Beruflich Dokumente
Kultur Dokumente
PKI Document PDF
Hochgeladen von
sshreddyOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
PKI Document PDF
Hochgeladen von
sshreddyCopyright:
Verfügbare Formate
Best Practices for PKI
Implementation Project
WHITE PAPER Management
Published by CSS Research | Q4 2016
An Overwhelming Need for PKI
The IT space is being dominated by the BYOD (Bring Your Own Device) and
Internet of Things (IOT) boom which is exponentially increasing the number
of connected devices to internal networks and the internet. Intel predicts that
200 billion objects will be internet-connected by 2020, and that number is ris-
ing every day.¹ Given that BYOD and IOT have become mainstream and more
objects are connected to the Internet every day, security concerns surrounding
device authentication and secure communication have become a major focus
of the organizations contributing to these initiatives – more risk means more
security controls.
Digital certificates issued from a Public Key Infrastructure (PKI) are undoubtedly
one of the most effective methods for securing and provisioning access to both
internally connected network enterprise resources and internet-connected
“things.” However, an effective PKI can be difficult to implement and manage
without knowledgeable and dedicated resources in-house.
Hurdles of Tackling a PKI Implementation
If you’re planning on building a PKI using internal resources, make sure you’re
aware of the potential hurdles you may face when depending on your staff to
get a PKI up and running:
• Division of deliverable ownership (i.e., the "two-headed hydra"):
A PKI project has a unique construct in that it will require significant partic-
ipation from at least two distinctly separate divisions within the organiza-
tion. A security team (usually reporting up to the CISO) will be required to
define the certificate policy the PKI will be required to operate under and
a Network Operations team (usually reporting to the CIO) to execute on
processes that are germane to the certificate lifecycle process.
Figure 1. Division of Deliverable Ownership
CISO CIO
Security Network Operations
Team Team
www.css-security.com | © 2016 Certified Security Solutions, Inc. All Rights Reserved. 1
WHITE PAPER | Best Practices for PKI Implementation of Project Management | Q4 2016
• Appropriate skill level and availability of internal expertise:
Having available, knowledgeable staff who possess the expertise
necessary to set up, implement and sustain a PKI on an ongoing
basis is critical. As recommended by Microsoft, your Network
Operations team will need specialists with the ability to:
"It is critical that the –– Create and modify certificate templates as needed by ap-
team responsible for plication owners
your PKI project takes
a holistic approach to –– Manually issue and revoke certificates as well as understand
implementation. They must how to setup auto-enrollment
be in place and adhered
to from the first step of –– Carry out server administration duties: hardware, applying
implementation in order to patches, and creating meaningful backups
be able to sustain the PKI
with full assurance that it will –– Publish Certificate Revocation Lists and manage the CA itself²
not be compromised."
Unfortunately, the field of PKI experts with enough knowledge to
sustain the day to day operation of a PKI is waning. Finding a reliable
expert who can not only design and implement a “healthy” PKI, but
maintain its health on an ongoing basis is becoming harder; as a
result, talent is also becoming more expensive.
It is critical that the team responsible for your PKI project takes a
holistic approach to implementation. They must understand that
specific practices and policies must be in place and adhered to from
the first step of implementation in order to be able to sustain the
PKI with full assurance that it will not be compromised. If you do not
have full confidence in your PKI resources, it’s a good indication that
looking into outside help may be a more viable option.
• Extreme sensitivity to policies and practices: A PKI cannot be
implemented haphazardly (i.e., running an install wizard and clicking
“next” through the options). Robust practices and policies must
be in place and the PKI must be correctly configured in order to
sustain the PKI’s assurance over the long-term so that specifically,
the trust level required is not, and will not be, compromised. More-
over, there must be an operating procedure for how to set up your
PKI, and guidelines for how it should be used throughout its life.
Failure to adhere to strong policies and practices can expose your
business to a number of risks that are difficult to recover from,
including but not limited to “man in the middle” attacks, identity
theft, and corporate espionage. A PKI can be a very effective tool
to mitigate these kinds of risks, but only if the appropriate trust
level is maintained.
www.css-security.com | © 2016 Certified Security Solutions, Inc. All Rights Reserved. 2
WHITE PAPER | Best Practices for PKI Implementation of Project Management | Q4 2016
Executing a Successful PKI
Implementation Project
The key to a successful PKI implementation is understanding the
entirety of the project. Each step from the beginning stages through
implementation must be thought out and planned. To begin the
planning process, consider the following best practices for initiating
a successful implementation.
