Beruflich Dokumente
Kultur Dokumente
A Survey On Verification of Outsourced Data Mining Computation
Originaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
A Survey On Verification of Outsourced Data Mining Computation
Copyright:
Verfügbare Formate
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 6, Issue 1, January - February 2017 ISSN 2278-6856
A Survey on Verification of Outsourced Data
Mining Computation
Umesh D Borse1, Dr.Lalit V Patil2
1
Department of Information Technology Smt. Kashibai Navale College of Engineering,(SKNCOE)
Pune, India.
2
Department of Information Technology Smt. Kashibai Navale College of Engineering (SKNCOE)
Pune, India.
Abstract Data mining is the process of analyzing the data from
Cloud computing is a computing where data is processed different perspectives and summarizing it into useful
using computing resources (e.g. Server). A Client of weak information that can be used to increase revenue, cuts
computational power outsourced their data to cloud (e.g. costs, or both. Data mining software is one of the
Server) for computation. This introduces Data mining as analytical tools for analyzing data. It permits users to
Service paradigm. Outsourcing data to the server facing a
analyze data from many different angles, differentiate it,
critical problem of verification. Whether the server returned
correct and complete computation result to the client. Other and summarize the relationships identified. Technically
issue is related to the security or privacy of outsourced data process of data mining used for finding patterns or co-
for computation. Then another issue is related to revenue relationship among dozens of fields in large relational
generation by cloud server. Most of the previous research databases. A general definition of frequent itemset mining
paper focus on different algorithms associated with frequent is finding a frequent occurrence of itemset from a
itemset mining and data security. Work on result integrity
collection of n no of itemset where support for that
verification is rare as compared to the data security and
efficient mining algorithms. This paper focuses on the
itemset is greater than or equal to the minimum support
problem of result verification of outsourced computation of threshold. An itemset is nothing but a collection of one or
frequent itemset. By generating power set, frequent and more items. Item can be anything. For e.g. Milk, Butter,
infrequent itemset and by creating M tree of a frequent Eggs, Coke, etc.
itemset, the result verification of frequent itemset mining
computation is done. This paper put forward an idea in the Cloud computing, an emerging trend of provisioning
end on verification of outsourced frequent itemset mining
scalable computing services, provides the opportunity that
computation by analyzing numerous work but different
authors in coming Section. The actual study reveals the data mining is offered as an outsourced service[1].
efficiency and effectiveness of the verification approaches. Frequent itemset mining plays important roles in data
analysis from a large database and many other significant
Keywords: Data mining as a service, Cloud computing, data mining task[6]. Frequent itemset mining has been
Frequent itemset mining, Result verification. proven essential in many applications such as market data
analysis, networking data study, and human gene
1. INTRODUCTION association study[1].A frequent itemset mining algorithm
Cloud computing is an Internet-based computing which runs on a set of text documents produced over a social
provides shared computer processing resources and data to network can display the central topic of discussion and
computers and other devices. On user demand access to pattern of usage of words in discussion threads and
shared computing resources (e.g., Computer Networks, blogs[6]. But frequent itemset mining is very expensive
Storage, Servers, Applications, and Services) which can computation task because of exponentially large data size.
be rapidly provisioned and released with minimal There for the weak computational power systems (Client)
management effort. Cloud computing provides various outsource their data to the computationally more powerful
capabilities to store and process users data in third-party systems (Server).It has been shown that outsourcing data
data centers; Third party data centers may be located far to a service provider brings several benefits to the data
from the user in the distance from across a city or across owner such as cost relief and a less commitment to storage
the world. In the simple word, cloud computing are and computational resources. This introduces the Data-
nothing but storing and accessing the stored data and Mining as Service (DMaS) paradigm[1]. Cloud computing
programs using the internet instead of computer's physical provides a natural solution for the Data Mining as Service
drive. paradigm. In the cloud computing era, a better solution is
to outsource the computations to a cloud service provider.
