Beruflich Dokumente
Kultur Dokumente
Diagnostics
Hochgeladen von
Hendra SoenderskovCopyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Diagnostics
Hochgeladen von
Hendra SoenderskovCopyright:
Verfügbare Formate
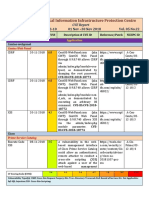
Summary Built: Mon, 22 Jul 2019 22:35:07 +0700
QKView generated: Wed, 17 Jul 2019 15:51:17 +0700
F5 iHealth Report Serial Number: f5-mduh-cntx
Platform: C117
Version: 13.1.0
ibasm-jamsostek-2.brisyariah.co.id
HIGH
H03165684 vCMP vulnerability CVE-2018-5518 Fixes Introduced In
K03165684 Malicious root users with access to a vCMP guest can disrupt service on adjacent vCMP guests running 12.1.3.4
on the same host. Exploiting this vulnerability causes the vcmpd process on the adjacent vCMP guest to 13.1.0.6
restart and produce a core file. This issue is only exploitable on a vCMP guest which is operating in
"host-only" or "bridged" mode. vCMP guests which are "isolated" are not impacted by this issue and do
14.1.0
not provide mechanism to exploit the vulnerability. Guests which are deployed in Appliance mode may
be impacted; however, the exploit is not possible from an Appliance mode guest. To exploit this
vulnerability, root access on a guest system deployed as "host-only" or "bridged" mode is required.
H07127032 TMM vulnerability CVE-2019-6624 Fixes Introduced In
K07127032 An undisclosed traffic pattern sent to a BIG-IP UDP virtual server may lead to a denial-of-service (DoS). 12.1.4.1
13.1.1.5
14.0.0.5
14.1.0.6
15.0.0
H08306700 DHCP client vulnerability CVE-2018-5732 Fixes Introduced In
K08306700 An out-of-bound memory access flaw was found in the way dhclient processed a DHCP response packet. 12.1.3.6
A malicious DHCP server could potentially use this flaw to crash dhclient processes running on DHCP 13.1.0.8
client machines via a crafted DHCP response packet.
14.0.0.3
14.1.0
H11186236 Linux kernel KVM subsystem vulnerability CVE-2019-6974 Fixes Introduced In
K11186236 In the Linux kernel before 4.20.8, kvm_ioctl_create_device in virt/kvm/kvm_main.c mishandles reference
counting because of a race condition, leading to a use-after-free.
H11718033 TMM WebSocket vulnerability CVE-2018-5504 Fixes Introduced In
K11718033 In some circumstances, the Traffic Management Microkernel (TMM) does not properly handle certain 12.1.3.2
malformed WebSocket requests/responses, which allows remote attackers to cause a denial of service 13.0.1
(DoS) or possible remote code execution on the BIG-IP system.
13.1.0.4
14.0.0
H19634255 TMM vulnerability CVE-2018-5535 Fixes Introduced In
K19634255 Specifically crafted HTTP responses, when processed by a Virtual Server with an associated QoE profile
that has Video enabled, may cause TMM to incorrectly buffer response data causing the TMM to restart
resulting in a Denial of Service.
H20134942 SSL Forward Proxy vulnerability CVE-2018-5527 Fixes Introduced In
K20134942 A remote attacker using undisclosed methods againstvirtual servers configured with a Client SSL or 13.1.0.8
Server SSL profile that has the SSL Forward Proxy feature enabled can force the Traffic Management 14.0.0
Microkernel (TMM) to leak memory. As a result, system memory usage increases over time, which may
eventually cause a decrease in performance or a system reboot due to memory exhaustion.
H23566124 BIG-IP TMUI vulnerability CVE-2019-6589 Fixes Introduced In
K23566124 A reflected cross-site scripting (XSS) vulnerability exists in an undisclosed page of the BIG-IP Traffic 11.6.3.3
Management User Interface (TMUI) also known as the BIG-IP Configuration utility. 12.1.4
13.1.1.4
14.0.0.3
14.1.0
Monday 22 July 2019 Page 1 of 21
ibasm-jamsostek-2.brisyariah.co.id
HIGH
H24383845 Bootstrap vulnerability CVE-2019-8331 Fixes Introduced In
K24383845 In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template
attribute.
H25573437 TMM vulnerability CVE-2018-5517 Fixes Introduced In
K25573437 Malformed TCP packets sent to a self IP address or a FastL4 virtual server may cause an interruption of 13.1.0.6
service. The control plane is not exposed to this issue. This issue impacts the data plane virtual servers
and self IPs.
H26618426 Linux SACK Slowness vulnerability CVE-2019-11478 Fixes Introduced In
K26618426 For products with None in the Versions known to be vulnerable column, there is no impact.For products
with ** in the various columns, F5 is still researching the issue and will update this article after
confirming the required information. F5 Support has no additional information about this issue.BIG-
IPThe BIG-IP system has no exposure to this vulnerability within the Traffic Management Microkernel
(TMM), including virtual servers and virtual IP addresses (also known as the data plane). However, the
BIG-IP system is vulnerable via the self IP addresses and the management interface (also known as the
control plane). A remote attacker can exploit this vulnerability to cause a denial of service (DoS) by
sending a sequence of specially crafted TCP packets.Backend systems accessed via a FastL4 virtual
serverBy its nature as a full-proxy, the BIG-IP system protects backend systems accessed through a
standard virtual server, as any attacker's TCP connection would be terminated at the BIG-IP
system. However, backend systems accessed via a FastL4 virtual server (a virtual server configured with
a FastL4 profile) are exposed by default as the attack traffic is forwarded as-is to the backend
system.Traffix SDCA remote attacker can exploit this vulnerability to cause a denial of service by
sending a sequence of specially crafted TCP SACK packets.
H37111863 NodeJS vulnerability CVE-2018-12120 Fixes Introduced In
K37111863 Node.js: All versions prior to Node.js 6.15.0: Debugger port 5858 listens on any interface by default: 13.1.1.5
When the debugger is enabled with `node --debug` or `node debug`, it listens to port 5858 on all 14.1.0.6
interfaces by default. This may allow remote computers to attach to the debug port and evaluate
arbitrary JavaScript. The default interface is now localhost. It has always been possible to start the
15.0.0
debugger on a specific interface, such as `node --debug=localhost`. The debugger was removed in
Node.js 8 and replaced with the inspector, so no versions from 8 and later are vulnerable.
H43121447 BIG-IP Client SSL vulnerability CVE-2018-5502 Fixes Introduced In
K43121447 Attackers may be able to disrupt services on the BIG-IP system with maliciously crafted client certificate. 13.0.1
This vulnerability affects virtual servers associated with Client SSL profile which enables the use of 13.1.0.4
client certificate authentication. Client certificate authentication is not enabled by default in Client SSL
profile. There is no control plane exposure.
14.0.0
H43625118 TMM vulnerability CVE-2018-15317 Fixes Introduced In
K43625118 An attacker sending specially crafted SSL records to a SSL Virtual Server will cause corruption in the 11.6.3.3
SSL data structures leading to intermittent decrypt BAD_RECORD_MAC errors. Clients will be unable to 14.0.0.3
access the application loadbalanced by a virtual server with an SSL profile until tmm is restarted.
14.1.0
H44462254 Reflected Cross-Site Scripting (XSS) vulnerability CVE-2018-15312 Fixes Introduced In
K44462254 A reflected Cross-Site Scripting (XSS) vulnerabilityexists in an undisclosed page of the BIG-IP 12.1.3.7
Configuration utility that allows an authenticated user to execute JavaScript for the currently logged-in 13.1.1.2
user.
14.0.0
14.1.0
H44923228 Oracle Java SE vulnerability CVE-2018-2783 Fixes Introduced In
K44923228 Vulnerability in the Java SE, Java SE Embedded, JRockit component of Oracle Java SE (subcomponent: 12.1.3.7
Security). Supported versions that are affected are Java SE: 6u181, 7u161 and 8u152; Java SE 13.1.1.2
Embedded: 8u152; JRockit: R28.3.17. Difficult to exploit vulnerability allows unauthenticated attacker
with network access via multiple protocols to compromise Java SE, Java SE Embedded, JRockit.
Successful attacks of this
Monday 22 July 2019 Page 2 of 21
ibasm-jamsostek-2.brisyariah.co.id
HIGH
vulnerability can result in unauthorized creation, deletion or modification access to critical data or all
Java SE, Java SE Embedded, JRockit accessible data as well as unauthorized access to critical data or
complete access to all Java SE, Java SE Embedded, JRockit accessible data. Note: Applies to client and
server deployment of Java. This vulnerability can be exploited through sandboxed Java Web Start
applications and sandboxed Java applets. It can also be exploited by supplying data to APIs in the
specified Component without using sandboxed Java Web Start applications or sandboxed Java applets,
such as through a web service. CVSS 3.0 Base Score 7.4 (Confidentiality and Integrity impacts). CVSS
Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:N).
H46940010 TMM vulnerability CVE-2018-5513 Fixes Introduced In
K46940010 A malformed Transport Layer Security (TLS) handshake causes the Traffic Management Microkernel 11.5.6
(TMM) to stop responding, leading to a disruption of service. This issue is only exposed on the data 11.6.3.2
plane when a Proxy SSL configuration is enabled. The control plane is not impacted by this issue.
12.1.3.4
13.0.1
13.1.0.4
14.0.0
H47527163 CGNAT/PPTP vulnerability CVE-2019-6611 Fixes Introduced In
K47527163 When processing certain rare data sequences occurring in PPTP VPN traffic, the BIG-IP system may 11.5.9
execute incorrect logic. The TMM may restart and produce a core file as a result of this condition. The 11.6.4
BIG-IP system provisioned with the CGNAT module and configured with a virtual server using a PPTP
profile is exposed to this vulnerability.
12.1.4.1
13.1.1.5
14.1.0.2
15.0.0
H494013 A password policy is not configured or can be strengthened. Fixes Introduced In
K15497 F5 recommends that you configure a secure password policy for the BIG-IP system.
K5962
There is no password policy in place.
H515699 Multiple MySQL vulnerabilities Fixes Introduced In
K16355 Multiple MySQL vulnerabilities. The CVE numbers included in this advisory are reported to allow
(through undisclosed mechanisms) a remote unauthorized attacker to perform read and write MySQL
access, receive privilege escalation, or cause a denial-of-service (DoS) of the MySQL service and
potentially stop critical data plane services.
H52319810 Apache Portable Runtime vulnerability CVE-2017-12613 Fixes Introduced In
K52319810 When apr_time_exp*() or apr_os_exp_time*() functions are invoked with an invalid month field value in 12.1.3.6
Apache Portable Runtime APR 1.6.2 and prior, out of bounds memory may be accessed in converting 13.1.0.6
this value to an apr_time_exp_t value, potentially revealing the contents of a different static heap value
or resulting in program termination, and may represent an information disclosure or denial of service
14.0.0.3
vulnerability to applications which call these APR functions with unvalidated external input.
H60104355 Linux kernel vulnerability CVE-2017-5970 Fixes Introduced In
K60104355 The ipv4_pktinfo_prepare function in net/ipv4/ip_sockglue.c in the Linux kernel through 4.9.9 allows 13.1.0.8
attackers to cause a denial of service (system crash) via (1) an application that makes crafted system 13.1.1
calls or possibly (2) IPv4 traffic with invalid IP options.
14.0.0.3
14.1.0
H64208870 TMM vulnerability CVE-2018-15319 Fixes Introduced In
K64208870 Malicious requests made to virtual servers with an HTTP profile can cause the TMM to restart. The issue 12.1.3.7
is exposed with the non-default "normalize URI" configuration options used in iRules and/or BIG-IP LTM 13.1.1.2
policies.
