Beruflich Dokumente
Kultur Dokumente
Tips For Choosing A Next-Generation Firewall
Hochgeladen von
Akram M. AlmotaaOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Tips For Choosing A Next-Generation Firewall
Hochgeladen von
Akram M. AlmotaaCopyright:
Verfügbare Formate
5 Tips for Choosing a
Next-Generation Firewall
Invest in a threat-focused Next-Generation Firewall (NGFW). Ask if it delivers…
Resources
Integrated Threat Defense
Get actionable, multi-layered protection. Requirements When Considering a
Next-Generation Firewall
Today’s multi-vector and persistent threats slip through gaps in protection and evade detection. A threat-focused
NGFW provides best-in-class security technologies that work together across the network and endpoints and are White Paper - Get the full checklist to
managed through a central console. Built on a comprehensive stateful firewall foundation, threat-focused NGFW protect your business from attacks.
technologies should include: Read Now.
Next-Generation IPS Cisco ASA Excels in Firewall Tests
Advanced Malware Protection
NSS Labs ranks Cisco highest in the
Application Visibility and Control most rigorous NGFW testing to date.
Reputation-based URL filtering Watch the video.
Application-level VPN
Cisco ASA NGFW Website
With integrated threat and advanced malware protection that continuously correlates threat intelligence across
security layers, you can identify and protect against sophisticated attacks. Stay up-to-date on the latest trends
and see what’s new in security from
Cisco.
Learn More.
Actionable Indicators of Compromise
Accelerate malware detection to mitigate risk.
The current industry standard time to detect a threat is between 100 to 200 days; that’s far too long. An NGFW should provide actionable indicators of
compromise (IoCs) that:
Correlate network and endpoint security intelligence
Provide highly accurate visibility into suspect and malicious file and host behavior
Prioritize infected hosts for rapid remediation
Actionable IoCs let you see malware activity on hosts and endpoints, understand the impact, and quickly contain and remediate.
Comprehensive Network Visibility
Increase security effectiveness with a holistic view.
You can’t protect what you can’t see. You need to monitor what’s happening on your network at all times.
An NGFW should provide full contextual awareness of:
Users, operating systems, and devices
Communications between virtual machines
Threats and vulnerabilities
Applications and website access
File transfers, and more
This level of insight helps you identify and address security gaps and fine-tune policies so as to reduce the number of significant events
requiring additional action.
Reduced Complexity and Costs
Unify security layers and automate for efficiencies.
A combination of advanced threats and a shortage of skilled IT security professionals is stretching IT departments to the max.
Look for an NGFW that:
Consolidates multiple layers of defenses on a single platform
Delivers consistent and robust security at scale
Automates routine security tasks like impact assessment, policy tuning, and user identification
By reducing complexity and costs your team is freed up to focus on events that matter most.
Integration with Third-Party Solutions
Maximize existing security investments.
You need to be able to share intelligence and better leverage existing security technologies to consolidate and streamline response.
Look for an NGFW that is open and integrates smoothly with an ecosystem of third-party security solutions like:
Vulnerability management systems
Network visualization and SIEM systems
Workflow remediation and ticketing systems
Network access control (NAC), and more
Third-party solution integration reduces your IT burden and total cost of ownership (TCO) and strengthens multi-layered protection.
Attacks will continue to evolve as will the IT environment you need to protect. Make sure the NGFW you select provides
tightly integrated, multi-layered threat protection. By sharing context and intelligence among security functions you
accelerate threat detection and response across your organization, and get the most from your investments.
