Beruflich Dokumente
Kultur Dokumente
37 1
Hochgeladen von
Gilbert OddoOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
37 1
Hochgeladen von
Gilbert OddoCopyright:
Verfügbare Formate
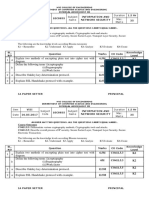
Packet Tracer Configuring VPNs (Optional)
Topology
Addressing Table
Device
Interface
IP Address
Subnet Mask
Default Gateway
G0/0
192.168.1.1
255.255.255.0
N/A
S0/0/0
10.1.1.2
255.255.255.252
N/A
G0/0
192.168.2.1
255.255.255.0
N/A
S0/0/0
10.1.1.1
255.255.255.252
N/A
S0/0/1
10.2.2.1
255.255.255.252
N/A
G0/0
192.168.3.1
255.255.255.0
N/A
S0/0/1
10.2.2.2
255.255.255.252
N/A
PC-A
NIC
192.168.1.3
255.255.255.0
192.168.1.1
PC-B
NIC
192.168.2.3
255.255.255.0
192.168.2.1
PC-C
NIC
192.168.3.3
255.255.255.0
192.168.3.1
R1
R2
R3
2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public.
Page 1 of 6
Packet Tracer Configuring VPNs (Optional)
ISAKMP Phase 1 Policy Parameters
Parameters
R1
R3
Key distribution method
Manual or ISAKMP
ISAKMP
ISAKMP
Encryption algorithm
DES, 3DES, or AES
AES
AES
Hash algorithm
MD5 or SHA-1
SHA-1
SHA-1
Authentication method
Pre-shared keys or RSA
pre-share
pre-share
Key exchange
DH Group 1, 2, or 5
DH 2
DH 2
IKE SA Lifetime
86400 seconds or less
86400
86400
cisco
cisco
ISAKMP Key
Bolded parameters are defaults. Other parameters need to be explicitly configured.
IPsec Phase 2 Policy Parameters
Parameters
R1
R3
Transform Set
VPN-SET
VPN-SET
Peer Hostname
R3
R1
Peer IP Address
10.2.2.2
10.1.1.2
Network to be encrypted
192.168.1.0/24
192.168.3.0/24
Crypto Map name
VPN-MAP
VPN-MAP
SA Establishment
ipsec-isakmp
ipsec-isakmp
Objectives
Part 1: Enable Security Features
Part 2: Configure IPsec Parameters on R1
Part 3: Configure IPsec Parameters on R3
Part 4: Verify the IPsec VPN
Scenario
In this activity, you will configure two routers to support a site-to-site IPsec VPN for traffic flowing from their
respective LANs. The IPsec VPN traffic will pass through another router that has no knowledge of the VPN.
IPsec provides secure transmission of sensitive information over unprotected networks such as the Internet.
IPsec acts at the network layer, protecting and authenticating IP packets between participating IPsec devices
(peers), such as Cisco routers.
Part 1: Enable Security Features
Step 1: Activate securityk9 module.
The Security Technology Package license must be enabled to complete this activity.
2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public.
Page 2 of 6
Packet Tracer Configuring VPNs (Optional)
Note: Both the user EXEC and privileged EXEX pass word is cisco.
a. Issue the show version command in the user EXEC or privileged EXEC mode to verify that the Security
Technology Package license is activated.
---------------------------------------------------------------Technology
Technology-package
Technology-package
Current
Type
Next reboot
----------------------------------------------------------------ipbase
ipbasek9
Permanent
ipbasek9
security
None
None
None
uc
None
None
None
data
None
None
None
Configuration register is 0x2102
b. If not, activate the securityk9 module for the next boot of the router, accept the license, save the
configuration, and reboot.
R1(config)# license boot module c2900 technology-package securityk9
R1(config)# end
R1# copy running-config startup-config
R1# reload
c.
After the reloading is completed, issue the show version again to verify the Security Technology
Package license activation.
