Beruflich Dokumente
Kultur Dokumente
Internet of Things (IoT) Taxonomy of Security
Hochgeladen von
KISHORE CCopyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Internet of Things (IoT) Taxonomy of Security
Hochgeladen von
KISHORE CCopyright:
Verfügbare Formate
2016 3rd International Conference on Electronic Design (ICED), August 11-12, 2016, Phuket, Thailand
Internet of Things (IoT): Taxonomy of Security
Attacks
Mukrimah Nawir1,2,*, Amiza Amir1,2,#, Naimah Yaakob1,2, Ong Bi Lynn2,3
School of Computer and Communication Engineering, Universiti Malaysia Perlis (UniMAP), Perlis, Malaysia.
2
Embedded, Network, and Advance Computing (ENAC), UniMAP, Perlis, Malaysia.
*mukrimah1992@gmail.com
#amizaamir@unimap.edu.my
Abstract The Internet of Things (IoT) comprises a complex
network of smart devices, which frequently exchange data
through the Internet. Given the significant growth of IoT as a
new technological paradigm, which may involve safety-critical
operations and sensitive data to be put online, its security aspect
is vital. This paper studies the network security matters in the
smart home, health care and transportation domains. It is
possible that the interruption might occur in IoT devices during
operation causing them to be in the shutdown mode. Taxonomy
of security attacks within IoT networks is constructed to assist
IoT developers for better awareness of the risk of security flaws
so that better protections shall be incorporated.
Keywords Internet of Things (IoT); IoT Security; Security
Attacks;
I. INTRODUCTION
Internet of Things (IoT) paradigm was care, introduced by
Kevin Ashton in the year 1998 [1][2][3][4]. He states that IoT
is the computers that knew everything about things and
using data that they collected without any help from a human
then interconnected to each other with the internet. IoT refers
to the interconnectivity among our frequently used electronic
devices along with the sensing capability and contextual
awareness [1][5][6].Given the efficiency and economic
benefits of IoT technology, IoT devices are developed widely
and rapidly across the nation. IoT applications are popular
worldwide with the term smart such as smart home, smart
watch, and smart city.
China introduced the concept of Sensing China as an
initiative to accelerate the development of IoT across the
country [3][4]. IoT components usually consist of sensors and
actuators which collect contextual information and perform
actions respectively. For example in a smart watch, a sensor
records the time for exercises, and an actuator calculates the
calories during activities. Another component is a coordinator,
which acts as a device manager that monitors the status and
operations of the smart things. It also sends an accumulated
report of their activities to IoT service provider. Local IoT
network and IoT cloud service are connected through a sensor
bridge.
978-1-5090-2160-4/16/$31.00 2016 IEEE
Usually, IoT service presented on the cloud (the reliable)
to enable accessing IoT objects anytime or anywhere so that
fast actions can be performed to control all the IoT devices.
For example, people can use their smartphone to give
commands to their smart car. IoT has three characteristics
[7][8]. First, it is a comprehensive awareness to get the
information by using smart objects and network connectivity.
Second, it allows the reliable transmission to maintain the high
accuracy and real time of the system. Third, it must
incorporate intelligent processing to make the systems
function smartly.An example in Fig. 1 shows the scenario of
IoT on smart watch application. More than one objects
interlinked to each other, where the laptop linked to the
smartphone, and the smartphone linked to a heart rate monitor
and so on. The attacker can compromise the laptop and
eventually get access to the heart rate monitor.
By the year 2020, the billions number of Internetconnected and sensor-enabled devices was estimated [1][6].
The IoT concept results in the information free flow amongst
various devices within the Internet [2]. The rising number of
devices linked via the IoT led to the high possibility of digital
disruption, or chaos might occur. Considering the high volume
of data is now being put online. IoT is susceptible to various
security attacks by hackers or organized criminals
Fig. 1. The scenario of Internet of Things on Smartwatch application.
321
2016 3rd International Conference on Electronic Design (ICED), August 11-12, 2016, Phuket, Thailand
Moreover, this data can be sensitive data or may involve
safety-critical operations (e.g., car and medical devices).
Hence, security viewpoint is a part of the major concern in the
development of IoT. Therefore, this paper studies the
vulnerability of IoT network security. A better understanding
of the security matters is crucial as adversary attacks are the
major hindrance to the development of IoT.
In section II, this paper describes the key elements that
involve in IoT systems. Then, the relationship of all elements
involves in IoT that might arise the security issues in various
domains (smart home environment, healthcare domain, and
transportation domain) discussed in section III. Climate topic
of this paper presents in section IV about the taxonomy
security attacks and last but not least is the conclusion (section
V) of the studies.
II. THE IOT KEY ELEMENTS
The integration of smart devices (things) achieves the
well-functioning of IoT in various domains such as healthcare,
smart home, smart city, smart transportation. However, the
interconnection of things results in the unprecedented
security issues [4]. The IoT concept requires several key
elements in its operation. Four important IoT components are
persons, intelligent object, technological ecosystem and
process [19].
For example, in healthcare domain (as shown in Fig.2), the
doctor checks the patient (person) to retrieve patient healths
problem. Then, medical activities (process) are performed
through any communication system (technological ecosystem)
by using any medical tools (intelligent object) like a
stethoscope, X-ray machine, heart rate monitor. Failure to
address the security issues within this domain can be fatal
since it may result in an inaccurate diagnosis.
