Beruflich Dokumente
Kultur Dokumente
Digital Image Processing by Using The Theory Ofbiometrics
Hochgeladen von
vasuvlsiOriginalbeschreibung:
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Digital Image Processing by Using The Theory Ofbiometrics
Hochgeladen von
vasuvlsiCopyright:
Verfügbare Formate
Digital image processing using theory of biometrics
CIHAN09
A TECHNICAL PAPER PRESENTATION
ON
DIGITAL IMAGE PROCESSING
USING
THEORY OF BIO-METRICS
PRESENTED BY:
MOHD AMEENUDDIN
E.C.E III YEAR II SEM
06801A0423
E-mail: ameen0723@gmail.com
Ph:09966589254
b. ashok Kumar
E.C.E III YEAR II SEM
06801A0404
E-mail: akumar063@gmail.com
Ph:09014119932
ARKAY COLLEGE
OF
ENGINEERING AND
TECHNOLOGY
ACHANPALLY, BODHAN
DIST: NIZAMABAD
Page 1 of 8
Digital image processing using theory of biometrics
IMAGE PROCESSING USING
THEORYOF
BIO-METRICS
Introduction
Abstract
What is a Biometrics system?
While humans have had the
innate ability to recognize and distinguish
different
faces
for
millions
of
years,
computers are just now catching up. In this
paper, we'll learn how computers are turning
your face into computer code so it can be
compared to thousands, if not millions, of
other faces. We'll also look at how facial
recognition
software
is
being
used
in
elections, criminal investigations and to
secure your personal computer.
Facial recognition methods
may vary, but they generally involve a series
of steps that serve to capture, analyze and
compare your face to a database of stored
images. A Software company called Visionics
developed Facial Recognition software called
Faceit. Potential applications even include
ATM and check-cashing security, Security
Law Enforcement & Security Surveillance
and voter database for duplicates. This
biometrics technology could also be used to
secure your computer files. By mounting a
Webcam to your computer and installing the
facial recognition software, your face can
become the password you use to get into your
computer. By implementing this technology
and the normal password security you are
getting double security to your valuable data.
Biometrics is a form of bioinformatics
that uses biological properties to identify
individuals.There are two main modules in a
biometrics system. "storing" and "comparing".
The systems must first store your information
before it can use this stored information to
compare and verify. The storing process however
differs
between
different
systems.
For instance, if the biometrics system
uses
thumb impression as
the
mode
of
verification, then your thumb impression will be
first captured in film and stored in the biometrics
database system. Instead of storing as it is, the
system
will
compress
and
store
it.
If for instance your face is used as the
mode of verification, then your face will be
photographed in different angles and stored in
the biometrics database systems. The same goes
for
voice
recording
and
eyes
mode
of
verification.
Once this storing process is done, the
'comparing' process is done daily or as and when
required. For example let us assume that your
company uses finger print biometrics systems.
When you come to office daily, there will be a
finger print reader at the entrance. You will have
to put your finger on this finger print reader
which will capture your finger print and send to
the biometrics system. The biometrics system
will then 'compare' this finger print to the finger
print that was previously stored in the database.
Page 2 of 8
Digital image processing using theory of biometrics
If
both
of
them
match
then
you
are
'employees pass are allowed access to
authenticated.
the company premises.
In all these above scenarios, signature
What is Face Recognition?
and photographs are used to verify a person's
Face recognition technology is the least
intrusive and fastest biometric technology. It
works with the most obvious individual
identifier the human face. Instead of requiring
people to place their hand on a reader or
precisely position their eye in front of a scanner,
identity. In reality any person can learn to use
another person's signature. Worse still are they
can replace your photograph with their own
photograph on these cards. Therefore, these
existing authentication methods are not secure
enough.
Biometrics solves these above issues.
face recognition systems unobtrusively take
pictures of people's faces as they enter a defined
area. There is no intrusion or delay, and in most
cases the subjects are entirely unaware of the
process. They do not feel "under surveillance"
Every person's face is unique. Each person's
thumb impression is also unique. Everyone's
voice is different from others. The eyes are also
unique for every person. Therefore it makes
sense to use these unique features of each person
or that their privacy has been invaded.
as
that doors can be opened by giving voice
commands. In some Hollywood movies, you
would have seen thumb impressions are used to
these
are
nothing
of
authentication.
passwords are no longer required. To enter one's
We have seen in James Bond movies
doors. All
means
Therefore for using computers,
What is Biometrics Security?
open
but
company, employee passes are no longer
required. Your body is sufficient. Using any parts
of your body the biometrics system can identify
you. America, Canada and some European
nations already use these security systems.