Technology Package License Information for Module:'c2900'
---------------------------------------------------------------Technology
Technology-package
Technology-package
Current
Type
Next reboot
----------------------------------------------------------------ipbase
ipbasek9
Permanent
ipbasek9
security
securityk9
Evaluation
securityk9
uc
None
None
None
data
None
None
None
d. Repeat Steps 1a to 1c with R3.
Part 2: Configure IPsec Parameters on R1
Step 1: Test connectivity.
Ping from PC-A to PC-C.
Step 2: Identify interesting traffic on R1.
Configure ACL 110 to identify the traffic from the LAN on R1 to the LAN on R3 as interesting. This interesting
traffic will trigger the IPsec VPN to be implemented whenever there is traffic between R1 to R3 LANs. All
other traffic sourced from the LANs will not be encrypted. Remember that due to the implicit deny any, there is
no need to add the statement to the list.
R1(config)# access-list 110 permit ip 192.168.1.0 0.0.0.255 192.168.3.0
0.0.0.255
2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public.
Page 3 of 6
Packet Tracer Configuring VPNs (Optional)
Step 3: Configure the ISAKMP Phase 1 properties on R1.
Configure the crypto ISAKMP policy 10 properties on R1 along with the shared crypto key cisco. Refer to the
ISAKMP Phase 1 table for the specific parameters to configure. Default values do not have to be configured
therefore only the encryption, key exchange method, and DH method must be configured.
R1(config)# crypto
R1(config-isakmp)#
R1(config-isakmp)#
R1(config-isakmp)#
R1(config-isakmp)#
R1(config)# crypto
isakmp policy 10
encryption aes
authentication pre-share
group 2
exit
isakmp key cisco address 10.2.2.2
Step 4: Configure the ISAKMP Phase 2 properties on R1.
Create the transform-set VPN-SET to use esp-3des and esp-sha-hmac. Then create the crypto map VPNMAP that binds all of the Phase 2 parameters together. Use sequence number 10 and identify it as an ipsecisakmp map.
R1(config)# crypto ipsec transform-set VPN-SET esp-3des esp-sha-hmac
R1(config)# crypto map VPN-MAP 10 ipsec-isakmp
R1(config-crypto-map)# description VPN connection to R3
R1(config-crypto-map)# set peer 10.2.2.2
R1(config-crypto-map)# set transform-set VPN-SET
R1(config-crypto-map)# match address 110
R1(config-crypto-map)# exit
Step 5: Configure the crypto map on the outgoing interface.
Finally, bind the VPN-MAP crypto map to the outgoing Serial 0/0/0 interface. Note: This is not graded.
R1(config)# interface S0/0/0
R1(config-if)# crypto map VPN-MAP
Part 3: Configure IPsec Parameters on R3
Step 1: Configure router R3 to support a site-to-site VPN with R1.
Now configure reciprocating parameters on R3. Configure ACL 110 identifying the traffic from the LAN on R3
to the LAN on R1 as interesting.
R3(config)# access-list 110 permit ip 192.168.3.0 0.0.0.255 192.168.1.0
0.0.0.255
Step 2: Configure the ISAKMP Phase 1 properties on R3.
Configure the crypto ISAKMP policy 10 properties on R3 along with the shared crypto key cisco.
R3(config)# crypto
R3(config-isakmp)#
R3(config-isakmp)#
R3(config-isakmp)#
R3(config-isakmp)#
R3(config)# crypto
isakmp policy 10
encryption aes
authentication pre-share
group 2
exit
isakmp key cisco address 10.1.1.2
2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public.
Page 4 of 6
Packet Tracer Configuring VPNs (Optional)
Step 3: Configure the ISAKMP Phase 2 properties on R1.
Like you did on R1, create the transform-set VPN-SET to use esp-3des and esp-sha-hmac. Then create the
crypto map VPN-MAP that binds all of the Phase 2 parameters together. Use sequence number 10 and
identify it as an ipsec-isakmp map.
