Beruflich Dokumente
Kultur Dokumente
Electronic Voting PDF
Hochgeladen von
Kannihya MishraOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Electronic Voting PDF
Hochgeladen von
Kannihya MishraCopyright:
Verfügbare Formate
See discussions, stats, and author profiles for this publication at: https://www.researchgate.
net/publication/325781283
Confidential E-Voting System Using Face Detection and Recognition
Article · June 2018
CITATIONS READS
0 853
1 author:
Rajendran Anandha Jothi
Alagappa University
18 PUBLICATIONS 6 CITATIONS
SEE PROFILE
All content following this page was uploaded by Rajendran Anandha Jothi on 15 June 2018.
The user has requested enhancement of the downloaded file.
International Journal of Engineering and Techniques - Volume 3 Issue 4, July-Aug 2017
RESEARCH ARTICLE OPEN ACCESS
Confidential E-Voting System Using Face Detection and
Recognition
Aanjana Devi.S 1, Dr.Palanisamy.V 2 and Anandha Jothi.R3
1,2,3
Department of Computer Applications, Alagappa University, Karaikudi.
Abstract:
In any developing country democracy plays an important role where a leader for a country is elected by the citizen. One of the
main issues in the conventional voting system is that it consumes lots of man-power as well as resources and the preparation have been
started many days before the commencement of the election. During this preparation some people may involve in illegal arrangement with
each other or try to replace with their henchmen in this process to win the election. It is a confidential process so it must be transparent,
Meddle-Proof, Usable, Authenticated, Accurate, Verifiability and Mobility. There are some drawbacks in conventional voting system such
as damage of machines, chances of violence, dummy voting and problem of proper monitoring. Manual voting system has been followed in
many parts of our country so people could not poll their vote because it is place oriented and there is region wise distribution, voters need to
reach the place of voting. To overcome these problems a new confidential E-Voting system is introduced which provides security to the
election system by detection and recognising voter’s face who is going to cast his/her vote. In this system the voter’s face is detected,
captured and stored in the database then match the captured image with the image already stored on database to recognise the person. If
match occurs then the person is allow to cast their vote once the vote is casted the same person will not be permitted to cast votes this provide
security against duplicate vote and fraudulent and make the system more efficient and user friendly.
Keywords — Accurate, Authentication, Eigen face , Viola Jones algorithm.
I. Introduction
Emphasize Biometric detection and recognition suggests
chronic recognition of a people in light of a Highlight
vector(s) gotten from their physiological or potentially
behavioural trademark. Biometric recognition frameworks
ought to give a solid individual acknowledgment plans to
either confirm or to decide the character of a person. Uses of
such a framework incorporate PC Frameworks security,
secure electronic keeping money, cell phones, credit cards,
secure access to Structures, wellbeing and social
administrations. By utilizing biometrics a man could be
distinguished based on "who she/he is" somewhat then "what
she/he has" (card, token, scratch) or she/he knows"(secret
key, Stick). This proposed system we construct a secure
biometric system for E-Voting using face detection and
recognition. Here we used two algorithms for face detection Fig 1. Face Detection Process
and recognition namely (viola Jones and Eigen face).
A. Face Detection Algorithm There are numerous systems has been looked into for
quite a long time and much advance has been proposed in
Face detection is one of the most difficult and demanding
writing the majority of the location strategy the majority of the
crisis in the pasture of computer revelation, owing to the huge
discovery strategies focused on recognizing frontal
differences produced by the difference in the facial advent,
countenances with enough lightning condition. Yang's
illumination, and facial expression. So that the division of
arranged this strategy into four sorts in his study: learning
each part of the face looks to be extremely nonlinear and
based, include invariant, format coordinating and
difficult in any space which is direct to the first picture space.
appearance-based. 1) Information based strategies displayed
In the constant applications like reconnaissance and
facial element utilizing human coding, for example, two
biometric, the camera restrictions and posture varieties make
symmetric, mouth, nose and so on 2) The element which are
the appropriation of human faces in highlight space more
invariant to stance and lighting condition are discover
entangled than that of frontal countenances. It additionally
utilizing highlight invariant technique. 3) The relationship
confounds the issue of strong face discovery.