The development of IoT brings out pitfall toward the user
and also its devices if no security measures are taken on it.
Subsequently, the IoT needs for the safety requirements such
as identification/authentication, reliability, confidentiality, and
non-repudiation to ensure that the IoT is secure from any
attacks that might launch towards them. This paper discusses
the security issues within three domains: the smart home
environment, health-care and transportation domain.
III. SECURITY ISSUES IN VARIOUS DOMAINS UPON IOT CONCEPT
The security issues on IoT should be enforced to achieve
secure communication contexts at different domains to give
benefits and advantages of this IoT system for humans.
A. Smart Home Environment
According to World Economic Forum, 92.1% rely on
10% of humans wear clothes that connected to the internet
[20]. For instance, people can speak or give any command
toward the devices (microphone) to ask any home appliances
(light, fan, etc.) to operate. IoT in a smart home environment
works by only allowing the authorized users to monitor all the
IoT devices in the home. For security purpose, three criteria
need to be valued: the confidentiality, auto-immunity, and
reliability, to protect the house against theft and intrusion.
Password of IoT devices should be confidential.IoT system
needs to have auto-immunity to predict or alert any abnormal
activities that occur (launched attacks to the device). The
auto-immunity enables the house to be protected by alarming
sound to alert the presence of an intrusion.
B. Healthcare Domain
The IoT concept in healthcare domain involves tracking,
authentication, automatic data collection and sensing [16]. For
example, the progress report of patients medical condition is
confidential, and this requires security mechanism to prevent
the data expose to an unauthorized party. By doing so, no one
can monitor and alter the information or give a false patients
medical report as well as to prevent a doctor from doing the
mistake to treat their patient. If no security mechanism was
adopted, this might cause the doctor to prescribe wrong
medicines or give bad treatments to their patient. For instance,
changes to a blood test result may worsen the patients
condition due to accepting a mismatched blood during
transferring blood process.
C. Transportation Domain
A new revolution in the passenger experiences is brought
by the investment of IoT. Apples iBeacon are used to enable
the entire operation can corporate each other to easier the
passengers life [6]. For example, Virgin Atlantic applies
iBeacons at Heathrow airport and American Airlines deploys
iBeacons at Dallas-Fort Worth (DFW) International Airport
[6]. Nowadays, most airlines allow passengers to use their
mobile phone to self-check-in for fast and smooth check-in
operation
The airlines need to secure passengers information to
ensure their customer feel safer and comfortable with all
operation involving IoT. Therefore, security mechanism of
IoT system should be confidential and kept from unauthorized
users. Usually, one passenger has one tag to make them
identifiable where to involve only the interaction between
providers and products [19]. It is essential for baggage and
claim later on. The sensor that identifiable needs to be
protected from attackers by using the method of block tag
introduced by Juels [4].
Fig. 2. IoT key elements in healthcare domain.
322
2016 3rd International Conference on Electronic Design (ICED), August 11-12, 2016, Phuket, Thailand
IV. TAXONOMY OF ATTACKS ON IOT
Without enumerated of security in IoT, attacks will
outweigh any of their intended benefits. There are several types
of attacks on IoT such as Spoofing/Altering/Replay Routing
attack, Denial of Service (DoS) attack, Sybil attack, and node
capture attack in IoT. TABLE I explain a comparative analysis
of different attacks on their target, weaknesses, and technique
of the security attacks.
TABLE I.
COMPARATIVE ANALYSIS OF ATTACKS WITHIN IOT
Attack
Target
Weaknesses
Denial of
Service (DoS)
attacks
IoT devices
that
connected
via the
Internet.
Reduction in
networks
capacity
Disable the
network
Wormholes
Location of
the packets
Problematic
in checking
the routing
information
Spoofed, alter
or replayed
routing
information
Routing
information
Detectable
of IoT
devices.
High end to
end latency
Routes
sources might
be extended
or shorten
Sybil
Integrity of
data
security and
resource
utilization
Launch
threat to
geographic
routing
protocol
Costly
network
Technique
IP enable status
contributes to a
pool thing.
Distributed
attack utilized
and auto shut the
IoT system.
Record the
packets at one
location then
tunnel it to a
different
location.
First, spoofer
only listens.
Only act when
the transmitter
stops sending a
signal, then
unreliable signal
send.
Propagate
malware to a
website. The
adversary is
masquerading
the normal users.
A. Spoofed, Alter, Replay Routing Information
The mutual direct attack is spoofing, altering and replay
routing that target on routing information where data exchange
between nodes occurs. During spoofing attacks the security
issue of the IoT devices detectability in the systems problem.
The attacks are created by generating a false error message,
creating a routing loop and many more techniques [17]. In the
beginning, spoofer does not transmit a signal, but they only
listen to the appropriate transmitter. When the legitimate
transmitter stops sending a signal to the legitimate receiver,
spoofer starts sending the unreliable signal [9].
As an example, an attacker pollutes the whole network by
sending fake routing information stating for instance that I
am the base station (dark square spot). On Facebook, a user is
asked to like something before she/he is allowed to access
the Internet and then be directed to a fake Facebook login page
was stolen. As the user login, this fake page would record
users credential, show a login error and then redirect the user
to the real Facebook page. This example shows how users
information stolen.