14.0.0.3
14.1.0
Monday 22 July 2019 Page 3 of 21
ibasm-jamsostek-2.brisyariah.co.id
HIGH
H64552448 SSL forward proxy vulnerability CVE-2018-5534 Fixes Introduced In
K64552448 Under certain conditions, TMM may core while processing SSL forward proxy traffic. 11.5.7
11.6.3.2
12.1.3.2
13.0.1
13.1.0.6
14.0.0
H64721111 vCMP vulnerability CVE-2018-5531 Fixes Introduced In
K64721111 Through undisclosed methods,adjacent network attackers can cause a denial of service for vCMP guest 11.5.7
and host systems. Attacks must be sourced from an adjacent network (Layer 2). 11.6.3.2
12.1.3.6
13.1.0.8
14.0.0
H686710 The /var/core directory contains core files Fixes Introduced In
K10062 The /var/core directory contains at least one core file. If this system is currently experiencing issues and
a core file was generated within the past 7 days, it could contain valuable diagnostic data. Older files are
likely no longer relevant, and may simply be consuming disk space unnecessarily.
The /var/core directory contains 1 core files for the following binaries that occurred within 7 days before this QKView's collection on
*Jul 17, 2019*:
scriptd:
86744 rw-r--r-- root root 44360497 2019-07-16 00:05:09 scriptd.bld0.0.1868.core.gz
H709036-1 The device SSL certificate is expired, about to expire, or not yet valid Fixes Introduced In
K8187 SSL certificates have specific date ranges that indicate when they are valid. The device certificate is not
K15664 currently valid.
K6353 The device certificate expired on Fri Aug 26 13:18:55 2011.
H72335002 TMM vulnerability CVE-2019-6623 Fixes Introduced In
K72335002 Undisclosed traffic sent to BIG-IP iSession virtual server may cause the Traffic Management Microkernel 12.1.4.1
(TMM) to restart, resulting in a Denial-of-Service (DoS). 13.1.1.5
14.0.0.5
14.1.0.6
15.0.0
H72442354 TMM vulnerability CVE-2018-15320 Fixes Introduced In
K72442354 Undisclosed traffic patterns may lead to denial of service conditions for the BIG-IP system. The 13.1.1.2
configuration which exposes this condition is the BIG-IP self IP address which is part of a VLAN group 14.0.0.3
and has the Port Lockdown setting configured with anything other than "allow-all".
14.1.0
H727910 The configuration contains user accounts with insecure passwords Fixes Introduced In
K11719 The passwords for the accounts listed below are either default passwords or commonly used
passwords, and are susceptible to compromise.
The user account 'root' has a default password
The user account 'admin_ha' has a common password
The user account 'bri' has a common password
H73008537 Apache Tomcat vulnerability CVE-2018-1336 Fixes Introduced In
K73008537 An improper handing of overflow in the UTF-8 decoder with supplementary characters can lead to an 14.1.0
infinite loop in the decoder causing a Denial of Service. Versions Affected: Apache Tomcat 9.0.0.M9 to
9.0.7, 8.5.0 to 8.5.30, 8.0.0.RC1 to 8.0.51, and
Monday 22 July 2019 Page 4 of 21
ibasm-jamsostek-2.brisyariah.co.id
HIGH
7.0.28 to 7.0.86.
H74009656 BIND vulnerability CVE-2018-5743 Fixes Introduced In
K74009656 BIG-IP / BIG-IQ / Enterprise Manager / F5 iWorkflowAn attacker mayexhaust file descriptors available to 14.0.0.5
the named process;as a result,network connections and the management oflog files or zone journal files 14.1.0.6
may be affected.BIG-IQ / Enterprise Manager / F5 iWorkflow may be vulnerable in their default
configuration, but the impact is limited to localhost, thereby, increasing the attack complexity. BIG-
IQ/Enterprise Manager/F5 iWorkflow is not vulnerablein standard and recommended
configurations.Traffix SDCThere is no impact; this F5 productis not affected by this vulnerability.
H74374841 Linux kernel vulnerability (FragmentSmack) CVE-2018-5391 Fixes Introduced In
K74374841 For products with vulnerable versions, this vulnerability allows a remote attacker to disrupt service. This 15.0.0
vulnerability affects only the BIG-IP management port.For products with None in the Versions known to
be vulnerable column, there is no impact.
H78234183 Linux SACK Panic vulnerability CVE-2019-11477 Fixes Introduced In
K78234183 For products with None in the Versions known to be vulnerable column, there is no impact.For products
with ** in the various columns, F5 is still researching the issue and will update this article after
confirming the required information. F5 Support has no additional information about this issue.BIG-
IPThe BIG-IP system has no exposure to this vulnerability within the Traffic Management Microkernel
(TMM), including virtual servers and virtual IP addresses (also known as the data plane). However, the
BIG-IP system is vulnerable via the self IP addresses and the management interface (also known as the
control plane). A remote attacker can exploit this vulnerability to cause a denial of service (DoS) by
sending a sequence of specially crafted TCP packets.Backend systems accessed via a FastL4 virtual
serverBy its nature as a full-proxy, the BIG-IP system protects backend systems accessed through a
standard virtual server, as any attacker's TCP connection would be terminated at the BIG-IP
system. However, backend systems accessed via a FastL4 virtual server(a virtual server configured with
a FastL4 profile) are exposed by default as the attack traffic is forwarded as-is to the backend
system.Traffix SDCA remote attacker can exploit this vulnerability to cause a denial of service by
sending a sequence of specially crafted TCP SACK packets.
H79902360 BIG-IP TMUI vulnerability CVE-2019-6625 Fixes Introduced In
K79902360 A reflected cross-site scripting (XSS) vulnerability exists in an undisclosed page of the BIG-IP Traffic 12.1.4.1
Management User Interface (TMUI) also known as the BIG-IP Configuration utility. 13.1.1.5
14.0.0.5
14.1.0.6
15.0.0
H98528405 BIG-IP BIND vulnerability CVE-2018-5740 Fixes Introduced In
K98528405 A flaw in the "deny-answer-aliases" feature can cause an INSIST assertion failure in named. 14.0.0.3
14.1.0
MEDIUM
H00056379 GNU Binutils vulnerability CVE-2019-9077 Fixes Introduced In
K00056379 An issue was discovered in GNU Binutils 2.32. It is a heap-based buffer overflow in
process_mips_specific in readelf.c via a malformed MIPS option section.
H00854051 Linux kernel vulnerability CVE-2018-13405 Fixes Introduced In
K00854051 The inode_init_owner function in fs/inode.c in the Linux kernel through 4.17.4 allows local users to
create files with an unintended group ownership, in a scenario where a directory is SGID to a certain
group and is writable by a user who is not a member of that group. Here, the non-member can trigger
creation of a plain file whose group ownership is that group. The intended behavior was that the non-
member can trigger creation of a directory (but not a plain file) whose group ownership is that group.
The non-member can escalate privileges by making the plain file executable and SGID.
Monday 22 July 2019 Page 5 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
H01043241 Linux kernel vulnerability CVE-2017-17448 Fixes Introduced In
K01043241 net/netfilter/nfnetlink_cthelper.c in the Linux kernel through 4.14.4 does not require the
CAP_NET_ADMIN capability for new, get, and del operations, which allows local users to bypass
intended access restrictions because the nfnl_cthelper_list data structure is shared across all net
namespaces.
H01713115 BIND vulnerability CVE-2019-6465 Fixes Introduced In
K01713115 BIG-IPAn attacker can exploit this vulnerabilitytorequest and receive a zonetransfer of a DLZ that 11.5.9
bypassestheallow-transfer accesscontrol list.BIG-IQ, F5 iWorkflow, and Enterprise ManagerThese F5 11.6.4
products are not vulnerablein the default, standard, and recommended configurations. This vulnerability
is exposed on these products when a custom configurationis applied to the named service.Traffix
12.1.4.1
SDCThere is no impact for this F5 product; it is not affected by this vulnerability. 13.1.1.5
14.1.0.2
H02236463 Linux kernel vulnerability CVE-2017-9075 Fixes Introduced In
K02236463 The sctp_v6_create_accept_sk function in net/sctp/ipv6.c in the Linux kernel through 4.11.1 mishandles 11.5.9
inheritance, which allows local users to cause a denial of service or possibly have unspecified other 11.6.4
impact via crafted system calls, a related issue to CVE-2017-8890.
12.1.4.1
13.1.1.2
14.0.0.3
14.1.0
H02613439 Linux kernel vulnerability CVE-2017-9076 Fixes Introduced In
K02613439 The dccp_v6_request_recv_sock function in net/dccp/ipv6.c in the Linux kernel through 4.11.1 11.5.9
mishandles inheritance, which allows local users to cause a denial of service or possibly have 11.6.4
unspecified other impact via crafted system calls, a related issue to CVE-2017-8890.
12.1.4.1
13.1.1.2
14.0.0.3
14.1.0
H07702240 BIG-IP Resource Administrator vulnerability CVE-2019-6618 Fixes Introduced In
K07702240 Users with the Resource Administrator role can modify sensitive portions of the file system if provided 11.5.9
Advanced Shell access, such as editing /etc/passwd. This allows modifications to user objects and is 11.6.4
contrary to our definition for the Resource Administrator role restrictions.
12.1.4.1
13.1.1.5
14.1.0.2
15.0.0
H08613310 BIND vulnerability CVE-2017-3145 Fixes Introduced In
K08613310 BIND was improperly sequencing cleanup operations on upstream recursion fetch contexts, leading in 11.6.3.2
some cases to a use-after-free error that can trigger an assertion failure and crash in named. 12.1.3.4
13.1.0.4
14.0.0
H11023978 Linux kernel vulnerability CVE-2017-6346 Fixes Introduced In
K11023978 Race condition in net/packet/af_packet.c in the Linux kernel before 4.9.13 allows local users to cause a
denial of service (use-after-free) or possibly have unspecified other impact via a multithreaded
application that makes PACKET_FANOUT setsockopt system calls.
H11068141 Python vulnerability CVE-2014-9365 Fixes Introduced In
K11068141 The HTTP clients in the (1) httplib, (2) urllib, (3) urllib2, and (4) xmlrpclib libraries in CPython (aka
Python) 2.x before 2.7.9 and 3.x before 3.4.3, when accessing an HTTPS URL, do not (a) check the
certificate against a trust store or verify that the server hostname matches a domain name in the
subject's (b) Common Name or (c) subjectAltName field of the X.509 certificate, which allows man-
in-the-middle attackers to spoof SSL servers via an arbitrary valid certificate.
Monday 22 July 2019 Page 6 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
H11315080 OpenSSH vulnerability CVE-2018-20685 Fixes Introduced In
K11315080 In OpenSSH 7.9, scp.c in the scp client allows remote SSH servers to bypass intended access
restrictions via the filename of . or an empty filename. The impact is modifying the permissions of the
target directory on the client side.
H11330536 BIG-IP Appliance mode vulnerability CVE-2019-6635 Fixes Introduced In
K11330536 When the BIG-IP system is licensed for Appliance mode, a user with either the Administrator or the 11.5.9
Resource Administrator rolecan bypass Appliance mode restrictions. 11.6.4
12.1.4.1
13.1.1.5
14.0.0.5
14.1.0.6
15.0.0
H13534168 GNU Binutils vulnerability CVE-2019-9070 Fixes Introduced In
K13534168 An issue was discovered in GNU libiberty, as distributed in GNU Binutils 2.32. It is a heap-based buffer 14.1.0
over-read in d_expression_1 in cp-demangle.c after many recursive calls.
H14363514 OpenSSL vulnerability CVE-2017-3736 Fixes Introduced In
K14363514 For configurations using iRulesLX, the connection between the iAppsLX administrative 14.1.0
interface and clients is vulnerable to high-complexity attacks on DH parameters used in
the HTTPS session. This vulnerability applies to the following platforms: BIG-IP
I4800, I4600 (C115) BIG-IP I2800, I2600 (C117) BIG-IP I10800, I10600 (C116)
BIG-IP I7800, I7600 (C118)
H15217245 Oracle Java SE vulnerability CVE-2018-2815 Fixes Introduced In
K15217245 Vulnerability in the Java SE, Java SE Embedded, JRockit component of Oracle Java SE (subcomponent: 12.1.3.7
Serialization). Supported versions that are affected are Java SE: 6u181, 7u171, 8u162 and 10; Java SE 13.1.1.2
Embedded: 8u161; JRockit: R28.3.17. Easily exploitable vulnerability allows unauthenticated attacker
with network access via multiple protocols to compromise Java SE, Java SE Embedded, JRockit.
Successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of
service (partial DOS) of Java SE, Java SE Embedded, JRockit. Note: Applies to client and server
deployment of Java. This vulnerability can be exploited through sandboxed Java Web Start applications
and sandboxed Java applets. It can also be exploited by supplying data to APIs in the specified
Component without using sandboxed Java Web Start applications or sandboxed Java applets, such as
through a web service. CVSS 3.0 Base Score 5.3 (Availability impacts). CVSS Vector:
(CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L).
H15526101 Linux kernel vulnerability CVE-2017-8824 Fixes Introduced In
K15526101 The dccp_disconnect function in net/dccp/proto.c in the Linux kernel through 4.14.3 allows local users to 13.1.1.2
gain privileges or cause a denial of service (use-after-free) via an AF_UNSPEC connect system call 14.1.0
during the DCCP_LISTEN state.
H17403481 Linux kernel vulnerability CVE-2018-8897 Fixes Introduced In
K17403481 A statement in the System Programming Guide of the Intel 64 and IA-32 Architectures Software 11.5.9
Developer's Manual (SDM) was mishandled in the development of some or all operating-system 11.6.3.3
kernels, resulting in unexpected behavior for #DB exceptions that are deferred by MOV SS or POP SS, as
demonstrated by (for example) privilege escalation in Windows, macOS, some Xen configurations, or
12.1.3.7
FreeBSD, or a Linux kernel crash. The MOV to SS and POP SS instructions inhibit interrupts (including 13.1.1.2
NMIs), data breakpoints, and single step trap exceptions until the instruction boundary following the 14.0.0.3
next instruction (SDM Vol. 3A; section 6.8.3). (The inhibited data breakpoints are those on memory 14.1.0
accessed by the MOV to SS or POP to SS instruction itself.) Note that debug exceptions are not inhibited
by the interrupt enable (EFLAGS.IF) system flag (SDM Vol. 3A; section 2.3). If the instruction following
the MOV to SS or POP to SS instruction is an instruction like SYSCALL, SYSENTER, INT 3, etc. that
transfers control to the operating system at CPL < 3, the debug exception is delivered after the
transfer to CPL < 3 is complete. OS kernels may not expect this order of events and may therefore
experience unexpected behavior when it occurs.
Monday 22 July 2019 Page 7 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
H18535734 BIG-IP Secure Vault vulnerability CVE-2019-6609 Fixes Introduced In
K18535734 This vulnerability impacts only the iSeries platforms. On these platforms, the secureKeyCapable 12.1.4.1
attribute is not set, which causes the Secure Vault feature to not use F5 hardware support to store the 13.1.1.4
unit key. Instead, the unit key is stored in plaintext on disk, as is the case for Z100 systems. Additionally,
this issue causes the unit key to be stored in UCS files taken on these platforms.
14.1.0.2
15.0.0
H19855851 Intel SPI Flash vulnerability CVE-2017-5703 Fixes Introduced In
K19855851 Configuration of SPI Flash in platforms based on multiple Intel platforms allow a local attacker to alter 14.1.0
the behavior of the SPI flash potentially leading to a Denial of Service.
H20222812 BIG-IP Configuration utility vulnerability CVE-2018-15327 Fixes Introduced In
K20222812 When authenticated administrative users run commands in the Traffic Management User Interface 13.1.1.2
(TMUI), also referred to as the BIG-IP Configuration utility, restrictions on allowed commands may not be 14.0.0.3
enforced.
14.1.0
H20934447 Linux kernel vulnerability CVE-2018-14634 Fixes Introduced In
K20934447 An integer overflow flaw was found in the Linux kernel's create_elf_tables() function. An 11.6.4
unprivileged local user with access to SUID (or otherwise privileged) binary could use this flaw to 13.1.1.5
escalate their privileges on the system. Kernel versions 2.6.x, 3.10.x and 4.14.x are believed to be
vulnerable.
14.1.0.6
15.0.0
H21350967 OpenSSH vulnerability CVE-2019-6111 Fixes Introduced In
K21350967 An issue was discovered in OpenSSH 7.9. Due to the scp implementation being derived from 1983 rcp,
the server chooses which files/directories are sent to the client. However, the scp client only performs
cursory validation of the object name returned (only directory traversal attacks are prevented). A
malicious scp server (or Man-in-The-Middle attacker) can overwrite arbitrary files in the scp client target
directory. If recursive operation (-r) is performed, the server can manipulate subdirectories as well (for
example, to overwrite the .ssh/authorized_keys file).
H21665601 OpenSSL vulnerability CVE-2018-0732 Fixes Introduced In
K21665601 During key agreement in a TLS handshake using a DH(E) based ciphersuite a malicious server can send 11.5.9
a very large prime value to the client. This will cause the client to spend an unreasonably long period of 11.6.3.3
time generating a key for this prime resulting in a hang until the client has finished. This could be
exploited in a Denial Of Service attack. Fixed in OpenSSL 1.1.0i-dev (Affected 1.1.0-1.1.0h). Fixed in
12.1.4
OpenSSL 1.0.2p-dev (Affected 1.0.2-1.0.2o). 13.1.1.2
14.1.0.2
15.0.0
H23030550 Linux kernel vulnerability CVE-2016-8399 Fixes Introduced In
K23030550 An elevation of privilege vulnerability in the kernel networking subsystem could enable a local malicious 11.5.5
application to execute arbitrary code within the context of the kernel. This issue is rated as Moderate 11.6.2
because it first requires compromising a privileged process and current compiler optimizations restrict
access to the vulnerable code. Product: Android. Versions: Kernel-3.10, Kernel-3.18. Android ID: A-
12.1.3
31349935. 13.1.0.8
13.1.1
14.0.0.3
14.1.0
H23328310 TMM vulnerability CVE-2018-15330 Fixes Introduced In
K23328310 Whenavirtual server usesthe inflate functionalityto process a gzip bomb as a payload, the BIG-IP system 12.1.4
will experience a fatal error and may cause the Traffic Management Microkernel (TMM) to produce a core 13.1.1.2
file.
14.0.0.3
14.1.0
H24578092 Linux kernel vulnerability CVE-2017-6001 Fixes Introduced In
K24578092 Race condition in kernel/events/core.c in the Linux kernel before 4.9.7 allows local users to gain
privileges via a crafted application that makes concurrent perf_event_open system calls for moving a
software group into a hardware context.
Monday 22 July 2019 Page 8 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
NOTE: this vulnerability exists because of an incomplete fix for CVE-2016-6786.
H25244852 BIND vulnerability CVE-2018-5745 Fixes Introduced In
K25244852 BIG-IPAn arbitrary attacker may exploit this vulnerability to cause a denial of service (DoS) on the named 11.5.9
service.BIG-IQ, F5 iWorkflow, and Enterprise ManagerThese F5 products are not vulnerablein the default, 11.6.4
standard, and recommended configurations. This vulnerability is exposed on these products when a
custom configurationis applied to the named service.Traffix SDCThere is no impact for thisF5 product; it
12.1.4.1
isnot affected by this vulnerability. 13.1.1.5
14.1.0.2
15.0.0
H27228191 Node.js vulnerability CVE-2018-7159 Fixes Introduced In
K27228191 The HTTP parser in all current versions of Node.js ignores spaces in the `Content-Length` header,
allowing input such as `Content-Length: 1 2` to be interpreted as having a value of `12`. The HTTP
specification does not allow for spaces in the `Content-Length` value and the Node.js HTTP parser has
been brought into line on this particular difference. The security risk of this flaw to Node.js users is
considered to be VERY LOW as it is difficult, and may be impossible, to craft an attack that makes use of
this flaw in a way that could not already be achieved by supplying an incorrect value for `Content-
Length`. Vulnerabilities may exist in user-code that make incorrect assumptions about the potential
accuracy of this value compared to the actual length of the data supplied. Node.js users crafting lower-
level HTTP utilities are advised to re-check the length of any input supplied after parsing is complete.
H27400151 SNMP vulnerability CVE-2019-6613 Fixes Introduced In
K27400151 SNMP may expose sensitive configuration objects over insecure transmission channels. This issue is 11.5.9
exposed when a passphrase is used with various profile types and is accessed using SNMPv2. 11.6.4
12.1.4.1
13.1.1.5
14.0.0
H28003839 tmsh utility vulnerability CVE-2018-15322 Fixes Introduced In
K28003839 A BIG-IP user granted with tmsh access may cause the BIG-IP system to experience denial-of-service 11.5.7
(DoS) when the BIG-IP user uses the tmsh utility to run the editcli preference commandand proceeds to 11.6.3.3
savethe changes to another filename repeatedly. This actionutilizes storage space on the /var partition
and when performed repeatedly causes the /var partition to befull.
12.1.3.6
13.1.0.8
13.1.1
14.0.0.3
14.1.0
H28241423 Linux kernel vulnerability CVE-2018-18559 Fixes Introduced In
K28241423 In the Linux kernel through 4.19, a use-after-free can occur due to a race condition between fanout_add
from setsockopt and bind on an AF_PACKET socket. This issue exists because of the
15fe076edea787807a7cdc168df832544b58eba6 incomplete fix for a race condition. The code mishandles
a certain multithreaded case involving a packet_do_bind unregister action followed by a packet_notifier
register action. Later, packet_release operates on only one of the two applicable linked lists. The
attacker can achieve Program Counter control.
H29146534 SBB Variant 4 vulnerability CVE-2018-3639 Fixes Introduced In
K29146534 Systems with microprocessors utilizing speculative execution and speculative execution of memory
reads before the addresses of all prior memory writes are known may allow unauthorized disclosure of
information to an attacker with local user access via a side-channel analysis, aka Speculative Store
Bypass (SSB), Variant 4.
H29280193 BIG-IP Configuration utility vulnerability CVE-2019-6597 Fixes Introduced In
K29280193 When authenticated administrative users run commands in the Traffic Management User Interface 11.5.9
(TMUI), also referred to as the BIG-IP Configuration utility, restrictions on allowed commands may not be 11.6.3.3
enforced.
12.1.4
13.1.1.2
14.0.0
Monday 22 July 2019 Page 9 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
H30500703 TMUI vulnerability CVE-2018-5511 Fixes Introduced In
K30500703 When authenticated administrative users run commands in the Traffic Management User Interface 13.0.1
(TMUI), also referred to as the BIG-IP Configuration utility, restrictions on allowed commands may not be 13.1.0.4
enforced.
14.0.0
H31603170 Linux kernel vulnerability CVE-2016-7097 Fixes Introduced In
K31603170 The filesystem implementation in the Linux kernel through 4.8.2 preserves the setgid bit during a setxattr 11.5.5
call, which allows local users to gain group privileges by leveraging the existence of a setgid program 11.6.2
with restrictions on execute permissions.
12.1.3
H32485746 OpenSSH vulnerability CVE-2016-10708 Fixes Introduced In
K32485746 sshd in OpenSSH before 7.4 allows remote attackers to cause a denial of service (NULL pointer
dereference and daemon crash) via an out-of-sequence NEWKEYS message, as demonstrated by
Honggfuzz, related to kex.c and packet.c.
