Beruflich Dokumente
Kultur Dokumente
Chapter 3 Ais
Hochgeladen von
May Anne Nanglegan0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
16 Ansichten6 SeitenA
Copyright
© © All Rights Reserved
Verfügbare Formate
DOCX, PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenA
Copyright:
© All Rights Reserved
Verfügbare Formate
Als DOCX, PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
16 Ansichten6 SeitenChapter 3 Ais
Hochgeladen von
May Anne NangleganA
Copyright:
© All Rights Reserved
Verfügbare Formate
Als DOCX, PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 6
Group 3
ETHICS, FRAUD and
INTERNAL CONTROL
SUMMARY OF CHAPTER 3
CHAPTER 03 2. The benefits of the decision should be distributed fairly
Ethics, Fraud, and Internal Control to those who share the risks. Those who do not benefit
should not carry the burden of risk.
I. ETHICS 3. Even if judged acceptable by the principles, the decision
should be implemented so as to minimize all of the risks
ETHICAL STANDARDS are derived from societal mores and deep- and avoid any unnecessary risks.
rooted personal beliefs about issues of right and wrong that are
not universally agreed upon. COMPUTER ETHICS is theanalysis of the nature and social
impact of computer technology and the corresponding
ETHICS pertains to the principles of conduct that individuals use formulation and justification of policies for the ethical use of
in making choices and guiding their behavior in situations that such technology.
involve the concepts of right and wrong.
THREE LEVELS OF COMPUTER ETHICS
BUSINESS ETHICS involves finding the answers to two questions: 1. Pop Computer Ethics is simply the exposure to stories
(1) How do managers decide what is right in conducting their and reports found in the popular media regarding the
business? good or bad ramifications of computer technology.
(2) Once managers have recognized what is right, how do they 2. Para Computer Ethics involves taking a real interest in
achieve it? computer ethics cases and acquiring some level of skill
and knowledge in the field
BUSINESS ETHICAL ISSUES can be divided into four areas: equity, 3. Theoretical Computer Ethics is of interest to
rights, honesty, and the exercise of corporate power. multidisciplinary researchers who apply the theories of
philosophy, sociology, and psychology to computer
1. EQUITY science with the goal of bringing some new
Executive Salaries understanding to the field.
Comparable Worth
Product Pricing COMPUTER ETHICAL ISSUES
2. RIGHTS 1. PRIVACY. People desire to be in full control of what and
Corporate Due Process how much information about themselves is available to
Employee Health Screening others, and to whom it is available.
Employee Privacy 2. SECURITY . Is an attempt to avoid such undesirable
Sexual Harassment events as a loss of confidentiality or data integrity.
Diversity Equal Employment Opportunity 3. OWNERSHIP OF PROPERTY LAWS . Designed to
Whistle-Blowing preserve real property rights have been extended to
3. HONESTY cover what is referred to as intellectual property, that is,
Employee and Management Conflicts of software.
Interest 4. EQUITY IN ACCESS . Some barriers to access are intrinsic
Security of Organization Data and Records to the technology of information systems, but some are
Misleading Advertising avoidable through careful system design.
Questionable Business Practices in Foreign 5. ENVIRONMENTAL ISSUES. Computers with high-speed
Countries printers allow for the production of printed documents
Accurate Reporting of Shareholder Interests faster than ever before and organizations should limit
4. EXERCISE OF CORPORATE POWER nonessential hard copies.
Political Action Committees 6. ARTIFICIAL INTELLIGENCE . A new set of social and
Workplace Safety ethical issues has arisen out of the popularity of expert
Product Safety systems.
Environmental Issues 7. UNEMPLOYMENT AND DISPLACEMENT . Many jobs
Divestment of Interests have been and are being changed as a result of the
Corporate Political Contributions availability of computer technology. People unable or
Downsizing and Plant Closures unprepared to change are displaced.
