Beruflich Dokumente
Kultur Dokumente
Distributed Systems: Chapter 09: Security
Hochgeladen von
Robin Rohit0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
5 Ansichten1 SeiteThis chapter discusses security issues in distributed systems including authentication, access control, encryption, and auditing. Authentication ensures that users are who they claim to be while access control determines what resources users can access. Encryption scrambles data during transmission to prevent unauthorized access and auditing logs activity to detect security breaches or abuse of privileges.
Originalbeschreibung:
Originaltitel
slides.09.pdf
Copyright
© © All Rights Reserved
Verfügbare Formate
PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenThis chapter discusses security issues in distributed systems including authentication, access control, encryption, and auditing. Authentication ensures that users are who they claim to be while access control determines what resources users can access. Encryption scrambles data during transmission to prevent unauthorized access and auditing logs activity to detect security breaches or abuse of privileges.
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
5 Ansichten1 SeiteDistributed Systems: Chapter 09: Security
Hochgeladen von
Robin RohitThis chapter discusses security issues in distributed systems including authentication, access control, encryption, and auditing. Authentication ensures that users are who they claim to be while access control determines what resources users can access. Encryption scrambles data during transmission to prevent unauthorized access and auditing logs activity to detect security breaches or abuse of privileges.
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 1
Distributed Systems
(3rd Edition)
Chapter 09: Security
Version: February 25, 2017
Das könnte Ihnen auch gefallen
- Cyber Risk Management Syllabus 4950 - 6800Dokument9 SeitenCyber Risk Management Syllabus 4950 - 6800leo5880Noch keine Bewertungen
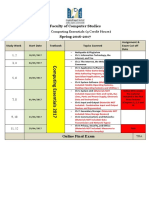
- TU170 Study Calendar 2017 VersionDokument1 SeiteTU170 Study Calendar 2017 VersionMohamed OsamaNoch keine Bewertungen
- ABC Computer WS-12Dokument1 SeiteABC Computer WS-12bershmindsystemNoch keine Bewertungen
- Data Security System (DSS) /data Synchronization: Improving The Performance and Security of MinesightDokument18 SeitenData Security System (DSS) /data Synchronization: Improving The Performance and Security of MinesightNurlanOruzievNoch keine Bewertungen
- Fujitsu e Microsoft Cluster Services With FibreCAT SXDokument17 SeitenFujitsu e Microsoft Cluster Services With FibreCAT SXAlcorNoch keine Bewertungen
- Model of Internetworking SecurityDokument11 SeitenModel of Internetworking SecurityekalveNoch keine Bewertungen
- Apts Kelompok 1Dokument78 SeitenApts Kelompok 1icmi safitriNoch keine Bewertungen
- Activities No. Name Criterion Outcomes MarksDokument2 SeitenActivities No. Name Criterion Outcomes MarksRobin RohitNoch keine Bewertungen
- Eee Staff Induction HandbookDokument27 SeitenEee Staff Induction HandbookRobin RohitNoch keine Bewertungen
- Chrysalis High - Common Brochure 2023-24Dokument4 SeitenChrysalis High - Common Brochure 2023-24Robin RohitNoch keine Bewertungen
- Equivalence and Relation 1Dokument57 SeitenEquivalence and Relation 1Robin RohitNoch keine Bewertungen
- CAS-Soh Orientation Handbook AY2019 2020Dokument29 SeitenCAS-Soh Orientation Handbook AY2019 2020Robin RohitNoch keine Bewertungen
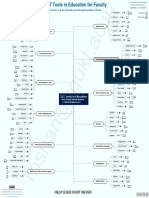
- ICT Tools in Education-RRoshan-SAIDokument15 SeitenICT Tools in Education-RRoshan-SAIRobin RohitNoch keine Bewertungen
- Staff HandbookDokument27 SeitenStaff HandbookRobin RohitNoch keine Bewertungen
- Security+ Guide To Network Security Fundamentals, Third EditionDokument49 SeitenSecurity+ Guide To Network Security Fundamentals, Third EditionRobin RohitNoch keine Bewertungen
- Data Science Applications and Research DirectionsDokument38 SeitenData Science Applications and Research DirectionsRobin Rohit100% (1)
- Public Key Infrastructure 101Dokument130 SeitenPublic Key Infrastructure 101Robin RohitNoch keine Bewertungen
- CS480 Cryptography and Information Security: 6. Data Encryption Standard (DES)Dokument43 SeitenCS480 Cryptography and Information Security: 6. Data Encryption Standard (DES)Robin RohitNoch keine Bewertungen
- The Advanced Encryption StandardDokument47 SeitenThe Advanced Encryption StandardRobin RohitNoch keine Bewertungen
- Security+ Guide To Network Security Fundamentals, Third EditionDokument61 SeitenSecurity+ Guide To Network Security Fundamentals, Third EditionRobin RohitNoch keine Bewertungen
- Security+ Guide To Network Security Fundamentals, Third EditionDokument51 SeitenSecurity+ Guide To Network Security Fundamentals, Third EditionRobin RohitNoch keine Bewertungen
- Security+ Guide To Network Security Fundamentals, Third EditionDokument52 SeitenSecurity+ Guide To Network Security Fundamentals, Third EditionRobin RohitNoch keine Bewertungen
- Security+ Guide To Network Security Fundamentals, Third EditionDokument62 SeitenSecurity+ Guide To Network Security Fundamentals, Third EditionRobin RohitNoch keine Bewertungen
- Chap 1 Wireless Technologies and StandardsDokument40 SeitenChap 1 Wireless Technologies and StandardsRobin RohitNoch keine Bewertungen
- Chap 1 Wireless Technologies and StandardsDokument40 SeitenChap 1 Wireless Technologies and StandardsRobin RohitNoch keine Bewertungen
- Subnetting Worked Examples and Exercises PDFDokument4 SeitenSubnetting Worked Examples and Exercises PDFRobin RohitNoch keine Bewertungen
- Subnetting Worked Examples and Exercises PDFDokument4 SeitenSubnetting Worked Examples and Exercises PDFRobin RohitNoch keine Bewertungen