Beruflich Dokumente
Kultur Dokumente
TMP 960 Black Hat Hacker Survey Report 2015467808520
Hochgeladen von
dexterrootOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
TMP 960 Black Hat Hacker Survey Report 2015467808520
Hochgeladen von
dexterrootCopyright:
Verfügbare Formate
Hackers confirm an alarming lack of
protection for privileged accounts
According to Thycotics 2015 Hacker Survey conducted at the annual Black Hat conference, hackers
continue to easily compromise privileged accounts the keys to the kingdom that help
them unlock access to virtually any part of your network, including mission critical data.
The report highlights disturbing news for security professionals and IT administrators alike. Despite
multi-millions of dollars invested in cybersecurity this past year, hackers shared several startling findings:
9 in 10 Hackers
45% of Hackers
94% of Hackers
believe its as easy--or even
easierto steal privileged
account credentials today
compared to the past two years!
reported that privileged
account credentials are their
most coveted target, giving
them the most direct access to
sensitive data.
find privileged credentials
in unprotected files such as
spreadsheets.
The takeaway from this years Hacker Survey is clearly expressed by cybersecurity expert
Dave Shackleford of IANS:
IF YOU DONT HAVE GOOD PRIVILEGED ACCOUNT MANAGEMENT, ATTACKERS
CAN TAKE YOUR CREDENTIALS AND START ACTING LIKE A TRUSTED USER.
Its imperative that organizations start implementing best practices to protect privileged account access
around the sensitive credentials most sought after by attackers today. This report contains several best
practices organizations can use to protect their privileged accounts, enforce stronger security policies
and stop a breach in its tracks, including:
Discover rogue accounts and secure
them immediately.
Rotate passwords on privileged
endpoints constantly.
Actively audit and monitor privileged
user access.
Enforce strong password policies for
end-users
PRIVILEGED
ACCOUNT
MANAGEMENT
p: +1 202-802-9399
e: sales@thycotic.com
www.thycotic.com
Thycotic Black Hat 2015
Hacker Survey Executive Report
Introduction: A growing focus on Privileged Account security
Data breaches continue to plague business enterprises daily, and its nearly impossible to stop attackers
from advancing into the basic layers of a companys IT infrastructure.
Today, the perimeter is not the security force it once was. Attackers are bypassing perimeter security
constantly, taking advantage of porous flaws that allow them some kind of access within your network
regardless of whether the business is a small operation or global enterprise. The key to protecting your
network and critical data is to learn how attackers think so you can add the right layers of security
designed to stop attack efforts from becoming successful.
Despite increased, or at least commensurate, levels of IT security spending over the past two years,
hackers today continue to compromise corporate networks with ease. It seems that even as more
security solutions and tools are deployed, just as many vulnerabilities are introduced that can lead to
network penetration.
In todays cyber security arena, the notion of using a traditional perimeter firewall as your primary line
of defense is no longer the impenetrable wall it used to be, as hackers and malicious actors consistently
find ways to sneak past the first trusted layer of defense. The combination of BYOD, distributed
networks, mismanaged user access, and the sheer volume of external attacks have created a complex
series of threat vectors that require unique defense-in-depth strategies, starting with inside the
perimeter at the core of the infrastructure and working outward from there.
According to a 2014 report sanctioned by Thycotic and IANS Research, 62% of data breach success directly
resulted from the abuse of privileged account credentials, stolen by attackers from deep inside the
network. This proves that traditional perimeter defense isnt enough to stop attackers from achieving
their goals.
In an effort to learn more about the methods by which hackers are able to successfully break into and
compromise enterprise networks, Thycotic sponsored an official poll conducted live onsite at Black Hat
USA 2015. Thycotic secured 201 responses from both self-identified white hat and black hat hackers,
and the results documented herein reveal some of the methods they use to infiltrate networks, and
demonstrate the focus with which they target privileged account credentials.
Thycotic Black Hat 2015
Hacker Survey Executive Report
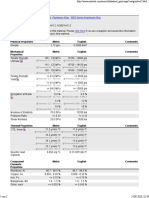
75% of hackers see no improvement in the protection of privileged account credentials.