H33924005 Oracle Java SE vulnerability CVE-2018-2799 Fixes Introduced In
K33924005 Vulnerability in the Java SE, Java SE Embedded, JRockit component of Oracle Java SE (subcomponent: 12.1.3.7
JAXP). Supported versions that are affected are Java SE: 7u171, 8u162 and 10; Java SE Embedded: 13.1.1.2
8u161; JRockit: R28.3.17. Easily exploitable vulnerability allows unauthenticated attacker with network
access via multiple protocols to compromise Java SE, Java SE Embedded, JRockit. Successful attacks
14.0.0.3
of this vulnerability can result in unauthorized ability to cause a partial denial of service (partial DOS) of 14.1.0
Java SE, Java SE Embedded, JRockit. Note: Applies to client and server deployment of Java. This
vulnerability can be exploited through sandboxed Java Web Start applications and sandboxed Java
applets. It can also be exploited by supplying data to APIs in the specified Component without using
sandboxed Java Web Start applications or sandboxed Java applets, such as through a web service.
CVSS 3.0 Base Score 5.3 (Availability impacts). CVSS Vector:
(CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L).
H34035645 Multiple Wireshark vulnerabilities Fixes Introduced In
K34035645 BIG-IPA remote attacker can transmit crafted packets while a BIG-IP administrator account runs the 12.1.3.6
tshark utility with the affected protocol parsers via Advanced Shell (bash). This causes the tshark utility 13.1.1.2
to stop responding and may allow remote code execution from the BIG-IP administrator account.BIG-IQ,
Enterprise Manager, F5 iWorkflow, ARX, LineRate, and Traffix SDCThere is no impact; these F5 products
14.0.0.3
are not affected by this vulnerability.
H35135935 Side-channel processor vulnerability CVE-2018-9056 (BranchScope) Fixes Introduced In
K35135935 Systems with microprocessors utilizing speculative execution may allow unauthorized disclosure of
information to an attacker with local user access via a side-channel attack on the directional branch
predictor, as demonstrated by a pattern history table (PHT), aka BranchScope.
H35209601 BIG-IP snmpd vulnerability CVE-2019-6606 Fixes Introduced In
K35209601 When processing certainSNMP requests with a request-id of 0, thesnmpdprocess may leak a small 11.6.4
amount of memory. 12.1.4
13.1.1.4
14.0.0.3
14.1.0
H35421172 Excess resource consumption due to low MSS values vulnerability Fixes Introduced In
K35421172 For products with None in the Versions known to be vulnerable column, there is no impact.For products
with ** in the various columns, F5 is still researching the issue and will update this article after
confirming the required information. F5 Support has no additional information about this issue.BIG-
IPThe BIG-IP system has no exposure to this vulnerability within the Traffic Management Microkernel
(TMM), including virtual servers and virtual IP addresses (also known as the data plane). However, the
BIG-IP system is vulnerable via the self IP addresses and the management interface (also known as the
control plane). A remote attacker can exploit this vulnerability to cause a denial of service (DoS) by
sending a sequence of specially crafted TCP packets.Backend systems accessed via a FastL4 virtual
serverBy its nature as a full-proxy, the BIG-IP
Monday 22 July 2019 Page 10 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
system protects backend systems accessed through a standard virtual server, as any attacker's
TCP connection would be terminated at the BIG-IP system. However, backend systems accessed via a
FastL4 virtual server(a virtual server configured with a FastL4 profile) are exposed by default as the
attack traffic is forwarded as-is to the backend system.Traffix SDCA remote attacker can exploit this
vulnerability to cause a denial of service by sending a sequence of specially crafted TCP packets.
H380461 Cookie impersonation detected from remote IP Fixes Introduced In
K10198 The BIG-IP system implements an authentication cache for all Configuration utility requests. The cache
K13048 works by storing information such as a username hash and the remote client's IP address in the memory
file-system. When the client sends a new request, it authenticates to the cache by submitting a
BIGIPAuthCookie to the BIG-IP system. In the event that the client's source IP address changes, the BIG-
IP system invalidates the cache entry and terminates the Configuration utility session. This behavior is
by design and is intended to prevent a user from impersonating or hijacking another user's
Configuration utility session.
On Wed Jul 3 07:59:02 2019 (about 14 days, 7 hours before this qkview was taken) 1 instance of the phrase 'Cookie impersonation
detected from remote IP' was found in the following file: './/var/log/httpd/httpd_errors.3_transformed'
H38941195 BIG-IP Resource Administrator vulnerability CVE-2019-6617 Fixes Introduced In
K38941195 A user with the Resource Administrator role is able to overwrite sensitive low-level files, such as 11.5.9
/etc/passwd, using SFTP to modify user permissions, without Advanced Shell access. This is contrary to 11.6.4
our definition for the Resource Administrator role restrictions.
12.1.4.1
13.1.1.5
14.1.0.2
H40443301 SNMP vulnerability CVE-2019-6640 Fixes Introduced In
K40443301 SNMP exposes sensitive configuration objects over insecure transmission channels. This issue is 11.5.9
exposed when a passphrase is inserted into various profile types and accessed using SNMPv2. 11.6.4
12.1.4.1
13.1.1.5
14.0.0.5
14.1.0.6
15.0.0
H40523020 Linux kernel vulnerability CVE-2018-16658 Fixes Introduced In
K40523020 An issue was discovered in the Linux kernel before 4.18.6. An information leak in
cdrom_ioctl_drive_status in drivers/cdrom/cdrom.c could be used by local attackers to read kernel
memory because a cast from unsigned long to int interferes with bounds checking. This is similar to
CVE-2018-10940.
H41704442 BIG-IP-reflected cross-site scripting vulnerability in an undisclosed Fixes Introduced In
K41704442 A BIG-IP-reflected cross-site scripting (XSS) vulnerability exists in an undisclosed Configuration utility 12.1.3.7
page. 13.1.1.2
14.0.0
H42027747 BIG-IP SNMP vulnerability CVE-2018-15328 Fixes Introduced In
K42027747 The passphrases for SNMPv3 users and trap destinations that are used forauthentication and privacy are 14.1.0
not handled by the BIG-IP system Secure Vault feature; they are written in the clear to the various
configuration files. (CVE-2018-15328)Note: The BIG-IP system Secure Vault feature provides an
additional layer of security to the BIG-IP system by encrypting passwords and passphrases, which the
system stores in its configuration files. For more information, refer to K73034260: Overview of the BIG-IP
system Secure Vault feature.
H42142782 Linux kernel vulnerability CVE-2017-15121 Fixes Introduced In
K42142782 A non-privileged user is able to mount a fuse filesystem on RHEL 6 or 7 and crash a system if an
application punches a hole in a file that does not end aligned to a page boundary.
Monday 22 July 2019 Page 11 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
H42378447 IPsec IKEv1 vulnerability CVE-2018-5389 Fixes Introduced In
K42378447 The Internet Key Exchange v1 main mode is vulnerable to offline dictionary or brute force attacks.
Reusing a key pair across different versions and modes of IKE could lead to cross-protocol
authentication bypasses. It is well known, that the aggressive mode of IKEv1 PSK is vulnerable to offline
dictionary or brute force attacks. For the main mode, however, only an online attack against PSK
authentication was thought to be feasible. This vulnerability could allow an attacker to recover a weak
Pre-Shared Key or enable the impersonation of a victim host or network.
H445453 Updating the BIG-IP ASM attack signatures Fixes Introduced In
K8217 The ASM attack signature file may fail to automatically update, or if automatic updates are not enabled,
attempts to manually update the file may fail.
Attack signatures are set to automatically update daily. The most recent update attempt was on 2019-07-17 03:17:14 and was
unsuccessful for the following reason: Signature file server cannot be reached (Can't get hostname IP address (Servers [198.41.0.4
192.228.79.201 192.33.4.12 199.7.91.13 198.97.190.53 ] did not give answers at /usr/lib/perl5/Net/DNS/Resolver/Recurse.pm line
112.%0aunable to resolve hostname callhome.f5.com via any method%0a)). Please download the Attack Signatures file and install
manually.
H44603900 BIG-IP Configuration utility vulnerability CVE-2019-6598 Fixes Introduced In
K44603900 Malformed requests to the Traffic Management User Interface (TMUI), also referred to as the BIG-IP 11.5.9
Configuration utility,may lead to disruption of TMUI services. This attack requires an authenticated user 11.6.3.3
with any role (other than the No Access role). The No Access user role cannot login and does not have
the access level to perform the attack.
12.1.3.6
13.1.0.8
14.0.0.3
14.1.0
H46524395 Appliance mode vulnerability CVE-2019-6614 Fixes Introduced In
K46524395 Internal methods used to prevent arbitrary file overwrites in Appliance Mode were not fully effective. An 12.1.4.1
authenticated attacker with a high privilege level may be able to bypass protections implemented in 13.1.1.5
appliance mode to overwrite arbitrary system files. (CVE-2019-6614)Note: Appliance mode is designed to
meet the needs of customers in especially sensitive sectors by limiting the BIG-IP system administrative
14.1.0.2
access to match that of a typical network appliance and not a multi-user UNIX device. When a BIG-IP 15.0.0
system is configured in Appliance mode, the Advanced Shell (bash) access to the file system is
restricted. For information about Appliance mode, refer to K12815: Overview of Appliance mode.
H50254952 BIG-IP Configuration utility vulnerability CVE-2018-5523 Fixes Introduced In
K50254952 When authenticated administrative users run commands in the Traffic Management User Interface 11.5.6
(TMUI), also referred to as the BIG-IP Configuration utility, restrictions on allowed commands may not be 11.6.3.2
enforced.
12.1.3.2
13.0.1
13.1.0.4
14.0.0
H51754851 BIG-IP system vulnerability CVE-2018-5512 Fixes Introduced In
K51754851 WhenLarge Receive Offload(LRO)and SYN cookies are enabled (default settings), undisclosed traffic 13.1.0.6
patterns may cause TMM to restart. 14.0.0
H52167636 TMM vulnerability CVE-2017-6153 Fixes Introduced In
K52167636 Features in the BIG-IP system that utilizeinflate functionality directly, via an iRule, or via the inflate code 11.5.6
from PEM module are subjected to a service disruption via a "Zip Bomb" attack. 11.6.3.2
12.1.3.2
13.1.0.4
14.0.0
Monday 22 July 2019 Page 12 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
H54252492 Side-channel processor vulnerability CVE-2018-3693 Fixes Introduced In
K54252492 Systems with microprocessors utilizing speculative execution and branch prediction may allow 15.0.0
unauthorized disclosure of information to an attacker with local user access via a speculative buffer
overflow and side-channel analysis. (CVE-2018-3693 also known as Spectre or Spectre-NG Variant
1.1)Bounds checking bypass - store
H54823184 glibc vulnerability CVE-2019-9169 Fixes Introduced In
K54823184 In the GNU C Library (aka glibc or libc6) through 2.29, proceed_next_node in posix/regexec.c has a heap-
based buffer over-read via an attempted case-insensitive regular-expression match.
H61223103 Linux kernel vulnerability CVE-2017-9074 Fixes Introduced In
K61223103 The IPv6 fragmentation implementation in the Linux kernel through 4.11.1 does not consider that the 13.1.0.8
nexthdr field may be associated with an invalid option, which allows local users to cause a denial of
service (out-of-bounds read and BUG) or possibly have unspecified other impact via crafted socket and
send system calls.
H61429540 Linux kernel vulnerability CVE-2017-9077 Fixes Introduced In
K61429540 The tcp_v6_syn_recv_sock function in net/ipv6/tcp_ipv6.c in the Linux kernel through 4.11.1 mishandles 11.5.9
inheritance, which allows local users to cause a denial of service or possibly have unspecified other 11.6.4
impact via crafted system calls, a related issue to CVE-2017-8890.
12.1.4.1
13.1.1.2
14.0.0.3
14.1.0
H61620494 TMUI vulnerability CVE-2018-15329 Fixes Introduced In
K61620494 When authenticated administrative users run commands in the Traffic Management User Interface 12.1.4
(TMUI), also referred to as the BIG-IP Configuration utility, restrictions on allowed commands may not be 13.1.1.2
enforced.
