Beruflich Dokumente
Kultur Dokumente
Isms-C Doc 6.2.1 PDF
Hochgeladen von
dhir.ankurOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Isms-C Doc 6.2.1 PDF
Hochgeladen von
dhir.ankurCopyright:
Verfügbare Formate
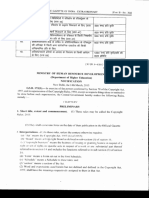
Document Control
Reference: ISMS-C DOC
WIRELESS NOTEBOOK COMPUTER 6.2.1
SECURITY (TIER 2) Issue No:
Issue Date:
Page: 1 of 2
This is a toolkit trial version only -
Buy the full ISMS ISO 27001: 2013 Documentation Toolkit
here
1 Scope1
All users of the Organisation Names wireless notebook computers [and other
mobile devices] are within the scope of this procedure.
2 Responsibilities
The Head of IT (CIO) is responsible for specifying and/or providing the firewalls,
anti-malware software, automatic updating, connectivity and backup facilities
required under this procedure.
The Head of HR is responsible for user training.
All users have specific responsibilities in terms of their User Agreements.
3 Procedure [ISO27002 Clause 6.2.1]
3.1 Organisation Name requires notebook computer level deployment of [the
companys specified] firewalls, anti-malware software, and automatic updating
facilities that are all up to date [and meet the corporate minimum standards, which
are specified in [ ] and in the User Agreement.
3.2 Organisation Name requires notebook computer level deployment of the corporate
policy on usernames and passwords (see control section 9.1 of the Manual), to
have a password protected screensaver, and to [password protect/encrypt] all Commented [A1]: If so, how is to be done?
folders containing [confidential] corporate information, and to disable folder and
printer sharing, all of which is specified in the User Agreement.
3.3 Organisation Name requires that notebook computers are physically protected
against theft and damage while in transit, in storage or in use and that, in cases of
loss or theft, the specified corporate policy (see User Agreement) for dealing with
such incidents is followed.
3.4 Organisation Name requires users (in the User Agreement) to ensure that all the
most recent operating system and application security-related patches, fixes and
updates have been installed.
3.5 Organisation Name requires (in the User Agreement) that notebook computers are
backed up in line with corporate specification [set out where?].
3.6 [].
3.7 [].
1
Chapter 21 of IT Governance: An International Guide to Data Security and ISO27001/ISO27002 deals with
mobile computing. This template will need to be expanded to take into account mobile phones, Blackberries,
PDAs and any other mobile devices, and adjusted to reflect different decisions on connectivity.
Organisation Name Classification_3
Customisable PROCEDURE template v3.0
Comments to feedback@itgovernance.co.uk
IT Governance Ltd 2015
www.itgovernance.co.uk
Document Control
Reference: ISMS-C DOC
WIRELESS NOTEBOOK COMPUTER 6.2.1
SECURITY (TIER 2) Issue No:
Issue Date:
Page: 2 of 2
3.8 [].
3.9 [].
3.10 Organisation Name provides users with appropriate training and awareness to
ensure that they understand the risks of wireless on the road computing and that
they understand and can carry out their agreed security obligations.
3.11 Work instruction ISMS DOC [ ] sets out how the corporate requirements set out in
Clause 3.1 and 3.4 above are enforced.
3.12 WI ISMS DOC [ ] sets out how the [VPN or other connectivity solution] is to be Commented [A2]: A risk assessment should drive your choice of
operated. connectivity
3.13 WI ISMS DOC [ ] sets out how e-mails are to be encrypted when sent from mobile Commented [A3]: A risk assessment should drive your decision
devices. on this
Document Owner and Approval
The Network Manager is the owner of this document and is responsible for ensuring
that this procedure is reviewed in line with the review requirements of the ISMS.
A current version of this document is available to [all/specified] members of staff
on the [corporate intranet] and is published [ ].
This procedure was approved by the Chief Information Security Officer (CISO) on
[date] and is issued on a version controlled basis under his/her signature.