It’s not what we make; Visit www.cisco.com/go/ngfw
it’s what we make possible. Follow us on Twitter @CiscoSecurity
Making security everywhere a reality. © 2015 Cisco and/or its affiliates. All rights reserved. Cisco Public
Das könnte Ihnen auch gefallen
- What Is A Firewall - CiscoDokument4 SeitenWhat Is A Firewall - CiscoShanie MsipaNoch keine Bewertungen
- Industry'S Most Effective NGFW Using The Fortinet Enterprise Firewall SolutionDokument3 SeitenIndustry'S Most Effective NGFW Using The Fortinet Enterprise Firewall SolutionLuis GutierrezNoch keine Bewertungen
- Cisco Firepower Next-Generation Firewall (NGFW) Data Sheet - CiscoDokument37 SeitenCisco Firepower Next-Generation Firewall (NGFW) Data Sheet - CiscoRajeev SinghalNoch keine Bewertungen
- Cisco Asa FirepowerDokument11 SeitenCisco Asa FirepowerMadhu ThamatamNoch keine Bewertungen
- Next Generation FirewallDokument6 SeitenNext Generation FirewallFelippe CoelhoNoch keine Bewertungen
- Cisco Firewall ComparisonDokument17 SeitenCisco Firewall Comparisona2z sourcing & solutionsNoch keine Bewertungen
- FortiGuard Security ServicesDokument8 SeitenFortiGuard Security Servicesdoris marcaNoch keine Bewertungen
- CatalogDokument11 SeitenCatalogBlankNoch keine Bewertungen
- Protecting Your Network From The Inside-Out: Internal Segmentation Firewall (ISFW)Dokument8 SeitenProtecting Your Network From The Inside-Out: Internal Segmentation Firewall (ISFW)ds2084Noch keine Bewertungen
- Security Advisory Issue 2Dokument10 SeitenSecurity Advisory Issue 2Vijendra RawatNoch keine Bewertungen
- Asa Firepower PDFDokument12 SeitenAsa Firepower PDFgacrNoch keine Bewertungen
- Forrester Best Defense NGFW Zero Trust Security Executive SummaryDokument3 SeitenForrester Best Defense NGFW Zero Trust Security Executive SummaryAhsan ZiaNoch keine Bewertungen
- Cisco Next Generation FirewallsDokument41 SeitenCisco Next Generation FirewallsPraveen RaiNoch keine Bewertungen
- TC - SECVFTD25 - PPT - Securing Enterprise Networks With Cisco Firepower Threat Defense Virtual Appliance v25 - drn1 - 4 PDFDokument303 SeitenTC - SECVFTD25 - PPT - Securing Enterprise Networks With Cisco Firepower Threat Defense Virtual Appliance v25 - drn1 - 4 PDFRayhan100% (1)
- Dell Soniwall Nsa 3600Dokument15 SeitenDell Soniwall Nsa 3600Felipe OchoaNoch keine Bewertungen
- Cisco Umbrella at A GlanceDokument4 SeitenCisco Umbrella at A GlanceKiril PetkovNoch keine Bewertungen
- Secure Endpoint Buyers GuideDokument8 SeitenSecure Endpoint Buyers GuideEddy StoicaNoch keine Bewertungen
- FortiGate VM ESXiDokument8 SeitenFortiGate VM ESXiEddy StoicaNoch keine Bewertungen
- FortiGate VM ESXiDokument8 SeitenFortiGate VM ESXiAliNoch keine Bewertungen
- Next Generation Firewalls and Intelligent Networking: MSCS Research ProposalDokument8 SeitenNext Generation Firewalls and Intelligent Networking: MSCS Research ProposalSalman AwanNoch keine Bewertungen
- Transforming Your Security: A New Era in Enterprise FirewallsDokument14 SeitenTransforming Your Security: A New Era in Enterprise Firewallsnirushan456Noch keine Bewertungen