14.0.0.3
14.1.0
H62750376 RADIUS authentication vulnerability CVE-2018-5515 Fixes Introduced In
K62750376 Using RADIUS authentication responses from a RADIUS server with IPv6 addresses may cause TMM to 13.1.0.6
crash, leading to a failover event.
H647564 Required IP addresses for ConfigSync and device service clustering Fixes Introduced In
K13946 For configuration synchronization (ConfigSync) and device service clustering (DSC) to function
properly, you must have the ConfigSync IP and failover IPs properly configured. Self IP addresses for
ConfigSync and failover must be defined and routable between device group members. To ensure the
most stable network failover configuration for redundant systems, choose two channels for network
failover communication. F5 considers it best practice to define two unicast addresses or a unicast and a
multicast failover address for each device in the device group.
Self IP addresses for ConfigSync and failover must be defined and routable between device group members.
H70321874 Oracle Java SE vulnerability CVE-2018-2795 Fixes Introduced In
K70321874 Vulnerability in the Java SE, Java SE Embedded, JRockit component of Oracle Java SE (subcomponent: 12.1.3.7
Security). Supported versions that are affected are Java SE: 6u181, 7u171, 8u162 and 10; Java SE 13.1.1.2
Embedded: 8u161; JRockit: R28.3.17. Easily exploitable vulnerability allows unauthenticated attacker
with network access via multiple protocols to compromise Java SE, Java SE Embedded, JRockit.
14.1.0
Successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of
service (partial DOS) of Java SE, Java SE Embedded, JRockit. Note: Applies to client and server
deployment of Java. This vulnerability can be exploited through sandboxed Java Web Start applications
and sandboxed Java applets. It can also be exploited by supplying data to APIs in the specified
Component without using sandboxed Java Web Start applications or sandboxed Java applets, such as
through a web service. CVSS 3.0 Base Score 5.3 (Availability impacts). CVSS Vector:
(CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L).
Monday 22 July 2019 Page 13 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
H709036 SSL certificates are expired, about to expire, or are not yet valid Fixes Introduced In
K8187 SSL certificates have specific date ranges that identify when they are valid. The following output lists
K15664 expired, nearly expired, and not yet valid certificates, grouped by their status and whether they are in
use by a BIG-IP traffic object. Please note that in qkview files generated on BIG-IP 11.x systems, this
diagnostic does not calculate whether SSL certificates are not yet valid.
Here is a summary of certificates grouped by status and usage:
Expired SSL certificates associated with one or more profiles, but not in use by any virtual servers:
SSL certificate '/Common/ib_2017_ev_fix(1).crt' has the expiration date Apr 10 23:59:59 2019 GMT
Profile using this certificate: /Common/ib_ssl
SSL certificate '/Common/IB_18.crt' has the expiration date Apr 10 12:00:00 2019 GMT
Profile using this certificate: /Common/IB_SSL_12_12_18
Expired SSL certificate not in use by any profiles or virtual servers:
SSL certificate '/Common/ib_2017_ev.crt' has the expiration date Apr 10 23:59:59 2019 GMT
H726514 There are not enough NTP servers either configured or reliably Fixes Introduced In
K3122 F5 recommends that you configure at least three external NTP servers. If fewer than three Network Time
K10240 Protocol (NTP) servers are reachable, the system will not be able to reliably detect incorrect time
sources.
The configured NTP server is: '172.17.3.8'
The BIG-IP system is not configured to use enough Network Time Protocol servers.
The following NTP server is not responding at all: '172.17.3.8'
H739950 Log messages indicate that large HTTP responses are bypassing BIG- Fixes Introduced In
K42301022 The /var/log/asm file reports that at least one HTTP responses was not parsed by BIG-IP ASM due to
response size. The 'max_filtered_html_length' parameter defines the maximum response size that BIG-IP
ASM can accumulate for the purpose of checking or extracting data from an HTTP response. When that
value is exceeded, the response is passed to the client without BIG-IP ASM processing. By default, the
value of 'max_filtered_html_length' is 50MB.
The /var/log/asm file contains at least one instance of 'ASM filtered HTML exceeded limit'.
H770025 F5 recommends removing orphaned configuration objects Fixes Introduced In
K15335 Over the course of a system's operation, various configuration objects may become orphaned as they
are created and then abandoned to accommodate changing business or application needs. While
orphaned configuration objects do not initially cause problems, if allowed to accumulate, you can
eventually encounter some of the following issues : performance degradation, increased memory and
CPU utilization, and hindered administration from unnecessarily large configurations that can result in
configuration conflicts such as IP address or object name conflicts.
Unused pools: /Common/vs_dev_brisonline, /Common/pool_test, /Common/vs_cms_https, /Common/vs_cms_internet,
/Common/vs_bsmartqa_mb, /Common/vs_sso_https, /Common/pool_vs_cms_https, /Common/vs_bsmartqa_mb2,
/Common/vs_cms_internet_https.
Unused nodes: /Common/172.17.3.25.
Unused policies: /Common/asm_auto_l7_policy_vs_brismartqa_mobile.
H770025-1 F5 recommends removing orphaned configuration objects Fixes Introduced In
K15335 Over the course of a system's operation, various configuration objects may become orphaned as they
K14620 are created and then abandoned to accommodate changing business or application needs. While
orphaned configuration objects do not initially cause problems, if allowed to accumulate, you can
eventually encounter some of the following issues : performance degradation, increased memory and
CPU utilization, and hindered administration from unnecessarily large configurations that can result in
configuration
Monday 22 July 2019 Page 14 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
conflicts such as IP address or object name conflicts.
The following SSL certificates are not currently in use by a virtual server: '/Common/IB_18.crt', '/Common/ib_2017_ev.crt',
'/Common/default.crt', '/Common/CA_IB.crt', '/Common/ib_2017_ev_fix(1).crt', '/Common/ca-bundle.crt', '/Common/f5-irule.crt', and
'/Common/f5-ca-bundle.crt'
H77313277 BIG-IP iControl & tmsh vulnerability CVE-2018-15325 Fixes Introduced In
K77313277 iControl and TMSH usage by authenticated users may leak a small amount of memory when executing 13.1.1.2
commands. 14.0.0.3
14.1.0
H80440915 Linux kernel vulnerability CVE-2017-7889 Fixes Introduced In
K80440915 The mm subsystem in the Linux kernel through 4.10.10 does not properly enforce the 13.1.1.2
CONFIG_STRICT_DEVMEM protection mechanism, which allows local users to read or write to kernel 14.0.0.3
memory locations in the first megabyte (and bypass slab-allocation access restrictions) via an
application that opens the /dev/mem file, related to arch/x86/mm/init.c and drivers/char/mem.c.
14.1.0
H82814400 Appliance mode tmsh vulnerability CVE-2019-6616 Fixes Introduced In
K82814400 Administrative users with TMOS Shell (tmsh) access can overwrite critical system files on the BIG-IP 11.5.9
system, which may result in bypass of whitelist/blacklist restrictions enforced by appliance mode. 11.6.4
12.1.4.1
13.1.1.5
14.1.0.2
15.0.0
H84024430 Linux kernel vulnerability CVE-2017-7542 Fixes Introduced In
K84024430 The ip6_find_1stfragopt function in net/ipv6/output_core.c in the Linux kernel through 4.12.3 allows local 11.5.6
users to cause a denial of service (integer overflow and infinite loop) by leveraging the ability to open a 11.6.3.1
raw socket.
12.1.3.3
13.1.0.8
14.0.0.3
14.1.0
H87659521 Appliance mode tmsh vulnerability CVE-2019-6615 Fixes Introduced In
K87659521 Administrator and Resource Administrator roles may exploit TMOS Shell (tmsh) access to bypass 11.5.9
Appliance mode restrictions on BIG-IP systems. 11.6.4
12.1.4.1
13.1.1.5
14.1.0.2
15.0.0
H91026261 BIG-IP TMM vulnerability CVE-2019-6594 Fixes Introduced In
K91026261 Multipath TCP (MPTCP) does not protect against multiple zero length DATA_FINs in the reassembly 11.6.3.3
queue, which can lead to an infinite loop in some circumstances. 12.1.4
13.1.1.2
14.0.0.3
14.1.0
H91229003 Side-channel processor vulnerabilities CVE-2017-5715, CVE-2017- Fixes Introduced In
K91229003 F5 continues to investigate the impact of the Spectre and Meltdown vulnerabilities on our products. 11.5.6
11.6.3.1
12.1.3.32
13.0.1
13.1.0.4
14.0.2
Monday 22 July 2019 Page 15 of 21
ibasm-jamsostek-2.brisyariah.co.id
MEDIUM
H93144355 Vim / Neovim vulnerability CVE-2019-12735 Fixes Introduced In
K93144355 getchar.c in Vim before 8.1.1365 and Neovim before 0.3.6 allows remote attackers to execute arbitrary OS
commands via the :source! command in a modeline, as demonstrated by execute in Vim, and
assert_fails or nvim_input in Neovim.
H94735334 Linux kernel vulnerability CVE-2018-10883 Fixes Introduced In
K94735334 A flaw was found in the Linux kernel's ext4 filesystem. A local user can cause an out-of-bounds
write in jbd2_journal_dirty_metadata(), a denial of service, and a system crash by mounting and
operating on a crafted ext4 filesystem image.
H95275140 OS Kernel and SMM mode L1 Terminal Fault vulnerability CVE-2018- Fixes Introduced In
K95275140 Systems with microprocessors utilizing speculative execution and address translations may allow
unauthorized disclosure of information residing in the L1 data cache to an attacker with local user
access via a terminal page fault and a side-channel analysis. (CVE-2018-3620 also known as
Foreshadow-NG)
LOW
H00373024 Apache vulnerability CVE-2016-8743 Fixes Introduced In
K00373024 An attacker may be able to perform HTTP request smuggling through specially crafted HTTP requests. 13.1.0.2
For more information about HTTP request smuggling, refer to Section 9.5 Request Smuggling of Internet
Engineering Task Force (RFC 7230).Note: This link takes you to a resource outside of AskF5. The third
party could remove the document without our knowledge.
H02215905 Wireshark vulnerabilities CVE-2018-16056, CVE-2018-16057, and CVE- Fixes Introduced In
K02215905 There is no impact; F5 products are not affected by this vulnerability.
H04912972 NTP vulnerability CVE-2018-7185 Fixes Introduced In
K04912972 The protocol engine in ntp 4.2.6 before 4.2.8p11 allows a remote attackers to cause a denial of service
(disruption) by continually sending a packet with a zero-origin timestamp and source IP address of the
"other side" of an interleaved association causing the victim ntpd to reset its association.
H05513373 Linux kernel vulnerability CVE-2016-9576 Fixes Introduced In
K05513373 The blk_rq_map_user_iov function in block/blk-map.c in the Linux kernel before 4.8.14 does not properly 11.5.5
restrict the type of iterator, which allows local users to read or write to arbitrary kernel memory locations 11.6.2
or cause a denial of service (use-after-free) by leveraging access to a /dev/sg device.
12.1.3
13.0.1
13.1.0.4
14.0.0
H08044291 OpenSSL vulnerability CVE-2018-0739 Fixes Introduced In
K08044291 Constructed ASN.1 types with a recursive definition (such as can be found in PKCS7) could eventually
exceed the stack given malicious input with excessive recursion. This could result in a Denial Of Service
attack. There are no such structures used within SSL/TLS that come from untrusted sources so this is
considered safe. Fixed in OpenSSL 1.1.0h (Affected 1.1.0-1.1.0g). Fixed in OpenSSL 1.0.2o (Affected
1.0.2b-1.0.2n).
H09052213 glibc vulnerability CVE-2015-8777 Fixes Introduced In
K09052213 The process_envvars function in elf/rtld.c in the GNU C Library (aka glibc or libc6) before 2.23 allows
local users to bypass a pointer-guarding protection mechanism via a zero value of the
LD_POINTER_GUARD environment variable.