Signature: Date:
Change History Record
Issue Description of Change Approval Date of Issue
1 Initial issue <Manager> Xx/yy/zz
This is a toolkit trial version only -
Buy the full ISMS ISO 27001: 2013 Documentation Toolkit
here
Organisation Name Classification_3
Customisable PROCEDURE template v3.0
Comments to feedback@itgovernance.co.uk
IT Governance Ltd 2015
www.itgovernance.co.uk
Das könnte Ihnen auch gefallen
- Isms-C Doc 16.1.5 PDFDokument2 SeitenIsms-C Doc 16.1.5 PDFdhir.ankurNoch keine Bewertungen
- User Access Management (Tier 2) : Buy The Full ISMS ISO 27001: 2013 Documentation Toolkit HereDokument3 SeitenUser Access Management (Tier 2) : Buy The Full ISMS ISO 27001: 2013 Documentation Toolkit HereFlamur PrapashticaNoch keine Bewertungen
- Security in Converged NetworksDokument22 SeitenSecurity in Converged NetworksKunalNoch keine Bewertungen
- MICROSERVICES SECURITY AND PRIVACY CHALLENGESDokument7 SeitenMICROSERVICES SECURITY AND PRIVACY CHALLENGESahmadNoch keine Bewertungen
- Inventory and Ownership of Assets (Tier 2) : Buy The Full ISMS ISO 27001: 2013 Documentation Toolkit HereDokument2 SeitenInventory and Ownership of Assets (Tier 2) : Buy The Full ISMS ISO 27001: 2013 Documentation Toolkit HereFlamur PrapashticaNoch keine Bewertungen
- NVMSTG011 HardeningGuide v1.0.0Dokument67 SeitenNVMSTG011 HardeningGuide v1.0.0Abhishek BahiratNoch keine Bewertungen
- 149.editedDokument5 Seiten149.editedTonnie KiamaNoch keine Bewertungen
- A 1-2-3 Approach To ICS Security: Part 1-Secure Industrial NetworksDokument5 SeitenA 1-2-3 Approach To ICS Security: Part 1-Secure Industrial Networksep230842Noch keine Bewertungen
- Running Head: Managing Desktop Security 1Dokument5 SeitenRunning Head: Managing Desktop Security 1Tonnie KiamaNoch keine Bewertungen
- IJIRET Sapna HD Network Security Issues Measures and Tools For Intruder AttacksDokument4 SeitenIJIRET Sapna HD Network Security Issues Measures and Tools For Intruder AttacksInternational Journal of Innovatory Research (IJIR), (IJIRET) & (IJIRSM).Noch keine Bewertungen
- Chapter-1 Introduction To System and Network Admin 1Dokument19 SeitenChapter-1 Introduction To System and Network Admin 1Tiruneh KibekabNoch keine Bewertungen
- What Is Network SecurityDokument3 SeitenWhat Is Network SecurityGirish BindalkarNoch keine Bewertungen
- Complete Protection On Digital surface-PHD InterviewDokument15 SeitenComplete Protection On Digital surface-PHD InterviewAnju ElzabethNoch keine Bewertungen
- A Study On Security Responsibilities and Adoption inDokument7 SeitenA Study On Security Responsibilities and Adoption inInternational Journal of Research in Engineering and TechnologyNoch keine Bewertungen
- Patch Management PolicyDokument6 SeitenPatch Management PolicysantoshNoch keine Bewertungen
- 3DS Information Security Overview ExternalDokument15 Seiten3DS Information Security Overview ExternalRaut AbhimanNoch keine Bewertungen
- Project Part 8-Windows Hardening RecommendationsDokument4 SeitenProject Part 8-Windows Hardening Recommendationspramod aloorNoch keine Bewertungen
- Interview Questions 2Dokument5 SeitenInterview Questions 2Ayesh HoshNoch keine Bewertungen
- 3com Intelligent Management Center (Imc) Endpoint Admission Defense (Ead)Dokument4 Seiten3com Intelligent Management Center (Imc) Endpoint Admission Defense (Ead)lluidysNoch keine Bewertungen
- A Paper On Intrusion DetectionDokument5 SeitenA Paper On Intrusion DetectionAtere OluwadamilolaNoch keine Bewertungen
- Assignment 1 (1) CSDokument4 SeitenAssignment 1 (1) CSHansu MalviyaNoch keine Bewertungen
- 001 Iccts2012 T003Dokument6 Seiten001 Iccts2012 T003satozNoch keine Bewertungen
- Security Issues For Cloud ComputingDokument9 SeitenSecurity Issues For Cloud ComputingResearch Cell: An International Journal of Engineering SciencesNoch keine Bewertungen
