Beruflich Dokumente
Kultur Dokumente
h323 Protocol Overview PDF
Hochgeladen von
EmadElDinEzzatOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
h323 Protocol Overview PDF
Hochgeladen von
EmadElDinEzzatCopyright:
Verfügbare Formate
Packetizer
H.323 Protocol Overview
Paul E. Jones
(October 2007)
Copyright 2007
Packetizer
Assumptions
Familiarity with audio, video, and data
conferencing
Familiarity with the role of
Coders/Decoders (codecs)
Familiarity with RTP/RTCP
www.packetizer.com
Packetizer
Sections
www.packetizer.com
Part 1: The Documentation
Part 2: High Level Overview
Part 3: ASN.1 Overview
Part 4: RAS
Part 5: Annex G/H.225.0
Part 6: H.225.0 Call Signaling
Part 7: H.245
Part 8: Fast Connect
Part 9: Extensibility
Part 10: TCS=0
Part 11: Odds and Ends
2
Packetizer
Part 1: The Documentation
www.packetizer.com
Packetizer
Who Defined H.323?
Recommendation H.323 is a standard
published by the International
Telecommunications Union
Telecommunications Sector (ITU-T)
Formerly known as CCITT
Refer to http://www.itu.int/ITU-T/
A permanent organ of the United Nations
System (refer to http://www.unsystem.org/)
www.packetizer.com
Packetizer
Base H.323 Documents
H.323 Umbrella document that describes the
usage of H.225.0, H.245, and other related
documents for delivery of packet-based
multimedia conferencing services
H.225.0 Describes three signaling protocols
(RAS, Call Signaling, and Annex G)
H.245 Multimedia control protocol (common to
H.310, H.323, and H.324)
www.packetizer.com
Packetizer
Typical H.323 Stack
Multimedia H.323
Applications, User Interface
Data
Applications
V.150
T.120
Media Control
T.38
Audio
Video
Codecs
Codecs
G.711
H.261
G.723.1
H.263
G.729
H.264
..
..
Terminal Control and Management
H.225.0
RTCP
Call
H.245
Signaling
H.225.0
RAS
RTP
UDP
TCP
TCP/UDP
UDP
TCP/UDP
TCP
UDP
IP
www.packetizer.com
Packetizer
Additional Documents
H.235 Security within H.245-based systems
H.245 Interworking with the PSTN
H.450.x Supplementary services
H.460.x Various H.323 protocol extensions
H.501 Protocol for mobility management and
inter/intra-domain communication
H.510 User, terminal, and service mobility
H.530 Security specification for H.510
www.packetizer.com
Packetizer
Implementers Guide
H.323-Series Implementers Guide
Addresses issues not adequately covered within
the aforementioned recommendations
Contains corrections to the aforementioned
recommendations
Updated every 9 months or so
Must be read in conjunction with the various
H.323-related Recommendations
www.packetizer.com
Packetizer
Annex versus Appendix
Often Recommendations will have Annexes
and appendices
An Annex is considered a normative part
of the Recommendation (i.e., it is part of the
standard)
An Appendix is considered a nonnormative part of the Recommendation
(i.e., it is informational only)
www.packetizer.com
Packetizer
H.323 Annexes
Annex A Mandatory H.245 messages
Annex B Procedures for layered video codecs
Annex C H.323 on ATM
Annex D Fax
Annex E UDP for Call Signaling
Annex F Simple Endpoint Type (SET)
Annex G Text telephony
Annex I Error prone channels (work in progress)
Annex J Secure SET
www.packetizer.com
10
Packetizer
H.323 Annexes
Annex K HTTP-based service control
Annex L Stimulus control protocol
Annex M.x Tunneling of various protocols
within H.323
Annex N QoS (work in progress)
Annex O Use of DNS (work in progress)
Annex P Modem over IP
Annex Q Far-end camera control
Annex R - Robustness
www.packetizer.com
11
Packetizer
H.323 Appendices
Appendix I Sample MC/terminal
communications
Appendix II Usage of RSVP
Appendix III Gatekeeper based user location
Appendix IV - Signalling prioritized alternative
logical channels in H.245
Appendix V - Use of E.164 and ISO/IEC 11571
numbering plans
www.packetizer.com
12
Packetizer
H.225.0 Annexes
Annex A RTP/RTCP (RFC 1889)
Annex B RTP profile (RFC 1890)
Annex C RTP payload for H.261
Annex D RTP payload for H.261A
Annex E Video packetization
Annex F Audio and multiplexed packetization
Annex G Communication between and within
Administrative Domains
Annex H ASN.1 Syntax
Annex I H.263+ packetization
www.packetizer.com
13
Packetizer
H.225.0 Appendices
Appendix I RTP/RTCP algorithms
(reference to RFC 1889)
Appendix II RTP profile (reference to
RFC 1890)
Appendix III H.261 packetization
(reference to RFC 2032)
Appendix IV TCP/IP/UDP usage
Appendix V ASN.1 usage
www.packetizer.com
14
Packetizer
H.245 Annexes
Annex A ASN.1 syntax
Annex B Semantic definition of messages
Annex C Procedures
Annex D Object identifier assignments
Annex E to M Various generic
capability definitions, including some
codecs
www.packetizer.com
15
Packetizer
H.245 Appendices
Appendix I Overview of ASN.1
Appendix II Example of H.245 procedures
Appendix III Timers and counters
Appendix IV H.245 extension procedure
Appendix V Using replacementFor
Appendix VI Example H.263 capabilities
Appendix VII Procedures and template for generic
capabilities
Appendix VIII List of generic capabilities for H.245
defined in other Recommendations
Appendix IX Usage of ASN.1 in H.245
www.packetizer.com
16
Packetizer
Part 2: High Level Overview
www.packetizer.com
17
Packetizer
Elements of an H.323 System
Terminals
Multipoint Control Units (MCUs)
Gateways
Gatekeeper
Border Elements / Peer Elements
www.packetizer.com
Referred to as
endpoints
18
Packetizer
Terminals
Telephones
Video phones
IVR devices
Voicemail Systems
Soft phones (e.g., NetMeeting)
T
www.packetizer.com
19
Packetizer
MCUs
Responsible for managing multipoint
conferences (two or more endpoints
engaged in a conference)
The MCU contains a Multipoint Controller
(MC) that manages the call signaling and
may optionally have Multipoint Processors
(MPs) to handle media mixing, switching,
or other media processing
MCU
www.packetizer.com
20
Packetizer
Gateways
The Gateway is composed of a Media Gateway
Controller (MGC) and a Media Gateway
(MG), which may co-exist or exist separately
The MGC handles call signaling and other nonmedia-related functions
The MG handles the media
Gateways interface H.323 to other networks,
including the PSTN, H.320 systems, other H.323
networks (proxy), etc.
