Beruflich Dokumente
Kultur Dokumente
Desktop Checklist-End User - 1
Hochgeladen von
Sk Sebatu MelakaOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Desktop Checklist-End User - 1
Hochgeladen von
Sk Sebatu MelakaCopyright:
Verfügbare Formate
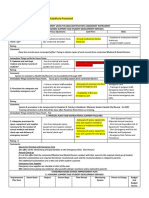
Desktop and Portable Computer Standard
Security Checklist for End-Users
Computer identification and location:
Completed by (please print): _______________________ Date: ______________
Signature: _________________________ Next scheduled review date: ______________
Managers signature: _________________________ Date: ______________
All computers that connect to the RIT network require the following: (5.1) Initials
1. Anti-virus software with updated signatures has been installed and enabled. (5.1.1)
2. All operating system and application security patches are up to date. (5.1.2)
3. Hardware or software that provides memory protection is enabled. F(5.1.3)
4. A personal firewall, software or hardware, is installed and enabled. (5.1.4)
5. Anti-spyware is installed, enabled, and up-to-date. (5.1.5)
6. Is this an RIT-owned or leased laptop? (Y/N) ____________ (5.2.1)
If No, skip to number 11.
7. Have you confirmed with your systems administrator that the laptop has whole-disk encryption (5.2.1)
properly installed and enabled, and that no user-configurable settings are interfering with the
software?
8. The encryption software and its policies are being managed by centralized ISO-approved (5.2.1.3)
security personnel.
9. Laptop is set to hibernate, rather than standby, when inactive for more than 30 minutes. (5.2.1.2.1)
10. The encryption software and its policies are controlled by centralized ISO-approved (5.2.1.3)
security personnel.
11. Is this an RIT-owned or leased desktop computer? (Y/N) ____________
If No, you may skip the remaining items on this checklist.
12. Anti-phishing controls have been installed and enabled. (5.2.3.1)
13. Users are aware that they must not leave their computer unattended without logging off or (5.2.4.1)
locking the computer first.
14. Are administrator privileges being used on this computer? (Y/N) ____________ (5.2.5.1)
If Yes, who is the dean or VP that has authorized the privileges? ___________________________
15. Have you confirmed with your systems administrator that an ISO-approved Host Intrusion (5.2.6.1)
Prevention System is installed and enabled on your machine?
RIT Information Security
infosec@rit.edu
https://www.rit.edu/security
Desktop Checklist-End User a2 1 of 1 revised 5/15/2009
Das könnte Ihnen auch gefallen
- Peraturan Chrome BookDokument1 SeitePeraturan Chrome BookSk Sebatu MelakaNoch keine Bewertungen
- Comprehensive Procurement Procedure Sample 2Dokument63 SeitenComprehensive Procurement Procedure Sample 2Pedro GardnerNoch keine Bewertungen
- ICT Computer Room Policy v1.6Dokument12 SeitenICT Computer Room Policy v1.6Sk Sebatu MelakaNoch keine Bewertungen
- NIST Checklist Developer PDFDokument74 SeitenNIST Checklist Developer PDFSk Sebatu MelakaNoch keine Bewertungen
- Contingency Plan ChecklistDokument1 SeiteContingency Plan ChecklistSk Sebatu MelakaNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (120)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Name Position Time of ArrivalDokument5 SeitenName Position Time of ArrivalRoseanne MateoNoch keine Bewertungen
- WukolumDokument2 SeitenWukolumHammed OkusiNoch keine Bewertungen