R3(config)# crypto ipsec transform-set VPN-SET esp-3des esp-sha-hmac
R3(config)# crypto map VPN-MAP 10 ipsec-isakmp
R3(config-crypto-map)# description VPN connection to R1
R3(config-crypto-map)# set peer 10.1.1.2
R3(config-crypto-map)# set transform-set VPN-SET
R3(config-crypto-map)# match address 110
R3(config-crypto-map)# exit
Step 4: Configure the crypto map on the outgoing interface.
Finally, bind the VPN-MAP crypto map to the outgoing Serial 0/0/1 interface. Note: This is not graded.
R3(config)# interface S0/0/1
R3(config-if)# crypto map VPN-MAP
Part 4: Verify the IPsec VPN
Step 1: Verify the tunnel prior to interesting traffic.
Issue the show crypto ipsec sa command on R1. Notice that the number of packets encapsulated,
encrypted, decapsulated and decrypted are all set to 0.
R1# show crypto ipsec sa
interface: Serial0/0/0
Crypto map tag: VPN-MAP, local addr 10.1.1.2
protected vrf: (none)
local ident (addr/mask/prot/port): (192.168.1.0/255.255.255.0/0/0)
remote ident (addr/mask/prot/port): (192.168.3.0/255.255.255.0/0/0)
current_peer 10.2.2.2 port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 0, #pkts encrypt: 0, #pkts digest: 0
#pkts decaps: 0, #pkts decrypt: 0, #pkts verify: 0
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 0, #recv errors 0
local crypto endpt.: 10.1.1.2, remote crypto endpt.:10.2.2.2
path mtu 1500, ip mtu 1500, ip mtu idb Serial0/0/0
current outbound spi: 0x0(0)
<output omitted>
Step 2: Create interesting traffic.
Ping PC-C from PC-A.
2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public.
Page 5 of 6
Packet Tracer Configuring VPNs (Optional)
Step 3: Verify the tunnel after interesting traffic.
On R1, re-issue the show crypto ipsec sa command. Now notice that the number of packets is more than 0
indicating that the IPsec VPN tunnel is working.
R1# show crypto ipsec sa
interface: Serial0/0/0
Crypto map tag: VPN-MAP, local addr 10.1.1.2
protected vrf: (none)
local ident (addr/mask/prot/port): (192.168.1.0/255.255.255.0/0/0)
remote ident (addr/mask/prot/port): (192.168.3.0/255.255.255.0/0/0)
current_peer 10.2.2.2 port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 3, #pkts encrypt: 3, #pkts digest: 0
#pkts decaps: 3, #pkts decrypt: 3, #pkts verify: 0
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 1, #recv errors 0
local crypto endpt.: 10.1.1.2, remote crypto endpt.:10.2.2.2
path mtu 1500, ip mtu 1500, ip mtu idb Serial0/0/0
current outbound spi: 0x0A496941(172583233)
<output omitted>
Step 4: Create uninteresting traffic.
Ping PC-B from PC-A.
Step 5: Verify the tunnel.
On R1, re-issue the show crypto ipsec sa command. Finally, notice that the number of packets has not
changed verifying that uninteresting traffic is not encrypted.
2013 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public.