Volume 6, Issue 1, January February 2017 Page 6
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 6, Issue 1, January - February 2017 ISSN 2278-6856
In addition to saving on overhead and labor costs, Most of security by using different encryption scheme and
the client outsources data to improved efficiency, greater mapping scheme on data content[7]. Most of the previous
productivity and the opportunity to focus on core products research paper focuses on various algorithms which are
and functions of the business. Outsourcing is a practice efficiently used in frequent itemset mining. Integrity
used by different companies to reduce costs by transferring verification outsourcing frequent itemset mining is rare
portions of work to outside suppliers rather than and challenging. Out of these above mentioned issues this
completing it internally. Outsourcing is an effective cost- paper focus on the first issue i.e. result integrity
saving strategy when used properly. verification of outsourced computation of frequent itemset
mining.
Although outsourcing data to the third party (server) is a
viable option to the data owners (client), but client hesitate This article has been classified as follows Section 2 is
to place trust on cloud computing. Outsourcing data to the dedicated to related work, Section 3 Related work, Section
cloud raises few issues 1) First issue is about the integrity 4 Acknowledgement and Section 5 Conclude efforts of the
of the computed results[1]. There are many possible work.
reasons for the cloud to cheat with computation result.
The correctness integrity of mining results can be 2. LITERATURE SURVEY
corrupted if the service provider is with random fault or This section of literature survey eventually reveals some
not honest (e.g., lazy, malicious, etc.).Or Computation facts based on thought analysis of many authors work as
result can be damaged if the service provider is honest but follows.
makes mistakes in the mining process. 2) The second Boxiang Dong, Ruilin Liu[1] Proposes an idea of efficient
issue is related to the security or privacy of outsourced probabilistic and deterministic verification approaches to
data for computation if service provider contaminates or verify whether the server has returned correct and
tampers computational result[5] or server can access to complete frequent itemsets. In proposed word probabilistic
valuable data of the owner and may learn or disclose approach is designed to catch mining result that does not
sensitive information from it.3) The third issue is related meet a predefined requirement and Deterministic
to revenue generation by cloud server[2]. A cloud would approach aims to find frequent itemset mining result are
like to improve its revenue by investing fewer resources incomplete and incorrect with 100% probability. The basic
while charging for more. A cloud server may provide idea is to create frequent and infrequent itemsets. Those
some fake results instead of being spending its resources infrequent itemsets are used as evidence to check server
in computing the correct ones. mining result. In this proposed
The existing research works contribute to practical data
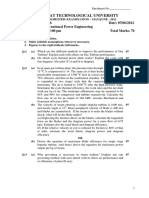
Table 1: Literature Survey on Verification of Outsourced Computation
Sr. Techniques
Title of Paper Methodology Advantages Disadvantages
No Used
Trust But Verify:
Verifying Result Propose efficient
Better performance Bilinear
Correctness of Out- probabilistic and Proposed work is
with respect to time to Pairing and
[1] sourced Frequent deterministic limited to small
construct evidence and Markel Hash
Itemset Mining in verification set of itemset
proof of itemset Tree
Data-mining-as-a- approaches
service Paradigm
Propose a protocol for
any efficiently
Limitation of Markel Hash
Practical Delegation computable function
Overhead of the using different Tree and X86
[2] of Computation using and An adaptation of
protocol itself is lower Operating computational
Multiple Servers the protocol for the X
systems model.
86 computation
models.
Volume 6, Issue 1, January February 2017 Page 7
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 6, Issue 1, January - February 2017 ISSN 2278-6856
Requires
Construct a Verifiable
How to Delegate and Allows arbitrary parties running an
Computation scheme Attribute-
Verify in Public to submit inputs for expensive
with a public based
[3] Verifiable Computa- delegation And verify preprocessing to
delegation and public Encryption
tion from Attribute- the correctness of the generate a secret
verifiability from any technique
Based Encryption results returned. key and
ABE scheme.
evaluation key
Propose the notion of Not be Bilinear
Verifiable Computa- a verifiable database applicable for Pairing,
The time cost is very
tion over Large with incremental the insertion VDB Scheme,
[4] low as compared to the
Database with updates that can lead operation due to Vector
existing scheme.
