Beruflich Dokumente
Kultur Dokumente
Srr320503 Computer Networks
Hochgeladen von
andhracollegesOriginalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Srr320503 Computer Networks
Hochgeladen von
andhracollegesCopyright:
Verfügbare Formate
www.andhracolleges.
com The Complete Information About Colleges in Andhra Pradesh
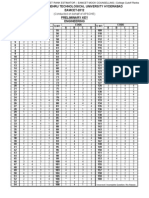
Code No: RR320503 Set No. 1
III B.Tech II Semester Supplimentary Examinations, Aug/Sep 2007
COMPUTER NETWORKS
( Common to Computer Science & Engineering, Information Technology,
Electronics & Control Engineering, Computer Science & Systems
Engineering and Electronics & Computer Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
www.andhracolleges.com
All Questions carry equal marks
⋆⋆⋆⋆⋆
1. (a) Two networks each provide a reliable connection oriented service. One of them
offers a reliable byte stream and other offers a reliable message stream. Are
they identical? If so, why is distinction made? If not give an example of how
they differ?
(b) List two advantages and two disadvantages of having international standards
for network, Protocols? [8+8]
2. (a) The following data fragment occurs in the middle of a data stream for which
the character-stuffing algorithm described in the text is used: DLE, STX, A,
DLE, B, DLE, ETX. What is the output after stuffing?
(b) When bit stuffing is used, is it possible for the loss, insertion, or modification
of a single bit to cause an error not detected by the checksum? If not, why
not? If so, how? Does the checksum length play a role here?
(c) Data link protocols almost always put the CRC in a trailer, rather than in a
header.Why? [6+6+4]
www.andhracolleges.com
3. (a) What is bridge? Explain the operation of a LAN bridge from 802.3 to 802.4.
(b) Explain the operation of transparent bridge. [8+8]
4. (a) Give three examples of protocol parameters that might be negotiated when a
connection is set up.
(b) Are there any circumstances when a virtual circuit service will (or at least
should) deliver packets out of order? Explain.
(c) Assuming that all routers and hosts are working properly and that all software
in both is free of all errors, is there any chance, however small, that a packet
will be delivered to the wrong destination? [6+6+4]
5. (a) Briefly explain the concepts of Flow Control and Buffering.
(b) Imagine that a two-way handshake rather than a three-way handshake were
used to set up connections. In other words, the third message was not required.
Are deadlocks now possible? Give an example or show that none exist. [8+8]
6. (a) Briefly discuss about the ways network can differ.
(b) Explain in detail Firewall operation. [8+8]
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR320503 Set No. 1
7. (a) What is Nagle’s algorithm? Explain the problem of silly window syndrome:
suggest a solution to this problem.
(b) Draw and explain the AAL1 cell format, headers and trailers. [8+8]
8. (a) What is DNS? Briefly discuss DNS Namespace.
(b) Explain, in detail principal DNS resource record types. [8+8]
www.andhracolleges.com
⋆⋆⋆⋆⋆
www.andhracolleges.com
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
2 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR320503 Set No. 2
III B.Tech II Semester Supplimentary Examinations, Aug/Sep 2007
COMPUTER NETWORKS
( Common to Computer Science & Engineering, Information Technology,
Electronics & Control Engineering, Computer Science & Systems
Engineering and Electronics & Computer Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
www.andhracolleges.com
All Questions carry equal marks
⋆⋆⋆⋆⋆
1. (a) List two advantages and two disadvantages of having international standards
for network, Protocols?
(b) With a neat diagram, explain the functionality of layers, protocols and inter-
faces. [8+8]
2. (a) The following data fragment occurs in the middle of a data stream for which
the character-stuffing algorithm described in the text is used: DLE, STX, A,
DLE, B, DLE, ETX. What is the output after stuffing?
(b) When bit stuffing is used, is it possible for the loss, insertion, or modification
of a single bit to cause an error not detected by the checksum? If not, why
not? If so, how? Does the checksum length play a role here?