GW
www.packetizer.com
21
Packetizer
Gatekeeper
The Gatekeeper is an optional component in
the H.323 system which is used for
admission control and address resolution
The gatekeeper may allow calls to be placed
directly between endpoints or it may route
the call signaling through itself to perform
functions such as follow-me/find-me,
forward on busy, etc.
GK
www.packetizer.com
22
Packetizer
Border Elements
Border Elements, which are often co-located with a
Gatekeeper, exchange addressing information and
participate in call authorization between administrative
domains
Border Elements may aggregate address information to
reduce the volume of routing information passed through
the network
Border elements may assist in call
authorization/authentication directly between two
administrative domains or via a clearinghouse
Peer elements are like border elements, but reside within
the interior of the administrative domain
BE
www.packetizer.com
23
Packetizer
Zone
A single Gatekeeper and all of the devices connected
to it
The physical location of the Gatekeeper with respect
to its endpoints is immaterial
There may be more than one physical Gatekeeper
device that provides the logical Gatekeeper
functionality for a zone
GW
GK
MCU
T
www.packetizer.com
There is no imposed limit
on the number or types of
devices in a zone
24
Packetizer
Administrative Domain
A collection of Zones that are under a single
administrative control (e.g., a service
provider or enterprise network)
There is no specified limit
on the number of Zones
within an Administrative
Domain
www.packetizer.com
25
Packetizer
Communication Between
Administrative Domains
Service providers or enterprise users have two options for
communicating between Administrative Domains
RAS Location Request (LRQ) messages
Annex G/H.225.0
Choice of protocols and topology is dictated by customer
requirements
Initial communication is generally for address resolution
only
Subsequent communication utilizes normal H.323
signaling between various elements to setup the call
www.packetizer.com
26
Packetizer
Topology with RAS
GK
GK
GK
GK
T
GK
T
www.packetizer.com
MCU
GW
GW
GK
GW
GW
GW
Hierarchical Gatekeeper
topology is widely used,
but explicitly discussed in
H.323
27
Packetizer
Topology with Annex G/H.225.0
BE
GK
BE
GK
T
GK
T
www.packetizer.com
MCU
GW
GW
GK
GW
GW
GW
28
Packetizer
High Level Call Flow
3. Collect replies to previous query
4. Grant
permission to
place call
GK
GK
7. Grant
permission
2. Try to resolve the address of the called party
1. Request
Permission to
place call
5. Attempt to establish the call
6. Request
permission
to accept call
GW
GW
8. Indicate connection establishment
www.packetizer.com
29
Packetizer
Part 3: ASN.1 Overview
www.packetizer.com
30
Packetizer
What is ASN.1?
Abstract Syntax Notation One
Protocol syntax language defined in ITU-T
Recommendations X.680 X.683
Provides various encoding rules, including
Packed Encoding Rules and XML encoding
rules
www.packetizer.com
31
Packetizer
Why ASN.1?
Separates the protocol syntax from the
encoding of the protocol that is transmitted
on the wire
Facilitate development of protocols that are
backward compatible
Allows developers to focus on the program
logic, rather than wasting time on parsing
tasks
www.packetizer.com
32
Packetizer
Packed Encoding Rules
The H.323 family of protocols use the
Packed Encoding Rules (PER), as specified
in ITU-T Recommendation X.691
PER is a very efficient, binary encoding
www.packetizer.com
33
Packetizer
Modules
Modules are syntax definitions for protocols
The syntax in Annex H/H.225.0 is one
module and the syntax for H.245 is one
module
One module can borrow definitions from
another module
www.packetizer.com
34
Packetizer
The ASN.1 Module in H.225.0
H323-MESSAGES DEFINITIONS AUTOMATIC TAGS ::=
--
BEGIN
-- The message and type definitions have been
-- omitted for brevity
IMPORTS
-SIGNED{},
ENCRYPTED{},
END
-- Of ASN.1
HASHED{},
ChallengeString,
TimeStamp,
RandomVal,
Password,
EncodedPwdCertToken,
ClearToken,
CryptoToken,
AuthenticationMechanism
FROM H235-SECURITY-MESSAGES
DataProtocolCapability,
T38FaxProfile
FROM MULTIMEDIA-SYSTEM-CONTROL;
www.packetizer.com
35
Packetizer
Common Integral Types
www.packetizer.com
INTEGER
OCTET STRING
NULL
BOOLEAN
IA5String
OBJECT IDENTIFER
BMPString
GeneralString
NumericString
36
Packetizer
Object Identifiers
Object Identifiers (OIDs) are a hierarchical
arrangement of integers that refer to some object
Used within LDAP and SNMP
Used within H.323-based systems to refer to
codecs, standard and non-standard protocol
extensions, etc.
Used to identify the particular version of H.225.0
or H.245 be transmitted (protocol identifier)
www.packetizer.com
37
Packetizer
Anatomy of an Object Identifier
{itu-t (0) recommendation (0) h (8) 2250 version (0) 6}
or
Common
within
ITU
documents
0.0.8.2250.0.6
Common
within
IETF
documents
www.packetizer.com
38
Packetizer
Common Syntax Structures
SEQUENCE think of C struct
SET think of C struct, but without order
for the members of the structure
CHOICE think of a C union
www.packetizer.com
39
Packetizer
Samples from H.225.0
H323-UserInformation ::= SEQUENCE
-- root for all Q.931 related ASN.1
{
h323-uu-pdu
H323-UU-PDU,
user-data SEQUENCE
{
protocol-discriminator
INTEGER
(0..255),
user-information
OCTET STRING (SIZE(1..131)),
...
} OPTIONAL,
...
}
www.packetizer.com
40
Packetizer
Samples from H.225.0 (cont.)
H323-UU-PDU ::= SEQUENCE
h245Control
SEQUENCE OF OCTET STRING OPTIONAL,
nonStandardControl
SEQUENCE OF NonStandardParameter OPTIONAL,
callLinkage
CallLinkage OPTIONAL,
h323-message-body
CHOICE
tunnelledSignallingMessage SEQUENCE
setup
Setup-UUIE,
callProceeding
CallProceeding-UUIE,
tunnelledProtocolID
TunnelledProtocol,
connect
Connect-UUIE,
messageContent
SEQUENCE OF OCTET STRING,
alerting
Alerting-UUIE,
tunnellingRequired
NULL OPTIONAL,
information
Information-UUIE,
nonStandardData
NonStandardParameter OPTIONAL,
releaseComplete
ReleaseComplete-UUIE,
...
facility
Facility-UUIE,
} OPTIONAL,
...,
provisionalRespToH245Tunneling
progress
Progress-UUIE,
empty
NULL,
status
Status-UUIE,
statusInquiry
StatusInquiry-UUIE,
setupAcknowledge
SetupAcknowledge-UUIE,
notify
Notify-UUIE
NULL OPTIONAL,
stimulusControl
StimulusControl OPTIONAL,
genericData
SEQUENCE OF GenericData OPTIONAL
},
nonStandardData
NonStandardParameter OPTIONAL,
...,
h4501SupplementaryService SEQUENCE OF OCTET STRING OPTIONAL,
h245Tunneling
www.packetizer.com
BOOLEAN,
41
Packetizer
Samples from H.225.0 (cont.)