Biometrics.
The Face:
Think of these scenarios.
1.
2.
3.
You go to a bank to withdraw money.
Your face is an important part of who
You fill up the withdrawal form, sign it
you are and how people identify you. Imagine
and give it to the bank clerk. Your
how hard it would be to recognize an individual
signature is used to verify your identity
if all faces looked the same. Except in the case of
You are shopping using your credit
identical twins, the face is arguably a person's
cards. While paying the photograph on
most unique physical characteristic. While
the credit cards and the signature on
humans have had the innate ability to recognize
the credit cards are used to verify your
and distinguish different faces for millions of
identity.
years, computers are just now catching up.
In big companies, all employees are
Visionics, a company based in New
issued an 'employee pass' with their
Jersey, is one of many developers of facial
photograph.
recognition technology. The twist to its particular
People
with
these
Page 3 of 8
Digital image processing using theory of biometrics
software, FaceIt, is that it can pick someone's
face out of a crowd, extract that face from the
rest of the scene and compare it to a database
full of stored images. In order for this software
to work, it has to know what a basic face looks
like.
These nodal points are measured to
create a numerical code, a string of numbers that
represents the face in a database. This code is
called a face print. Only 14 to 22 nodal points
are needed for the FaceIt software to complete
the recognition process.
In the next section, we'll look at how
Facial recognition software can be
used to find criminals in a crowd, turning a
the system goes about detecting, capturing and
storing faces.
mass of people into a big line up.
The Software:
Facial recognition software is based on
Facial recognition software falls into a
the ability to first recognize a face, which is a
technological feat in itself, and then measure
the various features of each face. If you look in
the mirror, you can see that your face has
certain distinguishable landmarks. These are the
peaks and valleys that make up the different
facial
features.
Visionics
defines
these
landmarks as nodal points. There are about 80
nodal points on a human face. Here are a few of
the nodal points that are measured by the
software:
Distance between eyes
Width of nose
Depth of eye sockets
Cheekbones
Jaw line
Chin
larger
group
biometrics.
of
technologies
Biometrics
uses
known
as
biological
information to verify identity. The basic idea
behind biometrics is that our bodies contain
unique properties that can be used to distinguish
us from others. Besides facial recognition,
biometric authentication methods also include
:
Fingerprint scan
Retina scan
Voice identification
Facial recognition methods may vary,
but they generally involve a series of steps that
serve to capture, analyze and compare your face
to a database of stored images. Here is the basic
process that is used by the FaceIt system to
capture and compare images:
Page 4 of 8
Digital image processing using theory of biometrics
Normalization is performed regardless of the
head's location and distance from the camera.
Light does not impact the normalization process.
Representation:
The system translates the facial data
into a unique code. This coding process allows
for easier comparison of the newly acquired
To identify someone, facial
recognition software compares newly
captured images to databases of stored
images.
facial data to stored facial data.
Matching:
The newly acquired facial data is
compared to the stored data and (ideally) linked
to at least one stored facial representation.
Detection:
The heart of the FaceIt
When the system is attached to a
facial
recognition system is the Local Feature
video surveillance system, the recognition
Analysis
software searches the field of view of a video
mathematical technique the system uses to
camera for faces. If there is a face in the view, it
encode faces. The system maps the face and
is detected within a fraction of a second. A
creates a face print, a unique numerical code for
multi-scale algorithm is used to search for
that face. Once the system has stored a face
faces in low resolution. (An algorithm is a
print, it can compare it to the thousands or
program that provides a set of instructions to
millions of face prints stored in a database. Each
accomplish a specific task). The system
face print is stored as an 84-byte file.
switches to a high-resolution search only after a
(LFA)
algorithm.
This
is
the
The system can match multiple face
head-like shape is detected.
prints at a rate of 60 million per minute from
memory or 15 million per minute from hard disk.
Alignment :
As comparisons are made, the system assigns a
Once a face is detected, the system
value to the comparison using a scale of one to
determines the head's position, size and pose. A
10. If a score is above a predetermined threshold,
face needs to be turned at least 35 degrees
a match is declared. The operator then views the
toward the camera for the system to register it.
two photos that have been declared a match to be
certain that the computer is accurate.