H12139752 BIG-IP SNMPD vulnerability CVE-2019-6608 Fixes Introduced In
K12139752 Under certain conditions, the snmpd process may leak memory on a multi-blade BIG-IP Virtual Clustered 11.6.4
Multiprocessing (vCMP) guest when processing authorized SNMP requests. 12.1.4
13.1.1.4
Monday 22 July 2019 Page 16 of 21
ibasm-jamsostek-2.brisyariah.co.id
LOW
14.0.0.3
14.1.0
H12252011 OpenSSH vulnerability CVE-2019-6109 Fixes Introduced In
K12252011 An issue was discovered in OpenSSH 7.9. Due to missing character encoding in the progress display, a
malicious server (or Man-in-The-Middle attacker) can employ crafted object names to manipulate the
client output, e.g., by using ANSI control codes to hide additional files being transferred. This affects
refresh_progress_meter() in progressmeter.c.
H13540723 NTP vulnerability CVE-2018-7184 Fixes Introduced In
K13540723 ntpd in ntp 4.2.8p4 before 4.2.8p11 drops bad packets before updating the "received" timestamp, which
allows remote attackers to cause a denial of service (disruption) by sending a packet with a zero-origin
timestamp causing the association to reset and setting the contents of the packet as the most recent
timestamp. This issue is a result of an incomplete fix for CVE-2015-7704.
H15412203 Linux kernel vulnerability CVE-2017-1000365 Fixes Introduced In
K15412203 The Linux Kernel imposes a size restriction on the arguments and environmental strings passed through
RLIMIT_STACK/RLIM_INFINITY (1/4 of the size), but does not take the argument and environment
pointers into account, which allows attackers to bypass this limitation. This affects Linux Kernel
versions 4.11.5 and earlier. It appears that this feature was introduced in the Linux Kernel version 2.6.23.
H15439022 glibc vulnerability CVE-2016-3075 Fixes Introduced In
K15439022 A stack overflow vulnerability (unbounded allocation) in _nss_dns_getnetbyname_r function was found.
H16845 MySQL vulnerability CVE-2015-3152 Fixes Introduced In
K16845 An unspecified vulnerability in the MySQL Client component in Oracle MySQL 5.7.2 and earlier allows an 14.0.0
attacker to downgrade MySQL SSL/TLS connections, snoop database queries and results, or directly
manipulate database contents.
H17075474 glibc vulnerability CVE-2016-4429 Fixes Introduced In
K17075474 Stack-based buffer overflow in the clntudp_call function in sunrpc/clnt_udp.c in the GNU C Library (aka
glibc or libc6) allows remote servers to cause a denial of service (crash) or possibly unspecified other
impact via a flood of crafted ICMP and UDP packets.
H21344224 Lazy FP state restore vulnerability CVE-2018-3665 Fixes Introduced In
K21344224 A Floating-Point (FP) state information leakage flaw was found in the way the Linux kernel saves and 13.1.1.2
restores the FP state during task switch. Linux kernels that follow the "Lazy FP Restore" scheme are 14.0.0.3
vulnerable to the FP state information leakage issue. An unprivileged, local attacker can use this flaw to
read FP state bits by conducting targeted cache side-channel attacks, similar to the Meltdown
14.1.0
vulnerability disclosed earlier this year.
H21462542 OpenSSL vulnerability CVE-2017-3735 Fixes Introduced In
K21462542 While parsing an IPAddressFamily extension in an X.509 certificate, it is possible to do a one-byte 14.0.0
overread. This would result in an incorrect text display of the certificate. This bug has been present
since 2006 and is present in all versions of OpenSSL since then.
H23734425 BIG-IP Configuration utility vulnerability CVE-2019-6600 Fixes Introduced In
K23734425 When remote authentication is enabled for administrative users and all external users are granted the 11.5.9
“guest” role, unsanitized values can be reflected to the client via the login page. This can 11.6.3.3
lead to a cross-site scripting attack against unauthenticated clients.
12.1.4
13.1.1.4
14.0.0.3
14.1.0
Monday 22 July 2019 Page 17 of 21
ibasm-jamsostek-2.brisyariah.co.id
LOW
H25552364 GNU C Library vulnerability CVE-2015-8985 Fixes Introduced In
K25552364 The pop_fail_stack function in the GNU C Library (aka glibc or libc6) allows context-dependent attackers
to cause a denial of service (assertion failure and application crash) via vectors related to extended
regular expression processing.
H31300402 Virtual Machine Manager L1 Terminal Fault vulnerability CVE-2018- Fixes Introduced In
K31300402 Systems with microprocessors utilizing speculative execution and address translations may allow
unauthorized disclosure of information residing in the L1 data cache to an attacker with local user
access with guest OS privilege via a terminal page fault and a side-channel analysis. (CVE-2018-3646also
known as Foreshadow-NG)
H32743437 OpenSSL vulnerability CVE-2016-7056 Fixes Introduced In
K32743437 The signing function in certain OpenSSL versions and forks is vulnerable to timing attacks when signing
with the standardized Elliptic Curve (EC) P-256.
H35040315 glibc vulnerability CVE-2016-10739 Fixes Introduced In
K35040315 In the GNU C Library (aka glibc or libc6) through 2.28, the getaddrinfo function would successfully parse
a string that contained an IPv4 address followed by whitespace and arbitrary characters, which could
lead applications to incorrectly assume that it had parsed a valid string, without the possibility of
embedded HTTP headers or other potentially dangerous substrings.
H37442533 TMOS Shell vulnerability CVE-2018-5516 Fixes Introduced In
K37442533 Authenticated users granted TMOS Shell (tmsh) access can access objects on the file system which 12.1.3
would normally be disallowed by tmsh restrictions. This allows for authenticated, low privileged 13.0.1
attackers to exfiltrate objects on the file system which should not be allowed.
13.1.0.6
13.1.1
14.0.0
H380932 Optional modules or features may be configurable but will not Fixes Introduced In
K16538 Modules or features that are listed as optional modules in the BIG-IP license may be configurable;
however, functionality for these modules or features is not active unless the license includes support for
the module.
The following Optional Modules may be configurable but are unlicensed:
Advanced Protocols
External Interface and Network HSM
Routing Bundle
SSL, Forward Proxy, 2XXX/i2XXX
H42531048 OpenSSH vulnerability CVE-2019-6110 Fixes Introduced In
K42531048 In OpenSSH 7.9, due to accepting and displaying arbitrary stderr output from the server, a malicious
server (or Man-in-The-Middle attacker) can manipulate the client output, for example to use ANSI control
codes to hide additional files being transferred.
H444724 The management interface is allowing access from public IP Fixes Introduced In
K7312 The management interface is ether configured to use a public IP address or is allowing public address to
K13309 access the Configuration Utility.
All IP addresses are allowed to access the Configuration Utility.
H51801290 RSRE Variant 3a vulnerability CVE-2018-3640 Fixes Introduced In
K51801290 Systems with microprocessors utilizing speculative execution and that perform speculative reads of
system registers may allow unauthorized disclosure of system parameters to an attacker with local user
access via a side-channel analysis, aka Rogue System Register Read (RSRE), Variant 3a.
Monday 22 July 2019 Page 18 of 21
ibasm-jamsostek-2.brisyariah.co.id
LOW
H543045 Error Message: Cpu utilization over 300 seconds is %, exceeded log Fixes Introduced In
K67045449 This message can indicate an overloaded system that is attempting to handle more traffic than it is
capable of.
Db variable 'cpu.logthreshold' is set to 80
On Wed Jul 17 16:00:09 2019 (0 seconds before this qkview was taken) 1 instance of the phrase 'Cpu utilization over 300 seconds
is' (refined by pattern 'exceeded log level %d+%%') was found in the following file: './/var/log/ltm'
H54610514 Linux kernel vulnerability CVE-2016-10088 Fixes Introduced In
K54610514 The sg implementation in the Linux kernel through 4.9 does not properly restrict write operations in 11.5.5
situations where the KERNEL_DS option is set, which allows local users to read or write to arbitrary 11.6.2
kernel memory locations or cause a denial of service (use-after-free) by leveraging access to a /dev/sg
device, related to block/bsg.c and drivers/scsi/sg.c. NOTE: this vulnerability exists because of an
12.1.3
incomplete fix for CVE-2016-9576. 13.0.1
13.1.0.4
H606742 MySQL vulnerability CVE-2016-2047 Fixes Introduced In
K53729441 The ssl_verify_server_cert function in sql-common/client.c in MariaDB before 5.5.47, 10.0.x before 14.0.0
10.0.23, and 10.1.x before 10.1.10; Oracle MySQL 5.5.48 and earlier, 5.6.29 and earlier, and 5.7.11 and
earlier; and Percona Server do not properly verify that the server hostname matches a domain name in
the subject's Common Name (CN) or subjectAltName field of the X.509 certificate, which allows man-in-
the-middle attackers to spoof SSL servers via a "/CN=" string in a field in a certificate, as demonstrated
by "/OU=/CN=bar.com/CN=foo.com."
H608114 glibc vulnerability CVE-2016-3706 Fixes Introduced In
K06493172 Stack-based buffer overflow in the getaddrinfo function in sysdeps/posix/getaddrinfo.c in the GNU C 14.1.0
Library (aka glibc or libc6) allows remote attackers to cause a denial of service (crash) via vectors
involving hostent conversion. NOTE: this vulnerability exists because of an incomplete fix for CVE-2013-
4458.
H62201745 OpenSSH vulnerability CVE-2016-10012 Fixes Introduced In
K62201745 The shared memory manager (associated with pre-authentication compression) in sshd in OpenSSH
before 7.4 does not ensure that a bounds check is enforced by all compilers, which might allows local
users to gain privileges by leveraging access to a sandboxed privilege-separation process, related to the
m_zback and m_zlib data structures. (CVE-2016-10012)
H62532311 jQuery vulnerability CVE-2012-6708 Fixes Introduced In
K62532311 jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function 15.0.0
does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery
determined whether the input was HTML by looking for the '<' character anywhere in the
string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed
versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character,
limiting exploitability only to attackers who can control the beginning of a string, which is far less
common.
H638394-26 Error Message: Clock advanced by <number> ticks Fixes Introduced In
K10095 The BIG-IP system daemon heartbeat is a recurring signal that a service generates. The BIG-IP system
continually monitors daemon heartbeat signals for certain daemons, such as the Traffic Management
Microkernel (TMM), to determine whether the service is running. The BIG-IP system logs an error
message when TMM fails to complete its polling loop and update its heartbeat signal within the
threshold period.
Between Thu Jul 11 03:08:54 2019 (about 6 days, 12 hours before this qkview was taken) and Sat Jul 13 00:08:52 2019 (about 4
days, 15 hours before this qkview was taken), 4 instances of the phrase 'Clock advanced by' were found in the following files:
'.//var/log/ltm.5_transformed_truncated' and './/var/log/ltm.7_transformed'
H640816 OpenSSH vulnerability CVE-2016-10011 Fixes Introduced In
K24324390 An information disclosure vulnerability exists in sshd within the realloc() function due to leakage of key 14.1.0
material to privilege-separated child processes when reading keys.
Monday 22 July 2019 Page 19 of 21
ibasm-jamsostek-2.brisyariah.co.id
LOW
H642410 OpenSSL vulnerability CVE-2016-7056 Fixes Introduced In
K32743437 The signing function in certain OpenSSL versions and forks is vulnerable to timing attacks when signing
with the standardized Elliptic Curve (EC) P-256.
H65271605 NTP vulnerability CVE-2016-1549 Fixes Introduced In
K65271605 A malicious authenticated peer can create arbitrarily-many ephemeral associations in order to win the
clock selection algorithm in ntpd in NTP 4.2.8p4 and earlier and NTPsec
3e160db8dc248a0bcb053b56a80167dc742d2b74 and a5fb34b9cc89b92a8fef2f459004865c93bb7f92 and
modify a victim's clock.