between a test picture and pre picture fall into layout
coordinating classification. 4) This appearance based strategy
incorporates machine learning methods to separate
discriminative element from a pre-named set. Identification
ISSN: 2395-1303 http://www.ijetjournal.org Page 81
International Journal of Engineering and Techniques - Volume 3 Issue 4, July-Aug 2017
Calculation Viola and Jones' calculation is utilized as the
premise of our outline. Probably aware there is a few
similitude’s in every single human face, we utilized this idea
as a Haar highlight to recognize confront in picture. Haar like
element which is utilized to recognize human face from the
picture and spare it as the primary coordinating point. We
actualize calculation to perceive the prepared pictures put
away in the database. The objective is to execute the
framework display for a specific face and recognize it from an
expansive number of put away faces with some recent
varieties too. It gives us effective approach to discover the
lower dimensional space. Picking the limit esteem is an
extremely huge element for execution of face distinguishing
proof in this approach. Other than that, the dimensional
diminishment of face space endless supply of confronts taken. Fig 2. Face recognition process
In this exploration paper, an improved answer for face The Eigen confront strategy is a standout amongst the most
acknowledgment is given by taking the upgraded estimation effective and easiest methodologies in building up a
of limit esteem and number of countenances. framework for Face Acknowledgment. The acknowledgment
is performed by anticipating new picture into the subspace
B.Face Recognition Algorithm reached out by the Eigen confronts ("confront space‟) and
The human face is an amazingly perplexing and dynamic after that arranging the face by differentiating its position into
structure with attributes that can rapidly and altogether the face space with the places of the distinguished people In
change with time. It is the essential concentration of Eigen confront strategy, the separation is measured between
consideration in social connections and assumes a noteworthy couples of pictures for acknowledgment after the dimensional
part in the transmission of character and feelings. decrease of the face space. On the off chance that the
Subsequently, confront acknowledgment is connected in separation is not as much as specific limit esteem, then it is
numerous essential regions, for example, security considered as a distinguished face else it is a unidentified
frameworks, distinguishing proof of culprits, and face. In the figure, we have two arrangements of picture
confirmation of charge cards et cetera. Shockingly, many face pieces preparing set picture square and test set picture piece.
highlights make improvement of facial acknowledgment In preparing set picture square, right off the bat the Eigen face
frameworks troublesome. This issue is tackled by the of picture in the database (prepared picture) is acquired. At
technique called Essential Part Examination. PCA is a that point the weight W1 is figured by utilizing the Eigen
projection method that finds an arrangement of projection confronts and the preparation set. In the testing set picture
vectors planned with the end goal that the anticipated square, input obscure picture X which is the caught picture is
information holds the most data about the first information. taken. The weight W2 is figured utilizing the info picture and
The most illustrative vectors are eigenvectors comparing to the Eigen confront. Estimation of D is figured by finding the
most noteworthy Eigen estimations of the covariance lattice. normal of separations amongst W1 and W2.
This technique lessens the dimensionality of information
space by anticipating information from M-dimensional space II. LITERATURE REVIEW
to P-dimensional space, where P and M. One of the least Firas.I.Hazzaa et.al [12] proposed a “Web Based Voting
complex and best PCA approaches utilized as a part of face System Using Fingerprint Design and Implementation”, to
acknowledgment frameworks is the purported Eigen confront facilitate enhanced performance with more secure voting
approach. This approach changes face into a little system and also implement web technology to compose the
arrangement of fundamental qualities, Eigenfaces, which are voting system more useful. The projected EVS permits the
the primary segments of the underlying arrangement of electorate to scrutinize their fingerprint that is coordinated
learning pictures (preparing set). Acknowledgment is finished with the existing copy stored in the database. This Web-based
by anticipating another picture in the Eigen confront Voting System using Fingerprint identification and provide
subspace, after which the individual is ordered by looking at acompetent way to transmit votes, liberated deception and
its position in Eigen confront space with the position of construct the scheme highly reliable, financial and rapid and
known people. The benefit of this approach over other face also use Minutiae-based fingerprint recognition and related
acknowledgment frameworks is in its straightforwardness, with higher precision.