When asked how the level of
difficulty has changed in terms
of the ability to compromise
privileged account credentials,
a vast majority (75%) of the
survey respondents indicated it
is just as easy today as it was
two years ago. Whats more,
an additional 12% said that it
is even easier today, despite
increased security spending.
When combining those two
respondent sets, a clear picture
emerges in which nearly 9 in 10
hackers believe it is as easy or
even easier to steal privileged
account credentials today.
Only 6% of hackers have NOT found privileged account credentials in unprotected files.
Thycotic Black Hat 2015
Hacker Survey Executive Report
One of the more foundational security practices in any organization is to protect credentials in encrypted
databases, or some kind of centrally managed solution, in order to limit exposure. Yet 94% of hackers
indicated they have found privileged account credentials arguably the most important source of access
to a network in unprotected files at least some of the time. In fact, 50% of hackers said this is the case
either all of the time (20%) or most of the time (30%) when they get their foot into the door of a
network and start looking around. The dangers here are immeasurable, as privileged account credentials
essentially serve as the keys to the kingdom and can unlock access to virtually any part of the network,
including mission critical data sources.
If you dont have good privileged account management,
attackers can take your credentials and start acting like a
trusted user. Dave Shackleford, Lead IANS Faculty
Hackers say sensitive credentials are the keys to large amounts of critical data.
Perhaps not surprising after the
previous finding, hackers covet
privileged
account
credentials
because of the access they provide to
critical data. In fact, when given the
choice between privileged account
credentials, end user credentials, user
documents and files, and network
configuration information, 45% of
hackers reported that privileged
account credentials are the targeted
asset that provides them the most
direct access to data. End user
credentials, which generally have
more limited access rights assigned to
them, were the second choice for hackers at 33%. Although limited, exposed end-user credentials still
pose a major risk because they are often the first target utilized in the attack chain to gain entry-level
access into the network. Using this as a foothold in the network, attackers then leverage a myriad of
methods to elevate the privileges of those end-user accounts or compromise existing privileged accounts
in order to gain full access to the critical data they are targeting.
Thycotic Black Hat 2015
Hacker Survey Executive Report
Hackers identify Healthcare as a top target.
Given the relative value of personal health information (PHI) to hackers, in contrast with credit card
numbers, healthcare organizations are at the top of the list when it comes to targeted industries. The
hackers surveyed at Black Hat also indicated that healthcare is the industry that seems the most
vulnerable to them as well. When asked which industry (among healthcare, financial services,
government, oil and gas/energy, and education) they considered healthcare be the ripest target for
breach vulnerability healthcare was the leading answer of 29% of all respondents. Financial services
and government followed closely though, garnering 25% and 24% respectively. Interestingly, despite the
various reasons that hackers might target oil and gas/energy concerns such as hacktivism, terrorism,
or simply financial gain only 1 in 10 respondents considered that industry to be the most vulnerable to
breaches.
Recommendations
As a mandatory response for the continuing trend of credential theft and privileged account abuse
regardless of current security spends, its imperative that organizations begin practicing some level of
privileged account management and access management around the sensitive credentials most sought
after by attackers today. Privileged account management is a segmentation of IT security that securely
discovers, controls, and manages privileged account passwords and access to those accounts. As the
data shows, hackers are not going to stop targeting these credentials any time soon.
Below are some best practices for organizations to protect privilege accounts, enforce stronger security
policies and stop a breach in its tracks.
Thycotic Black Hat 2015
Hacker Survey Executive Report
1. Discover rogue accounts and secure them immediately. Often, organizations have thousands of
privileged accounts floating around their network that they are not always aware of. Or, as seen
in the survey data, hackers tend to come across necessary credentials in unsecured files like
spreadsheets. These accounts include: local administrator, root accounts, domain administrator,
and service accounts to name a few. By properly discovering these accounts on a scheduled basis
and automatically bringing them into a secure, encrypted vault, organizations can create an
active inventory of their usage, properly vault credentials and begin managing who has access to
these sensitive accounts.