(c) Data link protocols almost always put the CRC in a trailer, rather than in a
header.Why? [6+6+4]
3. (a) What is time domain reflectometry? Write about 802.3 cabling.
www.andhracolleges.com
(b) Draw and Explain 802.3 frame format. [8+8]
4. (a) A computer on a 6-Mbps network is regulated by a token bucket. The token
bucket is filled at a rate of 1Mbps. It is initially filled to capacity with 8
megabits. How long can the computer transmit at the full 6 Mbps?
(b) Briefly discuss about congestion control in VC subnets. [8+8]
5. (a) Imagine a generalized n-army problem, in which the agreement of any two of
the armies is sufficient for victory. Does a protocol exist that allows blue to
win?
(b) Suppose that the clock-driven scheme for generating initial sequence numbers
is used with a 15-bit wide clock counter. The clock ticks once every 100msec,
and the maximum packet lifetime is 60sec. How often need resynchronization
take place
i. in the worst case?
ii. when the data consumes 240 sequence numbers/min?
(c) Why does the maximum packet lifetime, T, have to be large enough to ensure
that not only the packet, but also its acknowledgements, have vanished?
[6+6+4]
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR320503 Set No. 2
6. (a) What is tunneling? When it is used? Is it used in wireless LAN’s?
(b) Briefly discuss about connection less Internetworking. [8+8]
7. (a) Draw and explain the structure of the ATM Adaptation layer.
(b) Draw and explain the AAL1 cell format, headers and trailers. [8+8]
8. (a) Explain in detail methods of DES chaining.
www.andhracolleges.com
(b) Briefly discuss about IDEA. [8+8]
⋆⋆⋆⋆⋆
www.andhracolleges.com
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
2 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR320503 Set No. 3
III B.Tech II Semester Supplimentary Examinations, Aug/Sep 2007
COMPUTER NETWORKS
( Common to Computer Science & Engineering, Information Technology,
Electronics & Control Engineering, Computer Science & Systems
Engineering and Electronics & Computer Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
www.andhracolleges.com
All Questions carry equal marks
⋆⋆⋆⋆⋆
1. (a) Two networks each provide a reliable connection oriented service. One of them
offers a reliable byte stream and other offers a reliable message stream. Are
they identical? If so, why is distinction made? If not give an example of how
they differ?
(b) List two advantages and two disadvantages of having international standards
for network, Protocols? [8+8]
2. (a) Imagine a sliding window protocol using so many bits for sequence numbers
that wrap around never occurs. What relations must hold among the four
window edges and the window size?
(b) PPP is based closely on HDLC, which uses bit stuffing to prevent accidental
flag bytes within the payload from causing confusion. Give at least one reason
why PPP uses character stuffing instead. [8+8]
3. (a) Explain five key Assumptions in Dynamic channel allocation in LANs and
MANs.
www.andhracolleges.com
(b) Explain the multiple access protocol using which the stations about their trans-
missions as soon as they detect a collision? [8+8]
4. (a) With an example, explain Hierarchical Routing Algorithm.
(b) With an example, explain multicast Routing Algorithm. [8+8]
5. (a) Briefly discuss about Transport Layer quality of service parameters.
(b) Define the following terms.
i. Option Negotiation
ii. Transport quality
iii. Transport service user
iv. Transport service provider. [8+8]
6. (a) Briefly discuss ICMP.
(b) With an example, explain Address resolution protocol. [8+8]
7. (a) Give the format of UDP segment and TCP segment? Explain when UDP is
preferred to TCP?
(b) What are blocking calls, primitives and non-blocking primitives? [8+8]
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR320503 Set No. 3
8. (a) What is MOSPF? Discuss briefly about Multicast Backbone.
(b) Draw and Explain the hardware architecture of a Simple set-top box. [8+8]
⋆⋆⋆⋆⋆
www.andhracolleges.com
www.andhracolleges.com
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
2 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR320503 Set No. 4
III B.Tech II Semester Supplimentary Examinations, Aug/Sep 2007
COMPUTER NETWORKS
( Common to Computer Science & Engineering, Information Technology,
Electronics & Control Engineering, Computer Science & Systems
Engineering and Electronics & Computer Engineering)
Time: 3 hours Max Marks: 80
Answer any FIVE Questions
www.andhracolleges.com
All Questions carry equal marks
⋆⋆⋆⋆⋆
1. (a) List two advantages and two disadvantages of having international standards
for network, Protocols?