B. Sybil Attack
The emerging of IoT exposes a system to Sybil attack,
which is a single node that has multiple identities [17]. That
means adversary can be in more than one location at a time. It
is to degrade the integrity of data security and resource
utilization. In the year 2012, the statistics records of Sybil
attack in the online social network (OSNs), about 76 million
(72%) fake users on Facebook and 20 million Sybil on Twitter
per week [10].
Sybil attacks are launched to steal the information by
propagating malware to a website. Comprehensively, Sybil is
like a masquerade, which looks like ordinary users but it is
not. New media like Facebook, Twitter, and Instagram, are
prone Sybil attacks. Therefore, it is important to have a
security defense to maintain the IoT system so that it can keep
working correctly.
C. Denial of Service (DoS)
Blackmailer or activist endeavors to mess up or terminate
the network by launching the Denial of Service attack. DoS
attack is a particular attack on a network or a computational
resource, and the effect of DoS attack may contribute to the
reduction in network capacity.
There are two categories of DoS attack in IoT; Distributed
Denial Of Service (DDoS) and Ordinary DoS [11][12]. For
common DoS attack, a tool is required to send packets to an
intended system that crash the network or sometimes force the
system to restart. Meanwhile, DDoS can be a single attacker
but not powerful as a proxy attacker. From that, the impact of
this attack not only disabled the network but also prevent it to
be accessible to a very large network.
D. Attacks based on Device Property
Device property can be low-end devices class or high-end
devices class. These types of attacks give a different impact
toward the IoT system. IoT might result in a fatal error or only
a part of the system might act in abnormal behavior due to the
power of device property.
1) Low-end device class attack
Low-end devices class attack is an attack that involves
low power devices to attack the IoT system. By that, this class
is low cost by only connecting the system to outside via radio
link. They are same potential and network configuration that
act in a similar way. It is accessible to few sensor nodes of IoT
devices. For an example, the smartwatch can control remotely
any devices in home appliances like smart TV, and smart
refrigerator.
2) High-end device class attacks
Unlikely to the low-end device, high-end device class
attacks involves full-fledged devices to launch the attacks on
IoT system. This class connects their IoT devices via the
Internet so it can be accessed by a laptop (powerful device)
that has better CPU from anywhere and anytime.
323
2016 3rd International Conference on Electronic Design (ICED), August 11-12, 2016, Phuket, Thailand
E. Attacks based on Access Level
Based on the access level, there are two ways for attackers
to access the IoT system: passive and active. Access level
attacks affect the availability of the IoT systems.
1) Passive attacks
Passive attacks involve monitoring and eavesdropping
where they do not consent or do not know anything about the
user and do not disturb the communication in IoT [5][12][13].
They only learn or make use the information from the system.
For instance, Felix sends messages to Anne can be read the
contents by Darren. So Darren is called a passive attacker.
2) Active attacks
On contrary to passive attacks, active attacks try to
evade or break the protection feature of the information or
data by connecting to the district and messing up the
networking communication [5][12][14][15]. When Darren
reply the message to Anne, not Felix who suppose doing it.
Darren becomes an active attack.
F. Attacks based on Adversary Location
An adversary can be launched at anywhere to attacks the
IoT system. Insider or outsider attackers are attacks based on
adversary location.
1) Internal attacks
An internal attack is an attack that is started by a
component inside the security IoT border (Insider). In order
to launch the attack, the attacker tries to execute own
malicious code toward IoT devices. Insider divided into four
types of insider attacks; compromised actors, unintentional
actors, emotional attackers and technology perception actors
[21].
2) External attacks
Adversary located out of range the IoTs network
(public) yet still can access the IoT devices by remotely
known as external attackers. They do not know anything about
the IoT architecture that they are trying to access. Usually, a
try and error process is used to make it possible successful
access in the right IoT native network.
G. Attacks based on Attacks Strategy
To launch the attack, the attacker tries to execute own
malicious code toward IoT devices. Attackers have a strategy
to launch and destroy the IoT development. There are two
viewpoints of strategy attacks: physical or logical.
H. Attacks based on Information Damage Level
All IoT devices consist of sensors that monitor the
variability of parameters. Information that floating or
openness of the information easily modify by attackers. A set
of information damage level divided into six categories.
1) Interruption
Interruption attacks mainly intention the availability of
the system. By that, the resource exhaustion is one of the
results when an interrupt occurs. While the IoT operate it is
possible to interruption occurs in IoT device into shut down
mode.
2) Eavesdropping
An adversary blocks the receiver device from picking
transmitted packet when it eavesdrops the communication
channel. RFID devices have tendencies to be attacked through
eavesdropping. Confidentiality of IoT systems drops when
there is an eavesdropping in IoT devices.
3) Alteration
Information in IoT devices being altered or modified by
attackers threats the integrity of security requirements for IoT
system to well-functioning as its design. The reason for
attackers to do this unmannerly is to mislead the
communication protocol.
4) Fabrication
Fabrication threatens authentication of IoT system due
to attackers insert the imitation data in normal architecture of
IoT. By flooding the network of IoT system the fabrication
damage the information level of IoT device.
5) Message Replay
Allow interception and resend the original message and
modified it to compromise the target IoT devices. Likely in
Ethereal able seizure traffic that posted to a Web Service [12].