::=
OCTET STRING (SIZE(16))
ConferenceIdentifier
::=
GloballyUniqueID
RequestSeqNum
::=
INTEGER (1..65535)
GatekeeperIdentifier
::=
BMPString (SIZE(1..128))
BandWidth
::=
INTEGER (0..4294967295)
CallReferenceValue
::=
INTEGER (0..65535)
EndpointIdentifier
::=
BMPString (SIZE(1..128))
ProtocolIdentifier
::=
OBJECT IDENTIFIER
Definition of new types
GloballyUniqueID
BandwidthRequest ::= SEQUENCE --(BRQ)
{
requestSeqNum
RequestSeqNum,
endpointIdentifier
EndpointIdentifier,
conferenceID
ConferenceIdentifier,
callReferenceValue
CallReferenceValue,
callType
CallType OPTIONAL,
bandWidth
BandWidth,
nonStandardData
NonStandardParameter OPTIONAL,
...,
callIdentifier
CallIdentifier,
gatekeeperIdentifier
GatekeeperIdentifier OPTIONAL,
tokens
SEQUENCE OF ClearToken OPTIONAL,
cryptoTokens
SEQUENCE OF CryptoH323Token OPTIONAL,
integrityCheckValue
ICV OPTIONAL,
answeredCall
BOOLEAN,
callLinkage
CallLinkage OPTIONAL,
capacity
CallCapacity OPTIONAL,
usageInformation
RasUsageInformation OPTIONAL,
bandwidthDetails
SEQUENCE OF BandwidthDetails OPTIONAL,
genericData
SEQUENCE OF GenericData OPTIONAL
www.packetizer.com
42
Packetizer
Using an ASN.1 Compiler and
PER Encoder/Decoder
Compile the root ASN.1 module, along with
dependent modules (so that IMPORTS can be
taken), and link the resulting source files with
your application
To send a message
Populate the data structures generated by the compiler
Call encode() and then send the resulting data
When receiving a message
Call decode() to get appropriate data structures
www.packetizer.com
43
Packetizer
ASN.1 Resource Sites
Electronic books on ASN.1:
http://www.asn1.org/books/index.htm
ASN.1 Information Site:
http://asn1.elibel.tm.fr/
ASN.1 Consortium:
http://www.asn1.org/
www.packetizer.com
44
Packetizer
Part 4: RAS
www.packetizer.com
45
Packetizer
RAS
Registration, Admission, and Status
Used between the endpoint and its Gatekeeper in
order to
Allow the Gatekeeper to manage the endpoint
Allow the endpoint to request admission for a call
Allow the Gatekeeper to provide address resolution
functionality for the endpoint
RAS signaling is required when a Gatekeeper is
present in the network (i.e., the use of a
Gatekeeper is conditionally mandatory)
www.packetizer.com
46
Packetizer
General Format of RAS
RAS messages generally have three types
Request (xRQ)
Reject (xRJ)
Confirm (xCF)
Exceptions are
Information Request / Response / Ack / Nak
The nonStandardMessage
The unknownMessage response
Request in Progress (RIP)
Resource Available Indicate / Confirm (RAI/RAC)
Service Control Indication / Response
www.packetizer.com
47
Packetizer
RAS Port
Typically, RAS communications is carried out via
UDP through port 1719 (unicast) and 1718
(multicast)
For backward compatibility sake, an endpoint should be
prepared to receive a unicast message on port 1718 or
1719
Only UDP is defined for RAS communications
GRQ and LRQ may be send multicast, but are
generally sent unicast
All other RAS messages are sent unicast
www.packetizer.com
48
Packetizer
Gatekeeper Request - GRQ
When an endpoint comes to life, it should try to
discover a gatekeeper by sending a GRQ
message to a Gatekeeper
Address of a Gatekeeper may be provisioned
The endpoint may send a multicast GRQ
Address of a Gatekeeper may be found through DNS
queries (Annex O/H.323)
There may be multiple Gatekeepers that could
service an endpoint, thus an endpoint should look
through potentially several GCF/GRJ messages
for a reply
www.packetizer.com
49
Packetizer
Contents of a GRQ
GatekeeperRequest ::= SEQUENCE
{
requestSeqNum
RequestSeqNum,
protocolIdentifier
ProtocolIdentifier,
nonStandardData
NonStandardParameter OPTIONAL,
rasAddress
TransportAddress,
endpointType
EndpointType,
gatekeeperIdentifier
GatekeeperIdentifier OPTIONAL,
callServices
QseriesOptions
endpointAlias
SEQUENCE OF AliasAddress OPTIONAL,
OPTIONAL,
...,
alternateEndpoints
SEQUENCE OF Endpoint OPTIONAL,
tokens
SEQUENCE OF ClearToken OPTIONAL,
cryptoTokens
SEQUENCE OF CryptoH323Token OPTIONAL,
authenticationCapability SEQUENCE OF AuthenticationMechanism OPTIONAL,
algorithmOIDs
SEQUENCE OF OBJECT IDENTIFIER OPTIONAL,
integrity
SEQUENCE OF IntegrityMechanism OPTIONAL,
integrityCheckValue
ICV OPTIONAL,
supportsAltGK
NULL OPTIONAL,
featureSet
FeatureSet OPTIONAL,
genericData
SEQUENCE OF GenericData OPTIONAL
www.packetizer.com
50
Packetizer
Gatekeeper Reject - GRJ
If a Gatekeeper does not wish to provide service to
the endpoint, it will generally send a GRJ message
to the endpoint
As a security consideration to avoid DoS attacks, one
might want to consider ignoring requests from
unknown endpoints
The GRJ message will carry one of several
rejection reasons
As mentioned, most request messages have
reject and confirm counterparts. We will
discuss GRJ/GCF for illustration, but no special
attention is given to other xRJ messages.