(b) Write short notes on interfaces and services of ISO layers. [8+8]
2. (a) The following data fragment occurs in the middle of a data stream for which
the character-stuffing algorithm described in the text is used: DLE, STX, A,
DLE, B, DLE, ETX. What is the output after stuffing?
(b) When bit stuffing is used, is it possible for the loss, insertion, or modification
of a single bit to cause an error not detected by the checksum? If not, why
not? If so, how? Does the checksum length play a role here?
(c) Data link protocols almost always put the CRC in a trailer, rather than in a
header.Why? [6+6+4]
3. (a) Explain static channel allocation in LANs and MANs.
(b) Explain five key Assumptions in Dynamic channel allocation in LANs and
www.andhracolleges.com
MANs. [8+8]
4. (a) What is Broadcasting? With an example, explain about Reverse path for-
warding
(b) With an example, explain multicast Routing Algorithm. [8+8]
5. (a) What is forbidden region? Explain three-way handshake protocol used for
establishing connection.
(b) Explain in detail Four protocol scenarios for releasing a connection. [8+8]
6. (a) Briefly discuss about Concatenated Virtual Circuits.
(b) Explain firewalls, packet filter and a proxy in detail. [8+8]
7. (a) Why does the maximum packet lifetime, T, have to be large enough to ensure
that not only the packet, but also its acknowledgements, have vanished?
(b) AAL 3/4 allows multiple sessions to be multiplexed onto a single virtual circuit.
Give an example of a situation in which that has no value. Assume that one
virtual circuit has sufficient bandwidth to carry all the traffic.
(c) What is the payload size of the maximum length message that fits in a single
AAL 3/4 cell? [5+6+5]
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
1 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
www.andhracolleges.com The Complete Information About Colleges in Andhra Pradesh
Code No: RR320503 Set No. 4
8. (a) What is the role of SMI in network management?
(b) What is a key distribution centre? What is a certificate authority?
(c) In what way does a public key encrypted message digest provide a “better”
digital signature than using public key encrypted message? [5+6+5]
⋆⋆⋆⋆⋆
www.andhracolleges.com
www.andhracolleges.com
Seminar Topics - Scholarships - Admission/Entrance Exam Notifications
2 ofUSA-UK-Australia-Germany-France-NewZealand
2 Universities List
www.andhracolleges.com Engineering-MBA-MCA-Medical-Pharmacy-B.Ed-Law Colleges Information
Das könnte Ihnen auch gefallen
- Polycet 2014 SC BC Oc Certificatates Verification DatesDokument1 SeitePolycet 2014 SC BC Oc Certificatates Verification DatesandhracollegesNoch keine Bewertungen
- Polycet2014 Web Counselling NotificationDokument2 SeitenPolycet2014 Web Counselling NotificationandhracollegesNoch keine Bewertungen
- Eamcet Agriculture Last Ranks Cutoffs Andhracolleges Eamcet 2013 CutoffsDokument3 SeitenEamcet Agriculture Last Ranks Cutoffs Andhracolleges Eamcet 2013 Cutoffsandhracolleges33% (3)
- Polycet 2014 ST Certificatates Verification DatesDokument1 SeitePolycet 2014 ST Certificatates Verification DatesandhracollegesNoch keine Bewertungen
- JEE Main Advanced 2014 Paper I Maths Paper Answer SolutionsDokument4 SeitenJEE Main Advanced 2014 Paper I Maths Paper Answer Solutionsandhracolleges100% (1)
- JEE Main Advanced Paper I Answer Key 25 May 2014Dokument1 SeiteJEE Main Advanced Paper I Answer Key 25 May 2014andhracollegesNoch keine Bewertungen