Incremental Updates. to huge efficiency the vector Commitment
gain. commitment. Scheme.
A malicious miner
Propose and develop
cannot gain from The artificial
An Audit an audit environment,
performing any database takes
Environment for which consists of a Artificial
malicious actions and more time to
[5] Outsourcing of database transforma- Itemset
thus the returned generate as an
Frequent Itemset tion method and a Planting
mining result is both original database
Mining result verification
correct and complete is large.
method.
with high confidence.
work no fake itemset are used to check mining result. one is Public Delegation and other one is Public
Bilinear Pairing and Markel Hash Tree Technique are Verifiability, in which Public Delegation allows arbitrary
utilized for these approaches. This proposed methodology parties to submit inputs for delegation, and Public
has better performance with respect to time to construct Verifiability allows arbitrary parties (and not just the
evidence and proof of itemset and with the limitation that delegator) to verify the correctness of the results returned
proposed work is limited to a small set of an itemset. by the worker. The verifiable computation schemes with
the public delegation and public verifiability have
Ran Canetti, Ben Riva, Guy N. Rothblum[2] Introduces a advantage that this methodology allows arbitrary parties to
protocol for any efficiently computable function and an submit inputs for delegation, and verify the correctness of
adaptation of the protocol for the X 86 computation the results returned. Disadvantage of the proposed system
models and a prototype implementation, called Quin. As is it requires running an expensive preprocessing to
key concept of this methodology is outsource the generate a secret key and evaluation key before delegation.
computation to N number of cloud and client takes
number of return output out of that majority of same Xiaofeng Chen, Jin Li, JianWeng[4] introduce the notion
return output is the correct result of the outsourced of verifiable database with incremental updates (Inc-
computation. The client asks for the result of the function VDB).The update algorithm in Inc-VDB is an incremental
f(x) from two (or more) cloud servers. In case they make one, i.e., the client can efficiently compute the new cipher
contradictory claims about f(x), the client engages in a text and the updated tokens with previous values, rather
protocol with each of the servers, at the end of which the than from scratch. Thus, Inc-VDB schemes can lead to
client can efficiently determine the true claim as long as huge efficiency gain when the database undergoes
there is at least one honest server. In this protocol client frequent while small modifications. Also propose a
searches for inconsistencies between the intermediate general Inc-VDB framework by incorporating the
states of the two servers computations. In this Markel primitive of vector commitment and the encrypt-then-
Hash Tree and X 86 computational models is used for incremental MAC mode of encryption. Besides, the
computation. It having an advantage of an overhead of the proposed Inc-VDB scheme supports the public
protocol is itself low. This proposed methodology is verifiability. Also introduce a new property called
having a limitation of using the different operating accountability for VDB schemes. That is, after the client
system. detected the tampering of the server, the client should be
able to provide a proof to convince the judge of the facts.
Bryan Parno, Mariana Raykova, Vinod Vaikuntanathan[3] Author proves that the proposed Inc-VDB scheme satisfies
proposes public verifiable computation in two directions the property of accountability. The proposed methodology
Volume 6, Issue 1, January February 2017 Page 8
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 6, Issue 1, January - February 2017 ISSN 2278-6856
is used Bilinear Pairing, Verifiable Database, and Vector 3. RELATED WORK
commitment scheme. This proposed methodology provides
In [7] author focuses on the integrity and verification issue
an advantage that the time cost is minimal as compared to
in Uncertain Frequent Itemset mining problem during the
the existing scheme. But system has limitation that it not
outsourcing process, i.e., how the client verifies the
applicable to the insertion operation due to the vector
mining results. The author specifically explores and
commitment.
extends the existing work on deterministic frequent
itemset out-sourcing verification to the uncertain scenario.