H698361 The configuration contains a SNAT automap, but no floating self IP Fixes Introduced In
K7336 When SNAT automap is configured on a redundant BIG-IP system, but a floating self IP address is not
defined on each egress VLAN, load-balanced traffic may use an unintended SNAT address. A floating
self IP address is also required for connection mirroring between members of a redundant system. A
SNAT automap using a floating self IP address on the pool member VLAN has the added benefit of
separating monitor traffic from load-balanced traffic, which eases troubleshooting and helps avoid port
re-use collisions.
The following vlan does not have floating self-IP addresses:
/Common/vlan_ha
H701182 Non-ASCII characters removed from Qkview XML files Fixes Introduced In
Certain Non-ASCII characters cause parsing issues and prevent a ‘qkview’ file from being
processed by iHealth. These characters are removed at upload time so that the ‘qkview’
file can be viewed in iHealth. This is strictly an issue in the ‘qkview’ file, not the system
the ‘qkview’ file was generated from.
Non-ASCII characters were removed from the following XML files:
mcp_module.xml: 1,140 characters removed
asm_module.xml: 6 characters removed
H71877858 glibc vulnerability CVE-2016-8982 Fixes Introduced In
K71877858 Integer overflow in the strxfrm function in the GNU C Library (aka glibc or libc6) before 2.21 allows
context-dependent attackers to cause a denial of service (crash) or possibly execute arbitrary code via a
long string, which triggers a stack-based buffer overflow.
H75543432 PHP vulnerability CVE-2017-11628 Fixes Introduced In
K75543432 In PHP before 5.6.31, 7.x before 7.0.21, and 7.1.x before 7.1.7, a stack-based buffer overflow in the 11.5.7
zend_ini_do_op() function in Zend/zend_ini_parser.c could cause a denial of service or potentially allow 11.6.3.2
executing code. NOTE: this is only relevant for PHP applications that accept untrusted input (instead of
the system's php.ini file) for the parse_ini_string or parse_ini_file function, e.g., a web application
12.1.3.2
for syntax validation of php.ini directives. 13.1.0.8
14.0.0
H77508618 Multiple Oracle MySQL vulnerabilities Fixes Introduced In
K77508618 The CVE numbers included in this security advisory are reported to allow (through undisclosed
mechanisms) an unauthorized remote attacker to gain access to information, receive privilege
escalation, or cause a denial of service (DoS) of the MySQL service.
Monday 22 July 2019 Page 20 of 21
ibasm-jamsostek-2.brisyariah.co.id
LOW
H78131906 Apache HTTPD vulnerability CVE-2018-1301 Fixes Introduced In
K78131906 A specially crafted request could have crashed the Apache HTTP Server prior to version 2.4.30, due to an
out of bound access after a size limit is reached by reading the HTTP header. This vulnerability is
considered very hard if not impossible to trigger in non-debug mode (both log and build level), so it is
classified as low risk for common server usage.
H82570157 NTP vulnerability CVE-2018-7170 Fixes Introduced In
K82570157 ntpd in ntp 4.2.x before 4.2.8p7 and 4.3.x before 4.3.92 allows authenticated users that know the private
symmetric key to create arbitrarily-many ephemeral associations in order to win the clock selection of
ntpd and modify a victim's clock via a Sybil attack. This issue exists because of an incomplete fix
for CVE-2016-1549.
H95343321 Linux kernel vulnerability (SegmentSmack) CVE-2018-5390 Fixes Introduced In
K95343321 Linux kernel versions 4.9+ can be forced to make very expensive calls to tcp_collapse_ofo_queue() and 11.5.9
tcp_prune_ofo_queue() for every incoming packet which can lead to a denial of service. (CVE-2018- 11.6.4
5390)This vulnerability is also referred as SegmentSmack.
12.1.4.1
13.1.1.4
14.1.0
Monday 22 July 2019 Page 21 of 21
Das könnte Ihnen auch gefallen
- Diagnostics 2Dokument27 SeitenDiagnostics 2Karthick CyberNoch keine Bewertungen
- Release Notes PcVue 12020Dokument125 SeitenRelease Notes PcVue 12020Demian HesseNoch keine Bewertungen
- RKY-LX3 6.1.0.108 (C605E1R100P1) Software - Release - Notes - V2.0Dokument7 SeitenRKY-LX3 6.1.0.108 (C605E1R100P1) Software - Release - Notes - V2.0j.pinchettiNoch keine Bewertungen
- HUAWEI MAR-LX1A 10.0.0.167 (C431E8R2P7) Dual EEA Release NotesDokument9 SeitenHUAWEI MAR-LX1A 10.0.0.167 (C431E8R2P7) Dual EEA Release NotesjosebatresNoch keine Bewertungen
- DCS-932L Firmware Release Notes: ContentDokument5 SeitenDCS-932L Firmware Release Notes: Contentdočasná emailová adresaNoch keine Bewertungen
- Release Notes - CDR-790 - CDR-990 - FW1.58.1Dokument5 SeitenRelease Notes - CDR-790 - CDR-990 - FW1.58.1Ivan Felipe Salazar BermudezNoch keine Bewertungen
- Info SecutityDokument5 SeitenInfo SecutityDaud AhmedNoch keine Bewertungen
- Overview of F5 Vulnerabilities (August 2023)Dokument2 SeitenOverview of F5 Vulnerabilities (August 2023)shibosrimanmNoch keine Bewertungen
- Kemp LVM - Configuration - Guide-Web - User - Interface - WUIDokument343 SeitenKemp LVM - Configuration - Guide-Web - User - Interface - WUItNoch keine Bewertungen
- 4 - W4-Intro To Parallel and Distributed ComputingDokument33 Seiten4 - W4-Intro To Parallel and Distributed ComputingsabaNoch keine Bewertungen
- Azure - Windows Server - Host Scan - 2024 Jan q5trvkDokument410 SeitenAzure - Windows Server - Host Scan - 2024 Jan q5trvkeshensanjula2002Noch keine Bewertungen
- Windows Session 0 Isolation Impact On GPU As ServiceDokument3 SeitenWindows Session 0 Isolation Impact On GPU As Service3dmashupNoch keine Bewertungen
- Lightspeed Cache Vulnerability PaperDokument14 SeitenLightspeed Cache Vulnerability PaperMajedNoch keine Bewertungen
- Report A 2022-10-18 11 35 05Dokument12 SeitenReport A 2022-10-18 11 35 05Hand someNoch keine Bewertungen
- HONOR YAL-L21 10.0.0.194 (C431E9R5P1) Software Release NotesDokument9 SeitenHONOR YAL-L21 10.0.0.194 (C431E9R5P1) Software Release NotesKevin Blanquet PoolNoch keine Bewertungen
- How to reboot VPLEX management serverDokument3 SeitenHow to reboot VPLEX management serverVijayenNNoch keine Bewertungen
- Caja Blanca Yhn6enDokument101 SeitenCaja Blanca Yhn6enAlan ColmenaresNoch keine Bewertungen
- FinalDokument22 SeitenFinalAli MagnificaNoch keine Bewertungen
- J Sa SSLVPN 8.0r4 ReleasenotesDokument13 SeitenJ Sa SSLVPN 8.0r4 Releasenotesdaaim0Noch keine Bewertungen
- SAMSUNG Composite USB Driver v4 - 34 - ReleaseNotesDokument31 SeitenSAMSUNG Composite USB Driver v4 - 34 - ReleaseNotesmanole007Noch keine Bewertungen
- Cios Alpha Trouble Shooting ManualDokument92 SeitenCios Alpha Trouble Shooting ManualSohrab AbbasNoch keine Bewertungen
- Network Virtualisation Best Practices and Lessons Learned MigrationDokument19 SeitenNetwork Virtualisation Best Practices and Lessons Learned MigrationShyam KhadkaNoch keine Bewertungen
- ReportDokument7 SeitenReportAznimar ZainuddinNoch keine Bewertungen
- Analisis WEB PABELLONDokument93 SeitenAnalisis WEB PABELLONNelson TorresNoch keine Bewertungen
- HTML5 client for Microsoft Remote Desktop Service - RDR-ITDokument6 SeitenHTML5 client for Microsoft Remote Desktop Service - RDR-ITMarco DutraNoch keine Bewertungen
- Active Directory: Lab 1 QuestionsDokument2 SeitenActive Directory: Lab 1 QuestionsDaphneHarrisNoch keine Bewertungen
- S7plcsim Advanced Readme en-US en-USDokument5 SeitenS7plcsim Advanced Readme en-US en-USNhat Tan MaiNoch keine Bewertungen
- Smart Contract Security Audit DcipDokument16 SeitenSmart Contract Security Audit DcipMuhammad FazliNoch keine Bewertungen
- HUAWEI POT-LX1 10.0.0.260 (C431E8R4P1) Release NotesDokument6 SeitenHUAWEI POT-LX1 10.0.0.260 (C431E8R4P1) Release NotesKrzysztof GorączkoNoch keine Bewertungen
- DCS-932L Firmware Release Notes: ContentDokument5 SeitenDCS-932L Firmware Release Notes: ContentSouheil MhiriNoch keine Bewertungen
- PentestTools WebsiteScanner ReportDokument6 SeitenPentestTools WebsiteScanner ReportOlteanu TeodorNoch keine Bewertungen
- Firmware update for 615 series protection relays improves cyber security and protection functionsDokument9 SeitenFirmware update for 615 series protection relays improves cyber security and protection functionsFrancisco Aguirre VarasNoch keine Bewertungen
- Power Operation 2022 R1 - Release NotesDokument3 SeitenPower Operation 2022 R1 - Release NotesMohammad TahaNoch keine Bewertungen
- Dcs-7110 Revb Release Notes v3.03.04 Beta enDokument4 SeitenDcs-7110 Revb Release Notes v3.03.04 Beta enEhab AbdelsalamNoch keine Bewertungen
- HUAWEI ELE-L29 9.1.0.185 (C10E4R3P2) Software - Release - Notes - V2.3.2Dokument7 SeitenHUAWEI ELE-L29 9.1.0.185 (C10E4R3P2) Software - Release - Notes - V2.3.2edison arriagadaNoch keine Bewertungen
- PentestTools WebsiteScanner ReportDokument7 SeitenPentestTools WebsiteScanner ReportMario Sernaque RumicheNoch keine Bewertungen
- Intelivision 13touch: Global GuideDokument28 SeitenIntelivision 13touch: Global GuideEndra SunandarNoch keine Bewertungen
- Papercut Manual-16-0 PDFDokument1.118 SeitenPapercut Manual-16-0 PDFGecpsEdfPauloGuimarãesNoch keine Bewertungen
- Installion Guide WMS2012 PDFDokument5 SeitenInstallion Guide WMS2012 PDFJose Luis Perez GarciaNoch keine Bewertungen
- HUAWEI STK-LX3 10.0.0.228 (C605E3R2P1) Software Release NotesDokument6 SeitenHUAWEI STK-LX3 10.0.0.228 (C605E3R2P1) Software Release NotesMartín SayagoNoch keine Bewertungen
- CitrixXenApp 6 Scripting With Loadrunner Best Practices v2.31 PDFDokument22 SeitenCitrixXenApp 6 Scripting With Loadrunner Best Practices v2.31 PDFkalyan majeti100% (1)
- Net s7-1200 Modbus TCP en PDFDokument21 SeitenNet s7-1200 Modbus TCP en PDFjotaruiz30Noch keine Bewertungen
- HPE - A00042907en - Us - HPE 3PAR OS 3.2.2 MU6 Patch 99 Release NotesDokument11 SeitenHPE - A00042907en - Us - HPE 3PAR OS 3.2.2 MU6 Patch 99 Release Noteseduardo.rosales.islasNoch keine Bewertungen