PKI Implementation Best Practices
• Understand What Goes into the PKI Design: A common error
organizations make before even beginning a PKI project is fully
understanding what goes into the design. It may look simple
on paper, but the process of architecting a design that fits your
business needs and use cases is critical to verify before starting.
Michael Thomas, Know and document your organization’s needs and applicable
Director of Delivery use cases thoroughly. Each following step throughout the rest of
Certified Security the project will depend on these use cases, and an incomplete
Solutions or inaccurate inventory could, at the least, create more arduous
work to remediate the shortcomings, and at the worst, create
a PKI that will not satisfy the organization’s certificate needs.
Note that certain settings while building the PKI are “burned”
into its fabric with no option to modify them later.
“The key to a successful
PKI implementation is • Have a Uniform Policies and Practices Statement: Build out
understanding the entirety of robust policies and practice statements so that your security team
the project. Each step from (or external auditors) have a baseline to engage against when
the beginning stages through it comes to making sure the PKI is healthy during its lifecycle. If
implementation must be a PKI is implemented without proper policy and practices doc-
thought out and planned.” umented, a security or audit team will not have adequate tools
— Michael Thomas, Certified to determine what was intended to be delivered with this PKI,
Security Solutions (CSS) nor will they know if the assurance level has been appropriately
Director of Delivery maintained throughout its lifecycle. Creating these documents
will take a non-trivial amount of project time, but the benefits
of having them after the project is complete are huge.
www.css-security.com | © 2016 Certified Security Solutions, Inc. All Rights Reserved. 3
WHITE PAPER | Best Practices for PKI Implementation of Project Management | Q4 2016
• Plan and Account for the Root Signing Ceremony: Building
Figure 2. Building & Configuring the root CA (i.e., the root signing ceremony) is akin to creating a
the Root CA “master key” to an organization’s network and should be recog-
nized with the same sensitivity. The building and configuration of
the root CA should be well scripted in a controlled environment.
Depending on the assurance level desired for the PKI, this ceremo-
Root CA Creation ny will range from an informal execution of a scripting document
From the second the (low assurance) to a formal filmed event in a pre-authorized space
root CA is created, (high assurance). From the second the root CA is created, a chain
a chain of custody of custody is created which must remain intact from the minute it’s
is created which incepted throughout its lifetime. If this chain of custody is broken
must remain intact at any time, the potential for malware polluting the machine, er-
from the minute it’s roneous certificates being created, or the login security of a root
incepted throughout CA must be assumed to have happened and the root should be
its lifetime. considered compromised. At that point, your PKI is not trustworthy
and all certificates issued must be considered invalid – do not let
this happen to you. This is a security measure you have deliberate
control over from the beginning.
Intact chain of custody
• Verify That All PKI Components Are Properly Operationalized:
While moving into a steady state, make sure all components of the
PKI are properly operationalized. Like most assets created from a
project of this type, when it moves into being part of the corporate
infrastructure there’s no longer a project team accountable for
the maintenance and upkeep. A PKI requires a significant amount
of care and feeding to remain functional – these are dangerous
tripping points for security teams who were focused on simply
implementing the PKI, but not its ongoing operations.