8. MISUSE OF COMPUTERS . Computers can be misused in
MAKING ETHICAL DECISIONS many ways. Copying proprietary software, using a
Business organizations have conflicting responsibilities companys computer for personal benefit, and snooping
to their employees, shareholders, customers, and the through other peoples files are just a few obvious
public. Every major decision has consequences that examples.
potentially harm or benefit these constituents. Seeking
a balance between these consequences is the managers SARBANES-OXLEY ACT AND ETHICAL ISSUES
ethical responsibility. Sarbanes-Oxley Act (SOX), is the most significant securities law
since the Securities and Exchange Commission (SEC) Acts of 1933
ETHICAL PRINCIPLES that provide some guidance in the and 1934.
discharge of Managers Ethical Responsibility
1. The benefit from a decision must outweigh the risks.
Section 406 of SOX requires public companies to disclose to the 1. The fraud is perpetrated at levels of
SEC whether they have adopted a code of ethics that applies to management above the one to which internal
the organizations chief executive officer (CEO), CFO, controller, control structures generally relate.
or persons performing similar functions. 2. The fraud frequently involves using the financial
statements to create an illusion that an entity is
1. CONFLICTS OF INTEREST. The companys code of ethics healthier and more prosperous.
should outline procedures for dealing with actual or 3. If the fraud involves misappropriation of assets,
apparent conflicts of interest between personal and it frequently is shrouded in a maze of complex
professional relationships. business transactions, often involving related third
2. FULL AND FAIR DISCLOSURES. This provision states that parties.
the organization should provide full, fair, accurate,
timely, and understandable disclosures in the THE FRAUD TRIANGLE
documents, reports, and financial statements that it Fraud Triangle consists of three factors that contribute to or are
submits to the SEC and to the public. associated with management and employee fraud.
3. LEGAL COMPLIANCE. Codes of ethics should require 1. Situational Pressure, which includes personal or job-
employees to follow applicable governmental laws, related stresses that could coerce an individual to act
rules, and regulations. dishonestly
4. INTERNAL REPORTING OF CODE VIOLATIONS. The code 2. Opportunity, which involves direct access to assets
of ethics must provide a mechanism to permit prompt and/or access to information that controls assets
internal reporting of ethics violations. 3. Ethics, which pertains to ones character and degree of
5. ACCOUNTABILITY. An effective ethics program must moral opposition to acts of dishonesty.
take appropriate action when code violations occur.
II. FRAUD
FRAUD denotes a false representation of a material fact
made by one party to another party with the intent to
deceive and induce the other party to justifiably rely on the
fact to his or her detriment.
According to common law, a fraudulent act must meet the
following five conditions:
1. FALSE REPRESENTATION. There must be a false
statement or a nondisclosure.
2. MATERIAL FACT. A fact must be a substantial factor in
inducing someone to act.
3. INTENT. There must be the intent to deceive or the
knowledge that ones statement is false.
4. JUSTIFIABLE RELIANCE. The misrepresentation must have
been a substantial factor on which the injured party relied.
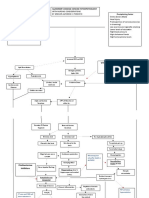
5. INJURY OR LOSS. The deception must have caused injury Figure 3-1 graphically depicts the interplay among these three
or loss to the victim of the fraud. forces. The figure suggests that an individual with a high level of
personal ethics, who is confronted by low pressure and limited
In accounting, fraud is also commonly known as White- opportunity to commit fraud, is more likely to behave honestly
Collar Crime, Defalcation, Embezzlement, And than one with weaker personal ethics, who is under high
Irregularities. pressure and exposed to greater fraud opportunities.
AUDITORS ENCOUNTER FRAUD AT TWO LEVELS: FRAUD SCHEMES
1. EMPLOYEE FRAUD, or fraud by nonmanagement FRAUD SCHEMES can be classified in a number of different
employees, is generally designed to directly convert ways. Three broad categories of fraud schemes are defined:
cash or other assets to the employees personal benefit. Fraudulent Statements, Corruption, And Asset Misappropriation.