W. K. Wong David W. Cheung Edward Hung[5] Proposed
For this purpose, the author extends the existing
and developed an audit environment, which consists of a
outsourcing frequent itemset mining work to uncertain
database transformation method and a result verification
area w.r.t. the two popular uncertain frequent itemset
method. The Figure 1 shows the architecture diagram of
definition criteria and the approximate uncertain frequent
an audit environment. The proposed work is used for a
itemset mining methods. Specifically, authors construct
database transformation method and a result verification
and improve the basic/enhanced verification scheme with
method. The primary component verification environment
such different uncertain frequent itemset definition
is an Artificial Itemset Planting (AIP) technique. The
respectively.
main component of this audit environment is an artificial
itemset planting technique. The approach to solve the
To verify the outsourced computation[8] proposed
integrity problem is to construct an audit environment.
different idea that client can use two or more cloud for the
Essentially, an audit environment consists of (i) a set of
computation instead of using a single cloud for
transformation methods that transform a database T to
computation. If the client wants better assurance of the
another database U, based on which the service provider
integrity of outsourced computation, then he can use more
will mine and return a mining result R; (ii) a set of
cloud for the guarantee. Minimum three clouds must be
verification methods that take R as an input and return a
utilized for computation to get the better assurance of the
deduction of whether R is correct and complete; (iii)
integrity of computation. Client outsourced his data to the
auxiliary data that assist the verification methods. An
three different clouds for computation, now all cloud
interesting property of this approach is that the audit
returns the output of computation out of that majority of
environment forms a standalone system. It is self-
the expected output to be his correct output. The
contained in the sense that the verification process can be
disadvantage of this proposed idea is client have to pay
done entirely by using only the auxiliary data that are
more if the number of clouds used more.
included in the environment. In other words, the original
database need not be accessed during verification. A
An author first introduces the rational lazy-and-partially-
malicious miner cannot benefit from performing any
dishonest workers[9] in the outsourcing computation
malicious actions and thus the returned mining result is
model. A new fair conditional payment scheme proposed
both correct and complete with a high confidence, but
for outsourcing computation that is only based on
artificial database takes more time to generate as an
traditional electronic cash systems. The proposed
original database is large.
construction uses a semi-trusted third party to get the
fairness and efficiency. However, the third party is only
involved in the protocol in case of any disputes. Compared
with the other existing solutions the proposed solution is
much more efficient. This advanced work has a
disadvantage that Third Party is not fully trusted, and may
collude with one party to obtain profits at the expense of
the other party.
Figure 1: The architecture of the scheme [5]
Volume 6, Issue 1, January February 2017 Page 9
International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)
Web Site: www.ijettcs.org Email: editor@ijettcs.org
Volume 6, Issue 1, January - February 2017 ISSN 2278-6856
4. PROPOSED SYSTEM design and implement a framework for verification of
outsourced data mining computation of frequent itemset.
ACKNOWLEDGEMENTS
I am extremely thankful to my guide Dr. L. V. Patil for
suggesting the topic for survey and providing all the
assistance needed to complete the work. He inspired me
greatly to work in this area. His guidance and discussions
with him are valuable in realization of this survey.
References
[1] Boxiang Dong, Ruilin Liu, Hui (Wendy) Wang,
Trust But Verify:Verifying Result Correctness of
Outsourced Frequent Itemset Mining in Data-
mining-as-a-service Paradigm IEEE Transactions
10.1109/ TSC.2015. 24363872015.
[2] Ran Canetti, Ben Riva, Guy N. Rothblum, Practical
Delegation of Computation using Multiple Servers
ACM 978-1-4503-0948-6/11/10 October 1721,
2011.
[3] Bryan Parno, Mariana Raykova, Vinod Vaikunta
Figure 2: Proposed system architecture for verification of nathan, How to Delegate and Verify in Public
outsourced data mining computation. Verifiable Computation from Attribute-Based
Encryption International Association for
The proposed work put forward an idea of verification of Cryptologic Research LNCS 7194, pp. 422439,
outsourced data mining computation of frequent itemset 2012.