speed and heartlessness to little or continuous changes on the Jambhulakar et.al [14] proposed “A Novel Security for
face. The issue is constrained to records that can be utilized to Online Voting System by Using Multiple Encryption
perceive the face. In particular, the pictures must be vertical Schemes”. Give protection to casting of vote when the vote is
frontal perspectives of human countenances. The plan surrender from ballet poll to voting server. Several encodings
depends on a data hypothesis technique that breaks down face to evade DOS hit. Safety has offered passive in addition to
pictures turn into a moment set of trademark highlight dynamic intruder and this system also grabs a decision of
pictures are called Eigen faces, which are in reality the chief convinced problems. This system use cryptography
parts of the essential preparing set of face pictures. techniques to obtain advantages of digital signature. Encode
ISSN: 2395-1303 http://www.ijetjournal.org Page 82
International Journal of Engineering and Techniques - Volume 3 Issue 4, July-Aug 2017
the forward votes to client server and send the encoding votes by capturing the face image and make their shares and
to voting server through internet and decode the vote prior to compare the shares with the shares already stored in database.
computation of votes. Asymmetric key are used to afford If the shares coincides with the previous shares in the database
protection from active interloper who can change vote that is then the person is allow to cast their votes otherwise they are
casted while it is transferred from client server to voting not permitted to cast their votes. There is no transparency and
server, for this purpose to avoid fraudulent digital signature is security to the system.
used during casting of vote and the digital signature is verified Niranjanmalwade et.al [10] proposed smart voting system
on the server side with the accurate digital signature of the with face recognition. In this system the electorate use
electorate that is known openly. For this reason each and android applications which are downloaded from internet and
every electorate must have their personal digital signature and the authentication will be done using system configuration
a communal digital signature identifier. This is a long term and face recognition. The main drawback or issues in this
process which increases time and cost complexity. system is that it can be used only in android mobiles i.e., this
Patilrahul et.al [7] suggest a system for E-Voting using face system is applicable only for android platform.
detection and finger print recognition which uses various III. Existing System
algorithms and techniques such as Eigen face, AES, and Current voting system is the conventional voting system built
besian classifier for providing highly reliable and secure on ballot machine where the voter are allow to cast their vote
system of voting. In this system the voting is done by by pressing the button along with the symbol on the voting
identifying the face image and finger prints of the electorate machine. So there arise some security risks that the person
who is going to cast their votes. The electorate information may cast their votes more than one time, fraudulent, breakage
are verified by capturing the face image through web camera of the system, theft may happen. In this conventional system
along with finger print and the electorate is allow to cast their ballot begin before a week and the voters are go to the polling
vote after checking the details with database information. The booth to cast their vote. In order to provide security huge
votes are stored and later the result is declared. manpower is required to avoid mal practices, to avoid such
Neha Gandhi [13] designs a secure online voting system using security issues and malpractices a new E-voting system have
biometrics and stenography to give biometric security as well been introduced using biometric technology which use face
as password security to electorate account. In this model a detection and recognition to cast their vote on their place
secret key is used along with voter image as key image to without moving to polling booth they can cast their votes
produce a new image to perform electorate authentication and through online. By using face as their identity which avoid the
to minimize risk factors such as hacking. It also provides security issues on conventional system.
protection against fraudulent behaviours. The main drawback
IV.Proposed System
is that process of encoding the image along with key is a long
In this proposed system we generate an idea of
term process.
E-voting system using biometrics face detection and
Ratnaprabha et.al [11] build an E-/voting system using
recognition. In this system two algorithms have been use for
“Auduino Software” to capture the face and finger print of an
face recognition and detection such as viola Jones and Eigen
individual and match the finger print and face image to the
face algorithms.
details in the “Aadhar” which are already stored in database
using Lab view and compare the details which are already
stored in PC and the casted vote is done but not the accurate
result is dispatched. This system just avoids duplication of
votes but it is not the robust one.
Priyataneja et.al [9] anticipated an online voting system by
face detection. In this system various algorithms such as
Gabor filter technique, Eigen face technique, Gold ratio
technique and Line Edge Map (LEM) techniques to detect the
face of an individual without any noise. This system is
embedded with mobile phones and the electorate is permit to
cast their votes through their mobile phone at their mobility
and convenience. This system obtains information from the
database which stores details of the particular voter through
Aadhar database. Due to usage of more number of techniques
leads to complexity of the system and also the voter should
aware of their availability of network they use because the
voting is done through their mobile phone these are the main
issues in this system. This system uses front camera of the
mobile to capture the face of the electorate so the phones
without front camera is not suitable for this approach.