www.css-security.com | © 2016 Certified Security Solutions, Inc. All Rights Reserved. 4
WHITE PAPER | Best Practices for PKI Implementation of Project Management | Q4 2016
Performing a Buildout
Whether you’re tackling PKI internally or with a partner, there are
many parties involved in its successful implementation. Therefore, it
is important to have a detailed implementation plan. The following
sample PKI implementation outline is a good starting point to illus-
trate how various project phases can be broken down and executed:
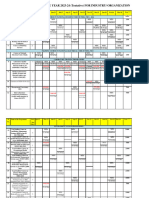
PKI Implementation: Weekly Project Phase Buildout
Phase 1
Week 1 • Project kick-off and design sessions
• First iteration of the design
Phase 2
• First iteration of the design
Week 2
• Create first iteration of the documented certificate policy (CP) and
certification practices statement (CPS)
Phase 3
• Review and sign-off of the design document (all security stakeholders)
Week 3
• Review and revise certificate policy (CP) and certificate practices statement
(CPS) documents
Phase 4
• Preparation for key signing ceremony and production rollout (i.e., complete
change management processes and assign roles for implementation)
Week 4
• Procure and install production hardware (HSMs and servers)
• Create a key signing document and prepare for the ceremony
Phase 5
• Complete root signing ceremony
• Create disaster recovery (DR) cryptography artifacts
Week 5 • Build and configure production of subordinate CAs
• Configure other ancillary PKI servers
• Validate the health of the new PKI
Phase 6
Week 6 • Validate migration strategy
• Begin issuing first set of production certificates
Phase 7
• Complete all documentation
Week
7-8 • Move PKI to steady state and assign ownership for ongoing tasks
• Project completion
www.css-security.com | © 2016 Certified Security Solutions, Inc. All Rights Reserved. 5
WHITE PAPER | Best Practices for PKI Implementation of Project Management | Q4 2016
Knowing Your Options – Implementing
PKI In-house vs. Working with an Expert
Executing a PKI deployment internally can be done successfully so long
as you have the necessary expertise and tools required to correctly ex-
ecute all aspects of the project. The biggest common pitfalls are a lack
of the right expertise and failure to give credence to preparation steps.
Implementing a PKI is complex, but if your security team is experienced
and armed with knowledge of all aspects of PKI, it’s a project that can be
carried out favorably.
The advantage of working with an external party is having access to in-
dustry best practices for dealing with this complex infrastructure, as well
as the knowledge and sensitivity to policies that ensure that your PKI isn’t
compromised from the outset. If you’re not confident that you have the
right internal specialists, do not go it alone!
A PKI partner will be able to:
• Provide professional PKI services with the necessary expertise to fa-
cilitate an infrastructure build.
• Assist with integration plans for PKI-enabled applications.
• Fully manage or assist with building a process to manage the lifecycle
of digital certificates.
• Develop, deliver, and maintain a strong public key infrastructure that
provides business value over the long term.
• Offer access to services designed specifically to meet your unique as-
surance requirements, which will allow your security and IT personnel
to focus on the objectives critical to their roles.
Deciding Whether Internal Execution
Is Right for You
Whether you deploy internally or work with a reputable provider who can
support your PKI project, it has to be done right. Make the best decision
for your business based on the resources available to you.
Unless you have access to a seasoned PKI consultant, carrying out a PKI
implementation will be considerably difficult. A third-party expert will be
objective and ensure that that the full process is carried out – no security
consideration will fall to the wayside. If you’re not fully confident in your
internal resources, get in touch with a PKI partner.
www.css-security.com | © 2016 Certified Security Solutions, Inc. All Rights Reserved. 6
WHITE PAPER | Best Practices for PKI Implementation of Project Management | Q4 2016
How CSS Can Help
PKI is not just a necessary evil – it has many beneficial business cases,
and can be leveraged for identity and access management. Knowing
that, it must be prepped and built correctly; if it isn’t, identity and access
management capabilities can create significant vulnerabilities within
your network. On the flipside, if it is done correctly, your network will
be locked down in a secure and convenient fashion.
At CSS, we use an effective, repeatable methodology for PKI implemen-
tation project management for every customer. We will take the time
to understand how you need to use your PKI and begin by building
the use cases that work for your business.
• Define PKI use cases
• Initiate custom PKI design
• Build policies and practices
• Build infrastructure
• Complete root signing ceremony
• Implement downstream applications
• Utilize the PKI and satisfy business use cases
CSS can assist you in addressing pressing PKI implementation chal-
lenges with the knowledge, experience, and operational efficiency
needed to execute an efficient and effective PKI project.
About Certified Security Solutions (CSS)
As the market leader in enterprise and IoT digital identity security for
data, devices and applications, CSS is a cyber security company that
builds and supports platforms to enable secure commerce for global
businesses connected to the Internet. Headquartered in Cleveland, Ohio,
with operations throughout North America, CSS is at the forefront of
delivering innovative software products and SaaS solutions that are
secure, scalable, economical and easy to integrate into any business.
Visit www.css-security.com for more information.