Facial recognition, like other forms of
Normalization :
biometrics, is considered a technology that will
The image of the head is scaled and
have many uses in the near future. In the next
rotated so that it can be registered and mapped
section, we will look how it is being used right
into
now.
an
appropriate
size
and
pose.
Page 5 of 8
Digital image processing using theory of biometrics
recognition
APPLICATIONS
OF
FACIAL
could eliminate possible criminal
activity.
RECOGNITION:
Potential
In addition to law enforcement and
security
surveillance,
facial
recognition
applications
even
include ATM and check-cashing security. The
software has several other uses, including:
software is able to quickly verify a customer's
face. After the user consents, the ATM or check-
Eliminating voter fraud
ATM and Check-cashing identity
verification
Computer security
Eliminating voter fraud:
One of the most innovative uses of
cashing kiosk captures a digital photo of the
customer. The facial recognition software then
generates a face print of the photograph to
protect customers against identity theft and
fraudulent
transactions.
By
using
facial
recognition software, there's no need for a
picture ID, bank card or personal identification
facial recognition is being employed by the
number (PIN) to verify a customer's identity.
Mexican government, which is using the
Computer security:
technology to weed out duplicate voter
registrations. To sway an election, people
will register several times under different
names so they can vote more than once.
Conventional methods have not been very
successful at catching these people. Using
the facial recognition technology, officials
can search through facial images in the
voter database for duplicates at the time of
This
biometric
technology
could also be used to secure your computer files.
By mounting a Webcam to your computer and
installing the facial recognition software, your
face can become the password you use to get
into your computer. IBM has incorporated the
technology into a screensaver for its A, T and X
series ThinkPad laptops.
registration. New images are compared to
the records already on file to catch those
who attempt to register under aliases.
ATM and Check-cashing
identity verification:
The major Advantage of a facial
recognition system over other
verification methods:
use
Many people who don't use banks
check-cashing
machines.
Facial
Page 6 of 8
Digital image processing using theory of biometrics
There are several practical reasons for
favoring
facial
recognition
over
other
biometrics for the purposes of identification.
recognition using Biometrics gives a new scope
to the modern era.
The finger print of those people
working in Chemical industries is
often
technologies, the incredible potential of facial
affected.
Therefore
Further, if we add both the facial
these
recognition and the normal password security we
companies should not use the finger
can have an added Double Security which is
print mode of authentication.
more reliable than one shield security, Just same
It is found that with age, the voice of a
as the quote Two heads are better than one.
person differs. Also when the person
has flu or throat infection the voice
changes or if there are too much noise
in the environment this method may
not authenticate correctly. Therefore
this method of verification is not
workable all the time
For people affected with diabetes, the
eyes
get
affected
resulting
in
differences.
Biometrics is an expensive security
solution.
Swiss European surveillance: facial
recognition and vehicle make,
model, color and license plate reader.
Conclusion
We conclude our paper on Facial
Recognition using Biometrics.
Potential applications are as follows:
Eliminating voter fraud
ATM and Check-cashing identity
verification
Computer security
Security law enforcement
Security surveillance
and
Side View.
While facial recognition can be used to
protect your private information, it can just as
easily be used to invade your privacy by taking
you picture when you are entirely unaware of
the
camera.
As
with
many
developing
Page 7 of 8
Digital image processing using theory of biometrics
Close-up of the Infrared Illuminator. This
light is invisible to the human eye but it
creates a day like environment for the
surveillance cameras.