- Grundfosliterature 6012934Dokument74 SeitenGrundfosliterature 6012934Aldo BiulchiNoch keine Bewertungen
- Royal Protocol Forcepoint ProjectDokument12 SeitenRoyal Protocol Forcepoint Projectrazzaque003Noch keine Bewertungen
- Manual - IE CS MBGW 2TX 1COM - V1.3.1 - 2023 02 20Dokument51 SeitenManual - IE CS MBGW 2TX 1COM - V1.3.1 - 2023 02 20isaacsavioNoch keine Bewertungen
- Change Notes FW V1200 TP3xxxx GEN3 ENDokument7 SeitenChange Notes FW V1200 TP3xxxx GEN3 ENNestor Dino DominiciNoch keine Bewertungen
- CCV Insync: System ManualDokument27 SeitenCCV Insync: System ManualPreda AndreiNoch keine Bewertungen
- Implementation of A Laboratory Video Monitoring System: Monitor Client Stream Media Server WED Emhedded Server SideDokument4 SeitenImplementation of A Laboratory Video Monitoring System: Monitor Client Stream Media Server WED Emhedded Server SideManyamPradeepNoch keine Bewertungen
- NS SD-WAN 9.2 Lab Guide-v4-FullDokument428 SeitenNS SD-WAN 9.2 Lab Guide-v4-Fullatreus ccNoch keine Bewertungen
- Vmware Vsphere 6.7: Optimize and Scale: Document VersionDokument24 SeitenVmware Vsphere 6.7: Optimize and Scale: Document Versionsybell8Noch keine Bewertungen
- Technical Support Specialist Automation 2019Dokument11 SeitenTechnical Support Specialist Automation 2019luis angel jimenez briones100% (2)
- TME39546Dokument5 SeitenTME39546prasadNoch keine Bewertungen
- M0n0wall HandbookDokument120 SeitenM0n0wall HandbookEDROS SOARESNoch keine Bewertungen
- 201 CertificationDokument43 Seiten201 CertificationSamir JhaNoch keine Bewertungen
- Huawei Mate 10 lite Software Release NotesDokument10 SeitenHuawei Mate 10 lite Software Release Notesezz amroNoch keine Bewertungen
- 16 31 May21 CVEDokument268 Seiten16 31 May21 CVEAkshat SinghNoch keine Bewertungen
- National Critical Infrastructure Protection Centre CVE Report Volume 5 Highlights VulnerabilitiesDokument4 SeitenNational Critical Infrastructure Protection Centre CVE Report Volume 5 Highlights VulnerabilitiesRavi SankarNoch keine Bewertungen
- Virtual Roaming Systems for GSM, GPRS and UMTS: Open Connectivity in PracticeVon EverandVirtual Roaming Systems for GSM, GPRS and UMTS: Open Connectivity in PracticeBewertung: 5 von 5 Sternen5/5 (1)
- IBM WebSphere Application Server Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesVon EverandIBM WebSphere Application Server Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesNoch keine Bewertungen
- (SSH Client, X-Server and Networking Tools) : Dede 172.18.151.193Dokument2 Seiten(SSH Client, X-Server and Networking Tools) : Dede 172.18.151.193Hendra SoenderskovNoch keine Bewertungen
- (SSH Client, X-Server and Networking Tools) : Dede 172.18.151.193Dokument10 Seiten(SSH Client, X-Server and Networking Tools) : Dede 172.18.151.193Hendra SoenderskovNoch keine Bewertungen
- Junos OS: UTM Sophos Antivirus Protection For Security DevicesDokument134 SeitenJunos OS: UTM Sophos Antivirus Protection For Security DevicesHendra SoenderskovNoch keine Bewertungen
- Huntsville Speaker PresentationsDokument72 SeitenHuntsville Speaker PresentationsHendra SoenderskovNoch keine Bewertungen
- (SSH Client, X-Server and Networking Tools) : Dede 172.18.151.194Dokument3 Seiten(SSH Client, X-Server and Networking Tools) : Dede 172.18.151.194Hendra SoenderskovNoch keine Bewertungen
- File - C - Users - X23 - Desktop - F5 - ASM Training PDFDokument1 SeiteFile - C - Users - X23 - Desktop - F5 - ASM Training PDFHendra SoenderskovNoch keine Bewertungen
- JNCIA Junos 2Dokument13 SeitenJNCIA Junos 2Hendra SoenderskovNoch keine Bewertungen
- (SSH Client, X-Server and Networking Tools) : Dede 172.18.151.194Dokument2 Seiten(SSH Client, X-Server and Networking Tools) : Dede 172.18.151.194Hendra SoenderskovNoch keine Bewertungen
- Pearson VUE Voucher Sales Order: Bill ToDokument1 SeitePearson VUE Voucher Sales Order: Bill ToHendra SoenderskovNoch keine Bewertungen
- Ivan Cahya Permana: Curriculum VitaeDokument6 SeitenIvan Cahya Permana: Curriculum VitaeAri TriwibowoNoch keine Bewertungen
- Ivan Cahya Permana: Curriculum VitaeDokument6 SeitenIvan Cahya Permana: Curriculum VitaeAri TriwibowoNoch keine Bewertungen
- Cisco Certified Network Associate Study Guide 7th Edition PdfDokument4 SeitenCisco Certified Network Associate Study Guide 7th Edition PdfHendra SoenderskovNoch keine Bewertungen
- Activity Report - Ipnet PDFDokument1 SeiteActivity Report - Ipnet PDFHendra SoenderskovNoch keine Bewertungen
- Juniper PracticeTest-rizkiDokument42 SeitenJuniper PracticeTest-rizkiHendra SoenderskovNoch keine Bewertungen
- VCE SimulatorDokument1 SeiteVCE SimulatorHendra SoenderskovNoch keine Bewertungen
- Palo Alto Ujian KuDokument7 SeitenPalo Alto Ujian KuHendra SoenderskovNoch keine Bewertungen
- SdfdsfsDokument1 SeiteSdfdsfsHendra SoenderskovNoch keine Bewertungen
- Palo Alto Ujian KuDokument7 SeitenPalo Alto Ujian KuHendra SoenderskovNoch keine Bewertungen
- Activity Report-DikonversiDokument1 SeiteActivity Report-DikonversiHendra SoenderskovNoch keine Bewertungen
- Implementation Guide For F5 Big-Ip Apm and SparkgatewayDokument12 SeitenImplementation Guide For F5 Big-Ip Apm and SparkgatewayHendra SoenderskovNoch keine Bewertungen
- F 5 BCGTMDokument157 SeitenF 5 BCGTMHendra SoenderskovNoch keine Bewertungen
- FGT Overview and DesignDokument11 SeitenFGT Overview and DesignUmAiR ANoch keine Bewertungen
- Readme 1 STDokument3 SeitenReadme 1 STmas_b9191838Noch keine Bewertungen
- AsdDokument518 SeitenAsdHendra SoenderskovNoch keine Bewertungen
- AsdasDokument2 SeitenAsdasHendra SoenderskovNoch keine Bewertungen
- f5 CheatDokument8 Seitenf5 CheatSureshReddy0% (1)
- INE Wireshark Technologies 1.1.1 PDFDokument11 SeitenINE Wireshark Technologies 1.1.1 PDFHendra SoenderskovNoch keine Bewertungen
- Bv9ARM-9 9 6Dokument199 SeitenBv9ARM-9 9 6Ali SayedNoch keine Bewertungen
- HahaDokument5 SeitenHahaHendra SoenderskovNoch keine Bewertungen
- Cyber ArkDokument2 SeitenCyber ArkHendra SoenderskovNoch keine Bewertungen
- Embedded Systems: Design, Analysis and VerificationDokument368 SeitenEmbedded Systems: Design, Analysis and Verificationmiladh1Noch keine Bewertungen
- Advanced Junos Security AjsecDokument3 SeitenAdvanced Junos Security Ajsecpismo76aNoch keine Bewertungen
- A To Z Computer Related Full FormDokument20 SeitenA To Z Computer Related Full FormNoob PlayerNoch keine Bewertungen
- Introduction To HCIDokument47 SeitenIntroduction To HCICHaz LinaNoch keine Bewertungen
- Teradata System Maintenance and Operations ProceduresDokument8 SeitenTeradata System Maintenance and Operations ProceduresKranthi Kumar.gNoch keine Bewertungen
- IBS Components with 4.3-10 Interface Combiners Smart POIDokument6 SeitenIBS Components with 4.3-10 Interface Combiners Smart POIdenny gloriousNoch keine Bewertungen
- 9A05602 Unix InternalsDokument4 Seiten9A05602 Unix InternalssivabharathamurthyNoch keine Bewertungen
- Logitech Z 5500 Service Manual: Read/DownloadDokument2 SeitenLogitech Z 5500 Service Manual: Read/DownloadMy Backup17% (6)
- Juniper Exam JN0-347 Practice TestDokument44 SeitenJuniper Exam JN0-347 Practice TestVeronag GonzálezNoch keine Bewertungen
- Ospf Basic Lab WalkthroughDokument7 SeitenOspf Basic Lab WalkthroughAek BenabadjaNoch keine Bewertungen
- Quick Start Guide - Barco - Encore E2Dokument2 SeitenQuick Start Guide - Barco - Encore E2OnceUponAThingNoch keine Bewertungen
- Deleted AUTOID99HC Series User Manual V1.2Dokument104 SeitenDeleted AUTOID99HC Series User Manual V1.2Tien BuiNoch keine Bewertungen
- ITIL-enabled Legacy Integration For Change and Release ManagementDokument10 SeitenITIL-enabled Legacy Integration For Change and Release ManagementNexio Technologies Inc.Noch keine Bewertungen
- Chapter 2 - TCP/IP ArchitectureDokument22 SeitenChapter 2 - TCP/IP ArchitectureJuan SantiagoNoch keine Bewertungen
- TSReader Hardware SupportDokument24 SeitenTSReader Hardware SupportDramane BonkoungouNoch keine Bewertungen
- DNS 3GPPDokument54 SeitenDNS 3GPPupeshalaNoch keine Bewertungen
- PS2 Keyboard Atmega32Dokument10 SeitenPS2 Keyboard Atmega32Richard Vicky Shendy WijayaNoch keine Bewertungen
- Cs6008 Human Computer Interaction L T P C 3 0 0 3Dokument1 SeiteCs6008 Human Computer Interaction L T P C 3 0 0 3Sasi RajiNoch keine Bewertungen
- TruControl 1000Dokument68 SeitenTruControl 1000Buentello B Gonzalez100% (2)
- KS Router multiscript combines MIDI channels into oneDokument2 SeitenKS Router multiscript combines MIDI channels into onecuentaNoch keine Bewertungen
- SAP LSMW Data Migration Tool Transfers Legacy Data with No CodingDokument4 SeitenSAP LSMW Data Migration Tool Transfers Legacy Data with No CodingSrinivasa Rao MullapudiNoch keine Bewertungen
- ST7735Dokument167 SeitenST7735jatonfireNoch keine Bewertungen
- Price ListDokument17 SeitenPrice ListvsathyapNoch keine Bewertungen
- How Orchard Works Orchard Foundations: Love This PDF? Add It To Your Reading List!Dokument8 SeitenHow Orchard Works Orchard Foundations: Love This PDF? Add It To Your Reading List!Amanda HarveyNoch keine Bewertungen
- Examining Data Runs of A Fragmented File in NTFSDokument15 SeitenExamining Data Runs of A Fragmented File in NTFSCarlos CajigasNoch keine Bewertungen
- Code Blocks SourceForgeDokument2 SeitenCode Blocks SourceForgesabar5Noch keine Bewertungen
- Drive TestDokument23 SeitenDrive TestJohnson Akanbi0% (2)
- Atmel Avr Start Programming in CDokument11 SeitenAtmel Avr Start Programming in CJaak KõusaarNoch keine Bewertungen
- 13 Effective Security Controls For ISO 27001 ComplianceDokument55 Seiten13 Effective Security Controls For ISO 27001 ComplianceRobert Mota HawksNoch keine Bewertungen
- Network Security ChallengesDokument26 SeitenNetwork Security ChallengesMfonobong John EkottNoch keine Bewertungen