Contact Us
css-security.com
877.715.5448
www.css-security.com | © 2016 Certified Security Solutions, Inc. All Rights Reserved. 7
WHITE PAPER | Best Practices for PKI Implementation of Project Management | Q4 2016
References
1. A Guide to the Internet of Things. (n.d.). Retrieved September 15,
2016 from http://www.intel.com/content/dam/www/public/us/
en/images/iot/guide-to-iot-infographic.png
2. Pyle, N. (2009, September 01). Designing and Implementing a
PKI: Part I Design and Planning. Retrieved September 15, 2016,
from https://blogs.technet.microsoft.com/askds/2009/09/01/
designing-and-implementing-a-pki-part-i-design-and-planning/
www.css-security.com | © 2016 Certified Security Solutions, Inc. All Rights Reserved. 8
Das könnte Ihnen auch gefallen
- Re Think Your PKIDokument13 SeitenRe Think Your PKIadede2009Noch keine Bewertungen
- Ncipher PKI Professional Services BrochureDokument4 SeitenNcipher PKI Professional Services BrochureMagoo GaoNoch keine Bewertungen
- 6 Pitfalls of a Poorly Designed PKI: Costly Compromises and Failed AuditsDokument2 Seiten6 Pitfalls of a Poorly Designed PKI: Costly Compromises and Failed AuditsMagoo GaoNoch keine Bewertungen
- PKI Deployment - Business Issues: An Oasis White PaperDokument15 SeitenPKI Deployment - Business Issues: An Oasis White Papersaryus2012Noch keine Bewertungen
- Cryptography 2022 Emerging Trends in Cryptography KeyfactorDokument14 SeitenCryptography 2022 Emerging Trends in Cryptography Keyfactorapi-654754384Noch keine Bewertungen
- IoT Developer Program Datasheet 05.06.21 SignedDokument2 SeitenIoT Developer Program Datasheet 05.06.21 SignedMurilo Alves da SilvaNoch keine Bewertungen
- Best Practices For Setting Up A Cybersecurity Operations Center - Joa - Eng - 0921Dokument8 SeitenBest Practices For Setting Up A Cybersecurity Operations Center - Joa - Eng - 0921mbghNoch keine Bewertungen
- PKI Digital Certificate DesignDokument3 SeitenPKI Digital Certificate Designprojectinbangalore279Noch keine Bewertungen
- Ethical Challenges and Opportunities Arising From Evolving TechnologiesDokument9 SeitenEthical Challenges and Opportunities Arising From Evolving Technologiesadmin kapNoch keine Bewertungen
- KBTG It & Security OperationDokument2 SeitenKBTG It & Security OperationSixaxiSNoch keine Bewertungen
- Ejbca Enterprise Vs Open Source CaDokument10 SeitenEjbca Enterprise Vs Open Source Caadede2009Noch keine Bewertungen
- Public Key Infrastructure - GeeksforGeeksDokument5 SeitenPublic Key Infrastructure - GeeksforGeeksDivyansh VaishNoch keine Bewertungen
- Security by Design:: Building Defense in Depth With An Application NetworkDokument7 SeitenSecurity by Design:: Building Defense in Depth With An Application Networkmjason1Noch keine Bewertungen
- Guide To Successful IoT ImplementationDokument14 SeitenGuide To Successful IoT ImplementationMaybe SomeplaceNoch keine Bewertungen
- Pki and Digital Certification Infrastructure PDFDokument6 SeitenPki and Digital Certification Infrastructure PDFmeunomeNoch keine Bewertungen
- Pki Services VerisgnDokument2 SeitenPki Services VerisgnCarlos CardosoNoch keine Bewertungen
- Digicert Private Pki Datasheet 2 8 17Dokument2 SeitenDigicert Private Pki Datasheet 2 8 17Indra MaulanaNoch keine Bewertungen
- Securing Your PKI Building Trust You Can Depend On WPDokument24 SeitenSecuring Your PKI Building Trust You Can Depend On WPNishantvermaNoch keine Bewertungen
