Beruflich Dokumente
Kultur Dokumente
Scea Books
Hochgeladen von
guntur123Originalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Scea Books
Hochgeladen von
guntur123Copyright:
Verfügbare Formate
Assignment Objectives
Section 1: Application Design Concepts and Principles
Explain the main advantages of an object-oriented approach to system design incl
uding the effect of encapsulation, inheritance, and use of interfaces on archite
ctural characteristics.
Describe how the principle of "separation of concerns" has been applied to the m
ain system tiers of a Java Platform, Enterprise Edition application. Tiers inclu
de client (both GUI and web), web (web container), business (EJB container), int
egration, and resource tiers.
Describe how the principle of "separation of concerns" has been applied to the l
ayers of a Java EE application. Layers include application, virtual platform (co
mponent APIs), application infrastructure (containers), enterprise services (ope
rating system and virtualization), compute and storage, and the networking
infrastructure layers.
Books:
1 Sun Certified Enterprise Architect for J2EE Technology Study Guide,
Mark Cade.
2 "SCEA study guide" - Allen and Bambara
Section 2: Common Architectures
Explain the advantages and disadvantages of two-tier architectures when examined
under the following topics: scalability, maintainability, reliability, availabi
lity, extensibility, performance, manageability, and security.
Explain the advantages and disadvantages of three-tier architectures when examin
ed under the following topics: scalability, maintainability, reliability, availa
bility, extensibility, performance, manageability, and security
Explain the advantages and disadvantages of multi-tier architectures when examin
ed under the following topics: scalability, maintainability, reliability, availa
bility, extensibility, performance, manageability, and security.
Explain the benefits and drawbacks of rich clients and browser-based clients as
deployed in a typical Java EE application.
Explain appropriate and inappropriate uses for web services in the Java EE platf
orm
Books:
1 Designing Enterprise Applications with the J2EE Platform
2 J2EE Architect's Handbook
Section 3: Integration and Messaging
Explain possible approaches for communicating with an external system from a Jav
a EE technology-based system given an outline description of those systems and o
utline the benefits and drawbacks of each approach.
Explain typical uses of web services and XML over HTTP as mechanisms to integrat
e distinct software components.
Explain how JCA and JMS are used to integrate distinct software components as pa
rt of an overall Java EE application.
Books:
1 Java EE 5 Tutorial. Part VI Services.
2 Enterprise Integration Patterns: Designing, Building, and Deploying Messaging
Solutions
3 J2EE Connector Architecture and Enterprise Application Integration
4 Java Message Service, Monson-Haefel & Chappell
Section 4: Business Tier Technologies
Explain and contrast uses for entity beans, entity classes, stateful and statele
ss session beans, and message-driven beans, and understand the advantages and di
sadvantages of each type.
Explain and contrast the following persistence strategies: container-managed per
sistence (CMP) BMP, JDO, JPA, ORM and using DAOs (Data Access Objects) and direc
t JDBC technology-based persistence under the following headings: ease of develo
pment, performance, scalability, extensibility, and security.
Explain how Java EE supports the deployment of server-side components implemente
d as web services and the advantages and disadvantages of adopting such an appro
ach.
Explain the benefits of the EJB 3 development model over previous EJB generation
s for ease of development including how the EJB container simplifies EJB develop
ment.
Books:
1 EJB 3 in Action
2 Pro EJB 3 Java Persistence API
3 Mastering EJB 3.0
4 Java EE 5 Tutorial. Part IV Enterprise Beans.
5 Java EE 5 Tutorial. Part V Persistence.
6 Nice to have SCBCD 5
Section 5: Web Tier Technologies
State the benefits and drawbacks of adopting a web framework in designing a Java
EE application
Explain standard uses for JSP pages and servlets in a typical Java EE applicatio
n.
Explain standard uses for JavaServer Faces components in a typical Java EE appli
cation.
Given a system requirements definition, explain and justify your rationale for c
hoosing a web-centric or EJB-centric implementation to solve the requirements. W
eb-centric means that you are providing a solution that does not use EJB compone
nts. EJB-centric solution will require an application server that supports EJB c
omponents.
Books:
1 Core JavaServer? Faces, Second Edition
2 Java EE 5 Tutorial. Part II The Web Tier.
3 Nice to have SCWCD
Section 6: Applicability of Java EE Technology
Given a specified business problem, design a modular solution that solves the pr
oblem using Java EE.
Explain how the Java EE platform enables service oriented architecture (SOA) -ba
sed applications.
Explain how you would design a Java EE application to repeatedly measure critica
l non-functional requirements and outline a standard process with specific strat
egies to refactor that application to improve on the results of the measurements
.
Books:
1 Java EE 5 Tutorial. Part VII Case Studies.
2 Practical J2EE Application Architecture
3 J2EE AntiPatterns?
4 Java EE 5 Tutorial. Part III Web Services.
5 SOA using Java Web services
Section 7: Patterns
From a list, select the most appropriate pattern for a given scenario. Patterns
are limited to those documented in the book - Alur, Crupi and Malks (2003). Core
J2EE Patterns: Best Practices and Design Strategies 2nd Edition and named using
the names given in that book.
From a list, select the most appropriate pattern for a given scenario. Patterns
are limited to those documented in the book - Gamma, Erich; Richard Helm, Ralph
Johnson, and John Vlissides (1995). Design Patterns: Elements of Reusable Object
-Oriented Software and are named using the names given in that book.
From a list, select the benefits and drawbacks of a pattern drawn from the book
- Gamma, Erich; Richard Helm, Ralph Johnson, and John Vlissides (1995). Design P
atterns: Elements of Reusable Object-Oriented Software.