Attackers hold the current conversation or session to be
replayed soon. At a later time, a replayed message will
confuse the IoT recipient device and from that cause a
dangerous toward the IoT system.
6) Man-in-the-middle
Attackers secretly relay and possibly alter the
communication between two parties who believe they are
directly communicating with each other. As in Fig. 3 when
X want to communicate to Y but attacker want to steal
some information in Y, attacker place two others node in
between (X that near to Y and Y near to X) [12][13].
1) Physical attacks
One strategy to blunt the IoT devices successful is by
the physical attack on the infrastructure of an IoT. For
example, adversary changes the behavior or structure of
devices that involve in IoT system.
2) Logical attacks
A logical attack is an attack when the communication
channel dysfunction after the adversary launched attacks on
the IoT system. Attackers do not harm the physical devices to
launch their attack.
Fig. 3. Man in the middle attacks.
324
2016 3rd International Conference on Electronic Design (ICED), August 11-12, 2016, Phuket, Thailand
Once X have done sending information to Y, Y
does not know the present of attacker they think the
information purely true from X. Let say, in the theft of
sensitive information call scenario between two peoples
(Bankers and Customer). In between of their conversation on
the phone another device allocated by the attacker so attackers
can know security information (bank password) of that
customer and steals their money in the bank.
K. Communication Protocol Stack attacks
The layer-based attack and the attempt by an adversary to
attack through communication protocol stack is shown in
TABLE II below. There are five levels involve, where the
attacker tries to compromise the objects of IoT.
TABLE II.
Layer
Physical
I. Host-based attacks
The types of host involve in launch upon security attacks
of IoT are users, software, and hardware compromise. IoT
devices are embedded devices where they consist of operating
system and system software inside them. Therefore, the IoT
devices can be attacks through the host of the IoT system.
Attacks
Jamming
Tampering
Collision
Data Link
1) User-compromise
A user may reveal the information or data such as
password or keys about the security credentials. For example,
a building insider gives a password of that building to be
accessible the IoT devices by an unauthorized user.
Exhaustion
Unfairness
Spoofed, altered or
replayed
routing
information
Selective
forwarding
2) Software-compromise
Software vulnerability where the attacker pushes the
IoT device to be in exhaustion state or resources buffer
overflows. For example, the laptop can be suddenly shutting
down due to the low battery. By that, other things cannot be
interoperability due to most of the system in sleeping mode.
Sinkhole
Network
Sybil
Wormholes
HELLO flood
3) Hardware-compromise
Within an IoT device, tampering with hardware is the
way adversary launch their host-based attacks. The host-based
attack on hardware compromise, where attackers inject
malicious code or stealing the actual driver or connecting to a
device. Moreover, an iPhone may be exploited by using a
malicious duplicate charger which installs a Trojan into that
device [18].
Acknowledgement
spoofing
Flooding
Transport
De-synchronization
Attacks
on
reliability and Clone
attack:
J. Protocol based attacks
There are two standpoints the adversaries might
compromise the protocol of IoT systems which can threat
security mechanism on the availability of IoT. Either by
deviation or disruption from the intentional protocol, the
attackers become selfish where doing some modification
toward the real information.
1) Deviation from protocol
An attacker does not follow the protocol in a normal
way. The tendency of outsider behaves normally as an insider
and doing malicious code on IoT system. The deviations from
protocol can possible attacks on two protocols. They are
application and networking protocol.
LAYER BASED ATTACKS WITH THEIR ATTACKS STRATEGIES
IN IOT SYSTEMS
Application
Clock
skewing,
Selective message
forwarding,
Data
aggregation
distortion
Methods/ Strategies attacks
Creates radio interference and
exhaustion on IoT devices.
Creates compromised nodes.
Simultaneously transmit two
nodes of the same frequency.
By repetitive collision the nodes.
Using above link layer attacks
Creates routing loops, extend or
shortening
sources
routes,
attracting or repelling network
from select nodes.
Choose what information that
gathered before transmit it.
Monitoring,
Redundancy,
Authentication
Single node duplicates its node to
be in multiple locations.
Selectively
tunneling
or
retransmit information to the IoT
devices.
Uses HELLO packets as weapon
to launch the attack on IoT
system
Spoof
the
link
layer
acknowledgments for overhead
packets.
Repeat the request of a new
connection until the IoT system
reach maximum level.
Disruption of an existing
connection.
The
adversaries
usually
masquerade like normal behavior
in IoT system. Attackers also can
still choose a message that he/she
intend in the IoT system and
launched their own malicious
activities.
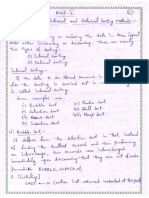
Fig.4 shows a taxonomy of security attacks on IoT by
hoping to help the researchers clearer and easier to understand
the insight of various types of security attack and summarizes
all the above discussion. There are eight categories can be
classified for attackers to attack the IoT system.
2) Protocol disruption
In the security of IoT context, the availability is one of
security attribute. This functional security requirement is
important to have a great IoT system. Unfortunately, attackers
can attack the protocol by disrupt either from inside or outside
the native network of IoT and bring up the issues on the
availability of IoT.
325
2016 3rd International Conference on Electronic Design (ICED), August 11-12, 2016, Phuket, Thailand
Fig. 4. Taxonomy of Security Attacks on IoT.