mining. The figure 2 shows proposed system architecture [4] Xiaofeng Chen, Jin Li, JianWeng, Jianfeng Ma, and
of outsourced data mining computation. The proposed Wenjing Lou, Verifiable Computation over Large
system architecture describes the process of verification of Database with Incremental Updates European
outsourced data mining computation of frequent itemset. Symposium on Research in Computer Security
In which end user outsourced the data to the cloud for (ESORICS 2014), LNCS8712, Springer, pp. 148-
frequent itemset mining. Then cloud returns the 162, 2014.
computation result to the end user. The end user generates [5] W. K. Wong, David W. Cheung, Edward Hung, An
Power set from the small set of the outsourced data. Then Audit Environment for Outsourcing of Frequent
compute for Top N frequent and Top N infrequent itemset Itemset Mining VLDB Endowment, August 2428,
by considering threshold value. Calculate the support for ACM 2009.
the Top N frequent and Top N infrequent itemset. The M [6] Zahra Farzanyar, Nick Cercone, Efficient Mining of
tree algorithm is used to form tree on the basis of the Frequent Itemsets in Social Network Data based on
support calculated. Same support value itemsets are MapReduce Framework ACM 978-1-4503-2240-9
clustered at node end. The same tree is formed for the /13/08 August 25-29, 2013.
return result from the cloud. Then end user compares both [7] Qiwei Lu, Wenchao Huang, Yan Xiong, and Xudong
the trees to verify the return result received from the Gong, Integrity Verification for Outsourcing
cloud. If the both tree matched then returned mining result Uncertain Frequent Itemset Mining arXiv:1307.
from the cloud is correct else return result is incorrect. At 2991v2 [cs.DB] 12Jul2013.
the end verification report is generated for the end user. [8] Ran Canetti, Ben Riva, Guy Rothblum, Verifiable
Computation with Two or More Clouds Workshop
5. CONCLUSION on Cryptography and Security in Clouds, 2011.
The presented paper is literature review on different [9] Xiaofeng Chen, Jin Li, and Willy Susilo, Senior
methodology used for the verification of frequent itemset Member, IEEE Efficient Fair Conditional Payments
mining computation. This presents the survey on different for Outsourcing Computations IEEE Transactions
research paper, finding advantages, disadvantages and on Information Forensics and Security, Vol. 7, No. 6,
different issues related to verification. Simple problem December 2012.
definition for research work has been derived from above
survey. An observed conclusion is need of enriched
framework for the verification. The future scope is to
Volume 6, Issue 1, January February 2017 Page 10
Das könnte Ihnen auch gefallen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Creative Photography Lab 52 Fun Exercises For Developing Self-Expression With Your CameraDokument146 SeitenCreative Photography Lab 52 Fun Exercises For Developing Self-Expression With Your Camerajwestmister100% (2)
- Customize AutoCAD P&ID with Engineering ItemsDokument33 SeitenCustomize AutoCAD P&ID with Engineering ItemsnunosobralNoch keine Bewertungen
- LightWave 3D 8 TexturingDokument505 SeitenLightWave 3D 8 Texturingmanjeethlal80% (5)
- Protec SPD BrochureDokument4 SeitenProtec SPD BrochureCrestNoch keine Bewertungen
- Process Control Valves TrainingDokument12 SeitenProcess Control Valves TrainingpptmnltNoch keine Bewertungen
- Design and Detection of Fruits and Vegetable Spoiled Detetction SystemDokument8 SeitenDesign and Detection of Fruits and Vegetable Spoiled Detetction SystemInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Impact of Covid-19 On Employment Opportunities For Fresh Graduates in Hospitality &tourism IndustryDokument8 SeitenImpact of Covid-19 On Employment Opportunities For Fresh Graduates in Hospitality &tourism IndustryInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Experimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterDokument7 SeitenExperimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Detection of Malicious Web Contents Using Machine and Deep Learning ApproachesDokument6 SeitenDetection of Malicious Web Contents Using Machine and Deep Learning ApproachesInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Customer