- ICET 2014 Preliminary Key Primary Key AndhracollegesDokument2 SeitenICET 2014 Preliminary Key Primary Key AndhracollegesandhracollegesNoch keine Bewertungen
- Eamcet 2014 Medical Question Paper AndhracollegesDokument62 SeitenEamcet 2014 Medical Question Paper Andhracollegesandhracolleges100% (1)
- Eamcet 2012 Medical PaperDokument60 SeitenEamcet 2012 Medical Paperandhracolleges100% (1)
- JEE Advanced 2014 Paper I Chemistry Paper Answer SolutionsDokument4 SeitenJEE Advanced 2014 Paper I Chemistry Paper Answer SolutionsandhracollegesNoch keine Bewertungen
- Eamcet 2014 Engineering Jntu Preliminary Key AndhracollegesDokument1 SeiteEamcet 2014 Engineering Jntu Preliminary Key AndhracollegesandhracollegesNoch keine Bewertungen
- EAMCET 2014 Agriculture & Medical Preliminary Answer KeysDokument1 SeiteEAMCET 2014 Agriculture & Medical Preliminary Answer KeysLohith_EnggNoch keine Bewertungen
- JEE Advanced 2014 Paper I PHYSICS Paper Answer SolutionsDokument6 SeitenJEE Advanced 2014 Paper I PHYSICS Paper Answer SolutionsandhracollegesNoch keine Bewertungen
- Eamcet 2014 Engineering Key Solutions AndhracollegesDokument42 SeitenEamcet 2014 Engineering Key Solutions Andhracollegesandhracolleges75% (8)
- Eamcet 2014 Medical Question Paper With Key Solutions AndhracollegesDokument62 SeitenEamcet 2014 Medical Question Paper With Key Solutions Andhracollegesandhracolleges100% (1)
- Andhracollege Eamcet 2014 Engineering Question Paper With Key SolutionsDokument62 SeitenAndhracollege Eamcet 2014 Engineering Question Paper With Key Solutionsandhracolleges50% (4)
- Eamcet 2014 Engineering Key SolutionsDokument42 SeitenEamcet 2014 Engineering Key Solutionsandhracolleges100% (1)
- Eamcet 2013 Engineering PaperDokument62 SeitenEamcet 2013 Engineering Paperandhracolleges0% (1)
- Polycet 2014 Question PaperDokument24 SeitenPolycet 2014 Question PaperandhracollegesNoch keine Bewertungen
- Eamcet 2012 Engineering PaperDokument62 SeitenEamcet 2012 Engineering Paperandhracolleges100% (1)
- Eamcet 2012 Medical Paper KeyDokument1 SeiteEamcet 2012 Medical Paper KeyandhracollegesNoch keine Bewertungen
- Eamcet 2012 Engineering Paper KeyDokument1 SeiteEamcet 2012 Engineering Paper KeyandhracollegesNoch keine Bewertungen
- Eamcet 2012 Engineering Paper KeyDokument1 SeiteEamcet 2012 Engineering Paper KeyandhracollegesNoch keine Bewertungen
- Eamcet 2008 Engineering PaperDokument62 SeitenEamcet 2008 Engineering PaperandhracollegesNoch keine Bewertungen
- Eamcet 2007 Engineering PaperDokument13 SeitenEamcet 2007 Engineering Paperandhracolleges100% (1)
- Eamcet 2010 Medical PaperDokument63 SeitenEamcet 2010 Medical PaperandhracollegesNoch keine Bewertungen
- Eamcet 2011 Engineering PaperDokument61 SeitenEamcet 2011 Engineering PaperandhracollegesNoch keine Bewertungen
- Eamcet 2013 Medical PaperDokument62 SeitenEamcet 2013 Medical PaperandhracollegesNoch keine Bewertungen
- Eamcet 2009 Engineering Chemistry PaperDokument16 SeitenEamcet 2009 Engineering Chemistry PaperandhracollegesNoch keine Bewertungen
- Eamcet 2006 Engineering PaperDokument14 SeitenEamcet 2006 Engineering PaperandhracollegesNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Ifs Audit ReportDokument74 SeitenIfs Audit ReportOzlem Mep67% (3)
- Svcet: Unit IV Traveling Waves On Transmission LineDokument21 SeitenSvcet: Unit IV Traveling Waves On Transmission LineDeepak CoolNoch keine Bewertungen
- 12 F 1501Dokument278 Seiten12 F 1501Marianna GulyásNoch keine Bewertungen