2. MANAGEMENT FRAUD ,is more insidious than
employee fraud because it often escapes detection until 1. FRAUDULENT STATEMENTS are associated with
the organization has suffered irreparable damage or management fraud. Whereas all fraud involves some
loss. Management fraud usually does not involve the form of financial misstatement, to meet the definition
direct theft of assets. under this class of fraud scheme the statement itself
must bring direct or indirect financial benefit to the
Management fraud typically contains three special perpetrator.
characteristics:
2. CORRUPTION involves an executive, manager, or III. INTERNAL CONTROL CONCEPTS AND
employee of the organization in collusion with an TECHNIQUES
outsider.
Internal Control System comprises policies, practices, and
four principal types of corruption:
procedures employed by the organization to achieve four broad
objectives:
A. BRIBERY, involves giving, offering, soliciting, or 1. To safeguard assets of the firm.
receiving things of value to influence an official in 2. To ensure the accuracy and reliability of accounting
the performance of his or her lawful duties. records and information.
B. ILLEGAL GRATUITIES, involves giving, receiving, 3. To promote efficiency in the firms operations.
offering, or soliciting something of value because of 4. To measure compliance with managements prescribed
an official act that has been taken. policies and procedures.
C. CONFLICTS OF INTEREST, occurs when an employee
acts on behalf of a third party during the discharge LIMITATIONS OF INTERNAL CONTROL ON ITS
of his or her duties or has self-interest in the activity EFFECTIVENESS.
being performed.
A.) the possibility of errorno system is perfect,
D. ECONOMIC EXTORTION, is the use (or threat) of
B.) circumventionpersonnel may circumvent the
force (including economic sanctions) by an
system through collusion or other means,
individual or organization to obtain something of
C.) management overridemanagement is in a
value.
position to override control procedures by
personally distorting transactions or by directing a
3.ASSET MISAPPROPRIATION in which assets are either
subordinate to do
directly or indirectly diverted to the perpetrators
benefit. D.) Changing conditionsconditions may change over
Skimming involves stealing cash from an organization time so that existing controls may become
before it is recorded on the organizations books and ineffectual.
records. One example of skimming is an employee who E.)
accepts payment from a customer but does not record The PreventiveDetectiveCorrective Internal Control Model
the sale.
Cash larceny involves schemes in which cash receipts PREVENTIVE CONTROLS
are stolen from an organization after they have been are passive techniques designed to reduce the
recorded in the organizations books and records. frequency of occurrence of undesirable events.
force compliance with prescribed or desired actions
OTHER FRAUDELENT ACTS and thus screen out aberrant events.
when designing internal control systems, an ounce of
1. Billing schemes, also known as vendor fraud, are prevention is most certainly worth a pound of cure.
perpetrated by employees who cause their employer to
issue a payment to a false supplier or vendor by DETECTIVE CONTROLS
submitting invoices for fictitious goods or services, form the second line of defense.
inflated invoices, or invoices for personal purchases. These are devices, techniques, and procedures designed
2. Check tampering involves forging or changing in some to identify and expose undesirable events that elude
material way a check that the organization has written preventive controls.
to a legitimate payee. Detective controls reveal specific types of errors by
3. Payroll fraud is the distribution of fraudulent paychecks comparing actual occurrences to pre-established
to existent and/or nonexistent employees. For example, standards.
a supervisor keeps an employee on the payroll who has
left the organization. CORRECTIVE CONTROLS
4. Expense reimbursement frauds are schemes in which are actions taken to reverse the effects of errors
an employee makes a claim for reimbursement of detected in the previous step.
fictitious or inflated business expenses. Thefts of cash There is an important distinction between detective
are schemes that involve the direct theft of cash on controls and corrective controls.