- Architecture of A Identity Based Firewall SystemDokument9 SeitenArchitecture of A Identity Based Firewall SystemAIRCC - IJNSANoch keine Bewertungen
- Security Summative Assignment Summer - 2022 - V2Dokument7 SeitenSecurity Summative Assignment Summer - 2022 - V2M17Noch keine Bewertungen
- Chapter 1: (Network Security) : PreambleDokument21 SeitenChapter 1: (Network Security) : PreambleArras DaouNoch keine Bewertungen
- 18 20 AnswerDokument23 Seiten18 20 Answers2187022Noch keine Bewertungen
- The ISC2 Cybersecurity LexiconDokument13 SeitenThe ISC2 Cybersecurity LexiconromawoodzNoch keine Bewertungen
- WP BESTPRAC Securing Intelligent Building Management SystemDokument16 SeitenWP BESTPRAC Securing Intelligent Building Management Systemkakyo29433Noch keine Bewertungen
- Cybersecurity standards and breach storiesDokument15 SeitenCybersecurity standards and breach storiesDhiraj ShindeNoch keine Bewertungen
- Laboratory Activity 2Dokument4 SeitenLaboratory Activity 2Game LikessNoch keine Bewertungen
- Single-Pane-Of-Glass Cloud Console: Providing Centralized Visibility, Management and Insight Across All OsesDokument20 SeitenSingle-Pane-Of-Glass Cloud Console: Providing Centralized Visibility, Management and Insight Across All OsesMing LeNoch keine Bewertungen
- Security Checklist For The Internet of Things: An Essential Guide To Securing Connected ProductsDokument13 SeitenSecurity Checklist For The Internet of Things: An Essential Guide To Securing Connected ProductsMartín Santiago FranciscoNoch keine Bewertungen
- Vulnerabilities, Threats, and AttacksDokument49 SeitenVulnerabilities, Threats, and Attacksjl101100% (1)
- Network Connection Policy SummaryDokument2 SeitenNetwork Connection Policy SummaryAmine RachedNoch keine Bewertungen
- SudhaDokument13 SeitenSudhabalaji xeroxNoch keine Bewertungen
- BalaBit Comply ISO 27011Dokument6 SeitenBalaBit Comply ISO 27011ziaire.natanaelNoch keine Bewertungen
- Essential Guide to IT OperationsDokument8 SeitenEssential Guide to IT OperationsZain HasanNoch keine Bewertungen
- Cse Instructor Materials Chapter7Dokument26 SeitenCse Instructor Materials Chapter7api-224615605Noch keine Bewertungen
- Secure Data in Wireless Sensor Network Via DesDokument25 SeitenSecure Data in Wireless Sensor Network Via Desadmin2146Noch keine Bewertungen
- Factsheet Checklist Security of ICS SCADA SystemsDokument6 SeitenFactsheet Checklist Security of ICS SCADA SystemsMoodaly BrayenNoch keine Bewertungen
- BSIA Cyber Secure It January 2019Dokument16 SeitenBSIA Cyber Secure It January 2019nsadnanNoch keine Bewertungen
- An Overview and Study of Security Issues & Challenges in Cloud ComputingDokument6 SeitenAn Overview and Study of Security Issues & Challenges in Cloud ComputingRoyal TNoch keine Bewertungen
- Halkyn Consulting SSAQDokument9 SeitenHalkyn Consulting SSAQAhmed M. SOUISSI100% (1)
- Implementation Guide For ICS Using The CIS Controls-1Dokument23 SeitenImplementation Guide For ICS Using The CIS Controls-1Getinet Admassu100% (1)
- Operations Security Policy Template v1.0Dokument10 SeitenOperations Security Policy Template v1.0rsgrthyjhNoch keine Bewertungen
- Ultramar Cibersecurity 30-05-23Dokument7 SeitenUltramar Cibersecurity 30-05-23Luis MontecinosNoch keine Bewertungen
- Update and Optimise Network Security: Inside This ReadingDokument7 SeitenUpdate and Optimise Network Security: Inside This ReadingTarik ShiguteNoch keine Bewertungen
- Term Paper On Cloud Security: Polinati Suresh Reddy Reg No-11703824 Sec - K17SD-A30Dokument6 SeitenTerm Paper On Cloud Security: Polinati Suresh Reddy Reg No-11703824 Sec - K17SD-A30Suresh Reddy PolinatiNoch keine Bewertungen
- Information Security Management System (ISMS) TemplateDokument10 SeitenInformation Security Management System (ISMS) TemplateLawChungTingNoch keine Bewertungen
- Trusting Your Cloud Provider. Protecting Private Virtual MachinesDokument11 SeitenTrusting Your Cloud Provider. Protecting Private Virtual MachinesAleksanderNoch keine Bewertungen