- ĐỀ SỐ 6 - KEYDokument6 SeitenĐỀ SỐ 6 - KEYAnh MaiNoch keine Bewertungen
- The Six Day War: Astoneshing Warfear?Dokument3 SeitenThe Six Day War: Astoneshing Warfear?Ruben MunteanuNoch keine Bewertungen
- Ermitage Academic Calendar IBP 2022-23Dokument1 SeiteErmitage Academic Calendar IBP 2022-23NADIA ELWARDINoch keine Bewertungen
- Professionals and Practitioners in Counselling: 1. Roles, Functions, and Competencies of CounselorsDokument70 SeitenProfessionals and Practitioners in Counselling: 1. Roles, Functions, and Competencies of CounselorsShyra PapaNoch keine Bewertungen
- Agrarian DisputesDokument15 SeitenAgrarian DisputesBryle Keith TamposNoch keine Bewertungen
- Color Code Look For Complied With ECE Look For With Partial Compliance, ECE Substitute Presented Look For Not CompliedDokument2 SeitenColor Code Look For Complied With ECE Look For With Partial Compliance, ECE Substitute Presented Look For Not CompliedMelanie Nina ClareteNoch keine Bewertungen
- Hho Dry DiagramDokument7 SeitenHho Dry Diagramdesertbloom100% (2)
- Jo LibbeDokument4 SeitenJo LibbejacNoch keine Bewertungen
- BARD 2014 Product List S120082 Rev2Dokument118 SeitenBARD 2014 Product List S120082 Rev2kamal AdhikariNoch keine Bewertungen
- CLP v2.0 - Session 8 Transformation in ChristDokument7 SeitenCLP v2.0 - Session 8 Transformation in Christarcee alcedo100% (2)
- Division of Pagadian City Zamboanga Del Sur National High SchooolDokument3 SeitenDivision of Pagadian City Zamboanga Del Sur National High SchooolMyra KadatuanNoch keine Bewertungen
- Fashion OrientationDokument7 SeitenFashion OrientationRAHUL16398Noch keine Bewertungen
- Soal SemesterDokument5 SeitenSoal SemesterWayan HamalNoch keine Bewertungen
- State of Cyber-Security in IndonesiaDokument32 SeitenState of Cyber-Security in IndonesiaharisNoch keine Bewertungen
- Ephesians 5.32-33Dokument2 SeitenEphesians 5.32-33Blaine RogersNoch keine Bewertungen
- The City Bride (1696) or The Merry Cuckold by Harris, JosephDokument66 SeitenThe City Bride (1696) or The Merry Cuckold by Harris, JosephGutenberg.org100% (2)
- 02-7 QCS 2014Dokument5 Seiten02-7 QCS 2014Raja Ahmed Hassan0% (1)
- PolinationDokument22 SeitenPolinationBala SivaNoch keine Bewertungen
- Ordnance Survey Business Portfolio Price ListDokument24 SeitenOrdnance Survey Business Portfolio Price ListjoebrickleyNoch keine Bewertungen
- User Guide: How To Register & Verify Your Free Paxum Personal AccountDokument17 SeitenUser Guide: How To Register & Verify Your Free Paxum Personal AccountJose Manuel Piña BarriosNoch keine Bewertungen
- Tata Contact UsDokument9 SeitenTata Contact UsS K SinghNoch keine Bewertungen
- "Ako Ang Daigdig" by Alejandro Abadilla: An AnalysisDokument3 Seiten"Ako Ang Daigdig" by Alejandro Abadilla: An AnalysisJog YapNoch keine Bewertungen
- Case Study of Asahi Glass CompanyDokument22 SeitenCase Study of Asahi Glass CompanyJohan ManurungNoch keine Bewertungen
- 08 - Case Law-Unknown Case Law ListDokument28 Seiten08 - Case Law-Unknown Case Law ListNausheen100% (1)
- Axess Group - Brazilian ComplianceDokument1 SeiteAxess Group - Brazilian ComplianceRicardoNoch keine Bewertungen
- The Game of KevukDokument8 SeitenThe Game of KevukTselin NyaiNoch keine Bewertungen
- Stamp Duty (Amendment) Act, 2022Dokument5 SeitenStamp Duty (Amendment) Act, 2022Kirunda ramadhanNoch keine Bewertungen
- Cement SegmentDokument18 SeitenCement Segmentmanish1895Noch keine Bewertungen