- The Public Key InfrastructureDokument6 SeitenThe Public Key InfrastructurekajulovNoch keine Bewertungen
- Session 5 Rev-FDokument17 SeitenSession 5 Rev-FTarik AmezianeNoch keine Bewertungen
- Certificate Issuance Provisioning For Connected Devices Factsheet enDokument2 SeitenCertificate Issuance Provisioning For Connected Devices Factsheet enpas2023wwNoch keine Bewertungen
- Au-Bp-Cio Ciso Practitioner Guidance On It Security Governance-Eng-2009 0Dokument17 SeitenAu-Bp-Cio Ciso Practitioner Guidance On It Security Governance-Eng-2009 0BMNoch keine Bewertungen
- CYBERSECURITY FOR MANAGERS: BUILD YOUR ACTION PLAN (39 charactersDokument13 SeitenCYBERSECURITY FOR MANAGERS: BUILD YOUR ACTION PLAN (39 charactersshadab umairNoch keine Bewertungen
- Get Cisco CertifiedDokument16 SeitenGet Cisco CertifiedAna C ArenasNoch keine Bewertungen
- KPMG IIOT Future State DevelopmentDokument4 SeitenKPMG IIOT Future State DevelopmentVi Anh TranNoch keine Bewertungen
- Public Key Infrastructure (PKI) ServicesDokument5 SeitenPublic Key Infrastructure (PKI) ServicesEncryption ConsultingNoch keine Bewertungen
- Kick-Off Meeting chatGPT For Cybersecurity - Session 1Dokument34 SeitenKick-Off Meeting chatGPT For Cybersecurity - Session 1MazharRizviNoch keine Bewertungen
- Ey An Integrated Vision To Manage Cyber Risk PDFDokument24 SeitenEy An Integrated Vision To Manage Cyber Risk PDFMaya M100% (1)
- ABC Technologies - Case StudyDokument15 SeitenABC Technologies - Case StudyNitin PandeyNoch keine Bewertungen
- Blockchain Services 2016Dokument8 SeitenBlockchain Services 2016RobinNoch keine Bewertungen
- PKI OverviewDokument3 SeitenPKI OverviewfilateiNoch keine Bewertungen
- 10 PKI Use Cases For Stronger Enterprise SecurityDokument43 Seiten10 PKI Use Cases For Stronger Enterprise SecuritySathishkumar JanakiramanNoch keine Bewertungen
- Accertify Case StudyDokument9 SeitenAccertify Case StudyhalockNoch keine Bewertungen
- Meraki Top Physec Trends Ebook English 20221101Dokument13 SeitenMeraki Top Physec Trends Ebook English 20221101syed tabrezNoch keine Bewertungen
- Ccie Security at A Glance PDFDokument2 SeitenCcie Security at A Glance PDFjaaniNoch keine Bewertungen
- Ebook Future Proofing Internal AuditDokument22 SeitenEbook Future Proofing Internal Auditgoyosito100% (1)
- EY Research 2019-2020 PDFDokument36 SeitenEY Research 2019-2020 PDFIshaan MakkerNoch keine Bewertungen
- AI-Optimized DevOps For Streamlined Cloud CI/CDDokument7 SeitenAI-Optimized DevOps For Streamlined Cloud CI/CDInternational Journal of Innovative Science and Research TechnologyNoch keine Bewertungen
- Letter To All OFIs Issuance of Risk-Based Cybersecurity Framework and Guidelines For Other Financial InstitutionsDokument43 SeitenLetter To All OFIs Issuance of Risk-Based Cybersecurity Framework and Guidelines For Other Financial InstitutionsjideNoch keine Bewertungen
- 6.senior Ict Officer Research and Development JSG 4Dokument2 Seiten6.senior Ict Officer Research and Development JSG 4telzyntechnologiesltdNoch keine Bewertungen
- JD - NV Strategy (SMT)Dokument2 SeitenJD - NV Strategy (SMT)Anish DalmiaNoch keine Bewertungen
- AI-Driven Malware Detection Using BlockchainDokument15 SeitenAI-Driven Malware Detection Using Blockchaintempmail7575Noch keine Bewertungen
- Sensors 22 08408 v2Dokument26 SeitenSensors 22 08408 v2keyeronNoch keine Bewertungen
- BrochureDokument6 SeitenBrochureSamuel Bamgboye kobomojeNoch keine Bewertungen