Fugatashlesha et.al [8] projected a secure online voting
system using face recognition. In this system they propose
online voting system use face recognition to secure the system
ISSN: 2395-1303 http://www.ijetjournal.org Page 83
International Journal of Engineering and Techniques - Volume 3 Issue 4, July-Aug 2017
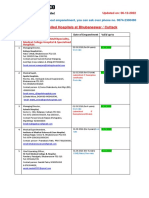
Fig 4. Algorithm Efficiency
Initially multi views of a voter/person face is captured with
webcam and voter details are entered with an appropriate
address, date of birth, number then it is trained and stored in a
database, A Person who wants to vote should correctly focus
Fig 3. System Architecture his/her face in front of webcam window then enter the card id
Using viola Jones algorithm face of an individual is number. After doing this if voter face and id number match
captured using webcam or camera then it is stored along with with the data base value then voter is successfully complete
the information of the voter. At the time of polling the voter is voting. The security level of our system is greatly improved
sit in front of the webcam or the camera on the laptop which is by the new application method for each voter. The user
connected on the voting server through internet then the face authentication process of the system is improved by adding
is captured and recognized using Eigen face and match the face recognition in an application which will identify whether
face with the face image stored on the database if the face is the particular user is authenticated user or not. The
matched or coincides with the face in the database the voter is recognition percentage of the scheme is protected as each
allow to declare their votes to the candidate whom they individual will have a dissimilar unique proportion. This
wished to elect otherwise the voter is not allow to elect their scheme will prevent the forbidden follows like equipping.
leader by voting. By this way we can avoid the duplication of Thus, the citizens can be sure that they alone can choose their
votes and frauds and also this can avoid malpractice and leaders, thus exercising their right in the democracy. The
minimize the time taken to cast the vote by moving to the procedure of online voting has the ability to decrease or
polling booth. eliminate unsolicited humanoid mistakes. In addition to its
V. Result and Discussion reliability, online voting can handle multiple modalities, and
provide better scalability for large elections. Online voting is
The investigational consequences are proved in this paper also an excellent mechanism that does not require
to confirm the feasibility of the suggested face recognition geographical proximity of the voters. Thus, we will be able to
technique. Also only 15% of Eigen faces with the largest change the face of today’s voting system by making it
Eigen values are adequate for the recognition of a person. The corruption less. It will give a fair chance to every leader to win
best optimized solution for face recognition is provided when on the basis of his/her talent, ability and not on the basis of
both the features are combined i.e. 15% of Eigen faces with strength of money, power and rule. The range of the scheme
largest Eigen values are chosen and threshold value is chosen can be elevated to the people, official or national level via a
0.8 times maximum of minimum the Euclidean distances from highly protected and effective database management system
all other images of each image, it will wholly improve the that could handle hundreds, thousands or billions of users.
recognition performance of the human face up to 97%. Table 1
Comparison Of Recognition Rate Orl Face Database For 20 Eigen
ISSN: 2395-1303 http://www.ijetjournal.org Page 84
International Journal of Engineering and Techniques - Volume 3 Issue 4, July-Aug 2017
S.no Training Testing Correct Outputs Recognition
Table 2 Images Images Per (out of 80 Tests) rate
Comparison Recognition Rate Varying Eigen Values For 8 Training Images Per Class Classes
Per Class
1 8 2 77 96.25%
• 1D-PCA-1Dimensional Principal Component Analysis
2 D
6 2 1D-PCA 75 Directional 2D-PCA
91.25%
• 2D-PCA-2 Dimensional Principal Component Analysis
3 4 2 71 86.25%
20 95% 96.25%
VI. Conclusion 4 2 2 65 78.75%
30 95% 95%
Several online voting system and methods are studied 40 95% 95%
related to E-Voting using biometrics. From the study we
50 95% 95%
proposed a secure Electronic voting system using biometrics
technique with face detection and recognition. This provide 60 95% 95%
robust and reliable user friendly encoded secure system for Detection”,Internatioal Journal Of Advanced Technology in
E-Voting which allow the recognized voter to cast their votes Engineering andScience, Vol.3, Issue. 1, March 2015.
