Beruflich Dokumente
Kultur Dokumente
Network Secuirty Seminar Topics
Hochgeladen von
Levale Xr0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
5 Ansichten1 Seitenetwork Secuirty seminar topics...
Copyright
© © All Rights Reserved
Verfügbare Formate
PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldennetwork Secuirty seminar topics...
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
5 Ansichten1 SeiteNetwork Secuirty Seminar Topics
Hochgeladen von
Levale Xrnetwork Secuirty seminar topics...
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 1
Introduction
What is Network Security
System Architecture
Basic Network Security & Security Vulnerabilities
Attacks on Different Layers
Authentication
Security on Different Layers
Network Attack Models
Authentication
Advantages
Problems
DoS and D-DoS
Firewall
Intrusion Detection Systems
Security Management
Conclusion
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Tata Motors Limited (Formerly TELCO, Short For Tata Engineering and Locomotive Company) Is An IndianDokument2 SeitenTata Motors Limited (Formerly TELCO, Short For Tata Engineering and Locomotive Company) Is An IndianLevale XrNoch keine Bewertungen
- Ogundokun 2021 J. Phys. Conf. Ser. 1767 012032Dokument15 SeitenOgundokun 2021 J. Phys. Conf. Ser. 1767 012032Levale XrNoch keine Bewertungen
- Chapter 1Dokument57 SeitenChapter 1Levale XrNoch keine Bewertungen
- Hafsa 131003112307 Phpapp02 PDFDokument47 SeitenHafsa 131003112307 Phpapp02 PDFLevale XrNoch keine Bewertungen
- Industry ProfileDokument2 SeitenIndustry ProfileLevale XrNoch keine Bewertungen
- Litz Quality Improvement Meeting: Levale XavierDokument7 SeitenLitz Quality Improvement Meeting: Levale XavierLevale XrNoch keine Bewertungen
- MasterchartDokument1 SeiteMasterchartLevale XrNoch keine Bewertungen
- Summer Internship Project: Master of Business AdministrationDokument90 SeitenSummer Internship Project: Master of Business AdministrationLevale XrNoch keine Bewertungen
- Automatic Text Detection Using Morphological Operations and InpaintingDokument5 SeitenAutomatic Text Detection Using Morphological Operations and InpaintingLevale XrNoch keine Bewertungen
- Question 4 & 12: Secondary School Level Higher School Level Bachelor Graduate Professional Post GraduateDokument4 SeitenQuestion 4 & 12: Secondary School Level Higher School Level Bachelor Graduate Professional Post GraduateLevale XrNoch keine Bewertungen
- TV Radio Notice & Pamphlets Social Networking Sites Newspapers & Magazines OthersDokument4 SeitenTV Radio Notice & Pamphlets Social Networking Sites Newspapers & Magazines OthersLevale XrNoch keine Bewertungen
- Figure No: 1.4 Most Popular CategoriesDokument7 SeitenFigure No: 1.4 Most Popular CategoriesLevale XrNoch keine Bewertungen
- AGENDA LitzDokument1 SeiteAGENDA LitzLevale XrNoch keine Bewertungen
- Question 4 & 12: Secondary School Level Higher School Level Bachelor Graduate Professional Post GraduateDokument4 SeitenQuestion 4 & 12: Secondary School Level Higher School Level Bachelor Graduate Professional Post GraduateLevale XrNoch keine Bewertungen
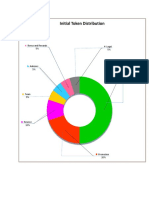
- Initial Token Distribution: Bonus and Rewards 5% Legal 5%Dokument1 SeiteInitial Token Distribution: Bonus and Rewards 5% Legal 5%Levale XrNoch keine Bewertungen
- Welcome To Robotcs: BY Mohammed Yaqoob H B.E, Hands On Trainer RoboticsDokument7 SeitenWelcome To Robotcs: BY Mohammed Yaqoob H B.E, Hands On Trainer RoboticsLevale XrNoch keine Bewertungen
- (Student Name) : in Partial Fulfillment of The Requirements For The Award of The DegreeDokument85 Seiten(Student Name) : in Partial Fulfillment of The Requirements For The Award of The DegreeLevale XrNoch keine Bewertungen
- CS/ It/ Mca/ Bca/ M.SC It/ BSC It E.E/ E.C./ EN Mech/ Civil Soft SkillsDokument3 SeitenCS/ It/ Mca/ Bca/ M.SC It/ BSC It E.E/ E.C./ EN Mech/ Civil Soft SkillsLevale XrNoch keine Bewertungen
- Fermi 120 TiteleDokument5 SeitenFermi 120 TiteleLevale XrNoch keine Bewertungen
- ArchitectureDokument2 SeitenArchitectureLevale XrNoch keine Bewertungen
- Questionnaire: Section A: Personal InformationsDokument23 SeitenQuestionnaire: Section A: Personal InformationsLevale XrNoch keine Bewertungen
- Project Report On Pizza HutDokument31 SeitenProject Report On Pizza HutLevale XrNoch keine Bewertungen
- Application of A SFCL For Fault Ride-Through Capability Enhancement of DG in A Micro-Grid System and Relay Protection CoordinationDokument8 SeitenApplication of A SFCL For Fault Ride-Through Capability Enhancement of DG in A Micro-Grid System and Relay Protection CoordinationLevale XrNoch keine Bewertungen