From a list, select the benefits and drawbacks of a specified Core J2EE pattern
drawn from the book Alur, Crupi and Malks (2003). Core J2EE Patterns: Best Pract
ices and Design Strategies 2nd Edition.
Books:
1 "Design Patterns", GoF
2 Core J2EE Patterns, 2nd ed.
3 Head First Design Patterns
Section 8: Security
Explain the client-side security model for the Java SE environment, including th
e Web Start and applet deployment modes.
Given an architectural system specification, select appropriate locations for im
plementation of specified security features, and select suitable technologies fo
r implementation of those features
Identify and classify potential threats to a system and describe how a given arc
hitecture will address the threats.
Describe the commonly used declarative and programmatic methods used to secure a
pplications built on the Java EE platform, for example use of deployment descrip
tors and JAAS.
Books:
1 Java EE 5 Tutorial. Part VI Services.
2 Java Security
3 Core Security Patterns
4 Sun JEE tutorial
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5795)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- Proficient Test2 Units3and4Dokument4 SeitenProficient Test2 Units3and4ana maria csalinas100% (2)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Administrator GuideDokument110 SeitenAdministrator Guidefrontize resourcesNoch keine Bewertungen
- Company Sim Card Authorization Letter CompleteDokument1 SeiteCompany Sim Card Authorization Letter CompleteLoGan Ben100% (5)
- Performance Evaluation of CDMA Router For Network-On-ChipDokument11 SeitenPerformance Evaluation of CDMA Router For Network-On-ChipAnonymous e4UpOQEPNoch keine Bewertungen
- ATN Full Site Script U4324Dokument2 SeitenATN Full Site Script U4324Heather WallaceNoch keine Bewertungen
- Addis Zemen NewDokument11 SeitenAddis Zemen Newtadele kassawNoch keine Bewertungen
- H80BVDPE Board DatasheetDokument1 SeiteH80BVDPE Board DatasheetGreg MorrisNoch keine Bewertungen
- The Internet, The Web and Electronic CommerceDokument16 SeitenThe Internet, The Web and Electronic CommerceBea BonitaNoch keine Bewertungen
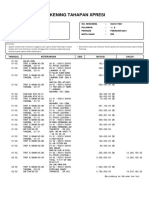
- Rekening Tahapan Xpresi: No. Rekening: 0541317821 Halaman: Periode: Februari 2021 Mata Uang: IDRDokument6 SeitenRekening Tahapan Xpresi: No. Rekening: 0541317821 Halaman: Periode: Februari 2021 Mata Uang: IDRRifaLutfiHabibiNoch keine Bewertungen
- Jignesh Badani 2022Dokument8 SeitenJignesh Badani 2022Satish Kumar SinhaNoch keine Bewertungen
- Pass Microsoft 98-366 Exam With 100% Guarantee: MTA Networking FundamentalsDokument6 SeitenPass Microsoft 98-366 Exam With 100% Guarantee: MTA Networking FundamentalsFeryo PermanaNoch keine Bewertungen
- Forum Sentry: Deployment Architecture ConceptsDokument10 SeitenForum Sentry: Deployment Architecture ConceptsKay AdeNoch keine Bewertungen
- 560CID11 Product InfoDokument2 Seiten560CID11 Product InfoGilbert H. Quiroga G.Noch keine Bewertungen
- Vol 14 No 2 - September 2014Dokument149 SeitenVol 14 No 2 - September 2014ijcsbiNoch keine Bewertungen
- La A972p PDFDokument51 SeitenLa A972p PDFnicolae7887169Noch keine Bewertungen
- 4146 NCB C6ugryr 305Dokument1 Seite4146 NCB C6ugryr 305Samastha Nair SamajamNoch keine Bewertungen
- ISU Master Data TemplateDokument7 SeitenISU Master Data TemplateAntonio RuizNoch keine Bewertungen
- Function DescriptionDokument9 SeitenFunction DescriptionCENTRAL UNITRACKERNoch keine Bewertungen
- Webshere Notes1Dokument76 SeitenWebshere Notes1Abhinav GargNoch keine Bewertungen
- Manual Lenovo ProyektorDokument15 SeitenManual Lenovo ProyektorDiyas AndhikaNoch keine Bewertungen
- Mvs Console CommandsDokument2 SeitenMvs Console Commandscheers_2008Noch keine Bewertungen
- Rj45 Connector 632705 - 0Dokument1 SeiteRj45 Connector 632705 - 0daithedayNoch keine Bewertungen
- Architecture: SAP R/3 Workload AnalysisDokument5 SeitenArchitecture: SAP R/3 Workload AnalysispapusahaNoch keine Bewertungen
- ABDownloader LogsDokument2 SeitenABDownloader LogsRam Eduard OrpillaNoch keine Bewertungen
- Wa0014.Dokument112 SeitenWa0014.Piyush KumarNoch keine Bewertungen
- Question What Is Difference Betwwen RSSI and RSCP (Archive) - Wire Free AllianceDokument2 SeitenQuestion What Is Difference Betwwen RSSI and RSCP (Archive) - Wire Free AllianceMohamedSaidNoch keine Bewertungen
- App Notes HBRDokument37 SeitenApp Notes HBRManoj KumarNoch keine Bewertungen
- Gw1000 ManualDokument51 SeitenGw1000 Manualyounger123456Noch keine Bewertungen
- infoPLC Net IRC5 Connection To S500 IOs Via Profinet PDFDokument28 SeiteninfoPLC Net IRC5 Connection To S500 IOs Via Profinet PDFgapam_2Noch keine Bewertungen
- At Command ZteDokument9 SeitenAt Command ZteMalausma NetNoch keine Bewertungen