10. Niranjanmalwade, Mahesh Tavare,Akshay kamble & Aniruddha
through mobile phone as well as through PC connected in Kamble ,”Smart Voting System with Face Recognition”, Vol.2,
network. Here Eigen face algorithm and viola jones are Issue.2, feb 2014.
suggested to provide highly secured, more reliable and robust 11. Ratnaprabha.S, TriniXavier.X, Deepika.V, Iswarya.C,”A Survey
E-Voting System. It also improves efficiency of the system On E-Voting System Using Audino Software” International
Journal Of Advanced Research In Electrical, Electronics And
and to provide user friendly environment for voters to cast Instrumental Engineering, Vol.5, Issue.2, Feb 2016.
their valuable votes. 12. Firas.I.Hazzaa, Seifedine kadry, Oursama kareem, zein,”Web
Based Voting System Using fingerprint Design And
VII. Acknowledgement Implementation”,Vol.2, Issue.4,Dec 2014.
13. Neha Gandhi “Study on security of Online Voting System Using
Here I would like to express my appreciation to Biometrics and Steganography” IJCSC, Vol.5,Mar-Sep
Prof.Dr.V.palanisamy for his guidance during the research 2014,pp.29-32.
work without his valuable assistance this research work 14. Jambulakar “A Novel Security For Online Voting system By Using
cannot be completed. I am also indeed to the college where I Multiple Encryption Scheme”, Internatioanl Journal of
Engineering And Technology, Vol.2, Issue 5
carried out my research at Alagappa University in the
department of computer science and engineering Principal
and staff for their support cooperation. Finally I would thank
my management for the valuable assistance during the course
of my study.
References
1. Face Recognition using Glass Watermarking Filters, Muhammad
sharif, Adeel khalid, Mudassar RAZA, Sajjad mohsin,
Department of Computer Sciences, comsats Institute of
Information Technology, Wah Cantt-Pakistan J.
2. Face Detection using Neural Network & Glass Watermarking
Wavelet Transform, Avinash Kaushal1, J P S Raina2, 1GCET,
Greater Noida, U.P., India; 2BBSBEC, Fatehgarh Sahib,
Punjab, India.
3. Heseltine, T., Pears, N., Austin, J.: Evaluation of image
pre-processing techniques for eigenface based face recognition.
In Proc. of the Second International Conference on Image and
Graphics, SPIE vol. 4875, (2002) 677-685.
4. Arati Kothari and Sampatkumari Maruti Bandagar . 2011.
“Performance & Evaluation of Face Recognition Algorithm”
World Journal of Science & Technology.
5. Ankita Ladda,Rasika Gunjal,Ratnavidya Kanawade & Sanjay
Agarawal 17 March 2013 “Automated Secure Attendance
System ” ICCSE.
6. Ahonen T, Hadid A, Pietika¨inen M, ‗‘Face recognition with local
binary patternsǁ. In Proceeding of European conference on
computer vision (ECCV2004), LNCS 3021, pp 469–481,2004
7. Patil rahul.H, Tarte babita.B, Wadekar sapana.S, Zurunge
Bakti.S, Prof .Phursule Rajesh, “A Secure E-Voting System
Using Face Recognition And Dactylogram”, International
Engineering Research Journal (IERJ), Vol. 2, Issue .2,pp.
758-762, 2016,ISSN 2395-1621.
8. Fugatashlesha, Gaikward Shital,Gangurde jyoti,swat
aishwarya,“Secured Online Voting System Using Face
Recognition”, Internatonal Journal of Advanced Research In
Science Management And Technology, Vol.2, Issue.6,Jun 2016.