- Ccie Security at A GlanceDokument2 SeitenCcie Security at A GlanceAbdul Rahaman GaffarNoch keine Bewertungen
- Why Get Certified: 13 Reasons For Seeking Training and CertificationDokument17 SeitenWhy Get Certified: 13 Reasons For Seeking Training and CertificationAlex T.Noch keine Bewertungen
- Internal Auditors Guide To Blockchain - 1554497668 PDFDokument8 SeitenInternal Auditors Guide To Blockchain - 1554497668 PDFSatyam KesharwaniNoch keine Bewertungen
- Enterprise Pki Manager Datasheet enDokument4 SeitenEnterprise Pki Manager Datasheet enTm UserNoch keine Bewertungen
- Ethical Hacking Training InstituteDokument7 SeitenEthical Hacking Training InstituteGuru Mohan DixitNoch keine Bewertungen
- IIT Roorkee CyberSecurity BrochureDokument15 SeitenIIT Roorkee CyberSecurity BrochureNihal ReddyNoch keine Bewertungen
- Career opportunities at Konza TechnopolisDokument5 SeitenCareer opportunities at Konza TechnopolisIsaacNoch keine Bewertungen
- Frank McGovern ResumeDokument2 SeitenFrank McGovern ResumeJosué RombaNoch keine Bewertungen
- OT For Industry 4.0Dokument26 SeitenOT For Industry 4.0Febryn Pradana Rifanda PutraNoch keine Bewertungen
- Implementing The NIST Cybersecurity Framework Using COBIT 5: A Step-by-Step Guide For Your EnterpriseDokument14 SeitenImplementing The NIST Cybersecurity Framework Using COBIT 5: A Step-by-Step Guide For Your Enterpriseandreasang89Noch keine Bewertungen
- Cyber Tech Radar 2022 Brochure PDF en v5 WEBDokument20 SeitenCyber Tech Radar 2022 Brochure PDF en v5 WEBdolamthienNoch keine Bewertungen
- Current Trends in Blockchain Implementations for Decentralized IdentityDokument17 SeitenCurrent Trends in Blockchain Implementations for Decentralized IdentityRafael V. PáezNoch keine Bewertungen
- Building Effective Cybersecurity Programs: A Security Manager’s HandbookVon EverandBuilding Effective Cybersecurity Programs: A Security Manager’s HandbookBewertung: 4.5 von 5 Sternen4.5/5 (3)
- Hands-On Microservices with Kubernetes: Build, deploy, and manage scalable microservices on KubernetesVon EverandHands-On Microservices with Kubernetes: Build, deploy, and manage scalable microservices on KubernetesBewertung: 5 von 5 Sternen5/5 (1)
- Modern Cybersecurity Strategies for Enterprises: Protect and Secure Your Enterprise Networks, Digital Business Assets, and Endpoint Security with Tested and Proven Methods (English Edition)Von EverandModern Cybersecurity Strategies for Enterprises: Protect and Secure Your Enterprise Networks, Digital Business Assets, and Endpoint Security with Tested and Proven Methods (English Edition)Noch keine Bewertungen
- Activating License Offline (Without Internet Access)Dokument3 SeitenActivating License Offline (Without Internet Access)sshreddyNoch keine Bewertungen
- Blackberry Uem: Release NotesDokument21 SeitenBlackberry Uem: Release NotessshreddyNoch keine Bewertungen
- Blackberry Enterprise Bridge For Android: User GuideDokument16 SeitenBlackberry Enterprise Bridge For Android: User GuidesshreddyNoch keine Bewertungen
- Zerto Virtual Replication Vsphere Enterprise GuidelinesDokument11 SeitenZerto Virtual Replication Vsphere Enterprise GuidelinessshreddyNoch keine Bewertungen
- Vsphere Distributed Switch Best PracticesDokument30 SeitenVsphere Distributed Switch Best PracticesnewbeoneNoch keine Bewertungen
- Blackberry Uem: Installation and UpgradeDokument54 SeitenBlackberry Uem: Installation and UpgradesshreddyNoch keine Bewertungen