hand in the organization Detective controls identify anomalies and draw
5. Non-cash fraud schemes involve the theft or misuse of attention to them.
the victim organizations non-cash assets. corrective controls actually fix the problem.
d. Significant and rapid growth that strains existing internal
controls.
e. The implementation of new technology into the
production process or information system that impacts
transaction processing.
f. The introduction of new product lines or activities with
which the organization has little experience.
g. Organizational restructuring resulting in the reduction
and/or reallocation of personnel such that business
operations and transaction processing are affected.
h. Entering into foreign markets that may impact
operations (that is, the risks associated with foreign
currency transactions).
i. Adoption of a new accounting principle that impacts the
preparation of financial statements.
3. INFORMATION AND COMMUNICATION. The
accounting information system consists of the
records and methods used to initiate, identify,
Figure 3-3 illustrates that the internal control shield is composed analyze, classify, and record the organizations
of three levels of control: preventive controls, detective controls, transactions and to account for the related assets
and corrective controls. This is the preventivedetective and liabilities.
corrective (PDC) control model.
AN EFFECTIVE ACCOUNTING INFORMATION SYSTEM WILL:
SAS 78/COSO INTERNAL CONTROL FRAMEWORK a. Identify and record all valid financial transactions.
b. Provide timely information about transactions in
The SAS 78/COSO framework consists of five components: the sufficient detail to permit proper classification and
control environment, risk assessment, information and financial reporting.
communication, monitoring, and control activities. c. Accurately measure the financial value of transactions
1. CONTROL ENVIRONMENT is the foundation for the so their effects can be recorded in financial statements.
other four control components. The control d. Accurately record transactions in the time period in
environment sets the tone for the organization and which they occurred.
influences the control awareness of its e. SAS 78/COSO requires that auditors obtain sufficient
management and employees. knowledge of the organizations information system to
understand
IMPORTANT ELEMENTS OF THE CONTROL ENVIRONMENT f. The classes of transactions that are material to the
a. The integrity and ethical values of management. financial statements and how those transactions are
b. The structure of the organization. initiated.
c. The participation of the organizations board of g. The accounting records and accounts that are used in
directors and the audit committee, if one exists. the processing of material transactions. The transaction
d. Managements philosophy and operating style. processing steps involved from the initiation of a
e. The procedures for delegating responsibility and transaction to its inclusion in the financial statements.
authority. The financial reporting process used to prepare financial
f. Managements methods for assessing performance. statements, disclosures, and accounting estimates.
g. External influences, such as examinations by regulatory
agencies.
h. The organizations policies and practices for managing 4. MONITORING is the process by which the quality of
its human resources. internal control design and operation can be
assessed. This may be accomplished by separate
procedures or by ongoing activities.
2. Organizations must perform a RISK ASSESSMENT to
identify, analyze, and manage risks relevant to
financial reporting. 5. CONTROL ACTIVITIES are the policies and
procedures used to ensure that appropriate actions
RISKS CAN ARISE OR CHANGE FROM CIRCUMSTANCES SUCH AS: are taken to deal with the organizations identified
a. Changes in the operating environment that impose new risks. Control activities can be grouped into two
or changed competitive pressures on the firm. distinct categories: information technology (IT)
b. New personnel who have a different or inadequate controls and physical controls.
understanding of internal control.
c. New or reengineered information systems that affect
transaction processing.
Control activities can be grouped into two distinct categories: 4. Accounting Records of an organization consist of source
documents, journals, and ledgers. These records capture
1. IT CONTROLS - relate specifically to the computer the economic essence of transactions and provide an
environment. audit trail of economic events.