2. Rotate passwords on privileged endpoints constantly. Because passwords are often a burden to
change manually, many credentials on privileged endpoints are left stale for years, making them
ripe for the picking for an attacker looking to escalate privilege during an attack. By constantly
rotating privileged account password lifecycles on a regular basis, youre stopping attackers in
their tracks from escalating privilege. During lifecycle management, make sure youre using a
PAM solution to generate and rotate complex, strong passwords that are difficult to crack.
3. Actively audit and monitor privileged user access. While securely vaulting credentials protects
them from direct exposure, and restricting user access to credentials limits potential misuse, it is
still important to build in a layer of monitoring around the use of those credentials in order to
verify that they are used appropriately and not abused. Audit trails are a must, to show who
accessed the credential, when they did so, and what was done with the credential. Additionally,
utilizing user or session monitoring tools can provide a recording of the activity performed with
the privileged credential to provide a forensic tool that can both determine what sort of malicious
activity took place on a system, or be used as a disaster recovery function to see what mistakes
may have been made to impact a system and more quickly undo the damage done.
4. Enforce strong password policies for end-users. While privileged accounts are the most coveted
credentials to provide attackers critical data access, end-user passwords are still an essential
checkmark in a hackers attack chain. Enforcing strong password policies on end-user credentials
helps protect those identities from being compromised during an attack. Passwords for end-users
should be reset, at a minimum, every 30-90 days, and be complex. Password changes should be
audited and performed via a self-service password reset mechanism to ensure your security
policys password complexity requirements are enforced, provide an audit log for compliance,
and improve employee experience by greatly reducing help desk calls, empowering end-users to
take control of their own password resets, and increasing ROI for internal support costs.
Survey Methodology
In August 2015, Thycotic surveyed 201 self-identified hackers live at the Black Hat 2014 event. Hackers
were defined as official attendees of the Black Hat conference who personally identified themselves as
a hacker at the time of the poll. Respondents remained anonymous to protect their personal identity.
For more information, please email sales@thycotic.com.
Das könnte Ihnen auch gefallen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Y 5Dokument2 SeitenY 5dexterrootNoch keine Bewertungen
- Y 4Dokument5 SeitenY 4dexterrootNoch keine Bewertungen
- Y 3Dokument6 SeitenY 3dexterrootNoch keine Bewertungen
- Y 2Dokument3 SeitenY 2dexterrootNoch keine Bewertungen
- Y1-Tehnical ReviewDokument2 SeitenY1-Tehnical ReviewdexterrootNoch keine Bewertungen
- BYODImplicationsforITs Complete PDFDokument5 SeitenBYODImplicationsforITs Complete PDFdexterrootNoch keine Bewertungen
- Evil Twin Access Point - WiFI Pumpkin - CybraryDokument6 SeitenEvil Twin Access Point - WiFI Pumpkin - CybrarydexterrootNoch keine Bewertungen
- Learning Services Securing Cisco Networks With Sourcefire Intrusion Prevention SystemDokument5 SeitenLearning Services Securing Cisco Networks With Sourcefire Intrusion Prevention Systemdexterroot0% (1)
- Iptables HowtoDokument226 SeitenIptables HowtodexterrootNoch keine Bewertungen
- How To Create Your FutureDokument44 SeitenHow To Create Your Futuredexterroot100% (1)
- Capture The Flag in Windows SecurityDokument13 SeitenCapture The Flag in Windows SecuritydexterrootNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Mid Term Exam 1Dokument2 SeitenMid Term Exam 1Anh0% (1)