- Vmware Whats New in Vsphere WhitepaperDokument32 SeitenVmware Whats New in Vsphere WhitepaperlaurNoch keine Bewertungen
- Mitel MiVoice Business Overview Brochure - ENDokument6 SeitenMitel MiVoice Business Overview Brochure - ENsshreddyNoch keine Bewertungen
- VMW White Paper VSPHR Whats New 6 0 PLTFRMDokument18 SeitenVMW White Paper VSPHR Whats New 6 0 PLTFRMsshreddyNoch keine Bewertungen
- Whats New Vmware Vcenter Server 50 Technical Whitepaper PDFDokument11 SeitenWhats New Vmware Vcenter Server 50 Technical Whitepaper PDFsshreddyNoch keine Bewertungen
- Additional Documents for Under 18 Student VisasDokument2 SeitenAdditional Documents for Under 18 Student VisassshreddyNoch keine Bewertungen
- Standard Tube MapDokument2 SeitenStandard Tube MapAntonella ErcolaniNoch keine Bewertungen
- VmwareVsphere PDFDokument1 SeiteVmwareVsphere PDFsshreddyNoch keine Bewertungen
- Exam MSFT AZ 103 Self Assessment Build5NinesDokument11 SeitenExam MSFT AZ 103 Self Assessment Build5NinessshreddyNoch keine Bewertungen
- Exam MSFT AZ 500 Self Assessment Build5NinesDokument12 SeitenExam MSFT AZ 500 Self Assessment Build5NinessshreddyNoch keine Bewertungen
- CylancePROTECT Admin Guide v2.0 Rev1Dokument73 SeitenCylancePROTECT Admin Guide v2.0 Rev1sshreddy33% (3)
- Exam MSFT AZ 400 Self Assessment Build5NinesDokument15 SeitenExam MSFT AZ 400 Self Assessment Build5NinessshreddyNoch keine Bewertungen
- Exam MSFT AZ 300 Self Assessment Build5NinesDokument15 SeitenExam MSFT AZ 300 Self Assessment Build5NinessshreddyNoch keine Bewertungen
- 1 Introduction Comptia A Plus 220 901 m1 SlidesDokument19 Seiten1 Introduction Comptia A Plus 220 901 m1 SlidessshreddyNoch keine Bewertungen
- VmwareVsphereNotes PDFDokument1 SeiteVmwareVsphereNotes PDFsshreddyNoch keine Bewertungen
- Torrent Downloadedsdfasdfw23f From 1337x.toDokument1 SeiteTorrent Downloadedsdfasdfw23f From 1337x.tosshreddyNoch keine Bewertungen
- Exam MSFT AZ 103 Self Assessment Build5NinesDokument11 SeitenExam MSFT AZ 103 Self Assessment Build5NinessshreddyNoch keine Bewertungen
- Torrent Downloaded From 1337x.toDokument1 SeiteTorrent Downloaded From 1337x.tosshreddyNoch keine Bewertungen
- Best Practices For PKI Implementation Project ManagementDokument8 SeitenBest Practices For PKI Implementation Project ManagementsshreddyNoch keine Bewertungen
- DownloadDokument303 SeitenDownloadsshreddyNoch keine Bewertungen
- VS5ICM M10 ResourceMonitoringDokument68 SeitenVS5ICM M10 ResourceMonitoringsshreddyNoch keine Bewertungen
- Delivering On Cisco's Unified Computing VisionDokument2 SeitenDelivering On Cisco's Unified Computing VisionsshreddyNoch keine Bewertungen
- Access and Authentication Control: © 2011 Vmware Inc. All Rights ReservedDokument26 SeitenAccess and Authentication Control: © 2011 Vmware Inc. All Rights ReservedsshreddyNoch keine Bewertungen
- Vs5icm m06 StorageDokument59 SeitenVs5icm m06 StoragesshreddyNoch keine Bewertungen
- Energy Audit Report for Arnav Industries Analyzes Conservation PotentialDokument8 SeitenEnergy Audit Report for Arnav Industries Analyzes Conservation PotentialAkshay KhadseNoch keine Bewertungen
- Unit 03 Special Areas of AuditDokument3 SeitenUnit 03 Special Areas of AuditVasim Ahmad50% (4)
- October 2015 PHILNITSDokument43 SeitenOctober 2015 PHILNITSPatrick Caguimbal DoctoleroNoch keine Bewertungen
- Delivery Environment Complexity Analytic Guide PDFDokument45 SeitenDelivery Environment Complexity Analytic Guide PDFMalcolm ShroffNoch keine Bewertungen