www.packetizer.com
51
Packetizer
Contents of a GRJ
GatekeeperReject ::= SEQUENCE
GatekeeperRejectReason ::= CHOICE
{
requestSeqNum
RequestSeqNum,
resourceUnavailable
NULL,
protocolIdentifier
ProtocolIdentifier,
terminalExcluded
NULL,
nonStandardData
NonStandardParameter OPTIONAL,
invalidRevision
NULL,
gatekeeperIdentifier
GatekeeperIdentifier
undefinedReason
NULL,
rejectReason
GatekeeperRejectReason,
OPTIONAL,
...,
...,
securityDenial
NULL,
altGKInfo
AltGKInfo OPTIONAL,
genericDataReason
NULL,
tokens
SEQUENCE OF ClearToken OPTIONAL,
neededFeatureNotSupported
NULL
cryptoTokens
SEQUENCE OF CryptoH323Token OPTIONAL,
integrityCheckValue
ICV OPTIONAL,
featureSet
FeatureSet OPTIONAL,
genericData
SEQUENCE OF GenericData OPTIONAL
www.packetizer.com
52
Packetizer
Gatekeeper Confirm - GCF
If the Gatekeeper wishes to provide service
to the endpoint, it will return a GCF
message
The GCF message will contain a number of
data elements that will later be used by the
endpoint
www.packetizer.com
53
Packetizer
Contents of a GCF
GatekeeperConfirm ::= SEQUENCE
{
requestSeqNum
RequestSeqNum,
protocolIdentifier
ProtocolIdentifier,
nonStandardData
NonStandardParameter OPTIONAL,
gatekeeperIdentifier
GatekeeperIdentifier
rasAddress
TransportAddress,
OPTIONAL,
...,
alternateGatekeeper
SEQUENCE OF AlternateGK OPTIONAL,
authenticationMode
AuthenticationMechanism OPTIONAL,
tokens
SEQUENCE OF ClearToken OPTIONAL,
cryptoTokens
SEQUENCE OF CryptoH323Token OPTIONAL,
algorithmOID
OBJECT IDENTIFIER OPTIONAL,
integrity
SEQUENCE OF IntegrityMechanism OPTIONAL,
integrityCheckValue
ICV OPTIONAL,
featureSet
FeatureSet OPTIONAL,
genericData
SEQUENCE OF GenericData OPTIONAL
www.packetizer.com
54
Packetizer
Gatekeeper Discovery
GK
1. GRQ
2. GCF
GW
GW
Communication is over
ports 1718 (multicast)
and, most commonly,
1719 (unicast)
www.packetizer.com
55
Packetizer
Gatekeeper Registration - RRQ
Once a Gatekeeper has been discovered, the endpoint
will then register with the Gatekeeper in order to receive
services
Communication is exclusively via port 1719 (unicast)
Endpoint will send an RRQ and expect to receive either an
RCF or RRJ
Reception of an RRJ simply means that the endpoint will
not receive services from the Gatekeeper, not that the
endpoint cannot communicate on the network
www.packetizer.com
56
Packetizer
Gatekeeper Registration (cont.)
During the registration process, the Gatekeeper will assign
an endpoint identifier to the endpoint, which is to be
used during subsequent communications with the
Gatekeeper
The endpoint will supply a list of endpoint alias addresses
and the Gatekeeper will indicate which ones it accepts
The Gatekeeper may grant the endpoint permission to
place calls without using the ARQ/ACF exchange (called
pre-granted ARQs)
The endpoint will indicate a time to live and the
Gatekeeper may accept that or a lower TTL value
www.packetizer.com
57
Packetizer
Lightweight RRQs
The time to live indicated in the RRQ
tells the Gatekeeper when it may freely
unregister the endpoint due to inactivity
The endpoint may renew its registration by
sending either a full RRQ message or a
lightweight RRQ (LW RRQ)
The LW RRQ message only contains a few
elements and is only intended to refresh the
endpoints registration
www.packetizer.com
58
Packetizer
Gatekeeper Registration (cont.)
GK
1. RRQ
2. RCF
GW
GW
Communication is
exclusively over port 1719
(unicast)
www.packetizer.com
59
Packetizer
Admission Request - ARQ
Once registered with a Gatekeeper, the endpoint may only
initiate or accept a call after first requesting admission to
the Gatekeeper via the ARQ message (except in the case
that pre-granted ARQs is in use)
The Gatekeeper may may accept (ACF) or reject (ARJ) the
request to place or accept a call
The endpoint will indicate the destination address(es) and
the Gatekeeper may (if canMapAlias is true) return an
alternate set of destination addresses
The endpoint uses a unique call reference value (CRV)
between itself and the GK to refer to this call (link
significant)
www.packetizer.com
60
Packetizer
Admission Request (cont.)
The endpoint will provide a Call Identifier (CallID), which
is a globally unique value
The endpoint will indicate a conference ID (CID), or 0 if
the conference ID is not known
This is unique if the call is point to point
This value is shared by all participants in the same multipoint
conference
Some devices do not properly handle CID=0
The endpoint will indicate the desired bandwidth and the
Gatekeeper may adjust that value to a lower value
The endpoint will indicate whether it is originating or
answering a call
www.packetizer.com
61
Packetizer
Admission Request (cont.)
GK
1. ARQ
2. ACF { GW2 }
GW
www.packetizer.com
3. SETUP
GW
62
Packetizer
Reference Value Soup
CRV Call Reference Value
16 bit integer that is link significant
most significant bit indicates the direction of the call (0 = originator, 1 =
terminator)
CRV used in the ARQ to originate a call must be the subsequent SETUP
message (interoperability with version 1)
CRV used in ARQ to answer a call does not have to be the same as that
received in SETUP
CID Conference Identifier
A Globally unique (UUID or GUID) identifier that is shared by all
participants in the same conference
CallID Call Identifier
A globally unique (UUID or GUID) identifier that is unique to that
particular call
www.packetizer.com
63
Packetizer
Location Request - LRQ
The LRQ message is sent by either an
endpoint or a Gatekeeper to a Gatekeeper in
order to resolve the address of an alias
address (e.g., to turn a telephone number
into an IP address)
While LRQs may be sent by endpoints, they
are almost exclusively sent by Gatekeepers
www.packetizer.com
64
Packetizer
Location Request (cont.)
3. LCF
4. ACF
GK
2. LRQ
1. ARQ
GK
7. ACF
6. ARQ
5. Attempt to establish the call
GW
www.packetizer.com
8. Indicate connection establishment
GW
65
Packetizer
Bandwidth Request - BRQ
Subsequent to initial call setup, the endpoint may
wish to to use more or less bandwidth than
previously indicated via the BRQ
Note that, while it is syntactically legal for the GK to
send a BRJ to a request asking for less bandwidth, this
makes no sense and should not be done
An endpoint must send a BRQ subsequent to
initial call establishment if the actual bandwidth
utilized is less than initially requested
www.packetizer.com
66
Packetizer
Bandwidth Request (cont.)
GK
1. BRQ
2. BCF
GW
GW
Established Call
www.packetizer.com
67
Packetizer
Disengage Request - DRQ
Once a call completes, the endpoint sends a DRQ
message to the Gatekeeper
The Gatekeeper may send a DRJ, but this is strongly
discouraged if an endpoint is sending a DRQ, it
means the call is over and cannot be rejected!