Satisfaction A Pillar of Total Quality ManagementDokument9 SeitenCustomer Satisfaction A Pillar of Total Quality ManagementInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- THE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSDokument7 SeitenTHE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- An Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewDokument9 SeitenAn Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Experimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterDokument7 SeitenExperimental Investigations On K/s Values of Remazol Reactive Dyes Used For Dyeing of Cotton Fabric With Recycled WastewaterInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Detection of Malicious Web Contents Using Machine and Deep Learning ApproachesDokument6 SeitenDetection of Malicious Web Contents Using Machine and Deep Learning ApproachesInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Analysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyDokument6 SeitenAnalysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Study of Customer Experience and Uses of Uber Cab Services in MumbaiDokument12 SeitenStudy of Customer Experience and Uses of Uber Cab Services in MumbaiInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Study of Customer Experience and Uses of Uber Cab Services in MumbaiDokument12 SeitenStudy of Customer Experience and Uses of Uber Cab Services in MumbaiInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Customer Satisfaction A Pillar of Total Quality ManagementDokument9 SeitenCustomer Satisfaction A Pillar of Total Quality ManagementInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- THE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSDokument7 SeitenTHE TOPOLOGICAL INDICES AND PHYSICAL PROPERTIES OF n-HEPTANE ISOMERSInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Soil Stabilization of Road by Using Spent WashDokument7 SeitenSoil Stabilization of Road by Using Spent WashInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Mexican Innovation System: A System's Dynamics PerspectiveDokument12 SeitenThe Mexican Innovation System: A System's Dynamics PerspectiveInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- An Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewDokument9 SeitenAn Importance and Advancement of QSAR Parameters in Modern Drug Design: A ReviewInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Advanced Load Flow Study and Stability Analysis of A Real Time SystemDokument8 SeitenAdvanced Load Flow Study and Stability Analysis of A Real Time SystemInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Analysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyDokument6 SeitenAnalysis of Product Reliability Using Failure Mode Effect Critical Analysis (FMECA) - Case StudyInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Staycation As A Marketing Tool For Survival Post Covid-19 in Five Star Hotels in Pune CityDokument10 SeitenStaycation As A Marketing Tool For Survival Post Covid-19 in Five Star Hotels in Pune CityInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- The Impact of Effective Communication To Enhance Management SkillsDokument6 SeitenThe Impact of Effective Communication To Enhance Management SkillsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Digital Record For Privacy and Security in Internet of ThingsDokument10 SeitenA Digital Record For Privacy and Security in Internet of ThingsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Deep Learning Based Assistant For The Visually ImpairedDokument11 SeitenA Deep Learning Based Assistant For The Visually ImpairedInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Secured Contactless Atm Transaction During Pandemics With Feasible Time Constraint and Pattern For OtpDokument12 SeitenSecured Contactless Atm Transaction During Pandemics With Feasible Time Constraint and Pattern For OtpInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- A Comparative Analysis of Two Biggest Upi Paymentapps: Bhim and Google Pay (Tez)Dokument10 SeitenA Comparative Analysis of Two Biggest Upi Paymentapps: Bhim and Google Pay (Tez)International Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Performance of Short Transmission Line Using