They fall into two broad groups: 5. Access Controls is to ensure that only authorized
a. General controls pertain to entity-wide concerns such as personnel have access to the firms assets.
controls over the data center, organization databases, Unauthorized access exposes assets to
systems development, and program maintenance. misappropriation, damage, and theft.
b. Application controls ensure the integrity of specific systems 6. Verification procedures are independent checks of the
such as sales order processing, accounts payable, and accounting system to identify errors and
payroll applications. misrepresentations. Verification differs from supervision
because it takes place after the fact, by an individual
2. PHYSICAL CONTROLS. who is not directly involved with the transaction or task
This class of controls relates primarily to the being verified.
human activities employed in accounting systems. Through independent verification procedures,
These activities may be purely manual, such as the management can assess;
physical custody of assets, or they may involve the 1. The performance of individuals.
physical use of computers to record transactions 2. the integrity of the transaction processing system.
or update accounts. 3. the correctness of data contained in accounting
Physical controls do not relate to the computer records.
logic that actually performs accounting tasks.
SIX CATEGORIES OF PHYSICAL CONTROL ACTIVITIES
1. Transaction Authorization is to ensure that all material
transactions processed by the information system are
valid and in accordance with managements objectives.
Authorizations may be general or specific.
2. Segregation of duties can take many forms, depending
on the specific duties to be controlled.
THREE OBJECTIVES segregation of duties
The segregation of duties should be such that the
authorization for a transaction is separate from the
processing of the transaction
Responsibility for the custody of assets should be
separate from the record-keeping responsibility.
The organization should be structured so that a
successful fraud requires collusion between two or
more individuals with incompatible responsibilities
3. In small organizations or in functional areas that lack
sufficient personnel, management must compensate for
the absence of segregation controls with close
supervision. For this reason, supervision is often called a
compensating control.
Das könnte Ihnen auch gefallen
- The Awesome Notes Tax On RC, NRC, RaDokument8 SeitenThe Awesome Notes Tax On RC, NRC, RaMay Anne NangleganNoch keine Bewertungen
- ICPAStudyCalendar 2017 To 2018 ZZZZZDokument6 SeitenICPAStudyCalendar 2017 To 2018 ZZZZZkirigaya kazutoNoch keine Bewertungen
- New Boa Syllabus - Financial Accounting & ReportingDokument3 SeitenNew Boa Syllabus - Financial Accounting & ReportingVoltairePeraltaNoch keine Bewertungen
- BAKELS BAKING POWDER Product SpecificationDokument1 SeiteBAKELS BAKING POWDER Product SpecificationMay Anne NangleganNoch keine Bewertungen
- BOA Syllabus MASDokument3 SeitenBOA Syllabus MASElizabeth YgotNoch keine Bewertungen
- AccDokument4 SeitenAccMay Anne NangleganNoch keine Bewertungen
- The Balanced Scorecard at Philips ElectronicsDokument5 SeitenThe Balanced Scorecard at Philips ElectronicsAudrius MiknevičiusNoch keine Bewertungen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5783)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (890)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (72)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Ethics: Foundations of Moral ValuationDokument7 SeitenEthics: Foundations of Moral ValuationCyril ColladoNoch keine Bewertungen
- Biblical Interpretation in 1 Maccabees: The Anachronism of A "Bible" For The Second-Temple PeriodDokument26 SeitenBiblical Interpretation in 1 Maccabees: The Anachronism of A "Bible" For The Second-Temple PeriodshmareparksNoch keine Bewertungen