The DRQ is an opportunity for the endpoint to
report information useful for billing
The Gatekeeper may also send a DRQ to force the
endpoint to disconnect the call
www.packetizer.com
68
Packetizer
Information Request - IRQ
The IRQ is sent by the Gatekeeper to the endpoint
to request information about one or all calls
There are many details about each call that are
reported to the Gatekeeper in the Information
Response (IRR) message
There are provisions in H.323 to allow the
endpoint to provide call information periodically
and unsolicited
The Gatekeeper may acknowledge or provide
negative acknowledgement to an unsolicited IRR
www.packetizer.com
69
Packetizer
Request In Progress - RIP
A RIP message may be sent by the endpoint
or the Gatekeeper to acknowledge receive
of a RAS message that cannot be responded
to in normal processing time
www.packetizer.com
70
Packetizer
Resource Availability - RAI
The Resource Available Indicate (RAI)
message is sent by an endpoint to indicate
when it has neared resource limits or is no
longer near a resource limit
The Gatekeeper replies with Resource
Available Confirm (RAC)
www.packetizer.com
71
Packetizer
Service Control Indication - SCI
This message is sent by either the endpoint or the
Gatekeeper to invoke some type of service
The responding entity replies with Service
Control Response (SCR)
The SCI/SCR messages are used for specific
services that are and will be defined for H.323,
including Gatekeeper requested tones and
announcements and stimulus control (Annex
K/H.323)
www.packetizer.com
72
Packetizer
Miscellaneous Messages
Unknown Message Response is sent to an
unrecognized message
Non-Standard Message is used to allow
Gatekeepers and endpoints to exchange
messages that are not standard
www.packetizer.com
73
Packetizer
RAS Timers and Retries
RAS message
www.packetizer.com
Time-out value (s)
Retry count
GRQ
RRQ
URQ
ARQ
BRQ
IRQ
IRR
DRQ
LRQ
RAI
SCI
74
Packetizer
Part 5: Annex G/H.225.0
www.packetizer.com
75
Packetizer
Standards
Annex G/H.225.0 Communication Between
And Within Administrative Domains
The actual protocol specification exists in H.501
Annex Gv1 (1999) focused on communication
between administrative domains
Annex Gv2 (2002) expanded the scope to include
communication within administrative domains
www.packetizer.com
76
Packetizer
Role
Annex G was originally designed with the clearinghouse
model in mind, wherein calls originate in one
administrative domain and terminate in another
That role was then expanded to include generally useful
address resolution functions, propagation of routing
information, etc.
Two new functional entities were introduced into the
H.323 network
Peer Element
Border Element
www.packetizer.com
77
Packetizer
RAS LRQ versus Annex G
Address resolution
Propagation of routing
information
Usage reporting
Access authorization (useful for
clearinghouses and nonclearinghouse environments)
A Border Element or Peer
Element can act as an
aggregation point (usually the
role of a Border Element)
Annex G/H.225.0
www.packetizer.com
RAS
Address resolution
78
Packetizer
Architecture
Back End
services
D
D
D
Gatekeeper/
Peer Element
B
Border
Element
B
Gatekeeper/
Peer Element
Administrative Domain A
Border
Element
Gatekeeper/
Peer Element
B
Gatekeeper/
Peer Element
Administrative Domain B
Interface D is out of
Scope
www.packetizer.com
79
Packetizer
H.501 Messages Supported by
Annex G/H.225.0 Entities
www.packetizer.com
ServiceRequest
ServiceConfirmation
ServiceRejection
ServiceRelease
DescriptorRequest
DescriptorConfirmation
DescriptorRejection
DescriptorIDRequest
DescriptorIDConfirmation
DescriptorIDRejection
DescriptorUpdate
DescriptorUpdateAck
AccessRequest
AccessConfirmation
AccessRejection
RequestInProgress
NonStandardRequest
NonStandardConfirmation
NonStandardRejection
UnknownMessageResponse
UsageRequest
UsageConfirmation
UsageRejection
UsageIndication
UsageIndicationConfirmation
UsageIndicationRejection
ValidationRequest
ValidationConfirmation
ValidationRejection
80
Packetizer
Part 6: H.225.0 Call Signaling
www.packetizer.com
81
Packetizer
Introduction
H.225.0 Call Signaling is used to establish
calls between two H.323 entities
It was derived from Q.931 (ISDN call
signaling), but was modified to be suitable
for use on a packet based network
ASN.1 was added to augment to Q.931
information and is stored in the User to
User Information Element from Q.931
H.225.0 also borrows messages from Q.932
www.packetizer.com
82
Packetizer
H.225.0 Call Signaling Message
TPKT Q.931 Header IE IE IE IE IE IE IE IE IE
...
IE IE IE IE IE IE IE IE IE IE IE IE UUIE
The UUIE refer to the User-User Information Element. It should be
the last octet in the chain, but some implementations do not properly
order IEs. It is comprised of 0x7E, HH, LL, PD, and DATA. 0x7E is
the identifier for the User-User IE, HH and LL are the length of DATA
in network byte order, PD is a protocol discriminator for ASN.1 (0x05)
and DATA is the ASN.1 PER encoded H323-UserInformation.
Various Information Elements (IEs) that are appropriate for the message type. These
are listed in H.225.0, but note that any valid Q.931 IE may be transmitted and should
not result in a protocol failure by the endpoint.
All messages have a Q.931 header that includes a single octet called the protocol discriminator
(0x08), three octets for the CRV (0x02, HH, LL, where 0x02 is the length of the CRV and HH and
LL are the two octets of the CRV in network byte order), and single octet for the message type
(specified in respective sections in Q.931).
Four octets that separate messages on the wire (necessary for TCP). They are defined in section 6 of RFC
1006. There are 0x03, 0x00, HH, LL. HH and LL represent the entire message length, including the
TPKT header, in network byte order.
www.packetizer.com
83
Packetizer
Information Elements
Information elements carry additional information
related to the specific message
For example, SETUP has, among other things, a
Calling Party Number IE, Called Party
Number IE, Display IE, etc.
Every H.225.0 message has a UUIE, though this is
not true of Q.931
H.225.0 made a number of changes to Q.931 and
should be the guiding document
www.packetizer.com
84
Packetizer
H.225.0 Call Signaling Messages
Setup
Call Proceeding
Alerting
Information
Release Complete
Facility
www.packetizer.com
Progress
Status
Status Inquiry
Setup Acknowledge
Notify
Connect
85
Packetizer
Basic Call Setup Signaling
Setup
Optional
Call Proceeding
Progress
Alerting
Connect
GW
GW
CONNECTED
Release Complete
www.packetizer.com
86
Packetizer
Comments on Call Establishment
The basic call setup procedures are pretty
straight forward
The setup procedure can be as simple as
Setup and Connect
Intermediate messages (labeled as optional
on the previous slide) are generally useful to
prevent timeout errors and to provide inband tones and announcements
www.packetizer.com
87
Packetizer
Progress Message and Progress
Indicator
When a user places a call, he or she expects
to hear a ringing tone or an announcement
providing some information about why the
call failed
These in-band tones and announcements
are provided by using the Progress message
and the Progress Indicator IE (PI)
Section 8.1.7.4/H.323 describes this more
fully
www.packetizer.com
88
Packetizer
RAS and H.225.0 Call Signaling
3. LCF
4. ACF
GK
GK
2. LRQ
1. ARQ
7. ACF
6. ARQ
5. Setup
GW
www.packetizer.com
8. Connect
GW
89
Packetizer
Overlapped Sending
In some cases, the user may not have entered a
complete telephone number
Overlapped sending allows the calling endpoint to
provide additional dialed digits to the called
endpoint during the call establishment procedure
Overlapped sending is generally most useful in
H.225.0 Call Signaling, but RAS also allows for
overlapped sending (refer to 8.1.12/H.323 for
details)
www.packetizer.com
90
Packetizer
Call Forwarding
A Facility message with reason callForwarded
allows for simple call redirection
The H.323 standard states that this shall only be
used for forwarding a call prior to connect
In reality, many vendors use it as a lightweight
means of performing a call transfer operation
H.450.2 more fully describes a call transfer
mechanism for H.323 systems
www.packetizer.com
91
Packetizer
Call Forwarding (cont.)