Page 8 of 8
Das könnte Ihnen auch gefallen
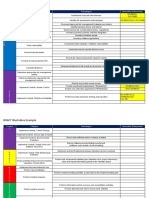
- DRAFT Illustrative Example: Function Category Subcategory Informative Reference(s)Dokument13 SeitenDRAFT Illustrative Example: Function Category Subcategory Informative Reference(s)holamundo123Noch keine Bewertungen
- Face Recognition Using PythonDokument9 SeitenFace Recognition Using PythonHarshit yadavNoch keine Bewertungen
- Otis Engineering Center Gien Field Component ManualDokument13 SeitenOtis Engineering Center Gien Field Component Manualnr1wolf_co_69529906100% (5)
- Lora Tech Intro PDFDokument39 SeitenLora Tech Intro PDFRoberto AmbrozioNoch keine Bewertungen
- Project Report Face Recognition PCADokument21 SeitenProject Report Face Recognition PCAGURTEJ SINGHNoch keine Bewertungen
- Service VAPT PresentationDokument14 SeitenService VAPT PresentationVinay wrksNoch keine Bewertungen
- Deloitte Cyber Threat Intelligence Cybersecurity 14Dokument6 SeitenDeloitte Cyber Threat Intelligence Cybersecurity 14jotaNoch keine Bewertungen
- MobileApp Checklist 2017Dokument21 SeitenMobileApp Checklist 2017Trico AndreasNoch keine Bewertungen
- Securing Atm by Image Processing - Facial Recognition AuthenticationDokument4 SeitenSecuring Atm by Image Processing - Facial Recognition AuthenticationijsretNoch keine Bewertungen
- LAN Architecture Diagram and ComponentsDokument6 SeitenLAN Architecture Diagram and ComponentsCik Ieda SuhaimiNoch keine Bewertungen
- Facial Recognition Using The Theory of Biometrics1Dokument9 SeitenFacial Recognition Using The Theory of Biometrics1Sudheer KumarNoch keine Bewertungen
- Face Recognition TechnologyDokument2 SeitenFace Recognition TechnologyRashmi SureshNoch keine Bewertungen
- How Artificial Intelligence Helps in Face Recognition Login and RegistrationDokument3 SeitenHow Artificial Intelligence Helps in Face Recognition Login and Registrationilyes bouallaguiNoch keine Bewertungen
- Face RecDokument6 SeitenFace Recsaravvanon_murthyNoch keine Bewertungen
- Gitam University (College of Engineering) Paper PresentationDokument8 SeitenGitam University (College of Engineering) Paper PresentationShaik FirozNoch keine Bewertungen
- Reconhecimento FacialDokument9 SeitenReconhecimento FacialJesuel Brito MundeiaNoch keine Bewertungen
- Facial Recognition Project FileDokument6 SeitenFacial Recognition Project FileabcNoch keine Bewertungen
- Facial RecognitionDokument23 SeitenFacial RecognitionChaithanya MannepalliNoch keine Bewertungen
- FACIAL RECOGNITION SYSTEM PRIf, ITf, ISf 2023 02 14Dokument9 SeitenFACIAL RECOGNITION SYSTEM PRIf, ITf, ISf 2023 02 14Kamilija VoitechovičNoch keine Bewertungen
- Foundation of Iot Lab: Project: Face Recognition System Using Python and Iot Guided By: Anuj Kumar GoelDokument9 SeitenFoundation of Iot Lab: Project: Face Recognition System Using Python and Iot Guided By: Anuj Kumar GoelSahul Kumar ParidaNoch keine Bewertungen
- Face Recognition Technology: What Are Biometrics?Dokument5 SeitenFace Recognition Technology: What Are Biometrics?pramodNoch keine Bewertungen
- Introduction: Face Recognition Using EigenfacesDokument3 SeitenIntroduction: Face Recognition Using EigenfacesRahul KaulNoch keine Bewertungen
- About Face Detection and RecognitionDokument4 SeitenAbout Face Detection and Recognitionsmaheshwari06Noch keine Bewertungen
- Face Recognigion-SystemDokument30 SeitenFace Recognigion-SystemOliifan BaayyooNoch keine Bewertungen
- Electronics and Communication EngineeringDokument14 SeitenElectronics and Communication EngineeringrajiNoch keine Bewertungen
- Online Transaction Security Using Face Recognition A ReviewDokument11 SeitenOnline Transaction Security Using Face Recognition A ReviewIJRASETPublicationsNoch keine Bewertungen
- 3D Face RecognitionDokument8 Seiten3D Face RecognitionSai Kiran Reddy MNoch keine Bewertungen
- AF and Face RecogDokument9 SeitenAF and Face RecogKALAI SELVAM .MNoch keine Bewertungen