9. Priya taneja, Rajender kumar trivaedi, Rajani Sharma,“A
Proposed Method Of Online Voting By Face
ISSN: 2395-1303 http://www.ijetjournal.org Page 85
View publication stats
Das könnte Ihnen auch gefallen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Example of Flight PMDG MD 11 PDFDokument2 SeitenExample of Flight PMDG MD 11 PDFVivekNoch keine Bewertungen
- The History of Music in Portugal - Owen ReesDokument4 SeitenThe History of Music in Portugal - Owen ReeseugenioamorimNoch keine Bewertungen
- Zigbee Technology:19-3-2010: Seminor Title DateDokument21 SeitenZigbee Technology:19-3-2010: Seminor Title Dateitdep_gpcet7225Noch keine Bewertungen
- Lab 2 - Permeability TestDokument9 SeitenLab 2 - Permeability TestAinur NasuhaNoch keine Bewertungen
- April 2021 BDA Case Study - GroupDokument4 SeitenApril 2021 BDA Case Study - GroupTinashe Chirume1Noch keine Bewertungen
- Channel & Lomolino 2000 Ranges and ExtinctionDokument3 SeitenChannel & Lomolino 2000 Ranges and ExtinctionKellyta RodriguezNoch keine Bewertungen
- Empanelled Hospitals List Updated - 06-12-2022 - 1670482933145Dokument19 SeitenEmpanelled Hospitals List Updated - 06-12-2022 - 1670482933145mechmaster4uNoch keine Bewertungen
- Advanced Physiotherapeutic SyllabusDokument1 SeiteAdvanced Physiotherapeutic SyllabusAnup SharmaNoch keine Bewertungen
- Operational Readiness and Airport TransferDokument2 SeitenOperational Readiness and Airport TransferochweriNoch keine Bewertungen
- Thermodynamic c106Dokument120 SeitenThermodynamic c106Драгослав БјелицаNoch keine Bewertungen
- The Serious Student of HistoryDokument5 SeitenThe Serious Student of HistoryCrisanto King CortezNoch keine Bewertungen
- MiddleWare Technology - Lab Manual JWFILESDokument171 SeitenMiddleWare Technology - Lab Manual JWFILESSangeetha BajanthriNoch keine Bewertungen
- RevlonDokument13 SeitenRevlonSarosh AtaNoch keine Bewertungen
- Medabots-Rokusho Version (European) - Medal Codes (Part 1) (GBA Cheats) - CodeTwink ForumsDokument5 SeitenMedabots-Rokusho Version (European) - Medal Codes (Part 1) (GBA Cheats) - CodeTwink Forumsdegraded 4resterNoch keine Bewertungen
- What Are Some of The Best Books On Computer ScienceDokument9 SeitenWhat Are Some of The Best Books On Computer ScienceSarthak ShahNoch keine Bewertungen
- AAR Shell ProgrammingDokument13 SeitenAAR Shell ProgrammingMarimuthu MuthaiyanNoch keine Bewertungen
- Using Visual Rating To Diagnose DementiaDokument10 SeitenUsing Visual Rating To Diagnose DementiaImágenes Rosendo GarcíaNoch keine Bewertungen
- Perturbation MethodsDokument29 SeitenPerturbation Methodsmhdr100% (1)
- June 2014 (v3) QP - Paper 3 CIE Physics IGCSEDokument20 SeitenJune 2014 (v3) QP - Paper 3 CIE Physics IGCSECole KhantNoch keine Bewertungen
- Chapter 13Dokument15 SeitenChapter 13anormal08Noch keine Bewertungen
- 2432 - Test Solutions - Tsol - 2432 - 21702Dokument5 Seiten2432 - Test Solutions - Tsol - 2432 - 21702Anmol PanchalNoch keine Bewertungen
- FHHR 013 Red Tag Procedure PDFDokument5 SeitenFHHR 013 Red Tag Procedure PDFN3N5YNoch keine Bewertungen
- SRS Document Battle Royale Origins - V2Dokument36 SeitenSRS Document Battle Royale Origins - V2Talha SajjadNoch keine Bewertungen
- Interbond 2340UPC: Universal Pipe CoatingDokument4 SeitenInterbond 2340UPC: Universal Pipe Coatingnoto.sugiartoNoch keine Bewertungen
- Cosmic Handbook PreviewDokument9 SeitenCosmic Handbook PreviewnkjkjkjNoch keine Bewertungen
- SAP HR - Legacy System Migration Workbench (LSMW)Dokument5 SeitenSAP HR - Legacy System Migration Workbench (LSMW)Bharathk KldNoch keine Bewertungen
- O'Dell v. Medallia, Inc. Et Al, 1 - 21-cv-07475, No. 1 (S.D.N.Y. Sep. 7, 2021)Dokument15 SeitenO'Dell v. Medallia, Inc. Et Al, 1 - 21-cv-07475, No. 1 (S.D.N.Y. Sep. 7, 2021)yehuditgoldbergNoch keine Bewertungen
- Marieb ch3dDokument20 SeitenMarieb ch3dapi-229554503Noch keine Bewertungen
- Big Bang Theory EpisodesDokument24 SeitenBig Bang Theory EpisodesBroly dbzNoch keine Bewertungen
- Slides - SARSDokument191 SeitenSlides - SARSCedric PoolNoch keine Bewertungen