Beruflich Dokumente
Kultur Dokumente
06rr410504 Network Security and Cryptography
Hochgeladen von
andhracollegesOriginalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
06rr410504 Network Security and Cryptography
Hochgeladen von
andhracollegesCopyright:
Verfügbare Formate
www.andhracolleges.
com The Complete Information About Colleges in Andhra Pradesh
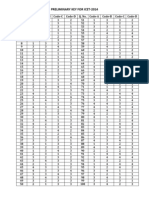
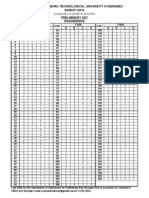
Code No: RR410504 Set No. 1
IV B.Tech I Semester Regular Examinations, November 2006
NETWORK SECURITY AND CRYPTOGRAPHY
(Computer Science & Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
⋆⋆⋆⋆⋆
www.andhracolleges.com
1. Discuss in detail Simple-DES.
2. Explain the process of encryption and decryption in IDEA algorithm.
3. (a) Explain public key Crypto Systems.
(b) Explain in detail about Euclid’s Algorithm.
(c) Give a brief account on Random number Generation.
4. (a) Explain Chinese Remainder Theorem.
[16M]
[16M]
[6M]
[5M]
[5M]
(b) Find all primitive roots of 7. [8+8]
5. (a) In what order should the signature function and the confidentiality function
be applied to message, and why?
(b) What are some threats associated with a direct digital signature scheme? [8+8]
6. (a) List limitations of SMTP/822 scheme?
(b) What are the MIME specifications? [8+8]
www.andhracolleges.com
7. (a) What are the basic approaches to building SAs?
(b) What are the roles of the Oakley key determination protocol and ISAKMP in
IPSec? [6+10]
8. (a) what information used by a typical packet-filtering router?
(b) What are some weaknesses of a packet-filtering router?
(c) What is the difference between a packet-filtering router and a stateful inspec-
tion firewall? [8+4+4]
⋆⋆⋆⋆⋆
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
1 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR410504 Set No. 2
IV B.Tech I Semester Regular Examinations, November 2006
NETWORK SECURITY AND CRYPTOGRAPHY
(Computer Science & Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
⋆⋆⋆⋆⋆
www.andhracolleges.com
1. (a) What is difference between diffusion and confusion?
(b) What is it importance to study the Feistel cipher?
2. Explain the process of encryption and decryption in RC5 algorithm.
3. Consider the following scheme
(a) Pick an odd number E
(b) Pick two prime numbers, P and Q, where (P-1)(Q-1)-1 is evenly distributed
by E
[6M]
[10M]
[16M]
(c) Multiply P and Q to get N
(d) Calculate D = (P −1)(Q−1)(E−1)+1
E
Is this scheme is equivalent to RSA ? Show why or why not [16M]
4. (a) what is a primitive root of a number?
(b) Find all primitive roots of 7.
(c) Using Fermat’s theorem, find 3201 mod 11. [6M+6M+4M]
www.andhracolleges.com
5. Define digital Signature. Explain its role in network security. [16M]
6. (a) Discuss cryptographic algorithms used in S/MIME
(b) List limitations of SMTP/822 scheme? [8+8]
7. (a) What are the basic approaches to building SAs?
(b) What are the roles of the Oakley key determination protocol and ISAKMP in
IPSec? [6+10]
8. Write notes on
(a) Trapdoors
(b) Logic bomb
(c) Trojan horses [5+5+6]
⋆⋆⋆⋆⋆
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
1 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR410504 Set No. 3
IV B.Tech I Semester Regular Examinations, November 2006
NETWORK SECURITY AND CRYPTOGRAPHY
(Computer Science & Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
⋆⋆⋆⋆⋆
www.andhracolleges.com
1. This problem provides a numerical example of encryption using a one-round version
of DES. We start with the same bit pattern for the key and plain text, namely,
In hexadecimal notation 0 1 2 3 4 5 6 7 8 9 A B C D E F
Inbinary notation: 0000 0001 0010 0011 0100 0101 0110 0111
1000 1001 1010 1011 1100 1101 1110 1111
(a) Derive K1 , the first - round subkey.
(b) Derive L0 , R0
(c) Expand R0 to get E[R0 ]
(d) Calculate A=E[R0 ] ⊕ K1 .
(e) Group the 48-bit result of (d) into sets of 6 bits and evaluate the corresponding
S-box substitutions.
(f) Cancatenate the results of (e) to get a 32-bit result,B.
(g) Apply the permutation to get P(B).