- Cisco Firepower Management CenterDokument16 SeitenCisco Firepower Management CenterAhmad BayhakiNoch keine Bewertungen
- CISCO Firepower NXGFWDokument24 SeitenCISCO Firepower NXGFWkishorsriramNoch keine Bewertungen
- The Umbrella Advantage What Makes Cisco Umbrella UniqueDokument14 SeitenThe Umbrella Advantage What Makes Cisco Umbrella Uniquepaulestephan76Noch keine Bewertungen
- Datanet AsaDokument40 SeitenDatanet AsaAntoniaNoch keine Bewertungen
- Sonicwall Network Security Appliance (Nsa) SeriesDokument14 SeitenSonicwall Network Security Appliance (Nsa) Seriesandroid klien01Noch keine Bewertungen
- Cisco Umbrella at A GlanceDokument4 SeitenCisco Umbrella at A GlanceAniket DeshpandeNoch keine Bewertungen
- FortiGate 1000DDokument6 SeitenFortiGate 1000DManuel HíjarNoch keine Bewertungen
- At A Glance c45 738938Dokument2 SeitenAt A Glance c45 738938Irvin TaypeNoch keine Bewertungen
- Fortigate - VM On Amazon Web Services: Data SheetDokument6 SeitenFortigate - VM On Amazon Web Services: Data SheetLuis RodriguesNoch keine Bewertungen
- Fortigate - VM On Amazon Web Services: Data SheetDokument6 SeitenFortigate - VM On Amazon Web Services: Data SheettantyoNoch keine Bewertungen
- Fortigate 100F Series: Data SheetDokument6 SeitenFortigate 100F Series: Data SheetAbdul Rahman ZainalNoch keine Bewertungen
- Protecting Hybrid Clouds InfographicDokument1 SeiteProtecting Hybrid Clouds Infographicabuoman08Noch keine Bewertungen
- Next Generation FirewallDokument8 SeitenNext Generation FirewallgeekNoch keine Bewertungen
- At A Glance c45 736624Dokument6 SeitenAt A Glance c45 736624ShanehalNoch keine Bewertungen
- Cisco Umbrella at A Glance: Security ChallengesDokument2 SeitenCisco Umbrella at A Glance: Security ChallengesSafia BOUZARNoch keine Bewertungen
- Fortiguard Labs Services & BundlesDokument2 SeitenFortiguard Labs Services & BundlesM3iatNoch keine Bewertungen
- Brksec 2028 PDFDokument133 SeitenBrksec 2028 PDFMadhu ThamatamNoch keine Bewertungen
- Cisco Defense Orchestrator: BenefitsDokument2 SeitenCisco Defense Orchestrator: Benefitspravin1350Noch keine Bewertungen
- Cisco Security Pocket GuideDokument24 SeitenCisco Security Pocket GuideEmmanuel Zama100% (1)
- Vanderbilt #Readyforanychallenge: Cybersecurity: How To Implement Best PracticesDokument6 SeitenVanderbilt #Readyforanychallenge: Cybersecurity: How To Implement Best Practicescs44Noch keine Bewertungen
- Protectwise 0 - ProtectWise Datasheet NDR Network Detection ResponseDokument2 SeitenProtectwise 0 - ProtectWise Datasheet NDR Network Detection Responseatul2651Noch keine Bewertungen
- En Secur BR NTWRKBSD ScrtyDokument16 SeitenEn Secur BR NTWRKBSD ScrtyUmutNoch keine Bewertungen
- Integrated Security:: Defending Against Evolving Threats With Self-Defending NetworksDokument4 SeitenIntegrated Security:: Defending Against Evolving Threats With Self-Defending NetworksNilesh KutariyarNoch keine Bewertungen
- Fortigate 600E Series: Data SheetDokument6 SeitenFortigate 600E Series: Data SheetEliranNoch keine Bewertungen
- CiscoWebSecurityAppliance Datasheet c78 729630Dokument8 SeitenCiscoWebSecurityAppliance Datasheet c78 729630chompitaNoch keine Bewertungen