V. CONCLUSION
Considering a significant amount of sensitive data to be
put online and the enabling of remote access of smart devices
across the world, security flaws within Internet of Things may
bring a huge drawback to the entire world. Such security
failures may disrupt the whole network of devices and may
cause fatal effects to the users. Therefore, security concern is a
major part that needs to be well studied before developing
more advanced Internet of Things (IoT) systems. In this paper,
we attempt to outline various attacks within IoT systems into a
well-structured taxonomy to assist researchers and developers
to plan appropriate security measures in their IoT
developments.
ACKNOWLEDGMENT
The research reported in this paper is supported by
Research Acculturation Grant Scheme (RAGS). The authors
would also like to express gratitude to the Malaysian Ministry
of Education (MOE) and University Malaysia Perlis for the
facilities provided.
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
REFERENCES
[1]
[2]
[3]
[4]
[5]
[6]
E..Y., Cybersecurity and The Internet of Things,EY. global, UK,
2015.
T.Borgohain, U.Kumar, and S.Sanyal, Survey of Security and Privacy
Issues of Things, arXiv preprint arXiv:1501.02211, 2015.
H. Zhou, The Internet of Things in the Cloud, in A Middleware
Perspective:CRC Press, 2012.
S. Li, L. Da Xu, and S. Zhao, The Internet of Things: A Survey, in
[Information Systems Frontiers], [Springer]. doi: [10.1007/s10796014-9492-7], New York, 2014, pp.243-299.
M. Mahmud Hossain, M.Fotouhi, and R. Hasan, Towards an Analysis
of Security Issues, Challenges and Open Problems in the Internet of
Things, in Services (SERVICES), 2015 IEEE World Congress on.
IEEE, 2015, pp.21-28.
S.Singh and N.Singh, Internet of Things (IoT):Security Challenges,
Business Opportunities & Reference Architecture for E-Commerce, in
Green Computing and Internet of Things (GCIoT), 2015 International
Conference on. IEEE, 2015, pp.1577-1581.
[17]
[18]
[19]
[20]
[21]
326
Q. Gou, L. Yan, Y. Liu, and Y. Li, Construction and Strategies in IoT
Security System, in Green Computing and Communications
(GreenCom), 2013 IEEE and Internet of Things (iThings/CPSCom),
IEEE International Conference on and IEEE Cyber, Physical and Social
Computing. IEEE, 2013, pp. 11291132.
Y. W. and X. Zhang, Internet of Things,in [International Workshop,
IoT], [Springer] 2012,Changsha, China, August 2011.
M. Harun Yilmaz and H. Arslan, A Survey: Spoofing Attacks in
Physical Layer Security, in 40th Annual IEEE Conference on Local
Comp. Networks, IEEE, pp. 812817, 2015.
K. Zhang, X. Liang, R. Lu, and X. Shen, Sybil attacks and their
defenses in the internet of things, IEEE Internet Things J., vol. 1, no. 5,
pp. 372383, 2014.
E. Alsaadi and A. Tubaishat, Internet of Things: Features , Challenges ,
and, vol. 4, no. 1, pp. 113, 2015.
Belapurkar, A. (2009). Distributed systems security: Issues, processes,
and solutions. Chichester, UK: John Wiley & Sons
S. Alam and D. De, Analysis of Security Threats in Wireless Sensor
Network, vol. 6, no. 2, pp. 3546, 2014.
I. Grand, E. Nancy, and T. Nancy, A Taxonomy of Attacks in RPLbased Internet of Things, vol. 18, no. 3, pp. 459473, 2016.
U. Sabeel and N. Chandra, Categorized Security Threats in the
Wireless Sensor Networks: Countermeasures and Security Management
Schemes, vol. 64, no. 16, pp. 1928, 2013.
L. Atzori, A. Iera, and G. Morabito, The Internet of Things: A
Survey, Comput. Networks, vol. 54, no. 15, pp. 27872805, 2010.
D. Nandal and V. Nandal, Security Threats in Wireless Sensor
Networks, vol. 11, no. 01, pp. 5963, 2011.
R. Billure, V. M. Tayur, and V. Mahesh, A Study on the Security
Challenges, pp. 247252, 2015.
A. Riahi, Y. Challal, E. Natalizio, Z. Chtourou, and A. Bouabdallah, A
Systemic Approach for IoT Security, in Distributed Computing in
Sensor Systems (DCOSS), 2013 IEEE International Conference on.
IEEE, 2013, pp. 351355
G.Press (2013, Feb), Internet of Things (IoT) Predictions | Whats The
Big
Data?
on
WordPress.com.
[Online].
Available:
http://whatsthebigdata.com/2016/02/13/internet-of-things-iotpredictions/. [Accessed: 23-Feb-2016].
I.Infosec (2015, June), Insider vs. Outsider Threats: Identify and Prevent
[Online]. Available: http://resources.infosecinstitute.com/insider-vsoutsider-threats-identify-and-prevent/.[Accessed: 13-June-2016].