- P 1 0000 06 (2000) - EngDokument34 SeitenP 1 0000 06 (2000) - EngTomas CruzNoch keine Bewertungen
- Electricity 10thDokument45 SeitenElectricity 10thSuryank sharmaNoch keine Bewertungen
- Supergrowth PDFDokument9 SeitenSupergrowth PDFXavier Alexen AseronNoch keine Bewertungen
- Instructions For Microsoft Teams Live Events: Plan and Schedule A Live Event in TeamsDokument9 SeitenInstructions For Microsoft Teams Live Events: Plan and Schedule A Live Event in TeamsAnders LaursenNoch keine Bewertungen
- A. The Machine's Final Recorded Value Was P1,558,000Dokument7 SeitenA. The Machine's Final Recorded Value Was P1,558,000Tawan VihokratanaNoch keine Bewertungen
- Cam Action: Series: Inch StandardDokument6 SeitenCam Action: Series: Inch StandardVishwa NNoch keine Bewertungen
- CIR Vs PAL - ConstructionDokument8 SeitenCIR Vs PAL - ConstructionEvan NervezaNoch keine Bewertungen
- Aluminum 3003-H112: Metal Nonferrous Metal Aluminum Alloy 3000 Series Aluminum AlloyDokument2 SeitenAluminum 3003-H112: Metal Nonferrous Metal Aluminum Alloy 3000 Series Aluminum AlloyJoachim MausolfNoch keine Bewertungen
- Ts Us Global Products Accesories Supplies New Docs Accessories Supplies Catalog916cma - PDFDokument308 SeitenTs Us Global Products Accesories Supplies New Docs Accessories Supplies Catalog916cma - PDFSRMPR CRMNoch keine Bewertungen
- Job Description For QAQC EngineerDokument2 SeitenJob Description For QAQC EngineerSafriza ZaidiNoch keine Bewertungen
- BST Candidate Registration FormDokument3 SeitenBST Candidate Registration FormshirazNoch keine Bewertungen
- Course Specifications: Fire Investigation and Failure Analysis (E901313)Dokument2 SeitenCourse Specifications: Fire Investigation and Failure Analysis (E901313)danateoNoch keine Bewertungen
- BSCSE at UIUDokument110 SeitenBSCSE at UIUshamir mahmudNoch keine Bewertungen
- Basic of An Electrical Control PanelDokument16 SeitenBasic of An Electrical Control PanelJim Erol Bancoro100% (2)
- Sourcing Decisions in A Supply Chain: Powerpoint Presentation To Accompany Powerpoint Presentation To AccompanyDokument58 SeitenSourcing Decisions in A Supply Chain: Powerpoint Presentation To Accompany Powerpoint Presentation To AccompanyAlaa Al HarbiNoch keine Bewertungen
- Low Cost Building ConstructionDokument15 SeitenLow Cost Building ConstructionAtta RehmanNoch keine Bewertungen
- TEVTA Fin Pay 1 107Dokument3 SeitenTEVTA Fin Pay 1 107Abdul BasitNoch keine Bewertungen
- How To Control A DC Motor With An ArduinoDokument7 SeitenHow To Control A DC Motor With An Arduinothatchaphan norkhamNoch keine Bewertungen
- Process States in Operating SystemDokument4 SeitenProcess States in Operating SystemKushal Roy ChowdhuryNoch keine Bewertungen
- TSR KuDokument16 SeitenTSR KuAngsaNoch keine Bewertungen
- HSBC in A Nut ShellDokument190 SeitenHSBC in A Nut Shelllanpham19842003Noch keine Bewertungen
- Unit Process 009Dokument15 SeitenUnit Process 009Talha ImtiazNoch keine Bewertungen
- Richards Laura - The Golden WindowsDokument147 SeitenRichards Laura - The Golden Windowsmars3942Noch keine Bewertungen
- PVAI VPO - Membership FormDokument8 SeitenPVAI VPO - Membership FormRajeevSangamNoch keine Bewertungen
- Section 8 Illustrations and Parts List: Sullair CorporationDokument1 SeiteSection 8 Illustrations and Parts List: Sullair CorporationBisma MasoodNoch keine Bewertungen
- Level 3 Repair: 8-1. Block DiagramDokument30 SeitenLevel 3 Repair: 8-1. Block DiagramPaulo HenriqueNoch keine Bewertungen
- Audit Certificate: (On Chartered Accountant Firm's Letter Head)Dokument3 SeitenAudit Certificate: (On Chartered Accountant Firm's Letter Head)manjeet mishraNoch keine Bewertungen
- CANELA Learning Activity - NSPE Code of EthicsDokument4 SeitenCANELA Learning Activity - NSPE Code of EthicsChristian CanelaNoch keine Bewertungen
- Polytropic Process1Dokument4 SeitenPolytropic Process1Manash SinghaNoch keine Bewertungen