- Internet Edge Design Oct 2015Dokument25 SeitenInternet Edge Design Oct 2015bigdrsmithNoch keine Bewertungen
- Cisco Asa With Firepower Services: Superior Multilayered ProtectionDokument19 SeitenCisco Asa With Firepower Services: Superior Multilayered ProtectionJose Luis Gutierrez GonzalezNoch keine Bewertungen
- Internal Segmentation Firewall: Security Where You Need It, When You Need ItDokument12 SeitenInternal Segmentation Firewall: Security Where You Need It, When You Need ItJulio JordanNoch keine Bewertungen
- Cisco Umbrella Dns Security Advantage PackageDokument4 SeitenCisco Umbrella Dns Security Advantage PackageKiril PetkovNoch keine Bewertungen
- Fortigate 400E Series: Data SheetDokument6 SeitenFortigate 400E Series: Data SheetKL SimNoch keine Bewertungen
- FortiGate 7000 Series BundleDokument9 SeitenFortiGate 7000 Series BundlepepeNoch keine Bewertungen
- Cisco Secure Firewall Threat Defense Virtual (Formerly FTDV/NGFWV)Dokument12 SeitenCisco Secure Firewall Threat Defense Virtual (Formerly FTDV/NGFWV)Wagner MarlonNoch keine Bewertungen
- Fortios 7.0: Fortinet'S Security Operating SystemDokument14 SeitenFortios 7.0: Fortinet'S Security Operating Systembalj balhNoch keine Bewertungen
- Fortios 7.0: Fortinet'S Security Operating SystemDokument14 SeitenFortios 7.0: Fortinet'S Security Operating SystemAbdul Rahman ZainalNoch keine Bewertungen
- Gartner NGFW Research NoteDokument3 SeitenGartner NGFW Research NoteJay JayNoch keine Bewertungen
- Check Point Integrated Security Architecture - BrochureDokument8 SeitenCheck Point Integrated Security Architecture - BrochureLuis RodriguesNoch keine Bewertungen
- FortiGate 500EDokument6 SeitenFortiGate 500ETv OrangeNoch keine Bewertungen
- Fortigate 2600f SeriesDokument6 SeitenFortigate 2600f SeriesAzhar HussainNoch keine Bewertungen
- Sensor Installation ManualDokument13 SeitenSensor Installation ManualAkram M. AlmotaaNoch keine Bewertungen
- CCTV RFP VSP CityDokument76 SeitenCCTV RFP VSP CityAkram M. AlmotaaNoch keine Bewertungen
- 2RFP FOR PROVISION OF A BULK SMS SMS SHORT CODE AND USSD GATEWAY SERVICE April 2021Dokument38 Seiten2RFP FOR PROVISION OF A BULK SMS SMS SHORT CODE AND USSD GATEWAY SERVICE April 2021Akram M. AlmotaaNoch keine Bewertungen
- Infrastructure Team Leader Position DescriptionDokument7 SeitenInfrastructure Team Leader Position DescriptionAkram M. AlmotaaNoch keine Bewertungen
- RFP - USSD Application Implementation RDokument17 SeitenRFP - USSD Application Implementation RAkram M. AlmotaaNoch keine Bewertungen
- Cloud ServicesDokument4 SeitenCloud ServicesAkram M. AlmotaaNoch keine Bewertungen
- Eudemon1000E G55Dokument2 SeitenEudemon1000E G55Akram M. AlmotaaNoch keine Bewertungen
- Request For Proposal Load Balancer SolutionDokument25 SeitenRequest For Proposal Load Balancer SolutionAkram M. AlmotaaNoch keine Bewertungen
- Statement of Work (SoW)Dokument13 SeitenStatement of Work (SoW)Akram M. AlmotaaNoch keine Bewertungen
- Eudemon1000E G5Dokument2 SeitenEudemon1000E G5Akram M. AlmotaaNoch keine Bewertungen
- Nac Fy16-17 RFPDokument8 SeitenNac Fy16-17 RFPAkram M. AlmotaaNoch keine Bewertungen