Setup
GW
Facility (Reason = Call Forwarded)
GW
Release Complete
Setup
GW
Sometimes called
Facility Call Transfer
www.packetizer.com
92
Packetizer
H.450.x
H.450.x is a whole series of supplementary
service specifications for H.323
H.450.1 is not a service, per se, but is the
document upon which all services are based
This series of document provide services
like call transfer, call park, call hold,
message waiting indication, etc.
www.packetizer.com
93
Packetizer
Part 7: H.245
www.packetizer.com
94
Packetizer
Comments on H.245
H.245 is a protocol shared by a number of H.32x series
protocols, including H.324M, which is used for multimedia
conferencing within 3GPP wireless networks
Like Q.931, not everything inside H.245 is applicable to
H.323
Refer to Annex A/H.323 for H.245 messages used by H.323
endpoints
There are a lot of H.245 messages but dont let that scare
you
H.245 signaling is intended to be carried out in parallel to
H.225.0 signaling and preferably before the CONNECT
message waiting for the CONNECT will delay media
establishment and result in media clipping
www.packetizer.com
95
Packetizer
Purpose
H.245 provides control to the multimedia
session that has been established
Terminal capability exchange
Master/Slave determinations
Logical channel signaling
Conference control
www.packetizer.com
96
Packetizer
H.245 Control Channel
H.245 messages are carried via a special
channel called the H.245 Control Channel
Opening the H.245 Control Channel is optional
(see later discussion on Fast Connect)
The H.245 channel is often a separate TCP
connection, but it may be tunneled inside of the
H.225.0 Call Signaling Channel
When using UDP for call signaling, the H.245
Control Channel must be tunneled inside the
H.225.0 call signaling channel
www.packetizer.com
97
Packetizer
H.245 Message
TPKT H.245 PDU H.245 PDU
...
H.245 PDU H.245 PDU
Additional H.245 PDUs may be encoded following the first one. However, many
implementations cannot handle this and, as such, it is ill-advised to place them end-toend like this. It is strongly recommended to place only one between each TPKT
header, but do be prepared for the case that more than one PDU does exist following
TPKT
H.245 messages are encoded in ASN.1 PER and follow the TPKT header in the H.245 Control
Channel.
Four octets that separate messages on the wire (necessary for TCP). They are defined in section 6 of RFC
1006. There are 0x03, 0x00, HH, LL. HH and LL represent the entire message length, including the
TPKT header, in network byte order.
www.packetizer.com
98
Packetizer
H.245 Tunneling
H.245 is generally transmitted on a separate
TCP connections by most older endpoints
Newer endpoints generally support H.245
Tunneling, which is the ability to place the
H.245 PDUs inside the H.225.0 Call
Signaling channel
When tunneling, TPKT is not used
Multiple H.245 PDUs may be tunneled in a
single H.225.0 message
www.packetizer.com
99
Packetizer
Four H.245 Message Types
(and examples of each)
Request
masterSlaveDetermination
terminalCapabilitySet
Response
masterSlaveDeterminationAck
terminalCapabilitySetAck
Command
sendTerminalCapabilitySet
Indication
userInput
www.packetizer.com
100
Packetizer
Capabilities Exchange
The capability exchange (or caps exchange) allows two
endpoints to exchange information about what media
capabilities they possess, such as G.711, G.723, H.261,
and H.263
Along with the type of media, specific details about the
maximum number of audio frames or samples per packet is
exchanged, information about support for silence
suppression (VAD), etc. are exchanged
Using this capability information, endpoints can select
preferred codes that are suitable to both parties
The terminalCapabilitySet (TCS) must be the first
message transmitted on the H.245 Control Channel
www.packetizer.com
101
Packetizer
Capabilities are Numbered
Each capability is
numbered in a
capability table
All attributes (VAD,
frames/packet, etc.) are
part of the the
capability in the table
www.packetizer.com
1 G.723.1
Sample
Capability
Table
2 G.711
3 H.261
4 H.264
5 T.38
102
Packetizer
Simultaneous Capabilities
When endpoints advertise capabilities, they
also advertise which capabilities may be
performed simultaneously
It may not be possible, for example, for an
endpoint to open a T.38 channel at the same
time as a V.150.1 channel
It may not be possible, due to bandwidth
limits, to open a high bit-rate video codec at
the same time as a high bit-rate audio codec
www.packetizer.com
103
Packetizer
Capability Descriptors
The capability
descriptor contains the
sets of simultaneous
capabilities
Only one descriptor
may be used at a time
(i.e., capabilities from
descriptor 1 and
descriptor 2 may not be
used simultaneously)
1 G.723.1
2 G.711
3 H.261
4 H.264
Simultaneous
Capabilities
5 T.38
Capability Table
1
2
3
4
Descriptor 1
www.packetizer.com
Descriptor 2
104
Packetizer
Master Slave Determination
Once capabilities are exchanged, the endpoints
negotiate master and slave roles
Actually the master/slave messages can be sent along
with the TCS message
The master in a point to point conference really
only has the power to indicate when channels are
in conflict (e.g., when one the other terminal tries
to open a channel that is not compatible)
The slave device must yield to the requests of the
master device and reconfigure channels
appropriately
www.packetizer.com
105
Packetizer
Logical Channel Signaling
Channels are opened by exchanging
openLocalChannel (OLC) messages
The OLC will contain one of the
capabilities that was previously advertised
by the other endpoint
Voice and video channels are
unidirectional, so each end must transmit
an OLC to open a logical channel
www.packetizer.com
106
Packetizer
Logical Channel Signaling (cont)
Within the OLC, a session ID is assigned
Session 1 is the default audio session, 2 is the
default video session, and 3 is the default data
session
Additional session IDs may be used, but are
assigned by the master in the call
There is a relationship between H.245 sessions
IDs and RTP: OLCs with the same session ID are
considered to be part of the same RTP/RTCP
session
www.packetizer.com
107
Packetizer
Closing the H.245 Control
Channel
H.323 specifies that, in order to close the H.245
Control Channel, the endpoint must:
Close all open logical channels
Wait for all acknowledgement messages
Send an endSession command
Wait for an endSession from the other side