Das könnte Ihnen auch gefallen
- Safeguarding the Digital Fortress: A Guide to Cyber Security: The IT CollectionVon EverandSafeguarding the Digital Fortress: A Guide to Cyber Security: The IT CollectionNoch keine Bewertungen
- Internet of Things Security, Device Authentication and Access Control A ReviewDokument11 SeitenInternet of Things Security, Device Authentication and Access Control A Reviewfalconinayat0% (1)
- Internet of Things (IoT) Security Current Status Challenges and Prospective MeasuresDokument6 SeitenInternet of Things (IoT) Security Current Status Challenges and Prospective MeasureslakshmisudarshanNoch keine Bewertungen
- IoT ConceptDokument7 SeitenIoT ConceptPedro Alexis Santos HernadezNoch keine Bewertungen
- Smart City Framework — GCC A Clear and Concise ReferenceVon EverandSmart City Framework — GCC A Clear and Concise ReferenceNoch keine Bewertungen
- IoT Device Management The Ultimate Step-By-Step GuideVon EverandIoT Device Management The Ultimate Step-By-Step GuideNoch keine Bewertungen
- Cyber SecurityDokument59 SeitenCyber Securityiulia_balteanuNoch keine Bewertungen
- Internet of Things (IoT) Cybersecurity Improvement Act of 2019Dokument9 SeitenInternet of Things (IoT) Cybersecurity Improvement Act of 2019MarkWarner100% (11)
- Security in IoT Social NetworksVon EverandSecurity in IoT Social NetworksFadi Al-TurjmanNoch keine Bewertungen
- Security Issues & Threats in IoT InfrastructureDokument5 SeitenSecurity Issues & Threats in IoT InfrastructureIjaems JournalNoch keine Bewertungen
- A Study of Cybercrimes in India Using Digital ForensicsDokument15 SeitenA Study of Cybercrimes in India Using Digital ForensicsIJRASETPublicationsNoch keine Bewertungen
- Iot & Web TechnologyDokument36 SeitenIot & Web TechnologyrenukaNoch keine Bewertungen
- Cloud Security With Virtualized Defense andDokument6 SeitenCloud Security With Virtualized Defense andmbamiahNoch keine Bewertungen
- The Internet of Things and Wearable Technology: Addressing Privacy and Security Concerns Without Derailing InnovationDokument93 SeitenThe Internet of Things and Wearable Technology: Addressing Privacy and Security Concerns Without Derailing InnovationMercatus Center at George Mason UniversityNoch keine Bewertungen
- POV-Internet of Things Nirmal Nag: Design Authority, SAP Enterprise ApplicationDokument20 SeitenPOV-Internet of Things Nirmal Nag: Design Authority, SAP Enterprise ApplicationNirmal NagNoch keine Bewertungen
- Securing The Internet of Things IoTDokument23 SeitenSecuring The Internet of Things IoTMoustafa NajmNoch keine Bewertungen
- Research Paper - A Synopsis On Cyber Terrorism and Warfare by Shreedeep RayamajhiDokument27 SeitenResearch Paper - A Synopsis On Cyber Terrorism and Warfare by Shreedeep RayamajhiShreedeepRayamajhi100% (5)
- Cyber Security BibliographyDokument6 SeitenCyber Security BibliographyhkingsmaNoch keine Bewertungen
- Definition of Ambient IntelligenceDokument3 SeitenDefinition of Ambient IntelligenceRaji MN100% (1)
- Draft TIC 3.0 Vol. 5 Service Provider Overlay HandbookDokument10 SeitenDraft TIC 3.0 Vol. 5 Service Provider Overlay HandbookJulio Cesar BalderramaNoch keine Bewertungen
- Cyber Security Challenges For India: An Assessment of Its PreparednessDokument17 SeitenCyber Security Challenges For India: An Assessment of Its PreparednessKanika SharmaNoch keine Bewertungen
- CIS Controls IoT Companion GuideDokument67 SeitenCIS Controls IoT Companion GuideRahmat PurwokoNoch keine Bewertungen
- Hands On Artificial Intelligence For IoT Prefinal1 PDFDokument48 SeitenHands On Artificial Intelligence For IoT Prefinal1 PDFaaaaNoch keine Bewertungen
- Smart Cards and Their Operating SystemsDokument15 SeitenSmart Cards and Their Operating SystemsheshokikiNoch keine Bewertungen
- BlockchainTechnologyandItsApplicationsinBusiness 13F3Y1 by AntefDokument17 SeitenBlockchainTechnologyandItsApplicationsinBusiness 13F3Y1 by AntefAntef IdrisiNoch keine Bewertungen
- Program: B.Tech CSE, 8 Semester, 4 Year CS801:Internet of Things Unit - 1 Introduction of IOT SensorsDokument23 SeitenProgram: B.Tech CSE, 8 Semester, 4 Year CS801:Internet of Things Unit - 1 Introduction of IOT SensorsjayaNoch keine Bewertungen
- Vietnam and Global AI Market AnalysisDokument41 SeitenVietnam and Global AI Market AnalysisBảo Khanh100% (1)