(h) Calculate R1=P(B) ⊕ L0
www.andhracolleges.com
(i) write down the cipher text. [16M]
2. Demonstrate that Blow Fish decryption is inverse of Blowfish encryption. [16M]
3. (a) Explain RSA Algorithm? [8M]
(b) In a RSA system, the public key of a given user is e=31,n=3599.What is the
private key of this user? [8M]
4. (a) Explain in detail about Extended Euclid’s Algorithm.
(b) Determine Multiplicative inverse of 550 in GF(1759). [8+8]
5. (a) what are digital signature standards?
(b) Explain Digital signature algorithm. [8+8]
6. (a) What problem was Kerberos designed to address?
(b) What are three threats associated with user authentication over a network or
Internet?
(c) List three approaches to secure user authentication over a network or Internet?
[4+4+8]
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR410504 Set No. 3
7. Write note on Encapsulating security payload. [16]
8. (a) what information used by a typical packet-filtering router?
(b) What are some weaknesses of a packet-filtering router?
(c) What is the difference between a packet-filtering router and a stateful inspec-
tion firewall? [8+4+4]
www.andhracolleges.com
⋆⋆⋆⋆⋆
www.andhracolleges.com
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
2 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR410504 Set No. 4
IV B.Tech I Semester Regular Examinations, November 2006
NETWORK SECURITY AND CRYPTOGRAPHY
(Computer Science & Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
All Questions carry equal marks
⋆⋆⋆⋆⋆
www.andhracolleges.com
1. Write short notes on :
(a) Avalanche effect
(b) Diffusion and confusion
(c) Steganography
(d) Caesar cipher
2. Explain the process of encryption and decryption in RC5 algorithm.
3. (a) Illustrate Diffie-hellman Key Exchange scheme for GF(P)
[4M]
[4M]
[4M]
[4M]
[16M]
[6M]
(b) Consider a diffie-helman scheme with a common prime q=11 and a primitive
rootα=2
i. If user A has public key YA = 9, what is A’s private key XA ?
ii. If user B has public key YB = 3, what is the shared key K? [10M]
4. (a) State and prove Fermat’s theorem?
(b) State and prove Euler’s theorem?
(c) Using Fermat’s theorem, find 3201 mod 11.
www.andhracolleges.com
[5M+5M+6M]
5. (a) What is the difference between weak and strong collision resistance?
(b) What is the role of a compression function in a hash function? [6+10]
6. (a) What problem was Kerberos designed to address?
(b) What are three threats associated with user authentication over a network or
Internet?
(c) List three approaches to secure user authentication over a network or Internet?
[4+4+8]
7. (a) What are the basic approaches to building SAs?
(b) What are the roles of the Oakley key determination protocol and ISAKMP in
IPSec? [6+10]
8. (a) List and briefly define four techniques used to avoid guessable password?
(b) In general terms, how does a worm propagate? [8+8]
⋆⋆⋆⋆⋆
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
1 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
Das könnte Ihnen auch gefallen
- Eamcet Agriculture Last Ranks Cutoffs Andhracolleges Eamcet 2013 CutoffsDokument3 SeitenEamcet Agriculture Last Ranks Cutoffs Andhracolleges Eamcet 2013 Cutoffsandhracolleges33% (3)
- Polycet2014 Web Counselling NotificationDokument2 SeitenPolycet2014 Web Counselling NotificationandhracollegesNoch keine Bewertungen
- Polycet 2014 ST Certificatates Verification DatesDokument1 SeitePolycet 2014 ST Certificatates Verification DatesandhracollegesNoch keine Bewertungen
- EAMCET 2014 Agriculture & Medical Preliminary Answer KeysDokument1 SeiteEAMCET 2014 Agriculture & Medical Preliminary Answer KeysLohith_EnggNoch keine Bewertungen
- Eamcet 2014 Engineering Key Solutions AndhracollegesDokument42 SeitenEamcet 2014 Engineering Key Solutions Andhracollegesandhracolleges75% (8)
- Polycet 2014 SC BC Oc Certificatates Verification DatesDokument1 SeitePolycet 2014 SC BC Oc Certificatates Verification DatesandhracollegesNoch keine Bewertungen