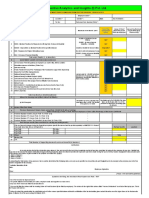
- Budget IT 2016 17Dokument11 SeitenBudget IT 2016 17Akram M. AlmotaaNoch keine Bewertungen
- State of OregonDokument15 SeitenState of OregonAkram M. AlmotaaNoch keine Bewertungen
- IT Systems Acquistion Budget TemplateDokument6 SeitenIT Systems Acquistion Budget TemplateAkram M. AlmotaaNoch keine Bewertungen
- Dbvisit Disaster Recovery Planning ChecklistDokument2 SeitenDbvisit Disaster Recovery Planning ChecklistAkram M. Almotaa100% (1)
- 5 Ways To Get The Most Out of Your IT BudgetDokument1 Seite5 Ways To Get The Most Out of Your IT BudgetAkram M. AlmotaaNoch keine Bewertungen
- How To Decision Your It BudgetDokument21 SeitenHow To Decision Your It BudgetAkram M. AlmotaaNoch keine Bewertungen
- TS-832PX, TS-832PXU-RP, TS-832PXU Compare Products - QNAPDokument12 SeitenTS-832PX, TS-832PXU-RP, TS-832PXU Compare Products - QNAPAkram M. AlmotaaNoch keine Bewertungen
- IT Budget Y2012 - Vae - 2Dokument6 SeitenIT Budget Y2012 - Vae - 2Akram M. AlmotaaNoch keine Bewertungen
- Budget IT Course 1Dokument1 SeiteBudget IT Course 1Akram M. AlmotaaNoch keine Bewertungen
- IT Declaration Form 2014-15 - After BudgetDokument2 SeitenIT Declaration Form 2014-15 - After BudgetAkram M. AlmotaaNoch keine Bewertungen
- Linksys X6200 VDSL ConfigurationDokument2 SeitenLinksys X6200 VDSL ConfigurationAkram M. AlmotaaNoch keine Bewertungen
- Draft Data Center SunterDokument21 SeitenDraft Data Center SunterAkram M. AlmotaaNoch keine Bewertungen
- TaiwanSYS-Bridge Mode - Configuration StepsDokument4 SeitenTaiwanSYS-Bridge Mode - Configuration StepsAkram M. AlmotaaNoch keine Bewertungen
- Modular Data Center MarketDokument3 SeitenModular Data Center MarketAkram M. AlmotaaNoch keine Bewertungen
- PAR IT CapexDokument1 SeitePAR IT CapexAkram M. AlmotaaNoch keine Bewertungen
- Huawei TaiShan 2280 Rack Server White Paper 02Dokument34 SeitenHuawei TaiShan 2280 Rack Server White Paper 02Akram M. AlmotaaNoch keine Bewertungen
- TaiwanSYS-Routed Mode - Configuration StepsDokument6 SeitenTaiwanSYS-Routed Mode - Configuration StepsAkram M. AlmotaaNoch keine Bewertungen
- Huawei SecondNth Data Center High Availability Solution White PaperDokument20 SeitenHuawei SecondNth Data Center High Availability Solution White PaperAkram M. AlmotaaNoch keine Bewertungen
- RFP UB-17-C-18 F5 Load Balancers v3Dokument28 SeitenRFP UB-17-C-18 F5 Load Balancers v3Akram M. AlmotaaNoch keine Bewertungen
- NetBotz 750 - NBRK0750Dokument2 SeitenNetBotz 750 - NBRK0750MERTAL JAYA ABADINoch keine Bewertungen
- Basics of Data Warehousing, MIS and ETLDokument36 SeitenBasics of Data Warehousing, MIS and ETLRavi VakulaNoch keine Bewertungen
- Case Management SystemDokument34 SeitenCase Management SystemRachell AculbeNoch keine Bewertungen
- MIS AssignmentDokument9 SeitenMIS AssignmentSachin NarulaNoch keine Bewertungen
- Red Hat Developer Toolset-4-4.0 Release Notes-En-USDokument20 SeitenRed Hat Developer Toolset-4-4.0 Release Notes-En-USeusphorusNoch keine Bewertungen