- 1.1. Preamble: Fingerprint Identification Application 1Dokument22 Seiten1.1. Preamble: Fingerprint Identification Application 1Kanaka Lakshmi SNoch keine Bewertungen
- Face Recognigion-SystemDokument30 SeitenFace Recognigion-SystemNikhil VarmaNoch keine Bewertungen
- Face Recognition TechnologyDokument15 SeitenFace Recognition Technologycharysahith528Noch keine Bewertungen
- Face Recognition Research Papers 2015Dokument5 SeitenFace Recognition Research Papers 2015fzk3bszq100% (1)
- Face Recognition TechnologyDokument3 SeitenFace Recognition TechnologyijsretNoch keine Bewertungen
- Face Recognition Using Extended Local Binary Pattern: 1. AbstractDokument11 SeitenFace Recognition Using Extended Local Binary Pattern: 1. AbstractkumukumuNoch keine Bewertungen
- VIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIDokument17 SeitenVIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIapi-291159108Noch keine Bewertungen
- Share Face Recognition TechnologyDokument15 SeitenShare Face Recognition TechnologyBikram RockNoch keine Bewertungen
- Crime Detection Through Facial Features 1.1. AbstractDokument10 SeitenCrime Detection Through Facial Features 1.1. AbstractPH VickyNoch keine Bewertungen
- Face RecognitionDokument42 SeitenFace RecognitionG.J. ShivRajNoch keine Bewertungen
- Bi Sy PRDokument23 SeitenBi Sy PRGovind KumarNoch keine Bewertungen
- Seminar Presentation ON: "Face Recognition Technology"Dokument14 SeitenSeminar Presentation ON: "Face Recognition Technology"SasidharKalidindiNoch keine Bewertungen
- Review Related Literature Foreign LiteratureDokument13 SeitenReview Related Literature Foreign LiteratureJane RobNoch keine Bewertungen
- Face Recognition TechnologyDokument30 SeitenFace Recognition TechnologyRsyedNoch keine Bewertungen
- Apps PDFDokument6 SeitenApps PDFOliifan BaayyooNoch keine Bewertungen
- Review of Related Literature For Face RecognitionDokument8 SeitenReview of Related Literature For Face Recognitionafmabzmoniomdc100% (1)
- How To Write Thesis Proposal On Face RecognitionDokument5 SeitenHow To Write Thesis Proposal On Face RecognitionRahajul Amin RajuNoch keine Bewertungen
- Kamenská - Facial RecognitionDokument9 SeitenKamenská - Facial RecognitionDominika KamenskáNoch keine Bewertungen
- Lecture Attendance Using Face RecognitionDokument14 SeitenLecture Attendance Using Face Recognitionthoshif khanNoch keine Bewertungen
- Atm With An EyeDokument25 SeitenAtm With An EyeKiran StridesNoch keine Bewertungen
- Face Detection and RecognitionDokument17 SeitenFace Detection and RecognitionAbhishek GargNoch keine Bewertungen
- Last AssignmentDokument2 SeitenLast AssignmentSapphire ChupeloNoch keine Bewertungen
- System AnalysisDokument7 SeitenSystem Analysisroshini roseNoch keine Bewertungen
- Facial RecognitionDokument2 SeitenFacial RecognitionkellyNoch keine Bewertungen
- Face Recognition Technology: Seminar ReportDokument35 SeitenFace Recognition Technology: Seminar ReportAekansh JainNoch keine Bewertungen
- CGV2255 PDFDokument8 SeitenCGV2255 PDFCeesay ModouNoch keine Bewertungen
- Facial Recognition System: Fundamentals and ApplicationsVon EverandFacial Recognition System: Fundamentals and ApplicationsNoch keine Bewertungen
- Welcome: Project TitleDokument27 SeitenWelcome: Project Title29 - 023 - Abid HasanNoch keine Bewertungen
- Face Recognition HomeworkDokument6 SeitenFace Recognition Homeworkafefkziai100% (1)
- Research Paper On Face RecognitionDokument6 SeitenResearch Paper On Face Recognitionfjluthulg100% (1)
- Face Reco 2Dokument3 SeitenFace Reco 2Sherry SherNoch keine Bewertungen
- Face RecognitionDokument17 SeitenFace Recognitionምንሼ ነው ዘመኑNoch keine Bewertungen
- Research Paper IeeeDokument5 SeitenResearch Paper Ieeemanish kumarNoch keine Bewertungen
- Face Recognition Systems A SurveyDokument34 SeitenFace Recognition Systems A SurveysNoch keine Bewertungen
- DIP FACE DetectionDokument16 SeitenDIP FACE DetectionRebenGaNoch keine Bewertungen