- John 1.1 (106 Traduções) PDFDokument112 SeitenJohn 1.1 (106 Traduções) PDFTayna Vilela100% (1)
- Amdocs FSDokument4 SeitenAmdocs FSlionrudrams81Noch keine Bewertungen
- OAU004301 UMG8900 Data Configuration and Routine Maintenance R003 ISSUE2!0!20050622Dokument56 SeitenOAU004301 UMG8900 Data Configuration and Routine Maintenance R003 ISSUE2!0!20050622firas1976Noch keine Bewertungen
- Chapter 4 Moral Principle 1Dokument24 SeitenChapter 4 Moral Principle 1Jerald Cernechez CerezaNoch keine Bewertungen
- DNV RP H101 - Risk Management in Marine and Subsea OperationsDokument54 SeitenDNV RP H101 - Risk Management in Marine and Subsea Operationsk-2100% (1)
- Chapter 17. Bothriocephalus Acheilognathi Yamaguti, 1934: December 2012Dokument16 SeitenChapter 17. Bothriocephalus Acheilognathi Yamaguti, 1934: December 2012Igor YuskivNoch keine Bewertungen
- Sea Creatures List, Prices, Shadow Sizes, and Times ACNH - Animal Crossing New Horizons (Switch) Game8Dokument1 SeiteSea Creatures List, Prices, Shadow Sizes, and Times ACNH - Animal Crossing New Horizons (Switch) Game8botonlouietNoch keine Bewertungen
- PROACTIVITYDokument8 SeitenPROACTIVITYShikhaDabralNoch keine Bewertungen
- Cooking Taoshobuddha Way Volume 2Dokument259 SeitenCooking Taoshobuddha Way Volume 2Taoshobuddha100% (3)
- Entrepreneurial Mindset and Opportunity RecognitionDokument4 SeitenEntrepreneurial Mindset and Opportunity RecognitionDevin RegalaNoch keine Bewertungen
- Being As Presence, Systemic ConsiderationsDokument34 SeitenBeing As Presence, Systemic ConsiderationsJuan ortizNoch keine Bewertungen
- Anaphylactic ShockDokument19 SeitenAnaphylactic ShockrutiranNoch keine Bewertungen
- Semester 1 FinalDokument29 SeitenSemester 1 FinalBudi NugrohoNoch keine Bewertungen
- Ajzen - Constructing A Theory of Planned Behavior QuestionnaireDokument7 SeitenAjzen - Constructing A Theory of Planned Behavior QuestionnaireEstudanteSax100% (1)
- Sharpe RatioDokument7 SeitenSharpe RatioSindhuja PalanichamyNoch keine Bewertungen
- No Going BackDokument39 SeitenNo Going BackandrophilemxNoch keine Bewertungen
- Stories of Narada Pancaratra and Lord Krishna's protection of devoteesDokument9 SeitenStories of Narada Pancaratra and Lord Krishna's protection of devoteesPedro RamosNoch keine Bewertungen
- Mania: Caring For A Person ExperiencingDokument6 SeitenMania: Caring For A Person ExperiencingGutsy JewelNoch keine Bewertungen
- Data NormalisationDokument10 SeitenData Normalisationkomal komalNoch keine Bewertungen
- Seminar Assignments Ticket Vending MachineDokument13 SeitenSeminar Assignments Ticket Vending MachineCandy SomarNoch keine Bewertungen
- Layher Allround Industri Stillas 2015 - Engelsk - Utskrift.2Dokument68 SeitenLayher Allround Industri Stillas 2015 - Engelsk - Utskrift.2cosmin todoran100% (1)
- UNIX Concepts: 1. How Are Devices Represented in UNIX?Dokument15 SeitenUNIX Concepts: 1. How Are Devices Represented in UNIX?api-3764166Noch keine Bewertungen
- Existing culture of third-gender students influenced by social mediaDokument9 SeitenExisting culture of third-gender students influenced by social mediaGilbert Gabrillo JoyosaNoch keine Bewertungen
- Conversational MessagesDokument35 SeitenConversational MessagesHenry Darius NamocNoch keine Bewertungen
- CGS PPT FinalDokument14 SeitenCGS PPT FinalAbc Xyz100% (1)
- Pathophysiology of Alzheimer's Disease With Nursing ConsiderationsDokument10 SeitenPathophysiology of Alzheimer's Disease With Nursing ConsiderationsTiger Knee100% (1)
- ILE RPG Programmer's GuideDokument504 SeitenILE RPG Programmer's GuidecrossaholicNoch keine Bewertungen
- Sociology of Behavioral ScienceDokument164 SeitenSociology of Behavioral ScienceNAZMUSH SAKIBNoch keine Bewertungen