- ICET 2014 Preliminary Key Primary Key AndhracollegesDokument2 SeitenICET 2014 Preliminary Key Primary Key AndhracollegesandhracollegesNoch keine Bewertungen
- JEE Advanced 2014 Paper I Chemistry Paper Answer SolutionsDokument4 SeitenJEE Advanced 2014 Paper I Chemistry Paper Answer SolutionsandhracollegesNoch keine Bewertungen
- JEE Main Advanced 2014 Paper I Maths Paper Answer SolutionsDokument4 SeitenJEE Main Advanced 2014 Paper I Maths Paper Answer Solutionsandhracolleges100% (1)
- JEE Main Advanced Paper I Answer Key 25 May 2014Dokument1 SeiteJEE Main Advanced Paper I Answer Key 25 May 2014andhracollegesNoch keine Bewertungen
- JEE Advanced 2014 Paper I PHYSICS Paper Answer SolutionsDokument6 SeitenJEE Advanced 2014 Paper I PHYSICS Paper Answer SolutionsandhracollegesNoch keine Bewertungen
- Eamcet 2014 Engineering Jntu Preliminary Key AndhracollegesDokument1 SeiteEamcet 2014 Engineering Jntu Preliminary Key AndhracollegesandhracollegesNoch keine Bewertungen
- Eamcet 2013 Engineering PaperDokument62 SeitenEamcet 2013 Engineering Paperandhracolleges0% (1)
- Eamcet 2014 Engineering Key SolutionsDokument42 SeitenEamcet 2014 Engineering Key Solutionsandhracolleges100% (1)
- Eamcet 2014 Medical Question Paper With Key Solutions AndhracollegesDokument62 SeitenEamcet 2014 Medical Question Paper With Key Solutions Andhracollegesandhracolleges100% (1)
- Eamcet 2013 Medical PaperDokument62 SeitenEamcet 2013 Medical PaperandhracollegesNoch keine Bewertungen
- Eamcet 2014 Medical Question Paper AndhracollegesDokument62 SeitenEamcet 2014 Medical Question Paper Andhracollegesandhracolleges100% (1)
- Andhracollege Eamcet 2014 Engineering Question Paper With Key SolutionsDokument62 SeitenAndhracollege Eamcet 2014 Engineering Question Paper With Key Solutionsandhracolleges50% (4)
- Eamcet 2011 Engineering PaperDokument61 SeitenEamcet 2011 Engineering PaperandhracollegesNoch keine Bewertungen
- Eamcet 2012 Engineering Paper KeyDokument1 SeiteEamcet 2012 Engineering Paper KeyandhracollegesNoch keine Bewertungen
- Eamcet 2012 Medical Paper KeyDokument1 SeiteEamcet 2012 Medical Paper KeyandhracollegesNoch keine Bewertungen
- Polycet 2014 Question PaperDokument24 SeitenPolycet 2014 Question PaperandhracollegesNoch keine Bewertungen
- Eamcet 2012 Medical PaperDokument60 SeitenEamcet 2012 Medical Paperandhracolleges100% (1)
- Eamcet 2010 Medical PaperDokument63 SeitenEamcet 2010 Medical PaperandhracollegesNoch keine Bewertungen
- Eamcet 2012 Engineering Paper KeyDokument1 SeiteEamcet 2012 Engineering Paper KeyandhracollegesNoch keine Bewertungen
- Eamcet 2008 Engineering PaperDokument62 SeitenEamcet 2008 Engineering PaperandhracollegesNoch keine Bewertungen
- Eamcet 2012 Engineering PaperDokument62 SeitenEamcet 2012 Engineering Paperandhracolleges100% (1)
- Eamcet 2007 Engineering PaperDokument13 SeitenEamcet 2007 Engineering Paperandhracolleges100% (1)
- Eamcet 2009 Engineering Chemistry PaperDokument16 SeitenEamcet 2009 Engineering Chemistry PaperandhracollegesNoch keine Bewertungen
- Eamcet 2006 Engineering PaperDokument14 SeitenEamcet 2006 Engineering PaperandhracollegesNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5783)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (890)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (72)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Implementacion de Algoritmos Cuanticos para PrincipiantesDokument94 SeitenImplementacion de Algoritmos Cuanticos para PrincipiantesBrandon Matthew Ruvalcaba CardenasNoch keine Bewertungen
- K-Means Clustering Algorithm Described in DetailDokument10 SeitenK-Means Clustering Algorithm Described in Detailadin80Noch keine Bewertungen
- 1 for - w - ≤ 6 0 for 6 ≤ -: H e e, 0≤w≤ π π w≤πDokument3 Seiten1 for - w - ≤ 6 0 for 6 ≤ -: H e e, 0≤w≤ π π w≤πAnonymous Ndsvh2soNoch keine Bewertungen