- AIE 62 V1i2 p102 107Dokument6 SeitenAIE 62 V1i2 p102 107BHUPANI SREE MADHUKIRAN ECEUG-2020 BATCHNoch keine Bewertungen
- ANN Azri LatestDokument20 SeitenANN Azri LatestAzri Mohd KhanilNoch keine Bewertungen
- Face Detection AppDokument15 SeitenFace Detection Apprithikashivani06Noch keine Bewertungen
- Facial Recognition System: Unlocking the Power of Visual IntelligenceVon EverandFacial Recognition System: Unlocking the Power of Visual IntelligenceNoch keine Bewertungen
- Digital Image Processing Question PapersDokument9 SeitenDigital Image Processing Question PapersvasuvlsiNoch keine Bewertungen
- Rr410507 Digital Speech and Image ProcessingDokument6 SeitenRr410507 Digital Speech and Image ProcessingvasuvlsiNoch keine Bewertungen
- R09-1!2!25-Image Processing and Pattern Recognition-Dform31.10.12Dokument1 SeiteR09-1!2!25-Image Processing and Pattern Recognition-Dform31.10.12vasuvlsiNoch keine Bewertungen
- R09-1!2!25-Image Processing and Pattern Recognition Barcoded-Dform31.10.12Dokument1 SeiteR09-1!2!25-Image Processing and Pattern Recognition Barcoded-Dform31.10.12vasuvlsiNoch keine Bewertungen
- Or321151 Image ProcessingDokument2 SeitenOr321151 Image ProcessingvasuvlsiNoch keine Bewertungen
- Nr-410507-Digital Speech and Image ProcessingDokument4 SeitenNr-410507-Digital Speech and Image ProcessingvasuvlsiNoch keine Bewertungen
- Windows Services Audio RecordingDokument2 SeitenWindows Services Audio RecordingArindam GhoshalNoch keine Bewertungen
- iVMS-4200 Client Software: User ManualDokument86 SeiteniVMS-4200 Client Software: User Manualflorin400Noch keine Bewertungen
- GoNet MBW NMS 1.1 Operational GuideDokument116 SeitenGoNet MBW NMS 1.1 Operational Guidehelberth73Noch keine Bewertungen
- Iec 60617 SymbolsDokument81 SeitenIec 60617 SymbolsRiad Saad RiadNoch keine Bewertungen
- Griaule Manual For Basic Knowledge in Technical and Licensing QuestionsDokument20 SeitenGriaule Manual For Basic Knowledge in Technical and Licensing QuestionsseduchNoch keine Bewertungen
- IMPACT ACTechnologiesv3LIS PDFDokument0 SeitenIMPACT ACTechnologiesv3LIS PDFsurya277Noch keine Bewertungen
- General Regression Neural Network Approach For Image Transformation Based Hybrid Graphical Password Authentication SystemDokument7 SeitenGeneral Regression Neural Network Approach For Image Transformation Based Hybrid Graphical Password Authentication SystemvamsiNoch keine Bewertungen
- Analysis & Dashboard - SG2Dokument370 SeitenAnalysis & Dashboard - SG2rajagopalan900% (1)
- Quiz Bit004 AiswfafinalsDokument4 SeitenQuiz Bit004 AiswfafinalsGabriel Patron100% (1)
- A Basic Windows Service in C#Dokument7 SeitenA Basic Windows Service in C#Породица СтолићNoch keine Bewertungen
- Guía de Firewall FortinetDokument102 SeitenGuía de Firewall FortinetFederico ParalachiNoch keine Bewertungen
- Ee793 Assignment 1Dokument5 SeitenEe793 Assignment 1Jayesh SongaraNoch keine Bewertungen
- CP R77 Gaia AdminGuideDokument234 SeitenCP R77 Gaia AdminGuideAgnelo RodriguesNoch keine Bewertungen
- Webex WeDokument788 SeitenWebex WeOsmar Perez LopezNoch keine Bewertungen
- Abb ConnectorsDokument116 SeitenAbb ConnectorsAlby JoyNoch keine Bewertungen
- Challan PDFDokument1 SeiteChallan PDFPINAKI BISWASNoch keine Bewertungen
- Streamvault SV 2000eDokument2 SeitenStreamvault SV 2000eJose Martin MotaNoch keine Bewertungen
- RKM Library Rules-27june2010Dokument9 SeitenRKM Library Rules-27june2010vedvivekaNoch keine Bewertungen
- Vicon Vero Quick StartDokument6 SeitenVicon Vero Quick StartJason WongNoch keine Bewertungen
- Cisco SPA Configuration: RouterDokument3 SeitenCisco SPA Configuration: RouterJuliano OlenickNoch keine Bewertungen
- Pfsense VPN PPTPDokument5 SeitenPfsense VPN PPTPandreaorlandiNoch keine Bewertungen
- Fresenius Kabi PDFDokument4 SeitenFresenius Kabi PDFgenaro aparicioNoch keine Bewertungen
- SAMBA Product PageDokument13 SeitenSAMBA Product PageHifive RaNoch keine Bewertungen