In reality, most endpoint vendors dont bother
they just use the H.225.0 Release Complete
command to terminate the call and close the H.245
Control Channel, as that is much more efficient
www.packetizer.com
108
Packetizer
Part 8: Fast Connect
www.packetizer.com
109
Packetizer
What is Fast Connect
Fast Connect (also improperly referred to as
fast start, after the name of the associated
field) is a means of establishing an H.323
call with as few as two messages
With the use of Fast Connect, there is no
need to open an H.245 channel, as long as
all needed media can be negotiated via Fast
Connect
www.packetizer.com
110
Packetizer
Initiating Fast Connect
When transmitting a SETUP message, the endpoint will
populate the fastStart element with OpenLogicalChannel
messages from H.245 (Note: these are just the data
structures, not the entire H.245 message)
Each OLC represents a proposed channel in either the
forward (transmitting from the caller to the called party)
or the reverse (transmitting from the called to the calling
party) direction
Each OLC with the same session ID number is considered
alternate proposals (i.e., if two proposals are made for
session ID 1, only one of the two may be selected)
www.packetizer.com
111
Packetizer
Responding to Fast Connect
To accept Fast Connect, an endpoint may select any
fastStart element in the SETUP message, populate the
necessary data fields (as specified in H.323), and return a
fastStart element in any message to the caller
An endpoint rejects Fast Connect by either explicitly
indicating so (there is a flag for this), initiating any H.245
communications, or providing an H.245 address for the
purposes of initiating H.245 communications
Until Fast Connect is accepted or rejected, the calling
endpoint may not initiate H.245 procedures (there is a
exception to this rule in H.323v4 designed to avoid race
conditions that would otherwise exist)
www.packetizer.com
112
Packetizer
A Fast Connect Call
3. LCF
4. ACF
GK
2. LRQ
GK
1. ARQ
7. ACF
6. ARQ
5. Setup (with fastStart)
GW
8. Connect (with fastStart)
GW
Of course, there are generally
intermediate H.225.0
messages fastStart should be
returned as quickly as possible
www.packetizer.com
113
Packetizer
Part 9: Extensibility
www.packetizer.com
114
Packetizer
Nonstandard Data
H.323 may be extended by vendors, service providers, or
national bodies by using the non-standard data fields
found throughout H.323 and H.245
The nonstandard data fields are essentially OCTET
STRINGS that be populated with any kind of data
Most often, vendors will create ASN.1 data structures that
are encoded within the non-standard data elements
The nonstandard data can be identified by object identifier,
vendor identifier
Vendor identifiers are comprised of a T.35 country, extension
(nationally assigned), and manufacturer code (nationally assigned)
www.packetizer.com
115
Packetizer
Generic Extensibility Framework
The Generic Extensibility Framework (GEF) was
introduced in H.323v4 to address the need to extend H.323
with features that are not necessarily of horizontal interest
One can think of GEF as a means of extending H.225.0 in
such a way as to not grow the base H.225.0 or H.323
documents, but still provide the same desired capability as
if such extensions had been added to the base documents
GEF capabilities (or feature sets) may be advertised,
signaled as desired or required, etc.
If a caller indicates that it requires feature X, but the called
entity cannot provide feature X, the call should not
complete
www.packetizer.com
116
Packetizer
GEF Documents
GEF-based extensions to H.323 are defined
in a series of documents number H.460.x
H.460.6, as an example, extends the concept
of Fast Connect in such a way that media
channels may be re-negotiated, closed, and
then re-opened on-the-fly without ever
starting H.245 procedures very useful for
routing to an IVR, then re-routing to a final
destination
www.packetizer.com
117
Packetizer
Part 10: TCS=0
www.packetizer.com
118
Packetizer
Third Party Pause and ReRouting
H.323v2 defined a mechanism whereby a third
party may pause an endpoint and then re-route
the call
This is done be sending an empty capability set
(TCS=0 or ECS)
The reception of this results in the receiver closing
its transmit channels and awaiting to be awoken
While it is paused the re-routing entity may reroute the call
www.packetizer.com
119
Packetizer
Leaving the Paused State
Once re-routed, the re-routing entity will transmit
a non-empty capability set, which indicates the
capabilities of the new remote endpoint
Upon leaving the paused state, the endpoint shall
reset its H.245 state machine and re-negotiate
master/slave, open channels, etc.
When leaving the paused state, a TCS message is
not sent, as it is considered the responsibility of
the re-routing entity
www.packetizer.com
120
Packetizer
Poor Mans Call Hold
Just as a Facility message with reason
callForwarded is used to transfer a call,
some use TCS=0 as a means of putting an
endpoint on hold
It works, but there is a more complete
Hold service specified in H.450.4
www.packetizer.com
121
Packetizer
Part 11: Odds and Ends
www.packetizer.com
122
Packetizer
Alternate Gatekeepers
For the purposes of redundancy, H.323 has the
notion of alternate Gatekeepers
When an endpoint registers with its Gatekeeper, it
will be provided with a list of alternate
Gatekeepers
If the primary Gatekeeper fails, the endpoint
switches over to an alternate Gatekeeper and
continues communication
More than one alternate Gatekeeper may be
provided to the endpoint
www.packetizer.com
123
Packetizer
Capacity Reporting
So as to prevent calls from being directed to
endpoints (especially Gateways) that are at
or near capacity, endpoints have the
wherewithal to report their call capacity
The capacity information shared includes
the maximum number of calls and the
current number of calls
This is a complementary feature to the RAI
message in RAS
www.packetizer.com
124
Packetizer
Alias Addresses
H.323 offers a number of alias address types
dialedDigits (formerly called e164)
h323-ID
url-ID
transportID
email-ID
partyNumber
mobileUIM
Of these, dialedDigits is the most widely used for placing calls (as
users today generally still use telephone numbers)
h323-IDs are of local significance and are usually just used between an
endpoint and its Gatekeeper