- Lesson 3.1 One To OneDokument25 SeitenLesson 3.1 One To OneMaricris OcampoNoch keine Bewertungen
- Backpropagation and gradient descent quiz answersDokument8 SeitenBackpropagation and gradient descent quiz answersJonafe Piamonte0% (1)
- CS502 Finl Term Hndsout by Dream TeamDokument88 SeitenCS502 Finl Term Hndsout by Dream Teamfakhira siddiqNoch keine Bewertungen
- Regularization Lecture: LASSO and Ridge RegressionDokument30 SeitenRegularization Lecture: LASSO and Ridge Regressionmayb3todayNoch keine Bewertungen
- Nc7201 Communication Network Security L T P CDokument1 SeiteNc7201 Communication Network Security L T P CAfrin BanuNoch keine Bewertungen
- New inrush detection method for transformer protection using instantaneous frequencyDokument14 SeitenNew inrush detection method for transformer protection using instantaneous frequencyMilovan LukovacNoch keine Bewertungen
- HW3 11 SolDokument5 SeitenHW3 11 SolShang Divina EbradaNoch keine Bewertungen
- A Strict Lyapunov Funtion For The Simple Pendulum - R.Kelly - V.SantibañezDokument5 SeitenA Strict Lyapunov Funtion For The Simple Pendulum - R.Kelly - V.SantibañezdiabelliforlifeNoch keine Bewertungen
- Quantifying Uncertainty in Pls Sem Based Mediation AnalysesDokument11 SeitenQuantifying Uncertainty in Pls Sem Based Mediation AnalysesAlessandra CassolNoch keine Bewertungen
- Block Diagram and Transfer FunctionsDokument20 SeitenBlock Diagram and Transfer FunctionsBatuhan Mutlugil 'Duman'Noch keine Bewertungen
- Chapter 2 2 HandoutsDokument8 SeitenChapter 2 2 Handoutsmeseret sisayNoch keine Bewertungen
- Spectral Clustering Tutorial for Image ClusteringDokument52 SeitenSpectral Clustering Tutorial for Image ClusteringReshma KhemchandaniNoch keine Bewertungen
- Genetic algorithms introduction with JGAP framework exampleDokument7 SeitenGenetic algorithms introduction with JGAP framework exampleLuis MoralesNoch keine Bewertungen
- Unknown Input Nonlinear Observer Design For Continuous and Discrete Time Systems With Input Recovery SchemeDokument14 SeitenUnknown Input Nonlinear Observer Design For Continuous and Discrete Time Systems With Input Recovery SchemeRanjit SinghNoch keine Bewertungen
- Convolutional neural networks for text classification: Implementing forward, backward and gradient checkingDokument3 SeitenConvolutional neural networks for text classification: Implementing forward, backward and gradient checkingYvonne Yifan ZhouNoch keine Bewertungen
- Sample Exam II PDFDokument2 SeitenSample Exam II PDFArsen DuisenbayNoch keine Bewertungen
- Horizon Academic Research Journal Vol. 4 No. 1Dokument406 SeitenHorizon Academic Research Journal Vol. 4 No. 1Horizon AcademicNoch keine Bewertungen
- Numerical AnalysisDokument114 SeitenNumerical AnalysisGuruKPONoch keine Bewertungen
- BCSE I A2 Group CPNM Assignment 3: (Optional)Dokument2 SeitenBCSE I A2 Group CPNM Assignment 3: (Optional)Anurag BandyopadhyayNoch keine Bewertungen
- Data Structures & Algorithm Course Outline PDFDokument2 SeitenData Structures & Algorithm Course Outline PDFAmmar Ajmal0% (1)
- HouseholderDokument9 SeitenHouseholderKhairil Sangbima100% (1)
- Present and CompoundDokument3 SeitenPresent and CompoundTricia LuceroNoch keine Bewertungen
- Neural Networks Cheat Sheet - 2020 PDFDokument14 SeitenNeural Networks Cheat Sheet - 2020 PDFjoseacvNoch keine Bewertungen
- CNN Object Detection Currency RecognitionDokument6 SeitenCNN Object Detection Currency RecognitionNatasha AdvaniNoch keine Bewertungen
- Exploratory Data Analysis & Data PreprocessingDokument16 SeitenExploratory Data Analysis & Data Preprocessinganirudh031090Noch keine Bewertungen
- 2017 - April - Automatic Recognition of Medicinal Plants Using Machine Learning TechniquesDokument10 Seiten2017 - April - Automatic Recognition of Medicinal Plants Using Machine Learning TechniquesSameerchand PudaruthNoch keine Bewertungen
- Eda 2Dokument21 SeitenEda 2Riya SinghNoch keine Bewertungen