Page 6 of 6
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Cryptographic Hash FunctionsDokument6 SeitenCryptographic Hash Functionsgraduation projectNoch keine Bewertungen
- An Analysis On Encryption - IB Maths Internal AssesmentDokument15 SeitenAn Analysis On Encryption - IB Maths Internal AssesmentAntonio JardimNoch keine Bewertungen
- C&NS Unit-4 R16Dokument31 SeitenC&NS Unit-4 R16Geethanjali KotaruNoch keine Bewertungen
- Practical State Recovery Attacks Against Legacy RNG ImplementationsDokument16 SeitenPractical State Recovery Attacks Against Legacy RNG ImplementationsandyNoch keine Bewertungen
- Passwordless Microsoft Account LoginDokument4 SeitenPasswordless Microsoft Account LoginDilshan ChristopherNoch keine Bewertungen
- 2 Ethereum TKDokument35 Seiten2 Ethereum TKDorianna EuspositouNoch keine Bewertungen
- Describe Oakley Key Determination Protocol. Explain SSL Handshake Protocol With ExampleDokument1 SeiteDescribe Oakley Key Determination Protocol. Explain SSL Handshake Protocol With ExamplepramelaNoch keine Bewertungen
- Cryptography Prateek SharmaDokument27 SeitenCryptography Prateek Sharmaapi-3811430Noch keine Bewertungen
- Survey Paper On CP-ABE Cloud Computing-51129037 PDFDokument3 SeitenSurvey Paper On CP-ABE Cloud Computing-51129037 PDFFisehaNoch keine Bewertungen
- Type of Attack Description Methods and Tools: War DrivingDokument5 SeitenType of Attack Description Methods and Tools: War DrivingjldrezNoch keine Bewertungen
- 3DES Encryption - Easily Encrypt or Decrypt Strings or FilesDokument4 Seiten3DES Encryption - Easily Encrypt or Decrypt Strings or FilesPedro MorrisNoch keine Bewertungen
- IJARCCE Paper FormatDokument4 SeitenIJARCCE Paper FormatBhaktiNoch keine Bewertungen
- How To - Sign XML Documents With Digital Signatures - Microsoft DocsDokument6 SeitenHow To - Sign XML Documents With Digital Signatures - Microsoft DocsJolumacaNoch keine Bewertungen
- The Enigma MachineDokument12 SeitenThe Enigma Machineapi-615372446Noch keine Bewertungen
- Advance Encryption StandardDokument41 SeitenAdvance Encryption Standardashodhiya14Noch keine Bewertungen
- DCSPDokument116 SeitenDCSPCompaniaDekartSRLNoch keine Bewertungen
- VLSI Implementation of Advanced Encryption Standard Using Rijndael AlgorithmDokument6 SeitenVLSI Implementation of Advanced Encryption Standard Using Rijndael AlgorithmInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- CRYPTOGRAPHY Student Notes PDFDokument65 SeitenCRYPTOGRAPHY Student Notes PDFSimone DurantiNoch keine Bewertungen
- CRYPTOGRAPHYDokument2 SeitenCRYPTOGRAPHYJessica Cabanting OngNoch keine Bewertungen
- Key Distribution ProblemDokument1 SeiteKey Distribution ProblemDeepa SainiNoch keine Bewertungen
- Crypto Products Backgrounder R0Dokument138 SeitenCrypto Products Backgrounder R0wsboldtNoch keine Bewertungen
- Confidentiality and Privacy ControlsDokument19 SeitenConfidentiality and Privacy Controlsmuhammad f laitupaNoch keine Bewertungen
- Tutorial 5-7Dokument19 SeitenTutorial 5-7lucyNoch keine Bewertungen
- RSA Hybrid Encryption Schemes: 1 MotivationsDokument14 SeitenRSA Hybrid Encryption Schemes: 1 MotivationsKiều Minh ĐứcNoch keine Bewertungen
- 7 EpassportDokument40 Seiten7 EpassportzennroNoch keine Bewertungen
- Larrabees Cipher 1884Dokument36 SeitenLarrabees Cipher 1884Max PowerNoch keine Bewertungen
- Mod 2 Notes CryptoDokument66 SeitenMod 2 Notes CryptoMahalaxmi GinnamNoch keine Bewertungen
- Reviewer Kay Sir JedDokument12 SeitenReviewer Kay Sir JedRic EstanislaoNoch keine Bewertungen
- Cryptography and Network SecurityDokument2 SeitenCryptography and Network SecurityVishwa Pratap SinghNoch keine Bewertungen
- Social 6th ClassDokument184 SeitenSocial 6th ClassShaik HussainNoch keine Bewertungen