- Cdpse Certified Data Privacy Solutions Engineer All in One Exam Guide Peter H Gregory Peter H Gregory Full ChapterDokument51 SeitenCdpse Certified Data Privacy Solutions Engineer All in One Exam Guide Peter H Gregory Peter H Gregory Full Chaptermary.peace563100% (19)
- RUCKUS H550 Data SheetDokument6 SeitenRUCKUS H550 Data SheetMarceloNoch keine Bewertungen
- T Sight TutorialDokument14 SeitenT Sight TutorialTri IriantoNoch keine Bewertungen
- Arm Based MicrocontrollerDokument27 SeitenArm Based MicrocontrollerNavin Khatri100% (1)
- Part2 5548C E60-E200 FunctDokument111 SeitenPart2 5548C E60-E200 FuncterbiliNoch keine Bewertungen
- Smart Test Series: 1-Circle The Correct One. (15x1 15)Dokument3 SeitenSmart Test Series: 1-Circle The Correct One. (15x1 15)Zaheer AhmedNoch keine Bewertungen
- Data Structures: Lecture 3: PointerDokument24 SeitenData Structures: Lecture 3: PointerHard FuckerNoch keine Bewertungen
- Big Data Issue Lack of Skills Chetan KhatriDokument6 SeitenBig Data Issue Lack of Skills Chetan KhatriSantosh Kumar GNoch keine Bewertungen
- Mrutyunjaya ResumeDokument3 SeitenMrutyunjaya ResumeMrutyunjaya padhiNoch keine Bewertungen
- Making Games With Python and PygameDokument94 SeitenMaking Games With Python and PygameTú ViếtNoch keine Bewertungen
- Phase 2 Systems Analysis - Session 5 - Requirements ModelingDokument36 SeitenPhase 2 Systems Analysis - Session 5 - Requirements ModelingLUKAS MahasiswaNoch keine Bewertungen
- CBR SystemDokument94 SeitenCBR SystemJose Rafael CruzNoch keine Bewertungen
- 110 6252 en R2 CLI Reference GuideDokument542 Seiten110 6252 en R2 CLI Reference GuideVictor LeonNoch keine Bewertungen
- Digitally Skilled TeacherDokument21 SeitenDigitally Skilled TeacherNelson VersozaNoch keine Bewertungen
- Classes As Place Holders Components in Super BomDokument24 SeitenClasses As Place Holders Components in Super BomHoài Vũ PhạmNoch keine Bewertungen
- Atoll 2.8 User GuideDokument37 SeitenAtoll 2.8 User GuideDiareza EljabbarNoch keine Bewertungen
- Los Precios No Incluyen Retencion en La FuenteDokument2 SeitenLos Precios No Incluyen Retencion en La FuenteJhon Fredy Perez ZamudioNoch keine Bewertungen
- Evolution of Mobile RadioDokument42 SeitenEvolution of Mobile RadioGopal KrishanNoch keine Bewertungen
- AC2 Practical: Category E (Based On Unit I)Dokument4 SeitenAC2 Practical: Category E (Based On Unit I)Neeta GaikwadNoch keine Bewertungen
- TM355: Communication Technologies: Block 3Dokument49 SeitenTM355: Communication Technologies: Block 3HusseinJdeedNoch keine Bewertungen
- 3DCreative Issue 002 Oct05Dokument70 Seiten3DCreative Issue 002 Oct05takkasilanakhon100% (7)
- Face Recognition Using Pca and Neural Network Model: Submitted by Aadarsh Kumar (15MIS0374Dokument11 SeitenFace Recognition Using Pca and Neural Network Model: Submitted by Aadarsh Kumar (15MIS0374KrajadarshNoch keine Bewertungen
- GPS Bus Tracking SystemDokument16 SeitenGPS Bus Tracking SystemkrishnaNoch keine Bewertungen
- RK 40Dokument2 SeitenRK 40groovey9040Noch keine Bewertungen
- Machine Learning Project Basic - Linear Regression - Kaggle PDFDokument10 SeitenMachine Learning Project Basic - Linear Regression - Kaggle PDFKarthikRaoNoch keine Bewertungen