- Content: Ambient IntelligenceDokument20 SeitenContent: Ambient Intelligencekrupashree100% (1)
- 15STM Blockchain-101Dokument15 Seiten15STM Blockchain-101Raghu VamsiNoch keine Bewertungen
- A Security Business Case For Common CriteriaDokument34 SeitenA Security Business Case For Common CriteriaAbdul RasheedNoch keine Bewertungen
- Technical Seminar On The Topic: R R ST Tut yDokument24 SeitenTechnical Seminar On The Topic: R R ST Tut yNitin RanjanNoch keine Bewertungen
- Artificial Intelligence Approaches For IoT Security: State of ArtDokument12 SeitenArtificial Intelligence Approaches For IoT Security: State of ArtIJAERS JOURNALNoch keine Bewertungen
- Securing Data in Iot Using Cryptography and SteganographyDokument8 SeitenSecuring Data in Iot Using Cryptography and Steganographymuneeb rahmanNoch keine Bewertungen
- Current Trends in ComputingDokument5 SeitenCurrent Trends in ComputingInfanta joneNoch keine Bewertungen
- Digital Assignment 1Dokument4 SeitenDigital Assignment 1Raj KamalNoch keine Bewertungen
- Internet of ThingsDokument8 SeitenInternet of ThingsZain FareedNoch keine Bewertungen
- Internet of ThingsDokument25 SeitenInternet of ThingsPRATIK MANUSMARENoch keine Bewertungen
- A Study On Review and Analysis of Cloud, Fog and Edge Computing PlatformsDokument7 SeitenA Study On Review and Analysis of Cloud, Fog and Edge Computing PlatformsInternational Journal of Innovative Science and Research TechnologyNoch keine Bewertungen
- IOT Networks and ProtocolsDokument27 SeitenIOT Networks and Protocolsfaisul faryNoch keine Bewertungen
- Security and Privacy in Big DataDokument2 SeitenSecurity and Privacy in Big DataInternational Journal of Innovative Science and Research TechnologyNoch keine Bewertungen
- The Challenges of Cyber CrimeDokument16 SeitenThe Challenges of Cyber CrimespreeasNoch keine Bewertungen
- Iso/Iec JTC 1: Internet of ThingsDokument17 SeitenIso/Iec JTC 1: Internet of ThingsChristen CastilloNoch keine Bewertungen
- SM Presentation On HTCDokument33 SeitenSM Presentation On HTCSohaib Anjum50% (2)
- Blockchain For Cybersecurity A Comprehensive SurveyDokument6 SeitenBlockchain For Cybersecurity A Comprehensive Surveyczeb100% (1)
- IOT Smart Cities Seminar IIDokument12 SeitenIOT Smart Cities Seminar IISumeet ChikkmatNoch keine Bewertungen
- Mis Cha2 Tele - 1399 10 22 7 37Dokument49 SeitenMis Cha2 Tele - 1399 10 22 7 37Ērmias Álemayehu100% (1)
- Artificial Intelligence in Information and Cyber SecurityDokument8 SeitenArtificial Intelligence in Information and Cyber SecurityMini MNoch keine Bewertungen
- Design and Implementation of Mobile Wallet Wtih Merchant PayDokument9 SeitenDesign and Implementation of Mobile Wallet Wtih Merchant Payfavour gabrielNoch keine Bewertungen
- SMART CITY, Technical Seminar: PPT, by Hoysal ShettyDokument17 SeitenSMART CITY, Technical Seminar: PPT, by Hoysal Shettyhoysal4s4kadmat0% (1)
- Enhancing Suricata For Cyber Security SCADA NetworksDokument5 SeitenEnhancing Suricata For Cyber Security SCADA NetworksEagle EyeNoch keine Bewertungen
- Internet of ThingsDokument7 SeitenInternet of ThingsRizwan Ahmed100% (1)
- Internet of Things For Smart CitiesDokument11 SeitenInternet of Things For Smart Citiesloory21100% (1)
- Blockchain For The Cybersecurity of Smart CityDokument66 SeitenBlockchain For The Cybersecurity of Smart CityGiovanni PintoNoch keine Bewertungen
- Cyber 027Dokument58 SeitenCyber 027Jesus BaetaNoch keine Bewertungen
- Information Security Project ReportDokument3 SeitenInformation Security Project ReportKhālid ḤussainNoch keine Bewertungen
- Spectrum Spats: There Is Simply Not Enough Spectrum To Go RoundDokument21 SeitenSpectrum Spats: There Is Simply Not Enough Spectrum To Go RoundKaran KadabaNoch keine Bewertungen
- Top 5 Examples of Smart City IoT SolutionsDokument15 SeitenTop 5 Examples of Smart City IoT SolutionsAkshatha PrabhuNoch keine Bewertungen
- Blockchain: Seminar ReportDokument30 SeitenBlockchain: Seminar ReportRishabh KumarNoch keine Bewertungen
- Cyber Terrorism (Seminar Part1)Dokument16 SeitenCyber Terrorism (Seminar Part1)itdep_gpcet7225100% (2)
- Data Structures ManualDokument98 SeitenData Structures ManualKISHORE CNoch keine Bewertungen
- WEb ProgrammingDokument1 SeiteWEb ProgrammingKISHORE CNoch keine Bewertungen