- Best Practices For Securing An Intelligent Building Management SystemDokument16 SeitenBest Practices For Securing An Intelligent Building Management SystembdsisiraNoch keine Bewertungen
- Annex To Circular On Cyber Security Framework For Primary (Urban) Cooperative Banks - IDokument4 SeitenAnnex To Circular On Cyber Security Framework For Primary (Urban) Cooperative Banks - IDhivya vikramNoch keine Bewertungen
- Linux Hardening PDFDokument4 SeitenLinux Hardening PDFAnoopNoch keine Bewertungen
- CPPPMUSABDokument75 SeitenCPPPMUSABMusabNoch keine Bewertungen
- Chapter-9 Security and Privacy Architecture: Technological University (Meiktila) Department of Information TechnologyDokument19 SeitenChapter-9 Security and Privacy Architecture: Technological University (Meiktila) Department of Information Technologyfna4463Noch keine Bewertungen
- Research Paper On Operating System SecurityDokument5 SeitenResearch Paper On Operating System Securityh03ch3b4100% (1)
- Chapert 3 and 4 PDF-1Dokument26 SeitenChapert 3 and 4 PDF-1Tora SarkarNoch keine Bewertungen
- Computer Science Self Management: Fundamentals and ApplicationsVon EverandComputer Science Self Management: Fundamentals and ApplicationsNoch keine Bewertungen
- Chapter 1Dokument10 SeitenChapter 1dhir.ankurNoch keine Bewertungen
- 4.3 Design (Amendment) Rules, 2008Dokument26 Seiten4.3 Design (Amendment) Rules, 2008dhir.ankurNoch keine Bewertungen
- 3.2 Copyrights (Amendment) Act, 2012Dokument14 Seiten3.2 Copyrights (Amendment) Act, 2012Ankur DhirNoch keine Bewertungen
- 3.3 Copyright Rules, 2013Dokument41 Seiten3.3 Copyright Rules, 2013dhir.ankurNoch keine Bewertungen
- Manual of Trade Marks: Practice & ProcedureDokument143 SeitenManual of Trade Marks: Practice & ProcedureSaurabh KumarNoch keine Bewertungen
- Ipr NotesDokument179 SeitenIpr NotesRajan MeenaNoch keine Bewertungen
- 1.2 Patent Rules 1970 - 11 March 2015Dokument95 Seiten1.2 Patent Rules 1970 - 11 March 2015dhir.ankurNoch keine Bewertungen
- Establishing An Integrated Management SyDokument65 SeitenEstablishing An Integrated Management Sydhir.ankurNoch keine Bewertungen
- Trade Mark RulesDokument282 SeitenTrade Mark Ruleslovingboy22Noch keine Bewertungen
- Chapter2975 PDFDokument25 SeitenChapter2975 PDFDivya ChauhanNoch keine Bewertungen
- DNV Brochure FOOD Tcm163-344274Dokument12 SeitenDNV Brochure FOOD Tcm163-344274dhir.ankurNoch keine Bewertungen
- Halalindia EcodesDokument5 SeitenHalalindia Ecodesdhir.ankurNoch keine Bewertungen
- QMR Q F PR03 001 Job Description MatrixDokument1 SeiteQMR Q F PR03 001 Job Description Matrixdhir.ankurNoch keine Bewertungen
- Application Form HALALDokument4 SeitenApplication Form HALALdhir.ankurNoch keine Bewertungen
- Business Ethics in India PerspectiveDokument7 SeitenBusiness Ethics in India PerspectiveniviNoch keine Bewertungen
- Pharma News 27 June 2022 PDF-1Dokument13 SeitenPharma News 27 June 2022 PDF-1dhir.ankurNoch keine Bewertungen
- Process FlowDokument1 SeiteProcess Flowdhir.ankurNoch keine Bewertungen
- Checklist MDRDokument162 SeitenChecklist MDRdhir.ankurNoch keine Bewertungen
- Ananya Consultants Application FormDokument2 SeitenAnanya Consultants Application Formdhir.ankurNoch keine Bewertungen
- Iso37001 Implementation Guide en MyDokument12 SeitenIso37001 Implementation Guide en MylovishNoch keine Bewertungen
- Flowchart For Reporting Ethics IssuesDokument1 SeiteFlowchart For Reporting Ethics Issuesdhir.ankurNoch keine Bewertungen
- Key Ethical PrinciplesDokument2 SeitenKey Ethical Principlesdhir.ankurNoch keine Bewertungen
- Asq Presentation Iso 13485Dokument48 SeitenAsq Presentation Iso 13485dhir.ankur100% (1)
- Declaration of Conformity MDD Class IDokument2 SeitenDeclaration of Conformity MDD Class Idhir.ankurNoch keine Bewertungen
- EthicsPolicy SampleTemplateDokument4 SeitenEthicsPolicy SampleTemplatedhir.ankurNoch keine Bewertungen