- Case Digest On Local GovernmentDokument46 SeitenCase Digest On Local GovernmentKenn Ian De VeraNoch keine Bewertungen
- Laboratory Testing Quality ManualDokument54 SeitenLaboratory Testing Quality ManualReama QumsanNoch keine Bewertungen
- Tier 1 Firms - Overview: Audit Quality Inspection and Supervision ReportDokument37 SeitenTier 1 Firms - Overview: Audit Quality Inspection and Supervision ReportAbdelmadjid djibrineNoch keine Bewertungen
- Third Party Due Diligence - Know Your Third Party - EY IndiaDokument8 SeitenThird Party Due Diligence - Know Your Third Party - EY Indiaeyindia.pdNoch keine Bewertungen
- Financial Performance and Position HighlightsDokument100 SeitenFinancial Performance and Position HighlightsSHAMSUL ARIF ZULFIKAR HUSNINoch keine Bewertungen
- HSE Management - Guidelines For Working Together in A Contract EnvironmentDokument72 SeitenHSE Management - Guidelines For Working Together in A Contract EnvironmentscrbdgharaviNoch keine Bewertungen
- FedRAMP Control Quick Guide V12Dokument2 SeitenFedRAMP Control Quick Guide V12Chris Hohman100% (1)
- B.C. Transportation Ministry Guidelines On Road Safety AuditsDokument11 SeitenB.C. Transportation Ministry Guidelines On Road Safety AuditsBob MackinNoch keine Bewertungen
- HR AuditDokument13 SeitenHR AuditRidhima Aggarwal100% (1)
- ISO 45001 2018 OHSMS Audit ChecklistDokument7 SeitenISO 45001 2018 OHSMS Audit ChecklistRonald Abadi TariganNoch keine Bewertungen
- Syllabus in Acctg. 13 Management Consultancy BSADokument10 SeitenSyllabus in Acctg. 13 Management Consultancy BSAAnonymous Vng49z7hNoch keine Bewertungen
- California Department of Health Care ServicesDokument109 SeitenCalifornia Department of Health Care ServicesKevin SmithNoch keine Bewertungen
- Experienced Finance Professional with Strong Accounting SkillsDokument5 SeitenExperienced Finance Professional with Strong Accounting SkillsAaronNoch keine Bewertungen
- Accounting Services ContractDokument4 SeitenAccounting Services ContractDv Accounting100% (1)
- AtDokument14 SeitenAtInny AginNoch keine Bewertungen
- Objective Bank Audit ProjectDokument18 SeitenObjective Bank Audit ProjectKUNAL GUPTANoch keine Bewertungen
- Sae7487 U6 - Bsbsus401 - NYC (Plagiarised)Dokument47 SeitenSae7487 U6 - Bsbsus401 - NYC (Plagiarised)Jyoti VermaNoch keine Bewertungen
- Supplier Quality & Food Safety Audit: Your LogoDokument6 SeitenSupplier Quality & Food Safety Audit: Your LogokarupukamalNoch keine Bewertungen
- Information Audit as a Management ToolDokument0 SeitenInformation Audit as a Management ToolKharisty HasanahNoch keine Bewertungen
- Annex A.1 - Concept Note!Dokument12 SeitenAnnex A.1 - Concept Note!kristinaNoch keine Bewertungen
- BIS Training - Calender - Industry - 2023-24Dokument7 SeitenBIS Training - Calender - Industry - 2023-24Dinesh SharmaNoch keine Bewertungen
- SIGIR Report January 2007 - All AppendicesDokument327 SeitenSIGIR Report January 2007 - All Appendicesapi-3736039Noch keine Bewertungen
- Chapter 8-SHEDokument77 SeitenChapter 8-SHEVip Bigbang100% (1)
- QMS NCRs and nonconformitiesDokument3 SeitenQMS NCRs and nonconformitiesSharaf AgeedNoch keine Bewertungen
- Audit Case StudyDokument3 SeitenAudit Case StudyTaha AhmedNoch keine Bewertungen
- The Comparison of The Deming Prize and The Baldrige Award: - HandoutsDokument37 SeitenThe Comparison of The Deming Prize and The Baldrige Award: - HandoutsKristy Anne Habito-Corpuz0% (1)