- Data StructuresDokument49 SeitenData StructuresKISHORE CNoch keine Bewertungen
- Apsrtc Ticket PDFDokument1 SeiteApsrtc Ticket PDFKISHORE C50% (4)
- Apsrtc Ticket PDFDokument1 SeiteApsrtc Ticket PDFKISHORE C50% (4)
- Geo-Spatial Location Spoofing Detection For Internet of ThingsDokument8 SeitenGeo-Spatial Location Spoofing Detection For Internet of ThingsKISHORE CNoch keine Bewertungen
- Edit Print Train TicketDokument2 SeitenEdit Print Train TicketTharun Vallabhu61% (151)
- CEHv8 Module 20 Penetration Testing PDFDokument104 SeitenCEHv8 Module 20 Penetration Testing PDFMehrdad100% (1)
- Ankit Fadia Workshop - CollegesDokument6 SeitenAnkit Fadia Workshop - CollegesHarshit KhandelwalNoch keine Bewertungen
- CST Web Application Testing Report PDFDokument33 SeitenCST Web Application Testing Report PDFKenedy GebremeskelNoch keine Bewertungen
- Vircom ModusCloud - Features Benefits GuideDokument15 SeitenVircom ModusCloud - Features Benefits GuideA JosephNoch keine Bewertungen
- CL CyberAware AE Sk2of2Dokument38 SeitenCL CyberAware AE Sk2of2ultigodlinkNoch keine Bewertungen
- HdfcLogs 20 June 23Dokument50 SeitenHdfcLogs 20 June 23Kavita SinghNoch keine Bewertungen
- Platform-Spec-8 - Chapter 3. SecurityDokument18 SeitenPlatform-Spec-8 - Chapter 3. SecurityCiprian Nicu RosuNoch keine Bewertungen
- HTTP TunnelDokument6 SeitenHTTP TunnelDarkWolf_TrueNoch keine Bewertungen
- (EV 2.1e) Apsys Asset InventoryDokument6 Seiten(EV 2.1e) Apsys Asset Inventorysohaib siddiqueNoch keine Bewertungen
- Checkpoint Interview Questions With Answer Part 4Dokument6 SeitenCheckpoint Interview Questions With Answer Part 4Files DownNoch keine Bewertungen
- 8.4.1.3 Lab - Configure Site-To-Site VPN Using CLIDokument16 Seiten8.4.1.3 Lab - Configure Site-To-Site VPN Using CLIngangaNoch keine Bewertungen
- Smart Homes Automation System Using Cloud Computing Based Enhancement SecurityDokument6 SeitenSmart Homes Automation System Using Cloud Computing Based Enhancement SecurityN AbderrahimNoch keine Bewertungen
- NIS2 Versus ISO27001 - 2022 Versus CIS v8Dokument5 SeitenNIS2 Versus ISO27001 - 2022 Versus CIS v8Vagabond PakistanNoch keine Bewertungen
- Cryptography: Matrices and Encryption: By: Joseph Pugliano and Brandon SehestedtDokument5 SeitenCryptography: Matrices and Encryption: By: Joseph Pugliano and Brandon SehestedtSathya NatarajanNoch keine Bewertungen
- Online Safety, Security, Ethics and NetiquetteDokument42 SeitenOnline Safety, Security, Ethics and NetiquetteBobbyMusicoDaitNoch keine Bewertungen
- Cybersecurity RoadmapDokument1 SeiteCybersecurity RoadmapislamelshahatNoch keine Bewertungen
- Monitor 14 0ctDokument3 SeitenMonitor 14 0ctabhaymvyas1144Noch keine Bewertungen
- Manual ArmitageDokument21 SeitenManual ArmitageD'grit Tokan TrickNoch keine Bewertungen
- 4 1 T4-DesDokument2 Seiten4 1 T4-DesJason ChristianNoch keine Bewertungen
- Top 10 Internet Safety RulesDokument4 SeitenTop 10 Internet Safety RulesEmma Dacutanan-UriarteNoch keine Bewertungen
- Licensing Team (Ingram)Dokument3 SeitenLicensing Team (Ingram)ali razaNoch keine Bewertungen
- Openssl CommandsDokument6 SeitenOpenssl CommandsKumar NavNoch keine Bewertungen
- Cayf12e - Testbank - 09 - SecurityDokument17 SeitenCayf12e - Testbank - 09 - Securityyosef mohamedNoch keine Bewertungen
- IPS Report Uni-2020-07-21-0900 - 3717Dokument12 SeitenIPS Report Uni-2020-07-21-0900 - 3717zeroxiclanNoch keine Bewertungen
- 2019-06-27 Item 3 - Case Study - How To Respond To A Cyber-AttackDokument22 Seiten2019-06-27 Item 3 - Case Study - How To Respond To A Cyber-AttackSumaiyaNoch keine Bewertungen
- Container Security Best Practices Cheat SheetDokument9 SeitenContainer Security Best Practices Cheat SheetmcskumarNoch keine Bewertungen
- 2023+CC+Domain+2+Study+Guide+by+ThorTeaches Com+v1 1Dokument17 Seiten2023+CC+Domain+2+Study+Guide+by+ThorTeaches Com+v1 1Palanivel KNoch keine Bewertungen
- Yn38 S6fu Yvkh A29x 7t2c 6svp v3fd z6wrDokument4 SeitenYn38 S6fu Yvkh A29x 7t2c 6svp v3fd z6wrwidya casNoch keine Bewertungen
- Threats of Computer System and Its Prevention: August 2017Dokument5 SeitenThreats of Computer System and Its Prevention: August 2017Namrata PaudelNoch keine Bewertungen
- SMU615-tech 758407 ENdDokument274 SeitenSMU615-tech 758407 ENdGustavo CasabonaNoch keine Bewertungen