- Bsi MD Risk Management For Medical Devices QaDokument10 SeitenBsi MD Risk Management For Medical Devices Qadhir.ankurNoch keine Bewertungen
- MDR Classification DocumentDokument17 SeitenMDR Classification Documentdhir.ankurNoch keine Bewertungen
- QCI AIMED Certification ProcessDokument14 SeitenQCI AIMED Certification ProcessAnkurNoch keine Bewertungen
- MDD Classification Document: Mapping of RequirementsDokument12 SeitenMDD Classification Document: Mapping of Requirementsdhir.ankurNoch keine Bewertungen
- What Is APQPDokument2 SeitenWhat Is APQPshanramaNoch keine Bewertungen
- Embedded C Programming, Linux, and Vxworks.: SynopsisDokument5 SeitenEmbedded C Programming, Linux, and Vxworks.: SynopsisSwarna Sekhar Dhar100% (1)
- Support LogDokument55 SeitenSupport LogБарба РискаNoch keine Bewertungen
- TFS Main ConceptsDokument7 SeitenTFS Main ConceptspatriciachfNoch keine Bewertungen
- Delta To Wye and V.VDokument4 SeitenDelta To Wye and V.VAiza CabolesNoch keine Bewertungen
- Resueltos AmortizadoDokument3 SeitenResueltos Amortizadopepito11111Noch keine Bewertungen
- AVR USBasp Users Manual PDFDokument30 SeitenAVR USBasp Users Manual PDFxem3Noch keine Bewertungen
- 8086 Case StudiesDokument4 Seiten8086 Case StudiesSunil Kumar100% (1)
- DifferenceDokument2 SeitenDifferenceTeresa Carter100% (1)
- Introduction To Codesign Do It Twice!: Max KleinerDokument12 SeitenIntroduction To Codesign Do It Twice!: Max KleinerMax KleinerNoch keine Bewertungen
- Legacy System Migration WorkbenchDokument16 SeitenLegacy System Migration WorkbenchDINESH SINGH BHATINoch keine Bewertungen
- Python Programs ListDokument12 SeitenPython Programs ListDevendra Singh RautelaNoch keine Bewertungen
- 02 Courier System ManagementDokument49 Seiten02 Courier System Managementranahamid007100% (3)
- Simulation of Non-Preemptive SJF CPU Scheduling AlgorithmDokument51 SeitenSimulation of Non-Preemptive SJF CPU Scheduling Algorithmresearch n technologyNoch keine Bewertungen
- SAP 129 Navigation PDFDokument6 SeitenSAP 129 Navigation PDFshakeelNoch keine Bewertungen
- ReadmeDokument2 SeitenReadmeeNoch keine Bewertungen
- Enter Service Mode SMCS-5000 Operator MonitorDokument8 SeitenEnter Service Mode SMCS-5000 Operator MonitormetanirvanaNoch keine Bewertungen
- 12.2 InstallDokument4 Seiten12.2 InstallMohamedAbdElaalNoch keine Bewertungen
- MasterCard Data Scientist Amudhan VenkatesanDokument6 SeitenMasterCard Data Scientist Amudhan Venkatesanramesh158Noch keine Bewertungen
- Project Computer GraphicsDokument18 SeitenProject Computer Graphicsvaku0% (2)
- Cuda PDFDokument18 SeitenCuda PDFXemenNoch keine Bewertungen
- BGP Regular ExpressionDokument6 SeitenBGP Regular Expressionneal_121187Noch keine Bewertungen
- LSMW BPDokument23 SeitenLSMW BPZacha ArvizuNoch keine Bewertungen
- Data Center Visualization With VisioDokument13 SeitenData Center Visualization With VisioNil PawarNoch keine Bewertungen
- Voice Activated Traffic Management System Using Apr 9600 Based On Embedded SystemDokument7 SeitenVoice Activated Traffic Management System Using Apr 9600 Based On Embedded SystemInternational Journal of Scientific Research and Engineering StudiesNoch keine Bewertungen
- FBW1102 enDokument603 SeitenFBW1102 enPaulNoch keine Bewertungen
- Basic Difference Between Server and Parallel JobsDokument2 SeitenBasic Difference Between Server and Parallel JobsAAKBAR99Noch keine Bewertungen
- EX200 - Red Hat Certified System Administrator (RHCSA) ExamDokument4 SeitenEX200 - Red Hat Certified System Administrator (RHCSA) ExamABDQ0% (1)
- infoPLC Net 68011496 HTML Basics For Simatic Cpus en PDFDokument42 SeiteninfoPLC Net 68011496 HTML Basics For Simatic Cpus en PDFrosemberg_trujilloNoch keine Bewertungen
- 105 - Installing OpenCVDokument3 Seiten105 - Installing OpenCVjdNoch keine Bewertungen
- Sun HostidDokument1 SeiteSun HostidDjvionico Perez100% (1)