url-ID (including the H.323 URL and tel URL) and e-mail addresses
are becoming more popular
www.packetizer.com
125
Packetizer
Informative H.323 Sites
Packetizer
http://www.packetizer.com/
H.323 Forum
http://www.h323forum.org/
H.323 Plus
http://www.h323plus.org/
www.packetizer.com
126
Packetizer
Packetizer
www.packetizer.com
127
Das könnte Ihnen auch gefallen
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5795)
- Science Pp3 - Unit 2Dokument37 SeitenScience Pp3 - Unit 2EmadElDinEzzatNoch keine Bewertungen
- Quality of Service (Qos) in High-Priority Applications: The Conversion Technology ExpertsDokument12 SeitenQuality of Service (Qos) in High-Priority Applications: The Conversion Technology ExpertsEmadElDinEzzatNoch keine Bewertungen
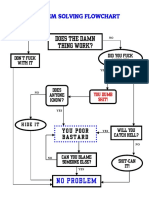
- Problem Solving Flowchart: Does The Damn Thing Work?Dokument1 SeiteProblem Solving Flowchart: Does The Damn Thing Work?EmadElDinEzzatNoch keine Bewertungen
- Whitepaper Jive Hosted VoipDokument9 SeitenWhitepaper Jive Hosted VoipEmadElDinEzzat100% (1)
- T-Matrix™: Toip Control & Gateway ProductsDokument2 SeitenT-Matrix™: Toip Control & Gateway ProductsEmadElDinEzzatNoch keine Bewertungen
- LM - Build An ARM-based Embedded Web ServerDokument46 SeitenLM - Build An ARM-based Embedded Web ServerEmadElDinEzzatNoch keine Bewertungen
- Workshop Ethernet2 Flyer E 0Dokument2 SeitenWorkshop Ethernet2 Flyer E 0EmadElDinEzzatNoch keine Bewertungen
- IP IP IP 语音话机及网关对接 3CX 3CX 3CX 3CX 电话系统Dokument8 SeitenIP IP IP 语音话机及网关对接 3CX 3CX 3CX 3CX 电话系统EmadElDinEzzatNoch keine Bewertungen
- DNSDokument194 SeitenDNSEmadElDinEzzatNoch keine Bewertungen
- Secure ServicesDokument22 SeitenSecure ServicesEmadElDinEzzatNoch keine Bewertungen
- Red Hat Network Satellite-5.4-Proxy Installation Guide-En-USDokument42 SeitenRed Hat Network Satellite-5.4-Proxy Installation Guide-En-USEmadElDinEzzatNoch keine Bewertungen
- HD Voice Game ChangerDokument16 SeitenHD Voice Game ChangerEmadElDinEzzatNoch keine Bewertungen
- GSA Mobile HD VoiceDokument6 SeitenGSA Mobile HD VoiceEmadElDinEzzatNoch keine Bewertungen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Article WritingDokument10 SeitenArticle WritingmutabargaybullayevnaNoch keine Bewertungen
- Polevoque 3Dokument46 SeitenPolevoque 3api-657593213Noch keine Bewertungen
- Dwnload Full Practicing Statistics Guided Investigations For The Second Course 1st Edition Kuiper Solutions Manual PDFDokument36 SeitenDwnload Full Practicing Statistics Guided Investigations For The Second Course 1st Edition Kuiper Solutions Manual PDFdavidkrhmdavis100% (11)
- 1 Hot Metal Tapping SOPDokument25 Seiten1 Hot Metal Tapping SOPSANJAY KUMAR PATINoch keine Bewertungen
- Tucker ComplaintDokument48 SeitenTucker ComplaintMike MarinoNoch keine Bewertungen
- Dior Product Development PresentationDokument59 SeitenDior Product Development PresentationSade WycheNoch keine Bewertungen
- Short Questions From 'The World Is Too Much With Us' by WordsworthDokument2 SeitenShort Questions From 'The World Is Too Much With Us' by WordsworthTANBIR RAHAMANNoch keine Bewertungen
- BI410 Plant Developmental BiologyDokument41 SeitenBI410 Plant Developmental BiologyLaisla CagliariNoch keine Bewertungen
- Research Poster 1Dokument1 SeiteResearch Poster 1api-662489107Noch keine Bewertungen
- ArcSight Profiler IntegrationDokument8 SeitenArcSight Profiler IntegrationemveNoch keine Bewertungen
- Violin Teaching in The New Millennium or Remembering The Future of Violin Performance by Gwendolyn Masin For Trinity College 2012Dokument241 SeitenViolin Teaching in The New Millennium or Remembering The Future of Violin Performance by Gwendolyn Masin For Trinity College 2012Matheus Felipe Lessa Oliveira100% (4)
- Principle of ManagementsDokument77 SeitenPrinciple of ManagementsJayson LucenaNoch keine Bewertungen
- Baby Romper Pattern and Sewing Tutorial 2014Dokument18 SeitenBaby Romper Pattern and Sewing Tutorial 2014Carolina Ribeiro100% (1)
- Managerial Accounting 14th Edition Warren Solutions Manual DownloadDokument28 SeitenManagerial Accounting 14th Edition Warren Solutions Manual DownloadRose Speers100% (22)
- Suspension Mansons 2Dokument45 SeitenSuspension Mansons 2Andres Silva67% (3)
- Vince - Michael - Intermediate - Language Assive 1Dokument5 SeitenVince - Michael - Intermediate - Language Assive 1Николай КолевNoch keine Bewertungen
- Playing Djembe PDFDokument63 SeitenPlaying Djembe PDFpbanerjeeNoch keine Bewertungen
- Banana Oil LabDokument5 SeitenBanana Oil LabjbernayNoch keine Bewertungen
- A Descriptive-Comparative StudyDokument32 SeitenA Descriptive-Comparative StudyJanelle DionisioNoch keine Bewertungen
- Preface: How To Use This BookDokument1 SeitePreface: How To Use This BookCarlos SaavedraNoch keine Bewertungen
- Tiktok, Identity Struggles and Mental Health Issues: How Are The Youth of Today Coping?Dokument6 SeitenTiktok, Identity Struggles and Mental Health Issues: How Are The Youth of Today Coping?Trúc NgânNoch keine Bewertungen
- Studi Penanganan Hasil Tangkapan Purse Seine Di KM Bina Maju Kota Sibolga Study of Purse Seine Catches Handling in KM Bina Maju Sibolga CityDokument8 SeitenStudi Penanganan Hasil Tangkapan Purse Seine Di KM Bina Maju Kota Sibolga Study of Purse Seine Catches Handling in KM Bina Maju Sibolga CitySavira Tapi-TapiNoch keine Bewertungen
- New Action Plan Launched To Enhance Somali Women's Role in Somalia's Maritime SectorDokument5 SeitenNew Action Plan Launched To Enhance Somali Women's Role in Somalia's Maritime SectorUNSOM (The United Nations Assistance Mission in Somalia)Noch keine Bewertungen
- Comparative DegreeDokument25 SeitenComparative DegreeAgung PriyanaNoch keine Bewertungen
- Stoke Rehabilitation NICE GuidelinesDokument591 SeitenStoke Rehabilitation NICE GuidelinesHardeep Singh BaliNoch keine Bewertungen
- The 296 Proposed New (Baseline & Monitoring) Methodologies Sent To The Executive BoardDokument264 SeitenThe 296 Proposed New (Baseline & Monitoring) Methodologies Sent To The Executive Boarddjuneja86Noch keine Bewertungen
- Lampiran 18-Lesson Plan 02Dokument5 SeitenLampiran 18-Lesson Plan 02San Louphlii ThaNoch keine Bewertungen
- Form A HypothesisDokument2 SeitenForm A Hypothesismrshong5bNoch keine Bewertungen
- What Is Immediate Assignment in GSMDokument9 SeitenWhat Is Immediate Assignment in GSMLindux50% (2)
- 1167 Nine Planets in TamilDokument1 Seite1167 Nine Planets in TamilmanijaiNoch keine Bewertungen