- York Ylcs 725 HaDokument52 SeitenYork Ylcs 725 HaDalila Ammar100% (2)
- An Introduction To Java Programming 3Dokument179 SeitenAn Introduction To Java Programming 3Aleksandar Dutina100% (2)
- Cybersecurity Essentials 1.0 Release Notes: PurposeDokument5 SeitenCybersecurity Essentials 1.0 Release Notes: PurposeRonny Kimer Fiestas VargasNoch keine Bewertungen
- F1160 1479757-1Dokument8 SeitenF1160 1479757-1Thaweekarn ChangthongNoch keine Bewertungen
- Company Work Execution Plan For A Long Form ContractDokument4 SeitenCompany Work Execution Plan For A Long Form Contractshojaee1063Noch keine Bewertungen
- Ina201 Industrial Network ArchitectureDokument2 SeitenIna201 Industrial Network ArchitectureFranNoch keine Bewertungen
- BOXER NH TC35DA TC40DA TC45DA Mount Instructions PDFDokument16 SeitenBOXER NH TC35DA TC40DA TC45DA Mount Instructions PDFjwdNoch keine Bewertungen
- A Brief Tutorial On Interval Type-2 Fuzzy Sets and SystemsDokument10 SeitenA Brief Tutorial On Interval Type-2 Fuzzy Sets and SystemstarekeeeNoch keine Bewertungen
- The Power of Slope SpectrosDokument2 SeitenThe Power of Slope SpectrosJohn SiricoNoch keine Bewertungen
- A Seminar Report On Virtualization Techniques in Cloud - ComputingDokument33 SeitenA Seminar Report On Virtualization Techniques in Cloud - ComputingParth AgarwalNoch keine Bewertungen
- Shot Blasting Machines: Laser PeeningDokument2 SeitenShot Blasting Machines: Laser Peeningrahul srivastavaNoch keine Bewertungen
- KW Tedder LeafletDokument32 SeitenKW Tedder Leafletinfo4826Noch keine Bewertungen
- Photography Is The: PictureDokument3 SeitenPhotography Is The: PictureJrom EcleoNoch keine Bewertungen
- Troubleshooting Data: Plug Seen From The Cable SideDokument2 SeitenTroubleshooting Data: Plug Seen From The Cable SideTomyNoch keine Bewertungen
- Tesco Shop On The GoDokument3 SeitenTesco Shop On The GoIkram KhokharNoch keine Bewertungen
- Analog Servo Drive: Description Power RangeDokument9 SeitenAnalog Servo Drive: Description Power RangeElectromateNoch keine Bewertungen
- Ethics Approval Process 20150223Dokument8 SeitenEthics Approval Process 20150223MPTScribidNoch keine Bewertungen
- Reservoir SimulationDokument75 SeitenReservoir SimulationEslem Islam100% (9)
- System Development Process: The Incremental Commitment ModelDokument20 SeitenSystem Development Process: The Incremental Commitment Modeloctopus2011Noch keine Bewertungen
- Quality Control TechniquesDokument10 SeitenQuality Control Techniquesdevilunleashed090% (1)
- E-Content #03 (RSR) Thesis and Research Paper Writing - A BriefDokument2 SeitenE-Content #03 (RSR) Thesis and Research Paper Writing - A Briefaravind mouryaNoch keine Bewertungen
- Norphonic VoIP D10003Dokument2 SeitenNorphonic VoIP D10003Topcom Toki-VokiNoch keine Bewertungen
- Windpro Directory - 04.02.11Dokument54 SeitenWindpro Directory - 04.02.11Krishnan Veeraraghavan100% (1)
- Final Drive Transmission Assembly - Prior To SN Dac0202754 (1) 9030Dokument3 SeitenFinal Drive Transmission Assembly - Prior To SN Dac0202754 (1) 9030Caroline RosaNoch keine Bewertungen
- Chato Vs HRETDokument1 SeiteChato Vs HRETTyrone HernandezNoch keine Bewertungen
- Elcometer 130: Soluble Salt ProfilerDokument8 SeitenElcometer 130: Soluble Salt ProfilerRomualdo CarlosNoch keine Bewertungen
- An Overview of Transceiver SystemsDokument11 SeitenAn Overview of Transceiver SystemssurvivalofthepolyNoch keine Bewertungen