Mathematical MethodDokument8 SeitenPerformance of Short Transmission Line Using Mathematical MethodInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Synthetic Datasets For Myocardial Infarction Based On Actual DatasetsDokument9 SeitenSynthetic Datasets For Myocardial Infarction Based On Actual DatasetsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Challenges Faced by Speciality Restaurants in Pune City To Retain Employees During and Post COVID-19Dokument10 SeitenChallenges Faced by Speciality Restaurants in Pune City To Retain Employees During and Post COVID-19International Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Predicting The Effect of Fineparticulate Matter (PM2.5) On Anecosystemincludingclimate, Plants and Human Health Using MachinelearningmethodsDokument10 SeitenPredicting The Effect of Fineparticulate Matter (PM2.5) On Anecosystemincludingclimate, Plants and Human Health Using MachinelearningmethodsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Anchoring of Inflation Expectations and Monetary Policy Transparency in IndiaDokument9 SeitenAnchoring of Inflation Expectations and Monetary Policy Transparency in IndiaInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Chasis+5Y18+-+FSCQ1265RT LA76933 LA78041 LA42352 BSC23-N0120+Hitachi+CDH-29GFS12 PDFDokument45 SeitenChasis+5Y18+-+FSCQ1265RT LA76933 LA78041 LA42352 BSC23-N0120+Hitachi+CDH-29GFS12 PDFdardoNoch keine Bewertungen
- Investigation On Thermal Characteristic of Banana Waste Wood Sawdust Briquette - PUBLISHEDDokument7 SeitenInvestigation On Thermal Characteristic of Banana Waste Wood Sawdust Briquette - PUBLISHEDku1zarinaNoch keine Bewertungen
- MD 5 SumDokument47 SeitenMD 5 SumBabay Si TagamaNoch keine Bewertungen
- BingDokument5 SeitenBingdheaNoch keine Bewertungen
- 120FF51A Installation Guide For SAP Solutions PDFDokument234 Seiten120FF51A Installation Guide For SAP Solutions PDFNaqib Hassan100% (1)
- Cylinder Head Valve Guide and Seat Inspection and RepairDokument1 SeiteCylinder Head Valve Guide and Seat Inspection and Repairnetifig352Noch keine Bewertungen
- Slice 3 Choice BoardDokument3 SeitenSlice 3 Choice Boardapi-463991923Noch keine Bewertungen
- Solucionario - Termodinamica - Cengel - 7ed (1) - 519-528Dokument10 SeitenSolucionario - Termodinamica - Cengel - 7ed (1) - 519-528Lizeth Maria lizarazoNoch keine Bewertungen
- Help - Walkthrough - Creating Beam and Plate Features - AutodeskDokument5 SeitenHelp - Walkthrough - Creating Beam and Plate Features - AutodeskTien HaNoch keine Bewertungen
- DabbawalaDokument27 SeitenDabbawalaAditya ShresthaNoch keine Bewertungen
- Noise Barriers Standards FrameworkDokument50 SeitenNoise Barriers Standards FrameworkanandalaharNoch keine Bewertungen
- GTU BE- Vth SEMESTER Power Engineering ExamDokument2 SeitenGTU BE- Vth SEMESTER Power Engineering ExamBHARAT parmarNoch keine Bewertungen
- Paytm Details - HistoryDokument12 SeitenPaytm Details - HistorySachin PoddarNoch keine Bewertungen
- BW17V1D24Dokument5 SeitenBW17V1D24Lye YpNoch keine Bewertungen
- Rsoft Installation GuideDokument39 SeitenRsoft Installation GuidekishoreputhaNoch keine Bewertungen
- MiVoice Office 400 Products BR enDokument12 SeitenMiVoice Office 400 Products BR enWalter MejiaNoch keine Bewertungen
- General DataDokument8 SeitenGeneral DataGurvinderpal Singh MultaniNoch keine Bewertungen
- Mechanical Fitting - ICE Level 3 - 06 10 14Dokument6 SeitenMechanical Fitting - ICE Level 3 - 06 10 14KingsleyOwunariDokuboNoch keine Bewertungen
- 2017-12-25 17:27:54Dokument3 Seiten2017-12-25 17:27:54Raghman JrNoch keine Bewertungen
- List of Portmanteau Words: GeneralDokument7 SeitenList of Portmanteau Words: GeneraltarzanNoch keine Bewertungen
- Netsh Wlan Start HostednetworkDokument3 SeitenNetsh Wlan Start HostednetworkM Nanda KumarNoch keine Bewertungen
- Chinese Material To AstmDokument4 SeitenChinese Material To Astmvalli rajuNoch keine Bewertungen
- Ligaya NG Buhay EnsembleDokument2 SeitenLigaya NG Buhay EnsembleFrinzess VelascoNoch keine Bewertungen
- Flux Cored Wires (Elga) PDFDokument15 SeitenFlux Cored Wires (Elga) PDFVladan TimotijevicNoch keine Bewertungen
- Adjustable Accurate Reference SourceDokument2 SeitenAdjustable Accurate Reference SourceJoey TorresNoch keine Bewertungen