDokument207 SeitenMarantz SR 5004 Service Manual PDFRobson LuizNoch keine Bewertungen
- Excite1 5TDokument43 SeitenExcite1 5TTihomir DrenovskiNoch keine Bewertungen
- Genesis Series ManualDokument16 SeitenGenesis Series ManualsashilaNoch keine Bewertungen
- New Acorn 180Dokument7 SeitenNew Acorn 180Anonymous KG9ThLMmA94% (17)
- Department Hand BookDokument157 SeitenDepartment Hand BookAraveetiCSReddyNoch keine Bewertungen